Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://lu-jacks.com
Are you over 18 and want to see adult content?
A complete backup of https://buyajupiterhome.com
Are you over 18 and want to see adult content?

A complete backup of https://saferinternet.at
Are you over 18 and want to see adult content?
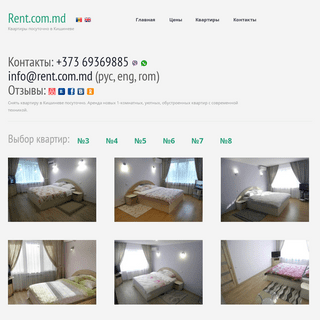
A complete backup of https://rent.com.md
Are you over 18 and want to see adult content?
A complete backup of https://fullycrypto.com
Are you over 18 and want to see adult content?
A complete backup of https://cooperativarascasola.com
Are you over 18 and want to see adult content?
A complete backup of https://syekhnurjati.ac.id
Are you over 18 and want to see adult content?

A complete backup of https://baikalfinans.com
Are you over 18 and want to see adult content?

A complete backup of https://eatmestraws.com
Are you over 18 and want to see adult content?
A complete backup of https://scbraga.pt
Are you over 18 and want to see adult content?
A complete backup of https://robo3d.com
Are you over 18 and want to see adult content?
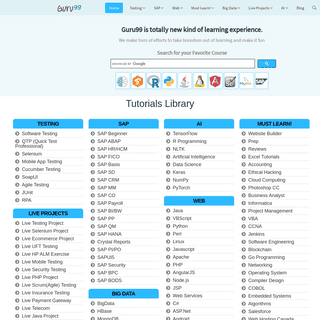
A complete backup of https://guru99.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of natureproductsbg.com
Are you over 18 and want to see adult content?
A complete backup of craftycookingmama.com
Are you over 18 and want to see adult content?

A complete backup of boysandgirlsclubs.org
Are you over 18 and want to see adult content?
A complete backup of inventorsdigest.com
Are you over 18 and want to see adult content?

A complete backup of digitalmedievalist.org
Are you over 18 and want to see adult content?
A complete backup of columnfivemedia.com
Are you over 18 and want to see adult content?

A complete backup of sivasceylannakliyat.com
Are you over 18 and want to see adult content?

A complete backup of seekingathena.com
Are you over 18 and want to see adult content?
Text
solutions.
GUIDE TO IOS APP TRANSPORT SECURITY (ATS) I’ve recently noticed a spike in questions from our customers — and specifically security analysts — about App Transport Security (ATS), or NSAppTransportSecurity, for iOS apps.ATS is a critical security practice for our customers in financial services and other regulated industries. MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right at your fingertips. Cover your bases and answer three key questions. What types of testing are necessary? What are all the areas of coverage? REVERSE ENGINEERING IMESSAGE TO HELP IMPROVE SECURITY Reverse Engineering iMessage: Leveraging the Hardware to Protect the Software. iMessage is a widely used secure messaging app and protocol across the Apple ecosystem. Curious about what it would be like to run iMessage on other platforms, we took a reverse engineering approach to understand how iMessage operates and examine possibilities to DEPARTING EMPLOYEES AND DATA THEFT Outlined in a 2009 study conducted by the Ponemon Institute, data theft is rampant in the business world. The study found that 59% of employees who either quit or are asked to leave take confidential or sensitive business information upon their departure. Done without the employer’s permission, this confidential electronic information hasthe
AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
DEFENSE IN DEPTH: MOBILE SECURITY, MDM, MAM & APP VETTING Mobile App Management (MAM) As a key component of EMM, mobile app management (MAM) provides core functionality to deploy, manage, inventory and wipe internally developed apps (and associated data) and 3rd-party mobile apps pulled from commercial app stores. MAM provides centralized control to push mobile apps to MDM-managed devices andprovides
GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications. UNAUTHORIZED APP DISCOVERED At this point, Routh suspected the app was unauthorized. Upon further analysis of the app, Routh discovered that the unauthorized app was a copy of Aetna’s official Android app with one difference -- the developer injected code into it. That code requested the GET_ACCOUNTS permission from Android, which allows for viewing what accounts are THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams. SOLUTIONS - NOWSECURE Mobile app security solutions for every developer. Learn more about our security testing, mobile pen tests, and industry specificsolutions.
GUIDE TO IOS APP TRANSPORT SECURITY (ATS) I’ve recently noticed a spike in questions from our customers — and specifically security analysts — about App Transport Security (ATS), or NSAppTransportSecurity, for iOS apps.ATS is a critical security practice for our customers in financial services and other regulated industries. MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right at your fingertips. Cover your bases and answer three key questions. What types of testing are necessary? What are all the areas of coverage? REVERSE ENGINEERING IMESSAGE TO HELP IMPROVE SECURITY Reverse Engineering iMessage: Leveraging the Hardware to Protect the Software. iMessage is a widely used secure messaging app and protocol across the Apple ecosystem. Curious about what it would be like to run iMessage on other platforms, we took a reverse engineering approach to understand how iMessage operates and examine possibilities to DEPARTING EMPLOYEES AND DATA THEFT Outlined in a 2009 study conducted by the Ponemon Institute, data theft is rampant in the business world. The study found that 59% of employees who either quit or are asked to leave take confidential or sensitive business information upon their departure. Done without the employer’s permission, this confidential electronic information hasthe
AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
DEFENSE IN DEPTH: MOBILE SECURITY, MDM, MAM & APP VETTING Mobile App Management (MAM) As a key component of EMM, mobile app management (MAM) provides core functionality to deploy, manage, inventory and wipe internally developed apps (and associated data) and 3rd-party mobile apps pulled from commercial app stores. MAM provides centralized control to push mobile apps to MDM-managed devices andprovides
GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications. UNAUTHORIZED APP DISCOVERED At this point, Routh suspected the app was unauthorized. Upon further analysis of the app, Routh discovered that the unauthorized app was a copy of Aetna’s official Android app with one difference -- the developer injected code into it. That code requested the GET_ACCOUNTS permission from Android, which allows for viewing what accounts are SOLUTIONS - NOWSECURE Mobile app security solutions for every developer. Learn more about our security testing, mobile pen tests, and industry specificsolutions.
ABOUT NOWSECURE: THE MOBILE SECURITY TECHNOLOGY COMPANY We are the experts in mobile app security testing software and services. Our mission is to deliver maximum customer value through the speed, accuracy, and efficiency of the NowSecure Platform with the most comprehensive mobile app security testing coverage of security, compliance and privacy risk vectors across third-party, custom, and business-critical mobile apps. NOWSECURE ANNOUNCES NOWSECURE WORKSTATION 6.0 Purpose-built for mobile pen testers and security analysts, NowSecure Workstation 6.0 enables deep interactive testing of mobile apps with a significant performance boost in user experience, testing speed and coverage, and extensibility to rapidly integrate additional testingtools and scripts.
THE ANALYST’S GUIDE TO MITM ISSUES IN MOBILE APPS The most common questions I get from mobile application security analysts pertain to man-in-the-middle (MiTM) attacks. Many people don’t understand the repercussions of these attacks or know what security controls to incorporate in their mobile apps to avoid theseissues.
NOWSECURE
�2021 NowSecure, Inc. All Rights Reserved. Privacy Policy FEDERAL GOVERNMENT MOBILE APP SECURITY CONCERNS NowSecure’s automated mobile app security testing solution also provides a repeatable and scalable process that maps findings to widely recognized standards such as CWE, CVE and NIAP to create a baseline of findings. This makes it possible for federal agencies to quantify and then remediate the risk. Many federal agencies have heldthemselves
NOWSECURE PLATFORM
How it Works No source code is required to get started, simply upload a compiled mobile binary from your development team via web, API or CI/CD Plugin or download a MOBILE SECURITY PRIMER · SECURE MOBILE DEVELOPMENT BEST Mobile security entails many of the challenges of Web security – a wide audience, rapid development, and continuous network connectivity – combined with the risks common to more traditional fat client applications such as buffer management, local encryption, and malware. One of the unique features to the mobile environment is the prevalence IMPLEMENT SECURE DATA STORAGE · SECURE MOBILE DEVELOPMENT Read PDF Implement Secure Data Storage Details. Storing data securely on a mobile device requires proper technique. Whenever possible, simply do not store/cache data. This is the most sure way to avoid data compromise on the device. ANDROID APPS TESTED AND GOOGLE SAFETYNET ATTESTATION API The SafetyNet Attestation API can prevent an app from running on a compromised device and potentially spilling sensitive user data. Using the attestation API is a great way to make sensitive apps as secure as possible. On the other hand, people that use a modified version of Android won’t be able to use apps that implement the check. THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams. GUIDE TO IOS APP TRANSPORT SECURITY (ATS) I’ve recently noticed a spike in questions from our customers — and specifically security analysts — about App Transport Security (ATS), or NSAppTransportSecurity, for iOS apps.ATS is a critical security practice for our customers in financial services and other regulated industries. PANDAS AND TIGERS AND BEARS: REASONS TO WORRY ABOUT STATE In its recent Global Threat Report, Crowdstrike reported a 21% increase in nation-state cyberattacks in 2020. Crowdstrike is one of several intelligence sources that use mythological labeling of threat actor organizations with loaded emotional connotations like Wicked Panda, Charming Kitten and Cozy Bear.So how ready for Bear should mobile app developers and mobile app security analysts be? MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right at your fingertips. Cover your bases and answer three key questions. What types of testing are necessary? What are all the areas of coverage?CHEE-YOUNG KIM
Co-Founder. As a Co-founder, Chee-Young has been able to scale the company and brings 20+ years of experience in financial operations for large enterprises. She is passionate about bringing awareness of Science, Technology, Engineering, Arts and Math (STEAM) related education and careers to women and girls. She received a B.S. inAccountancy
AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
REVERSE ENGINEERING WITH JAVASCRIPT view raw hello.c hosted with _ by GitHub $ clang hello.c -o hello $ ./hello f() is at 0x106a81ec0 Number: 0 Number: 1 Number: 2 I . Take note of the address of f(), which is 0x106a81ec0 here. This is the memory address where the function f() starts inside the hello appUs process, and due to Address Space Layout Randomization it will most likely be different between each run. DEFENSE IN DEPTH: MOBILE SECURITY, MDM, MAM & APP VETTING Mobile App Management (MAM) As a key component of EMM, mobile app management (MAM) provides core functionality to deploy, manage, inventory and wipe internally developed apps (and associated data) and 3rd-party mobile apps pulled from commercial app stores. MAM provides centralized control to push mobile apps to MDM-managed devices andprovides
TLS 1.3: 4 KEY TAKEAWAYS FOR MOBILE SECURITY TEAMS The most exciting development of TLS 1.3 is the faster, simplified handshake process. TLS uses symmetric cryptography to encrypt data, the keys of which are uniquely generated via a secret negotiation at the start of a session, or also known as the TLS handshake. TLS 1.3’s handshake shortens process time and reduces session latencygiven it
IMPLEMENT SECURE DATA STORAGE · SECURE MOBILE DEVELOPMENT Read PDF Implement Secure Data Storage Details. Storing data securely on a mobile device requires proper technique. Whenever possible, simply do not store/cache data. This is the most sure way to avoid data compromise on the device. THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams. GUIDE TO IOS APP TRANSPORT SECURITY (ATS) I’ve recently noticed a spike in questions from our customers — and specifically security analysts — about App Transport Security (ATS), or NSAppTransportSecurity, for iOS apps.ATS is a critical security practice for our customers in financial services and other regulated industries. PANDAS AND TIGERS AND BEARS: REASONS TO WORRY ABOUT STATE In its recent Global Threat Report, Crowdstrike reported a 21% increase in nation-state cyberattacks in 2020. Crowdstrike is one of several intelligence sources that use mythological labeling of threat actor organizations with loaded emotional connotations like Wicked Panda, Charming Kitten and Cozy Bear.So how ready for Bear should mobile app developers and mobile app security analysts be? MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right at your fingertips. Cover your bases and answer three key questions. What types of testing are necessary? What are all the areas of coverage?CHEE-YOUNG KIM
Co-Founder. As a Co-founder, Chee-Young has been able to scale the company and brings 20+ years of experience in financial operations for large enterprises. She is passionate about bringing awareness of Science, Technology, Engineering, Arts and Math (STEAM) related education and careers to women and girls. She received a B.S. inAccountancy
AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
REVERSE ENGINEERING WITH JAVASCRIPT view raw hello.c hosted with _ by GitHub $ clang hello.c -o hello $ ./hello f() is at 0x106a81ec0 Number: 0 Number: 1 Number: 2 I . Take note of the address of f(), which is 0x106a81ec0 here. This is the memory address where the function f() starts inside the hello appUs process, and due to Address Space Layout Randomization it will most likely be different between each run. DEFENSE IN DEPTH: MOBILE SECURITY, MDM, MAM & APP VETTING Mobile App Management (MAM) As a key component of EMM, mobile app management (MAM) provides core functionality to deploy, manage, inventory and wipe internally developed apps (and associated data) and 3rd-party mobile apps pulled from commercial app stores. MAM provides centralized control to push mobile apps to MDM-managed devices andprovides
TLS 1.3: 4 KEY TAKEAWAYS FOR MOBILE SECURITY TEAMS The most exciting development of TLS 1.3 is the faster, simplified handshake process. TLS uses symmetric cryptography to encrypt data, the keys of which are uniquely generated via a secret negotiation at the start of a session, or also known as the TLS handshake. TLS 1.3’s handshake shortens process time and reduces session latencygiven it
IMPLEMENT SECURE DATA STORAGE · SECURE MOBILE DEVELOPMENT Read PDF Implement Secure Data Storage Details. Storing data securely on a mobile device requires proper technique. Whenever possible, simply do not store/cache data. This is the most sure way to avoid data compromise on the device.EVENTS ARCHIVE
NowSecure is a proud sponosr of DevSecOps Day at RSA Conference. Join us on May 19th for thought-provoking keynotes. cutting-edge innovation, and interactive networking opportunities connecting cybersecurity's best minds and biggest ideas. NOWSECURE ANNOUNCES NOWSECURE WORKSTATION 6.0 Purpose-built for mobile pen testers and security analysts, NowSecure Workstation 6.0 enables deep interactive testing of mobile apps with a significant performance boost in user experience, testing speed and coverage, and extensibility to rapidly integrate additional testingtools and scripts.
MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right at your fingertips. Cover your bases and answer three key questions. What types of testing are necessary? What are all the areas of coverage? FEDERAL GOVERNMENT MOBILE APP SECURITY CONCERNS NowSecure’s automated mobile app security testing solution also provides a repeatable and scalable process that maps findings to widely recognized standards such as CWE, CVE and NIAP to create a baseline of findings. This makes it possible for federal agencies to quantify and then remediate the risk. Many federal agencies have heldthemselves
DEPARTING EMPLOYEES AND DATA THEFT Outlined in a 2009 study conducted by the Ponemon Institute, data theft is rampant in the business world. The study found that 59% of employees who either quit or are asked to leave take confidential or sensitive business information upon their departure. Done without the employer’s permission, this confidential electronic information hasthe
4 COMMON MOBILE APP SECURITY RISKS YOU SHOULD NOT IGNORE Kevin Beaver, CISSP is an information security consultant, writer, and professional speaker with Atlanta, GA-based Principle Logic, LLC with over 28 years of experience in IT and 22 years in information security. He specializes in performing independent security assessments, with a focus on application and IoT testing, to help businesses minimize their IT risks, take the pain out of compliance CVSS SCORES TO MEASURE MOBILE APP RISK Developed by the Forum for Incident Response and Security Teams (FIRST), the Common Vulnerability Scoring System (CVSS) is a universal open and standardized method for rating IT vulnerabilities and determining the urgency of response. This CVSS value, which ranges from zero to 10, helps security analysts prioritize risk as they lookto identify
HOW MOBILE APPS FUEL THE FOOTBALL FAN EXPERIENCE NFL teams redesigned their mobile apps to enhance the fan experience. Fans can use their smartphones for digital ticketing, live video streaming, in-seat concessions, and augmented reality. However, a NowSecure analysis shows most of these apps have privacy risks,especially on iOS.
GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications. ACCUWEATHER IOS APP PRIVACY ISSUES: LESSONS & TAKEAWAYS AccuWeather iOS app sent location data to third parties. Last week, a security researcher published an article claiming that the AccuWeather app for iOS sent data to a third party including: GPS data – longitude, latitude, altitude, speed. Wi-Fi router data – Basic Service Set Identifier (BSSID) — the MAC address for the wirelessaccess
THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams. SOLUTIONS - NOWSECURE Mobile app security solutions for every developer. Learn more about our security testing, mobile pen tests, and industry specificsolutions.
GUIDE TO IOS APP TRANSPORT SECURITY (ATS) I’ve recently noticed a spike in questions from our customers — and specifically security analysts — about App Transport Security (ATS), or NSAppTransportSecurity, for iOS apps.ATS is a critical security practice for our customers in financial services and other regulated industries.SUPPORT - NOWSECURE
NowSecure experts are here to help. There are several support options available to NowSecure customers. Want to quickly search our knowledge base of existing materials? Sign into NowSecure Help Center for self-service tools such as user guides, trouble shooting tips, release notes, how-to videos, technical blogs, and to open a support ticket.CHEE-YOUNG KIM
Co-Founder. As a Co-founder, Chee-Young has been able to scale the company and brings 20+ years of experience in financial operations for large enterprises. She is passionate about bringing awareness of Science, Technology, Engineering, Arts and Math (STEAM) related education and careers to women and girls. She received a B.S. inAccountancy
GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications.NOWSECURE
�2021 NowSecure, Inc. All Rights Reserved. Privacy Policy DEPARTING EMPLOYEES AND DATA THEFT Outlined in a 2009 study conducted by the Ponemon Institute, data theft is rampant in the business world. The study found that 59% of employees who either quit or are asked to leave take confidential or sensitive business information upon their departure. Done without the employer’s permission, this confidential electronic information hasthe
AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
NOWSECURE PLATFORM
How it Works No source code is required to get started, simply upload a compiled mobile binary from your development team via web, API or CI/CD Plugin or download a THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams. SOLUTIONS - NOWSECURE Mobile app security solutions for every developer. Learn more about our security testing, mobile pen tests, and industry specificsolutions.
GUIDE TO IOS APP TRANSPORT SECURITY (ATS) I’ve recently noticed a spike in questions from our customers — and specifically security analysts — about App Transport Security (ATS), or NSAppTransportSecurity, for iOS apps.ATS is a critical security practice for our customers in financial services and other regulated industries.SUPPORT - NOWSECURE
NowSecure experts are here to help. There are several support options available to NowSecure customers. Want to quickly search our knowledge base of existing materials? Sign into NowSecure Help Center for self-service tools such as user guides, trouble shooting tips, release notes, how-to videos, technical blogs, and to open a support ticket.CHEE-YOUNG KIM
Co-Founder. As a Co-founder, Chee-Young has been able to scale the company and brings 20+ years of experience in financial operations for large enterprises. She is passionate about bringing awareness of Science, Technology, Engineering, Arts and Math (STEAM) related education and careers to women and girls. She received a B.S. inAccountancy
GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications.NOWSECURE
�2021 NowSecure, Inc. All Rights Reserved. Privacy Policy DEPARTING EMPLOYEES AND DATA THEFT Outlined in a 2009 study conducted by the Ponemon Institute, data theft is rampant in the business world. The study found that 59% of employees who either quit or are asked to leave take confidential or sensitive business information upon their departure. Done without the employer’s permission, this confidential electronic information hasthe
AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
NOWSECURE PLATFORM
How it Works No source code is required to get started, simply upload a compiled mobile binary from your development team via web, API or CI/CD Plugin or download aNOWSECURE PLATFORM
Streamline modern testing practices. NowSecure Platform is tailored to meet the unique needs and complex infrastructure of the modern mobile SDLC, providing security and privacy testing solutions, including API testing, that are continuous, customizable, and accurate. CUSTOMERS - NOWSECURE The world's most demanding organizations and advanced security teams trust NowSecure for mobile app security and privacy testing of custom-developed, commercial, and business-critical mobile apps. Learn more about NowSecure customers and the vast array of industries protected from unsafe mobile apps. NOWSECURE WORKSTATION NowSecure Workstation is the ultimate power tool for mobile app security analysts and pen tester productivity. Our pre-configured hardware and software kit compresses mobile app vulnerability assessment time from days to hours. See how you can achieveNOWSECURE
�2021 NowSecure, Inc. All Rights Reserved. Privacy Policy MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right at your fingertips. Cover your bases and answer three key questions. What types of testing are necessary? What are all the areas of coverage? STATIC VS DYNAMIC SECURITY TESTING FOR MOBILE APPS A lot of organizations out there are trying to fix their app as quickly as possible. False positives really cut down on the time they can spend doing better testing, fixing bigger problems, and really helping train their security analysts and developers. False positives suck. NowSecure’s dynamic security testing can help transform yourapp
MOBILE APP SECURITY VS WEB APP SECURITY NowSecure found the best way to deal with , coming from our forensics background, is in a very empirical way. You can do a bunch of testing of your code. You can do source code analysis and typically generate a lot of false positives. You spend a lot of time looking at the results. REVERSE ENGINEERING WITH JAVASCRIPT view raw hello.c hosted with _ by GitHub $ clang hello.c -o hello $ ./hello f() is at 0x106a81ec0 Number: 0 Number: 1 Number: 2 I . Take note of the address of f(), which is 0x106a81ec0 here. This is the memory address where the function f() starts inside the hello appUs process, and due to Address Space Layout Randomization it will most likely be different between each run. DEFENSE IN DEPTH: MOBILE SECURITY, MDM, MAM & APP VETTING Mobile App Management (MAM) As a key component of EMM, mobile app management (MAM) provides core functionality to deploy, manage, inventory and wipe internally developed apps (and associated data) and 3rd-party mobile apps pulled from commercial app stores. MAM provides centralized control to push mobile apps to MDM-managed devices andprovides
IMPLEMENT SECURE DATA STORAGE · SECURE MOBILE DEVELOPMENT Read PDF Implement Secure Data Storage Details. Storing data securely on a mobile device requires proper technique. Whenever possible, simply do not store/cache data. This is the most sure way to avoid data compromise on the device. THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams. SOLUTIONS - NOWSECURE Mobile app security solutions for every developer. Learn more about our security testing, mobile pen tests, and industry specificsolutions.
GUIDE TO IOS APP TRANSPORT SECURITY (ATS) I’ve recently noticed a spike in questions from our customers — and specifically security analysts — about App Transport Security (ATS), or NSAppTransportSecurity, for iOS apps.ATS is a critical security practice for our customers in financial services and other regulated industries.SUPPORT - NOWSECURE
NowSecure experts are here to help. There are several support options available to NowSecure customers. Want to quickly search our knowledge base of existing materials? Sign into NowSecure Help Center for self-service tools such as user guides, trouble shooting tips, release notes, how-to videos, technical blogs, and to open a support ticket.CHEE-YOUNG KIM
Co-Founder. As a Co-founder, Chee-Young has been able to scale the company and brings 20+ years of experience in financial operations for large enterprises. She is passionate about bringing awareness of Science, Technology, Engineering, Arts and Math (STEAM) related education and careers to women and girls. She received a B.S. inAccountancy
GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications.NOWSECURE
�2021 NowSecure, Inc. All Rights Reserved. Privacy Policy DEPARTING EMPLOYEES AND DATA THEFT Outlined in a 2009 study conducted by the Ponemon Institute, data theft is rampant in the business world. The study found that 59% of employees who either quit or are asked to leave take confidential or sensitive business information upon their departure. Done without the employer’s permission, this confidential electronic information hasthe
AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
NOWSECURE PLATFORM
How it Works No source code is required to get started, simply upload a compiled mobile binary from your development team via web, API or CI/CD Plugin or download a THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams. SOLUTIONS - NOWSECURE Mobile app security solutions for every developer. Learn more about our security testing, mobile pen tests, and industry specificsolutions.
GUIDE TO IOS APP TRANSPORT SECURITY (ATS) I’ve recently noticed a spike in questions from our customers — and specifically security analysts — about App Transport Security (ATS), or NSAppTransportSecurity, for iOS apps.ATS is a critical security practice for our customers in financial services and other regulated industries.SUPPORT - NOWSECURE
NowSecure experts are here to help. There are several support options available to NowSecure customers. Want to quickly search our knowledge base of existing materials? Sign into NowSecure Help Center for self-service tools such as user guides, trouble shooting tips, release notes, how-to videos, technical blogs, and to open a support ticket.CHEE-YOUNG KIM
Co-Founder. As a Co-founder, Chee-Young has been able to scale the company and brings 20+ years of experience in financial operations for large enterprises. She is passionate about bringing awareness of Science, Technology, Engineering, Arts and Math (STEAM) related education and careers to women and girls. She received a B.S. inAccountancy
GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications.NOWSECURE
�2021 NowSecure, Inc. All Rights Reserved. Privacy Policy DEPARTING EMPLOYEES AND DATA THEFT Outlined in a 2009 study conducted by the Ponemon Institute, data theft is rampant in the business world. The study found that 59% of employees who either quit or are asked to leave take confidential or sensitive business information upon their departure. Done without the employer’s permission, this confidential electronic information hasthe
AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
NOWSECURE PLATFORM
How it Works No source code is required to get started, simply upload a compiled mobile binary from your development team via web, API or CI/CD Plugin or download aNOWSECURE PLATFORM
Streamline modern testing practices. NowSecure Platform is tailored to meet the unique needs and complex infrastructure of the modern mobile SDLC, providing security and privacy testing solutions, including API testing, that are continuous, customizable, and accurate. CUSTOMERS - NOWSECURE The world's most demanding organizations and advanced security teams trust NowSecure for mobile app security and privacy testing of custom-developed, commercial, and business-critical mobile apps. Learn more about NowSecure customers and the vast array of industries protected from unsafe mobile apps. NOWSECURE WORKSTATION NowSecure Workstation is the ultimate power tool for mobile app security analysts and pen tester productivity. Our pre-configured hardware and software kit compresses mobile app vulnerability assessment time from days to hours. See how you can achieveNOWSECURE
�2021 NowSecure, Inc. All Rights Reserved. Privacy Policy MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right at your fingertips. Cover your bases and answer three key questions. What types of testing are necessary? What are all the areas of coverage? STATIC VS DYNAMIC SECURITY TESTING FOR MOBILE APPS A lot of organizations out there are trying to fix their app as quickly as possible. False positives really cut down on the time they can spend doing better testing, fixing bigger problems, and really helping train their security analysts and developers. False positives suck. NowSecure’s dynamic security testing can help transform yourapp
MOBILE APP SECURITY VS WEB APP SECURITY NowSecure found the best way to deal with , coming from our forensics background, is in a very empirical way. You can do a bunch of testing of your code. You can do source code analysis and typically generate a lot of false positives. You spend a lot of time looking at the results. REVERSE ENGINEERING WITH JAVASCRIPT view raw hello.c hosted with _ by GitHub $ clang hello.c -o hello $ ./hello f() is at 0x106a81ec0 Number: 0 Number: 1 Number: 2 I . Take note of the address of f(), which is 0x106a81ec0 here. This is the memory address where the function f() starts inside the hello appUs process, and due to Address Space Layout Randomization it will most likely be different between each run. DEFENSE IN DEPTH: MOBILE SECURITY, MDM, MAM & APP VETTING Mobile App Management (MAM) As a key component of EMM, mobile app management (MAM) provides core functionality to deploy, manage, inventory and wipe internally developed apps (and associated data) and 3rd-party mobile apps pulled from commercial app stores. MAM provides centralized control to push mobile apps to MDM-managed devices andprovides
IMPLEMENT SECURE DATA STORAGE · SECURE MOBILE DEVELOPMENT Read PDF Implement Secure Data Storage Details. Storing data securely on a mobile device requires proper technique. Whenever possible, simply do not store/cache data. This is the most sure way to avoid data compromise on the device. THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams.CHEE-YOUNG KIM
Chee-Young co-founded NowSecure in 2009 and is passionate about spreading awareness of tech-related careers to women and girls. MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right at your fingertips. Cover your bases and answer three key questions. What types of testing are necessary? What are all the areas of coverage?NOWSECURE PLATFORM
PRIVACY DISCLOSURE: NowSecure uses first party and third party cookies to provide functions of this website and our services, to uniquely identify visitors, to analyze use REVERSE ENGINEERING WITH JAVASCRIPT view raw hello.c hosted with _ by GitHub $ clang hello.c -o hello $ ./hello f() is at 0x106a81ec0 Number: 0 Number: 1 Number: 2 I . Take note of the address of f(), which is 0x106a81ec0 here. This is the memory address where the function f() starts inside the hello appUs process, and due to Address Space Layout Randomization it will most likely be different between each run. AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications. MOBILE SECURITY PRIMER · SECURE MOBILE DEVELOPMENT BESTSEE MORE ONBOOKS.NOWSECURE.COM
TLS 1.3: 4 KEY TAKEAWAYS FOR MOBILE SECURITY TEAMS The most exciting development of TLS 1.3 is the faster, simplified handshake process. TLS uses symmetric cryptography to encrypt data, the keys of which are uniquely generated via a secret negotiation at the start of a session, or also known as the TLS handshake. TLS 1.3’s handshake shortens process time and reduces session latencygiven it
IMPLEMENT SECURE DATA STORAGE · SECURE MOBILE DEVELOPMENT Read PDF Implement Secure Data Storage Details. Storing data securely on a mobile device requires proper technique. Whenever possible, simply do not store/cache data. This is the most sure way to avoid data compromise on the device. THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams.CHEE-YOUNG KIM
Chee-Young co-founded NowSecure in 2009 and is passionate about spreading awareness of tech-related careers to women and girls. MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right at your fingertips. Cover your bases and answer three key questions. What types of testing are necessary? What are all the areas of coverage?NOWSECURE PLATFORM
PRIVACY DISCLOSURE: NowSecure uses first party and third party cookies to provide functions of this website and our services, to uniquely identify visitors, to analyze use REVERSE ENGINEERING WITH JAVASCRIPT view raw hello.c hosted with _ by GitHub $ clang hello.c -o hello $ ./hello f() is at 0x106a81ec0 Number: 0 Number: 1 Number: 2 I . Take note of the address of f(), which is 0x106a81ec0 here. This is the memory address where the function f() starts inside the hello appUs process, and due to Address Space Layout Randomization it will most likely be different between each run. AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD AFLogical™ Open Source Edition Now Available for Download. July 29, 2017. Mobile Security Solutions. ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, Android aficionados, and forensics gurus alike. Better yet, download the free,open
GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications. MOBILE SECURITY PRIMER · SECURE MOBILE DEVELOPMENT BESTSEE MORE ONBOOKS.NOWSECURE.COM
TLS 1.3: 4 KEY TAKEAWAYS FOR MOBILE SECURITY TEAMS The most exciting development of TLS 1.3 is the faster, simplified handshake process. TLS uses symmetric cryptography to encrypt data, the keys of which are uniquely generated via a secret negotiation at the start of a session, or also known as the TLS handshake. TLS 1.3’s handshake shortens process time and reduces session latencygiven it
IMPLEMENT SECURE DATA STORAGE · SECURE MOBILE DEVELOPMENT Read PDF Implement Secure Data Storage Details. Storing data securely on a mobile device requires proper technique. Whenever possible, simply do not store/cache data. This is the most sure way to avoid data compromise on the device. ANDROID APPS PUT DATA OF 100M PLAY STORE USERS AT RISK Security researchers have discovered that some popular Android apps leaked the data of over 100 million users after developers failed due to a misconfiguration of third party cloud services.SUPPORT - NOWSECURE
NowSecure experts are here to help. There are several support options available to NowSecure customers. Want to quickly search our knowledge base of existing materials? Sign into NowSecure Help Center for self-service tools such as user guides, trouble shooting tips, release notes, how-to videos, technical blogs, and to open a support ticket. NOWSECURE ANNOUNCES WORLD'S MOST ADVANCED 3RD-PARTY MOBILE NowSecure Announces World’s Most Advanced 3rd-Party Mobile App Security Vetting NowSecure INTEL -- the latest addition to the NowSecure Platform -- empowers enterprises with the highest quality 3rd-party mobile app security intelligence REVERSE ENGINEERING IMESSAGE TO HELP IMPROVE SECURITY Reverse Engineering iMessage: Leveraging the Hardware to Protect the Software. iMessage is a widely used secure messaging app and protocol across the Apple ecosystem. Curious about what it would be like to run iMessage on other platforms, we took a reverse engineering approach to understand how iMessage operates and examine possibilities to GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications. HOW MOBILE APPS FUEL THE FOOTBALL FAN EXPERIENCE NFL teams redesigned their mobile apps to enhance the fan experience. Fans can use their smartphones for digital ticketing, live video streaming, in-seat concessions, and augmented reality. However, a NowSecure analysis shows most of these apps have privacy risks,especially on iOS.
THE ANALYST’S GUIDE TO MITM ISSUES IN MOBILE APPS The most common questions I get from mobile application security analysts pertain to man-in-the-middle (MiTM) attacks. Many people don’t understand the repercussions of these attacks or know what security controls to incorporate in their mobile apps to avoid theseissues.
CVSS SCORES TO MEASURE MOBILE APP RISK At NowSecure, we believe in referencing open-source standards and industry guidelines when evaluating mobile risk. With the ever-changing mobile landscape, we believe these guidelines offer incredible benefit to security leaders when identifying and prioritizing the remediation of code defects and vulnerabilities as well as tracking metrics to show company leadership. AVOID QUERY STRING FOR SENSITIVE DATA · SECURE MOBILE Details. A major bank breach was executed with a simple query string modification “attack.”. Query string parameters are more visible and can often be unexpectedly cached (web history, webserver or proxy logs, etc.) Using an unencrypted query string for meaningful data should be avoided. If credentials are transmitted as query string ACCUWEATHER IOS APP PRIVACY ISSUES: LESSONS AccuWeather iOS app sent location data to third parties. Last week, a security researcher published an article claiming that the AccuWeather app for iOS sent data to a third party including: GPS data – longitude, latitude, altitude, speed. Wi-Fi router data – Basic Service Set Identifier (BSSID) — the MAC address for the wirelessaccess
THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams. SOLUTIONS - NOWSECURE Mobile app security solutions for every developer. Learn more about our security testing, mobile pen tests, and industry specificsolutions.
NOWSECURE ANNOUNCES NOWSECURE WORKSTATION 6.0 Purpose-built for mobile pen testers and security analysts, NowSecure Workstation 6.0 enables deep interactive testing of mobile apps with a significant performance boost in user experience, testing speed and coverage, and extensibility to rapidly integrate additional testingtools and scripts.
CHEE-YOUNG KIM
Chee-Young co-founded NowSecure in 2009 and is passionate about spreading awareness of tech-related careers to women and girls.NOWSECURE PLATFORM
PRIVACY DISCLOSURE: NowSecure uses first party and third party cookies to provide functions of this website and our services, to uniquely identify visitors, to analyze useSUPPORT - NOWSECURE
Support. Questions? NowSecure experts are here to help. There are several support options available to NowSecure customers. Want to quickly search our knowledge base of existing materials? AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, VULNERABILITY TEST SUITE FOR ANDROID Vulnerability Test Suite is an open source mobile app designed to check for vulnerabilities on an Android device and give users the status of potential vulnerabilities. MOBILE SECURITY PRIMER · SECURE MOBILE DEVELOPMENT BESTSEE MORE ONBOOKS.NOWSECURE.COM
UNAUTHORIZED APP DISCOVERED Unauthorized app discovered. Counterfeit apps developed by unauthorized parties and published to official or unofficial app stores (and elsewhere on the Internet) can damage a company’s brand name and put their customers at risk. THE MOBILE APP SECURITY EXPERTS| NOWSECUREPRODUCTSSOLUTIONSCUSTOMERSRESOURCESCOMPANYNOWSECURE PLATFORM Visibility into supply chain risk across mobile app portfolio . Continuously monitor all the mobile apps you build, buy and use for standards-based security, privacy, and compliance risks with insight and collaboration across dev, security, mobile and GRC teams. SOLUTIONS - NOWSECURE Mobile app security solutions for every developer. Learn more about our security testing, mobile pen tests, and industry specificsolutions.
NOWSECURE ANNOUNCES NOWSECURE WORKSTATION 6.0 Purpose-built for mobile pen testers and security analysts, NowSecure Workstation 6.0 enables deep interactive testing of mobile apps with a significant performance boost in user experience, testing speed and coverage, and extensibility to rapidly integrate additional testingtools and scripts.
CHEE-YOUNG KIM
Chee-Young co-founded NowSecure in 2009 and is passionate about spreading awareness of tech-related careers to women and girls.NOWSECURE PLATFORM
PRIVACY DISCLOSURE: NowSecure uses first party and third party cookies to provide functions of this website and our services, to uniquely identify visitors, to analyze useSUPPORT - NOWSECURE
Support. Questions? NowSecure experts are here to help. There are several support options available to NowSecure customers. Want to quickly search our knowledge base of existing materials? AFLOGICAL™ OPEN SOURCE EDITION NOW AVAILABLE FOR DOWNLOAD ### We have released AFLogical 㢠Open Source Edition on our GitHub. The Open Source Edition has been released for use by non-law enforcement personnel, VULNERABILITY TEST SUITE FOR ANDROID Vulnerability Test Suite is an open source mobile app designed to check for vulnerabilities on an Android device and give users the status of potential vulnerabilities. MOBILE SECURITY PRIMER · SECURE MOBILE DEVELOPMENT BESTSEE MORE ONBOOKS.NOWSECURE.COM
UNAUTHORIZED APP DISCOVERED Unauthorized app discovered. Counterfeit apps developed by unauthorized parties and published to official or unofficial app stores (and elsewhere on the Internet) can damage a company’s brand name and put their customers at risk. ABOUT NOWSECURE: THE MOBILE SECURITY TECHNOLOGY COMPANY We are the experts in mobile app security testing software and services. Our mission is to deliver maximum customer value through the speed, accuracy, and efficiency of the NowSecure Platform with the most comprehensive mobile app security testing coverage of security, compliance and privacy risk vectors across third-party, custom, and business-critical mobile apps.NOWSECURE PLATFORM
Fully automate security and privacy testing with standards for mobile apps you build and use within one easy-to-use portal. With NowSecure Platform, test pre-prod and/or published iOS/Android binaries while monitoring the apps that power your workforce. NOWSECURE WORKSTATION NowSecure Workstation is the ultimate power tool for mobile app security analysts and pen tester productivity. Our pre-configured hardware and software kit compresses mobile app vulnerability assessment time from days to hours. See how you can achieve NOWSECURE ANNOUNCES NOWSECURE WORKSTATION 6.0 Purpose-built for mobile pen testers and security analysts, NowSecure Workstation 6.0 enables deep interactive testing of mobile apps with a significant performance boost in user experience, testing speed and coverage, and extensibility to rapidly integrate additional testingtools and scripts.
MOBILE APP SECURITY BLOG: NEWS, ADVICE, AND RESEARCH A mobile app security blog with the latest information, advice, research, and inspiration about mobile app security from renowned mobile security experts. MOBILE APP SECURITY TESTING CHECKLIST A complete list of mobile app security testing requirements, right atyour fingertips.
NOWSECURE
STATIC VS DYNAMIC SECURITY TESTING FOR MOBILE APPS Tony Ramirez is a Senior Application Security Analyst at NowSecure. He holds a master’s degree in cyber forensics and security from Illinois Institute of Technology. GUIDE TO IOS APP TRANSPORT SECURITY (ATS) I’ve recently noticed a spike in questions from our customers — and specifically security analysts — about App Transport Security (ATS), or NSAppTransportSecurity, for iOS apps.ATS is a critical security practice for our customers in financial services and other regulated industries. GUIDE TO NETWORK SECURITY CONFIGURATION IN ANDROID P When Android 6.0 Marshmallow was released, Google introduced the manifest attribute android:usesCleartextTraffic as a means to protect against accidental use of cleartext traffic. Android 7.0 Nougat extended this attribute by introducing the Android Network Security Configuration feature, which allows developers to be more prescriptive about secure communications. NEWS: NowSecure Announces API Security Testing Search this website __ Contact UsTry for Free
Deliver Secure Mobile Apps FasterMenu
* Products Menu
* NowSecure Platform * NowSecure Workstation* NowSecure Data
* NowSecure Services* Solutions Menu
* Solutions by Need
Menu
* Mobile App Security Testing * API Security Testing* Mobile DevSecOps
* Mobile App Penetration Testing * Mobile App Vetting for Supply Chain * Solutions by IndustryMenu
* Government
* Financial Services * Retail and Hospitality* Customers
* Resources Menu
* Mobile App Security In the News * Mobile App Security Library* Blog
* Events
* Open Source Software Menu* Radare
* Frida
* Capstone
* Company Menu
* Team
* Partners
* Investors
* Media
* Careers
* Contact Us
Contact Us Try for Free WEB TRAFFIC HAS MOVED TO MOBILE APPS...HAS YOUR SECURITY?
Over 60% of digital media time is now spent on mobile apps – and attackers are on the move. Test mobile app security and privacy with automation. Manage mobile risk. Reduce costs. Scale growth in amobile-first world.
Try It Free
Learn More
* As Featured In
*
*
*
*
*
*
DELIVER SECURE MOBILE APPS FASTER SCALABLE AUTOMATION SOFTWARE PURPOSE-BUILT FOR MOBILE APPS Automate security tests on-demand or integrated directly into your mobile CI/CD pipeline. Get high accuracy coverage through static, dynamic and interactive analysis of iOS/Android binaries and connected APIs on real devices.Learn more >
VISIBILITY INTO RISK ACROSS MOBILE APPS YOU BUILD AND USE Ensure consistent security & privacy testing and continuously monitor all the mobile apps you build and use with insight and collaboration across dev, security, mobile and GRC teams.Learn more >
MOBILE APP PEN TESTING SERVICES, TRAINING AND MORE From urgent testing deadlines to setting up a mobile appsec program and accelerating with software, our team’s expertise supports you throughout your mobile app journey.Learn more >
THE PREFERRED CHOICE OF MOBILE APP SECURITY & MOBILE DEVOPS TEAMS Learn why industry leaders choose NowSecure > CASE STUDY: U.S. MARSHALS SERVICE We rarely get things that are ready to go out of the box, but when we received the NowSecure solution, we were up and running the same day." Derrick Smith CEO, NSight365Read the Case Study
EXPERIENCE BEST-IN-CLASS MOBILE APP SECURITY TESTING (MAST) IDC named NowSecure a Leader in 2 Marketscape reports for MAST. Seewhy.
Try it free
NOWSECURE PRODUCTS
* NowSecure Platform * NowSecure Workstation* NowSecure Data
* NowSecure ServicesSOLUTIONS
* By Need
* By Industry
RESOURCES
* Resource Library
* Events
* Blog
* OSS
* Customer Support
COMPANY
* About Us
* Team
* Partners
* Careers
* Customers
* Contact Us
FOLLOW US
__ __
__
Get the latest news and updates.*
Add Me to the List
� 2020 NowSecure All rights reserved. LicensePrivacy Policy
Disclosure
×
PRIVACY DISCLOSURE: NowSecure uses first party and third party cookies to provide functions of this website and our services, to uniquely identify visitors, to analyze use of our website, and to target our marketing. You can choose to block cookies using your browser settings. By continuing to use our website or services you indicate your agreement. To learn more about the cookies we use and how we may collect and use your personal data, visit our Privacy PolicyAccept
The cookie settings on this website are set to "allow cookies" to give you the best browsing experience possible. If you continue to use this website without changing your cookie settings or you click "Accept" below then you are consenting to this.Close
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0