Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://bigblueball.com
Are you over 18 and want to see adult content?

A complete backup of https://genymoney.ca
Are you over 18 and want to see adult content?

A complete backup of https://primis.tech
Are you over 18 and want to see adult content?

A complete backup of https://cholesterolrem.com
Are you over 18 and want to see adult content?

A complete backup of https://golaravel.com
Are you over 18 and want to see adult content?

A complete backup of https://greetingcarduniverse.com
Are you over 18 and want to see adult content?
A complete backup of https://valeriecampion.com
Are you over 18 and want to see adult content?
A complete backup of https://agenangka4.net
Are you over 18 and want to see adult content?

A complete backup of https://bodhum.net
Are you over 18 and want to see adult content?
A complete backup of https://genesis.vision
Are you over 18 and want to see adult content?
A complete backup of https://automoto.ua
Are you over 18 and want to see adult content?

A complete backup of https://donorschoose.org
Are you over 18 and want to see adult content?
Favourite Annotations

Planning and Design Engineering Consultants | Kimley-Horn
Are you over 18 and want to see adult content?
After Effects Plugins - aescripts.com - aescripts + aeplugins - aescripts.com
Are you over 18 and want to see adult content?
Юрий Ключевский - Личный блог о веб-разработке и веб-дизайне
Are you over 18 and want to see adult content?

Watches | Designer & Luxury Watches Online UK | The Watch Hut
Are you over 18 and want to see adult content?
Text
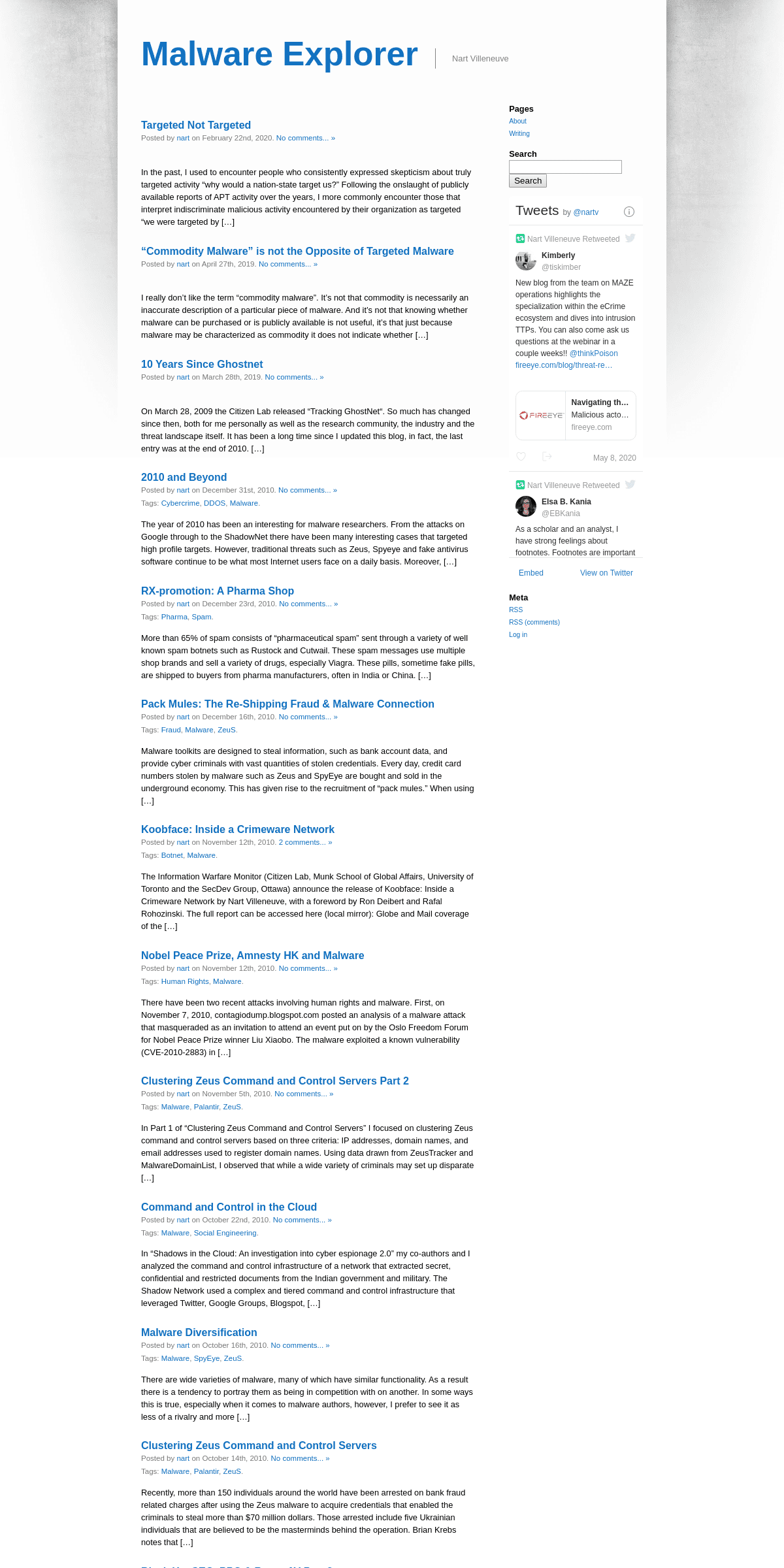
MALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
If the malware is used by a variety of actors, some of whom conduct targeted activity and some that engage in indiscriminate activity then it requires an additional assessment to determine what type of actor is most likely involved in any particular case. But even that is murky. This should give pause to defenders who use “commoditymalware
INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. JR02-2009 TRACKING GHOSTNET JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ s GOOGLE ADWORDS: ADVERTISING IN CHINA Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
If the malware is used by a variety of actors, some of whom conduct targeted activity and some that engage in indiscriminate activity then it requires an additional assessment to determine what type of actor is most likely involved in any particular case. But even that is murky. This should give pause to defenders who use “commoditymalware
INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. JR02-2009 TRACKING GHOSTNET JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ s GOOGLE ADWORDS: ADVERTISING IN CHINA Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
After it was established that 23.56 % of "attacks" are by WannaCry, the causes add up to: 67 % Phish mail + 16 % Mal Websites/ Web Ads =83 % None of
MALWARE EXPLORER
There have been two recent attacks involving human rights and malware. First, on November 7, 2010, contagiodump.blogspot.com posted an analysis of a malware attack that masqueraded as an invitation to attend an event put on by the Oslo Freedom Forum for Nobel Peace Prize winner Liu Xiaobo. The malware exploited a known vulnerability (CVE-2010-2883) in AdobeMALWARE EXPLORER
In Part 1 of “Clustering Zeus Command and Control Servers” I focused on clustering Zeus command and control servers based on three criteria: IP addresses, domain names, and email addresses used to register domain names. Using data drawn from ZeusTracker and MalwareDomainList, I observed that while a wide variety of criminals may set up disparate Zeus operations there may be “core” set EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
Google’s New Approach. Posted by nart on January 12th, 2010. 60 comments ». Tags: China, Google, Internet Surveillance, Malware. Google has just announced that there were successful attacks against their infrastructure resulting in the theft of intellectual property. Google traced the attacks to China and although the attributionMALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
ZeuS is a well known crimeware tool kit that is readily available online. The tool allows even the most unskilled to operate a botnet. Typically, Zeus has been associated with banking fraud. Recently, there have been a series of attacks using the Zeus malware that appear to be less motivated by bank fraud and more focused on acquiring data from compromised computers.MALWARE EXPLORER
And I agree completely. In China, the censorship IS in the router. Nearly all modern routers come with the ability to configure Access Control Lists (ACLs). These are commonly used to combat Denial of Service (DoS) attacks, slow the spread of worms/viruses, to block phishing sites, and to block the addresses of known spammers. JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
MALWARE ATTACKS ON SOLID OAK AFTER DISPUTE WITH GREENDAM After researchers discovered that portions of China’s Greendam filtering software were stolen from an American filtering company’s software, Cybersitter, the company that produces the software, Solid Oak, same under a targeted malware attack. This short post from the Malware Lab (www.malwarelab.org) analyzes two samples from the attacksMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
If the malware is used by a variety of actors, some of whom conduct targeted activity and some that engage in indiscriminate activity then it requires an additional assessment to determine what type of actor is most likely involved in any particular case. But even that is murky. This should give pause to defenders who use “commoditymalware
JR02-2009 TRACKING GHOSTNET JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ s GOOGLE ADWORDS: ADVERTISING IN CHINA Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
If the malware is used by a variety of actors, some of whom conduct targeted activity and some that engage in indiscriminate activity then it requires an additional assessment to determine what type of actor is most likely involved in any particular case. But even that is murky. This should give pause to defenders who use “commoditymalware
JR02-2009 TRACKING GHOSTNET JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ s GOOGLE ADWORDS: ADVERTISING IN CHINA Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
After it was established that 23.56 % of "attacks" are by WannaCry, the causes add up to: 67 % Phish mail + 16 % Mal Websites/ Web Ads =83 % None of
MALWARE EXPLORER
On March 28, 2009 the Citizen Lab released “Tracking GhostNet“. So much has changed since then, both for me personally as well as the research community, the EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
In Part 1 of “Clustering Zeus Command and Control Servers” I focused on clustering Zeus command and control servers based on three criteria: IP addresses, domain names, and email addresses used to register domain names. Using data drawn from ZeusTracker and MalwareDomainList, I observed that while a wide variety of criminals may set up disparate Zeus operations there may be “core” setMALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
Google has just announced that there were successful attacks against their infrastructure resulting in the theft of intellectual property. Google traced the attacks to China and although the attribution regarding the Chinese government is unclear, Google also discovered that the attackers also attempted to compromise the Gmail accounts of Chinese human rights activists.MALWARE EXPLORER
ZeuS is a well known crimeware tool kit that is readily available online. The tool allows even the most unskilled to operate a botnet. Typically, Zeus has been associated with banking fraud. Recently, there have been a series of attacks using the Zeus malware that appear to be less motivated by bank fraud and more focused on acquiring data from compromised computers.MALWARE EXPLORER
And I agree completely. In China, the censorship IS in the router. Nearly all modern routers come with the ability to configure Access Control Lists (ACLs). These are commonly used to combat Denial of Service (DoS) attacks, slow the spread of worms/viruses, to block phishing sites, and to block the addresses of known spammers. JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
MALWARE ATTACKS ON SOLID OAK AFTER DISPUTE WITH GREENDAM After researchers discovered that portions of China’s Greendam filtering software were stolen from an American filtering company’s software, Cybersitter, the company that produces the software, Solid Oak, same under a targeted malware attack. This short post from the Malware Lab (www.malwarelab.org) analyzes two samples from the attacksMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
If the malware is used by a variety of actors, some of whom conduct targeted activity and some that engage in indiscriminate activity then it requires an additional assessment to determine what type of actor is most likely involved in any particular case. But even that is murky. This should give pause to defenders who use “commoditymalware
JR02-2009 TRACKING GHOSTNET JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ s GOOGLE ADWORDS: ADVERTISING IN CHINA Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
If the malware is used by a variety of actors, some of whom conduct targeted activity and some that engage in indiscriminate activity then it requires an additional assessment to determine what type of actor is most likely involved in any particular case. But even that is murky. This should give pause to defenders who use “commoditymalware
JR02-2009 TRACKING GHOSTNET JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ s GOOGLE ADWORDS: ADVERTISING IN CHINA Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
After it was established that 23.56 % of "attacks" are by WannaCry, the causes add up to: 67 % Phish mail + 16 % Mal Websites/ Web Ads =83 % None of
MALWARE EXPLORER
On March 28, 2009 the Citizen Lab released “Tracking GhostNet“. So much has changed since then, both for me personally as well as the research community, the EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
In Part 1 of “Clustering Zeus Command and Control Servers” I focused on clustering Zeus command and control servers based on three criteria: IP addresses, domain names, and email addresses used to register domain names. Using data drawn from ZeusTracker and MalwareDomainList, I observed that while a wide variety of criminals may set up disparate Zeus operations there may be “core” setMALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
Google has just announced that there were successful attacks against their infrastructure resulting in the theft of intellectual property. Google traced the attacks to China and although the attribution regarding the Chinese government is unclear, Google also discovered that the attackers also attempted to compromise the Gmail accounts of Chinese human rights activists.MALWARE EXPLORER
ZeuS is a well known crimeware tool kit that is readily available online. The tool allows even the most unskilled to operate a botnet. Typically, Zeus has been associated with banking fraud. Recently, there have been a series of attacks using the Zeus malware that appear to be less motivated by bank fraud and more focused on acquiring data from compromised computers.MALWARE EXPLORER
And I agree completely. In China, the censorship IS in the router. Nearly all modern routers come with the ability to configure Access Control Lists (ACLs). These are commonly used to combat Denial of Service (DoS) attacks, slow the spread of worms/viruses, to block phishing sites, and to block the addresses of known spammers. JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
MALWARE ATTACKS ON SOLID OAK AFTER DISPUTE WITH GREENDAM After researchers discovered that portions of China’s Greendam filtering software were stolen from an American filtering company’s software, Cybersitter, the company that produces the software, Solid Oak, same under a targeted malware attack. This short post from the Malware Lab (www.malwarelab.org) analyzes two samples from the attacksMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
In Part 1 of “Clustering Zeus Command and Control Servers” I focused on clustering Zeus command and control servers based on three criteria: IP addresses, domain names, and email addresses used to register domain names. Using data drawn from ZeusTracker and MalwareDomainList, I observed that while a wide variety of criminals may set up disparate Zeus operations there may be “core” setMALWARE EXPLORER
If the malware is used by a variety of actors, some of whom conduct targeted activity and some that engage in indiscriminate activity then it requires an additional assessment to determine what type of actor is most likely involved in any particular case. But even that is murky. This should give pause to defenders who use “commoditymalware
JR02-2009 TRACKING GHOSTNET JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
GOOGLE ADWORDS: ADVERTISING IN CHINA Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
In Part 1 of “Clustering Zeus Command and Control Servers” I focused on clustering Zeus command and control servers based on three criteria: IP addresses, domain names, and email addresses used to register domain names. Using data drawn from ZeusTracker and MalwareDomainList, I observed that while a wide variety of criminals may set up disparate Zeus operations there may be “core” setMALWARE EXPLORER
If the malware is used by a variety of actors, some of whom conduct targeted activity and some that engage in indiscriminate activity then it requires an additional assessment to determine what type of actor is most likely involved in any particular case. But even that is murky. This should give pause to defenders who use “commoditymalware
JR02-2009 TRACKING GHOSTNET JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
GOOGLE ADWORDS: ADVERTISING IN CHINA Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
After it was established that 23.56 % of "attacks" are by WannaCry, the causes add up to: 67 % Phish mail + 16 % Mal Websites/ Web Ads =83 % None of
MALWARE EXPLORER
There have been two recent attacks involving human rights and malware. First, on November 7, 2010, contagiodump.blogspot.com posted an analysis of a malware attack that masqueraded as an invitation to attend an event put on by the Oslo Freedom Forum for Nobel Peace Prize winner Liu Xiaobo. The malware exploited a known vulnerability (CVE-2010-2883) in Adobe EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
MALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
On March 28, 2009 the Citizen Lab released “Tracking GhostNet“. So much has changed since then, both for me personally as well as the research community, theMALWARE EXPLORER
ZeuS is a well known crimeware tool kit that is readily available online. The tool allows even the most unskilled to operate a botnet. Typically, Zeus has been associated with banking fraud. Recently, there have been a series of attacks using the Zeus malware that appear to be less motivated by bank fraud and more focused on acquiring data from compromised computers. JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
SEARCH MONITOR PROJECT: TOWARD A MEASURE OF TRANSPARENCY Nart Villeneuve is a PHD student at the University of Toronto and a Senior Research Fellow at the Citizen Lab at the Munk Centre of International Studies.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ sMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
JR02-2009 TRACKING GHOSTNETGHOSTNET HUAWEIGHOSTNET PARANORMALGHOSTNETAPTGHOSTNET PYTORCH
JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. SEARCH MONITOR PROJECT: TOWARD A MEASURE OF TRANSPARENCY Nart Villeneuve is a PHD student at the University of Toronto and a Senior Research Fellow at the Citizen Lab at the Munk Centre of International Studies.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
GOOGLE ADWORDS: ADVERTISING IN CHINAGOOGLE ADVERTISING CODEGOOGLE ADVERTISING COSTGOOGLE ADVERTISING ONLINEFREE GOOGLE ADVERTISING Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
JR02-2009 TRACKING GHOSTNETGHOSTNET HUAWEIGHOSTNET PARANORMALGHOSTNETAPTGHOSTNET PYTORCH
JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. SEARCH MONITOR PROJECT: TOWARD A MEASURE OF TRANSPARENCY Nart Villeneuve is a PHD student at the University of Toronto and a Senior Research Fellow at the Citizen Lab at the Munk Centre of International Studies.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
GOOGLE ADWORDS: ADVERTISING IN CHINAGOOGLE ADVERTISING CODEGOOGLE ADVERTISING COSTGOOGLE ADVERTISING ONLINEFREE GOOGLE ADVERTISING Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
After it was established that 23.56 % of "attacks" are by WannaCry, the causes add up to: 67 % Phish mail + 16 % Mal Websites/ Web Ads =83 % None of
MALWARE EXPLORER
There have been two recent attacks involving human rights and malware. First, on November 7, 2010, contagiodump.blogspot.com posted an analysis of a malware attack that masqueraded as an invitation to attend an event put on by the Oslo Freedom Forum for Nobel Peace Prize winner Liu Xiaobo. The malware exploited a known vulnerability (CVE-2010-2883) in AdobeMALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ s MEASURING GLOBAL INTERNET FILTERING 1 Measuring Global Internet Filtering Robert Faris and Nart Villeneuve The Scope and Depth of Global Internet Filtering In this chapter, we set out to provide an overview ofEVASION TACTICS
EVASION TACTICS NART VILLENEUVE GLOBAL ONLINE CENSORSHIP IS GROWING, BUT SO ARE THE MEANS TO CHALLENGE IT AND PROTECT PRIVACY The number of countries that censor and monitor their citizens’ use of the 4 BARRIERS TO COOPERATION 4 Barriers to Cooperation An Analysis of the Origins of International Efforts to Protect Children Online Nart Villeneuve Introduction While providing an innovativeMALWARE EXPLORER
The file, a.htm, contains malicious code that attempts to exploit Microsoft DirectShow. 17 Anyone visiting 64tianwang.com using Internet Explorer was likely compromised. Soon after the discovery of a new 0day exploit, this time in Microsoft Office, the attackers changed the directory used in the initial attack, “css”, to “cssbak” and began serving the Microsoft Office Web Components A FEW OF THE OFFENDERS OTHER TYPES OF CONTENT BLOCKED crazyshit.com beer.com navy.mil ready.gov gmail.com allsearchengines.com A FEW OF THE OFFENDERS gay issues (21%) provocative attire (19%) search engines (14%)MALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
JR02-2009 TRACKING GHOSTNETGHOSTNET HUAWEIGHOSTNET PARANORMALGHOSTNETAPTGHOSTNET PYTORCH
JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. SEARCH MONITOR PROJECT: TOWARD A MEASURE OF TRANSPARENCY Nart Villeneuve is a PHD student at the University of Toronto and a Senior Research Fellow at the Citizen Lab at the Munk Centre of International Studies.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
GOOGLE ADWORDS: ADVERTISING IN CHINAGOOGLE ADVERTISING CODEGOOGLE ADVERTISING COSTGOOGLE ADVERTISING ONLINEFREE GOOGLE ADVERTISING Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”.MALWARE EXPLORER
Writing. Villeneuve, N. & Dela Torre, J. (2013) FAKEM RAT: Malware Disguised as Windows Messenger and Yahoo! Messenger. Villeneuve, N. & Bennett, J. (2012) Detecting APT Activity with Network Traffic Analysis. Trend Micro. (2012). Adding Android and Mac OS X Malware to the APT Toolbox. Sancho, Dela Torre, Mastukawa, Villeneuve & McArdle.(2012
MALWARE EXPLORER
Contact. Email: nart.villeneuve gmail.com. The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
JR02-2009 TRACKING GHOSTNETGHOSTNET HUAWEIGHOSTNET PARANORMALGHOSTNETAPTGHOSTNET PYTORCH
JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft. SEARCH MONITOR PROJECT: TOWARD A MEASURE OF TRANSPARENCY Nart Villeneuve is a PHD student at the University of Toronto and a Senior Research Fellow at the Citizen Lab at the Munk Centre of International Studies.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
GOOGLE ADWORDS: ADVERTISING IN CHINAGOOGLE ADVERTISING CODEGOOGLE ADVERTISING COSTGOOGLE ADVERTISING ONLINEFREE GOOGLE ADVERTISING Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
After it was established that 23.56 % of "attacks" are by WannaCry, the causes add up to: 67 % Phish mail + 16 % Mal Websites/ Web Ads =83 % None of
MALWARE EXPLORER
There have been two recent attacks involving human rights and malware. First, on November 7, 2010, contagiodump.blogspot.com posted an analysis of a malware attack that masqueraded as an invitation to attend an event put on by the Oslo Freedom Forum for Nobel Peace Prize winner Liu Xiaobo. The malware exploited a known vulnerability (CVE-2010-2883) in AdobeMALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ s MEASURING GLOBAL INTERNET FILTERING 1 Measuring Global Internet Filtering Robert Faris and Nart Villeneuve The Scope and Depth of Global Internet Filtering In this chapter, we set out to provide an overview ofEVASION TACTICS
EVASION TACTICS NART VILLENEUVE GLOBAL ONLINE CENSORSHIP IS GROWING, BUT SO ARE THE MEANS TO CHALLENGE IT AND PROTECT PRIVACY The number of countries that censor and monitor their citizens’ use of the 4 BARRIERS TO COOPERATION 4 Barriers to Cooperation An Analysis of the Origins of International Efforts to Protect Children Online Nart Villeneuve Introduction While providing an innovativeMALWARE EXPLORER
The file, a.htm, contains malicious code that attempts to exploit Microsoft DirectShow. 17 Anyone visiting 64tianwang.com using Internet Explorer was likely compromised. Soon after the discovery of a new 0day exploit, this time in Microsoft Office, the attackers changed the directory used in the initial attack, “css”, to “cssbak” and began serving the Microsoft Office Web Components A FEW OF THE OFFENDERS OTHER TYPES OF CONTENT BLOCKED crazyshit.com beer.com navy.mil ready.gov gmail.com allsearchengines.com A FEW OF THE OFFENDERS gay issues (21%) provocative attire (19%) search engines (14%)MALWARE EXPLORER
On March 28, 2009 the Citizen Lab released “Tracking GhostNet“. So much has changed since then, both for me personally as well as the research community, the industry and the threat landscape itself.MALWARE EXPLORER
Regalado, D., Villeneuve, N. & Railton Scott, J. (2015) Behind the Syrian Conflict’s Digital Frontlines Villeneuve, N., Moran, N., Haq, T. & Scott, Mike. (2014MALWARE EXPLORER
Contact. Email: nart.villeneuvegmail.com; The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
JR02-2009 TRACKING GHOSTNETGHOSTNET HUAWEIGHOSTNET PARANORMALGHOSTNETAPTGHOSTNET PYTORCH
JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 SEARCH MONITOR PROJECT: TOWARD A MEASURE OF TRANSPARENCY Nart Villeneuve is a PHD student at the University of Toronto and a Senior Research Fellow at the Citizen Lab at the Munk Centre of International Studies. INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
GOOGLE ADWORDS: ADVERTISING IN CHINAGOOGLE ADVERTISING CODEGOOGLE ADVERTISING COSTGOOGLE ADVERTISING ONLINEFREE GOOGLE ADVERTISING Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
On March 28, 2009 the Citizen Lab released “Tracking GhostNet“. So much has changed since then, both for me personally as well as the research community, the industry and the threat landscape itself.MALWARE EXPLORER
Regalado, D., Villeneuve, N. & Railton Scott, J. (2015) Behind the Syrian Conflict’s Digital Frontlines Villeneuve, N., Moran, N., Haq, T. & Scott, Mike. (2014MALWARE EXPLORER
Contact. Email: nart.villeneuvegmail.com; The postings on this blog represent my own views — and only my own — and don’t necessarily represent the positions or opinions of my employer. EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP … EVERYONE’S GUIDE TO BY-PASSING INTERNET CENSORSHIP FOR CITIZENS WORLDWIDE A CIVISEC PROJECT The Citizen Lab The University of TorontoSeptember, 2007
JR02-2009 TRACKING GHOSTNETGHOSTNET HUAWEIGHOSTNET PARANORMALGHOSTNETAPTGHOSTNET PYTORCH
JR02-2009 Tracking GhostNet - TABLE OF CONTENTS Summary p. 5 Introduction p. 7 Rise of the cyber spies p. 7 A focus on China p. 9 Outline of Report p. 9 Part One: Context and background p. 10 SEARCH MONITOR PROJECT: TOWARD A MEASURE OF TRANSPARENCY Nart Villeneuve is a PHD student at the University of Toronto and a Senior Research Fellow at the Citizen Lab at the Munk Centre of International Studies. INVESTIGATING CYBER ESPIONAGE 2 JR03-2010 Shadows in the Cloud - FOREWORD I Foreword Crime and espionage form a dark underworld of cyberspace. Whereas crime is usually the first to seek out new opportunities and methods, espionage usually follows in its wake, borrowing techniques and tradecraft.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times JR01-2008 INFORMATION WARFARE MONITOR JOINT REPORT ONI 3 JR01-2008 BREACHING TRUST Foreword We are very pleased to introduce the first Information Warfare Monitor/ONI Asia joint report, Breaching Trust: An analysis of surveillance and security practices on China’s TOM-Skype platform, written by Nart Villeneuve, Psiphon Fellow, the Citizen Lab, Munk Centre for International Studies, the University ofToronto.
GOOGLE ADWORDS: ADVERTISING IN CHINAGOOGLE ADVERTISING CODEGOOGLE ADVERTISING COSTGOOGLE ADVERTISING ONLINEFREE GOOGLE ADVERTISING Google AdWords: Advertising in China https://adwords.google.com/select/chinafaq.html?hl=en_US 2 of 2 2/20/2006 4:39 PM In order to run your AdWords ad, please sendMALWARE EXPLORER
After it was established that 23.56 % of "attacks" are by WannaCry, the causes add up to: 67 % Phish mail + 16 % Mal Websites/ Web Ads =83 % None of
MALWARE EXPLORER
There have been two recent attacks involving human rights and malware. First, on November 7, 2010, contagiodump.blogspot.com posted an analysis of a malware attack that masqueraded as an invitation to attend an event put on by the Oslo Freedom Forum for Nobel Peace Prize winner Liu Xiaobo. The malware exploited a known vulnerability (CVE-2010-2883) in AdobeMALWARE EXPLORER
Traffic Direction Systems (TDS) are used as landing pages that direct traffic to malicious content based on a variety of criteria such as operating system, browser version and geographic location.MALWARE EXPLORER
By Nart Villeneuve and Greg Walton. Overview. There have been recent reports of malware attacks on journalists based in China. The attacks specifically targeted Chinese employees working for media organizations, including Reuters, the Straits Times, Dow Jones, Agence France Presse, and Ansa. 1 These employees received an email from “Pam ” who claimed to be an editor with the Straits Times 8 CONTROL AND RESISTANCE ATTACKS ON BURMESE OPPOSITION MEDIA 8 Control and Resistance Attacks on Burmese Opposition Media Nart Villeneuve and Masashi Crete-Nishihata Burma is consistently identifi ed by human rights organizations as one of the world ’ sEVASION TACTICS
EVASION TACTICS NART VILLENEUVE GLOBAL ONLINE CENSORSHIP IS GROWING, BUT SO ARE THE MEANS TO CHALLENGE IT AND PROTECT PRIVACY The number of countries that censor and monitor their citizens’ use of the MEASURING GLOBAL INTERNET FILTERING 1 Measuring Global Internet Filtering Robert Faris and Nart Villeneuve The Scope and Depth of Global Internet Filtering In this chapter, we set out to provide an overview of 4 BARRIERS TO COOPERATION 4 Barriers to Cooperation An Analysis of the Origins of International Efforts to Protect Children Online Nart Villeneuve Introduction While providing an innovativeMALWARE EXPLORER
The file, a.htm, contains malicious code that attempts to exploit Microsoft DirectShow. 17 Anyone visiting 64tianwang.com using Internet Explorer was likely compromised. Soon after the discovery of a new 0day exploit, this time in Microsoft Office, the attackers changed the directory used in the initial attack, “css”, to “cssbak” and began serving the Microsoft Office Web Components A FEW OF THE OFFENDERS OTHER TYPES OF CONTENT BLOCKED crazyshit.com beer.com navy.mil ready.gov gmail.com allsearchengines.com A FEW OF THE OFFENDERS gay issues (21%) provocative attire (19%) search engines (14%)MALWARE EXPLORER
Nart Villeneuve
TARGETED NOT TARGETED Posted by nart on February 22nd, 2020. No comments... » In the past, I used to encounter people who consistently expressed skepticism about truly targeted activity “why would a nation-state target us?” Following the onslaught of publicly available reports of APT activity over the years, I more commonly encounter those that interpret indiscriminate malicious activity encountered by their organization as targeted “we were targeted by “COMMODITY MALWARE” IS NOT THE OPPOSITE OF TARGETED MALWARE Posted by nart on April 27th, 2019. No comments... » I really don’t like the term “commodity malware”. It’s not that commodity is necessarily an inaccurate description of a particular piece of malware. And it’s not that knowing whether malware can be purchased or is publicly available is not useful, it’s that just because malware may be characterized as commodity it does not indicate whether 10 YEARS SINCE GHOSTNET Posted by nart on March 28th, 2019. No comments... » On March 28, 2009 the Citizen Lab released “Tracking GhostNet“. So much has changed since then, both for me personally as well as the research community, the industry and the threat landscape itself. It has been a long time since I updated this blog, in fact, the last entry was at the end of 2010.2010 AND BEYOND
Posted by nart on December 31st, 2010. No comments... » Tags: Cybercrime , DDOS, Malware
.
The year of 2010 has been an interesting for malware researchers. From the attacks on Google through to the ShadowNet there have been many interesting cases that targeted high profile targets. However, traditional threats such as Zeus, Spyeye and fake antivirus software continue to be what most Internet users face on a daily basis.Moreover,
RX-PROMOTION: A PHARMA SHOP Posted by nart on December 23rd, 2010. No comments... »Tags: Pharma , Spam
.
More than 65% of spam consists of “pharmaceutical spam” sent through a variety of well known spam botnets such as Rustock and Cutwail. These spam messages use multiple shop brands and sell a variety of drugs, especially Viagra. These pills, sometime fake pills, are shipped to buyers from pharma manufacturers, often in India orChina.
PACK MULES: THE RE-SHIPPING FRAUD & MALWARE CONNECTION Posted by nart on December 16th, 2010. No comments... » Tags: Fraud , Malware, ZeuS
.
Malware toolkits are designed to steal information, such as bank account data, and provide cyber criminals with vast quantities of stolen credentials. Every day, credit card numbers stolen by malware such as Zeus and SpyEye are bought and sold in the underground economy. This has given rise to the recruitment of “pack mules.”When using
KOOBFACE: INSIDE A CRIMEWARE NETWORK Posted by nart on November 12th, 2010. 2 comments... » Tags: Botnet , Malware.
The Information Warfare Monitor (Citizen Lab, Munk School of Global Affairs, University of Toronto and the SecDev Group, Ottawa) announce the release of Koobface: Inside a Crimeware Network by Nart Villeneuve, with a foreword by Ron Deibert and Rafal Rohozinski. The full report can be accessed here (local mirror): Globe and Mailcoverage of the
NOBEL PEACE PRIZE, AMNESTY HK AND MALWARE Posted by nart on November 12th, 2010. No comments... » Tags: Human Rights , Malware.
There have been two recent attacks involving human rights and malware. First, on November 7, 2010, contagiodump.blogspot.com posted an analysis of a malware attack that masqueraded as an invitation to attend an event put on by the Oslo Freedom Forum for Nobel Peace Prize winner Liu Xiaobo. The malware exploited a known vulnerability(CVE-2010-2883) in
CLUSTERING ZEUS COMMAND AND CONTROL SERVERS PART 2 Posted by nart on November 5th, 2010. No comments... » Tags: Malware , Palantir, ZeuS
.
In Part 1 of “Clustering Zeus Command and Control Servers” I focused on clustering Zeus command and control servers based on three criteria: IP addresses, domain names, and email addresses used to register domain names. Using data drawn from ZeusTracker and MalwareDomainList, I observed that while a wide variety of criminals may set up disparate COMMAND AND CONTROL IN THE CLOUD Posted by nart on October 22nd, 2010. No comments... » Tags: Malware , Social Engineering.
In “Shadows in the Cloud: An investigation into cyber espionage 2.0” my co-authors and I analyzed the command and control infrastructure of a network that extracted secret, confidential and restricted documents from the Indian government and military. The Shadow Network used a complex and tiered command and control infrastructure that leveraged Twitter, Google Groups, Blogspot, MALWARE DIVERSIFICATION Posted by nart on October 16th, 2010. No comments... » Tags: Malware , SpyEye, ZeuS
.
There are wide varieties of malware, many of which have similar functionality. As a result there is a tendency to portray them as being in competition with on another. In some ways this is true, especially when it comes to malware authors, however, I prefer to see it as less of a rivalry and more CLUSTERING ZEUS COMMAND AND CONTROL SERVERS Posted by nart on October 14th, 2010. No comments... » Tags: Malware , Palantir, ZeuS
.
Recently, more than 150 individuals around the world have been arrested on bank fraud related charges after using the Zeus malware to acquire credentials that enabled the criminals to steal more than $70 million dollars. Those arrested include five Ukrainian individuals that are believed to be the masterminds behind the operation. BrianKrebs notes that
BLACK HAT SEO, PPC & ROGUEAV PART 2 Posted by nart on October 8th, 2010. No comments... »Tags: Malware , PPC
, RogueAV
, SEO
.
Part 1 of “Black Hat SEO, PPC & RogueAV” focused on the type and amount of incoming traffic generated through BlackHat SEO methods. This traffic is monetized through the use of RogueAV, Pay-Per-Click and Pay-Per-Install affiliates. This post continues the analysis of this campaign by providing a inside look at this BHSEO operation. Theattackers
KRAJABOT
Posted by nart on September 30th, 2010. No comments... » Tags: Kraja , Malware.
The Kraja botnet has managed to compromise 185,645 computers, the vast majority of which are located in Russia. Of the 199,513 unique IP addresses recorded from compromised computers, 87.88% are in IP address ranges assigned to Russia. The name “Kraja botnet” comes from an image located on the command and control server which wasoriginally
OLD THREATS ARE CURRENT THREATS Posted by nart on September 29th, 2010. No comments... »Tags: Malware .
Despite the fact that the authors of the Pinch Trojan were “pinched” by law enforcement in 2007, the Pinch Trojan continues to be a current threat both because the source code is available (so anyone can modify it and release a variant) but also because old versions of Pinch continue to be effectively used. In� Back...
*
PAGES
* About
* Writing
SEARCH
*
META
*
RSS
RSS (comments)
Log in
Except where otherwise noted, content on this site is licensed under a Creative Commons License.
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0