Are you over 18 and want to see adult content?
More Annotations
Private Jet Charter | Jet Hire Cost | Air Charter | UK | USA | Europe
Are you over 18 and want to see adult content?

Java mini projects With Source Code - ProjectsGeek
Are you over 18 and want to see adult content?
ComoHacerPara.com - Consejos, Guías y Tutoriales
Are you over 18 and want to see adult content?
صفحه اصلی | اولین و بزرگترین مجموعه اتاق فرار در ایران
Are you over 18 and want to see adult content?

times-journal.com | DeKalb County's Oldest Newspaper
Are you over 18 and want to see adult content?
militaria,wędkarstwo,obrona,gazy,survival,kabury,spodnie,polary
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of rafflespaint.com
Are you over 18 and want to see adult content?
Microsoft Azure App Service - Welcome
Are you over 18 and want to see adult content?
พระเครื่องดี เกจิดัง พิธีขลัง มวลสารศักดิ์สิทธิ์ | Amulet24.com
Are you over 18 and want to see adult content?
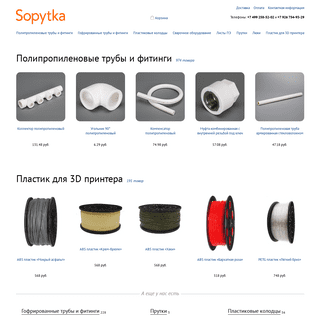
Sopytka.ru — Интернет-магазин полипропиленовых труб и фитингов
Are you over 18 and want to see adult content?

Your essential guide to the business of influencer marketing | Influencer Update
Are you over 18 and want to see adult content?

Женский журнал У мадам.net: красота, здоровье, дети
Are you over 18 and want to see adult content?

Mortgage Brokerage Toronto | Commercial and Residential Mortgage Toronto, ON
Are you over 18 and want to see adult content?
Text
FERRUH MAVITUNA
Ferruh Mavituna. Bio. I’m the CEO of Invicti Security, makers of Acunetix and Netsparker. We solve something that no one is able solve: “Securing thousands of applications”. I believe in aggressive automation in business, everything needs to be automated. This is the core design principle for Invicti’s products. “Automate what canbe
FAST WAY TO EXTRACT DATA FROM ERROR BASED SQL INJECTIONS Fast way to extract data from Error Based SQL Injections What is this? This attack described in Advanced SQL Injection in SQL Server Applications paper by Chris Anley İNTERNETTE KIMLIK GIZLEME , IP GIZLEMEK , IP GIZLEMETRANSLATE THIS PAGEMAKALE HAKKINDANEDEN ?UYGULAMALARDA IP GIZLEMESIE-MAIL GÜVENLIĞISEE MORE ON FERRUH.MAVITUNA.COM OSX' I WINDOWS' A BENZETME OSX' in kısa yolları her ne kadar Windows' a benzese de büyük değişiklikler içeriyor. Özetle üzerinde Apple logosu olan buton "Command" diye çağırılıyor ve Ctrl yerine bu butonu kullanmanız gerekiyor. Mesela bir yazıyı kalınlaştırmak için Command + B yi kullanıyorsunuz. Buradaki sorun Command butonu ile Ctrl butonunun FLAWED CSRF PROTECTIONS Before going into the details and the vulnerability in WordPress, I need to say all of credit should go to Gareth Heyes, he talked about CSS Overlays before, but shame on me that I missed his point in the first place. When I looked into his new tool PoC for CSRF bypass in delicious, I realised that, this is a big deal.I know the exploitation requires lots of stuff but it's still important and KABLOSUZ AĞLARA SALDIRI VE DEFANS Kablosuz (Wireless, Wi-Fi) ağların tespiti, kablosuz ağlara saldırı ve kablosuz ağların güvenliği Ön Bilgi. Kablosuz ağlar uzun bir zamandır aktif halde kullanıma geçmesine rağmen Türkiye’ de 2005 itibarı ile yaygınlaşmaya başladı. MOZILLA' NIN SITESI YENILENDI Mozilla' nın sitesi yenilenmiş.Gerçekten de çok hoş ve şık. Her ne kadar trendy olsa da. ROCKET COMMANDER YAZALIMTRANSLATE THIS PAGE Coding4Fun süper bir makale ve video serisi ile gelmiş. Rocket Commander geliştirilmesi. Gerçek bir 3D shooter, C# Express ileyazılmış.
GETTING REAL
Dediğim gibi bugün Getting Real' ı bitirdim (son bir kaç bölüm essay kaldı).Son zamanlarda bir çok konuda kısa notlar tutuyorum, bu notlar da Gettin Real' dan: Less Features MOZILLA FIREFOX LOCALHOST İLGINÇLIĞITRANSLATE THIS PAGE Pek aktif Firefox kullanan biri değilim dün bir sistem kontrolü için Firefox' ta http://localhost:4536 şeklinde bir giriş yaptım ve karşıma birden LocalhostFERRUH MAVITUNA
Ferruh Mavituna. Bio. I’m the CEO of Invicti Security, makers of Acunetix and Netsparker. We solve something that no one is able solve: “Securing thousands of applications”. I believe in aggressive automation in business, everything needs to be automated. This is the core design principle for Invicti’s products. “Automate what canbe
FAST WAY TO EXTRACT DATA FROM ERROR BASED SQL INJECTIONS Fast way to extract data from Error Based SQL Injections What is this? This attack described in Advanced SQL Injection in SQL Server Applications paper by Chris Anley İNTERNETTE KIMLIK GIZLEME , IP GIZLEMEK , IP GIZLEMETRANSLATE THIS PAGEMAKALE HAKKINDANEDEN ?UYGULAMALARDA IP GIZLEMESIE-MAIL GÜVENLIĞISEE MORE ON FERRUH.MAVITUNA.COM OSX' I WINDOWS' A BENZETME OSX' in kısa yolları her ne kadar Windows' a benzese de büyük değişiklikler içeriyor. Özetle üzerinde Apple logosu olan buton "Command" diye çağırılıyor ve Ctrl yerine bu butonu kullanmanız gerekiyor. Mesela bir yazıyı kalınlaştırmak için Command + B yi kullanıyorsunuz. Buradaki sorun Command butonu ile Ctrl butonunun FLAWED CSRF PROTECTIONS Before going into the details and the vulnerability in WordPress, I need to say all of credit should go to Gareth Heyes, he talked about CSS Overlays before, but shame on me that I missed his point in the first place. When I looked into his new tool PoC for CSRF bypass in delicious, I realised that, this is a big deal.I know the exploitation requires lots of stuff but it's still important and KABLOSUZ AĞLARA SALDIRI VE DEFANS Kablosuz (Wireless, Wi-Fi) ağların tespiti, kablosuz ağlara saldırı ve kablosuz ağların güvenliği Ön Bilgi. Kablosuz ağlar uzun bir zamandır aktif halde kullanıma geçmesine rağmen Türkiye’ de 2005 itibarı ile yaygınlaşmaya başladı. MOZILLA' NIN SITESI YENILENDI Mozilla' nın sitesi yenilenmiş.Gerçekten de çok hoş ve şık. Her ne kadar trendy olsa da. ROCKET COMMANDER YAZALIMTRANSLATE THIS PAGE Coding4Fun süper bir makale ve video serisi ile gelmiş. Rocket Commander geliştirilmesi. Gerçek bir 3D shooter, C# Express ileyazılmış.
GETTING REAL
Dediğim gibi bugün Getting Real' ı bitirdim (son bir kaç bölüm essay kaldı).Son zamanlarda bir çok konuda kısa notlar tutuyorum, bu notlar da Gettin Real' dan: Less Features MOZILLA FIREFOX LOCALHOST İLGINÇLIĞITRANSLATE THIS PAGE Pek aktif Firefox kullanan biri değilim dün bir sistem kontrolü için Firefox' ta http://localhost:4536 şeklinde bir giriş yaptım ve karşıma birden Localhost WHY PLATFORM MATTERS IN WEB APPLICATION SECURITY? I wrote this article about 2 years ago in Turkish.Recently Whitehat released a quite nice paper about vulnerability counts per programming language/framework.That report kind of backs up this article however many took and advertised it wrongly as it sounded like “choice of framework has virtually no effect on security”.So I decided to write it in English again. VISUAL STUDIO' DA BILMENIZ GEREKEN KISAYOL TUŞLARITRANSLATE THIS PAGE Bu da bir diğer süper kısayol, ilk üç te. Toggle Bookmark : F9. İmlecin ( cursor anasını satayım) bulunduğu yeri daha sonra dönebilmek için bookmarklamanızı sağlıyor Go To Bookmark ile birlikte kullanılmalı. ( bunun türkçesi hakkında fikrim yok) Go to Next Bookmark : F4. Sizi bir sonraki bookmarkınıza götürür. F9ve F4
GENEL KÜLTÜR ÇAĞIMIZIN EN BÜYÜK YALANIDIRTRANSLATE THIS PAGE Bir çoğumuz büyürken hep ikinci defa düşünülmemiş klişe laflarla büyüdük, bunun ana nedeni kimsenin yaptığını ve duyduğunu sorgulamamasıydı. HAYAT, BAHAMA ADALARI, BALIKÇI KÖYÜNDE YAŞAMAKTRANSLATE THIS PAGE Blog yazmaya ara verdiğim en uzun süre buydu sanırım. İşlere odaklanırken kafayı yememek için hayatımdaki bazı şeyleri listemden çıkartmıştım, bunlardan biri de blog yazmaktı.Sizin haberiniz yok, blog yazmadığım sürede çok olay gelişti. ROCKET COMMANDER YAZALIMTRANSLATE THIS PAGE Coding4Fun süper bir makale ve video serisi ile gelmiş. Rocket Commander geliştirilmesi. Gerçek bir 3D shooter, C# Express ileyazılmış.
NUMARALARA, PSIKOLOJIK ATRAKSIYONLARA, POLITIK …TRANSLATE THIS PAGE Do you believe in tricks? Eskiden başka bir adreste olan bu blog' u ilk açarken bir düşüncem vardı az ama öz bir ziyaretçi oluşturmak. Binlerce kişinin okuması önemli değil ancak birileri ziyaret etsin ve bu birileri bundan gizlice zevk alsın.AMAZON LIGHT
Amazon Light güzel fikir kötü iş örneği. Kullanılabilir bir çalışma olmamış. Nereden çıktı Amazon API derseniz ? Şimdi yeni küçük bir proje planından çıktı deriz. ASP ile açık kaynak kodlu bir Amazon temelli kitaplık sistemi geliştirmeyebaşlıyorum.
TIBET WILL BE FREE!
Stunderts for a Free Tibet Çin - Google ortaklaşa sansür birleşmesini protesto ediyor ve 14 Şubat' ta Google ile olan aşklarını bitiriyorlar - noluv4google. Bu aktivist dostalarımızı Tibet Will be Free! blog' unda da takip edebiliriz. MOZILLA FIREFOX LOCALHOST İLGINÇLIĞITRANSLATE THIS PAGE Pek aktif Firefox kullanan biri değilim dün bir sistem kontrolü için Firefox' ta http://localhost:4536 şeklinde bir giriş yaptım ve karşıma birden Localhost MÜKEMMEL BIR DÜNYADA...TRANSLATE THIS PAGE Bazı eylemler vardır sadece mükemmel bir dünyada yada NŞA (normal şartlar altında) çalışırlar.İşte bunlar genelde hiç bir işe yaramaz. Fazlamesai' de Çalıntı laptoplara sınır (ya da biri bizi gözetliyor) başlığını okuyunca güleyim mi ağlayayım mıbilemedim.
FERRUH MAVITUNA
Ferruh Mavituna. Bio. I’m the CEO of Invicti Security, makers of Acunetix and Netsparker. We solve something that no one is able solve: “Securing thousands of applications”. I believe in aggressive automation in business, everything needs to be automated. This is the core design principle for Invicti’s products. “Automate what canbe
FAST WAY TO EXTRACT DATA FROM ERROR BASED SQL INJECTIONS Fast way to extract data from Error Based SQL Injections What is this? This attack described in Advanced SQL Injection in SQL Server Applications paper by Chris Anley WHY PLATFORM MATTERS IN WEB APPLICATION SECURITY? I wrote this article about 2 years ago in Turkish.Recently Whitehat released a quite nice paper about vulnerability counts per programming language/framework.That report kind of backs up this article however many took and advertised it wrongly as it sounded like “choice of framework has virtually no effect on security”.So I decided to write it in English again. UNIX COMMAND INJECTION CHEAT SHEET Short, yet quite useful command injection cheat sheet. Executing Commands. Seperating Commands: blah;blah2 ; PIPE: blah | blah2 ;PIPEZ: blah ^ blah2
WEB WIZ FORUMS REGISTRATION RULES XSS VULNERABILITY ----- WEB WIZ FORUMS REGISTRATION RULES XSS VULNERABILITY ----- Online URL : http://ferruh.mavituna.com/article/?528 XSS / Cross Site Scripting attack allows anPSYCHO FOLDER
I've got a routine of extracting downloaded video files, appending subtitles where required and moving them to the server that my PS3 connects, so I can watch it on my TV. URI HANDLERS FROM HELL About 3 years ago I wrote about how browser integrated 3rd party tools are stupid and exposing users to new attacks (post in Turkish - basically it's talking about Winamp exploit and IE-Winamp integration issue ).. Nowadays whole security community is talking about Firefox / IE remote command execution issues and how URI Handlers are bad. If we keep combining and integrating stuff, we will be PRAGMATIC PROGRAMMER NOTLARI Pragmatic Programmer programlama konusundaki harika kitaplardan biri ve uzun süredir okumaya başlamayı düşünüyordum. Bugün safari hesabımı tekrar açtırdım ve okumaya başladım ve ilk bölümün ortalarındayım.. Kitaptan bazı notlar alıyorum, aldığım notların bir kısmı: One broken window, left unrepaired for any substantial length of time, instills in the inhabitants of HTTP PROXY FOR XSS CHANNELS Last week I was reading the brief of Black Hat Europe 2007 Kicking Down the Cross Domain Door (One XSS at a Time) speak. It seems a nice one and there is a very good idea in it, using a proxy for a XSS Proxy like XSS Shell or Beef.. Since I’m not quite sure that’s the intention of speakers but for sure they are going to present a verysimilar concept.
XSS SHELL RELEASED
I started to develop XSS Shell about 2-3 months ago after finish core features because lots of reasons, I didn't resume it. Finally about a week ago I just fixed some bugs andFERRUH MAVITUNA
Ferruh Mavituna. Bio. I’m the CEO of Invicti Security, makers of Acunetix and Netsparker. We solve something that no one is able solve: “Securing thousands of applications”. I believe in aggressive automation in business, everything needs to be automated. This is the core design principle for Invicti’s products. “Automate what canbe
FAST WAY TO EXTRACT DATA FROM ERROR BASED SQL INJECTIONS Fast way to extract data from Error Based SQL Injections What is this? This attack described in Advanced SQL Injection in SQL Server Applications paper by Chris Anley WHY PLATFORM MATTERS IN WEB APPLICATION SECURITY? I wrote this article about 2 years ago in Turkish.Recently Whitehat released a quite nice paper about vulnerability counts per programming language/framework.That report kind of backs up this article however many took and advertised it wrongly as it sounded like “choice of framework has virtually no effect on security”.So I decided to write it in English again. UNIX COMMAND INJECTION CHEAT SHEET Short, yet quite useful command injection cheat sheet. Executing Commands. Seperating Commands: blah;blah2 ; PIPE: blah | blah2 ;PIPEZ: blah ^ blah2
WEB WIZ FORUMS REGISTRATION RULES XSS VULNERABILITY ----- WEB WIZ FORUMS REGISTRATION RULES XSS VULNERABILITY ----- Online URL : http://ferruh.mavituna.com/article/?528 XSS / Cross Site Scripting attack allows anPSYCHO FOLDER
I've got a routine of extracting downloaded video files, appending subtitles where required and moving them to the server that my PS3 connects, so I can watch it on my TV. URI HANDLERS FROM HELL About 3 years ago I wrote about how browser integrated 3rd party tools are stupid and exposing users to new attacks (post in Turkish - basically it's talking about Winamp exploit and IE-Winamp integration issue ).. Nowadays whole security community is talking about Firefox / IE remote command execution issues and how URI Handlers are bad. If we keep combining and integrating stuff, we will be PRAGMATIC PROGRAMMER NOTLARI Pragmatic Programmer programlama konusundaki harika kitaplardan biri ve uzun süredir okumaya başlamayı düşünüyordum. Bugün safari hesabımı tekrar açtırdım ve okumaya başladım ve ilk bölümün ortalarındayım.. Kitaptan bazı notlar alıyorum, aldığım notların bir kısmı: One broken window, left unrepaired for any substantial length of time, instills in the inhabitants of HTTP PROXY FOR XSS CHANNELS Last week I was reading the brief of Black Hat Europe 2007 Kicking Down the Cross Domain Door (One XSS at a Time) speak. It seems a nice one and there is a very good idea in it, using a proxy for a XSS Proxy like XSS Shell or Beef.. Since I’m not quite sure that’s the intention of speakers but for sure they are going to present a verysimilar concept.
XSS SHELL RELEASED
I started to develop XSS Shell about 2-3 months ago after finish core features because lots of reasons, I didn't resume it. Finally about a week ago I just fixed some bugs andX13 DB EDITOR V1~
{X13 v2 is out Now !} About X13 Db Editor; Demo; Download; Features; Customizing; Setup; License; Contact - Support; About X13 Db Editor; X13 DB Editor is a database editor that allows everybody to put nearly any database on the web for viewing and/or editing without needing anycoding.
MIND PERFORMANCE HACKS, BOOK REVIEW AND NOTES This is one of the best books which I read recently. It opened several new doors in my mind. Whole book is about some hacks (includes 75 hacks) for your mind such as mnemonic tricks, being more productive, doing math simply, overcoming stage fright etc. URI HANDLERS FROM HELL About 3 years ago I wrote about how browser integrated 3rd party tools are stupid and exposing users to new attacks (post in Turkish - basically it's talking about Winamp exploit and IE-Winamp integration issue ).. Nowadays whole security community is talking about Firefox / IE remote command execution issues and how URI Handlers are bad. If we keep combining and integrating stuff, we will be FIREFOX MASTER PASSWORD DIALOG WEAKNESS In client-side security history we've seen so many badly designed interfaces and technologies which lead to phising and several spoofing attacks (remember chrome window spoofing in IE?Today I've noticed that Firefox Master Password Dialog is almost identical with Firefox JavaScript Prompt dialog.Potentially an attacker can show a Prompt dialog and capture the master password. FLAWED CSRF PROTECTIONS Before going into the details and the vulnerability in WordPress, I need to say all of credit should go to Gareth Heyes, he talked about CSS Overlays before, but shame on me that I missed his point in the first place. When I looked into his new tool PoC for CSRF bypass in delicious, I realised that, this is a big deal.I know the exploitation requires lots of stuff but it's still important and IE SHELL URI DOWNLOAD AND EXECUTE, POC EXPLOIT Code is based on http://www.securityfocus.com/archive/1/367878( POC by Jelmer) message. I just added a new feature download and then execute application. Also I use MYSQL IF QUERY HANDLING REMOTE DENIAL OF SERVICE VULNERABILITY Güvenlik Açıklarını Bildirme Sorunu nda bahsettiğim MySQL DoS açığı da yayınlandı.. MySQL IF Query Handling Remote Denial Of Service Vulnerability. Hayır "Neil" HIZLI VE PIS VIRTUAL DOMAIN OLUŞTURMACA Üzerinde çalıştığım bir yazılım için bir çok virtual domain oluşturmam gerekiyordu. Şu şekilde bir direk metabase.xml (sadece IIS 6.0+) e kopyalanıp yapışitırılacak bir script yaptım.Aşağıdaki kod basit olarak bir klasördeki tüm alt klasörlerin isimlerinden IIS' e bir virtual domain açıyor.HIDDEN PAYBACK LIST
Currently I can not publish my entire payback list online because of potential legal problems. Hidden payback list is including some online services (services like rapidshare), personally cracked applications and some enterprise applications. ASP.NET - OTOMATIK KOD VS. - FERRUH.MAVITUNA.COM RSI hikayesinden dolayı bir şey yapamadığımdan vaktimi kitap okuyarak ve Warhammer 40000, Squad Command oynayarak geçiriyorum. Şimdi pragmatic programmer' da şu kısım ilgimi çekti :But using a wizard designed by a guru does not automatically make Joe developer equally expert. Joe can feel pretty good—he's just produced a mass of code and a pretty spiffy-looking program.* Ferruh Mavituna
* Archive
* RSS
* About
A SIMPLE GUIDE TO RISK FREE STARTUP10-12-2013
Here is my “MAGICAL”solution to start your own company withoutrisking
PREREQUISITES
You need to;
* have the technical skills * have some basic social/business skills If you don’t have this don’t even think about starting your own startup, your best bet would be just finding a good co-founder or being the #1 employeeYour startup;
* shouldn’t be an operation heavy _shouldn’t require 10 employee, $1M infrastructure investment etc._ * shouldn’t be socialHOW
*
Find the idea
*
Design and code a working proof of concept, super light MVP while working on your current job*
You’ll need maximum 1 year to deliver the product yourself*
Pitch it to people you know Right now all you need is money that’s enough for you to survive one year. Let’s call it $80K. Get as lower as you can without beinguncomfortable.
If you can't find and convince at least 3-4 people to invest one year salary to this project (_or combination of them to invest this amount_) then do not do startups. Do give away up to 49% of the company. Do not care. So the valuation of your company will be about 2 x your annual burn rate. i.e. $80K x 2=$160K You can always try incubators as well, the local ones can be easier to penetrate if there is any.*
Only accept investment from people whose fine to lose the investment. Do not take money from relatives, friends etc. You really don’t want that kind of pressure. You don’t want any extra pressure, you need to know that it’s OKto lose that money.
*
Now you have 1 year care free time to do your thing. Quit your work and start working on your startup.*
Hopefully at the end of the year you have something that works and shows potential. This is the hard bit, if it’s obviously working and bringing money in then good for you. If it’s not bringing in any money but shows potential you need to stick with it. Try to stick with it maximum of another 6 months, re-evaluate if you are still not ramen profitable, drop it.*
If you’re ramen profitable, great you have a successful startup. If not then no worries, shut it down and find a job. If you cannot find a job within a month do not start your own company that means you don’t meet one of the prerequisites of this guide; technically notgood enough.
Congratulations, you have just started and failed (or succeeded) a risk free startup. If you failed you lost some time but you learned more than you bargained for and you can always submit “Why I failed my startup” post to Hacker News . Not to mention that someone will send you a job offer right after thatpost anyway.
If you like you can repeat this many times until actually make it a reality or to figure out that you don't have what it takes to do this. Don’t forget you only need to get it right once.Close
FORGOT PASSWORD?
Please put in your email: Send me my password!Close message
Login
* This blog post
* All blog posts
Subscribe to this blog post's comments through...*
*
*
*
RSS Feed
SUBSCRIBE VIA EMAIL
Subscribe
Subscribe to this blog's comments through...*
*
*
*
RSS Feed
SUBSCRIBE VIA EMAIL
Subscribe Follow the discussionCOMMENTS (11)
Logging you in...
Close
LOGIN TO INTENSEDEBATE Or create an accountUsername or Email:
Password:
Forgot login?
Cancel LOGIN
Close WordPress.com
Username or Email:
Password:
Lost your password?
Cancel LOGIN
Dashboard | Edit profile| Logout
* Logged in as
Admin Options
Disable comments for this pageSave Settings
Sort by: Date Rating Last ActivityLoading comments...
0 Vote up Vote down
@ommunist _· 337 weeks ago_ If you failed - your startup was not risk-free. Reply 0 replies _· active 337 weeks ago_ +13 Vote up Vote down @yortuc _· 334 weeks ago_ where is the joy in "risk free" start up? Reply 0 replies _· active 334 weeks ago_ -2 Vote up Vote down @hserdarb _· 330 weeks ago_ I agree with most of you mentioned, but for developer entrepreneurs the "lean start-up" philosophy eliminates the risk factor and reduces the cost so much... in a weekend you can test your idea if people are interested in or keen to pay for it...on the other hand,
in life there is a situation that you have to be an entrepreneur and succeed (not joking, or meaning wanting it too much) in some cases trying in loop to succeed till die ( :) ), is the only better option then the other ways... Reply 0 replies _· active 233 weeks ago_ -1 Vote up Vote down googfan _· 297 weeks ago_ start up risk free where is? Reply 0 replies _· active 297 weeks ago_ +2 Vote up Vote down hüseyin serbest _· 262 weeks ago_ yardım ve görüşleriniz için tesekkurler. Reply 0 replies _· active 262 weeks ago_ -5 Vote up Vote down bedrettin aydın _· 262 weeks ago_ verdiğiniz paylaşımlar ve yorumlar için tesekkurler. Reply 0 replies _· active 262 weeks ago_ -1 Vote up Vote down Hakkı Eser _· 261 weeks ago_ 3-4 senedir değerli bulupda takip ettiğim tek blog yeni yazılar yazmaması üzücü... Reply 0 replies _· active 261 weeks ago_ +1 Vote up Vote down markapr _· 256 weeks ago_ emeklerinizden dolayı teşekkürler. Reply 0 replies _· active 256 weeks ago_ -8 Vote up Vote down mutlu _· 217 weeks ago_ Bunca zamandır yazacak cok şey birikmiştir. Ha gayret ;) Reply 0 replies _· active 217 weeks ago_ -2 Vote up Vote down turkaywebtasarim _· 212 weeksago_
start up risk free where is.. Reply 0 replies _· active 212 weeks ago_ -8 Vote up Vote down celilcan _· 185 weeks ago_ Türkçe siteni yayına almanı bekliyoruz sevgili ferruh Reply 0 replies _· active 185 weeks ago_POST A NEW COMMENT
Enter text right here! Comment as a Guest, or login: * Login to IntenseDebate * Login to WordPress.com* Login to Twitter
Go back
Tweet this comment
Connected as (Logout)
Email (optional)
Not displayed publicly.Name
Website (optional)
Displayed next to your comments. Not displayed publicly. If you have a website, link to it here. Posting anonymously.Tweet this comment
SUBMIT COMMENT
Subscribe to None Replies All new comments Comments by IntenseDebate Enter text right here! Reply as a Guest, or login: * Login to IntenseDebate * Login to WordPress.com* Login to Twitter
Go back
Tweet this comment
Connected as (Logout)
Email (optional)
Not displayed publicly.Name
Website (optional)
Displayed next to your comments. Not displayed publicly. If you have a website, link to it here. Posting anonymously.Tweet this comment
Cancel SUBMIT COMMENT Subscribe to None Replies All new commentsRECENT BLOG POSTS
See all of the blog posts* Yaşıyor!
* Uygulama Güvenliği Günü * .NET Geliştiricileri Aranıyor * Hayat, Bahama Adaları, Balıkçı Köyünde Yaşamak * Mutluluğun Anahtarı: Umursamamak* IstSec 11
* Startup Fikri Bulmaca* Korkuları Yenmek
* Startup, Ürün, Reklam ve Para ama özellikle Para * AnkaSEC '10 - Ankara Bilgi Güvenliği KonferansıDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0