Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://kosen-k.go.jp
Are you over 18 and want to see adult content?

A complete backup of https://solaranlagen-portal.com
Are you over 18 and want to see adult content?

A complete backup of https://intervac-homeexchange.com
Are you over 18 and want to see adult content?
A complete backup of https://maxim.com.au
Are you over 18 and want to see adult content?
A complete backup of https://evergreen.edu
Are you over 18 and want to see adult content?

A complete backup of https://neacollege.com
Are you over 18 and want to see adult content?
A complete backup of https://publicsphereproject.org
Are you over 18 and want to see adult content?

A complete backup of https://sinarmas.com
Are you over 18 and want to see adult content?
A complete backup of https://openforum.com.au
Are you over 18 and want to see adult content?

A complete backup of https://forum-raspberrypi.de
Are you over 18 and want to see adult content?

A complete backup of https://gbpics.to
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of dalepumas.bolavip.com/noticias/Pumas-UNAM-entrega-condolencias-por-fallecimiento-del-periodista-Jorge-Witke
Are you over 18 and want to see adult content?

A complete backup of www.jagran.com/news/education-ctet-2020-registration-for-july-5-exam-to-close-soon-check-how-to-apply-at-ct
Are you over 18 and want to see adult content?

A complete backup of www.pagina12.com.ar/248830-murio-jorge-todesca
Are you over 18 and want to see adult content?
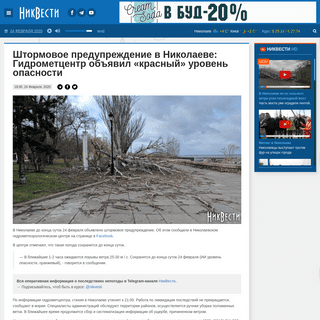
A complete backup of nikvesti.com/news/politics/180876
Are you over 18 and want to see adult content?
A complete backup of www.futbolperuano.com/peruanos-en-el-exterior/noticias/werder-bremen-vs-borussia-dortmund-en-vivo-online-cl
Are you over 18 and want to see adult content?
Text
INDEX
Index. 1139 . btrfs. command 785 Btrfs filesystem 742, 756, 772–773, 783–788 and Docker 930 setup 784–786 shallow copies 788 snapshots 786–787, 787–7881 WHERE TO START
4 Chapter 1 Where to Start and rules of thumb that help you recover systems from adversity, and we help you choose solutions that scale as your empire grows in size, complexity, and heterogeneity. 48 THE X WINDOW SYSTEM 1412 The X Window System, also called X11 or simply X, is the foundation for most graphical user environments for UNIX and Linux . X is the natural successor to a19 SLIP AND PPP
406 19 SLIP and PPP 19.1 I NTRODUCTION A typical UNIX environment consists of hosts connected with some type of network hardware, such as Ethernet. On top of this hardware, hostsDAEMONS 29 DAEMONS
Daemons 29.3 xinetd and inetd: manage daemons 887 The telinit command changes init’s run level once the system is up. For example, telinit 4 forces init to go to 50 SERIAL DEVICES AND TERMINALS 1448 Chapter 50 Serial Devices and Terminals and easy to crimp onto the ends of custom-cut cables . An inexpensive crimping tool is required . Several systems map the28 ACCOUNTING
Chapter 28 Accounting 643 sitting idle.” Well, here is an example of using process accounting to tackle a serious breach of security: When the Internet Worm hit in the Fall of 1988, it created several mis- chievous processes called -sh.30 UUCP - ADMIN
672 30 UUCP 30.1 I NTRODUCTION UUCP (UNIX-to-UNIX copy) is a set of programs and protocols that allow computers to communicate over serial connections, networks, or ordi- 26 DISK SPACE MANAGEMENT 618 26 Disk Space Management 26.1 I NTRODUCTION It has been said that the only thing all UNIX systems have in common is the login message asking users to clean up their files and use less disk FOREWORD - ADMIN.COM xxvii Foreword I was quite excited to preview this Linux-only edition of the UNIX System Adminis- tration Handbook.The third edition of USAH included coverage of Red Hat Linux, but it was only one of four very different variants of UNIX.INDEX
Index. 1139 . btrfs. command 785 Btrfs filesystem 742, 756, 772–773, 783–788 and Docker 930 setup 784–786 shallow copies 788 snapshots 786–787, 787–7881 WHERE TO START
4 Chapter 1 Where to Start and rules of thumb that help you recover systems from adversity, and we help you choose solutions that scale as your empire grows in size, complexity, and heterogeneity. 48 THE X WINDOW SYSTEM 1412 The X Window System, also called X11 or simply X, is the foundation for most graphical user environments for UNIX and Linux . X is the natural successor to a19 SLIP AND PPP
406 19 SLIP and PPP 19.1 I NTRODUCTION A typical UNIX environment consists of hosts connected with some type of network hardware, such as Ethernet. On top of this hardware, hostsDAEMONS 29 DAEMONS
Daemons 29.3 xinetd and inetd: manage daemons 887 The telinit command changes init’s run level once the system is up. For example, telinit 4 forces init to go to 50 SERIAL DEVICES AND TERMINALS 1448 Chapter 50 Serial Devices and Terminals and easy to crimp onto the ends of custom-cut cables . An inexpensive crimping tool is required . Several systems map the28 ACCOUNTING
Chapter 28 Accounting 643 sitting idle.” Well, here is an example of using process accounting to tackle a serious breach of security: When the Internet Worm hit in the Fall of 1988, it created several mis- chievous processes called -sh.30 UUCP - ADMIN
672 30 UUCP 30.1 I NTRODUCTION UUCP (UNIX-to-UNIX copy) is a set of programs and protocols that allow computers to communicate over serial connections, networks, or ordi- 26 DISK SPACE MANAGEMENT 618 26 Disk Space Management 26.1 I NTRODUCTION It has been said that the only thing all UNIX systems have in common is the login message asking users to clean up their files and use less disk FOREWORD - ADMIN.COM xxvii Foreword I was quite excited to preview this Linux-only edition of the UNIX System Adminis- tration Handbook.The third edition of USAH included coverage of Red Hat Linux, but it was only one of four very different variants of UNIX. UNIX AND LINUX SYSTEM ADMINISTRATION HANDBOOK, FIFTH EDTION UNIX and Linux System Administration Handbook, Fifth Edition, is today’s definitive guide to installing, configuring, and maintaining any UNIX or Linux system, including systems that supply core Internet and cloud infrastructure.1 WHERE TO START
4 Chapter 1 Where to Start and rules of thumb that help you recover systems from adversity, and we help you choose solutions that scale as your empire grows in size, complexity, and heterogeneity.28 ACCOUNTING
Chapter 28 Accounting 643 sitting idle.” Well, here is an example of using process accounting to tackle a serious breach of security: When the Internet Worm hit in the Fall of 1988, it created several mis- chievous processes called -sh. FOREWORD - ADMIN.COM Foreword xlv Out of that era came the first edition of this book and all the editions that followed it. In the parlance of the times, we called the authors “Evi and crew” or perhaps “EviSCRIPTING/SHELL
Loops 45 Scripting/Shell if ; then case $message_level in 0) message_level_text="Error" ;; 1) message_level_text="Warning" ;; ROUTING TABLES YOU CAN EXAMINE A MACHINE’S ROUTING TABLE 466 Chapter 14 TCP/IP Networking Routing tables You can examine a machine’s routing table with netstat -r.Use netstat -rn to avoid DNS lookups and present all DOC/SPEC - ADMIN.COM 808 Chapter 20 Electronic Mail Tons of Exim documentation are available on-line, as are a couple of books by the author of the software. Googling for Exim questions often seems to lead to24 USENET NEWS
563 24 Usenet News 24.1 I NTRODUCTION Usenet is a software system that distributes messages (“articles”) to many sites around the world. It is not really a type of network, butDNS - ADMIN.COM
Title: DNS.fm Author: Garth Created Date: 3/14/2012 12:07:24 AM SCRIPTING - ADMIN.COM Title: Scripting.fm Author: Garth Created Date: 2/9/2011 6:31:26 PM UNIX AND LINUX SYSTEM ADMINISTRATION HANDBOOK, FIFTH EDTIONLINUX SYSTEM ADMINISTRATION HANDBOOK PDFLINUX HANDBOOK PDFUNIX ADMINISTRATION PDFUNIX VS LINUX I'm teaching a course that uses UNIX and Linux System Administration Handbook as a textbook. Are there slides, outlines, or other materials available for instructors? Unfortunately, no. This is something we'd like to do, but the scope of the book makes it likely that different courses will choose to focus on different aspects of the material included in the book.1 WHERE TO START
4 Chapter 1 Where to Start and rules of thumb that help you recover systems from adversity, and we help you choose solutions that scale as your empire grows in size, complexity, and heterogeneity. 50 SERIAL DEVICES AND TERMINALS 1448 Chapter 50 Serial Devices and Terminals and easy to crimp onto the ends of custom-cut cables . An inexpensive crimping tool is required . Several systems map theINDEX
Index. 1139 . btrfs. command 785 Btrfs filesystem 742, 756, 772–773, 783–788 and Docker 930 setup 784–786 shallow copies 788 snapshots 786–787, 787–788DAEMONS 29 DAEMONS
Daemons 29.3 xinetd and inetd: manage daemons 887 The telinit command changes init’s run level once the system is up. For example, telinit 4 forces init to go to 48 THE X WINDOW SYSTEM 1412 The X Window System, also called X11 or simply X, is the foundation for most graphical user environments for UNIX and Linux . X is the natural successor to a19 SLIP AND PPP
406 19 SLIP and PPP 19.1 I NTRODUCTION A typical UNIX environment consists of hosts connected with some type of network hardware, such as Ethernet. On top of this hardware, hosts30 UUCP - ADMIN
672 30 UUCP 30.1 I NTRODUCTION UUCP (UNIX-to-UNIX copy) is a set of programs and protocols that allow computers to communicate over serial connections, networks, or ordi-TRIBUTE TO EVI
xl Every field has an avatar who defines and embodies that space. For system admin-istration, that person is Evi Nemeth. This is the 5th edition of a book that Evi led as an author for almost three decades. Although Evi wasn’t able to physically join us in writing this edition, she’s with usEMAIL - ADMIN
Title: Email.fm Author: Garth Created Date: 9/6/2011 11:09:39 PM UNIX AND LINUX SYSTEM ADMINISTRATION HANDBOOK, FIFTH EDTIONLINUX SYSTEM ADMINISTRATION HANDBOOK PDFLINUX HANDBOOK PDFUNIX ADMINISTRATION PDFUNIX VS LINUX I'm teaching a course that uses UNIX and Linux System Administration Handbook as a textbook. Are there slides, outlines, or other materials available for instructors? Unfortunately, no. This is something we'd like to do, but the scope of the book makes it likely that different courses will choose to focus on different aspects of the material included in the book.1 WHERE TO START
4 Chapter 1 Where to Start and rules of thumb that help you recover systems from adversity, and we help you choose solutions that scale as your empire grows in size, complexity, and heterogeneity. 50 SERIAL DEVICES AND TERMINALS 1448 Chapter 50 Serial Devices and Terminals and easy to crimp onto the ends of custom-cut cables . An inexpensive crimping tool is required . Several systems map theINDEX
Index. 1139 . btrfs. command 785 Btrfs filesystem 742, 756, 772–773, 783–788 and Docker 930 setup 784–786 shallow copies 788 snapshots 786–787, 787–788DAEMONS 29 DAEMONS
Daemons 29.3 xinetd and inetd: manage daemons 887 The telinit command changes init’s run level once the system is up. For example, telinit 4 forces init to go to 48 THE X WINDOW SYSTEM 1412 The X Window System, also called X11 or simply X, is the foundation for most graphical user environments for UNIX and Linux . X is the natural successor to a19 SLIP AND PPP
406 19 SLIP and PPP 19.1 I NTRODUCTION A typical UNIX environment consists of hosts connected with some type of network hardware, such as Ethernet. On top of this hardware, hosts30 UUCP - ADMIN
672 30 UUCP 30.1 I NTRODUCTION UUCP (UNIX-to-UNIX copy) is a set of programs and protocols that allow computers to communicate over serial connections, networks, or ordi-TRIBUTE TO EVI
xl Every field has an avatar who defines and embodies that space. For system admin-istration, that person is Evi Nemeth. This is the 5th edition of a book that Evi led as an author for almost three decades. Although Evi wasn’t able to physically join us in writing this edition, she’s with usEMAIL - ADMIN
Title: Email.fm Author: Garth Created Date: 9/6/2011 11:09:39 PMINDEX
1136 We have alphabetized files under their last components. And in most cases, only the last component is listed. For example, to find index entries relating to the /etc/mail/aliases file, look under aliases.Our friendly vendors have forced our hand by hiding standardfiles in
SCRIPTING/SHELL
Loops 45 Scripting/Shell if ; then case $message_level in 0) message_level_text="Error" ;; 1) message_level_text="Warning" ;;28 ACCOUNTING
Chapter 28 Accounting 643 sitting idle.” Well, here is an example of using process accounting to tackle a serious breach of security: When the Internet Worm hit in the Fall of 1988, it created several mis- chievous processes called -sh.FOREWORD - ADMIN
Foreword xlv Out of that era came the first edition of this book and all the editions that followed it. In the parlance of the times, we called the authors “Evi and crew” or perhaps “Evi DOC/SPEC - ADMIN.COM 808 Chapter 20 Electronic Mail Tons of Exim documentation are available on-line, as are a couple of books by the author of the software. Googling for Exim questions often seems to lead toSCRIPTING - ADMIN
Title: Scripting.fm Author: Garth Created Date: 2/9/2011 6:30:46 PM24 USENET NEWS
563 24 Usenet News 24.1 I NTRODUCTION Usenet is a software system that distributes messages (“articles”) to many sites around the world. It is not really a type of network, but FOREWORD - ADMIN.COM xxvii Foreword I was quite excited to preview this Linux-only edition of the UNIX System Adminis- tration Handbook.The third edition of USAH included coverage of Red Hat Linux, but it was only one of four very different variants of UNIX. SCRIPTING - ADMIN.COM Title: Scripting.fm Author: Garth Created Date: 2/9/2011 6:31:26 PMEMAIL - ADMIN
Title: Email.fm Author: Garth Created Date: 9/6/2011 11:09:39 PM Cover image and cartoons by Lisa Haney “I recommend this book for anyone administering UNIX or Linux systems.” David | 15 reviewers made a similar statement “It's well written, easy to read and very informative.” Gary L. Roach | 12 reviewers made a similar statement “Best Linux book I have purchased ever to date.” Josh | 15 reviewers made a similar statement We are pleased to announce the completely updated fifth edition of _UNIX and Linux System Administration Handbook!_ The book is published by Addison-WesleyProfessional.
“This edition is for those whose systems live in the cloud or in virtualized data centers; those whose administrative work largely takes the form of automation and configuration source code; those who collaborate closely with developers, network engineers, compliance officers, and all the other worker bees who inhabit the modernhive.”
— from the Foreword by Paul Vixie, Internet Hall of Fame-recognized innovator and founder of ISC and FarsightSecurity
“As an author, editor, and publisher, I never paid much attention to the competition— except in a few cases. This is one of those cases. _UNIX System Administration Handbook_ is one of the few books we ever measured ourselvesagainst.”
— from the 4th Edition Foreword by Tim O'Reilly, founder ofO'Reilly Media
FIND IT ONLINE
Print and Kindle editions Print and ePub (Nook) editions Publisher's site; print and DRM-free PDF editions Online access & PDF chapters (subscription service)SAMPLES AND EXTRAS
* SAMPLE CHAPTERS
* Table of Contents
* Tribute to Evi
* Preface
* Foreword
* Where to Start
* Index
* PAST FOREWORDS
* LAH1E by Linus Torvalds * ULSAH4E by Tim O'Reilly * USAH2E by Allman and McKusick * USAH1E by Dennis Ritchie* OTHER RESOURCES
* Errata and updates (4th Edition) * Frequently asked questions* OBSOLETE CHAPTERS
* SLIP and PPP (USAH2E) * Usenet News (USAH2E) * Disk Space Management (USAH2E) * Accounting (USAH2E)* UUCP (USAH2E)
* Daemons (LAH2E)
* Serial Devices and Terminals (ULSAH4E) * The X Windows System (ULSAH4E)ABOUT THE BOOK
UNIX and Linux System Administration Handbook, Fifth Edition, is today’s definitive guide to installing, configuring, and maintaining any UNIX or Linux system, including systems that supply core Internet and cloud infrastructure. Updated for new distributions and cloud environments, this comprehensive guide covers best practices for every facet of system administration, including storage management, network design and administration, security, web hosting, automation, configuration management, performance analysis, virtualization, DNS, security, and the management of IT service organizations. The authors—world-class, hands-on technologists—offer indispensable new coverage of cloud platforms, the DevOps philosophy, continuous deployment, containerization, monitoring, and many other essential topics. Whatever your role in running systems and networks built on UNIX or Linux, this conversational, well-written guide will improve your efficiency and help solve your knottiestproblems.
CONTACT US
x
ERRATA FOR UNIX AND LINUX SYSTEM ADMINISTRATION HANDBOOK, 4E We usually have the opportunity to make corrections before each printing. Therefore, your book's complement of errors may vary depending on its printing. To determine your printing, look at the last line of the copyright page. Found a problem not listed here? Please let us know. YOUR PRINTING: First printing Second printing Third printing Fourth printing Fifth printingUPDATED PAGES
ISSUES
p33
PAGE 33
The backquoted command WC -L /ETC/PASSWD seen in the page's last command line should actually be WC -L < /ETC/PASSWD. The issue is that WC -L prints out filenames as well as line counts when filenames are supplied on the command line. Here, only the line count is wanted.p44
PAGE 44
Contrary to Table 2.2, BASH has no string equivalents to the numeric -le and -ge operators. The >= and <= operators listed in Table 2.2 do not exist. The > and < operators do exist. However, they must be backslash-escaped or double bracketed to prevent them from being interpreted as I/O redirection characters.p45
PAGE 45
The loop variable in the example for loop is actually called script. The text refers to it as file.p51-52
PAGES 51 AND 52
The regular expression shown on pages 51–52 for matching various spellings of Moammar Gadhafi's name is OK as originally printed. However, the accompanying text does not explain why the (?)+ group (a component of the last name match) allows repetition. The + is there to accommodate variants such as Quadhdhafi. Really, that fragment should be (?){1,2} so that only one or two occurrences are permissible. More generally, it's worth noting that this regex is permissive. Not every string that it matches is a legitimate spelling of Gadhafi's name. However, it should match all legitimate spellings.p153
PAGE 153
The cross-reference in the last line of the first paragraph under THE SETUID AND SETGID BITS points to the wrong place. The referenced material is on page 105, not page 106.p466
PAGE 466
The ROUTE commands at the bottom of the page are shell commands, not excerpts from a startup script as the surrounding text mightimply.
The # character indicates root's shell prompt, not the comment character used in shell scripts.p574
PAGE 574
DNS Punycode names begin with xn--, not xf-- as stated in thetext.
p808
PAGE 808
In addition to having its own conventions, Debian's version of Exim configuration uses the M4 preprocessor. We don't describe the Debian system in this book.p817
PAGE 817
There are two errors on this page. In the sentence "The sender's address is not checked because many user agents get confused by error returns," replace "sender's address" with "recipient's address." The paragraph that starts "We next check the destination domain..." claims that DKIM verification is not performed during this step. That is incorrect; DKIM is in fact enabled.p821
PAGE 821
It is not entirely accurate to say that "If a message receives a pass or decline from all the routers in the sequence, it is bounced as an unroutable address." In fact, Exim may either bounce or reject such messages, depending on the context.p827
PAGE 827
Contrary to the statement in the DEBUGGING section, EXIM does fork when given the -D flag. However, it does not detach itself from the control terminal.p852
PAGE 852
In the configuration file excerpt, the line that sets dkim_selector should do a lookup on $dkim_domain, not $sender_address_domain as shown. NO FORMAL ERRATA ARE AVAILABLE FOR THIS PRINTING YET. WE WILL UPDATE THIS LIST AFTER THE NEXT PRINTING HAS BEENFINALIZED.
x
FREQUENTLY ASKED QUESTIONS ABOUT ULSAH4E I'm teaching a course that uses _UNIX and Linux System Administration Handbook_ as a textbook. Are there slides, outlines, or other materials available for instructors? Unfortunately, no. This is something we'd like to do, but the scope of the book makes it likely that different courses will choose to focus on different aspects of the material included in the book. If you have specific suggestions for supplementary materials that you would find helpful,please let us know.
I'm interested in translating your book into anotherlanguage.
Translation and foreign sales rights are handled by Prentice Hall. Please contact us and we will put you in touch with the rightpeople.
Is your book available as an eBook? What formats are available? ULSAH5E is available as a printed book, a Kindle book, a Nook-compatible ePub book, a DRM-free PDF file, and as an online resource through Safari Books Online . Please see the links on the home page. Hey! I found a mistake! You suck! We usually have the opportunity to make corrections before each printing. Please send us a note describing the issue and we will make sure it is addressed. (And thanks for yourhelp!)
There's a problem with my printed copy of the book. A small number of books were sent into distribution with missing pages or with pages out of order. If you've ended up with one of these copies, please let us know and we will hook you up with areplacement.
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0