Are you over 18 and want to see adult content?
More Annotations
DECORATOR'S NOTEBOOK ethical homeware and gifts to buy online
Are you over 18 and want to see adult content?

Road Bike City | Best Bike Deals & Promotions
Are you over 18 and want to see adult content?

Laura in the Kitchen - Starring Laura Vitale | Internet Cooking Show
Are you over 18 and want to see adult content?

Самые дорогие монеты Украины, России, СССР, цены и разновидности на сайте Монеты ин юа
Are you over 18 and want to see adult content?
Система приема электронных онлайн платежей на сайте через сервис PayU | PayU Russia
Are you over 18 and want to see adult content?

Portalul Asociatiilor Judetene de Fotbal | frf-ajf.ro
Are you over 18 and want to see adult content?

Sienge é o Software para Construção Civil
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of circuitospcine.com.br
Are you over 18 and want to see adult content?
A complete backup of majalahniaga.com
Are you over 18 and want to see adult content?
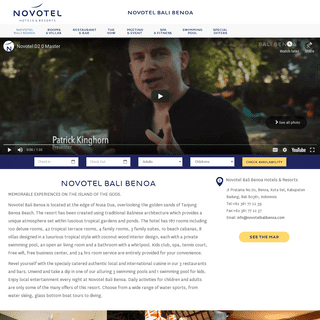
A complete backup of novotelbalibenoa.com
Are you over 18 and want to see adult content?
A complete backup of belliskincare.com
Are you over 18 and want to see adult content?
Text
PARTNER LOGIN
Forcepoint Global Partner Program. Login failed. Please contact your regional representative below. < back to login. Forgot Password. Regional Representative Contacts: North America. Latin America & Caribbean. Europe, Middle East, Africa, and Asia Pacific. SYSTEM REQUIREMENTS FOR THIS VERSION 8 CPU cores (2.5 GHz), 16 GB available RAM, 400 GB Disk space. Web Security and Data Security. 8 CPU cores (2.5 GHz), 20 GB available RAM, 400 GB Disk Space. Email Security and Data Security. 8 CPU cores (2.5 GHz), 20 GB available RAM, 400 GB Disk Space. REAL-TIME THREAT ANALYSIS WITH CSI: ACE INSIGHT 5 reports remaining CSI ACE Insight is a tool for assessing the current state and risk level of a web link or IP address. CSI ACE Insight performs real-time content analysis, and then displays a report of its findings. Files are analyzed in the Forcepoint Advanced Malware Detection™ tool, a sandbox that identifies threats and, ifapplicable
RELEASE NOTES FOR FORCEPOINT ONE ENDPOINT V20.12 Release Notes for Forcepoint One Endpoint v20.12. Use these Release Notes to learn what's new and improved in this Forcepoint™ One Endpoint release. The following Forcepoint One Endpoint versions are new in this release: This release reflects changes since the Forcepoint One Endpoint v20.09 release on September 24, 2020. LDAP FILTER FOR USERS, GROUPS, AND EMAIL LDAP filter for users, groups, and email. In the Directory Synchronization Client, there are 3 synchronization types (groups, users, and email), each with its own LDAP search set up. The searches are independent of one another to give you flexibility in selecting the appropriate data. For example, you can use the LDAP groupattribute to select
UNINSTALLING ENDPOINT SOFTWARE To uninstall with package: 1. Follow the procedure for Creating and distributing Websense endpoints using SDCCM or SMS. 2. In step 1, select Per-system uninstall. 3. Complete the remaining procedures. 4. After deploying the package, the Websense Endpoint will be uninstalled from the defined list ofBACKUP AND RESTORE
Restoring from backup. When a backup is restored, all current settings for the appliance or module are erased. The appliance is always restarted after a restore. Before performing a restore, stop all TRITON Architecture components running off the appliance. Full appliance restores and module-specific restores require that theseconditions are
INTEGRATED WINDOWS AUTHENTICATION Integrated Windows Authentication (IWA) is a robust method of authenticating users who belong to shared-trust Windows domains (one or many). Integrated Windows Authentication: Uses Kerberos and SPNEGO. Supports NTLM in both explicit and transparent proxy modes. Supports NTLMv2 and NTLMv1 with Session Security. CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
HOW IS A PAC FILE CONSUMED? Although the PAC file can be placed on each individual client machine, this is an uncommon and inefficient approach. The common arrangementis to host
PARTNER LOGIN
Forcepoint Global Partner Program. Login failed. Please contact your regional representative below. < back to login. Forgot Password. Regional Representative Contacts: North America. Latin America & Caribbean. Europe, Middle East, Africa, and Asia Pacific. SYSTEM REQUIREMENTS FOR THIS VERSION 8 CPU cores (2.5 GHz), 16 GB available RAM, 400 GB Disk space. Web Security and Data Security. 8 CPU cores (2.5 GHz), 20 GB available RAM, 400 GB Disk Space. Email Security and Data Security. 8 CPU cores (2.5 GHz), 20 GB available RAM, 400 GB Disk Space. REAL-TIME THREAT ANALYSIS WITH CSI: ACE INSIGHT 5 reports remaining CSI ACE Insight is a tool for assessing the current state and risk level of a web link or IP address. CSI ACE Insight performs real-time content analysis, and then displays a report of its findings. Files are analyzed in the Forcepoint Advanced Malware Detection™ tool, a sandbox that identifies threats and, ifapplicable
RELEASE NOTES FOR FORCEPOINT ONE ENDPOINT V20.12 Release Notes for Forcepoint One Endpoint v20.12. Use these Release Notes to learn what's new and improved in this Forcepoint™ One Endpoint release. The following Forcepoint One Endpoint versions are new in this release: This release reflects changes since the Forcepoint One Endpoint v20.09 release on September 24, 2020. LDAP FILTER FOR USERS, GROUPS, AND EMAIL LDAP filter for users, groups, and email. In the Directory Synchronization Client, there are 3 synchronization types (groups, users, and email), each with its own LDAP search set up. The searches are independent of one another to give you flexibility in selecting the appropriate data. For example, you can use the LDAP groupattribute to select
UNINSTALLING ENDPOINT SOFTWARE To uninstall with package: 1. Follow the procedure for Creating and distributing Websense endpoints using SDCCM or SMS. 2. In step 1, select Per-system uninstall. 3. Complete the remaining procedures. 4. After deploying the package, the Websense Endpoint will be uninstalled from the defined list ofBACKUP AND RESTORE
Restoring from backup. When a backup is restored, all current settings for the appliance or module are erased. The appliance is always restarted after a restore. Before performing a restore, stop all TRITON Architecture components running off the appliance. Full appliance restores and module-specific restores require that theseconditions are
INTEGRATED WINDOWS AUTHENTICATION Integrated Windows Authentication (IWA) is a robust method of authenticating users who belong to shared-trust Windows domains (one or many). Integrated Windows Authentication: Uses Kerberos and SPNEGO. Supports NTLM in both explicit and transparent proxy modes. Supports NTLMv2 and NTLMv1 with Session Security. CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
HOW IS A PAC FILE CONSUMED? Although the PAC file can be placed on each individual client machine, this is an uncommon and inefficient approach. The common arrangementis to host
MY ACCOUNT REGISTRATION close X More Info. Enter the name of a known corporate contact within your company who can verify you. INTEGRATED WINDOWS AUTHENTICATION Integrated Windows Authentication (IWA) is a robust method of authenticating users who belong to shared-trust Windows domains (one or many). Integrated Windows Authentication: Uses Kerberos and SPNEGO. Supports NTLM in both explicit and transparent proxy modes. Supports NTLMv2 and NTLMv1 with Session Security.OPERATING TIPS
Featured; Websense Threat Report; Websense Security Predictions; The Forrester Wave™: SaaS Web Content Security, Q2 2015; Gartner 2015 Magic Quadrant For Secure Web Gateways WEBSITES THAT HAVE DIFFICULTY TRANSITING CONTENT GATEWAY To find the name of the WebEx site: 1. On the Content Gateway host, change directory to /opt/WCG/sxsuite/log and open or view inbound_access.log. 2. Most often, the unresolved CONNECT will be in close proximity to a successful *.webex.com connect, so start by searching for webex.com. SYSTEM REQUIREMENTS FOR THIS VERSION Forcepoint LLC provides "best effort" support for newer versions of Red Hat Enterprise Linux. Under "best effort" support, Technical Support makes a best effort to troubleshoot cases in standard fashion unless the issue is deemed a Red Hat Enterprise Linux-specific issue, at which point you must contact Red Hat directly for assistance. CONFIGURING FILTERING SETTINGS Configuring filtering settings. Use the Settings > General > Filtering page to establish basic settings for how Internet requests are handled. Use the General Filtering section to determine how policies are applied to users when multiple group policies could apply; specify keyword search options; and set password override, account overrideTABLE OF CONTENTS
Editing appliance settings from the appliances list. Managing domain and IP address groups. Adding a domain group FORCEPOINT DLP PORTS The most robust and effective implementation of Forcepoint DLP depends on certain ports being open to support the mechanics of the software. The ports for Forcepoint DLP components are 17500-17515 by default. These ports must be left open for all Forcepoint DLP software and hardware configurations. If you have a security policy in place CONFIGURING TLS ON YOUR CONNECTIONS 1. 2. Click the server name of the inbound or outbound email gateway that you want to configure. 3. Click Edit. 4. Add security and encryption strength settings to the connections on which you wish to enforce TLS. Typically these are the same inbound and outbound. Inbound TLS settings apply to all inbound connections. CONFIGURING RELAY CONTROL OPTIONS Configure relay control settings in the Settings > Inbound/Outbound > Relay Control page as follows: 1. In the Inbound Relay Options section, set any desired option that is based on the Sender Policy Framework (SPF) of the sender domain: Reject mail if no SPF record exists. Reject mail if the SPF record does not match the sender'sdomain or a
BACKUP AND RESTORE
Restoring from backup. When a backup is restored, all current settings for the appliance or module are erased. The appliance is always restarted after a restore. Before performing a restore, stop all TRITON Architecture components running off the appliance. Full appliance restores and module-specific restores require that theseconditions are
MANAGING CERTIFICATES 1. Go to Configure > SSL > Certificates > Certificate Authorities. 2. Select the name of the authority whose status you want to change. 3. In the pop-up window, select Click to change status to. Depending on the status of the certificate, your choice is allow or deny. If you change the status to deny, a red X appears next to the name of the THE FORCEPOINT DLP TRAFFIC LOG The Forcepoint DLP traffic log. Use the Main > Logs > Traffic Log page in the Data Security module of the Security Manager to see details of the traffic monitored over specific periods, as well as the action taken. For the endpoint channel, the log displays only traffic that breaches policy. To customize the information shown in each column CONFIGURING FILTERING SETTINGS Configuring filtering settings. Use the Settings > General > Filtering page to establish basic settings for how Internet requests are handled. Use the General Filtering section to determine how policies are applied to users when multiple group policies could apply; specify keyword search options; and set password override, account override INSTALLING THE ENDPOINT ON A SINGLE MACHINE (CLASSIC PROXY Follow the steps below to deploy an endpoint client on a single machine. 1. Unzip the downloaded endpoint file to a location on the machine. 2. Open a command-line window, and navigate to the location of the unzipped endpoint files. 3. Where WSCONTEXT= xxxx is the unique GPO configuration code noted from the Endpoint Download page in theportal.
PROXY QUERY PAGE
Proxy query page. For clients that use a PAC file to connect to the cloud service, a proxy query page is available that allows you to confirm whether the browser is correctly configured. (Because clients using the Direct Connect endpoint do not send traffic through the proxy, the query page cannot be used to validate connections fromthese
THE FORCEPOINT DLP SYSTEM LOG The Forcepoint DLP system log. Use the Main > Logs > System Log page in the Data Security module of the Security Manager to see system actions sent from different Forcepoint components, such as Forcepoint DLP servers, protectors, gateways, and policy engines. Examine the details of each action, including the date and time it occurred andthe
WINDOWS ACTIVE DIRECTORY (NATIVE MODE) In order for Websense User Service to communicate with Active Directory in Native Mode, you must provide information about the global catalog servers in your network. 1. Click Add, next to the Global catalog servers list. The Add Global Catalog Server page appears. 2. Provide the IPv4 address or hostname of the global catalogserver: If you
LOG SERVER TROUBLESHOOTING GUIDE Log Server Troubleshooting 4 3. Make sure there is sufficient disk space on the SQL machine to create the Log Database files. This may mean creating the Log Database on a drive other than C. CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
BACKUP AND RESTORE
Restoring from backup. When a backup is restored, all current settings for the appliance or module are erased. The appliance is always restarted after a restore. Before performing a restore, stop all TRITON Architecture components running off the appliance. Full appliance restores and module-specific restores require that theseconditions are
MANAGING CERTIFICATES 1. Go to Configure > SSL > Certificates > Certificate Authorities. 2. Select the name of the authority whose status you want to change. 3. In the pop-up window, select Click to change status to. Depending on the status of the certificate, your choice is allow or deny. If you change the status to deny, a red X appears next to the name of the THE FORCEPOINT DLP TRAFFIC LOG The Forcepoint DLP traffic log. Use the Main > Logs > Traffic Log page in the Data Security module of the Security Manager to see details of the traffic monitored over specific periods, as well as the action taken. For the endpoint channel, the log displays only traffic that breaches policy. To customize the information shown in each column CONFIGURING FILTERING SETTINGS Configuring filtering settings. Use the Settings > General > Filtering page to establish basic settings for how Internet requests are handled. Use the General Filtering section to determine how policies are applied to users when multiple group policies could apply; specify keyword search options; and set password override, account override INSTALLING THE ENDPOINT ON A SINGLE MACHINE (CLASSIC PROXY Follow the steps below to deploy an endpoint client on a single machine. 1. Unzip the downloaded endpoint file to a location on the machine. 2. Open a command-line window, and navigate to the location of the unzipped endpoint files. 3. Where WSCONTEXT= xxxx is the unique GPO configuration code noted from the Endpoint Download page in theportal.
PROXY QUERY PAGE
Proxy query page. For clients that use a PAC file to connect to the cloud service, a proxy query page is available that allows you to confirm whether the browser is correctly configured. (Because clients using the Direct Connect endpoint do not send traffic through the proxy, the query page cannot be used to validate connections fromthese
THE FORCEPOINT DLP SYSTEM LOG The Forcepoint DLP system log. Use the Main > Logs > System Log page in the Data Security module of the Security Manager to see system actions sent from different Forcepoint components, such as Forcepoint DLP servers, protectors, gateways, and policy engines. Examine the details of each action, including the date and time it occurred andthe
WINDOWS ACTIVE DIRECTORY (NATIVE MODE) In order for Websense User Service to communicate with Active Directory in Native Mode, you must provide information about the global catalog servers in your network. 1. Click Add, next to the Global catalog servers list. The Add Global Catalog Server page appears. 2. Provide the IPv4 address or hostname of the global catalogserver: If you
LOG SERVER TROUBLESHOOTING GUIDE Log Server Troubleshooting 4 3. Make sure there is sufficient disk space on the SQL machine to create the Log Database files. This may mean creating the Log Database on a drive other than C. CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
MANAGING CERTIFICATES 1. Go to Configure > SSL > Certificates > Certificate Authorities. 2. Select the name of the authority whose status you want to change. 3. In the pop-up window, select Click to change status to. Depending on the status of the certificate, your choice is allow or deny. If you change the status to deny, a red X appears next to the name of the CONFIGURING FILTERING SETTINGS Configuring filtering settings. Use the Settings > General > Filtering page to establish basic settings for how Internet requests are handled. Use the General Filtering section to determine how policies are applied to users when multiple group policies could apply; specify keyword search options; and set password override, account override INTEGRATED WINDOWS AUTHENTICATION Integrated Windows Authentication (IWA) is a robust method of authenticating users who belong to shared-trust Windows domains (one or many). Integrated Windows Authentication: Uses Kerberos and SPNEGO. Supports NTLM in both explicit and transparent proxy modes. Supports NTLMv2 and NTLMv1 with Session Security. ENABLING SSL SUPPORT Enabling SSL support. 1. 2. Under Features > Protocols, set HTTPS to On. If you are deployed with the DLP Module and it is configured to inspect HTTPS traffic, you must enable HTTPS. 3. Click Apply and then Restart. 4. Enter the name of the SSL certificate file. NEXT GENERATION FIREWALL Next Generation Firewall 330 Series Hardware Guide Models 330, 331, 335, 335W Revision B CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
ADMINISTRATOR ACCOUNT PASSWORD RECOVERY Administrator account password recovery. Have a temporary password sent to the email address configured on the appliance. Contact Forcepoint Technical Support to receive a temporary password by providing the security code displayed on the console. See CONFIGURING RELAY CONTROL OPTIONS Configure relay control settings in the Settings > Inbound/Outbound > Relay Control page as follows: 1. In the Inbound Relay Options section, set any desired option that is based on the Sender Policy Framework (SPF) of the sender domain: Reject mail if no SPF record exists. Reject mail if the SPF record does not match the sender'sdomain or a
DIRECTORY SYNCHRONIZATION CLIENT ADMINISTRATOR’S GUIDE Introducing the Directory Synchronization Client 4 Directory Synchronization Client This is an example Active Directory schema:Below are some
FORCEPOINT SECURITY INFORMATION EVENT MANAGEMENT (SIEM Security Information Event Management 2 Configuration for each Multiplexer instance is stored by its Policy Server. This means that you can configure different settings forBACKUP AND RESTORE
Restoring from backup. When a backup is restored, all current settings for the appliance or module are erased. The appliance is always restarted after a restore. Before performing a restore, stop all TRITON Architecture components running off the appliance. Full appliance restores and module-specific restores require that theseconditions are
MANAGING CERTIFICATES 1. Go to Configure > SSL > Certificates > Certificate Authorities. 2. Select the name of the authority whose status you want to change. 3. In the pop-up window, select Click to change status to. Depending on the status of the certificate, your choice is allow or deny. If you change the status to deny, a red X appears next to the name of the THE FORCEPOINT DLP TRAFFIC LOG The Forcepoint DLP traffic log. Use the Main > Logs > Traffic Log page in the Data Security module of the Security Manager to see details of the traffic monitored over specific periods, as well as the action taken. For the endpoint channel, the log displays only traffic that breaches policy. To customize the information shown in each column CONFIGURING FILTERING SETTINGS Configuring filtering settings. Use the Settings > General > Filtering page to establish basic settings for how Internet requests are handled. Use the General Filtering section to determine how policies are applied to users when multiple group policies could apply; specify keyword search options; and set password override, account override INSTALLING THE ENDPOINT ON A SINGLE MACHINE (CLASSIC PROXY Follow the steps below to deploy an endpoint client on a single machine. 1. Unzip the downloaded endpoint file to a location on the machine. 2. Open a command-line window, and navigate to the location of the unzipped endpoint files. 3. Where WSCONTEXT= xxxx is the unique GPO configuration code noted from the Endpoint Download page in theportal.
PROXY QUERY PAGE
Proxy query page. For clients that use a PAC file to connect to the cloud service, a proxy query page is available that allows you to confirm whether the browser is correctly configured. (Because clients using the Direct Connect endpoint do not send traffic through the proxy, the query page cannot be used to validate connections fromthese
THE FORCEPOINT DLP SYSTEM LOG The Forcepoint DLP system log. Use the Main > Logs > System Log page in the Data Security module of the Security Manager to see system actions sent from different Forcepoint components, such as Forcepoint DLP servers, protectors, gateways, and policy engines. Examine the details of each action, including the date and time it occurred andthe
WINDOWS ACTIVE DIRECTORY (NATIVE MODE) In order for Websense User Service to communicate with Active Directory in Native Mode, you must provide information about the global catalog servers in your network. 1. Click Add, next to the Global catalog servers list. The Add Global Catalog Server page appears. 2. Provide the IPv4 address or hostname of the global catalogserver: If you
LOG SERVER TROUBLESHOOTING GUIDE Log Server Troubleshooting 4 3. Make sure there is sufficient disk space on the SQL machine to create the Log Database files. This may mean creating the Log Database on a drive other than C. CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
BACKUP AND RESTORE
Restoring from backup. When a backup is restored, all current settings for the appliance or module are erased. The appliance is always restarted after a restore. Before performing a restore, stop all TRITON Architecture components running off the appliance. Full appliance restores and module-specific restores require that theseconditions are
MANAGING CERTIFICATES 1. Go to Configure > SSL > Certificates > Certificate Authorities. 2. Select the name of the authority whose status you want to change. 3. In the pop-up window, select Click to change status to. Depending on the status of the certificate, your choice is allow or deny. If you change the status to deny, a red X appears next to the name of the THE FORCEPOINT DLP TRAFFIC LOG The Forcepoint DLP traffic log. Use the Main > Logs > Traffic Log page in the Data Security module of the Security Manager to see details of the traffic monitored over specific periods, as well as the action taken. For the endpoint channel, the log displays only traffic that breaches policy. To customize the information shown in each column CONFIGURING FILTERING SETTINGS Configuring filtering settings. Use the Settings > General > Filtering page to establish basic settings for how Internet requests are handled. Use the General Filtering section to determine how policies are applied to users when multiple group policies could apply; specify keyword search options; and set password override, account override INSTALLING THE ENDPOINT ON A SINGLE MACHINE (CLASSIC PROXY Follow the steps below to deploy an endpoint client on a single machine. 1. Unzip the downloaded endpoint file to a location on the machine. 2. Open a command-line window, and navigate to the location of the unzipped endpoint files. 3. Where WSCONTEXT= xxxx is the unique GPO configuration code noted from the Endpoint Download page in theportal.
PROXY QUERY PAGE
Proxy query page. For clients that use a PAC file to connect to the cloud service, a proxy query page is available that allows you to confirm whether the browser is correctly configured. (Because clients using the Direct Connect endpoint do not send traffic through the proxy, the query page cannot be used to validate connections fromthese
THE FORCEPOINT DLP SYSTEM LOG The Forcepoint DLP system log. Use the Main > Logs > System Log page in the Data Security module of the Security Manager to see system actions sent from different Forcepoint components, such as Forcepoint DLP servers, protectors, gateways, and policy engines. Examine the details of each action, including the date and time it occurred andthe
WINDOWS ACTIVE DIRECTORY (NATIVE MODE) In order for Websense User Service to communicate with Active Directory in Native Mode, you must provide information about the global catalog servers in your network. 1. Click Add, next to the Global catalog servers list. The Add Global Catalog Server page appears. 2. Provide the IPv4 address or hostname of the global catalogserver: If you
LOG SERVER TROUBLESHOOTING GUIDE Log Server Troubleshooting 4 3. Make sure there is sufficient disk space on the SQL machine to create the Log Database files. This may mean creating the Log Database on a drive other than C. CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
MANAGING CERTIFICATES 1. Go to Configure > SSL > Certificates > Certificate Authorities. 2. Select the name of the authority whose status you want to change. 3. In the pop-up window, select Click to change status to. Depending on the status of the certificate, your choice is allow or deny. If you change the status to deny, a red X appears next to the name of the CONFIGURING FILTERING SETTINGS Configuring filtering settings. Use the Settings > General > Filtering page to establish basic settings for how Internet requests are handled. Use the General Filtering section to determine how policies are applied to users when multiple group policies could apply; specify keyword search options; and set password override, account override INTEGRATED WINDOWS AUTHENTICATION Integrated Windows Authentication (IWA) is a robust method of authenticating users who belong to shared-trust Windows domains (one or many). Integrated Windows Authentication: Uses Kerberos and SPNEGO. Supports NTLM in both explicit and transparent proxy modes. Supports NTLMv2 and NTLMv1 with Session Security. ENABLING SSL SUPPORT Enabling SSL support. 1. 2. Under Features > Protocols, set HTTPS to On. If you are deployed with the DLP Module and it is configured to inspect HTTPS traffic, you must enable HTTPS. 3. Click Apply and then Restart. 4. Enter the name of the SSL certificate file. NEXT GENERATION FIREWALL Next Generation Firewall 330 Series Hardware Guide Models 330, 331, 335, 335W Revision B CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
ADMINISTRATOR ACCOUNT PASSWORD RECOVERY Administrator account password recovery. Have a temporary password sent to the email address configured on the appliance. Contact Forcepoint Technical Support to receive a temporary password by providing the security code displayed on the console. See CONFIGURING RELAY CONTROL OPTIONS Configure relay control settings in the Settings > Inbound/Outbound > Relay Control page as follows: 1. In the Inbound Relay Options section, set any desired option that is based on the Sender Policy Framework (SPF) of the sender domain: Reject mail if no SPF record exists. Reject mail if the SPF record does not match the sender'sdomain or a
DIRECTORY SYNCHRONIZATION CLIENT ADMINISTRATOR’S GUIDE Introducing the Directory Synchronization Client 4 Directory Synchronization Client This is an example Active Directory schema:Below are some
FORCEPOINT SECURITY INFORMATION EVENT MANAGEMENT (SIEM Security Information Event Management 2 Configuration for each Multiplexer instance is stored by its Policy Server. This means that you can configure different settings for HOW FORCEPOINT WEB SECURITY CLOUD WORKS Forcepoint Web Security Cloud operates as a proxy server for HTTP and HTTPS traffic, as well as FTP over HTTP. When users request a web resource, their browsers do not connect directly to Internet web servers (shown in the following diagram as origin servers), but instead connect to the cloud proxy, which in turn relays requests tothe origin server.
BACKUP AND RESTORE
Restoring from backup. When a backup is restored, all current settings for the appliance or module are erased. The appliance is always restarted after a restore. Before performing a restore, stop all TRITON Architecture components running off the appliance. Full appliance restores and module-specific restores require that theseconditions are
INSTALLATION AND DEPLOYMENT GUIDE Installation and Deployment Guide 3 Introducing Forcepoint One Endpoint If your organization has deployed an earlier version of Forcepoint One Endpoint, CONFIGURE MAIL FLOW IN OFFICE 365 2. From the left navigation pane, select Admin > Exchange. 3. From the left navigation pane, select Mail Flow. 4. Create a connector that routes mail from Office 365 to Forcepoint Email Security in Azure: a. From the top of the page, click Connectors, and then click the plus sign (+) to add a new connector. b. CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
LDAP AUTHENTICATION
In the Authentication section, click LDAP On, and then click Apply. 3. Configure the Global authentication options. 4. Go to Configure > Security > Access Control > LDAP. 5. Enter the hostname of the LDAP server. 6. Enter the port on which Content Gateway communicates withthe LDAP server.
CONFIGURING LOG SERVER If your environment uses SQL Server clustering, enter the virtual IP address for the cluster. 4. Enter the name of the Default database (wslogdb70, by default). 5. Indicate whether or not to Use SSL to connect to the Log Database. When SSL encryption is enabled: THE FORCEPOINT DLP SYSTEM LOG The Forcepoint DLP system log. Use the Main > Logs > System Log page in the Data Security module of the Security Manager to see system actions sent from different Forcepoint components, such as Forcepoint DLP servers, protectors, gateways, and policy engines. Examine the details of each action, including the date and time it occurred andthe
WINDOWS ACTIVE DIRECTORY (NATIVE MODE)ENABLE ACTIVE DIRECTORY DOMAIN SERVICESINSTALL ACTIVE DIRECTORY DOMAIN SERVICESTART ACTIVE DIRECTORY DOMAIN SERVICESTURN ON ACTIVE DIRECTORY DOMAIN SERVICESACTIVE DIRECTORY DOMAIN SERVICES DOWNLOADACTIVE DOMAIN DIRECTORY SERVICEWINDOWS 10
In order for Websense User Service to communicate with Active Directory in Native Mode, you must provide information about the global catalog servers in your network. 1. Click Add, next to the Global catalog servers list. The Add Global Catalog Server page appears. 2. Provide the IPv4 address or hostname of the global catalogserver: If you
UNINSTALLING THE ENDPOINT FROM THE MAC Click OK. Then enter the endpoint anti-tampering password that you setin the portal.
HOW FORCEPOINT WEB SECURITY CLOUD WORKS Forcepoint Web Security Cloud operates as a proxy server for HTTP and HTTPS traffic, as well as FTP over HTTP. When users request a web resource, their browsers do not connect directly to Internet web servers (shown in the following diagram as origin servers), but instead connect to the cloud proxy, which in turn relays requests tothe origin server.
BACKUP AND RESTORE
Restoring from backup. When a backup is restored, all current settings for the appliance or module are erased. The appliance is always restarted after a restore. Before performing a restore, stop all TRITON Architecture components running off the appliance. Full appliance restores and module-specific restores require that theseconditions are
INSTALLATION AND DEPLOYMENT GUIDE Installation and Deployment Guide 3 Introducing Forcepoint One Endpoint If your organization has deployed an earlier version of Forcepoint One Endpoint, CONFIGURE MAIL FLOW IN OFFICE 365 2. From the left navigation pane, select Admin > Exchange. 3. From the left navigation pane, select Mail Flow. 4. Create a connector that routes mail from Office 365 to Forcepoint Email Security in Azure: a. From the top of the page, click Connectors, and then click the plus sign (+) to add a new connector. b. CONTENT GATEWAY ALARM MESSAGES This alarm is a reminder that downloads of the security scanning data files used by Content Gateway analysis has been suspended. It is recommended that you not clear this alarm until the delay time has been reset. Port Mirroring cannot work unless SSL decryption isenabled also.
LDAP AUTHENTICATION
In the Authentication section, click LDAP On, and then click Apply. 3. Configure the Global authentication options. 4. Go to Configure > Security > Access Control > LDAP. 5. Enter the hostname of the LDAP server. 6. Enter the port on which Content Gateway communicates withthe LDAP server.
CONFIGURING LOG SERVER If your environment uses SQL Server clustering, enter the virtual IP address for the cluster. 4. Enter the name of the Default database (wslogdb70, by default). 5. Indicate whether or not to Use SSL to connect to the Log Database. When SSL encryption is enabled: THE FORCEPOINT DLP SYSTEM LOG The Forcepoint DLP system log. Use the Main > Logs > System Log page in the Data Security module of the Security Manager to see system actions sent from different Forcepoint components, such as Forcepoint DLP servers, protectors, gateways, and policy engines. Examine the details of each action, including the date and time it occurred andthe
WINDOWS ACTIVE DIRECTORY (NATIVE MODE)ENABLE ACTIVE DIRECTORY DOMAIN SERVICESINSTALL ACTIVE DIRECTORY DOMAIN SERVICESTART ACTIVE DIRECTORY DOMAIN SERVICESTURN ON ACTIVE DIRECTORY DOMAIN SERVICESACTIVE DIRECTORY DOMAIN SERVICES DOWNLOADACTIVE DOMAIN DIRECTORY SERVICEWINDOWS 10
In order for Websense User Service to communicate with Active Directory in Native Mode, you must provide information about the global catalog servers in your network. 1. Click Add, next to the Global catalog servers list. The Add Global Catalog Server page appears. 2. Provide the IPv4 address or hostname of the global catalogserver: If you
UNINSTALLING THE ENDPOINT FROM THE MAC Click OK. Then enter the endpoint anti-tampering password that you setin the portal.
WEBSENSE CONTENT GATEWAY Websense Content Gateway (Content Gateway) is a Linux-based, high-performance Web proxy and cache that provides real-time content scanning and Web site classification to protect network computers from malicious Web content while controlling employee access to dynamic, user-generated Web 2.0 content.Web content has evolved from a static information source to a sophisticated platform for 2 MANAGING CERTIFICATES 1. Go to Configure > SSL > Certificates > Certificate Authorities. 2. Select the name of the authority whose status you want to change. 3. In the pop-up window, select Click to change status to. Depending on the status of the certificate, your choice is allow or deny. If you change the status to deny, a red X appears next to the name of the INTEGRATED WINDOWS AUTHENTICATION Integrated Windows Authentication (IWA) is a robust method of authenticating users who belong to shared-trust Windows domains (one or many). Integrated Windows Authentication: Uses Kerberos and SPNEGO. Supports NTLM in both explicit and transparent proxy modes. Supports NTLMv2 and NTLMv1 with Session Security. CONFIGURING YOUR FIREWALL TO CONNECT TO THE CLOUD SERVICE Configuring your firewall to connect to the cloud service. In order for the cloud service to manage web traffic from your network, your firewall must allow TCP connections outbound to Forcepoint data centers on specific ports. The table below details the ports that may be used, depending on your configuration. Port. Required for. REAL-TIME THREAT ANALYSIS WITH CSI: ACE INSIGHT 5 reports remaining CSI ACE Insight is a tool for assessing the current state and risk level of a web link or IP address. CSI ACE Insight performs real-time content analysis, and then displays a report of its findings. Files are analyzed in the Forcepoint Advanced Malware Detection™ tool, a sandbox that identifies threats and, ifapplicable
CONFIGURE MAIL FLOW IN OFFICE 365 2. From the left navigation pane, select Admin > Exchange. 3. From the left navigation pane, select Mail Flow. 4. Create a connector that routes mail from Office 365 to Forcepoint Email Security in Azure: a. From the top of the page, click Connectors, and then click the plus sign (+) to add a new connector. b. CONFIGURING LOG SERVER If your environment uses SQL Server clustering, enter the virtual IP address for the cluster. 4. Enter the name of the Default database (wslogdb70, by default). 5. Indicate whether or not to Use SSL to connect to the Log Database. When SSL encryption is enabled: ENABLING SSL SUPPORT Enabling SSL support. 1. 2. Under Features > Protocols, set HTTPS to On. If you are deployed with the DLP Module and it is configured to inspect HTTPS traffic, you must enable HTTPS. 3. Click Apply and then Restart. 4. Enter the name of the SSL certificate file.TIME AND DATE
Stop all Forcepoint services before changing the time. Then, set the time and make certain the time is consistent across all serversrunning services.
HOW THE SERVICE WORKS FOR ROAMING USERS This article describes how the cloud service handles users who are roaming – that is, users accessing the Internet away from your network. Typically, this applies to users who are traveling or working at another location, and connecting their company laptop to a Wi-Fi network belonging to another organization, such as a hotel, a home network, or another business. Skip to main contentForcepoint
Enter your keywords
Is Type
* Company
Back
* About Us
* Executive Team
* Customers
* Newsroom
* Careers
* Events
* Contact Us
* Cybersecurity Experience Center * Support & TrainingBack
* Support
* Training
* Implementation Packages* Find a Partner
* Partners
Back
* Partner Login
* Request a Partner Login * Global Partner Program * Accredited Services Partners* Become a Partner
* Find a Distributor* MSSP Program
* Technology Partners * Authorized Training Center (ATC) Program * Partner Sales Training* Blogs
EnglishEspañol (América Latina)FrançaisDeutschItalianoPortuguês简体中文繁體中文日本語한국어Türkçe* Data & IP
Back
Securing data at rest, in-motion, and in-use across hybridenvironments.
We are a 9x leader in Gartner’s Enterprise DLP Magic Quadrant.SCHEDULE A DEMO
* Products
* CASB: Cloud Access Security Broker * DLP: Data Loss Prevention * UEBA: Behavioral Analytics* I Need To
* Protect Data in the Cloud * Securely Implement Office 365 * Dynamic Data Protection* Comply with GDPR
* Next-Gen My Data Protection View All Data & IP Protection Products and Use Cases* Cloud & Network
Back
Transform your network and security for the cloud. Forcepoint NGFW is a visionary for the 3rd year in Gartner's 2019 Magic Quadrant for NGFW.SCHEDULE A DEMO
* Products
* NGFW: Next Generation Firewall* Web Security
* CASB: Cloud Access Security Broker* Email Security
* I Need To
* Connect and Secure Remote Offices and Branches * Modernize My Hybrid Network * Access and Move Data on Separate Networks View All Cloud & Network Security Products and Use Cases* Insider Threat
Back
Protect your workforce and supply chain from insider theft andsabotage.
Stopping insider threats for over 15 years with over 1M endpointsprotected.
SCHEDULE A DEMO
* Products
* UEBA: Behavioral Analytics* Insider Threat
* DLP: Data Loss Prevention* I Need To
* Start an Insider Threat Program View All Workforce Protection Products and Use Cases* Our Platform
Back
* Converged Security Platform* Forcepoint X-Labs
* Technology Partners * Deployment Options* View All Products
* Industries
Back
* Government
* Critical Infrastructure * Financial Services* Healthcare
* Retail
* Resources
Back
* Watch/Listen
* Videos
* Webcasts
* Podcasts
* Download
* Brochures
* Datasheets
* Infographics
* Read
* eBooks
* Analyst Reports
* Whitepapers
* Reports
* Case Studies
* Cyber Edu
* Schedule a Demo
Schedule a Demo Main Menu RISK-ADAPTIVE PROTECTION ADAPTIVE SECURITY THROUGH BEHAVIORAL ANALYTICSGet A Demo
BEST-IN-CLASS PRODUCTS DESIGNED TO INTEGRATE SEAMLESSLY WITH YOUR EXISTING ENVIRONMENT.WEB
52% better efficacy than the closest competitor. Meet Forcepoint's Web SecurityNETWORK
3x Gartner Magic Quadrant Visionary. Meet Forcepoint's NGFW and SD-WANCLOUD
Supports any cloud application on the market. Meet Forcepoint's CASBDATA
9x Gartner Magic Quadrant Leader. Meet Forcepoint's DLPINSIDER THREAT
Stopping insider threats for over 15 years with over 1M endpointsprotected.
Meet Forcepoint's Insider ThreatBrowse all products
OUR SOFTWARE PROTECTS THOUSANDS OF COMPANIES WORLDWIDE See customer stories FORCEPOINT “RECOMMENDED” IN NSS LABS NGFW GROUP TEST FOR SEVENTHYEAR IN A ROW
Forcepoint’s position confirms what we hear from our customer regarding our solution’s excellent combination of security as wellas cost-efficiency.
Read the Report
LATEST UPDATES FROM FORCEPOINTWEBCAST
2019 GOVERNMENT CYBERSECURITY PREDICTIONSWATCH THE WEBCAST
Blog
SEEING WHAT WE BELIEVE: MY THOUGHTS ON YEAR THREE AT FORCEPOINTRead the Blog
News
FORCEPOINT STRENGTHENS GLOBAL PARTNER PROGRAM TO DYNAMICALLY ACCELERATE ADOPTION OF BEHAVIOR-CENTRIC CYBERSECURITYOct 8, 2019
FORCEPOINT STRENGTHENS GLOBAL PARTNER PROGRAM TO DYNAMICALLY ACCELERATE ADOPTION OF BEHAVIOR-CENTRIC CYBERSECURITYRead the News
NEW ZEALAND CYBER SECURITY SUMMIT 2019Events
Oct 16, 2019 |
WellingtonNew Zealand NEW ZEALAND CYBER SECURITY SUMMIT 2019 Join Forcepoint at booth 10 to uncover "intelligent" data protection. Talk to our experts about our leading data protection solutions plus play our Security Posture game to win a Bose Smart Speaker Max worth $379! Attend out round table where we will be discussing the topic "Secure your Data and your Users with Confidence whether in Cloud/ Hybrid / On premise"Get Registered
READY TO LEARN MORE?Get a Demo
PROTECTING THE HUMAN POINT IS BOTH FORCEPOINT'S VISION AND THE FOCUSOF OUR PRODUCTS.
SCHEDULE A LIVE DEMO WITH A FORCEPOINT REPRESENTATIVESchedule a Demo
* Stay Up To Speed
* Join Our Mailing List* Feedback
* Report a Vulnerability* Contact Us
* Other
* Careers
* Services
* Free Trials
Terms & Conditions
Legal and Privacy
� 2019 Forcepoint
* YouTube
* RSS
3X MAGIC QUADRANT VISIONARY FOR NGFWGet the report
Gartner report
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0