Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://susskind.com
Are you over 18 and want to see adult content?
A complete backup of https://shiftcomm.com
Are you over 18 and want to see adult content?
A complete backup of https://mstdn.beer
Are you over 18 and want to see adult content?
A complete backup of https://avebiom.org
Are you over 18 and want to see adult content?
A complete backup of https://takingitglobal.org
Are you over 18 and want to see adult content?
A complete backup of https://bruichladdich.com
Are you over 18 and want to see adult content?
A complete backup of https://electrolube.com
Are you over 18 and want to see adult content?
A complete backup of https://allvectorlogo.com
Are you over 18 and want to see adult content?

A complete backup of https://horizonbrokers.com
Are you over 18 and want to see adult content?

A complete backup of https://beldicountryclub.com
Are you over 18 and want to see adult content?

A complete backup of https://sunburst.com
Are you over 18 and want to see adult content?
A complete backup of https://accuesp.com
Are you over 18 and want to see adult content?
Favourite Annotations
Resources, Data and Commentary on Australian Politics
Are you over 18 and want to see adult content?

Photo Slideshow Software with 3D Effects | SmartSHOW 3D
Are you over 18 and want to see adult content?
Buy Wholefoods Online | Whole foods UK | Organic Foods | Health Foods
Are you over 18 and want to see adult content?
The Wordrobe magazine luxury travel and food - TheWordrobe.com
Are you over 18 and want to see adult content?

hostifex.com | 526: Invalid SSL certificate
Are you over 18 and want to see adult content?
Healthy Builderz — Your online daily source of healthy news.
Are you over 18 and want to see adult content?

Imodium aiuta a combattere la diarrea | IMODIUM<sup>®</sup>
Are you over 18 and want to see adult content?
Text
ThreatSense engine.
WIN32/CHAINSAW.C
Short description Win32/Chainsaw.C is a worm that spreads via network exploiting vulnerabilities of the operating system.WIN32/AGENT.PCU
The trojan contains an URL address. The HTTP protocol is used. Win32/Agent.PCU is a trojan that repeatedly tries to connect to various URL addresses. It tries to download several files from the addresses. A string with variable content is used instead of %variable% . The files are then executed.TOP THREATS
1992 - 2021 ESET, spol. s r.o. - All rights reserved. Trademarks used therein are trademarks or registered trademarks of ESET, spol. s r.o. or ESET North America.WIN32/RAMNIT.A
The virus spreads by exploiting a vulnerability in the operating system of the targeted machine. This vulnerability is described in CVE-2010-2568 . The Windows Shell allows local users or remote attackers to execute arbitrary code via a crafted *.lnk, *.pif shortcut file when its icon is displayed. No further user interactionis required to
WIN32/VBBOT.V
Short description The trojan contains a backdoor. It can be controlled remotely. Installation The trojan creates the following files:WIN32/NOONLIGHT.B
Short description. Win32/NoonLight.B is a worm that spreads via e-mail, P2P networks and shared folders. The file is run-time compressed using PECompact . WIN32/TROJANDOWNLOADER.NECURS.A Short description Win32/TrojanDownloader.Necurs.A is a trojan which tries to download other malware from the Internet. It uses techniques common for rootkits. WIN32/PSW.ONLINEGAMES.NMY Installation. When executed, the trojan copies itself into the %system% folder using the following name: kavo.exe (115749 B) The following file is dropped in the same folder: kavo0.dll (124928 B) The following files are dropped into the %temp% folder: gxylc.dll (26910 B) zs.sys (3450 B) The trojan creates and runs a new thread with itsown
LNK/EXPLOIT.CVE-2010-2568 LNK/Exploit.CVE-2010-2568 is a generic detection for specially-crafted malicious shortcut files that exploit the vulnerability in the Windows Shell . This vulnerability is described in CVE-2010-2568 . The trojan is usually a part of other malware. HOME | ESET VIRUSRADAR ESET Online Scanner Show More Tools. ESET Online Scanner is a fast and free tool that detects and removes threats on your PC. Utilizing only your browser, it scans your computer with ESET's award-winningThreatSense engine.
WIN32/CHAINSAW.C
Short description Win32/Chainsaw.C is a worm that spreads via network exploiting vulnerabilities of the operating system.WIN32/AGENT.PCU
The trojan contains an URL address. The HTTP protocol is used. Win32/Agent.PCU is a trojan that repeatedly tries to connect to various URL addresses. It tries to download several files from the addresses. A string with variable content is used instead of %variable% . The files are then executed.TOP THREATS
1992 - 2021 ESET, spol. s r.o. - All rights reserved. Trademarks used therein are trademarks or registered trademarks of ESET, spol. s r.o. or ESET North America.WIN32/RAMNIT.A
The virus spreads by exploiting a vulnerability in the operating system of the targeted machine. This vulnerability is described in CVE-2010-2568 . The Windows Shell allows local users or remote attackers to execute arbitrary code via a crafted *.lnk, *.pif shortcut file when its icon is displayed. No further user interactionis required to
WIN32/VBBOT.V
Short description The trojan contains a backdoor. It can be controlled remotely. Installation The trojan creates the following files:WIN32/NOONLIGHT.B
Short description. Win32/NoonLight.B is a worm that spreads via e-mail, P2P networks and shared folders. The file is run-time compressed using PECompact . WIN32/TROJANDOWNLOADER.NECURS.A Short description Win32/TrojanDownloader.Necurs.A is a trojan which tries to download other malware from the Internet. It uses techniques common for rootkits. WIN32/PSW.ONLINEGAMES.NMY Installation. When executed, the trojan copies itself into the %system% folder using the following name: kavo.exe (115749 B) The following file is dropped in the same folder: kavo0.dll (124928 B) The following files are dropped into the %temp% folder: gxylc.dll (26910 B) zs.sys (3450 B) The trojan creates and runs a new thread with itsown
LNK/EXPLOIT.CVE-2010-2568 LNK/Exploit.CVE-2010-2568 is a generic detection for specially-crafted malicious shortcut files that exploit the vulnerability in the Windows Shell . This vulnerability is described in CVE-2010-2568 . The trojan is usually a part of other malware.WIN32/RAMNIT.A
The virus spreads by exploiting a vulnerability in the operating system of the targeted machine. This vulnerability is described in CVE-2010-2568 . The Windows Shell allows local users or remote attackers to execute arbitrary code via a crafted *.lnk, *.pif shortcut file when its icon is displayed. No further user interactionis required to
TOP THREATS
1992 - 2021 ESET, spol. s r.o. - All rights reserved. Trademarks used therein are trademarks or registered trademarks of ESET, spol. s r.o. or ESET North America. WIN32/TROJANDOWNLOADER.NECURS.A Short description Win32/TrojanDownloader.Necurs.A is a trojan which tries to download other malware from the Internet. It uses techniques common for rootkits.WIN32/NOONLIGHT.B
Short description Win32/NoonLight.B is a worm that spreads via e-mail, P2P networks and shared folders. The file is run-time compressed usingPECompact .
WIN32/ROVNIX.A
Win32/Rovnix.A replaces the original MBR (Master Boot Record) of the hard disk drive with its own program code. The trojan may create and run a new thread with its own program code within any running process. After the installation is complete, the trojan deletes the originalexecutable file.
WIN32/PEERFRAG.EU
Spreading via P2P networks. Win32/Peerfrag.EU is a worm that spreads via P2P networks. The worm searches for shared folders of the following programs: It tries to place a copy of itself into thefolders.
LNK/EXPLOIT.CVE-2010-2568 LNK/Exploit.CVE-2010-2568 is a generic detection for specially-crafted malicious shortcut files that exploit the vulnerability in the Windows Shell . This vulnerability is described in CVE-2010-2568 . The trojan is usually a part of other malware.WIN32/DORKBOT.B
Short description Win32/Dorkbot.B is a worm that spreads via removable media. The worm serves as a backdoor.WIN32/CONFICKER.AA
Short description Win32/Conficker.AA is a worm that spreads via shared folders and removable media. It connects to remote machines in attempt to exploit the Server Service vulnerability.WIN32/SALITY.NAR
Win32/Sality.NAR is a polymorphic file infector. The virus searches local and network drives for files with one of the following extensions: .exe. Files are infected by adding a new section that contains the virus . The host file is modified in a way that causes the virus to be executed prior to running the original code. Skip to main content* Home
* Threat Encyclopaedia* Glossary
* Statistics
* Update Info
* Tools
* Reports
* Threat Radar Report, February 2014+
−
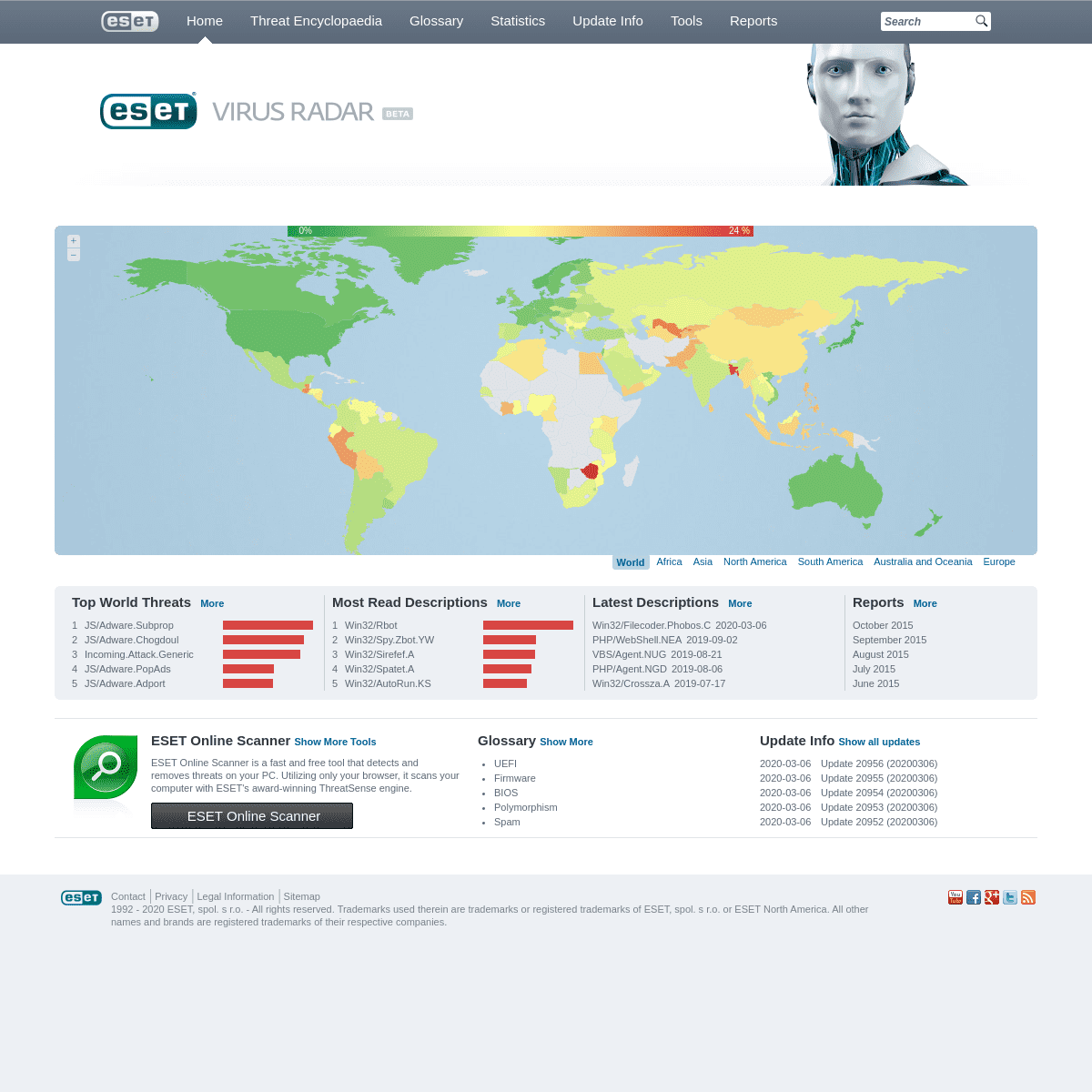
0%
24 %
* World
* Africa
* Asia
* North America
* South America
* Australia and Oceania* Europe
TOP WORLD THREATSMORE1
JS/Adware.Subprop
2
JS/Adware.Chogdoul
3
Incoming.Attack.Generic4
JS/Adware.PopAds
5
JS/Adware.Adport
MOST READ DESCRIPTIONSMORE1
Win32/Rbot
2
Win32/Spy.Zbot.YW
3
Win32/Sirefef.A
4
Win32/Spatet.A
5
Win32/AutoRun.KS
LATEST DESCRIPTIONSMORE * Win32/Filecoder.Phobos.C2020-03-06
* PHP/WebShell.NEA 2019-09-02 * VBS/Agent.NUG 2019-08-21 * PHP/Agent.NGD 2019-08-06 * Win32/Crossza.A 2019-07-17REPORTSMORE
* October 2015
* September 2015
* August 2015
* July 2015
* June 2015
ESET ONLINE SCANNERSHOW MORE TOOLS ESET Online Scanner is a fast and free tool that detects and removes threats on your PC. Utilizing only your browser, it scans your computer with ESET's award-winning ThreatSense engine.ESET Online Scanner
GLOSSARYSHOW MORE
* UEFI
* Firmware
* BIOS
* Polymorphism
* Spam
UPDATE INFOSHOW ALL UPDATES2020-03-06
Update 20956 (20200306)2020-03-06
Update 20955 (20200306)2020-03-06
Update 20954 (20200306)2020-03-06
Update 20953 (20200306)2020-03-06
Update 20952 (20200306)* Contact |
* Privacy |
* Legal Information |* Sitemap
1992 - 2020 ESET, spol. s r.o. - All rights reserved. Trademarks used therein are trademarks or registered trademarks of ESET, spol. s r.o. or ESET North America. All other names and brands are registered trademarks of their respective companies. Please enable Javascript to ensure correct displaying of this content and refresh this page.Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0