Are you over 18 and want to see adult content?
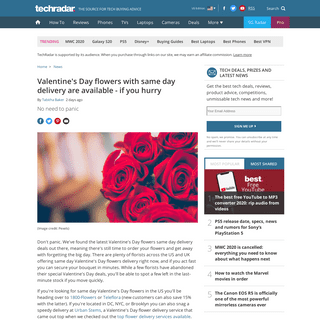
More Annotations

A complete backup of www.bbc.com/news/entertainment-arts-51517973
Are you over 18 and want to see adult content?

A complete backup of www.gala.fr/l_actu/news_de_stars/photos-leila-kaddour-boudadi-enceinte-a-39-ans-la-journaliste-de-france-2-
Are you over 18 and want to see adult content?

A complete backup of www.20minutes.fr/sport/2719255-20200215-tour-provence-nairo-quintana-impose-maitre-mont-ventoux-petit-decep
Are you over 18 and want to see adult content?

A complete backup of telugu.samayam.com/telugu-movies/cinema-news/vijay-deverakonda-world-famous-lover-public-talk-and-audience-
Are you over 18 and want to see adult content?

A complete backup of elcomercio.pe/deporte-total/futbol-mundial/transmision-en-directo-atletico-nacional-vs-deportivo-cali-en-vi
Are you over 18 and want to see adult content?

A complete backup of www.huffingtonpost.it/entry/concorrente-corregge-la-domanda-di-chi-vuol-essere-milionario-queste-non-sono-m
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://babytula.com
Are you over 18 and want to see adult content?

A complete backup of https://pfjones.co.uk
Are you over 18 and want to see adult content?

A complete backup of https://berenstainbears.com
Are you over 18 and want to see adult content?

A complete backup of https://kernpharma.com
Are you over 18 and want to see adult content?
A complete backup of https://csgostash.com
Are you over 18 and want to see adult content?

A complete backup of https://infofru.com
Are you over 18 and want to see adult content?
A complete backup of https://goodfruit.com
Are you over 18 and want to see adult content?
A complete backup of https://publicbikes.com
Are you over 18 and want to see adult content?

A complete backup of https://lakersstore.com
Are you over 18 and want to see adult content?
A complete backup of https://getnotion.com
Are you over 18 and want to see adult content?
A complete backup of https://x-cart.com
Are you over 18 and want to see adult content?

A complete backup of https://sclegal.org
Are you over 18 and want to see adult content?
Text
ABOUT THIS SITE
about this site. This page originated some time ago as a text generated page built from perl scripts. Later it became a blog because I had run out of time to create parts which I found useful in WordPress. Later, for performance reasons WordPress doesn't reallyscale on
WELCOME
6tunnel, 6tunnel, allowing v6 for v4 programs. DNS, sooner AXFR is gone the better. encryption, be sure to hide the plain text. netmon, interface throughput. netrs, interface throughput. nt proxy authentication. orange. my perforce quick start guide. plus.netservice.
RBL PAGE - USENIX.ORG.UKSEE MORE ON USENIX.ORG.UK REQUST FOR RBL REMOVAL HELP Removal help. Please note, this form will not be processed automatically. We try to investigate your request as soon as possible, but due to volumes of requests you may not get a response for days. If you would like to delist sooner, please use the automatic system, here are the details on how to use that, please read them. Please enter theRBL CHECKER
RBL Check against known DNSBLs. This page below will list various RBL listings for your IP address. I am in no way responsible for the listing of your IP address at the remote servers below. If you want to have an address removed you will need to contact the administratorthere.
UNIX BEARDS
Alan Cox has done a serious amount of kernel hacking, hence his huge unkempt beard. Something is wrong with this picture, Andrew Morton, a unix expert and kernel programmer must have passed the beard like the Olympic torch to Alan Cox. Dennis Ritchie, one man behind C, UNIX and much more, has a full beard. So too does Brian Kernighan. WET SHAVING WITH SOAP AND DOUBLE EDGE RAZORS Work the cream onto your face, dip briefly into sink water (only one or two mm to wet the brush), work into a foam on your face. Shave with the grain to remove the bulk of the stubble. Rinse face to remove excess cream. Apply cream again, dip again briefly as above.LATEX AND MAKEFILES
LaTeX documents do not crash on legal trials like MS Word documents when they're merged together.. The main reason I like LaTeX is that it can be given variables at build time, rather than when the document is being written, similar to system environment variables. REWRITEMAPS AND MOD_REWRITE rewritemaps and mod_rewrite. RewriteMaps are extremely useful, especially if you have a large database of links that you're moving from and old site structure. The redirectmaps allow for indexing/hash of data through the use of external programs or DBM files. CONFIG_SCHED_AUTOGROUP 3.0.0 general settings, autogroup. Of course, if you just want to modify the config file yourself, by hand then you'll be looking for this option: CONFIG_SCHED_AUTOGROUP=y. The most outstanding thing that you may notice about this is just how much smoother the whole system appears to function once the scheduler has been configured this way.ABOUT THIS SITE
about this site. This page originated some time ago as a text generated page built from perl scripts. Later it became a blog because I had run out of time to create parts which I found useful in WordPress. Later, for performance reasons WordPress doesn't reallyscale on
WELCOME
6tunnel, 6tunnel, allowing v6 for v4 programs. DNS, sooner AXFR is gone the better. encryption, be sure to hide the plain text. netmon, interface throughput. netrs, interface throughput. nt proxy authentication. orange. my perforce quick start guide. plus.netservice.
RBL PAGE - USENIX.ORG.UKSEE MORE ON USENIX.ORG.UK REQUST FOR RBL REMOVAL HELP Removal help. Please note, this form will not be processed automatically. We try to investigate your request as soon as possible, but due to volumes of requests you may not get a response for days. If you would like to delist sooner, please use the automatic system, here are the details on how to use that, please read them. Please enter theRBL CHECKER
RBL Check against known DNSBLs. This page below will list various RBL listings for your IP address. I am in no way responsible for the listing of your IP address at the remote servers below. If you want to have an address removed you will need to contact the administratorthere.
UNIX BEARDS
Alan Cox has done a serious amount of kernel hacking, hence his huge unkempt beard. Something is wrong with this picture, Andrew Morton, a unix expert and kernel programmer must have passed the beard like the Olympic torch to Alan Cox. Dennis Ritchie, one man behind C, UNIX and much more, has a full beard. So too does Brian Kernighan. WET SHAVING WITH SOAP AND DOUBLE EDGE RAZORS Work the cream onto your face, dip briefly into sink water (only one or two mm to wet the brush), work into a foam on your face. Shave with the grain to remove the bulk of the stubble. Rinse face to remove excess cream. Apply cream again, dip again briefly as above.LATEX AND MAKEFILES
LaTeX documents do not crash on legal trials like MS Word documents when they're merged together.. The main reason I like LaTeX is that it can be given variables at build time, rather than when the document is being written, similar to system environment variables. REWRITEMAPS AND MOD_REWRITE rewritemaps and mod_rewrite. RewriteMaps are extremely useful, especially if you have a large database of links that you're moving from and old site structure. The redirectmaps allow for indexing/hash of data through the use of external programs or DBM files. CONFIG_SCHED_AUTOGROUP 3.0.0 general settings, autogroup. Of course, if you just want to modify the config file yourself, by hand then you'll be looking for this option: CONFIG_SCHED_AUTOGROUP=y. The most outstanding thing that you may notice about this is just how much smoother the whole system appears to function once the scheduler has been configured this way. BOOKS - USENIX.ORG.UK A great insight into travel. cyber. Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin's Most Dangerous Hackers. 0385544405. How the era of cyber espionage has taken hold. Mindf*ck: Inside Cambridge Analytica’s Plot to Break the World. 1788164997. WET SHAVING WITH SOAP AND DOUBLE EDGE RAZORS Work the cream onto your face, dip briefly into sink water (only one or two mm to wet the brush), work into a foam on your face. Shave with the grain to remove the bulk of the stubble. Rinse face to remove excess cream. Apply cream again, dip again briefly as above. PLEASE.INI - USENIX.ORG.UK NAME. please.ini - configuration file for access. DESCRIPTION. The please.ini file contains one or more that hold ACL for users of the please and pleaseedit programs.. please.ini is an ini file, sections can be named with a short description of what the section provides. You may then find this helpful when listing rights with please -l.. Rules are read and applied in the order theyLATEX AND MAKEFILES
LaTeX documents do not crash on legal trials like MS Word documents when they're merged together.. The main reason I like LaTeX is that it can be given variables at build time, rather than when the document is being written, similar to system environment variables. WHAT ARE MY OPEN PORTS Scanning 40.77.167.97 for open ports. Device is not responding to ICMP ping requests. You are stealth like. Good job! PERFORCE QUICK START If you inspect this you may note the following line: This is a clever way of starting the Perforce server ' p4d ' upon request. rsh in the P4PORT environment tells the p4 client to spawn the /bin/sh shell. Normally you would see tcp or ssl followed by an IP and TCP port address here, but rsh works to execute a command. TSOCKS, THE USEFUL WAY We need to setup the SSH configuration now. $ /usr/bin/ssh -D 1085 -o TCPKeepAlive=yes -o ServerAliveInterval=60 192.168.0.1. -D signifies that we want to create a socks server on port 1085. We would like TCP Keep-Alives, at intervals of 60 seconds. 192.168.0.1 is the host we're connecting to. Leave that running in the background and we can get POWERSHELL - USENIX.ORG.UK powershell on linux or windows. Now, lets try using a powershell pipe and see if that changes anything. A powershell pipe construct can be used against a loop, so that you iterate each of the input objectitems.
SUDO MAIN PAGE
Sudo (su "do") allows a system administrator to delegate authority to give certain users (or groups of users) the ability to run some (or all) commands as root or another user while providing an audit trail of the commands and their arguments. For more information, see the introduction to Sudo . Sudo is free software, distributed under an ISCTOOLBOX LTD
www.toolbox.co.uk Units 2, 3 and 4 Millennium Court Enterprise Way Evesham Worcs WR11 1GS The dealings which I had with Toolbox/toolbox.co.uk are listed below. BOOKS - USENIX.ORG.UK A great insight into travel. cyber. Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin's Most Dangerous Hackers. 0385544405. How the era of cyber espionage has taken hold. Mindf*ck: Inside Cambridge Analytica’s Plot to Break the World. 1788164997.ABOUT THIS SITE
about this site. This page originated some time ago as a text generated page built from perl scripts. Later it became a blog because I had run out of time to create parts which I found useful in WordPress. Later, for performance reasons WordPress doesn't reallyscale on
WELCOME
6tunnel, 6tunnel, allowing v6 for v4 programs. DNS, sooner AXFR is gone the better. encryption, be sure to hide the plain text. netmon, interface throughput. netrs, interface throughput. nt proxy authentication. orange. my perforce quick start guide. plus.netservice.
RBL PAGE - USENIX.ORG.UKSEE MORE ON USENIX.ORG.UK WET SHAVING WITH SOAP AND DOUBLE EDGE RAZORS Work the cream onto your face, dip briefly into sink water (only one or two mm to wet the brush), work into a foam on your face. Shave with the grain to remove the bulk of the stubble. Rinse face to remove excess cream. Apply cream again, dip again briefly as above. PLEASE.INI - USENIX.ORG.UKSEE MORE ON USENIX.ORG.UK REQUST FOR RBL REMOVAL HELP Removal help. Please note, this form will not be processed automatically. We try to investigate your request as soon as possible, but due to volumes of requests you may not get a response for days. If you would like to delist sooner, please use the automatic system, here are the details on how to use that, please read them. Please enter theUNIX BEARDS
Alan Cox has done a serious amount of kernel hacking, hence his huge unkempt beard. Something is wrong with this picture, Andrew Morton, a unix expert and kernel programmer must have passed the beard like the Olympic torch to Alan Cox. Dennis Ritchie, one man behind C, UNIX and much more, has a full beard. So too does Brian Kernighan.RBL CHECKER
RBL Check against known DNSBLs. This page below will list various RBL listings for your IP address. I am in no way responsible for the listing of your IP address at the remote servers below. If you want to have an address removed you will need to contact the administratorthere.
SUDO MAIN PAGE
Sudo (su "do") allows a system administrator to delegate authority to give certain users (or groups of users) the ability to run some (or all) commands as root or another user while providing an audit trail of the commands and their arguments. For more information, see the introduction to Sudo . Sudo is free software, distributed under an ISC BOOKS - USENIX.ORG.UK A great insight into travel. cyber. Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin's Most Dangerous Hackers. 0385544405. How the era of cyber espionage has taken hold. Mindf*ck: Inside Cambridge Analytica’s Plot to Break the World. 1788164997.ABOUT THIS SITE
about this site. This page originated some time ago as a text generated page built from perl scripts. Later it became a blog because I had run out of time to create parts which I found useful in WordPress. Later, for performance reasons WordPress doesn't reallyscale on
WELCOME
6tunnel, 6tunnel, allowing v6 for v4 programs. DNS, sooner AXFR is gone the better. encryption, be sure to hide the plain text. netmon, interface throughput. netrs, interface throughput. nt proxy authentication. orange. my perforce quick start guide. plus.netservice.
RBL PAGE - USENIX.ORG.UKSEE MORE ON USENIX.ORG.UK WET SHAVING WITH SOAP AND DOUBLE EDGE RAZORS Work the cream onto your face, dip briefly into sink water (only one or two mm to wet the brush), work into a foam on your face. Shave with the grain to remove the bulk of the stubble. Rinse face to remove excess cream. Apply cream again, dip again briefly as above. PLEASE.INI - USENIX.ORG.UKSEE MORE ON USENIX.ORG.UK REQUST FOR RBL REMOVAL HELP Removal help. Please note, this form will not be processed automatically. We try to investigate your request as soon as possible, but due to volumes of requests you may not get a response for days. If you would like to delist sooner, please use the automatic system, here are the details on how to use that, please read them. Please enter theUNIX BEARDS
Alan Cox has done a serious amount of kernel hacking, hence his huge unkempt beard. Something is wrong with this picture, Andrew Morton, a unix expert and kernel programmer must have passed the beard like the Olympic torch to Alan Cox. Dennis Ritchie, one man behind C, UNIX and much more, has a full beard. So too does Brian Kernighan.RBL CHECKER
RBL Check against known DNSBLs. This page below will list various RBL listings for your IP address. I am in no way responsible for the listing of your IP address at the remote servers below. If you want to have an address removed you will need to contact the administratorthere.
SUDO MAIN PAGE
Sudo (su "do") allows a system administrator to delegate authority to give certain users (or groups of users) the ability to run some (or all) commands as root or another user while providing an audit trail of the commands and their arguments. For more information, see the introduction to Sudo . Sudo is free software, distributed under an ISC BOOKS - USENIX.ORG.UK A great insight into travel. cyber. Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin's Most Dangerous Hackers. 0385544405. How the era of cyber espionage has taken hold. Mindf*ck: Inside Cambridge Analytica’s Plot to Break the World. 1788164997.RBL CHECKER
RBL Check against known DNSBLs. This page below will list various RBL listings for your IP address. I am in no way responsible for the listing of your IP address at the remote servers below. If you want to have an address removed you will need to contact the administratorthere.
LATEX AND MAKEFILES
LaTeX documents do not crash on legal trials like MS Word documents when they're merged together.. The main reason I like LaTeX is that it can be given variables at build time, rather than when the document is being written, similar to system environment variables. SNMP MIB - USENIX.ORG.UK SNMP MIB. This should get important available OIDS for SNMP requests. This document might seem out of place but its here because I had to do some conversion between MRTG and IfIndexes and OIDs, this helped greatly so I've copied it here and theFFMPEG CHEAT SHEET
Convert mp4 audio to wav. $ ffmpeg -i input.mp4 -vn -acodec pcm_s16le -ar 44100 -ac 2 output.wav. Remove audio from video file: $ ffmpeg -i video.3gp -vcodec copy -an newvideo.3gp. Converting formats. $ ffmpeg -i video.mkv -acodec copy -vcodec copy video.mp4. Turning a mp4 audio file with chapters into individual mp3 files per chapter. POWERSHELL - USENIX.ORG.UK powershell on linux or windows. Now, lets try using a powershell pipe and see if that changes anything. A powershell pipe construct can be used against a loop, so that you iterate each of the input objectitems.
PINEBOOK PRO AND CROSS COMPILING how to cross compile with rust/cargo. Since x86_64 isn't aarch64 binaries compiled for Intel/AMD will not be compatible with ARM. The Pinebook Pro is aarch64, therefore we need to be able to compile binaries with ease for either. TSOCKS, THE USEFUL WAY We need to setup the SSH configuration now. $ /usr/bin/ssh -D 1085 -o TCPKeepAlive=yes -o ServerAliveInterval=60 192.168.0.1. -D signifies that we want to create a socks server on port 1085. We would like TCP Keep-Alives, at intervals of 60 seconds. 192.168.0.1 is the host we're connecting to. Leave that running in the background and we can get REWRITEMAPS AND MOD_REWRITE rewritemaps and mod_rewrite. RewriteMaps are extremely useful, especially if you have a large database of links that you're moving from and old site structure. The redirectmaps allow for indexing/hash of data through the use of external programs or DBM files.SUDO MAIN PAGE
Sudo (su "do") allows a system administrator to delegate authority to give certain users (or groups of users) the ability to run some (or all) commands as root or another user while providing an audit trail of the commands and their arguments. For more information, see the introduction to Sudo . Sudo is free software, distributed under an ISC BOOKS - USENIX.ORG.UK A great insight into travel. cyber. Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin's Most Dangerous Hackers. 0385544405. How the era of cyber espionage has taken hold. Mindf*ck: Inside Cambridge Analytica’s Plot to Break the World. 1788164997.ABOUT THIS SITE
about this site. This page originated some time ago as a text generated page built from perl scripts. Later it became a blog because I had run out of time to create parts which I found useful in WordPress. Later, for performance reasons WordPress doesn't reallyscale on
WELCOME
6tunnel, 6tunnel, allowing v6 for v4 programs. DNS, sooner AXFR is gone the better. encryption, be sure to hide the plain text. netmon, interface throughput. netrs, interface throughput. nt proxy authentication. orange. my perforce quick start guide. plus.netservice.
UNIX BEARDS
Alan Cox has done a serious amount of kernel hacking, hence his huge unkempt beard. Something is wrong with this picture, Andrew Morton, a unix expert and kernel programmer must have passed the beard like the Olympic torch to Alan Cox. Dennis Ritchie, one man behind C, UNIX and much more, has a full beard. So too does Brian Kernighan. WET SHAVING WITH SOAP AND DOUBLE EDGE RAZORS Work the cream onto your face, dip briefly into sink water (only one or two mm to wet the brush), work into a foam on your face. Shave with the grain to remove the bulk of the stubble. Rinse face to remove excess cream. Apply cream again, dip again briefly as above. RBL PAGE - USENIX.ORG.UKSEE MORE ON USENIX.ORG.UKRBL CHECKER
RBL Check against known DNSBLs. This page below will list various RBL listings for your IP address. I am in no way responsible for the listing of your IP address at the remote servers below. If you want to have an address removed you will need to contact the administratorthere.
TSOCKS, THE USEFUL WAY We need to setup the SSH configuration now. $ /usr/bin/ssh -D 1085 -o TCPKeepAlive=yes -o ServerAliveInterval=60 192.168.0.1. -D signifies that we want to create a socks server on port 1085. We would like TCP Keep-Alives, at intervals of 60 seconds. 192.168.0.1 is the host we're connecting to. Leave that running in the background and we can get CONFIG_SCHED_AUTOGROUP 3.0.0 general settings, autogroup. Of course, if you just want to modify the config file yourself, by hand then you'll be looking for this option: CONFIG_SCHED_AUTOGROUP=y. The most outstanding thing that you may notice about this is just how much smoother the whole system appears to function once the scheduler has been configured this way.SUDO MAIN PAGE
Sudo (su "do") allows a system administrator to delegate authority to give certain users (or groups of users) the ability to run some (or all) commands as root or another user while providing an audit trail of the commands and their arguments. For more information, see the introduction to Sudo . Sudo is free software, distributed under an ISC BOOKS - USENIX.ORG.UK A great insight into travel. cyber. Sandworm: A New Era of Cyberwar and the Hunt for the Kremlin's Most Dangerous Hackers. 0385544405. How the era of cyber espionage has taken hold. Mindf*ck: Inside Cambridge Analytica’s Plot to Break the World. 1788164997.ABOUT THIS SITE
about this site. This page originated some time ago as a text generated page built from perl scripts. Later it became a blog because I had run out of time to create parts which I found useful in WordPress. Later, for performance reasons WordPress doesn't reallyscale on
WELCOME
6tunnel, 6tunnel, allowing v6 for v4 programs. DNS, sooner AXFR is gone the better. encryption, be sure to hide the plain text. netmon, interface throughput. netrs, interface throughput. nt proxy authentication. orange. my perforce quick start guide. plus.netservice.
UNIX BEARDS
Alan Cox has done a serious amount of kernel hacking, hence his huge unkempt beard. Something is wrong with this picture, Andrew Morton, a unix expert and kernel programmer must have passed the beard like the Olympic torch to Alan Cox. Dennis Ritchie, one man behind C, UNIX and much more, has a full beard. So too does Brian Kernighan. WET SHAVING WITH SOAP AND DOUBLE EDGE RAZORS Work the cream onto your face, dip briefly into sink water (only one or two mm to wet the brush), work into a foam on your face. Shave with the grain to remove the bulk of the stubble. Rinse face to remove excess cream. Apply cream again, dip again briefly as above. RBL PAGE - USENIX.ORG.UKSEE MORE ON USENIX.ORG.UKRBL CHECKER
RBL Check against known DNSBLs. This page below will list various RBL listings for your IP address. I am in no way responsible for the listing of your IP address at the remote servers below. If you want to have an address removed you will need to contact the administratorthere.
TSOCKS, THE USEFUL WAY We need to setup the SSH configuration now. $ /usr/bin/ssh -D 1085 -o TCPKeepAlive=yes -o ServerAliveInterval=60 192.168.0.1. -D signifies that we want to create a socks server on port 1085. We would like TCP Keep-Alives, at intervals of 60 seconds. 192.168.0.1 is the host we're connecting to. Leave that running in the background and we can get CONFIG_SCHED_AUTOGROUP 3.0.0 general settings, autogroup. Of course, if you just want to modify the config file yourself, by hand then you'll be looking for this option: CONFIG_SCHED_AUTOGROUP=y. The most outstanding thing that you may notice about this is just how much smoother the whole system appears to function once the scheduler has been configured this way.SUDO MAIN PAGE
Sudo (su "do") allows a system administrator to delegate authority to give certain users (or groups of users) the ability to run some (or all) commands as root or another user while providing an audit trail of the commands and their arguments. For more information, see the introduction to Sudo . Sudo is free software, distributed under an ISC UNIX/LINUX AND BSD JUSTIFICATION AND FEASIBILITY FOR THE My primary reason for choosing Linux above a more traditional UNIX (*BSD or OpenSolaris) is the availability of ionice. This is a scheduling tool for processes on Linux to run in priority groups, either when IO is available, realtime or normal. This is something that makes Linux more of a QoS choice. CORRECTLY IDENTIFYING RHEL VERSION There are different ways to identify which version of RHEL, CentOs, Rocky, ScientificLinux, OracleLinux. Lets go through them, but first, if you just want a reliable way of getting your EL version, look at the provider of /etc/redhat-release, then queryformat the version ofthat:
RBL CHECKER
RBL Check against known DNSBLs. This page below will list various RBL listings for your IP address. I am in no way responsible for the listing of your IP address at the remote servers below. If you want to have an address removed you will need to contact the administratorthere.
WHAT IS MY IP ADDRESS IP: 157.55.39.135: Signed integer value-1657329785: Unsigned integer value: 2637637511: Binary value: 10011101001101110010011110000111: Hexadecimal value: 9d372787LATEX AND MAKEFILES
LaTeX documents do not crash on legal trials like MS Word documents when they're merged together.. The main reason I like LaTeX is that it can be given variables at build time, rather than when the document is being written, similar to system environment variables. REWRITEMAPS AND MOD_REWRITE rewritemaps and mod_rewrite. RewriteMaps are extremely useful, especially if you have a large database of links that you're moving from and old site structure. The redirectmaps allow for indexing/hash of data through the use of external programs or DBM files. WHAT IS MY IP ADDRESS News. Ads help server costs, we rely on their revenue (and donations, too) to fund hosting. SNMP MIB - USENIX.ORG.UK SNMP MIB. This should get important available OIDS for SNMP requests. This document might seem out of place but its here because I had to do some conversion between MRTG and IfIndexes and OIDs, this helped greatly so I've copied it here and the POWERSHELL - USENIX.ORG.UK powershell on linux or windows. Now, lets try using a powershell pipe and see if that changes anything. A powershell pipe construct can be used against a loop, so that you iterate each of the input objectitems.
SUDO MAIN PAGE
Sudo (su "do") allows a system administrator to delegate authority to give certain users (or groups of users) the ability to run some (or all) commands as root or another user while providing an audit trail of the commands and their arguments. For more information, see the introduction to Sudo . Sudo is free software, distributed under an ISC We use cookies for personalised adverts on this site. PayPal donation is another mechanism for support if you prefer.HOSTED SERVICES
* why unix
* wet shaving
* unix beards
* about this site
* books
* RBL service
* forum
This site needs your supportamount
GBP
NEWS
Ads help server costs, we rely on their revenue (and donations, too)to fund hosting.
WELCOME
* Networks
* Linux/Unix
* Computers
* Digital photography* Security
* Hosting providers
* Other
NETWORKS
* 6tunnel , 6tunnel, allowing v6 for v4 programs * DNS , sooner AXFR is gone the better * encryption , be sure to hide the plain text * netmon , interface throughput * nt proxy authentication* orange
* my perforce quick start guide* plus.net service
* TCP port scanner
* ppp settings
* snmp counters
* socat, SOCKS and SSL* ssh
* three (3)
* throttling connections with iptables and trafficcontrol
* vodafone
* what is my IP
LINUX/UNIX
* ansible
* apache
* asterisk
* ata over ethernet
* bash
* CONFIG_SCHED_AUTOGROUP* debian
* docker
* evilwm
* fcgid notes
* find
* fonts , not as simple as you may think* gdm
* git
* htaccess tips and tricks* jsp notes
* LaTeX
* locating computers: how to find thatlost host
* mutt
* mediawiki for weblogs * meminfo and other useful bits of /proc * MS powershell on linux * printing in linux* qmail goodness
* rewritemap
* scom on linux
* screen
* sudo
* TAL , Template Attribute Language* tsocks
* vim
* why is unix better * why is xterm better* xargs
COMPUTERS
* advent 4211 netbook * dell latitude e5430 amusement * english dictionary lookup * sun oracle T5240 disk brackets * freenas on artigo a2000 * ZFS and the HP N54LDIGITAL PHOTOGRAPHY
* digital photography notes * GIMP shopping notesSECURITY
* GnuPG
HOSTING PROVIDERS
* BitFolk
* RamNode
OTHER
* good service
* bad service
* bikes
* connection problem generator * 1930's spouse test * mixcloud stream retrieval * easy to remember password generator* RBL checker
* royal jelly
* qr barcode generator * vitality point tracking * yahoo messes up mail for b3ta * yahoo group mail box retrieval Last modified: 1580066141.41Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0