Are you over 18 and want to see adult content?
More Annotations

A complete backup of https://electrolux.cz
Are you over 18 and want to see adult content?
A complete backup of https://welkoop.nl
Are you over 18 and want to see adult content?
A complete backup of https://brevardsheriff.com
Are you over 18 and want to see adult content?
A complete backup of https://naab.org
Are you over 18 and want to see adult content?
A complete backup of https://chisholm-poster.com
Are you over 18 and want to see adult content?
A complete backup of https://frenchconnection.com.au
Are you over 18 and want to see adult content?
A complete backup of https://lifepositive.com
Are you over 18 and want to see adult content?
A complete backup of https://pureprescriptions.com
Are you over 18 and want to see adult content?

A complete backup of https://cashflowsbank.mobi
Are you over 18 and want to see adult content?

A complete backup of https://6wresearch.com
Are you over 18 and want to see adult content?

A complete backup of https://utowndc.com
Are you over 18 and want to see adult content?
Favourite Annotations
Order Ferrari, Lamborghini & Maserati Parts Online | New & Aftermarket Parts: +44 (0)1787 477 169
Are you over 18 and want to see adult content?
Premium Speakers of Substance – Conference Speakers
Are you over 18 and want to see adult content?
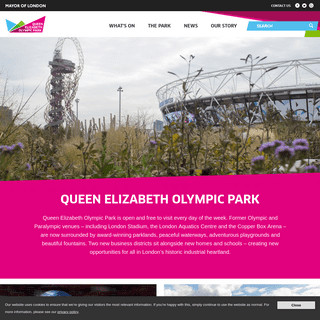
Home | Queen Elizabeth Olympic Park
Are you over 18 and want to see adult content?
Houses, Land & Property - PROPERTIBAZAR.COM
Are you over 18 and want to see adult content?
Green by Mercy – Exploring the world of plant-based beauty.
Are you over 18 and want to see adult content?
CV-Tricks.com – Learn Machine Learning, AI & Computer vision
Are you over 18 and want to see adult content?
Attractions of America - Top Attractions & Sights in USA
Are you over 18 and want to see adult content?
Tiempo de Invertir - !Llegó la hora de invertir en ti!
Are you over 18 and want to see adult content?
webstacker.net | 521: Web server is down
Are you over 18 and want to see adult content?
Text
Search for:
LINUX AUDIT
The Linux security blog about Auditing, Hardening, and Compliance* RSS
Menu
* Home
* Linux Security
* Lynis
* About
THE 101 OF ELF FILES ON LINUX: UNDERSTANDING AND ANALYSIS OPENSSH SECURITY AND HARDENING HOW TO SECURE A LINUX SYSTEM HOW TO BECOME A LINUX SECURITY EXPERT?2019-05-15
Michael Boelen Development23 comments
THE 101 OF ELF FILES ON LINUX: UNDERSTANDING AND ANALYSIS Some of the true craftsmanship in the world we take for granted. One of these things is the common tools on Linux, like ps and ls. Even though the commands might be perceived as simple, there is more to it when looking under the hood. This is where ELF or the Executable and Linkable Format comes in. A file format that used a lot, yet truly understood by only a few. Let’s get this understanding with this introduction tutorial! By readingRead more
2018-07-17
Michael Boelen Open source8 comments
HOW TO PROMOTE YOUR OPEN SOURCE PROJECT Getting more out of your project (including more users!) Do you have an open source project, yet you feel that it could more users? You are not alone! Many other open source projects have the same problem. The good news is that with only a few steps, you can new and more active users. Time to learn how promotion can be done without the pushy tricks that marketing and salespeople use. Traction is everything Traction in software projects is similarRead more
2018-07-10
(last updated at January 10th, 2019) Michael BoelenSSH
6 comments
OPENSSH SECURITY AND HARDENING SSH or Secure Shell is the popular protocol for doing system administration on Linux systems. It runs on most systems, often with its default configuration. As this service opens up a potential gateway into the system, it is one of the steps to hardening a Linux system. This article covers the SSH security tips to secure the OpenSSH service and increase the defenses of the system. OpenSSH security OpenSSH is under development by the security fanatics from the OpenBSD project. Every newRead more
2018-06-27
(last updated at June 28th, 2018) Michael BoelenKernel
, Linux
12 comments
LIVEPATCH: LINUX KERNEL UPDATES WITHOUT REBOOTING If you run a Linux server, software patching is a task that will have to be performed on a regular basis. Although most programs can be auto-restarted with a tool like needrestart, there is one exception: the kernel. Wouldn’t it be a nice if we could update the kernel without the mandatory reboot? Here is livepatch, the feature of the Linux kernel that makes it possible. Let’s discover how it works and if you can use it on your system.Read more
2018-06-23
(last updated at July 9th, 2018) Michael BoelenAuditing
, Hardening
, Linux
2 comments
HOW TO SECURE A LINUX SYSTEM Every Linux system will benefit from more security, especially if it contains sensitive data. With so many resources available on the internet, one might think that securing Linux has become easy. We know it is not. Linux system hardening takes a good amount of understanding about how the Linux kernel works. It also requires a good understanding of the operating system principles. In this guide, we will help you to get this understanding and provide you with tips andtools. The
Read more
2018-06-17
(last updated at July 10th, 2018) Michael BoelenFirewall
One comment
BPFILTER: THE NEXT-GENERATION LINUX FIREWALL The Linux community has a continuous drive to enhance the GNU/Linux kernel. When we look at network traffic filtering, we moved from ipchains to iptables. More recently we saw the introduction of nftables. Next in line is BPFILTER, part of the development work for the Linux 4.18 kernel. What is BPFILTER? BPFILTER is short for BPF based packet filtering framework. In other words, it is a framework that does packet filtering and is based on BPF. Interestingly, BPF itself is an acronymRead more
2018-06-12
(last
updated at July 22nd, 2018) Michael BoelenCareer
HOW TO BECOME A LINUX SECURITY EXPERT? Years ago it was a challenge to find screenshots of devices running Linux. Nowadays, Linux can power phones, TV’s, computer systems, mainframes, and many more devices. With more devices, the demand for Linux knowledge will continue to grow. At the same time, the demand for security is higher than ever. All the media attention and regulations like GDPR, asks for more Linux security specialists. In this post, the goal is to answer the question: How to become a Linuxsecurity expert?
Read more
2017-12-21
(last updated at May 27th, 2018) Michael BoelenLinux
One comment
THE STATE OF LINUX SECURITY IN 2017 Linux security (2017 edition) The year is closing, so it is time to review Linux security. Like last year, we look at the state of Linux security. A collection of the finest moments. Did we forget something important? Let us know in the comments. This post will remain updated in the upcoming weeks. As this post may appear on HN, Reddit, Slashdot, and other high-traffic sites, this post is heavily cached. Comments may show up with some delay. January: MongoDB, DebianRead more
2017-09-06
(last updated at June 22nd, 2018) Michael Boelen System AdministrationLeave a
comment
TROUBLESHOOTING A FULL /BOOT PARTITION ON UBUNTU A regular issue with systems running Ubuntu is that may fill up the /boot partition. You might have discovered it when running apt, which refused to work. That is unfortunate, as you also need apt to resolve the issue. After trying several options, we found a way to resolve this catch 22, with just three steps. Opposed to other solutions, you don’t need to move files or do other tricky things on your system. Still a word of caution: any tasks youRead more
2017-08-15 Michael
Boelen Linux
LINUX SECURITY MYTHS Myth busting: Linux security As the author of Lynis, I have to run several Linux systems for testing Linux security defenses. And if you do something long enough, some get to see you as a Linux security expert. When that happens, you get asked questions. Surprisingly they are often related to some of the myths. Time to share a few I got asked. If you received this link from me directly, then most likely you asked one :) Linux systemsRead more
2017-04-16
(last updated at July 6th, 2018) Michael Boelen5 comments
POSTFIX HARDENING GUIDE FOR SECURITY AND PRIVACY Postfix is a common software component on servers for receiving or sending email. It has a lot of configuration options available, including those to improve your Postfix security. This Postfix security and privacy guide will help with hardening your Postfix configuration. After you are finished, your system will have improved defenses against spam, abuse, and leaking sensitive data. Why Postfix hardening? Every service that is connected to the internet is sooner or later to be abused by automated scripts. For example,Read more
2017-03-21
Michael Boelen SystemAdministration
7 comments
UNDERSTANDING WHAT RUNS ON YOUR LINUX SYSTEM (AND WHY) Linux processes and daemons Each Linux system has a bunch of processes running. Most of these processes might be familiar to you if you regularly use a command like ps or top to display them. Processes may look like just an item in a list. They are actually complicated pieces of code that are tamed by a memory manager. To truly understand how your system is running, knowledge of process (or memory) management is of great help. So let’s makeRead more
2017-03-13
Michael Boelen FreeBSDLeave a comment
VULNERABLE PACKAGES ON FREEBSD: PKG AUDIT Auditing FreeBSD with pkg audit FreeBSD is definitely another beast than Linux. In some areas, FreeBSD is really a powerful operating system. Package management is maybe not the first one you may think of. Typically FreeBSD users have two options when it comes to installing packages. Ports collection The ports tree allows the administration to build software they need, with the compilation flags he or she prefers. This makes the software optimized and typically the last versions are available. The downsideRead more
2017-02-23
Michael Boelen
Troubleshooting
Leave a comment
TROUBLESHOOTING GUIDE FOR LYNIS Troubleshooting Lynis This document helps with solving most common issues experienced when running Lynis. Errors No hostid and/or hostid2 found Some systems do not have the OpenSSH server package installed. In this case, the hostid2 value may be missing. During the upload it may result in an error. Error: No hostid and/or hostid2 found. Can not upload report file. To see what Lynis discovered, use the show command. lynis show hostids If the hostid2 is missing, we can tellLynis
Read more
2017-02-22
(last updated at July 2nd, 2018) Michael Boelen System Administration, Time
Leave a comment
CONFIGURE THE TIME ZONE (TZ) ON LINUX SYSTEMS Having the right time set on a Linux system is important for data synchronization, forensics, and troubleshooting. Next step is to configure the correct time zone. This article will help you: See the current time configuration Learn how to configure the time zone Time zone information We will have a look on how to check and configure the time zone on Linux systems. Show current time zone Most new Linux distributions use systemd now. With the timedatectl command we canquickly see the
Read more
12 3
…15
�
ABOUT LINUX AUDIT
This blog is part of our mission: _help individuals and companies, to scan and secure their systems_. We simply love Linux security, system hardening, and questions regarding compliance. Besides the blog, we have our security auditing tool Lynis. Open source, GPL, and free to use.Lynis project page
For those with enterprise needs, or want to audit multiple systems, there is an Enterprise version. "One security solution to audit, harden, and secure your Linux/UNIXsystems."
BENEFITS:
* Perform audits within a few minutes * Central management * Powerful reporting * Compliance checks (e.g. PCI DSS) * Additional plugins and more testsLearn More
Enjoy the articles!
LINUX AND UNIX SECURITY AUTOMATION Lynis is a free and open source security scanner. It helps with testing the defenses of your Linux, macOS, and Unix systems. Typical use-cases for this software include system hardening, vulnerability scanning, and checking compliance with security standards (PCI-DSS,ISO27001, etc).
Download
RECENT POSTS
* The 101 of ELF files on Linux: Understanding and Analysis * How to promote your open source project * OpenSSH security and hardening * Livepatch: Linux kernel updates without rebooting * How to secure a Linux system * BPFILTER: the next-generation Linux firewallCONTACT
This blog is part of our mission to share valuable tips about Linux security. We are reachable via @linuxauditCOMPANY DETAILS
CISOfy
De Klok 28,
5251 DN, Vlijmen, The Netherlands+31-20-2260055
Website: https://cisofy.com* RSS
A Linux security blog about system auditing, server hardening, andcompliance.
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0