Are you over 18 and want to see adult content?
More Annotations

antsle: Private Cloud Servers, Designed for Developer.
Are you over 18 and want to see adult content?

Expansión | Actualidad, Economía, Negocios
Are you over 18 and want to see adult content?

فروشگاه اینترنتی فازنول | لامپ ال ای دی | فروش ابزار اندازه گیری
Are you over 18 and want to see adult content?

raptikigiaolous, μεταποιήσεις, πατρόν,οδηγίες, ραφές και υφάσματα
Are you over 18 and want to see adult content?

Manx Loaghtan Wool, buy online, shipped worldwide.
Are you over 18 and want to see adult content?

Winetraveler • Wine's complex, travel shouldn't be.
Are you over 18 and want to see adult content?
#1 SMM PANEL IN THE WORLD FOR 5 YEARS! | JustAnotherPanel.com
Are you over 18 and want to see adult content?
Favourite Annotations
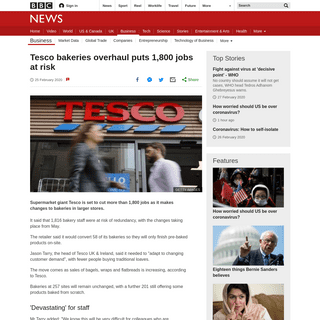
A complete backup of www.bbc.co.uk/news/business-51626529
Are you over 18 and want to see adult content?

A complete backup of www.semana.com/deportes/articulo/solo-caminar-en-cancha-era-una-victoria-los-duros-golpes-que-llevaron-a-ma
Are you over 18 and want to see adult content?
A complete backup of lelum.pl/m-jak-milosc-260220-js-teresa-lipowska/
Are you over 18 and want to see adult content?

A complete backup of www.bbc.co.uk/sport/football/51619328
Are you over 18 and want to see adult content?

A complete backup of polskatimes.pl/kim-jest-jolka-rosiek-ktora-stracila-glowe-dla-prezydenta-andrzeja-dudy-nie-nazywajcie-mnie-
Are you over 18 and want to see adult content?
Text
JHALDERM.COM
LET'S ENCRYPT: AN AUTOMATED CERTIFICATEAUTHORITY TO Let’s Encrypt: An Automated Certificate Authority to Encrypt the Entire Web CCS ’19, November 11–15, 2019, London, United Kingdom generate a private key, create a certificate signing request (CSR), THE SECURITY IMPACT OF HTTPS INTERCEPTION The Security Impact of HTTPS Interception Zakir Durumeric _, Zane Ma†, Drew Springall , Richard Barnes‡, Nick Sullivan§, Elie Bursztein¶, Michael Bailey†, J. Alex Halderman , Vern Paxsonk_ University of Michigan † University of Illinois Urbana-Champaign ‡ Mozilla § Cloudflare ¶ Google kUniversity of California Berkeley _International Computer Science Institute THE MATTER OF HEARTBLEED The Matter of Heartbleed *Zakir Durumeric1, James Kasten1, David Adrian1, J. Alex Halderman1, Michael Bailey1,2 1 University of Michigan 2 University of Illinois, Urbana Champaign {zakir, jdkasten, davadria, jhalderm}@umich.edu, mdbailey@illinois.edu *Frank Li3, Nicholas Weaver3,4, Johanna Amann4, Jethro Beekman3, Mathias Payer3,5, Vern Paxson3,4 3 EECS, University of California, Berkeley SECURITY ANALYSIS OF THE ESTONIAN INTERNET VOTING SYSTEM Security Analysis of the Estonian Internet Voting System Drew Springall† Travis Finkenauer† Zakir Durumeric† Jason Kitcat‡ Harri Hursti Margaret MacAlpine J. Alex Halderman† †University of Michigan, Ann Arbor, MI, U.S.A. ‡Open Rights Group, U.K. For additional materials and contact information, visitestoniaevoting.org.
CAN VOTERS DETECT MALICIOUS MANIPULATION OF BALLOT MARKING advanced users assessed the hazard before engaging in the activity. There may be effective ways to improve voter verification performance. Many studies have applied lessons from Cranor, AN INTERNET-WIDE VIEW OF INTERNET-WIDE SCANNING This paper appeared in Proceedings of the 23rd USENIX Security Symposium, August 2014. An Internet-Wide View of Internet-Wide Scanning Zakir Durumeric University of Michigan zakir@umich.edu SECURITY ANALYSIS OF THE DIEBOLD ACCUVOTE-TS VOTING MACHINE 2.1 Classes of Attacks 2.1.1 Vote-Stealing Attacks The AccuVote-TS machine we studied is vulnerable to attacks that steal votes from one candidate and give them J. ALEX HALDERMANPUBLICATIONSTEACHING Director, University of Michigan Center for Computer Security and Society. email: jhalderm@eecs.umich.edu office: +1 734-647-1806. Beyster Building, Room 4717. 2260 Hayward Street. Ann Arbor, MI 48109-2121. PAC-MAN ON THE SEQUOIA AVC-EDGE DRE VOTING MACHINE What is the Sequoia AVC Edge? It's a touch-screen DRE (direct-recording electronic) voting machine. Like all DREs, it stores votes in a computer memory.In 2008, the AVC Edge was used in 161 jurisdictions with almost 9 million registered voters, including large parts of Louisiana, Missouri, Nevada, and Virginia, according to Verified Voting.. Where did this machine come from? ANALYSIS OF THE MEDIAMAX CD3 COPY-PREVENTION SYSTEMSEE MORE ONJHALDERM.COM
LET'S ENCRYPT: AN AUTOMATED CERTIFICATEAUTHORITY TO Let’s Encrypt: An Automated Certificate Authority to Encrypt the Entire Web CCS ’19, November 11–15, 2019, London, United Kingdom generate a private key, create a certificate signing request (CSR), THE SECURITY IMPACT OF HTTPS INTERCEPTION The Security Impact of HTTPS Interception Zakir Durumeric _, Zane Ma†, Drew Springall , Richard Barnes‡, Nick Sullivan§, Elie Bursztein¶, Michael Bailey†, J. Alex Halderman , Vern Paxsonk_ University of Michigan † University of Illinois Urbana-Champaign ‡ Mozilla § Cloudflare ¶ Google kUniversity of California Berkeley _International Computer Science Institute THE MATTER OF HEARTBLEED The Matter of Heartbleed *Zakir Durumeric1, James Kasten1, David Adrian1, J. Alex Halderman1, Michael Bailey1,2 1 University of Michigan 2 University of Illinois, Urbana Champaign {zakir, jdkasten, davadria, jhalderm}@umich.edu, mdbailey@illinois.edu *Frank Li3, Nicholas Weaver3,4, Johanna Amann4, Jethro Beekman3, Mathias Payer3,5, Vern Paxson3,4 3 EECS, University of California, Berkeley SECURITY ANALYSIS OF THE ESTONIAN INTERNET VOTING SYSTEM Security Analysis of the Estonian Internet Voting System Drew Springall† Travis Finkenauer† Zakir Durumeric† Jason Kitcat‡ Harri Hursti Margaret MacAlpine J. Alex Halderman† †University of Michigan, Ann Arbor, MI, U.S.A. ‡Open Rights Group, U.K. For additional materials and contact information, visitestoniaevoting.org.
CAN VOTERS DETECT MALICIOUS MANIPULATION OF BALLOT MARKING advanced users assessed the hazard before engaging in the activity. There may be effective ways to improve voter verification performance. Many studies have applied lessons from Cranor, AN INTERNET-WIDE VIEW OF INTERNET-WIDE SCANNING This paper appeared in Proceedings of the 23rd USENIX Security Symposium, August 2014. An Internet-Wide View of Internet-Wide Scanning Zakir Durumeric University of Michigan zakir@umich.edu SECURITY ANALYSIS OF THE DIEBOLD ACCUVOTE-TS VOTING MACHINE 2.1 Classes of Attacks 2.1.1 Vote-Stealing Attacks The AccuVote-TS machine we studied is vulnerable to attacks that steal votes from one candidate and give themJ. ALEX HALDERMAN
Democracy Live’s OmniBallot platform is a web-based system for blank ballot delivery, ballot marking, and online voting. In early 2020, three states—Delaware, West Virginia, and New Jersey—announced that they would allow certain voters to cast votes online using OmniBallot, but, despite the well established risks of Internet voting, the system has never before undergone a public PAC-MAN ON THE SEQUOIA AVC-EDGE DRE VOTING MACHINE What is the Sequoia AVC Edge? It's a touch-screen DRE (direct-recording electronic) voting machine. Like all DREs, it stores votes in a computer memory.In 2008, the AVC Edge was used in 161 jurisdictions with almost 9 million registered voters, including large parts of Louisiana, Missouri, Nevada, and Virginia, according to Verified Voting.. Where did this machine come from? LET'S ENCRYPT: AN AUTOMATED CERTIFICATEAUTHORITY TO Let’s Encrypt: An Automated Certificate Authority to Encrypt the Entire Web CCS ’19, November 11–15, 2019, London, United Kingdom generate a private key, create a certificate signing request (CSR), CV - J. ALEX HALDERMAN J. Alex Halderman Professor, Computer Science and Engineering University of Michigan 2260 Hayward Street Ann Arbor, mi48109usa (office) +17346471806jhalderm@eecs.umich.edu A CONVENIENT METHOD FOR SECURELY MANAGING PASSWORDS any location. We rely on very little input—the user’s iden-tity (perhaps an email address), the name of the account (e.g., the server domain name), and a single master pass- UNDERSTANDING THE MIRAI BOTNET Understanding the Mirai Botnet Manos Antonakakis Tim April‡ Michael Bailey† Matthew Bernhard/ Elie Bursztein Jaime Cochran. Zakir Durumeric/ J. Alex Halderman/ Luca Invernizzi Michalis Kallitsis§ Deepak Kumar† Chaz Lever Zane Ma† Joshua Mason† Damian Menscher Chad Seaman‡ Nick Sullivan. Kurt Thomas Yi Zhou† ‡Akamai Technologies.Cloudflare Georgia Institute of Technology Google DOI:10.1145/1506409.1506429 LEST WE REMEMBER: COLD-BOOT May 2009 | Vol. 52 | no. 5 | communications of the acm 91 Lest We Remember: Cold-Boot Attacks on Encryption Keys By J. Alex Halderman, Seth D. Schoen, Nadia Heninger, William Clarkson, William Paul, LEST WE REMEMBER: COLD BOOT ATTACKS ON ENCRYPTION KEYS Memory Type Chip Maker Memory Density Make/Model Year A SDRAM Infineon 128Mb Dell Dimension 4100 1999 B DDR Samsung 512Mb ToshibaPorteg´ ´e 2001
FENG HAO AND PETER Y A RYAN (EDS.) REAL-WORLD ELECTRONIC Practical Attacks on Real-world E-voting 147 Figure 7.1: The Diebold AccuVote-TS was the most common DRE in the U.S. . 7.2 TouchscreenDREs
NEITHER SNOW NOR RAIN NOR MITMAN EMPIRICAL ANALYSIS OF Neither Snow Nor Rain Nor MITM An Empirical Analysis of Email Delivery Security Zakir Durumeric† David Adrian† Ariana Mirian† James Kasten† Elie Bursztein‡ Nicolas Lidzborski‡ Kurt Thomas‡ Vijay Eranti‡ Michael Bailey§ J. Alex Halderman† † University of Michigan ‡ Google, Inc. § University of Illinois, Urbana Champaign {zakir, davadria, amirian, jdkasten, jhalderm J. ALEX HALDERMANPUBLICATIONSTEACHING Director, University of Michigan Center for Computer Security and Society. email: jhalderm@eecs.umich.edu office: +1 734-647-1806. Beyster Building, Room 4717. 2260 Hayward Street. Ann Arbor, MI 48109-2121. ANALYSIS OF THE MEDIAMAX CD3 COPY-PREVENTION SYSTEMSEE MORE ONJHALDERM.COM
LET'S ENCRYPT: AN AUTOMATED CERTIFICATEAUTHORITY TO Let’s Encrypt: An Automated Certificate Authority to Encrypt the Entire Web CCS ’19, November 11–15, 2019, London, United Kingdom generate a private key, create a certificate signing request (CSR), CONJURE: SUMMONING PROXIES FROM UNUSED ADDRESS SPACE Conjure: Summoning Proxies from Unused Address Space CCS ’19, November 11–15, 2019, London, United Kingdom Client RefractionStation Handshake
THE SECURITY IMPACT OF HTTPS INTERCEPTION The Security Impact of HTTPS Interception Zakir Durumeric _, Zane Ma†, Drew Springall , Richard Barnes‡, Nick Sullivan§, Elie Bursztein¶, Michael Bailey†, J. Alex Halderman , Vern Paxsonk_ University of Michigan † University of Illinois Urbana-Champaign ‡ Mozilla § Cloudflare ¶ Google kUniversity of California Berkeley _International Computer Science Institute CAN VOTERS DETECT MALICIOUS MANIPULATION OF BALLOT MARKING advanced users assessed the hazard before engaging in the activity. There may be effective ways to improve voter verification performance. Many studies have applied lessons from Cranor, A CONVENIENT METHOD FOR SECURELY MANAGING PASSWORDS A Convenient Method for Securely Managing Passwords J. Alex Halderman Princeton University jhalderm@cs.princeton.edu Brent Waters StanfordUniversity
SECURITY ANALYSIS OF THE ESTONIAN INTERNET VOTING SYSTEM Security Analysis of the Estonian Internet Voting System Drew Springall† Travis Finkenauer† Zakir Durumeric† Jason Kitcat‡ Harri Hursti Margaret MacAlpine J. Alex Halderman† †University of Michigan, Ann Arbor, MI, U.S.A. ‡Open Rights Group, U.K. For additional materials and contact information, visitestoniaevoting.org.
AN INTERNET-WIDE VIEW OF INTERNET-WIDE SCANNING This paper appeared in Proceedings of the 23rd USENIX Security Symposium, August 2014. An Internet-Wide View of Internet-Wide Scanning Zakir Durumeric University of Michigan zakir@umich.edu SECURITY ANALYSIS OF THE DIEBOLD ACCUVOTE-TS VOTING MACHINE 2.1 Classes of Attacks 2.1.1 Vote-Stealing Attacks The AccuVote-TS machine we studied is vulnerable to attacks that steal votes from one candidate and give them J. ALEX HALDERMANPUBLICATIONSTEACHING Director, University of Michigan Center for Computer Security and Society. email: jhalderm@eecs.umich.edu office: +1 734-647-1806. Beyster Building, Room 4717. 2260 Hayward Street. Ann Arbor, MI 48109-2121. ANALYSIS OF THE MEDIAMAX CD3 COPY-PREVENTION SYSTEMSEE MORE ONJHALDERM.COM
LET'S ENCRYPT: AN AUTOMATED CERTIFICATEAUTHORITY TO Let’s Encrypt: An Automated Certificate Authority to Encrypt the Entire Web CCS ’19, November 11–15, 2019, London, United Kingdom generate a private key, create a certificate signing request (CSR), CONJURE: SUMMONING PROXIES FROM UNUSED ADDRESS SPACE Conjure: Summoning Proxies from Unused Address Space CCS ’19, November 11–15, 2019, London, United Kingdom Client RefractionStation Handshake
THE SECURITY IMPACT OF HTTPS INTERCEPTION The Security Impact of HTTPS Interception Zakir Durumeric _, Zane Ma†, Drew Springall , Richard Barnes‡, Nick Sullivan§, Elie Bursztein¶, Michael Bailey†, J. Alex Halderman , Vern Paxsonk_ University of Michigan † University of Illinois Urbana-Champaign ‡ Mozilla § Cloudflare ¶ Google kUniversity of California Berkeley _International Computer Science Institute CAN VOTERS DETECT MALICIOUS MANIPULATION OF BALLOT MARKING advanced users assessed the hazard before engaging in the activity. There may be effective ways to improve voter verification performance. Many studies have applied lessons from Cranor, A CONVENIENT METHOD FOR SECURELY MANAGING PASSWORDS A Convenient Method for Securely Managing Passwords J. Alex Halderman Princeton University jhalderm@cs.princeton.edu Brent Waters StanfordUniversity
SECURITY ANALYSIS OF THE ESTONIAN INTERNET VOTING SYSTEM Security Analysis of the Estonian Internet Voting System Drew Springall† Travis Finkenauer† Zakir Durumeric† Jason Kitcat‡ Harri Hursti Margaret MacAlpine J. Alex Halderman† †University of Michigan, Ann Arbor, MI, U.S.A. ‡Open Rights Group, U.K. For additional materials and contact information, visitestoniaevoting.org.
AN INTERNET-WIDE VIEW OF INTERNET-WIDE SCANNING This paper appeared in Proceedings of the 23rd USENIX Security Symposium, August 2014. An Internet-Wide View of Internet-Wide Scanning Zakir Durumeric University of Michigan zakir@umich.edu SECURITY ANALYSIS OF THE DIEBOLD ACCUVOTE-TS VOTING MACHINE 2.1 Classes of Attacks 2.1.1 Vote-Stealing Attacks The AccuVote-TS machine we studied is vulnerable to attacks that steal votes from one candidate and give them AN INTERNET-WIDE VIEW OF ICS DEVICES An Internet-Wide View of ICS Devices Ariana Mirian† Zane Ma‡ David Adrian† Matthew Tischer‡ Thasphon Chuenchujit‡ Tim Yardley‡ Robin Berthier‡ Joshua Mason‡ Zakir Durumeric†‡ J. Alex Halderman† Michael Bailey‡ † University of Michigan ‡ University of Illinois at Urbana-Champaign Abstract—Industrial control systems have become ubiquitous, A CONVENIENT METHOD FOR SECURELY MANAGING PASSWORDS any location. We rely on very little input—the user’s iden-tity (perhaps an email address), the name of the account (e.g., the server domain name), and a single master pass- TRACKING CERTIFICATE MISISSUANCE IN THE WILD Tracking Certificate Misissuance in the Wild Deepak Kumar , Zhengping Wang , Matthew Hyder , Joseph Dickinson , Gabrielle Beck†, David Adrian†, Joshua Mason , Zakir Durumeric †‡, J. Alex Halderman†, Michael Bailey University of Illinois Urbana-Champaign † University of Michigan ‡ Stanford University Abstract—Certificate Authorities (CAs) regularly make me- A SEARCH ENGINE FOR 3D MODELS Figure 1: Screenshot of our search engine for 3D models. It allows a user to specify a query using any combination of keywords and sketches (left). Then, for each query, it returns a ranked set of thumbnail NEITHER SNOW NOR RAIN NOR MITMAN EMPIRICAL ANALYSIS OF Neither Snow Nor Rain Nor MITM An Empirical Analysis of Email Delivery Security Zakir Durumeric† David Adrian† Ariana Mirian† James Kasten† Elie Bursztein‡ Nicolas Lidzborski‡ Kurt Thomas‡ Vijay Eranti‡ Michael Bailey§ J. Alex Halderman† † University of Michigan ‡ Google, Inc. § University of Illinois, Urbana Champaign {zakir, davadria, amirian, jdkasten, jhalderm SKETCHA: A CAPTCHA BASED ON LINE DRAWINGS OF 3D MODELS Sketcha: A Captcha Based on Line Drawings of 3D Models Steven A. Ross Princeton University Princeton, NJ, USA saross@cs.princeton.edu J.Alex Halderman
IN DEFENSE OF PSEUDORANDOM SAMPLE SELECTION In Defense of Pseudorandom Sample Selection Joseph A.Calandrino*, J.Alex Halderman*, and Edward W. Felten*,y *Center for Information Technology Policy and Dept.of Computer Science, Princeton University yWoodrow Wilson School of Public and International Affairs, Princeton University fjcalandr,jhalderm,felteng@cs.princeton.edu This paper first appeared in Proc. 2008 CAN DRES PROVIDE LONG-LASTING SECURITY? THE CASE OF RETURN machines. Similar to California’s top-to-bottom review, the reviewers had access to voting machines and source code. Again, critical security flaws were discovered . BEFORE THE COPYRIGHT OFFICE OF THE LIBRARY OF … 2 I. Submitting Party J. Alex Halderman is a noted computer security and privacy researcher and an assistant professor of electric engineering and computer science at the University of ILLUMINATING THE SECURITY ISSUES SURROUNDING LIGHTS-OUT This paper appeared in Proceedings of the 7th USENIX Workshop on Offensive Technologies (WOOT ’13), August 2013. Illuminating the Security Issues Surrounding Lights-Out Server Management Anthony J. Bonkoski University of Michigan J. ALEX HALDERMANPUBLICATIONSTEACHING Director, University of Michigan Center for Computer Security and Society. email: jhalderm@eecs.umich.edu office: +1 734-647-1806. Beyster Building, Room 4717. 2260 Hayward Street. Ann Arbor, MI 48109-2121. ANALYSIS OF THE MEDIAMAX CD3 COPY-PREVENTION SYSTEMSEE MORE ONJHALDERM.COM
LET'S ENCRYPT: AN AUTOMATED CERTIFICATEAUTHORITY TO Let’s Encrypt: An Automated Certificate Authority to Encrypt the Entire Web CCS ’19, November 11–15, 2019, London, United Kingdom generate a private key, create a certificate signing request (CSR), CONJURE: SUMMONING PROXIES FROM UNUSED ADDRESS SPACE Conjure: Summoning Proxies from Unused Address Space CCS ’19, November 11–15, 2019, London, United Kingdom Client RefractionStation Handshake
THE SECURITY IMPACT OF HTTPS INTERCEPTION The Security Impact of HTTPS Interception Zakir Durumeric _, Zane Ma†, Drew Springall , Richard Barnes‡, Nick Sullivan§, Elie Bursztein¶, Michael Bailey†, J. Alex Halderman , Vern Paxsonk_ University of Michigan † University of Illinois Urbana-Champaign ‡ Mozilla § Cloudflare ¶ Google kUniversity of California Berkeley _International Computer Science Institute CAN VOTERS DETECT MALICIOUS MANIPULATION OF BALLOT MARKING advanced users assessed the hazard before engaging in the activity. There may be effective ways to improve voter verification performance. Many studies have applied lessons from Cranor, A CONVENIENT METHOD FOR SECURELY MANAGING PASSWORDS A Convenient Method for Securely Managing Passwords J. Alex Halderman Princeton University jhalderm@cs.princeton.edu Brent Waters StanfordUniversity
SECURITY ANALYSIS OF THE ESTONIAN INTERNET VOTING SYSTEM Security Analysis of the Estonian Internet Voting System Drew Springall† Travis Finkenauer† Zakir Durumeric† Jason Kitcat‡ Harri Hursti Margaret MacAlpine J. Alex Halderman† †University of Michigan, Ann Arbor, MI, U.S.A. ‡Open Rights Group, U.K. For additional materials and contact information, visitestoniaevoting.org.
AN INTERNET-WIDE VIEW OF INTERNET-WIDE SCANNING This paper appeared in Proceedings of the 23rd USENIX Security Symposium, August 2014. An Internet-Wide View of Internet-Wide Scanning Zakir Durumeric University of Michigan zakir@umich.edu SECURITY ANALYSIS OF THE DIEBOLD ACCUVOTE-TS VOTING MACHINE 2.1 Classes of Attacks 2.1.1 Vote-Stealing Attacks The AccuVote-TS machine we studied is vulnerable to attacks that steal votes from one candidate and give them J. ALEX HALDERMANPUBLICATIONSTEACHING Director, University of Michigan Center for Computer Security and Society. email: jhalderm@eecs.umich.edu office: +1 734-647-1806. Beyster Building, Room 4717. 2260 Hayward Street. Ann Arbor, MI 48109-2121. ANALYSIS OF THE MEDIAMAX CD3 COPY-PREVENTION SYSTEMSEE MORE ONJHALDERM.COM
LET'S ENCRYPT: AN AUTOMATED CERTIFICATEAUTHORITY TO Let’s Encrypt: An Automated Certificate Authority to Encrypt the Entire Web CCS ’19, November 11–15, 2019, London, United Kingdom generate a private key, create a certificate signing request (CSR), CONJURE: SUMMONING PROXIES FROM UNUSED ADDRESS SPACE Conjure: Summoning Proxies from Unused Address Space CCS ’19, November 11–15, 2019, London, United Kingdom Client RefractionStation Handshake
THE SECURITY IMPACT OF HTTPS INTERCEPTION The Security Impact of HTTPS Interception Zakir Durumeric _, Zane Ma†, Drew Springall , Richard Barnes‡, Nick Sullivan§, Elie Bursztein¶, Michael Bailey†, J. Alex Halderman , Vern Paxsonk_ University of Michigan † University of Illinois Urbana-Champaign ‡ Mozilla § Cloudflare ¶ Google kUniversity of California Berkeley _International Computer Science Institute CAN VOTERS DETECT MALICIOUS MANIPULATION OF BALLOT MARKING advanced users assessed the hazard before engaging in the activity. There may be effective ways to improve voter verification performance. Many studies have applied lessons from Cranor, A CONVENIENT METHOD FOR SECURELY MANAGING PASSWORDS A Convenient Method for Securely Managing Passwords J. Alex Halderman Princeton University jhalderm@cs.princeton.edu Brent Waters StanfordUniversity
SECURITY ANALYSIS OF THE ESTONIAN INTERNET VOTING SYSTEM Security Analysis of the Estonian Internet Voting System Drew Springall† Travis Finkenauer† Zakir Durumeric† Jason Kitcat‡ Harri Hursti Margaret MacAlpine J. Alex Halderman† †University of Michigan, Ann Arbor, MI, U.S.A. ‡Open Rights Group, U.K. For additional materials and contact information, visitestoniaevoting.org.
AN INTERNET-WIDE VIEW OF INTERNET-WIDE SCANNING This paper appeared in Proceedings of the 23rd USENIX Security Symposium, August 2014. An Internet-Wide View of Internet-Wide Scanning Zakir Durumeric University of Michigan zakir@umich.edu SECURITY ANALYSIS OF THE DIEBOLD ACCUVOTE-TS VOTING MACHINE 2.1 Classes of Attacks 2.1.1 Vote-Stealing Attacks The AccuVote-TS machine we studied is vulnerable to attacks that steal votes from one candidate and give them ANALYSIS OF THE MEDIAMAX CD3 COPY-PREVENTION SYSTEM Update, June 21, 2004. Velvet Revolver's new release Contraband, which topped U.S. album sales charts this week, contains anti-copying software from SunnComm that is substantially similar to the earlier version of the technology described in this report.I have performed a preliminary inspection of the new system, and like its predecessor, it appears to provide only minimal protection against THE MATTER OF HEARTBLEED The Matter of Heartbleed *Zakir Durumeric1, James Kasten1, David Adrian1, J. Alex Halderman1, Michael Bailey1,2 1 University of Michigan 2 University of Illinois, Urbana Champaign {zakir, jdkasten, davadria, jhalderm}@umich.edu, mdbailey@illinois.edu *Frank Li3, Nicholas Weaver3,4, Johanna Amann4, Jethro Beekman3, Mathias Payer3,5, Vern Paxson3,4 3 EECS, University of California, Berkeley AN INTERNET-WIDE VIEW OF ICS DEVICES An Internet-Wide View of ICS Devices Ariana Mirian† Zane Ma‡ David Adrian† Matthew Tischer‡ Thasphon Chuenchujit‡ Tim Yardley‡ Robin Berthier‡ Joshua Mason‡ Zakir Durumeric†‡ J. Alex Halderman† Michael Bailey‡ † University of Michigan ‡ University of Illinois at Urbana-Champaign Abstract—Industrial control systems have become ubiquitous, A CONVENIENT METHOD FOR SECURELY MANAGING PASSWORDS A Convenient Method for Securely Managing Passwords J. Alex Halderman Princeton University jhalderm@cs.princeton.edu Brent Waters StanfordUniversity
TRACKING CERTIFICATE MISISSUANCE IN THE WILD Tracking Certificate Misissuance in the Wild Deepak Kumar , Zhengping Wang , Matthew Hyder , Joseph Dickinson , Gabrielle Beck†, David Adrian†, Joshua Mason , Zakir Durumeric †‡, J. Alex Halderman†, Michael Bailey University of Illinois Urbana-Champaign † University of Michigan ‡ Stanford University Abstract—Certificate Authorities (CAs) regularly make me- IN DEFENSE OF PSEUDORANDOM SAMPLE SELECTION In Defense of Pseudorandom Sample Selection Joseph A.Calandrino*, J.Alex Halderman*, and Edward W. Felten*,y *Center for Information Technology Policy and Dept.of Computer Science, Princeton University yWoodrow Wilson School of Public and International Affairs, Princeton University fjcalandr,jhalderm,felteng@cs.princeton.edu This paper first appeared in Proc. 2008 SKETCHA: A CAPTCHA BASED ON LINE DRAWINGS OF 3D MODELS Sketcha: A Captcha Based on Line Drawings of 3D Models Steven A. Ross Princeton University Princeton, NJ, USA saross@cs.princeton.edu J.Alex Halderman
DEFEATING VANISH WITH LOW-COST SYBIL ATTACKS AGAINST LARGE Vanish is an intriguing approach to an important prob-lem1; unfortunately, in its present form, it is insecure.In this paper, we show that data stored using the deployed Vanish system can be recovered long after it is supposed to have NEITHER SNOW NOR RAIN NOR MITMAN EMPIRICAL ANALYSIS OF Neither Snow Nor Rain Nor MITM An Empirical Analysis of Email Delivery Security Zakir Durumeric† David Adrian† Ariana Mirian† James Kasten† Elie Bursztein‡ Nicolas Lidzborski‡ Kurt Thomas‡ Vijay Eranti‡ Michael Bailey§ J. Alex Halderman† † University of Michigan ‡ Google, Inc. § University of Illinois, Urbana Champaign {zakir, davadria, amirian, jdkasten, jhalderm BEFORE THE COPYRIGHT OFFICE OF THE LIBRARY OF … 2 I. Submitting Party J. Alex Halderman is a noted computer security and privacy researcher and an assistant professor of electric engineering and computer science at the University ofJ. ALEX HALDERMAN
Professor of Computer Science & Engineering , University of Michigan Director, University of Michigan Center for Computer Security and Societyemail:
jhalderm@eecs.umich.eduoffice:
+1 734-647-1806
Beyster Building, Room 47172260 Hayward Street
Ann Arbor, MI 48109-2121twitter:
@jhalderm
� CURRICULUM VITAE RESEARCH AND ADVISING My research focuses on computer security and privacy , with an emphasis on problems that broadly impact society and public policy. Topics that interest me include software security, network security, data privacy, anonymity, election cybersecurity, censorship resistance, computer forensics, ethics, and cybercrime. I'm also interested in the interaction of technology with politics and international affairs. Members of my lab: Benjamin VanderSloot , Matthew Bernhard , Allison McDonald , Henry Meng . Alumni include: David Adrian , Zakir Durumeric , Drew Springall , Eric Wustrow , James Kasten , Travis Finkenauer , Scott Wolchok, Gabrielle Beck
, Ben Burgess
, Ariana Mirian
, Deepak Kumar ,
Colleen Swanson , Will Scott � PAST SEMESTERS TEACHING Fall 2020 — EECS 498.5: Election Cybersecurity Winter 2020 — EECS 388: Introduction to Computer Security Coursera — Securing Digital Democracy(massive online
course)
� ALL PUBLICATIONS SELECTED PUBLICATIONS Can Voters Detect Malicious Manipulation of Ballot Marking Devices?Matthew Bernhard,
Allison McDonald, Henry Meng, Jensen Hwa, Nakul Bajaj, Kevin Chang, and J. Alex Halderman _Proc. 41st IEEE Symposium on Security and Privacy_ Oakland ’20, San Francisco, May 2020 Let’s Encrypt: An Automated Certificate Authority to Encrypt the Entire Web Josh Aas, Richard Barnes, Benton Case, Zakir Durumeric, Peter Eckersley, Alan Flores-López, J. Alex Halderman, Jacob Hoffman-Andrews, James Kasten, Eric Rescorla, Seth Schoen, and Brad Warren _Proc. 26th ACM Conference on Computer and Communications Security_ CCS ’19, London, November 2019 Tracking Certificate Misissuance in the Wild Deepak Kumar, Zhengping Wang, Matthew Hyder, Joseph Dickinson, Gabrielle Beck, David Adrian, Joshua Mason, Zakir Durumeric, J. Alex Halderman, andMichael Bailey
_Proc. 39th IEEE Symposium on Security and Privacy_ Oakland ’18, San Francisco, May 2018 Understanding the Mirai Botnet Manos Antonakakis, Tim April, Michael Bailey, Matt Bernhard, Elie Bursztein, Jaime Cochran, Zakir Durumeric, J. Alex Halderman, Luca Invernizzi, Michalis Kallitsis, Deepak Kumar, Chaz Lever, Zane Ma, Joshua Mason, Damian Menscher, Chad Seaman, Nick Sullivan, Kurt Thomas, and Yi Zhou _Proc. 26th USENIX Security Symposium_ Sec ’17, Vancouver, August 2017 DROWN: Breaking TLS using SSLv2(site
) Nimrod Aviram, Sebastian Schinzel, Juraj Somorovsky, Nadia Heninger, Maik Dankel, Jens Steube, Luke Valenta, David Adrian, J. Alex Halderman, Viktor Dukhovni, Emilia Käsper, Shaanan Cohney, Susanne Engels, Christof Paar, andYuval Shavitt
_Proc. 25th USENIX Security Symposium_ Sec ’16, Austin, TX, August 2016 — PWNIE AWARD FOR BEST CRYPTOATTACK
Imperfect Forward Secrecy: How Diffie-Hellman Fails in Practice(site
) David Adrian, Karthikeyan Bhargavan, Zakir Durumeric, Pierrick Gaudry, Matthew Green, J. Alex Halderman, Nadia Heninger, Drew Springall, Emmanuel Thomé, Luke Valenta, Benjamin VanderSloot, Eric Wustrow, Santiago Zanella-Béguelin, and Paul Zimmermann _Proc. 22nd ACM Conference on Computer and Communications Security_ CCS ’15, October 2015; reprinted in _Commun. ACM_ , 2019 — BEST PAPER AWARD Neither Snow nor Rain nor MITM: An Empirical Analysis of Email Delivery Security Zakir Durumeric, David Adrian, Ariana Mirian, James Kasten, Elie Bursztein, Nicholas Lidzborski, Kurt Thomas, Vijay Eranti, Michael Bailey, and J. Alex Halderman _Proc. 15th ACM Internet Measurement Conference_ IMC ’15, Tokyo, October 2015 — IRTF APPLIED NETWORKING RESEARCHPRIZE
The Matter of Heartbleed (site ) Zakir Durumeric, Frank Li, James Kasten, Johanna Amann, Jethro Beekman, Mathias Payer, Nicolas Weaver, David Adrian, Vern Paxson, Michael Bailey, andJ. Alex Halderman
_Proc. 14th ACM Internet Measurement Conference_ IMC ’14, Vancouver, November 2014 — BEST PAPER AWARD Security Analysis of the Estonian Internet Voting System(site )
Drew Springall, Travis Finkenauer, Zakir Durumeric, Jason Kitcat, Harri Hursti, Margaret MacAlpine, and J. Alex Halderman _Proc. 21st ACM Conference on Computer and Communications Security_ CCS ’14, Scottsdale, AZ, November 2014 ZMap: Fast Internet-wide Scanning and its Security Applications(site )
Zakir Durumeric, Eric Wustrow, and J. Alex Halderman _Proc. 22nd USENIX Security Symposium_ Sec ’13, Washington, D.C., August 2013 Mining Your Ps and Qs: Widespread Weak Keys in Network Devices(site )
Nadia Heninger, Zakir Durumeric, Eric Wustrow, andJ. Alex Halderman
_Proc. 21st USENIX Security Symposium_ Sec ’12, Bellevue, WA, August 2012 — BEST PAPER AWARD Telex: Anticensorship in the Network Infrastructure(site )
Eric Wustrow, Scott Wolchok, Ian Goldberg, and J. Alex Halderman _Proc. 20th USENIX Security Symposium_ Sec ’11, San Francisco, August 2011 — PET AWARD RUNNER-UP Security Analysis of India’s Electronic Voting Machines(video
) Scott Wolchok,
Eric Wustrow, J. Alex Halderman, Hari K. Prasad, Arun Kankipati, Sai Krishna Sakhamuri, Vasavya Yagati, and Rop Gonggrijp _Proc. 17th ACM Conference on Computer and Communications Security_ CCS ’10, Chicago, October 2010 Lest We Remember: Cold Boot Attacks on Encryption Keys(video
) J. Alex Halderman, Seth Schoen, Nadia Heninger, William Clarkson, William Paul, Joseph A. Calandrino, Ariel Feldman, Jacob Appelbaum, and Edward W. Felten _Proc. 17th USENIX Security Symposium_ — BEST STUDENT PAPER Sec ’08, San Jose, CA, August 2008; reprinted in _Commun. ACM_, May 2009
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0