Are you over 18 and want to see adult content?
More Annotations
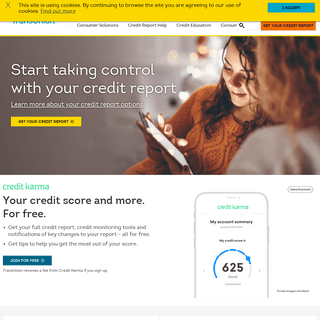
A complete backup of callcredit.co.uk
Are you over 18 and want to see adult content?

A complete backup of akademiapilki.pl
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://chessscottishterriers.weebly.com/
Are you over 18 and want to see adult content?
A complete backup of http://amrut.gov.in/content/innerpage/project.php
Are you over 18 and want to see adult content?
A complete backup of https://www.websiteperu.com/site/animetv.ge
Are you over 18 and want to see adult content?
A complete backup of https://www.escobarvip.me/sinifta-soyunan-liseliler/
Are you over 18 and want to see adult content?
A complete backup of https://chinaq.tv/cn191126/29.html
Are you over 18 and want to see adult content?
A complete backup of https://tacojournalism.blogspot.com/
Are you over 18 and want to see adult content?
A complete backup of https://www.blogger.com/profile/07854917775183890002
Are you over 18 and want to see adult content?

A complete backup of https://www.blogger.com/profile/09642783331392794777
Are you over 18 and want to see adult content?

A complete backup of http://veryaoionline.net/categoria/manga/page/33
Are you over 18 and want to see adult content?
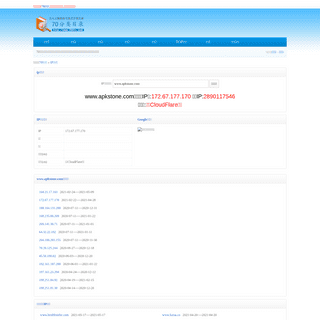
A complete backup of https://www.70dir.com/seo/ip/www.apkstone.com/
Are you over 18 and want to see adult content?
Text
LOGIN - IDENTITYIQ
MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. Privacy HOW HACKERS CAN STEAL YOUR PASSWORDS The first one is simple: the algorithm tries all the words in the dictionary. Depending on the computing power of a system, the entire dictionary can be tested within a matter of seconds. The other technique is used when a hacker acquires a hash (usually from a TERMS AND CONDITIONS HOW TO RECEIVE FINANCIAL ASSISTANCE AND RELIEF DURING THE The coronavirus pandemic has already dealt a severe blow to the American economy and has caused financial insecurity for countless citizens. The situation seems poised to PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FOR The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. IDIQ LAUNCHES DATABREACHIQ SERVICES TO HELP BUSINESSES Temecula, California, May 12, 2020 – IDIQ, the company behind the credit and identity theft monitoring IdentityIQ® brand, today launched DataBreachIQ® services to help businesses prepare and manage data security breaches. The new service comes at a time when businesses are experiencing an unprecedented number of data breaches,including at
HOW CREDIT CARD PRE-APPROVAL OFFERS WORK 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved.LOGIN - IDENTITYIQ
MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. Privacy HOW HACKERS CAN STEAL YOUR PASSWORDS The first one is simple: the algorithm tries all the words in the dictionary. Depending on the computing power of a system, the entire dictionary can be tested within a matter of seconds. The other technique is used when a hacker acquires a hash (usually from aLOGIN - IDENTITYIQ
MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. Privacy CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for HERE ARE THE TOP 3 ONLINE SCAMS AND HOW TO AVOID THEM The recent Federal Bureau of Investigations Internet Crime Report shows that cybercrime has spiked, leaving hundreds of thousands of victims and costing more than $4 billion.. The FBI received a record number of reports last year totaling 791,790, a 69% growth from 2019. Moreover, losses due to internet crime increased by $700 million, growing from $3.5 billion in 2019 to $4.2 billion in 2020. HOW TO RECEIVE FINANCIAL ASSISTANCE AND RELIEF DURING THE The coronavirus pandemic has already dealt a severe blow to the American economy and has caused financial insecurity for countless citizens. The situation seems poised to HOW TO SPOT A DEBT COLLECTION SCAM Here are some of the red flags of a debt collection scam. 1. The Debt Collector Breaks the Law. The Fair Debt Collection Practices Act (FDCPA) makes it illegal for debt collectors to engage in many types of abusive or deceptive behavior. Fraudulent debt collectors are already breaking the law, so they may not be as careful to avoid the THE PROS AND CONS OF AUTOMATIC BILL PAYMENTS Less billing oversight. Automatic bill payments can make customers complacent when it comes to their bills, causing them to spend less time reviewing charges and fees. You might miss a mistake that caused you to overpay, or overlook a company raising your rates. Risk of overdrafting: Automated billing systems don’t know if you haveenough
8 WARNING SIGNS YOU MIGHT BE A VICTIM OF IDENTITY THEFT Here are eight warning signs you might be a victim of identity theft: 1. Debt Collection Calls for Accounts You Didn’t Open. Unexpected calls from debt collectors are one of the telltale signs of identity theft. By the time debt collectors start calling, accounts have already been opened in your name and gone unpaid for many months. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your CREDIT FREEZE VS. CREDIT LOCK: DIFFERENCES ALONG WITH PROS In short, credit freezes and credit locks serve similar functions – they restrict access to your credit file so that fraudsters can’t open phony lines of credit in your name. There are pros and cons to both, and the main differences are cost, convenience, level of protection, and legal recourse. SHOULD YOU PAY YOUR CREDIT CARD STATEMENT BALANCE OR If you have the money, paying either your statement balance or your current balance is a great way to manage your credit card. It allows you to take advantage of the benefits of a credit card – such as rewards – without going into debt or paying interest charges. Paying the statement balance means you won’t be charged interest on TRUSTED CREDIT & IDENTITY THEFT PROTECTION Protect your data with identity theft protection & credit monitoring that includes 3-bureau credit reporting, dark web scans, fraud alerts,& more.
MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for HOW HACKERS CAN STEAL YOUR PASSWORDS Passwords are your first line of defense for protecting your digital identity. As important as they are, however, about 52% of people still use the same passwords across multiple accounts and 24% use a variation of common passwords that are easy to hack. TERMS AND CONDITIONS TRUSTED CREDIT & IDENTITY THEFT PROTECTION Protect your data with identity theft protection & credit monitoring that includes 3-bureau credit reporting, dark web scans, fraud alerts,& more.
MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for HOW HACKERS CAN STEAL YOUR PASSWORDS Passwords are your first line of defense for protecting your digital identity. As important as they are, however, about 52% of people still use the same passwords across multiple accounts and 24% use a variation of common passwords that are easy to hack. TERMS AND CONDITIONS CYBERCRIME IS ON THE RISE The recent Verizon Data Breach Investigations report shows that global cybercrime is on the rise. It’s a frightening prospect at first glance, but the The recent Verizon cybercrime report shows that global cybercrime is on the rise. Here are tips on how you can help protectyourself.
HERE ARE THE TOP 3 ONLINE SCAMS AND HOW TO AVOID THEM The recent Federal Bureau of Investigations Internet Crime Report shows that cybercrime has spiked, leaving hundreds of thousands of victims and costing more than $4 billion.. The FBI received a record number of reports last year totaling 791,790, a 69% growth from 2019. Moreover, losses due to internet crime increased by $700 million, growing from $3.5 billion in 2019 to $4.2 billion in 2020. CHILD IDENTITY THEFT: PREVENTION & PROTECTION GUIDE Child identity theft is becoming a serious and costly problem that can affect families long after their children become adults. In fact, more than a million children were affected by identity fraud and it cost families more than $540 million out of pocket in 2017 alone. HOW TO SPOT A DEBT COLLECTION SCAM When creditors sell your unpaid debt to a collection agency, the debt collector can reach out to you directly to try and collect what you owe. But Criminals posing as legitimate debt collectors may target you if you owe a debt, using deception or intimidation to collect debts you don’t owe, or they have no authority to collect. HOW TO RECEIVE FINANCIAL ASSISTANCE AND RELIEF DURING THE The coronavirus pandemic has already dealt a severe blow to the American economy and has caused financial insecurity for countless citizens. The situation seems poised to WHAT IS CREDENTIAL STUFFING? Hackers can use different techniques and methods to steal your passwords. One way they can use your stolen personal data is called credential stuffing. One way they can use your stolen personal data is called credential stuffing. Read on to learn more about what credential stuffing entails and how you can help protect yourself. 8 WARNING SIGNS YOU MIGHT BE A VICTIM OF IDENTITY THEFT Here are eight warning signs you might have had your personal information stolen and could be a victim of identity theft. HOW CREDIT CARD PRE-APPROVAL OFFERS WORK The business of credit card pre-approvals is simply a marketing tactic to get customers to apply and is not a guaranteed approval. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING There is a lot of coordination that goes into planning a vacation – you’ve got to arrange travel, lodging, logistics, food, and more – and that’s all while you figure out how to pay for your trip! THE PROS AND CONS OF AUTOMATIC BILL PAYMENTS These days, many banks and service providers offer automatic payments to make paying your bills a little easier. This feature lets the companies you do business with automatically charge your credit card or debit your bank account on a predetermined date every month. TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FOR The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TO Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FOR The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TO Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view CYBERCRIME IS ON THE RISE The recent Verizon Data Breach Investigations report shows that global cybercrime is on the rise. It’s a frightening prospect at first glance, but the The recent Verizon cybercrime report shows that global cybercrime is on the rise. Here are tips on how you can help protectyourself.
LOGIN - IDENTITYIQ
MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. Privacy CHILD IDENTITY THEFT: PREVENTION & PROTECTION GUIDE Child Identity Theft: Prevention & Protection Guide. Child identity theft is becoming a serious and costly problem that can affect families long after their children become adults. In fact, more than a million children were affected by identity fraud and it cost families more than $540 million out of pocket in 2017 alone. HOW HACKERS CAN STEAL YOUR PASSWORDS The first one is simple: the algorithm tries all the words in the dictionary. Depending on the computing power of a system, the entire dictionary can be tested within a matter of seconds. The other technique is used when a hacker acquires a hash (usually from a CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for HERE ARE THE TOP 3 ONLINE SCAMS AND HOW TO AVOID THEM The recent Federal Bureau of Investigations Internet Crime Report shows that cybercrime has spiked, leaving hundreds of thousands of victims and costing more than $4 billion.. The FBI received a record number of reports last year totaling 791,790, a 69% growth from 2019. Moreover, losses due to internet crime increased by $700 million, growing from $3.5 billion in 2019 to $4.2 billion in 2020. HOW TO SPOT A DEBT COLLECTION SCAM Here are some of the red flags of a debt collection scam. 1. The Debt Collector Breaks the Law. The Fair Debt Collection Practices Act (FDCPA) makes it illegal for debt collectors to engage in many types of abusive or deceptive behavior. Fraudulent debt collectors are already breaking the law, so they may not be as careful to avoid the HOW TO RECEIVE FINANCIAL ASSISTANCE AND RELIEF DURING THE The coronavirus pandemic has already dealt a severe blow to the American economy and has caused financial insecurity for countless citizens. The situation seems poised to THE PROS AND CONS OF AUTOMATIC BILL PAYMENTS Less billing oversight. Automatic bill payments can make customers complacent when it comes to their bills, causing them to spend less time reviewing charges and fees. You might miss a mistake that caused you to overpay, or overlook a company raising your rates. Risk of overdrafting: Automated billing systems don’t know if you haveenough
HOW CREDIT CARD PRE-APPROVAL OFFERS WORK Essentially, a credit card pre-approval is simply a marketing trick for credit card issuers to generate interest among potential customers that meet certain criteria. If you submit an application, the credit card company can still decline your application or offer you different terms. If you want to review pre-approval letters for great offers TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FOR The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TO Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FOR The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TO Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view CYBERCRIME IS ON THE RISE The recent Verizon Data Breach Investigations report shows that global cybercrime is on the rise. It’s a frightening prospect at first glance, but the The recent Verizon cybercrime report shows that global cybercrime is on the rise. Here are tips on how you can help protectyourself.
LOGIN - IDENTITYIQ
MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. Privacy CHILD IDENTITY THEFT: PREVENTION & PROTECTION GUIDE Child Identity Theft: Prevention & Protection Guide. Child identity theft is becoming a serious and costly problem that can affect families long after their children become adults. In fact, more than a million children were affected by identity fraud and it cost families more than $540 million out of pocket in 2017 alone. HOW HACKERS CAN STEAL YOUR PASSWORDS The first one is simple: the algorithm tries all the words in the dictionary. Depending on the computing power of a system, the entire dictionary can be tested within a matter of seconds. The other technique is used when a hacker acquires a hash (usually from a CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for HERE ARE THE TOP 3 ONLINE SCAMS AND HOW TO AVOID THEM The recent Federal Bureau of Investigations Internet Crime Report shows that cybercrime has spiked, leaving hundreds of thousands of victims and costing more than $4 billion.. The FBI received a record number of reports last year totaling 791,790, a 69% growth from 2019. Moreover, losses due to internet crime increased by $700 million, growing from $3.5 billion in 2019 to $4.2 billion in 2020. HOW TO SPOT A DEBT COLLECTION SCAM Here are some of the red flags of a debt collection scam. 1. The Debt Collector Breaks the Law. The Fair Debt Collection Practices Act (FDCPA) makes it illegal for debt collectors to engage in many types of abusive or deceptive behavior. Fraudulent debt collectors are already breaking the law, so they may not be as careful to avoid the HOW TO RECEIVE FINANCIAL ASSISTANCE AND RELIEF DURING THE The coronavirus pandemic has already dealt a severe blow to the American economy and has caused financial insecurity for countless citizens. The situation seems poised to THE PROS AND CONS OF AUTOMATIC BILL PAYMENTS Less billing oversight. Automatic bill payments can make customers complacent when it comes to their bills, causing them to spend less time reviewing charges and fees. You might miss a mistake that caused you to overpay, or overlook a company raising your rates. Risk of overdrafting: Automated billing systems don’t know if you haveenough
HOW CREDIT CARD PRE-APPROVAL OFFERS WORK Essentially, a credit card pre-approval is simply a marketing trick for credit card issuers to generate interest among potential customers that meet certain criteria. If you submit an application, the credit card company can still decline your application or offer you different terms. If you want to review pre-approval letters for great offers TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FOR The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TO Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FOR The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TO Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view CYBERCRIME IS ON THE RISE The recent Verizon Data Breach Investigations report shows that global cybercrime is on the rise. It’s a frightening prospect at first glance, but the The recent Verizon cybercrime report shows that global cybercrime is on the rise. Here are tips on how you can help protectyourself.
LOGIN - IDENTITYIQ
MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. Privacy CHILD IDENTITY THEFT: PREVENTION & PROTECTION GUIDE Child Identity Theft: Prevention & Protection Guide. Child identity theft is becoming a serious and costly problem that can affect families long after their children become adults. In fact, more than a million children were affected by identity fraud and it cost families more than $540 million out of pocket in 2017 alone. HOW HACKERS CAN STEAL YOUR PASSWORDS The first one is simple: the algorithm tries all the words in the dictionary. Depending on the computing power of a system, the entire dictionary can be tested within a matter of seconds. The other technique is used when a hacker acquires a hash (usually from a CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for HERE ARE THE TOP 3 ONLINE SCAMS AND HOW TO AVOID THEM The recent Federal Bureau of Investigations Internet Crime Report shows that cybercrime has spiked, leaving hundreds of thousands of victims and costing more than $4 billion.. The FBI received a record number of reports last year totaling 791,790, a 69% growth from 2019. Moreover, losses due to internet crime increased by $700 million, growing from $3.5 billion in 2019 to $4.2 billion in 2020. HOW TO SPOT A DEBT COLLECTION SCAM Here are some of the red flags of a debt collection scam. 1. The Debt Collector Breaks the Law. The Fair Debt Collection Practices Act (FDCPA) makes it illegal for debt collectors to engage in many types of abusive or deceptive behavior. Fraudulent debt collectors are already breaking the law, so they may not be as careful to avoid the HOW TO RECEIVE FINANCIAL ASSISTANCE AND RELIEF DURING THE The coronavirus pandemic has already dealt a severe blow to the American economy and has caused financial insecurity for countless citizens. The situation seems poised to THE PROS AND CONS OF AUTOMATIC BILL PAYMENTS Less billing oversight. Automatic bill payments can make customers complacent when it comes to their bills, causing them to spend less time reviewing charges and fees. You might miss a mistake that caused you to overpay, or overlook a company raising your rates. Risk of overdrafting: Automated billing systems don’t know if you haveenough
HOW CREDIT CARD PRE-APPROVAL OFFERS WORK Essentially, a credit card pre-approval is simply a marketing trick for credit card issuers to generate interest among potential customers that meet certain criteria. If you submit an application, the credit card company can still decline your application or offer you different terms. If you want to review pre-approval letters for great offers TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FORPHISHING MALWARE DEFINITIONMALWARE ATTACKS 2018MOST COMMON TYPES OF MALWAREMALWARE ATTACK NEWSSPEAR PHISHING MALWAREMALWARE PHISHING SCAMS The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TOCARDS LIKE TEFERI S PROTECTIONTEFERI S PROTECTION DECKTEFERI S PROTECTION MTGTEFERI S PROTECTION REPRINTTEFERI S PROTECTION RULINGTEFERI SPROTECTION TCG
Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FORPHISHING MALWARE DEFINITIONMALWARE ATTACKS 2018MOST COMMON TYPES OF MALWAREMALWARE ATTACK NEWSSPEAR PHISHING MALWAREMALWARE PHISHING SCAMS The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TOCARDS LIKE TEFERI S PROTECTIONTEFERI S PROTECTION DECKTEFERI S PROTECTION MTGTEFERI S PROTECTION REPRINTTEFERI S PROTECTION RULINGTEFERI SPROTECTION TCG
Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view CYBERCRIME IS ON THE RISE The recent Verizon Data Breach Investigations report shows that global cybercrime is on the rise. It’s a frightening prospect at first glance, but the The recent Verizon cybercrime report shows that global cybercrime is on the rise. Here are tips on how you can help protectyourself.
LOGIN - IDENTITYIQ
MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. Privacy CHILD IDENTITY THEFT: PREVENTION & PROTECTION GUIDE Child Identity Theft: Prevention & Protection Guide. Child identity theft is becoming a serious and costly problem that can affect families long after their children become adults. In fact, more than a million children were affected by identity fraud and it cost families more than $540 million out of pocket in 2017 alone. HOW HACKERS CAN STEAL YOUR PASSWORDS The first one is simple: the algorithm tries all the words in the dictionary. Depending on the computing power of a system, the entire dictionary can be tested within a matter of seconds. The other technique is used when a hacker acquires a hash (usually from a CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for HERE ARE THE TOP 3 ONLINE SCAMS AND HOW TO AVOID THEM The recent Federal Bureau of Investigations Internet Crime Report shows that cybercrime has spiked, leaving hundreds of thousands of victims and costing more than $4 billion.. The FBI received a record number of reports last year totaling 791,790, a 69% growth from 2019. Moreover, losses due to internet crime increased by $700 million, growing from $3.5 billion in 2019 to $4.2 billion in 2020. HOW TO SPOT A DEBT COLLECTION SCAM Here are some of the red flags of a debt collection scam. 1. The Debt Collector Breaks the Law. The Fair Debt Collection Practices Act (FDCPA) makes it illegal for debt collectors to engage in many types of abusive or deceptive behavior. Fraudulent debt collectors are already breaking the law, so they may not be as careful to avoid the HOW TO RECEIVE FINANCIAL ASSISTANCE AND RELIEF DURING THE The coronavirus pandemic has already dealt a severe blow to the American economy and has caused financial insecurity for countless citizens. The situation seems poised to THE PROS AND CONS OF AUTOMATIC BILL PAYMENTS Less billing oversight. Automatic bill payments can make customers complacent when it comes to their bills, causing them to spend less time reviewing charges and fees. You might miss a mistake that caused you to overpay, or overlook a company raising your rates. Risk of overdrafting: Automated billing systems don’t know if you haveenough
HOW CREDIT CARD PRE-APPROVAL OFFERS WORK Essentially, a credit card pre-approval is simply a marketing trick for credit card issuers to generate interest among potential customers that meet certain criteria. If you submit an application, the credit card company can still decline your application or offer you different terms. If you want to review pre-approval letters for great offers TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FORPHISHING MALWARE DEFINITIONMALWARE ATTACKS 2018MOST COMMON TYPES OF MALWAREMALWARE ATTACK NEWSSPEAR PHISHING MALWAREMALWARE PHISHING SCAMS The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TOCARDS LIKE TEFERI S PROTECTIONTEFERI S PROTECTION DECKTEFERI S PROTECTION MTGTEFERI S PROTECTION REPRINTTEFERI S PROTECTION RULINGTEFERI SPROTECTION TCG
Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view TRUSTED CREDIT & IDENTITY THEFT PROTECTION IdentityIQ vs. Lifelock. Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. Secure Max Plan - $29.99. MEMBER.IDENTITYIQ.COM MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. TERMS AND CONDITIONS CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for CORSAIR CAPITAL ACQUIRES MAJORITY STAKE IN IDIQ® Investment to Accelerate Growth of Leading Identity Theft and Credit Protection Company New York – December 16, 2020 – Corsair Capital LLC (“Corsair”), one of the longest-standing private equity firms focused on business and financial services, today announced that it has acquired a majority stake in IDIQ®, a tech-enabled leader in credit report and identity theft monitoring. PHISHING AND MALWARE ATTACKS MOST COMMON TECHNIQUES FORPHISHING MALWARE DEFINITIONMALWARE ATTACKS 2018MOST COMMON TYPES OF MALWAREMALWARE ATTACK NEWSSPEAR PHISHING MALWAREMALWARE PHISHING SCAMS The most common techniques for credential theft are phishing at 67%, followed by malware at 33%, according to NTT Security, an IT service management company. In most cases, a combination of the two are used as phishing-related attacks remain the most popular method of delivering malware to end-user systems. CREDIT CARD FRAUD V. DEBIT CARD FRAUD: ARE YOU PROTECTED Credit card users are protected by the Fair Credit Billing Act (FCBA). Similar to the EFTA, this law ensures that if a consumer reports his or her credit card missing or stolen, they face no liability for any fraudulent charges thereafter. However, the FCBA also states that consumers’ liability cannot exceed $50 for any fraudulent creditcard
IDIQ CEO BRINGS IDENTITY THEFT PROTECTION EXPERTISE TOCARDS LIKE TEFERI S PROTECTIONTEFERI S PROTECTION DECKTEFERI S PROTECTION MTGTEFERI S PROTECTION REPRINTTEFERI S PROTECTION RULINGTEFERI SPROTECTION TCG
Learn more about the importance of identity theft protection from Scott Hermann – CEO of IDIQ and one of the nation’s leading experts in credit monitoring, identity theft protection and data breaches – during “The Balancing Act” morning show airing Feb. 10 and Feb. 20 on the Lifetime network. BOOKING A VACATION? HERE’S HOW TO SPOT RENTAL LISTING Protecting yourself from rental listing scams requires some diligence, but there are some signs that will help you spot if the rental you’re looking at is actually a front for a scam. Here are some ways to recognize a possible scam: Payment is requested in the form of wires or gift cards: Some scammers will ask you to wire money for your 7-ELEVEN CUSTOMER DATA EXPOSED IN APP SECURITY BREACH The 7-Eleven Fuel app suffered a data breach in Australia last week that exposed users’ personal details. The app uses customer location and pricing data to help drivers find the best gas prices at local 7-Elevens, and lock in the low prices by prepaying. A customer reported the breach to 7-Eleven when he discovered he was able to view CYBERCRIME IS ON THE RISE The recent Verizon Data Breach Investigations report shows that global cybercrime is on the rise. It’s a frightening prospect at first glance, but the The recent Verizon cybercrime report shows that global cybercrime is on the rise. Here are tips on how you can help protectyourself.
LOGIN - IDENTITYIQ
MEMBER LOGIN. Need Help? Forgot username or password Customer Activation. Contact Us Privacy Policy | Terms of Use © 2021 IdentityIQ | All Rights Reserved. Privacy CHILD IDENTITY THEFT: PREVENTION & PROTECTION GUIDE Child Identity Theft: Prevention & Protection Guide. Child identity theft is becoming a serious and costly problem that can affect families long after their children become adults. In fact, more than a million children were affected by identity fraud and it cost families more than $540 million out of pocket in 2017 alone. HOW HACKERS CAN STEAL YOUR PASSWORDS The first one is simple: the algorithm tries all the words in the dictionary. Depending on the computing power of a system, the entire dictionary can be tested within a matter of seconds. The other technique is used when a hacker acquires a hash (usually from a CHECK SCAMS ARE ON THE RISE Check scams are staging a comeback as criminals continue to seize on the confusion the COVID-19 pandemic has created in people’s lives and finances. Recently, Wells Fargo sent a message to bank customers warning them to be on the lookout for check scammers.. One age group in particular – the 18 to 24 group – is especially vulnerable because they aren’t as familiar with what to look for HERE ARE THE TOP 3 ONLINE SCAMS AND HOW TO AVOID THEM The recent Federal Bureau of Investigations Internet Crime Report shows that cybercrime has spiked, leaving hundreds of thousands of victims and costing more than $4 billion.. The FBI received a record number of reports last year totaling 791,790, a 69% growth from 2019. Moreover, losses due to internet crime increased by $700 million, growing from $3.5 billion in 2019 to $4.2 billion in 2020. HOW TO SPOT A DEBT COLLECTION SCAM Here are some of the red flags of a debt collection scam. 1. The Debt Collector Breaks the Law. The Fair Debt Collection Practices Act (FDCPA) makes it illegal for debt collectors to engage in many types of abusive or deceptive behavior. Fraudulent debt collectors are already breaking the law, so they may not be as careful to avoid the HOW TO RECEIVE FINANCIAL ASSISTANCE AND RELIEF DURING THE The coronavirus pandemic has already dealt a severe blow to the American economy and has caused financial insecurity for countless citizens. The situation seems poised to THE PROS AND CONS OF AUTOMATIC BILL PAYMENTS Less billing oversight. Automatic bill payments can make customers complacent when it comes to their bills, causing them to spend less time reviewing charges and fees. You might miss a mistake that caused you to overpay, or overlook a company raising your rates. Risk of overdrafting: Automated billing systems don’t know if you haveenough
HOW CREDIT CARD PRE-APPROVAL OFFERS WORK Essentially, a credit card pre-approval is simply a marketing trick for credit card issuers to generate interest among potential customers that meet certain criteria. If you submit an application, the credit card company can still decline your application or offer you different terms. If you want to review pre-approval letters for great offersSkip to content
* What Is ID Theft?
* How We Protect You* Plans & Pricing
* Articles
* Education
* Newsroom
* Login
* Start Membership
* What Is ID Theft?
* How We Protect You* Plans & Pricing
* Articles
* Education
* Newsroom
* Login
* Start Membership
* What Is ID Theft?
* How We Protect You* Plans & Pricing
* Articles
* Education
* Newsroom
* Login
* Start Membership
* What Is ID Theft?
* How We Protect You* Plans & Pricing
* Articles
* Education
* Newsroom
* Login
* Start Membership
* What Is ID Theft?
* How We Protect You* Plans & Pricing
* Articles
* Education
* Newsroom
* Login
* Start Membership
HomeMichael Scheumack 2020-08-18T19:56:46+00:00STOP WORRYING ABOUT
DATA THREATS & THIEVES. GET IDENTITYIQ SERVICES. -------------------------IDENTITY THEFT AND
CREDIT PROTECTION
START YOUR 24/7 COMPLETE PROTECTION TODAY! $29.99/MOGet Protected Now
16.7 MILLION CONSUMERS HAVE BEEN IMPACTED BY IDENTITY THEFT ¹ On average, identity theft victims suffer over $1K in fraud and countless hours of stress. Our team of U.S.-BASED CUSTOMER SERVICE experts and restoration specialists is ready to step in and help when you need protection most. ⁴ MORE THAN 1.5 BILLION PERSONAL RECORDS HAVE BEEN EXPOSED IN DATABREACHES ²
Data breaches have exposed most Americans to some form of identity theft. IdentityIQ services monitor your PII (personally identifiable information) and ALERT YOU OF FRAUDULENT ACTIVITY. If your data is ever compromised, we help restore your identity and provide identity theft insurance to assist with costs you incur. ⁵ IDENTITY THIEVES USE STOLEN INFORMATION WITHIN MINUTES ³ Identity theft moves at the speed of technology, giving thieves the ability to use your information within minutes. We monitor and scan billions of records to NOTIFY YOU OF CERTAIN SUSPICIOUS ACTIVITY. ⁶ WHEN IDENTITY THEFT HAPPENS, YOU MAY NOT EVEN KNOW IT. _NEW CREDIT APPLICATIONS | EVENT REGISTRATIONS | DOCTOR VISITS | COLLEGE ENROLLMENT | ONLINE SHOPPING_ Personal information is everywhere. Criminals are most effective when their victims are uninformed. Identity theft protection puts controlback in your hands.
Protect your personal data with IdentityIQ services. Our team utilizes innovative and enhanced monitoring techniques that protect your credit and your identity, so you can get back to your life. WHY DO THIEVES STEAL YOUR IDENTITY? One of the first questions a victim of identity theft asks themselves is, “Why would someone want my identity?” For an identity thief, opening credit cards in your name, making fraudulent purchases, or using your personal information when being questioned by the police are just a part of a long list of what they are able to do with your stolen identity. Identity theft can happen to anyone at any time. Your identity is made up of multiple layers of information that includes more than just your Social Security number. WHAT CAN A THIEF DO WITH YOUR IDENTIFIABLE INFORMATION? Identity theft protection prevents your personal data from being used maliciously. Stop worrying about: * Fraudulent credit card purchases * Criminal identity theft * Missing tax refunds* Mortgage fraud
* Stolen retirement savingsHow We Can Help__
HOW SAFE ARE YOU AND YOUR FAMILY FROM IDENTITY THEFT?MAIL THEFT
Each day, sensitive mail sits in your mailbox, exposed to thieves who use your stolen mail to exploit your information. We actively monitor international most-wanted lists and aggressively scan national criminal record databases to identify potential threats. Other companies only search for convictions, but we alert you to both convictions and arrests.Learn More >>
INTERNET SCAMS AND COMPUTER FRAUD As technology adapts, people become more willing to give out their payment information online. Thieves hijack your personal information once it has been submitted if the website isn’t securely encrypted. We monitor your transactions and alert you to suspicious activity.Learn More >>
LOST WALLET
This is a situation all people are afraid of encountering. When your purse or wallet is stolen, every form of identification and payment you have is now at risk. Even though this is an older method of theft, it is still effective and causes unnecessary stress for the victim. We monitor your name, Social Security number, and other personal identifiable information to help protect your identity from maliciousthieves.
Learn More >>
CREDIT CARD FRAUD
Fraudulent credit and debit card purchases feel like a personal violation. Often, sorting out these unapproved purchases takes valuable time and effort away from your day. That’s why we include enhanced credit monitoring in select products. With this service, you are alerted to things like your TransUnion® credit score changing by 10+ points, authorized users being added to your credit card accounts, a new auto lease in your name, and more.Learn More >>
DATA BREACH
A data breach occurs when secure information is accessed by a malicious user. Today, hackers find their way through even the most secure firewalls to gain access. Data breaches have left millions of people at risk for identity theft, and many are unaware. We scan the dark web and use enhanced monitoring techniques to identify unauthorized use of your personal information before it hits you whereit hurts.
Learn More >>
SOCIAL SECURITY FRAUD In 2018 alone, the Social Security Administration issued 4 separate warnings to seniors about fraudulent Social Security and Medicare communications. More and more, thieves target seniors to obtain information that could be used to steal their social security and Medicare benefits. We monitor for new applications opened using your name or Social Security number while also alerting you of activity occurring on your credit report.9Learn More >>
THEFT AND HOME INVASION If you’ve ever been a victim of theft, you know how scary it can be. Even if you haven’t, you can easily imagine what it would be like to have someone invade your personal space. After a theft incident, you may experience unsolicited calls. If you provide personal information over these calls, you may be helping fill in gaps the criminal needs to complete a profile for you. In this case, knowing what to do and recognizing what to look for is only half the battle. We help you understand techniques like this in order to keep your personalinformation secure.
Learn More >>
SYNTHETIC IDENTITY THEFT Children are especially vulnerable to synthetic identity theft. This type of fraud occurs when a criminal uses a combination of real and fictitious information to create a new identity. Often, thieves will use a real social security number in combination with a fictitious name or address to create a false identity. Once created, thieves can do things like run up credit cards and enter into new auto loans. If the compromised Social Security Number is that of a loved one, it could take years to recover completely. With our included family identity protection, your dependent children are protected with up to $25,000 in identity theft insurance coverage.Learn More >>
Learn How We Protect You__ OUR IDENTITY THEFT PROTECTION WORKS SO YOU DON’T HAVE TO. IdentityIQ identity theft protection plans are dedicated to helping you and your family find peace of mind in all stages of your financiallives.
CREDIT REPORTING AND SCORE ALERTS We monitor your credit report for suspicious activity and provide you with multiple reports per year because we know it’s one of the most effective ways to detect identity theft. * 12 reports/scores per year * Reports from all 3 bureaus * Will not hurt your scoreLearn More
ENHANCED CREDIT MONITORING Best-in-class service starts with offering more than just basic credit monitoring. We take it to the next level. * New account alerts * New cleared user alerts * Score change alertsLearn More
DARK WEB MONITORING
We patrol the dark web and search for your personal information, then we notify you of anything suspicious.* SSN, name, home +
* Global dark web search * 25+ languages monitoredLearn More
PII AND DATA BREACH MONITORING We monitor for changes in data related to your non-credit based personally identifiable information (PII) andnotify you when changesoccur.
* SSN trace
* Change of address
* Int’l criminal record searchLearn More
APPLICATION MONITORING In many cases, suspicious transactions on your credit card or bank account can be one of the first signs of identity theft. * Utilities, phone, accounts * Millions of transactions * Transaction monitoringLearn More
IDENTITY THEFT INSURANCE ⁸ If you have out of pocket costs due to ID theft, you’re covered with up to $1 million in ID theft insurance. ⁸* Lost wages
* Legal/expert expenses * Stolen funds reimbursedLearn More
IDENTITY RESTORATION If you ever become a victim of identity theft, we are here to personally help you restore your name. * Full ID theft restoration * Dedicated case manager * 100% U.S. based fraud restoration serviceLearn More
FAMILY PROTECTION
Child identity theft can affect your children long into adulthood. If your child’s information is compromised, your plan includes family identity theft insurance to help cover damages. * Full ID theft restoration * $25,000 theft insuranceLearn More
View All Services
IDENTITYIQ VS. LIFELOCK Our carefully selected suite of identity protection and credit monitoring services integrate the power of the most advanced business information resources to inform, protect, alert, and assist in the event of identity theft or credit reporting problems. SECURE MAX PLAN - $29.99*
* __ SECURE MAX PLAN – $29.99 * __ 12 Credit Reports and Scores From all 3 Bureaus per Year * __ Enhanced 3 Bureau Credit Monitoring __ * __ Family Protection included at no cost __ * __ Daily Score Alerts and Monthly Score Tracker __ * __ Credit Score Simulator * __ $1 Million Identity Theft Insurance ⁸, Application Monitoring, Internet Monitoring, SSN Monitoring, and Change of AddressGet Protection Now!
ULTIMATE PLAN - $29.99*
* __ ULTIMATE PLAN – $29.99 * __ 1 Report per Year * __ Basic Credit Monitoring * __ $5.99 / Additional Child (may include additional services) * __ Monthly Score Tracker* __ None
* __ $1 Million Identity Theft Insurance, Application Monitoring, Internet Monitoring, SSN Monitoring, and Change of Address All trademarks and tradenames used in price comparisons are acknowledged to be the copyright of their respective owners. IdentityIQ services are not affiliated with the Symantec corporation or any of its brands, including LifeLock. Price comparison and features for LifeLock are shown on this site as presented at www.lifelock.com and may change. COMPREHENSIVE PROTECTION PLANSPLANS
999monthly
* 3 Bureau Credit Reports & Scores * Daily 3 Bureau Credit Report Monitoring * Dark Web & Internet Monitoring * IQAlerts with Application Monitoring* SSN Alerts
* Up to $1 Million in Stolen Funds Reimbursement * Synthetic ID Theft Protection * Up to $1 Million in Personal Expense Compensation* Change of Address
* File Sharing Network Searches * Up to $1 Million in Coverage for Lawyers and Experts * Lost Wallet Assistance * Checking Account Report * Opt-out IQ (Junk Mail/Do Not Call List) * US-Based ID Restoration Service * Alerts on Crimes Committed in Your Name * Score Change Alerts * Credit Score Tracker * Credit Scores Simulator * Family Protection – $25K ID Theft Insurance – ID FraudRestoration
* Fraud Restoration with LPOASECURE PLUS
$999monthly
* Annual
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
Get Protected Now
SECURE PRO
$1999monthly
* Bi-Annual
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
Get Protected Now
SECURE MAX
$2999monthly
* Monthly
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
* __
Get Protected Now
COMPREHENSIVE PROTECTION PLANSSECURE MAX
$ 29 99 monthly
Get Protected Now
Monthly 3 Bureau
Credit Reports & ScoresMAX FEATURES
* 3-Bureau Credit Report Monitoring * Dark Web & Internet Monitoring * Up to $1 Million in Stolen Funds Reimbursement⁸ * Coverage for Lawyers and Experts⁸ * Coverage for Personal Expense Compensation⁸ * IQ Alerts with Application Monitoring* SSN Alerts
* Synthetic ID Theft Protection* Change of Address
* File Sharing Network Searches * Lost Wallet Assistance * Checking Account Report * Opt-out IQ (Junk Mail/Do Not Call List) * U.S.-Based ID Restoration Service * Enhanced Credit Report Monitoring * Alerts on Crimes Committed in Your Name * Score Change Alerts * Credit Score Tracker * Credit Scores Simulator * Family Protection – $25K ID Theft Insurance – ID FraudRestoration
* Fraud Restoration with LPOARead More
SECURE PRO
$ 19 99 monthly
Get Protected Now
Bi-Annual 3 Bureau
Credit Reports & ScoresPRO FEATURES
* 3-Bureau Credit Report Monitoring * Dark Web & Internet Monitoring * Up to $1 Million in Stolen Funds Reimbursement⁸ * Coverage for Lawyers and Experts⁸ * Coverage for Personal Expense Compensation⁸ * IQ Alerts with Application Monitoring* SSN Alerts
* Synthetic ID Theft Protection* Change of Address
* File Sharing Network Searches * Lost Wallet Assistance * Checking Account Report * Opt-out IQ (Junk Mail/Do Not Call List) * US-Based ID Restoration Service * Enhanced Credit Report Monitoring * Alerts on Crimes Committed in Your Name * Score Change Alerts * Credit Score Tracker * Credit Scores Simulator * Family Protection – $25K ID Theft Insurance – ID FraudRestoration
* Fraud Restoration with LPOARead More
SECURE PLUS
$ 9 99 monthly
Get Protected Now
Annual 3 Bureau
Credit Reports & ScoresPLUS FEATURES
* 1-Bureau Credit Report Monitoring * Dark Web & Internet Monitoring * Up to $1 Million in Stolen Funds Reimbursement⁸ * Coverage for Lawyers and Experts⁸ * Coverage for Personal Expense Compensation⁸ * IQ Alerts with Application Monitoring* SSN Alerts
* Synthetic ID Theft Protection* Change of Address
* File Sharing Network Searches * Lost Wallet Assistance * Checking Account Report * Opt-out IQ (Junk Mail/Do Not Call List) * US-Based ID Restoration Service * Enhanced Credit Report Monitoring * Alerts on Crimes Committed in Your Name * Score Change Alerts * Credit Score Tracker * Credit Scores Simulator * Family Protection – $25K ID Theft Insurance – ID FraudRestoration
* Fraud Restoration with LPOARead More
View All Plans & PricingWHAT IS ID THEFT?
What motivates someone to commit identity theft and how would you be affected if your personal information got into the wrong hands?Learn More__
HOW WE PROTECT YOU
We combine our services with the power of the most advanced business information resources to assist you in the event of identity theft.Learn More__
PLANS & PRICING
IdentityIQ offers a variety of identity and credit protection packages that allow you to choose the best plan for your needs and budget.Learn More__
READY TO BE PROTECTED? Start your membership today.Get Protected Now
* Login
* Articles
* Affiliates
* Careers
* Privacy Policy
* Terms & Conditions* 877-875-4347
1 https://www.javelinstrategy.com/press-release/identity-fraud-hits-all-time-high-167-million-us-victims-2017-according-new-javelin 2 https://www.idtheftcenter.org/2016databreaches.html 3 https://www.consumer.ftc.gov/blog/2017/05/how-fast-will-identity-thieves-use-stolen-info 4,5,6,7 See Plans and Pricing 8 1,000,000 ID Theft Coverage – provides up to $1,000,000 in coverage for: funds stolen by unauthorized electronic funds transfer from an account in your name, legal fees, miscellaneous expenses, and up to $1,500 per week (five weeks maximum) for wages lost while resolving a stolen identity event. Family members means the enrollee’s children under the age of twenty-four (24) who permanently live in the same residence as the enrollee at the time of the stolen identity event. Underwritten by AIG.9
https://www.forbes.com/sites/robinseatonjefferson/2018/08/22/ssa-issues-warning-of-social-security-and-medicare-fraud � 2020 IDIQ® provider of IdentityIQ® services | AllRights Reserved
Facebook Instagram
Go to Top
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0