Are you over 18 and want to see adult content?
More Annotations

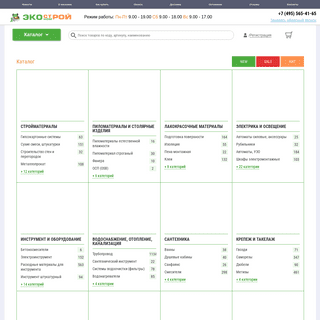
A complete backup of bursasancak.com.tr
Are you over 18 and want to see adult content?

A complete backup of pentrucomunitate.ro
Are you over 18 and want to see adult content?

A complete backup of edsmythcomedy.com
Are you over 18 and want to see adult content?

A complete backup of cutterandsquidge.com
Are you over 18 and want to see adult content?
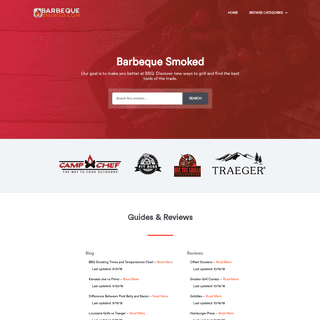
A complete backup of barbequesmoked.com
Are you over 18 and want to see adult content?
A complete backup of forococheselectricos.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of comuniquefirst.com.br
Are you over 18 and want to see adult content?
A complete backup of prostart.ucoz.ru
Are you over 18 and want to see adult content?

A complete backup of cupcakehog-blog-blog.tumblr.com
Are you over 18 and want to see adult content?

A complete backup of highridgefarm.me
Are you over 18 and want to see adult content?
Text
BACKUP RESTORE
Overview. Starting from the 4.0 release Cognito supports restoring backups from the 'vectra' CLI login. Limitations. Restore can only be performed when the backup file was taken from the running release ofFIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. P TROUBLESHOOTING INTERFACE AND ETHERNET ERRORS Cognito Detect Sensor appliances, or Cognito Detect Brain appliances in mixed mode, present several CLI commands to assist administrators investigating Ethernet issues. This article documents the 'show traffic stats' command. show traffic stats SET UP LDAP AUTHENTICATION Vectra Cognito's LDAP Authentication supports the following configurations: Active Directory (AD) or any LDAP server such as OpenLDAP STARTTLS and PLAINTEXT are supported. Notes: LDAPS ( usually QSFP SUPPORT FOR 40G INTERFACES ON S101 PLATFORM This article covers the specifics of the S101 platform as relates to the 40G interfaces on this platform. The article on recommended SFPs still applies to this platform and should be read in conjunction with this article.. The 40G interfaces on the S101 platform support 40G QSFPs or 10G SFPs (with adapter if required) that fully comply withall standards.
WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname: CHANGE NOTES FOR COGNITO TRIAGE TEMPLATES AND PRE-DEFINED Cognito version 4.11 Triage Templates (Initial release) Domain Groups (Initial Release) Cognito version 4.12 IP Groups (Initial release) Cognito version 4.14 IP Groups Triage Templates SUSPICIOUS REMOTE DESKTOP Attack Behaviors Covered/Model Purpose. Suspicious Remote Desktop (SRD) is designed to identify attackers accessing your internal machines via Microsoft’s Remote Desktop Protocol (RDP) through compromised hosts and/or compromised credentials. VMWARE VSENSOR DEPLOYMENT INSTRUCTIONS The below instructions will allow you to deploy virtual sensors using the Center UI. For instructions on how to deploy using the brain command-line interface, click here.. Enable Auto-pairing and change the password (Settings > General > Sensors)BACKUP RESTORE
Overview. Starting from the 4.0 release Cognito supports restoring backups from the 'vectra' CLI login. Limitations. Restore can only be performed when the backup file was taken from the running release ofFIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. P TROUBLESHOOTING INTERFACE AND ETHERNET ERRORS Cognito Detect Sensor appliances, or Cognito Detect Brain appliances in mixed mode, present several CLI commands to assist administrators investigating Ethernet issues. This article documents the 'show traffic stats' command. show traffic stats SET UP LDAP AUTHENTICATION Vectra Cognito's LDAP Authentication supports the following configurations: Active Directory (AD) or any LDAP server such as OpenLDAP STARTTLS and PLAINTEXT are supported. Notes: LDAPS ( usually QSFP SUPPORT FOR 40G INTERFACES ON S101 PLATFORM This article covers the specifics of the S101 platform as relates to the 40G interfaces on this platform. The article on recommended SFPs still applies to this platform and should be read in conjunction with this article.. The 40G interfaces on the S101 platform support 40G QSFPs or 10G SFPs (with adapter if required) that fully comply withall standards.
WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname: CHANGE NOTES FOR COGNITO TRIAGE TEMPLATES AND PRE-DEFINED Cognito version 4.11 Triage Templates (Initial release) Domain Groups (Initial Release) Cognito version 4.12 IP Groups (Initial release) Cognito version 4.14 IP Groups Triage Templates RESTORE BACK UP TO NEW BRAIN FROM OLD BRAIN Introduction to restoring a back up to a new brain. Backups taken by the automated backup and brain-to-brain backup features may be restored from the command line interface (CLI) on the brain after logging in to the serial console or using SSH. In both cases the default credentials may be found in this article.. In the event a brain needs to be replaced because of any reason, one step in the TROUBLESHOOTING INTERFACE AND ETHERNET ERRORS Cognito Detect Sensor appliances, or Cognito Detect Brain appliances in mixed mode, present several CLI commands to assist administrators investigating Ethernet issues. This article documents the 'show traffic stats' command. show traffic stats LEVERAGING COGNITO FOR CASE MANAGEMENT Terminology. Cognito refers to a Vectra Networks headend – a Cognito brain – along with its sensors, installed and in production on a customer premise.; Case: A case is an investigation that a team is working based on what’s been detected.Case data includes PCAPS, detection details and metadata, and other relevant information that Cognito has identified. SET UP SAML SINGLE SIGN-ON (SSO) SAML 2.0-based Single Sign-On to Vectra Detect UI. Customers can now setup SSO federation to a SAML 2.0-based identity provider For release 6.2, Vectra has validated Azure AD, others are planned to follow COGNITO AND DNS OVER HTTPS (DOH) DoH is widely recognized as a privacy enhancing measure but not a security preserving measure (recognizing these are fundamentally different). Allowing the use of DoH in an enterprise environment represents a security risk, not only in an organization’s ability to monitor, but in their ability to actually respond to incidents within an environment and will ultimately result in a loss of COGNITO SELF-DETECTION EVENTS Expected metadata sharing activity, multi-home fronted tunnel and related Cognito detections. Cognito connects to Vectra cloud infrastructure to maintain health monitoring services for customers via api.vectranetworks.com and automatic updates via update2.vectranetworks.com. Additionally, for customers who have opted-in to sharing detection metadata with Vectra (for the purpose ofimproving
TRAFFIC GRAPH SHOWING NO TRAFFIC (0 MBPS) The traffic graphs on the Cognito Brain are populated using the traffic data captured by the Sensors (or the capture interfaces on the Brain itself if operating in Mixed mode).. The traffic graphs are intended for use as basic health checks and therefore show a fixedduration.
SETTING UP BACKUPS TO WINDOWS SERVER USING OPENSSH OR Overview. Vectra Support offers the following article as a general guide to set up an SCP/SFTP server on a Windows server. The guide below is not exhaustive and will need to be adjusted for individual Windows versions and permissions. CHANGE NOTES FOR COGNITO TRIAGE TEMPLATES AND PRE-DEFINED Cognito version 4.11 Triage Templates (Initial release) Domain Groups (Initial Release) Cognito version 4.12 IP Groups (Initial release) Cognito version 4.14 IP Groups Triage Templates MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor. SUSPICIOUS REMOTE DESKTOP Attack Behaviors Covered/Model Purpose. Suspicious Remote Desktop (SRD) is designed to identify attackers accessing your internal machines via Microsoft’s Remote Desktop Protocol (RDP) through compromised hosts and/or compromised credentials. COGNITO DETECT SYSLOG GUIDE Overview The Vectra® AI X-series platform can be configured to send various event logs over Syslog messages for storage and analysis. Syslog messages include information displayed in the Xseries user interface, although in some cases the representations in the user interface may consist of derived values. INTEL ACTIVE MANAGEMENT TECHNOLOGY Vectra has received some inquiries about the recently revealed Intel AMT (Intel Active Management Technology) vulnerability that impacts many Intel systems produced over the last 10 years.This is a critical bug that allows an attacker to get sub-OS privileges on a given machine quite easily.BACKUP RESTORE
Overview. Starting from the 4.0 release Cognito supports restoring backups from the 'vectra' CLI login. Limitations. Restore can only be performed when the backup file was taken from the running release of VMWARE VSENSOR DEPLOYMENT INSTRUCTIONS The below instructions will allow you to deploy virtual sensors using the Center UI. For instructions on how to deploy using the brain command-line interface, click here.. Enable Auto-pairing and change the password (Settings > General > Sensors)FIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F SET UP LDAP AUTHENTICATION Vectra Cognito's LDAP Authentication supports the following configurations: Active Directory (AD) or any LDAP server such as OpenLDAP STARTTLS and PLAINTEXT are supported. Notes: LDAPS ( usually HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. P RECALL HOST DASHBOARD The Recall Host Dashboard is the landing page for most users as you pivot from the Host view in Detect to look at historical metadata in Recall. If a user goes to any host page in the Cognito UI, a WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname: SUSPICIOUS REMOTE DESKTOP Attack Behaviors Covered/Model Purpose. Suspicious Remote Desktop (SRD) is designed to identify attackers accessing your internal machines via Microsoft’s Remote Desktop Protocol (RDP) through compromised hosts and/or compromised credentials. COGNITO DETECT SYSLOG GUIDE Overview The Vectra® AI X-series platform can be configured to send various event logs over Syslog messages for storage and analysis. Syslog messages include information displayed in the Xseries user interface, although in some cases the representations in the user interface may consist of derived values. INTEL ACTIVE MANAGEMENT TECHNOLOGY Vectra has received some inquiries about the recently revealed Intel AMT (Intel Active Management Technology) vulnerability that impacts many Intel systems produced over the last 10 years.This is a critical bug that allows an attacker to get sub-OS privileges on a given machine quite easily.BACKUP RESTORE
Overview. Starting from the 4.0 release Cognito supports restoring backups from the 'vectra' CLI login. Limitations. Restore can only be performed when the backup file was taken from the running release of VMWARE VSENSOR DEPLOYMENT INSTRUCTIONS The below instructions will allow you to deploy virtual sensors using the Center UI. For instructions on how to deploy using the brain command-line interface, click here.. Enable Auto-pairing and change the password (Settings > General > Sensors)FIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F SET UP LDAP AUTHENTICATION Vectra Cognito's LDAP Authentication supports the following configurations: Active Directory (AD) or any LDAP server such as OpenLDAP STARTTLS and PLAINTEXT are supported. Notes: LDAPS ( usually HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. P RECALL HOST DASHBOARD The Recall Host Dashboard is the landing page for most users as you pivot from the Host view in Detect to look at historical metadata in Recall. If a user goes to any host page in the Cognito UI, a WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname: VMWARE VSENSOR DEPLOYMENT INSTRUCTIONS The below instructions will allow you to deploy virtual sensors using the Center UI. For instructions on how to deploy using the brain command-line interface, click here.. Enable Auto-pairing and change the password (Settings > General > Sensors) INTEL ACTIVE MANAGEMENT TECHNOLOGY Vectra has received some inquiries about the recently revealed Intel AMT (Intel Active Management Technology) vulnerability that impacts many Intel systems produced over the last 10 years.This is a critical bug that allows an attacker to get sub-OS privileges on a given machine quite easily. LEVERAGING COGNITO FOR CASE MANAGEMENT Terminology. Cognito refers to a Vectra Networks headend – a Cognito brain – along with its sensors, installed and in production on a customer premise.; Case: A case is an investigation that a team is working based on what’s been detected.Case data includes PCAPS, detection details and metadata, and other relevant information that Cognito has identified. SET UP SAML SINGLE SIGN-ON (SSO) SAML 2.0-based Single Sign-On to Vectra Detect UI. Customers can now setup SSO federation to a SAML 2.0-based identity provider For release 6.2, Vectra has validated Azure AD, others are planned to follow RECALL HOST DASHBOARD The Recall Host Dashboard is the landing page for most users as you pivot from the Host view in Detect to look at historical metadata in Recall. If a user goes to any host page in the Cognito UI, a SUSPICIOUS REMOTE EXECUTION Attack Behaviors Covered/Model Purpose. Suspicious Remote Execution (SRE) is designed to identify attackers utilizing remote execution tools like PSEXEC, smbexec, winexec, remote scheduler (AT), COGNITO DETECT LICENSING METRIC Overview This guide covers common questions around the Cognito Detect subscription license metric. How is the Vectra Cognito Detect product licensed? Vectra subscription licensing is based on usage UNDERSTANDING THE DETECT V2.1 HEALTH API You can now proactively monitor your Cognito Detect appliance and sensors with the new v2.1 health REST API endpoint. The ability to monitor system health via API reduces the need for manual operat TRAFFIC GRAPH SHOWING NO TRAFFIC (0 MBPS) The traffic graphs on the Cognito Brain are populated using the traffic data captured by the Sensors (or the capture interfaces on the Brain itself if operating in Mixed mode).. The traffic graphs are intended for use as basic health checks and therefore show a fixedduration.
CHANGE NOTES FOR COGNITO TRIAGE TEMPLATES AND PRE-DEFINED Cognito version 4.11 Triage Templates (Initial release) Domain Groups (Initial Release) Cognito version 4.12 IP Groups (Initial release) Cognito version 4.14 IP Groups Triage Templates SUSPICIOUS REMOTE DESKTOP Attack Behaviors Covered/Model Purpose. Suspicious Remote Desktop (SRD) is designed to identify attackers accessing your internal machines via Microsoft’s Remote Desktop Protocol (RDP) through compromised hosts and/or compromised credentials.FIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F SETTING UP BACKUPS TO WINDOWS SERVER USING OPENSSH OR Overview. Vectra Support offers the following article as a general guide to set up an SCP/SFTP server on a Windows server. The guide below is not exhaustive and will need to be adjusted for individual Windows versions and permissions. QSFP SUPPORT FOR 40G INTERFACES ON S101 PLATFORM This article covers the specifics of the S101 platform as relates to the 40G interfaces on this platform. The article on recommended SFPs still applies to this platform and should be read in conjunction with this article.. The 40G interfaces on the S101 platform support 40G QSFPs or 10G SFPs (with adapter if required) that fully comply withall standards.
MANUALLY MAPPING DETECT FOR O365 AND NETWORK ACCOUNTS There are 2 ways to link accounts, automatically using AD context, which we recommend, or manually by specifying the domains to map to specific realms. Read on AD context auto mapping here https:// CONFIGURING THE IP ADDRESS OF A NEW BRAIN OR SENSOR Newly deployed Cognito appliances, whether a Brain or Sensor, need an IP address configured to permit them to be accessible over the network. This IP address is used for Sensor-to-Brain communication, for the SSH command line interface and, in the case of the Cognito Brain, the web user interface. WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname:VECTRANETWORKS.COM
301 Moved Permanently. openresty MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor. HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. P SUSPICIOUS REMOTE DESKTOP Attack Behaviors Covered/Model Purpose. Suspicious Remote Desktop (SRD) is designed to identify attackers accessing your internal machines via Microsoft’s Remote Desktop Protocol (RDP) through compromised hosts and/or compromised credentials.FIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F SETTING UP BACKUPS TO WINDOWS SERVER USING OPENSSH OR Overview. Vectra Support offers the following article as a general guide to set up an SCP/SFTP server on a Windows server. The guide below is not exhaustive and will need to be adjusted for individual Windows versions and permissions. QSFP SUPPORT FOR 40G INTERFACES ON S101 PLATFORM This article covers the specifics of the S101 platform as relates to the 40G interfaces on this platform. The article on recommended SFPs still applies to this platform and should be read in conjunction with this article.. The 40G interfaces on the S101 platform support 40G QSFPs or 10G SFPs (with adapter if required) that fully comply withall standards.
MANUALLY MAPPING DETECT FOR O365 AND NETWORK ACCOUNTS There are 2 ways to link accounts, automatically using AD context, which we recommend, or manually by specifying the domains to map to specific realms. Read on AD context auto mapping here https:// CONFIGURING THE IP ADDRESS OF A NEW BRAIN OR SENSOR Newly deployed Cognito appliances, whether a Brain or Sensor, need an IP address configured to permit them to be accessible over the network. This IP address is used for Sensor-to-Brain communication, for the SSH command line interface and, in the case of the Cognito Brain, the web user interface. WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname:VECTRANETWORKS.COM
301 Moved Permanently. openresty MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor. HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. PBACKUP RESTORE
Overview. Starting from the 4.0 release Cognito supports restoring backups from the 'vectra' CLI login. Limitations. Restore can only be performed when the backup file was taken from the running release of COGNITO AND DNS OVER HTTPS (DOH) DoH is widely recognized as a privacy enhancing measure but not a security preserving measure (recognizing these are fundamentally different). Allowing the use of DoH in an enterprise environment represents a security risk, not only in an organization’s ability to monitor, but in their ability to actually respond to incidents within an environment and will ultimately result in a loss of VMWARE VSENSOR DEPLOYMENT INSTRUCTIONS The below instructions will allow you to deploy virtual sensors using the Center UI. For instructions on how to deploy using the brain command-line interface, click here.. Enable Auto-pairing and change the password (Settings > General > Sensors) M29 QUICK START GUIDE See attachment at the bottom for the full document Purpose This document is intended to help customers or partners with the initial configuration of Vectra M29 appliances. This is limited to bas SET UP SAML SINGLE SIGN-ON WITH OKTA Notes of Interest For additional background information regarding Detect's support of SAML refer to the following article from when SAML support was released (Version 6.2) https://support.vectran UNDERSTANDING COGNITO DETECT HOST NAMING Overview The goal of Cognito's Detect Host Naming is to provide human-readable names associated with known hosts. Host names result from known information about the host. Each observed name is refe DETECTIONS DESTINED FOR COLLECTOR.*.VECTRA.AI Summary If you are forwarding metadata to Cognito Recall the following detections may fire on the brain: HTTPS Hidden Tunnel with the destination: collector..recall.vectra.ai Sma CREATING TRIAGE FILTERS USING THE REST API Cognito Triage Filters can be viewed, created, and modified through the public API. In this article, we will explore an example of creating a new triage filter using the public API. Full public API CONFIGURING THE IP ADDRESS OF A NEW BRAIN OR SENSOR Newly deployed Cognito appliances, whether a Brain or Sensor, need an IP address configured to permit them to be accessible over the network. This IP address is used for Sensor-to-Brain communication, for the SSH command line interface and, in the case of the Cognito Brain, the web user interface. MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor. SUSPICIOUS REMOTE DESKTOP Attack Behaviors Covered/Model Purpose. Suspicious Remote Desktop (SRD) is designed to identify attackers accessing your internal machines via Microsoft’s Remote Desktop Protocol (RDP) through compromised hosts and/or compromised credentials.FIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F WHAT IS THE RETURN PROCESS FOR AN RMA? How does the RMA process work? Vectra will ship a replacement unit to you, and provide assistance with configuring that unit to replace the original unit. After that, or in parallel to it, you w SETTING UP BACKUPS TO WINDOWS SERVER USING OPENSSH OR Overview. Vectra Support offers the following article as a general guide to set up an SCP/SFTP server on a Windows server. The guide below is not exhaustive and will need to be adjusted for individual Windows versions and permissions. MANUALLY MAPPING DETECT FOR O365 AND NETWORK ACCOUNTS There are 2 ways to link accounts, automatically using AD context, which we recommend, or manually by specifying the domains to map to specific realms. Read on AD context auto mapping here https://VECTRANETWORKS.COM
301 Moved Permanently. openresty WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname: CONFIGURING THE IP ADDRESS OF A NEW BRAIN OR SENSOR Newly deployed Cognito appliances, whether a Brain or Sensor, need an IP address configured to permit them to be accessible over the network. This IP address is used for Sensor-to-Brain communication, for the SSH command line interface and, in the case of the Cognito Brain, the web user interface. MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor. HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. P SUSPICIOUS REMOTE DESKTOP Attack Behaviors Covered/Model Purpose. Suspicious Remote Desktop (SRD) is designed to identify attackers accessing your internal machines via Microsoft’s Remote Desktop Protocol (RDP) through compromised hosts and/or compromised credentials.FIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F WHAT IS THE RETURN PROCESS FOR AN RMA? How does the RMA process work? Vectra will ship a replacement unit to you, and provide assistance with configuring that unit to replace the original unit. After that, or in parallel to it, you w SETTING UP BACKUPS TO WINDOWS SERVER USING OPENSSH OR Overview. Vectra Support offers the following article as a general guide to set up an SCP/SFTP server on a Windows server. The guide below is not exhaustive and will need to be adjusted for individual Windows versions and permissions. MANUALLY MAPPING DETECT FOR O365 AND NETWORK ACCOUNTS There are 2 ways to link accounts, automatically using AD context, which we recommend, or manually by specifying the domains to map to specific realms. Read on AD context auto mapping here https://VECTRANETWORKS.COM
301 Moved Permanently. openresty WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname: CONFIGURING THE IP ADDRESS OF A NEW BRAIN OR SENSOR Newly deployed Cognito appliances, whether a Brain or Sensor, need an IP address configured to permit them to be accessible over the network. This IP address is used for Sensor-to-Brain communication, for the SSH command line interface and, in the case of the Cognito Brain, the web user interface. MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor. HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. PBACKUP RESTORE
Overview. Starting from the 4.0 release Cognito supports restoring backups from the 'vectra' CLI login. Limitations. Restore can only be performed when the backup file was taken from the running release of COGNITO AND DNS OVER HTTPS (DOH) DoH is widely recognized as a privacy enhancing measure but not a security preserving measure (recognizing these are fundamentally different). Allowing the use of DoH in an enterprise environment represents a security risk, not only in an organization’s ability to monitor, but in their ability to actually respond to incidents within an environment and will ultimately result in a loss of VMWARE VSENSOR DEPLOYMENT INSTRUCTIONS The below instructions will allow you to deploy virtual sensors using the Center UI. For instructions on how to deploy using the brain command-line interface, click here.. Enable Auto-pairing and change the password (Settings > General > Sensors) PAIRING A HARDWARE SENSOR WITH A NEW BRAIN This article covers pairing a hardware sensor with a new or different Cognito Brain. Please note that virtual Sensors are permanently M29 QUICK START GUIDE See attachment at the bottom for the full document Purpose This document is intended to help customers or partners with the initial configuration of Vectra M29 appliances. This is limited to bas SET UP SAML SINGLE SIGN-ON WITH OKTA Notes of Interest For additional background information regarding Detect's support of SAML refer to the following article from when SAML support was released (Version 6.2) https://support.vectran DETECTIONS DESTINED FOR COLLECTOR.*.VECTRA.AI Summary If you are forwarding metadata to Cognito Recall the following detections may fire on the brain: HTTPS Hidden Tunnel with the destination: collector..recall.vectra.ai Sma CONFIGURING THE IP ADDRESS OF A NEW BRAIN OR SENSOR Newly deployed Cognito appliances, whether a Brain or Sensor, need an IP address configured to permit them to be accessible over the network. This IP address is used for Sensor-to-Brain communication, for the SSH command line interface and, in the case of the Cognito Brain, the web user interface. CREATING TRIAGE FILTERS USING THE REST API Cognito Triage Filters can be viewed, created, and modified through the public API. In this article, we will explore an example of creating a new triage filter using the public API. Full public API MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor. SUSPICIOUS REMOTE DESKTOP Attack Behaviors Covered/Model Purpose. Suspicious Remote Desktop (SRD) is designed to identify attackers accessing your internal machines via Microsoft’s Remote Desktop Protocol (RDP) through compromised hosts and/or compromised credentials.FIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F WHAT IS THE RETURN PROCESS FOR AN RMA? How does the RMA process work? Vectra will ship a replacement unit to you, and provide assistance with configuring that unit to replace the original unit. After that, or in parallel to it, you w SETTING UP BACKUPS TO WINDOWS SERVER USING OPENSSH OR Overview. Vectra Support offers the following article as a general guide to set up an SCP/SFTP server on a Windows server. The guide below is not exhaustive and will need to be adjusted for individual Windows versions and permissions. MANUALLY MAPPING DETECT FOR O365 AND NETWORK ACCOUNTS There are 2 ways to link accounts, automatically using AD context, which we recommend, or manually by specifying the domains to map to specific realms. Read on AD context auto mapping here https://VECTRANETWORKS.COM
301 Moved Permanently. openresty WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname: CONFIGURING THE IP ADDRESS OF A NEW BRAIN OR SENSOR Newly deployed Cognito appliances, whether a Brain or Sensor, need an IP address configured to permit them to be accessible over the network. This IP address is used for Sensor-to-Brain communication, for the SSH command line interface and, in the case of the Cognito Brain, the web user interface. MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor. HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. P SUSPICIOUS REMOTE DESKTOP Attack Behaviors Covered/Model Purpose. Suspicious Remote Desktop (SRD) is designed to identify attackers accessing your internal machines via Microsoft’s Remote Desktop Protocol (RDP) through compromised hosts and/or compromised credentials.FIREEYE EDR FAQ
What is FireEye? FireEye Endpoint Security is a unified endpoint security platform for preventative protection, post-breach detection, automated investigation, and response. Integration: How does F WHAT IS THE RETURN PROCESS FOR AN RMA? How does the RMA process work? Vectra will ship a replacement unit to you, and provide assistance with configuring that unit to replace the original unit. After that, or in parallel to it, you w SETTING UP BACKUPS TO WINDOWS SERVER USING OPENSSH OR Overview. Vectra Support offers the following article as a general guide to set up an SCP/SFTP server on a Windows server. The guide below is not exhaustive and will need to be adjusted for individual Windows versions and permissions. MANUALLY MAPPING DETECT FOR O365 AND NETWORK ACCOUNTS There are 2 ways to link accounts, automatically using AD context, which we recommend, or manually by specifying the domains to map to specific realms. Read on AD context auto mapping here https://VECTRANETWORKS.COM
301 Moved Permanently. openresty WINDOWS EVENT LOG INGESTION Configuration of Detect Under Settings > External Connectors > Windows Event Log Ingestion use the following: Type: Raw TCP Data Format: xml Receiving port: 4637 (fixed) Server IP/hostname: CONFIGURING THE IP ADDRESS OF A NEW BRAIN OR SENSOR Newly deployed Cognito appliances, whether a Brain or Sensor, need an IP address configured to permit them to be accessible over the network. This IP address is used for Sensor-to-Brain communication, for the SSH command line interface and, in the case of the Cognito Brain, the web user interface. MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor. HOW TO CONFIGURE CARBON BLACK RESPONSE (ON-PREM This guide is for the configuration of Carbon Black Response only. Support for Carbon Black Defense (Cloud) was added as of version 6.6. Documentation for that configuration is not yet available. PBACKUP RESTORE
Overview. Starting from the 4.0 release Cognito supports restoring backups from the 'vectra' CLI login. Limitations. Restore can only be performed when the backup file was taken from the running release of COGNITO AND DNS OVER HTTPS (DOH) DoH is widely recognized as a privacy enhancing measure but not a security preserving measure (recognizing these are fundamentally different). Allowing the use of DoH in an enterprise environment represents a security risk, not only in an organization’s ability to monitor, but in their ability to actually respond to incidents within an environment and will ultimately result in a loss of VMWARE VSENSOR DEPLOYMENT INSTRUCTIONS The below instructions will allow you to deploy virtual sensors using the Center UI. For instructions on how to deploy using the brain command-line interface, click here.. Enable Auto-pairing and change the password (Settings > General > Sensors) M29 QUICK START GUIDE See attachment at the bottom for the full document Purpose This document is intended to help customers or partners with the initial configuration of Vectra M29 appliances. This is limited to bas SET UP SAML SINGLE SIGN-ON WITH OKTA Notes of Interest For additional background information regarding Detect's support of SAML refer to the following article from when SAML support was released (Version 6.2) https://support.vectran DETECTIONS DESTINED FOR COLLECTOR.*.VECTRA.AI Summary If you are forwarding metadata to Cognito Recall the following detections may fire on the brain: HTTPS Hidden Tunnel with the destination: collector..recall.vectra.ai Sma UNDERSTANDING COGNITO DETECT HOST NAMING Overview The goal of Cognito's Detect Host Naming is to provide human-readable names associated with known hosts. Host names result from known information about the host. Each observed name is refe CREATING TRIAGE FILTERS USING THE REST API Cognito Triage Filters can be viewed, created, and modified through the public API. In this article, we will explore an example of creating a new triage filter using the public API. Full public API CONFIGURING THE IP ADDRESS OF A NEW BRAIN OR SENSOR Newly deployed Cognito appliances, whether a Brain or Sensor, need an IP address configured to permit them to be accessible over the network. This IP address is used for Sensor-to-Brain communication, for the SSH command line interface and, in the case of the Cognito Brain, the web user interface. MIRRORING TRAFFIC FROM A PHYSICAL SWITCH TO A VIRTUAL It may be desirable to mirror traffic from a physical switch to a Vectra Cognito vSensor. There are two ways to mirror traffic from a physical switch into a VMware ESXi hypervisor host for monitoring by a Vectra Cognito vSensor.LIVE WEBINAR
Uncover the Top 10 Threat Detections in Microsoft Azure AD and Office365
Secure your spot >
Secure
your spot >
WE STOP RANSOMWARE.
Stop ransomware in its tracks with AI-driven threat detection andresponse.
WHAT IS NDR?LEARN MORE Support Community BlogContact us
Solutions
Solutions
Cloud Security Detect Ransomware Secure Your Remote Workforce Threat Hunting and InvestigationsRisk and Compliance
Elevate Your SOC VisibilityReplace Aging IDPS
MITRE ATT&CK Model
Industries
Critical National InfrastructureEnergy
and Utilities
Federal
Government Financial ServicesHealthcare
Higher Education
Manufacturing
Pharmaceuticals
and Medical Device
Retail
Remote PoV
Experience our
remote Proof of ValueSolarWinds Response
How should you detect and respond to the breach?Gartner Report
Get the latest Gartner Market Guide for NDRProducts & Services
Products & Services
Cognito Platform How We Do ItCognito Detect
Cognito Detect for Office 365Cognito Recall
Cognito Stream
Services API Tools
Competitive
Vectra vs. Darktrace Vectra vs.ExtraHop
Remote PoV
Experience our
remote Proof of ValueSolarWinds Response
How should you detect and respond to the breach?Gartner Report
Get the latest Gartner Market Guide for NDRPartners
Partners
Partner Program Managed Service PartnersService Partners
Technology Partners
Partner Portal
CrowdStrike MicrosoftSplunk
Remote PoV
Experience our
remote Proof of ValueSolarWinds Response
How should you detect and respond to the breach?Gartner Report
Get the latest Gartner Market Guide for NDRAbout
About Us
Company Leadership Board ofDirectors Investors
Careers
News Releases
Blogs Events & Webinars Media Coverage RecognitionContact Us
Remote PoV
Experience our
remote Proof of ValueSolarWinds Response
How should you detect and respond to the breach?Gartner Report
Get the latest Gartner Market Guide for NDRResources
Resources
Browse All Resources Blogs Case studiesCompetitive
Compliance
Datasheets
E-books
Industry Research
Product
Integration
Solution
Overviews
Videos
White Papers
Remote PoV
Experience our
remote Proof of ValueSolarWinds Response
How should you detect and respond to the breach?Gartner Report
Get the latest Gartner Market Guide for NDRSchedule Demo
-> COVID-19 Update from CEO Hitesh Sheth SolutionsCloud Security Detect Ransomware Secure Your Remote Workforce Threat Hunting and InvestigationsRisk and Compliance
Elevate Your SOC VisibilityReplace Aging IDPS
MITRE ATT&CK Model
Critical National InfrastructureEnergy
and Utilities
Federal
Government Financial ServicesHealthcare
Higher Education
Manufacturing
Pharmaceuticals
and Medical Device
Retail
Products and ServicesCognito Platform How We Do It Cognito Detect Cognito Detect for Office 365Cognito Recall
Cognito Stream
Services API Tools
Vectra vs. DarktraceVectra vs. ExtraHop
PartnersPartner Program Manage Service PartnersService Partners
Technology Partners
Partner Portal
CrowdStrike
Microsoft Splunk
AboutCompany Leadership Board ofDirectors Investors
Careers
News releases
Blogs
EventsWebcastsMedia Coverage Recognition Contact Us ResourcesBrowse all Resources Blogs CaseStudies Competitive
Compliance
Datasheets
E-Books
Industry Research
Product
Integration
Solution
Overviews
Videos
Webcasts
White Papers
Support
Blog SCHEDULE DEMO WHAT'S NEW AT VECTRANEW CLOUD DATA
See the top 10 threat detections in Azure AD and Office 365 and whatthey indicate.
GET REPORT
WHAT GARTNER SAYS
Why they say network detection and response is key to defend against supply chain attacks.LEARN MORE
NEW REPORT
New Survey reveals 71% of companies suffer an average of 7 accounttakeovers.
DOWNLOAD REPORT
WHY NOW
Attackers are inside your cloud, data center, IoTand enterprise.
You need to detect and stop the threats BEFORE they cause damage.
Time to invest in Threat Detection and Response to find and stop threats that are inside your organization. Only 2 things matter. Time to detect an adversary and time to respond. THE NETWORK IS THE SINGLE BIGGEST GAIN IN THREAT VISIBILITY. Time is the most precious resource when detecting and responding to hidden attackers active inside your organization. The sooner you have visibility, the sooner you can stop it.WHY NDR
PREVENTION DOESN'T STOP THREATS “Organizations spend disproportionate amounts of resources and money trying to block a threat that can’t be blocked.” How to Respond to the 2020 Threat Landscape Gartner Research Note Published 17 June 2020 by Analyst John Watts NETWORK DETECTION AND RESPONSE IS FOUNDATIONAL TO THE SOC VISIBILITY TRIAD NDR is the fastest and most efficient way to find threats in your cloud, data center, enterprise network, and IoT devices. It saves valuable time by automatically analyzing users, devices and their traffic, and prioritizing alerts. Learn more >Learn more >WHY VECTRA
We have developed an AI-driven cybersecurity platform that detects attacker behaviors to protect your hosts and users from being compromised, regardless of location. Unlike other solutions, Vectra Cognito provides high fidelity alerts instead of more noise, and does not decrypt your data so you can be secure and maintain privacy. Today’s cyberattacks will use any means of entry, so we provide a single platform to cover cloud, data center, enterprise networks, and IoT devices, not just critical assets. Learn more >Learn more >200%
REDUCED WORKLOAD
Ensure that a compromise in your organization never becomes aheadline.
Learn More >
REDUCE RISK
100%
DECREASED TIME TO RESPOND Make sure that your analysts are working on the right incidents at theright time.
Learn More >
EFFICIENT SECURITY
$7 Million
ELIMINATED NEED FOR POST-BREACH FORENSIC ANALYSIS Assess and seamlessly adapt to changes in security and regulatorymandates.
Learn More >
COMPLIANCE
6 Month ROI
GAINED VISIBILITY INTOUNKNOWN ATTACKS
Gain business confidence with greater visibility and security posture across your cloud footprint.Learn More >
CLOUD
SECURITY
THE VECTRA DIFFERENCE: SECURITY RESEARCH + DATA SCIENCE ENRICH DATA BY PAIRING RESEARCH AND DATA SCIENCE.SECURITY RESEARCH
Team of WORLD LEADING SECURITY RESEARCHERS distill attacker behaviors sourced from securing the world's most sensitive assets SECURITY ANALYST IN SOFTWARE Automated Tier-1 activities resulting in 34X WORKLOAD REDUCTION and maps to 97% of the MITRE ATT&CK frameworkDATA SCIENCE
Team of PHD DATA SCIENTISTS who codify behaviors across unsupervised, supervised and deep learning models
A New Threat Detection Model VECTRA THREAT DETECTION AND RESPONSE PLATFORM The Vectra platform collects, detects and prioritizes high-fidelity alerts in real time and responds with automated enforcement or alerts to security personnel. Security teams use this information for threat hunting and retrospective investigations via a subscription service. To build customized security analytics, Vectra enriches and streams the data to SIEMs and data lakes.Learn more >
Advisory
and Testing
SOC TRANSFORMATION
INCIDENT RESPONSE PLANNING BENCHMARKING AND METRICSImplementation
Services
Installed, optimized and ready to respondSidekick
Services
Vectra expert security analysts on your teamTechnical
Support
Award winning 24/7 help that solves your problemsCOGNITO STREAM
Send security-enriched metadata to data lakes and/or SIEMCOGNITO RECALL
Investigate and hunt in a cloud-based applicationCOGNITO DETECT
for Network
Detect and prioritize hidden threats in network traffic using AICOGNITO DETECT
for Microsoft Office 365 Detect and prioritize hidden threats in O365 using AICOGNITO DETECT
for Microsoft Office 365 Detect and prioritize hidden threats in O365 using AICommunity
USER GROUP MEETINGS
EXECUTIVE CUSTOMER ADVISORY EVENTSONLINE COMMUNITY
COGNITO NDR PLATFORM Cloud, users, IoT, data centerSecurity-enriched
Real time and historical Scalable architectureOUR CUSTOMERS
“Vectra automates tedious, labor intensive threat hunting and detects, scores and prioritizes the highest-risk threats.” – Jojo Maalouf, IT Security Manager at HYDRO OTTAWAGet the CaseStudy >
“Cognito filled a gap. We needed to know what we didn’t know, and Cognito showed us what was hidden.” – Brett Walmsley, CTO at NHS BOLTONGet the Case Study > “Vectra gives us access to the right people to make sure our journey is a success. Vectra is passionate about putting the customerfirst.”
– Carmello Gallo, Cybersecurity Manager at ED&F MANGet the CaseStudy >
Contact Us
General: info@vectra.ai Support: support@vectra.aiHeadquarters
550 S. Winchester Blvd., Suite 200 San Jose, CA, USA 95128 SolutionsCloud Security Detect Ransomware Secure Remote Workforce Threat Hunting and InvestigationsRisk and Compliance
Elevate Your SOC Visibility Replacing Aging IDPS MITRE ATT&CK Model Products & ServicesCognito Platform How We Do It Cognito DetectCognito Detect for
Office 365Cognito Recall Cognito StreamServices API Tools
Vectra vs. DarktraceVectra vs. ExtraHop
IndustriesCritical National InfrastructureEnergy
and Utilities
Federal Government
Financial Services
Healthcare
Higher Education
Manufacturing
Pharmaceuticals
and Medical Devices
Retail
PartnersPartner Program Managed Service PartnersService Partners
Technology Partners
Partner Portal
CrowdStrike
Microsoft Splunk
ResourcesCase studiesCompetitive
Compliance Briefs
Datasheets
E-books
Industry Research
Product
Integrations
Solution
Overviews
Videos
White Papers
Blog
AboutCompany Leadership CareersNews Releases
Media Coverage
Recognition Events &Webinars Support
LegalTerms of Service Terms of Use Privacy and Security Vectra Ethics HotlineTrademarks
� 2020 Vectra AI, Inc. All rights reserved. We use cookies to deliver a better browsing experience, analyze site traffic, personalize content, and serve targeted ads. Continuing to use this site also provides consent to our use of cookies. Acceptcookies
Close
AddThis
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0