Are you over 18 and want to see adult content?
More Annotations

A complete backup of https://ninanews.com
Are you over 18 and want to see adult content?

A complete backup of https://govhealthit.com
Are you over 18 and want to see adult content?

A complete backup of https://fusionretrobooks.com
Are you over 18 and want to see adult content?

A complete backup of https://elmanana.com
Are you over 18 and want to see adult content?
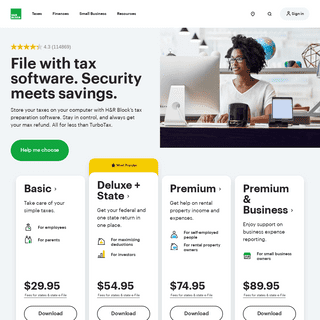
A complete backup of https://taxcut.com
Are you over 18 and want to see adult content?

A complete backup of https://sigar.mil
Are you over 18 and want to see adult content?

A complete backup of https://yellowsheet.ca
Are you over 18 and want to see adult content?

A complete backup of https://hockey.de
Are you over 18 and want to see adult content?
A complete backup of https://momsintofitness.com
Are you over 18 and want to see adult content?
A complete backup of https://caribbeannewsdigital.com
Are you over 18 and want to see adult content?
A complete backup of https://asphaltlegends.com
Are you over 18 and want to see adult content?

A complete backup of https://brightmove.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://intervozes.org.br
Are you over 18 and want to see adult content?
A complete backup of https://pro2bro.online
Are you over 18 and want to see adult content?

A complete backup of https://xclusivetouch.co.uk
Are you over 18 and want to see adult content?
A complete backup of https://ianwelsh.net
Are you over 18 and want to see adult content?
A complete backup of https://qui.click
Are you over 18 and want to see adult content?

A complete backup of https://gero-spa.com
Are you over 18 and want to see adult content?

A complete backup of https://wikipedia.at
Are you over 18 and want to see adult content?

A complete backup of https://libertybellsports.com
Are you over 18 and want to see adult content?
A complete backup of https://carma.com
Are you over 18 and want to see adult content?
A complete backup of https://willerexpress.com
Are you over 18 and want to see adult content?
A complete backup of https://money-central.net
Are you over 18 and want to see adult content?
A complete backup of https://brightvision.se
Are you over 18 and want to see adult content?
Text
TRAININGS - RECON
18 to 21 June - Windows Internals for Reverse Engineers. Learn the internals of the Windows NT kernel architecture, including Windows 10 “Threshold 2” and “Redstone 1”, as well as Server 2016, in order to learn how rootkits, PLA implants, NSA backdoors, and other kernel-mode malware exploit the various system functionalities, mechanisms and data structures to do their dirty work. REVERSING IOT: XIAOMI ECOSYSTEM Reversing IoT: Xiaomi Ecosystem Gain cloud independence and additional functionality by firmware modification (CC BY-NC-SA 4.0) REVERSE ENGINEERING OF BLOCKCHAIN SMART CONTRACTS What is Ethereum? “Ethereum is a decentralized platform that runs smart contracts: applications that run exactly as programmed without any possibility of downtime, censorship, fraud or third-party interference.”Create by Vitalik Buterin & Gavin Wood - 2013 White paper: Description of the project Yellow paper: Ethereum's formal specification (Technical) DIY ARM DEBUGGER FOR WI-FI CHIPS USING NEXMON TO PERFORM DIY ARM Debugger for Wi-Fi Chips Using Nexmon to Perform Single-Step Debugging and More on Proprietary Wi-Fi Chips Matthias Schulz Powered by: Matthias Schulz | SEEMOO | TU Darmstadt | DIY ARM Debugger for Wi-Fi Chips 1 Debugger FITBIT FIRMWARE HACKING 18 Newer trackers come with encryption enabled by default We need to know how encrypted firmware updates work Trackers use XTEA/AES in EAX mode: • 2 byte nonce in beginning of each dump • 128 bit encryption key, extractable from EEPROM via memory readout attack • 8 byte authentication MAC in the end of each dump before length field Firmware is based on LibTomCrypt (C) REVERSE ENGINEERING WINDOWS DEFENDER’S JAVASCRIPT ENGINE Tavis and Natalie at P0 dropped some awesome bugs Interest in JS engines, but I hadn’t written JS since college I had reverse engineered AVs before,THE M/O/VFUSCATOR
80515bc: mov eax,ds:0x835d81a 80515c1: mov ebx,DWORD PTR 80515c7: mov edx,DWORD PTR ds:0x835d7da 80515cd: moveax,0x0
MONITORING & CONTROLLING KERNEL-MODE EVENTS BY HYPERPLATFORM 4 Satoshi Tanda (@standa_t) – Reverse engineer interested in the Windows kernel – Implemented HyperPlatform – Threat Researcher at Sophos specializing in behaviour based detection on Windows Igor Korkin (@Igorkorkin) – An independent researcher focusing on cyber security science: memory forensics, rootkit detection & spy technologies – Co-researcher, focused on application of BREAKING CODE READ PROTECTION ON THE NXP LPC-FAMILY By: Chris Gerlinsky Scheduled on: January 28 at 16:00. A look at bypassing the Code Read Protection in the NXP LPC family of ARM microcontrollers. This is an example of one of the simple security features found in common microcontrollers, and how it is easilybypassed.
RECON.CXRECON MONTREAL 2020ARCHIVESCONTACTCFPTRAININGSSPONSORS RECON.CX. RECON Montreal 2020. RECON MTL 2020 JUNE 19-20-21 Hilton Double Tree Montreal, Canada CLICK HERE . Montreal 2018 Slides. Montreal 2018 Slides. Brussels 2018 Slides. Brussels 2018 Slides. Montreal 2017 Slides. Montreal 2017 Slides.TRAININGS - RECON
18 to 21 June - Windows Internals for Reverse Engineers. Learn the internals of the Windows NT kernel architecture, including Windows 10 “Threshold 2” and “Redstone 1”, as well as Server 2016, in order to learn how rootkits, PLA implants, NSA backdoors, and other kernel-mode malware exploit the various system functionalities, mechanisms and data structures to do their dirty work. REVERSING IOT: XIAOMI ECOSYSTEM Reversing IoT: Xiaomi Ecosystem Gain cloud independence and additional functionality by firmware modification (CC BY-NC-SA 4.0) REVERSE ENGINEERING OF BLOCKCHAIN SMART CONTRACTS What is Ethereum? “Ethereum is a decentralized platform that runs smart contracts: applications that run exactly as programmed without any possibility of downtime, censorship, fraud or third-party interference.”Create by Vitalik Buterin & Gavin Wood - 2013 White paper: Description of the project Yellow paper: Ethereum's formal specification (Technical) DIY ARM DEBUGGER FOR WI-FI CHIPS USING NEXMON TO PERFORM DIY ARM Debugger for Wi-Fi Chips Using Nexmon to Perform Single-Step Debugging and More on Proprietary Wi-Fi Chips Matthias Schulz Powered by: Matthias Schulz | SEEMOO | TU Darmstadt | DIY ARM Debugger for Wi-Fi Chips 1 Debugger FITBIT FIRMWARE HACKING 18 Newer trackers come with encryption enabled by default We need to know how encrypted firmware updates work Trackers use XTEA/AES in EAX mode: • 2 byte nonce in beginning of each dump • 128 bit encryption key, extractable from EEPROM via memory readout attack • 8 byte authentication MAC in the end of each dump before length field Firmware is based on LibTomCrypt (C) REVERSE ENGINEERING WINDOWS DEFENDER’S JAVASCRIPT ENGINE Tavis and Natalie at P0 dropped some awesome bugs Interest in JS engines, but I hadn’t written JS since college I had reverse engineered AVs before,THE M/O/VFUSCATOR
80515bc: mov eax,ds:0x835d81a 80515c1: mov ebx,DWORD PTR 80515c7: mov edx,DWORD PTR ds:0x835d7da 80515cd: moveax,0x0
MONITORING & CONTROLLING KERNEL-MODE EVENTS BY HYPERPLATFORM 4 Satoshi Tanda (@standa_t) – Reverse engineer interested in the Windows kernel – Implemented HyperPlatform – Threat Researcher at Sophos specializing in behaviour based detection on Windows Igor Korkin (@Igorkorkin) – An independent researcher focusing on cyber security science: memory forensics, rootkit detection & spy technologies – Co-researcher, focused on application of BREAKING CODE READ PROTECTION ON THE NXP LPC-FAMILY By: Chris Gerlinsky Scheduled on: January 28 at 16:00. A look at bypassing the Code Read Protection in the NXP LPC family of ARM microcontrollers. This is an example of one of the simple security features found in common microcontrollers, and how it is easilybypassed.
CONFERENCE - RECON.CX REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. ADVANCED FUZZING AND CRASH ANALYSIS Price: 4600$ CAD before May 1, 5400$ CAD after. The Advanced Fuzzing and Crash Analysis training class is designed to introduce students to the best tools and technology available for automating vulnerability discovery and crash triage with a focus on delivering a practical approach to applying this technology in real deployments. CONFERENCE - RECON.CX WHAT. REcon is a computer security conference held annually in Montreal, Canada; and this year, for the second time, we are also happy to offer a Brussels sister event.Recon offers a single track of presentations over the span of three days with a focus on reverseengineering and
RECON TRAINING
Bio. Alex Ionescu is the Chief Architect at CrowdStrike, Inc. Alex is a world-class security architect and consultant expert in low-level system software, kernel development, security training, and reverse engineering. He is coauthor of the last two editions of the Windows Internals series, along with Mark Russinovich and David Solomon. WINDOWS INTERNALS FOR REVERSE ENGINEERS 5400$ CAD. Learn the internals of the Windows NT kernel architecture, including Windows 10 “Threshold 2” and “Redstone 1”, as well as Server 2016, in order to learn how rootkits, PLA implants, NSA backdoors, and other kernel-mode malware exploit the various system functionalities, mechanisms and data structures to do their dirtywork.
RECON MONTREAL 2017
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. It is held annually in Montreal, Canada. It offers a single track of presentations over the span of three days with a focus on reverse engineering and advanced exploitation techniques. For more information, includingpricing and
RECON TRAINING
Security of BIOS/UEFI System Firmware from Attacker's and Defender's Perspective. Instructors: Yuriy Bulygin, Oleksandr Bazhaniuk, Andrew Furtak and John Loucaides Dates: 16-18 June 2015 Capacity: 20 A variety of attacks targeting system firmware have been discussed publicly, drawing attention to the pre-boot and firmware components of the platform such as BIOS and SMM, OS BREAKING CODE READ PROTECTION ON THE NXP LPC-FAMILY By: Chris Gerlinsky Scheduled on: January 28 at 16:00. A look at bypassing the Code Read Protection in the NXP LPC family of ARM microcontrollers. This is an example of one of the simple security features found in common microcontrollers, and how it is easilybypassed.
INTEL ME SECRETS
Intel ME Secrets Hidden code in your chipset and how to discover what exactly it does Igor Skochinsky Hex-Rays RECON 2014 Montreal DESIGNING A MINIMAL OPERATING SYSTEM TO EMULATE 32/64BITS Designing a minimal operating system to emulate 32/64bits x86 code snippets, shellcode or malware in Bochs Presented by: Elias Bachaalany(@0xeb), Microsoft
RECON.CXRECON MONTREAL 2020ARCHIVESCONTACTCFPTRAININGSSPONSORS RECON.CX. RECON Montreal 2020. RECON MTL 2020 JUNE 19-20-21 Hilton Double Tree Montreal, Canada CLICK HERE . Montreal 2018 Slides. Montreal 2018 Slides. Brussels 2018 Slides. Brussels 2018 Slides. Montreal 2017 Slides. Montreal 2017 Slides. CONFERENCE - RECON.CX REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.RECON TRAINING
Bio. Alex Ionescu is the Chief Architect at CrowdStrike, Inc. Alex is a world-class security architect and consultant expert in low-level system software, kernel development, security training, and reverse engineering. He is coauthor of the last two editions of the Windows Internals series, along with Mark Russinovich and David Solomon. REVERSE ENGINEERING OF BLOCKCHAIN SMART CONTRACTS What is Ethereum? “Ethereum is a decentralized platform that runs smart contracts: applications that run exactly as programmed without any possibility of downtime, censorship, fraud or third-party interference.”Create by Vitalik Buterin & Gavin Wood - 2013 White paper: Description of the project Yellow paper: Ethereum's formal specification (Technical) REVERSING IOT: XIAOMI ECOSYSTEM Reversing IoT: Xiaomi Ecosystem Gain cloud independence and additional functionality by firmware modification (CC BY-NC-SA 4.0) DIY ARM DEBUGGER FOR WI-FI CHIPS USING NEXMON TO PERFORM DIY ARM Debugger for Wi-Fi Chips Using Nexmon to Perform Single-Step Debugging and More on Proprietary Wi-Fi Chips Matthias Schulz Powered by: Matthias Schulz | SEEMOO | TU Darmstadt | DIY ARM Debugger for Wi-Fi Chips 1 Debugger REVERSE ENGINEERING WINDOWS DEFENDER’S JAVASCRIPT ENGINE Tavis and Natalie at P0 dropped some awesome bugs Interest in JS engines, but I hadn’t written JS since college I had reverse engineered AVs before, FITBIT FIRMWARE HACKING 18 Newer trackers come with encryption enabled by default We need to know how encrypted firmware updates work Trackers use XTEA/AES in EAX mode: • 2 byte nonce in beginning of each dump • 128 bit encryption key, extractable from EEPROM via memory readout attack • 8 byte authentication MAC in the end of each dump before length field Firmware is based on LibTomCrypt (C)THE M/O/VFUSCATOR
80515bc: mov eax,ds:0x835d81a 80515c1: mov ebx,DWORD PTR 80515c7: mov edx,DWORD PTR ds:0x835d7da 80515cd: moveax,0x0
MONITORING & CONTROLLING KERNEL-MODE EVENTS BY HYPERPLATFORM 4 Satoshi Tanda (@standa_t) – Reverse engineer interested in the Windows kernel – Implemented HyperPlatform – Threat Researcher at Sophos specializing in behaviour based detection on Windows Igor Korkin (@Igorkorkin) – An independent researcher focusing on cyber security science: memory forensics, rootkit detection & spy technologies – Co-researcher, focused on application of RECON.CXRECON MONTREAL 2020ARCHIVESCONTACTCFPTRAININGSSPONSORS RECON.CX. RECON Montreal 2020. RECON MTL 2020 JUNE 19-20-21 Hilton Double Tree Montreal, Canada CLICK HERE . Montreal 2018 Slides. Montreal 2018 Slides. Brussels 2018 Slides. Brussels 2018 Slides. Montreal 2017 Slides. Montreal 2017 Slides. CONFERENCE - RECON.CX REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.RECON TRAINING
Bio. Alex Ionescu is the Chief Architect at CrowdStrike, Inc. Alex is a world-class security architect and consultant expert in low-level system software, kernel development, security training, and reverse engineering. He is coauthor of the last two editions of the Windows Internals series, along with Mark Russinovich and David Solomon. REVERSE ENGINEERING OF BLOCKCHAIN SMART CONTRACTS What is Ethereum? “Ethereum is a decentralized platform that runs smart contracts: applications that run exactly as programmed without any possibility of downtime, censorship, fraud or third-party interference.”Create by Vitalik Buterin & Gavin Wood - 2013 White paper: Description of the project Yellow paper: Ethereum's formal specification (Technical) REVERSING IOT: XIAOMI ECOSYSTEM Reversing IoT: Xiaomi Ecosystem Gain cloud independence and additional functionality by firmware modification (CC BY-NC-SA 4.0) DIY ARM DEBUGGER FOR WI-FI CHIPS USING NEXMON TO PERFORM DIY ARM Debugger for Wi-Fi Chips Using Nexmon to Perform Single-Step Debugging and More on Proprietary Wi-Fi Chips Matthias Schulz Powered by: Matthias Schulz | SEEMOO | TU Darmstadt | DIY ARM Debugger for Wi-Fi Chips 1 Debugger REVERSE ENGINEERING WINDOWS DEFENDER’S JAVASCRIPT ENGINE Tavis and Natalie at P0 dropped some awesome bugs Interest in JS engines, but I hadn’t written JS since college I had reverse engineered AVs before, FITBIT FIRMWARE HACKING 18 Newer trackers come with encryption enabled by default We need to know how encrypted firmware updates work Trackers use XTEA/AES in EAX mode: • 2 byte nonce in beginning of each dump • 128 bit encryption key, extractable from EEPROM via memory readout attack • 8 byte authentication MAC in the end of each dump before length field Firmware is based on LibTomCrypt (C)THE M/O/VFUSCATOR
80515bc: mov eax,ds:0x835d81a 80515c1: mov ebx,DWORD PTR 80515c7: mov edx,DWORD PTR ds:0x835d7da 80515cd: moveax,0x0
MONITORING & CONTROLLING KERNEL-MODE EVENTS BY HYPERPLATFORM 4 Satoshi Tanda (@standa_t) – Reverse engineer interested in the Windows kernel – Implemented HyperPlatform – Threat Researcher at Sophos specializing in behaviour based detection on Windows Igor Korkin (@Igorkorkin) – An independent researcher focusing on cyber security science: memory forensics, rootkit detection & spy technologies – Co-researcher, focused on application of CONFERENCE - RECON.CX REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. AUTOMATING REVERSE ENGINEERING WITH MACHINE LEARNING AND Reverse engineering (RE) applications (e.g. malware and vulnerability analysis) have historically been a manual and time-intensive process performed by skilled practitioners. In this course, we will introduce, discuss, and demonstrate (via labs) how Binary Analysis and Machine Learning (ML) techniques can be leveraged to address automation andscaling challenges
RECON MONTREAL 2019
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. It is held annually in Montreal, Canada. It offers a single track of presentations over the span of three days with a focus on reverse engineering and advanced exploitation techniques. For more information, includingpricing and
TRAININGS - RECON
18 to 21 June - Windows Internals for Reverse Engineers. Learn the internals of the Windows NT kernel architecture, including Windows 10 “Threshold 2” and “Redstone 1”, as well as Server 2016, in order to learn how rootkits, PLA implants, NSA backdoors, and other kernel-mode malware exploit the various system functionalities, mechanisms and data structures to do their dirty work. BINARY LITERACY: SYSTEMATIC STATIC REVERSE ENGINEERING This four-day course contains a thorough introduction to static reverse engineering, the act of deriving meaning from assembly language code simply by reading it. SGX ENCLAVE PROGRAMMING: COMMON MISTAKES AGENDA AND SPECIAL NOTE ON THE TIME ALLOCATION •Damn Vulnerable approach •SGX Enclave and threat model change •PSW (platform software), SDK and the structure of applications with SGX enclave •DVSE itself, its code quality and finding hardware •List of bad practices (WKMs) •DVSE Demo •Tools and better practices (BKMs) 3 Note that SGX is a bit complicated and some of this talk willRECON MONTREAL 2017
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. It is held annually in Montreal, Canada. It offers a single track of presentations over the span of three days with a focus on reverse engineering and advanced exploitation techniques. For more information, includingpricing and
HACKING TOSHIBA LAPTOPS Decompression Unknown format Default unpacker is a 16-bit EXE There’s an alternative one, 32-bit!INTEL ME SECRETS
Intel ME Secrets Hidden code in your chipset and how to discover what exactly it does Igor Skochinsky Hex-Rays RECON 2014 Montreal WINDOWS PRIVILEGE ESCALATION THROUGH AND ALPC … Page 5 of 26 2 June 2008 Following is a list of some of the reported vulnerabilities: MS00-003 - Spoofed LPC Port Request (Impersonate a privileged user) MS00-070 - Multiple LPC and LPC Ports Vulnerabilities (Privilege escalation and message leaking) MS03-031 - Cumulative Patch for Microsoft SQL Server (Privilege escalation) MS04-044 - Vulnerabilities in Windows Kernel and LSASS (Privilege RECON.CXRECON MONTREAL 2020ARCHIVESCONTACTCFPTRAININGSSPONSORSRECON 2020RECON 2020 MOVIERECON MOVIE TRAILERHONDA RECON 2021REFIT RECON 2021JEEP RUBICON RECON 2019 RECON.CX. RECON Montreal 2020. RECON MTL 2020 JUNE 19-20-21 Hilton Double Tree Montreal, Canada CLICK HERE . Montreal 2018 Slides. Montreal 2018 Slides. Brussels 2018 Slides. Brussels 2018 Slides. Montreal 2017 Slides. Montreal 2017 Slides. CONFERENCE - RECON.CX REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.RECON.CX
RECON Montreal 2018. RECON MTL 2018 JUNE 15-16-17 Hyatt Regency Montreal, Canada CLICK HERE . RECON Brussels 2018. RECON BRX 2018 February 2-3-4 The Egg Brussels, Belgium CLICK HERE . Montreal 2017Slides.
RECON MONTREAL 2019GHOST RECON GUN LIST REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. It is held annually in Montreal, Canada. It offers a single track of presentations over the span of three days with a focus on reverse engineering and advanced exploitation techniques. For more information, includingpricing and
SLIDES - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.ARCHIVES - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.SCHEDULE - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. DIY ARM DEBUGGER FOR WI-FI CHIPS USING NEXMON TO PERFORM DIY ARM Debugger for Wi-Fi Chips Using Nexmon to Perform Single-Step Debugging and More on Proprietary Wi-Fi Chips Matthias Schulz Powered by: Matthias Schulz | SEEMOO | TU Darmstadt | DIY ARM Debugger for Wi-Fi Chips 1 Debugger FITBIT FIRMWARE HACKING 18 Newer trackers come with encryption enabled by default We need to know how encrypted firmware updates work Trackers use XTEA/AES in EAX mode: • 2 byte nonce in beginning of each dump • 128 bit encryption key, extractable from EEPROM via memory readout attack • 8 byte authentication MAC in the end of each dump before length field Firmware is based on LibTomCrypt (C) REVERSE ENGINEERING OF BLOCKCHAIN SMART CONTRACTS What is Ethereum? “Ethereum is a decentralized platform that runs smart contracts: applications that run exactly as programmed without any possibility of downtime, censorship, fraud or third-party interference.”Create by Vitalik Buterin & Gavin Wood - 2013 White paper: Description of the project Yellow paper: Ethereum's formal specification (Technical) RECON.CXRECON MONTREAL 2020ARCHIVESCONTACTCFPTRAININGSSPONSORSRECON 2020RECON 2020 MOVIERECON MOVIE TRAILERHONDA RECON 2021REFIT RECON 2021JEEP RUBICON RECON 2019 RECON.CX. RECON Montreal 2020. RECON MTL 2020 JUNE 19-20-21 Hilton Double Tree Montreal, Canada CLICK HERE . Montreal 2018 Slides. Montreal 2018 Slides. Brussels 2018 Slides. Brussels 2018 Slides. Montreal 2017 Slides. Montreal 2017 Slides. CONFERENCE - RECON.CX REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.RECON.CX
RECON Montreal 2018. RECON MTL 2018 JUNE 15-16-17 Hyatt Regency Montreal, Canada CLICK HERE . RECON Brussels 2018. RECON BRX 2018 February 2-3-4 The Egg Brussels, Belgium CLICK HERE . Montreal 2017Slides.
RECON MONTREAL 2019GHOST RECON GUN LIST REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. It is held annually in Montreal, Canada. It offers a single track of presentations over the span of three days with a focus on reverse engineering and advanced exploitation techniques. For more information, includingpricing and
SLIDES - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.ARCHIVES - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.SCHEDULE - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. DIY ARM DEBUGGER FOR WI-FI CHIPS USING NEXMON TO PERFORM DIY ARM Debugger for Wi-Fi Chips Using Nexmon to Perform Single-Step Debugging and More on Proprietary Wi-Fi Chips Matthias Schulz Powered by: Matthias Schulz | SEEMOO | TU Darmstadt | DIY ARM Debugger for Wi-Fi Chips 1 Debugger FITBIT FIRMWARE HACKING 18 Newer trackers come with encryption enabled by default We need to know how encrypted firmware updates work Trackers use XTEA/AES in EAX mode: • 2 byte nonce in beginning of each dump • 128 bit encryption key, extractable from EEPROM via memory readout attack • 8 byte authentication MAC in the end of each dump before length field Firmware is based on LibTomCrypt (C) REVERSE ENGINEERING OF BLOCKCHAIN SMART CONTRACTS What is Ethereum? “Ethereum is a decentralized platform that runs smart contracts: applications that run exactly as programmed without any possibility of downtime, censorship, fraud or third-party interference.”Create by Vitalik Buterin & Gavin Wood - 2013 White paper: Description of the project Yellow paper: Ethereum's formal specification (Technical)RECON MONTREAL 2020
WHAT. REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. It is held annually in Montreal, Canada.It offers a single track of presentations over the span of three days with a focus on reverse engineering and advanced exploitation techniques.SLIDES - RECON
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. TRAININGS - RECON.CX Windows Internals for Reverse Engineers. Learn the internals of the Windows NT kernel architecture, including Windows 10 “Threshold 2” and “Redstone 1”, as well as Server 2016, in order to learn how rootkits, PLA implants, NSA backdoors, and other kernel-mode malware exploit the various system functionalities, mechanisms and data structures to do their dirty work.RECON TRAINING
Bio. Alex Ionescu is the Chief Architect at CrowdStrike, Inc. Alex is a world-class security architect and consultant expert in low-level system software, kernel development, security training, and reverse engineering. He is coauthor of the last two editions of the Windows Internals series, along with Mark Russinovich and David Solomon.SCHEDULE - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.RECON.CX
Author: Ilfak Guilfanov Created Date: 2/9/2018 9:53:36 PM REVERSING FREERTOS ON EMBEDDED DEVICES 14 RECON 2017 Brussels Introducing Free RTOS • Small and very lean RTOS developed by Real Time Engineers Ltd • Free and open source environment (there is a commercial version) BINARY LITERACY: SYSTEMATIC STATIC REVERSE ENGINEERING This four-day course contains a thorough introduction to static reverse engineering, the act of deriving meaning from assembly language code simply by reading it.CFP - RECON
Recon Montreal - Call For Papers - June 15 - 17 - 2018 - RECON MONTREAL 2018 - 0xE - CFP - Training Registration - Conference -Submit! - PGP key
MCSEMA: STATIC TRANSLATION OF X86 INSTRUCTIONS TO LLVM McSema: Static Translation of X86 Instructions to LLVM ARTEM DINABURG, ARTEM@TRAILOFBITS.COM ANDREW RUEF, ANDREW@TRAILOFBITS.COM ^This research was developed with funding from the Defense Advanced Research Projects Agency ~DARPA . _ RECON.CXRECON MONTREAL 2020ARCHIVESCONTACTCFPTRAININGSSPONSORSRECON 2020RECON 2020 MOVIERECON MOVIE TRAILERHONDA RECON 2021REFIT RECON 2021JEEP RUBICON RECON 2019 RECON.CX. RECON Montreal 2020. RECON MTL 2020 JUNE 19-20-21 Hilton Double Tree Montreal, Canada CLICK HERE . Montreal 2018 Slides. Montreal 2018 Slides. Brussels 2018 Slides. Brussels 2018 Slides. Montreal 2017 Slides. Montreal 2017 Slides. CONFERENCE - RECON.CX REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.RECON.CX
RECON Montreal 2018. RECON MTL 2018 JUNE 15-16-17 Hyatt Regency Montreal, Canada CLICK HERE . RECON Brussels 2018. RECON BRX 2018 February 2-3-4 The Egg Brussels, Belgium CLICK HERE . Montreal 2017Slides.
RECON MONTREAL 2019GHOST RECON GUN LIST REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. It is held annually in Montreal, Canada. It offers a single track of presentations over the span of three days with a focus on reverse engineering and advanced exploitation techniques. For more information, includingpricing and
SLIDES - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.ARCHIVES - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.SCHEDULE - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. DIY ARM DEBUGGER FOR WI-FI CHIPS USING NEXMON TO PERFORM DIY ARM Debugger for Wi-Fi Chips Using Nexmon to Perform Single-Step Debugging and More on Proprietary Wi-Fi Chips Matthias Schulz Powered by: Matthias Schulz | SEEMOO | TU Darmstadt | DIY ARM Debugger for Wi-Fi Chips 1 Debugger FITBIT FIRMWARE HACKING 18 Newer trackers come with encryption enabled by default We need to know how encrypted firmware updates work Trackers use XTEA/AES in EAX mode: • 2 byte nonce in beginning of each dump • 128 bit encryption key, extractable from EEPROM via memory readout attack • 8 byte authentication MAC in the end of each dump before length field Firmware is based on LibTomCrypt (C) REVERSE ENGINEERING OF BLOCKCHAIN SMART CONTRACTS What is Ethereum? “Ethereum is a decentralized platform that runs smart contracts: applications that run exactly as programmed without any possibility of downtime, censorship, fraud or third-party interference.”Create by Vitalik Buterin & Gavin Wood - 2013 White paper: Description of the project Yellow paper: Ethereum's formal specification (Technical) RECON.CXRECON MONTREAL 2020ARCHIVESCONTACTCFPTRAININGSSPONSORSRECON 2020RECON 2020 MOVIERECON MOVIE TRAILERHONDA RECON 2021REFIT RECON 2021JEEP RUBICON RECON 2019 RECON.CX. RECON Montreal 2020. RECON MTL 2020 JUNE 19-20-21 Hilton Double Tree Montreal, Canada CLICK HERE . Montreal 2018 Slides. Montreal 2018 Slides. Brussels 2018 Slides. Brussels 2018 Slides. Montreal 2017 Slides. Montreal 2017 Slides. CONFERENCE - RECON.CX REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.RECON.CX
RECON Montreal 2018. RECON MTL 2018 JUNE 15-16-17 Hyatt Regency Montreal, Canada CLICK HERE . RECON Brussels 2018. RECON BRX 2018 February 2-3-4 The Egg Brussels, Belgium CLICK HERE . Montreal 2017Slides.
RECON MONTREAL 2019GHOST RECON GUN LIST REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. It is held annually in Montreal, Canada. It offers a single track of presentations over the span of three days with a focus on reverse engineering and advanced exploitation techniques. For more information, includingpricing and
SLIDES - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.ARCHIVES - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.SCHEDULE - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. DIY ARM DEBUGGER FOR WI-FI CHIPS USING NEXMON TO PERFORM DIY ARM Debugger for Wi-Fi Chips Using Nexmon to Perform Single-Step Debugging and More on Proprietary Wi-Fi Chips Matthias Schulz Powered by: Matthias Schulz | SEEMOO | TU Darmstadt | DIY ARM Debugger for Wi-Fi Chips 1 Debugger FITBIT FIRMWARE HACKING 18 Newer trackers come with encryption enabled by default We need to know how encrypted firmware updates work Trackers use XTEA/AES in EAX mode: • 2 byte nonce in beginning of each dump • 128 bit encryption key, extractable from EEPROM via memory readout attack • 8 byte authentication MAC in the end of each dump before length field Firmware is based on LibTomCrypt (C) REVERSE ENGINEERING OF BLOCKCHAIN SMART CONTRACTS What is Ethereum? “Ethereum is a decentralized platform that runs smart contracts: applications that run exactly as programmed without any possibility of downtime, censorship, fraud or third-party interference.”Create by Vitalik Buterin & Gavin Wood - 2013 White paper: Description of the project Yellow paper: Ethereum's formal specification (Technical)RECON MONTREAL 2020
WHAT. REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. It is held annually in Montreal, Canada.It offers a single track of presentations over the span of three days with a focus on reverse engineering and advanced exploitation techniques.SLIDES - RECON
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. TRAININGS - RECON.CX Windows Internals for Reverse Engineers. Learn the internals of the Windows NT kernel architecture, including Windows 10 “Threshold 2” and “Redstone 1”, as well as Server 2016, in order to learn how rootkits, PLA implants, NSA backdoors, and other kernel-mode malware exploit the various system functionalities, mechanisms and data structures to do their dirty work.RECON TRAINING
Bio. Alex Ionescu is the Chief Architect at CrowdStrike, Inc. Alex is a world-class security architect and consultant expert in low-level system software, kernel development, security training, and reverse engineering. He is coauthor of the last two editions of the Windows Internals series, along with Mark Russinovich and David Solomon.SCHEDULE - RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques.RECON.CX
Author: Ilfak Guilfanov Created Date: 2/9/2018 9:53:36 PM REVERSING FREERTOS ON EMBEDDED DEVICES 14 RECON 2017 Brussels Introducing Free RTOS • Small and very lean RTOS developed by Real Time Engineers Ltd • Free and open source environment (there is a commercial version) BINARY LITERACY: SYSTEMATIC STATIC REVERSE ENGINEERING This four-day course contains a thorough introduction to static reverse engineering, the act of deriving meaning from assembly language code simply by reading it.CFP - RECON
Recon Montreal - Call For Papers - June 15 - 17 - 2018 - RECON MONTREAL 2018 - 0xE - CFP - Training Registration - Conference -Submit! - PGP key
MCSEMA: STATIC TRANSLATION OF X86 INSTRUCTIONS TO LLVM McSema: Static Translation of X86 Instructions to LLVM ARTEM DINABURG, ARTEM@TRAILOFBITS.COM ANDREW RUEF, ANDREW@TRAILOFBITS.COM ^This research was developed with funding from the Defense Advanced Research Projects Agency ~DARPA . _RECON.CX
REcon is a computer security conference with a focus on reverse engineering and advanced exploitation techniques. -------------------------RECON Montreal 2020
RECON MTL 2020
JUNE 19-20-21
Hilton Double TreeMontreal, Canada
CLICK HERE
►
Montreal 2018 SlidesMontreal 2018
Slides
Brussels 2018 Slides Brussels 2018 Slides Montreal 2017 SlidesMontreal 2017
Slides
Brussels 2018 SlidesBrussels 2018
Slides
Montreal 2017 recordingsMontreal 2017
Recordings
Brussels 2018 VideosBrussels 2017
Recordings
RECON.CX
* info@recon.cx
* RECONMTL
Platinum sponsors
� 2005-2019 RECON.CXDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0
