Are you over 18 and want to see adult content?
More Annotations

A complete backup of carakandunganhamil.com
Are you over 18 and want to see adult content?
A complete backup of kallanishenergy.com
Are you over 18 and want to see adult content?
A complete backup of poemsearcher.com
Are you over 18 and want to see adult content?

A complete backup of indoorleddisplayscreen.com
Are you over 18 and want to see adult content?
A complete backup of moonshinegrill.com
Are you over 18 and want to see adult content?
A complete backup of freeonlinecasinoww.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of idrivesafely.com
Are you over 18 and want to see adult content?
A complete backup of clermont-ferrand.fr
Are you over 18 and want to see adult content?
A complete backup of accountingexplained.com
Are you over 18 and want to see adult content?
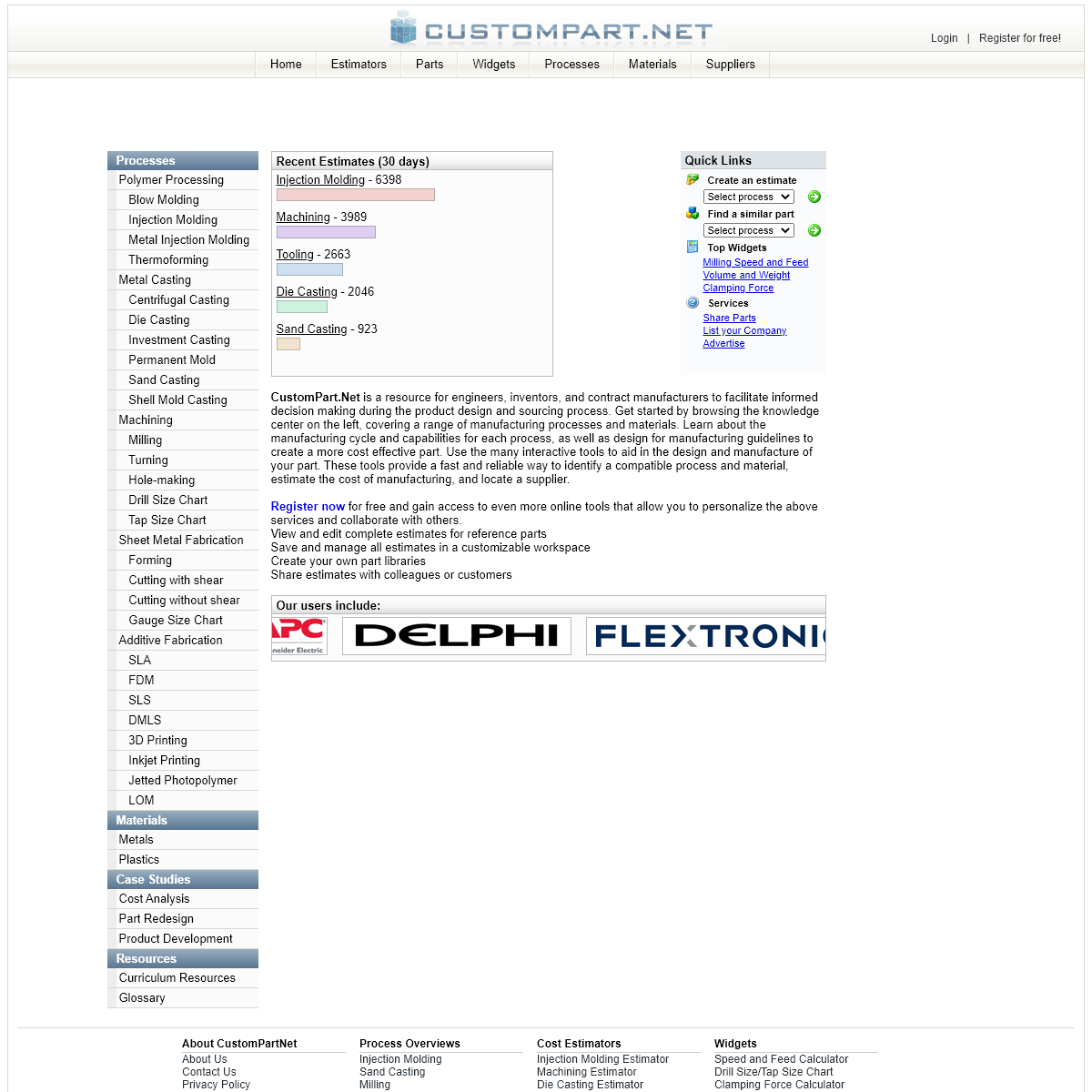
A complete backup of custompartnet.com
Are you over 18 and want to see adult content?

A complete backup of dissertation-help-online.co.uk
Are you over 18 and want to see adult content?

A complete backup of careerpilot.org.uk
Are you over 18 and want to see adult content?

A complete backup of nibblemethis.com
Are you over 18 and want to see adult content?
Text
IMMUNITY INC.
Since 2002 IMMUNITY has been a specialized, detail-oriented security provider, with only top-tier security experts on staff. IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown.PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
IMMUNITY INC : WHO WE ARE Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. Immunity is known for its aggressive and real-world approach to assessments. Immunity has grown its unique technologyofferings
CONTACT - IMMUNITY INC. We can be reached between the hours of 9am - 5pm (Eastern Time Zone) Immunity Inc. 2751 N. Miami Ave. Suite #7 Miami, Florida 33127 CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and security professionals worldwide. For users new to CANVAS or experienced users looking to get just a little more out of CANVAS we have PDF-based tutorials available forWEB HACKING
Web Hacking. Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerable systems. Security professionals with some hands on web hacking experience will get the most out of this course. Immunity's trainers have developed a prerequisite evaluation for all potential students totake
DOCUMENTATION
Each row in the Network Listing Tab represents a Basic Service Set (BSS). A BSS can be formed by either infrastructure mode redistribution points, or by peer-to-peer ad hoc topology devices. The Type values for BSSs are “AP”, or “Ad-Hoc”. In this manual, we will refer to them as Access Points (AP) as that is the most common network architecture. CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1 DEFEATING DEP, THE IMMUNITY DEBUGGER WAY 11/12/08 11 SearchDEP Example 7C91990D 66 83 26 00 66 83 66 fƒ&.fƒf 7C919915 02 00 83 66 04 00 5E 5D .ƒf.^] 7C91991D C2 04 00 Â. Binary Data Possible Disassemblies 7C91991A 005E 5D | ADD BYTE PTR DS:,BL 7C91991D C2 0400 | RETN 4IMMUNITY INC.
Since 2002 IMMUNITY has been a specialized, detail-oriented security provider, with only top-tier security experts on staff. IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown.PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
IMMUNITY INC : WHO WE ARE Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. Immunity is known for its aggressive and real-world approach to assessments. Immunity has grown its unique technologyofferings
CONTACT - IMMUNITY INC. We can be reached between the hours of 9am - 5pm (Eastern Time Zone) Immunity Inc. 2751 N. Miami Ave. Suite #7 Miami, Florida 33127 CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and security professionals worldwide. For users new to CANVAS or experienced users looking to get just a little more out of CANVAS we have PDF-based tutorials available forWEB HACKING
Web Hacking. Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerable systems. Security professionals with some hands on web hacking experience will get the most out of this course. Immunity's trainers have developed a prerequisite evaluation for all potential students totake
DOCUMENTATION
Each row in the Network Listing Tab represents a Basic Service Set (BSS). A BSS can be formed by either infrastructure mode redistribution points, or by peer-to-peer ad hoc topology devices. The Type values for BSSs are “AP”, or “Ad-Hoc”. In this manual, we will refer to them as Access Points (AP) as that is the most common network architecture. CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1 DEFEATING DEP, THE IMMUNITY DEBUGGER WAY 11/12/08 11 SearchDEP Example 7C91990D 66 83 26 00 66 83 66 fƒ&.fƒf 7C919915 02 00 83 66 04 00 5E 5D .ƒf.^] 7C91991D C2 04 00 Â. Binary Data Possible Disassemblies 7C91991A 005E 5D | ADD BYTE PTR DS:,BL 7C91991D C2 0400 | RETN 4SERVICES OVERVIEW
Consulting Services Overview. Immunity offers specialized attack and assessment services, including penetration testing, application assessments, vulnerability analysis, reverse engineering, architecture review and source code review. New clients are often surprised to learn about the existence of unpublicized or unpatched vulnerabilitiesin
WEB HACKING
Web Hacking. Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerable systems. Security professionals with some hands on web hacking experience will get the most out of this course. Immunity's trainers have developed a prerequisite evaluation for all potential students totake
CAREERS - IMMUNITY INC. Careers. Services Overview. Immunity Adversary Simulation. Application Vulnerability Analysis. Exploit Development & Reverse Engineering. Network Security Assessment. Penetration Testing. Process Review. Source Code Analysis. IMMUNITY INC: KNOWING YOU'RE SECURE Overview. Traditionally penetration testing tools target hosts one at a time. SWARM differs in that it can deploy any CANVAS module, exploit or reconnaissance tool against large sections of a cyber range inminutes to hours.
DOCUMENTATION
Each row in the Network Listing Tab represents a Basic Service Set (BSS). A BSS can be formed by either infrastructure mode redistribution points, or by peer-to-peer ad hoc topology devices. The Type values for BSSs are “AP”, or “Ad-Hoc”. In this manual, we will refer to them as Access Points (AP) as that is the most common network architecture.IMMUNITY DEBUGGER
Immunity Debugger is a powerful new way to write exploits, analyze malware, and reverse engineer binary files. It builds on a solid user interface with function graphing, the industry's first heap analysis tool built specifically for heap creation, and a large and well supported Python API for easy extensibility. APPLICATION VULNERABILITY ANALYSIS Application Vulnerability Analysis. Immunity offers specialized attack and assessment services, including penetration testing, application assessments, vulnerability analysis, reverse engineering, architecture review and source code review. Immunity adopts various methods to conduct application vulnerability analysis, always with the goal of NETWORK SECURITY ASSESSMENT Network Security Assessment. Immunity uses CANVAS's proprietary scanning and reconnaissance methods, as well as other publicly available tools, to assess the security of networks and systems accessible on client networks. Service identification, host OS identification, remote language detection, and unique data interception techniques are just CANVAS EARLY UPDATES CANVAS Early Updates Program. Immunity CANVAS is heavily QA'd and on a monthly release cycle, however a select number of Immunity's clients rely on up-to-the-minute vulnerability information as Immunity produces material. Immunity is often first to market with new exploits and proof of concept exploit code following "Microsoft Tuesdays". LINUX KERNEL EXPLOITATION Linux Kernel Exploitation. The Immunity Linux Kernel Exploitation class focuses on modern exploit development and vulnerability discovery techniques. Intermediate to advanced exploit development skills are recommended for students wishing to this class. For additional information or pricing quotes please send an email to training@immunityincdotcom.IMMUNITY INC.
Since 2002 IMMUNITY has been a specialized, detail-oriented security provider, with only top-tier security experts on staff. IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown.PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. IMMUNITY INC : WHO WE ARE What is Immunity? Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and CONTACT - IMMUNITY INC. We can be reached between the hours of 9am - 5pm (Eastern Time Zone) Immunity Inc. 2751 N. Miami Ave. Suite #7 Miami, Florida 33127 CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1 DEFEATING DEP, THE IMMUNITY DEBUGGER WAY 11/12/08 11 SearchDEP Example 7C91990D 66 83 26 00 66 83 66 fƒ&.fƒf 7C919915 02 00 83 66 04 00 5E 5D .ƒf.^] 7C91991D C2 04 00 Â. Binary Data Possible Disassemblies 7C91991A 005E 5D | ADD BYTE PTR DS:,BL 7C91991D C2 0400 | RETN 4 THE ADVANTAGES OF BLOCK-BASED PROTOCOL ANALYSIS FOR The Advantages of Block-Based Protocol Analysis for Security Testing Dave Aitel Immunity,Inc. 111 E. 7th St. Suite 64, NY NY 10009, USA dave@immunitysec.com February, 4 2002 Abstract. 0DAYS: HOW HACKING REALLY WORKS 0days: How hacking really works V 1.0 Jan 29, 2005 Dave Aitel dave@immunitysec.comIMMUNITY INC.
Since 2002 IMMUNITY has been a specialized, detail-oriented security provider, with only top-tier security experts on staff. IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown.PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. IMMUNITY INC : WHO WE ARE What is Immunity? Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and CONTACT - IMMUNITY INC. We can be reached between the hours of 9am - 5pm (Eastern Time Zone) Immunity Inc. 2751 N. Miami Ave. Suite #7 Miami, Florida 33127 CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1 DEFEATING DEP, THE IMMUNITY DEBUGGER WAY 11/12/08 11 SearchDEP Example 7C91990D 66 83 26 00 66 83 66 fƒ&.fƒf 7C919915 02 00 83 66 04 00 5E 5D .ƒf.^] 7C91991D C2 04 00 Â. Binary Data Possible Disassemblies 7C91991A 005E 5D | ADD BYTE PTR DS:,BL 7C91991D C2 0400 | RETN 4 THE ADVANTAGES OF BLOCK-BASED PROTOCOL ANALYSIS FOR The Advantages of Block-Based Protocol Analysis for Security Testing Dave Aitel Immunity,Inc. 111 E. 7th St. Suite 64, NY NY 10009, USA dave@immunitysec.com February, 4 2002 Abstract. 0DAYS: HOW HACKING REALLY WORKS 0days: How hacking really works V 1.0 Jan 29, 2005 Dave Aitel dave@immunitysec.comSERVICES OVERVIEW
Consulting Services Overview. Immunity offers specialized attack and assessment services, including penetration testing, application assessments, vulnerability analysis, reverse engineering, architecture review and source code review.CONSULTANTS
Consultants. Significant experience and knowledge is needed to offer quality security assessment services. Immunity is a specialized, detail-oriented security provider, with only top-tier security expertson
CAREERS - IMMUNITY INC. �CANVAS, ®SILICA, ®Innuendo, ®El Jefe, ®Immunity, and �Infiltrate are all registered trademarks of Immunity Inc. © 2020 Immunity Inc. All rights reservedDOCUMENTATION
Each row in the Network Listing Tab represents a Basic Service Set (BSS). A BSS can be formed by either infrastructure mode redistribution points, or by peer-to-peer ad hoc topology devices. The Type values for BSSs are “AP”, or “Ad-Hoc”. In this manual, we will refer to them as Access Points (AP) as that is the most common network architecture.PENETRATION TESTING
Penetration Testing. Penetration Testing is Immunity Service's premier consulting option. Our experienced team of security consultants assumes the role of real world attackers that will stop at nothing to compromise your infrastructure.WEB HACKING
Web Hacking. Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerablesystems.
SILICA
Overview. Understanding the vulnerabilities of your WiFi network can be challenging as users can easily create networks on demand, or even perhaps unintentionally. TECHNICAL PAPERS & PRESENTATIONS Technical Papers & Presentations These white papers, technical papers and presentations have been given all over the world at securityconferences.
EL JEFE - IMMUNITYSEC.COM Download. Download El Jefe Here! Overview. El Jefe is a Windows-based process monitoring solution. El Jefe produces a unique view into how processes are created, what privileges they possess and what child processes they spawn. WIRELESS SECURITY ASSESSMENT Wireless Security Assessment. Immunity's wireless security specialists have several years of experience assessing wireless infrastructure in environments as diverse as government services, entertainment venues, retail, transportation, and the financial sector.IMMUNITY INC.
Since 2002 IMMUNITY has been a specialized, detail-oriented security provider, with only top-tier security experts on staff. IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown.PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
IMMUNITY INC : WHO WE ARE Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. Immunity is known for its aggressive and real-world approach to assessments. Immunity has grown its unique technologyofferings
CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and security professionals worldwide. For users new to CANVAS or experienced users looking to get just a little more out of CANVAS we have PDF-based tutorials available for CONTACT - IMMUNITY INC. We can be reached between the hours of 9am - 5pm (Eastern Time Zone) Immunity Inc. 2751 N. Miami Ave. Suite #7 Miami, Florida 33127 CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1 DEFEATING DEP, THE IMMUNITY DEBUGGER WAY 11/12/08 11 SearchDEP Example 7C91990D 66 83 26 00 66 83 66 fƒ&.fƒf 7C919915 02 00 83 66 04 00 5E 5D .ƒf.^] 7C91991D C2 04 00 Â. Binary Data Possible Disassemblies 7C91991A 005E 5D | ADD BYTE PTR DS:,BL 7C91991D C2 0400 | RETN 4 0DAYS: HOW HACKING REALLY WORKS 0days: How hacking really works V 1.0 Jan 29, 2005 Dave Aitel dave@immunitysec.com THE ADVANTAGES OF BLOCK-BASED PROTOCOL ANALYSIS FOR The Advantages of Block-Based Protocol Analysis for Security Testing Dave Aitel Immunity,Inc. 111 E. 7th St. Suite 64, NY NY 10009, USA dave@immunitysec.com February, 4 2002 Abstract.IMMUNITY INC.
Since 2002 IMMUNITY has been a specialized, detail-oriented security provider, with only top-tier security experts on staff. IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown.PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
IMMUNITY INC : WHO WE ARE Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. Immunity is known for its aggressive and real-world approach to assessments. Immunity has grown its unique technologyofferings
CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and security professionals worldwide. For users new to CANVAS or experienced users looking to get just a little more out of CANVAS we have PDF-based tutorials available for CONTACT - IMMUNITY INC. We can be reached between the hours of 9am - 5pm (Eastern Time Zone) Immunity Inc. 2751 N. Miami Ave. Suite #7 Miami, Florida 33127 CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1 DEFEATING DEP, THE IMMUNITY DEBUGGER WAY 11/12/08 11 SearchDEP Example 7C91990D 66 83 26 00 66 83 66 fƒ&.fƒf 7C919915 02 00 83 66 04 00 5E 5D .ƒf.^] 7C91991D C2 04 00 Â. Binary Data Possible Disassemblies 7C91991A 005E 5D | ADD BYTE PTR DS:,BL 7C91991D C2 0400 | RETN 4 0DAYS: HOW HACKING REALLY WORKS 0days: How hacking really works V 1.0 Jan 29, 2005 Dave Aitel dave@immunitysec.com THE ADVANTAGES OF BLOCK-BASED PROTOCOL ANALYSIS FOR The Advantages of Block-Based Protocol Analysis for Security Testing Dave Aitel Immunity,Inc. 111 E. 7th St. Suite 64, NY NY 10009, USA dave@immunitysec.com February, 4 2002 Abstract.PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
CONSULTING SERVICES OVERVIEW Consulting Services Overview. Immunity offers specialized attack and assessment services, including penetration testing, application assessments, vulnerability analysis, reverse engineering, architecture review and source code review. New clients are often surprised to learn about the existence of unpublicized or unpatched vulnerabilitiesin
CAREERS - IMMUNITY INC. Careers. Services Overview. Immunity Adversary Simulation. Application Vulnerability Analysis. Exploit Development & Reverse Engineering. Network Security Assessment. Penetration Testing. Process Review. Source Code Analysis.CONSULTANTS
Consultants. Significant experience and knowledge is needed to offer quality security assessment services. Immunity is a specialized, detail-oriented security provider, with only top-tier security experts on its staff. Immunity draws on its staff's vast knowledge and skill-set to analyze an application for all potential vulnerabilities,known
WEB HACKING
Web Hacking. Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerablesystems.
IMMUNITY DEBUGGER
Immunity Debugger is a powerful new way to write exploits, analyze malware, and reverse engineer binary files. It builds on a solid user interface with function graphing, the industry's first heap analysis tool built specifically for heap creation, and a large and well supported Python API for easy extensibility.PENETRATION TESTING
Penetration Testing. Penetration Testing is Immunity Service's premier consulting option. Our experienced team of security consultants assumes the role of real world attackers that will stop at nothing to compromise your infrastructure. You can focus the scope of the engagement on specific parts of your infrastructure, or open up thescope for
DOCUMENTATION
Each row in the Network Listing Tab represents a Basic Service Set (BSS). A BSS can be formed by either infrastructure mode redistribution points, or by peer-to-peer ad hoc topology devices. The Type values for BSSs are “AP”, or “Ad-Hoc”. In this manual, we will refer to them as Access Points (AP) as that is the most common network architecture. NETWORK SECURITY ASSESSMENT Network Security Assessment. Immunity uses CANVAS's proprietary scanning and reconnaissance methods, as well as other publicly available tools, to assess the security of networks and systems accessible on client networks. Service identification, host OS identification, remote language detection, and unique data interception techniques are just WIRELESS SECURITY ASSESSMENT Wireless Security Assessment. Immunity's wireless security specialists have several years of experience assessing wireless infrastructure in environments as diverse as government services, entertainment venues, retail, transportation, and the financial sector. When combined with our specialization in the identification of new or previouslyIMMUNITY INC.
IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown. Because of IMMUNITY's focus on offensive techniques, we are able to mimic the skill-set of a genuine threat. IMMUNITY prides itself on demonstrating the TRUE risk that a vulnerability poses to anorganization.
PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
IMMUNITY INC : WHO WE ARE Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. Immunity is known for its aggressive and real-world approach to assessments. Immunity has grown its unique technologyofferings
EDUCATION OVERVIEW
Education Overview. Immunity training is not just the standard assortment of Ethical Hacking, Penetration Testing, and VulnerabilityAssessment courses.
CONTACT - IMMUNITY INC. Visit @immunityinc on Twitter. IMMUNITY INC SECURES BOTH GOVERNMENT & COMMERCIAL contact us. HEADQUARTERS 2751 N. Miami Ave. Suite #7 Miami FL 33127. Email: sales@immunityinc.com. Phone: +1 786.220.0600. CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and security professionals worldwide. For users new to CANVAS or experienced users looking to get just a little more out of CANVAS we have PDF-based tutorials available forWEB HACKING
Web Hacking. Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerablesystems.
IMMUNITY DEBUGGER
Immunity Debugger is a powerful new way to write exploits, analyze malware, and reverse engineer binary files. It builds on a solid user interface with function graphing, the industry's first heap analysis tool built specifically for heap creation, and a large and well supported Python API for easy extensibility. CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1IMMUNITY INC.
IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown. Because of IMMUNITY's focus on offensive techniques, we are able to mimic the skill-set of a genuine threat. IMMUNITY prides itself on demonstrating the TRUE risk that a vulnerability poses to anorganization.
PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
IMMUNITY INC : WHO WE ARE Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. Immunity is known for its aggressive and real-world approach to assessments. Immunity has grown its unique technologyofferings
EDUCATION OVERVIEW
Education Overview. Immunity training is not just the standard assortment of Ethical Hacking, Penetration Testing, and VulnerabilityAssessment courses.
CONTACT - IMMUNITY INC. Visit @immunityinc on Twitter. IMMUNITY INC SECURES BOTH GOVERNMENT & COMMERCIAL contact us. HEADQUARTERS 2751 N. Miami Ave. Suite #7 Miami FL 33127. Email: sales@immunityinc.com. Phone: +1 786.220.0600. CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and security professionals worldwide. For users new to CANVAS or experienced users looking to get just a little more out of CANVAS we have PDF-based tutorials available forWEB HACKING
Web Hacking. Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerablesystems.
IMMUNITY DEBUGGER
Immunity Debugger is a powerful new way to write exploits, analyze malware, and reverse engineer binary files. It builds on a solid user interface with function graphing, the industry's first heap analysis tool built specifically for heap creation, and a large and well supported Python API for easy extensibility. CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
SERVICES OVERVIEW
Consulting Services Overview. Immunity offers specialized attack and assessment services, including penetration testing, application assessments, vulnerability analysis, reverse engineering, architecture review and source code review. New clients are often surprised to learn about the existence of unpublicized or unpatched vulnerabilitiesin
EDUCATION OVERVIEW
Education Overview. Immunity training is not just the standard assortment of Ethical Hacking, Penetration Testing, and VulnerabilityAssessment courses.
CONTACT - IMMUNITY INC. Visit @immunityinc on Twitter. IMMUNITY INC SECURES BOTH GOVERNMENT & COMMERCIAL contact us. HEADQUARTERS 2751 N. Miami Ave. Suite #7 Miami FL 33127. Email: sales@immunityinc.com. Phone: +1 786.220.0600. CAREERS - IMMUNITY INC. Careers. Services Overview. Immunity Adversary Simulation. Application Vulnerability Analysis. Exploit Development & Reverse Engineering. Network Security Assessment. Penetration Testing. Process Review. Source Code Analysis. SILICA - IMMUNITY INC. SILICA Product Features. SILICA leverages Ubuntu 16.04 LTS 64bit and is supplied as a virtual machine. Included with SILICA there is a high performance Panda Wireless USB adapter that greatly increases the wireless performance over the base WiFi chip sets that are included in most commercial laptops.DOCUMENTATION
Each row in the Network Listing Tab represents a Basic Service Set (BSS). A BSS can be formed by either infrastructure mode redistribution points, or by peer-to-peer ad hoc topology devices. The Type values for BSSs are “AP”, or “Ad-Hoc”. In this manual, we will refer to them as Access Points (AP) as that is the most common network architecture. APPLICATION VULNERABILITY ANALYSIS Application Vulnerability Analysis. Immunity offers specialized attack and assessment services, including penetration testing, application assessments, vulnerability analysis, reverse engineering, architecture review and source code review. Immunity adopts various methods to conduct application vulnerability analysis, always with the goal of NETWORK SECURITY ASSESSMENT Network Security Assessment. Immunity uses CANVAS's proprietary scanning and reconnaissance methods, as well as other publicly available tools, to assess the security of networks and systems accessible on client networks. Service identification, host OS identification, remote language detection, and unique data interception techniques are just THE ADVANTAGES OF BLOCK-BASED PROTOCOL ANALYSIS FOR The Advantages of Block-Based Protocol Analysis for Security Testing. Dave Aitel. Immunity,Inc. 111 E. 7 th St. Suite 64, NY NY 10009, USA. dave@immunitysec.comIMMUNITY INC.
IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown. Because of IMMUNITY's focus on offensive techniques, we are able to mimic the skill-set of a genuine threat. IMMUNITY prides itself on demonstrating the TRUE risk that a vulnerability poses to anorganization.
PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
IMMUNITY INC : WHO WE ARE Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. Immunity is known for its aggressive and real-world approach to assessments. Immunity has grown its unique technologyofferings
CONTACT - IMMUNITY INC. Visit @immunityinc on Twitter. IMMUNITY INC SECURES BOTH GOVERNMENT & COMMERCIAL contact us. HEADQUARTERS 2751 N. Miami Ave. Suite #7 Miami FL 33127. Email: sales@immunityinc.com. Phone: +1 786.220.0600.EDUCATION OVERVIEW
Education Overview. Immunity training is not just the standard assortment of Ethical Hacking, Penetration Testing, and VulnerabilityAssessment courses.
CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and security professionals worldwide. For users new to CANVAS or experienced users looking to get just a little more out of CANVAS we have PDF-based tutorials available forWEB HACKING
Web Hacking. Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerable systems. Security professionals with some hands on web hacking experience will get the most out of this course. Immunity's trainers have developed a prerequisite evaluation for all potential students totake
APPLICATION VULNERABILITY ANALYSIS Application Vulnerability Analysis. Immunity offers specialized attack and assessment services, including penetration testing, application assessments, vulnerability analysis, reverse engineering, architecture review and source code review. Immunity adopts various methods to conduct application vulnerability analysis, always with the goal of CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1IMMUNITY INC.
IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown. Because of IMMUNITY's focus on offensive techniques, we are able to mimic the skill-set of a genuine threat. IMMUNITY prides itself on demonstrating the TRUE risk that a vulnerability poses to anorganization.
PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
IMMUNITY INC : WHO WE ARE Immunity was founded in 2002 and was immediately noticed for its breakthrough technologies and industry-recognized team. Immunity has since evolved into a global leader in the assessment and penetration testing space. Immunity is known for its aggressive and real-world approach to assessments. Immunity has grown its unique technologyofferings
CONTACT - IMMUNITY INC. Visit @immunityinc on Twitter. IMMUNITY INC SECURES BOTH GOVERNMENT & COMMERCIAL contact us. HEADQUARTERS 2751 N. Miami Ave. Suite #7 Miami FL 33127. Email: sales@immunityinc.com. Phone: +1 786.220.0600.EDUCATION OVERVIEW
Education Overview. Immunity training is not just the standard assortment of Ethical Hacking, Penetration Testing, and VulnerabilityAssessment courses.
CANVAS - IMMUNITY INC. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive, reliable exploit development framework to penetration testers and security professionals worldwide. For users new to CANVAS or experienced users looking to get just a little more out of CANVAS we have PDF-based tutorials available forWEB HACKING
Web Hacking. Immunity's Web Hacking course focuses on understanding common web hacking techniques by having students exploit vulnerable systems. Security professionals with some hands on web hacking experience will get the most out of this course. Immunity's trainers have developed a prerequisite evaluation for all potential students totake
APPLICATION VULNERABILITY ANALYSIS Application Vulnerability Analysis. Immunity offers specialized attack and assessment services, including penetration testing, application assessments, vulnerability analysis, reverse engineering, architecture review and source code review. Immunity adopts various methods to conduct application vulnerability analysis, always with the goal of CANVAS DOCUMENTATION CANVAS Documentation. Individual CANVAS module documentation is viewable in the CANVAS GUI, standard documentation is included at every release in CANVAS changelog, written tutorials are also available, but the best way to document CANVAS usage is with examples: CANVAS EXPLOIT CATEGORIES EXPLAINED Immunity White Paper CANVAS Exploit Categories Explained November 9th, 2009 By: Alex McGeorge, Immunity Inc. 1PRODUCTS OVERVIEW
Immunity Products. Immunity provides a premiere suite of software and network security assessment tools that cover every phase of your offensive information security life-cycle. From tip-of-spear exploitation through CANVAS and SILICA, to long term Nation-State grade persistence with INNUENDO, the Immunity product line up willkeep your red
SERVICES OVERVIEW
Consulting Services Overview. Immunity offers specialized attack and assessment services, including penetration testing, application assessments, vulnerability analysis, reverse engineering, architecture review and source code review. New clients are often surprised to learn about the existence of unpublicized or unpatched vulnerabilitiesin
EDUCATION OVERVIEW
Education Overview. Immunity training is not just the standard assortment of Ethical Hacking, Penetration Testing, and VulnerabilityAssessment courses.
CAREERS - IMMUNITY INC. Careers. Services Overview. Immunity Adversary Simulation. Application Vulnerability Analysis. Exploit Development & Reverse Engineering. Network Security Assessment. Penetration Testing. Process Review. Source Code Analysis.IMMUNITY DEBUGGER
Immunity Debugger is a powerful new way to write exploits, analyze malware, and reverse engineer binary files. It builds on a solid user interface with function graphing, the industry's first heap analysis tool built specifically for heap creation, and a large and well supported Python API for easy extensibility.CONSULTANTS
Consultants. Significant experience and knowledge is needed to offer quality security assessment services. Immunity is a specialized, detail-oriented security provider, with only top-tier security experts on its staff. Immunity draws on its staff's vast knowledge and skill-set to analyze an application for all potential vulnerabilities,known
SILICA - IMMUNITY INC. SILICA Product Features. SILICA leverages Ubuntu 16.04 LTS 64bit and is supplied as a virtual machine. Included with SILICA there is a high performance Panda Wireless USB adapter that greatly increases the wireless performance over the base WiFi chip sets that are included in most commercial laptops.CANVAS TUTORIALS
CANVAS Tutorials. The following links are PDF versions of CANVAS usage tutorials that originally appeared on the forums. As we continue to convert the old material to this format the list of available tutorials will increase. Immunity's CANVAS makes available hundreds of exploits, an automated exploitation system, and a comprehensive,reliable
WEB APPLICATION TESTING Web Application Testing. Assessments of web applications are usually performed from the perspective of unauthorized and authorized users, with the first goal of ensuring known vulnerabilities in the web servers, application servers, and databases are not present. NETWORK SECURITY ASSESSMENT Network Security Assessment. Immunity uses CANVAS's proprietary scanning and reconnaissance methods, as well as other publicly available tools, to assess the security of networks and systems accessible on client networks. Service identification, host OS identification, remote language detection, and unique data interception techniques are just* RESOURCES
* RESELLERS
* PARTNERS
* CAREERS
* CLIENT LOGIN
* CONTACT
* COMPANY
* SERVICES
* PRODUCTS
* EDUCATION
* BLOG
* Services Overview
* Immunity Adversary Simulation * Application Vulnerability Analysis * Exploit Development & Reverse Engineering * Network Security Assessment * Penetration Testing* Process Review
* Source Code Analysis * Web Application Testing * Wireless Security Assessment* Consultants
* When Choosing a Service Provider* Products Overview
* CANVAS
* CANVAS 3rd Party Products * CANVAS Early Updates* Immunity Debugger
* El Jefe
* Innuendo
* Silica
* Education Overview* Web Hacking
* Linux Kernel Exploitation * Current Class Schedule* Immunity Products
* Immunity Services
COMPANY SERVICES
* Services Overview
* Immunity Adversary Simulation * Application Vulnerability Analysis * Exploit Development & Reverse Engineering * Network Security Assessment * Penetration Testing* Process Review
* Source Code Analysis * Web Application Testing * Wireless Security Assessment* Consultants
* When Choosing a Service ProviderPRODUCTS
* Products Overview
* CANVAS
* CANVAS 3rd Party Products * CANVAS Early Updates* Immunity Debugger
* El Jefe
* Innuendo
* Silica
EDUCATION
* Education Overview* Web Hacking
* Linux Kernel Exploitation * Current Class ScheduleBLOG
* Immunity Products
* Immunity Services
* RESOURCES
* RESELLERS
* PARTNERS
* CAREERS
* CLIENT LOGIN
* CONTACT
EXCLUSIVELY OFFENSE
INFILTRATE
CONFERENCE
TBD 2021
MORE INFORMATION
IMMUNITY IS NOW
PART OF APPGATE
MORE INFORMATION
IMMUNITY
ETHOS
AGGRESSIVE, REAL WORLD APPROACH PROVIDING INDEPENDENT, HAND-CRAFTED SOLUTIONS FOR CONTINUOUS AND EVOLVING SECURITY THREATSMORE INFORMATION
INNUENDO
AN ADVANCED PENETRATION TESTING TOOL FOR MODELING ADVANCED ATTACKERS FOR PENETRATION TESTERS AND SECURITY PROFESSIONALS WORLDWIDE.MORE INFORMATION
CANVAS
ADVANCED PENETRATION TESTING A TRUSTED SECURITY ASSESSMENT TOOL THAT ALLOWS PENETRATION TESTING AND HOSTILE ATTACK SIMULATIONS TO BE CONDUCTED BY SECURITY PROFESSIONALS.MORE INFORMATION
KNOWING YOU'RE SECURE INTELLIGENT SECURITY ANALYSIS WHAT SETS IMMUNITY APART FROM OTHER SECURITY CONSULTING FIRMS? Since 2002 IMMUNITY has been a specialized, detail-oriented security provider, with only top-tier security experts on staff. IMMUNITY draws from this vast knowledge and diverse skill sets to analyze all potential vulnerabilities - both known and unknown. Because of IMMUNITY's focus on offensive techniques, we are able to mimic the skill-set of a genuine threat. IMMUNITY prides itself on demonstrating the TRUE risk that a vulnerability poses to an organization. IMMUNITY works hard to show exactly how far and how deep an attacker can go with a single discovered vulnerability. Going beyond just a risk score and theoretical attacks. IMMUNITY SERVICES LLC OFFERS A COMPREHENSIVE RANGE OF CONSULTING SERVICES TO HELP IDENTIFY AND PROTECT YOUR BUSINESS FROM SECURITYTHREATS SUCH AS:
* Immunity Adversary Simulation * Application Vulnerability Assessment * Architecture Review * Exploit Development * External Information Risk and Assessment * IDS & IPS Performance Testing * Network Security Assessment * Penetration Testing * Reverse Engineering * Social Engineering Assessment * Source Code Analysis * Telephony/VOIP Assessment * Wireless Security AssessmentEMERGENCY RESPONSE
HAVE YOU BEEN COMPROMISED? No attack is too advanced or persistent for us. Contact us now to minimize damage and avoid becoming a headline.CONTACT US
LATEST IN
IMMUNITYMEDIA
__TWITTER
__VIDEOS
__PRODUCT
BLOG
__SERVICES
BLOG
Check out our demonstration of chaining the ie_mshtml_doublefree clientside exploit with the wndextra_oob_lpe explo… https://t.co/BbOhGWrGc8@Immunityinc May 20 New CANVAS 7.29 release is OUT! It includes 3 new exploits, two of them can be chained together to go from client… https://t.co/NTFjgl3lkO@Immunityinc May 14 CANVAS 7.28 Release - Check it out! https://t.co/ExaN2uQClO Includes: local privilege escalation exploits targetin… https://t.co/Ekp814Rwg2@Immunityinc Apr 2 Check out Immunity's blog post: Misconfigurations in Java XML Parsers by Anibal Irrera https://t.co/GgOelHfTm8@Immunityinc Feb 17Immunity Videos
Fri, 14 May 2021
Immunity Videos
Wed, 21 Apr 2021
Immunity Videos
Fri, 16 Apr 2021
Immunity Videos
Fri, 20 Nov 2020
Recent
kernel memory disclosure bugs in CANVAS In July 2017, a blogpost from Anders Fogh introduced the idea of leaking kernel memory from the unprivileged userland. This was laterfollow...
Tue, 13 Nov 2018
A few notes about the exploitation of CVE-2017-3623 (aka EBBISLAND) on Solaris 10 (x86/amd64)The advisory CVE-2017-3623 i...Mon, 10 Jul 2017
INNUENDO
RPC: shell
This is the third installment of this series. Here are links for the first and second. For this post we're going to take a look at theimple...
Wed, 14 Dec 2016
Leveraging
INNUENDO's RPC for Fun and Profit: tagging For the second installment of this series (see the previous here), we're going to take a look at the new tagging functionality that wasadde...
Fri, 09 Sep 2016
Misconfigurations
in Java XML Parsers
Misconfigurations in Java XML ParsersXML is a powerful data format that can elegantly encapsulate any conceivable kind of information....Wed, 17 Feb 2021
PHPMyAdmin
3.5.X-3.5.8 Reflected XSS: What could have been, but really wasn't. (This blog post is from Leff (Lautaro Fain), one of our consultants, and I asked him to do a special project, as documented below.)1.Introd...
Wed, 06 Feb 2019
Solving
Sokohashv2.0 full of Angr on Ekoparty 2016 In memory of Pocho, the Panther. RIP buddy.Last Ekoparty I got the chance to try my luck solving one of Core Security challenges. For awhil...
Wed, 02 Nov 2016
Strategic
Recommendations and Bug Bounties I have so many feelings about bug bounties. First of all, bug bounties turn your penetration testing program into a hilarious cross between...
Tue, 05 Jul 2016
Visit @immunityinc on Twitter IMMUNITY INC SECURES BOTH GOVERNMENT & COMMERCIAL contact us HEADQUARTERS 2751 N. Miami Ave. Suite #7 Miami FL 33127 * Email: sales@immunityinc.com * Phone: +1 786.220.0600 �CANVAS, ®SILICA, ®Innuendo, ®El Jefe, ®Immunity, and �Infiltrate are all registered trademarks of Immunity Inc. � 2020 Immunity Inc. All rights reserved Privacy Policy | Cookie Policy | Terms of Use PRIVACY PREFERENCE CENTER*
YOUR PRIVACY
*
TARGETING COOKIES
*
STRICTLY NECESSARY COOKIES*
FUNCTIONAL COOKIES
*
PERFORMANCE COOKIES
YOUR PRIVACY
When you visit any website, it may store or retrieve information on your browser, mostly in the form of cookies. This information might be about you, your preferences or your device and is mostly used to make the site work as you expect it to. The information does not usually directly identify you, but it can give you a more personalized web experience. Because we respect your right to privacy, you can choose not to allow some types of cookies. Click on the different category headings to find out more and change our default settings. However, blocking some types of cookies may impact your experience of the site and the services we are able to offer.TARGETING COOKIES
Always Active
These cookies may be set through our site by our advertising partners. They may be used by those companies to build a profile of your interests and show you relevant adverts on other sites. They do not store directly personal information, but are based on uniquely identifying your browser and internet device. If you do not allow these cookies, you will experience less targeted advertising. STRICTLY NECESSARY COOKIESAlways Active
These cookies are necessary for the website to function and cannot be switched off in our systems. They are usually only set in response to actions made by you which amount to a request for services, such as setting your privacy preferences, logging in or filling in forms. You can set your browser to block or alert you about these cookies, but some parts of the site will not then work. These cookies do not store any personally identifiable information.FUNCTIONAL COOKIES
Always Active
These cookies enable the website to provide enhanced functionality and personalisation. They may be set by us or by third party providers whose services we have added to our pages. If you do not allow these cookies then some or all of these services may not function properly.PERFORMANCE COOKIES
Always Active
These cookies allow us to count visits and traffic sources so we can measure and improve the performance of our site. They help us to know which pages are the most and least popular and see how visitors move around the site. All information these cookies collect is aggregated and therefore anonymous. If you do not allow these cookies we will not know when you have visited our site, and will not be able to monitorits performance.
BACK BUTTON BACK
Vendor Search
Filter Button
Consent Leg.Interest checkbox label label checkbox label label checkbox label labelClear
checkbox label labelApply Cancel
Confirm My Choices
Allow All
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0