Are you over 18 and want to see adult content?
More Annotations

A complete backup of mgronline.com/local/detail/9630000015200
Are you over 18 and want to see adult content?

A complete backup of news.abplive.com/entertainment/television/bigg-boss-13-asim-riaz-for-the-win-gauahar-khan-picks-her-winner-
Are you over 18 and want to see adult content?

A complete backup of www.iltempo.it/cultura-spettacoli/2020/02/15/news/grande-fratello-vip-4-nomination-serena-enardu-pago-ferna
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of gainesvillecoins.com
Are you over 18 and want to see adult content?

A complete backup of closertotruth.com
Are you over 18 and want to see adult content?
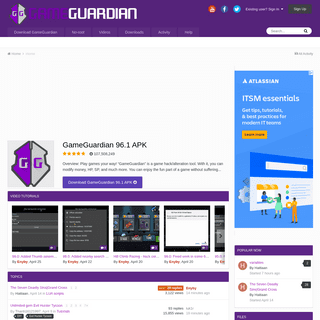
A complete backup of gameguardian.net
Are you over 18 and want to see adult content?
Text
DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. AN OBJECTION TO THE ECOSYSTEM IS MOVING Daniel Gultsch An Objection to ‘The ecosystem is moving’ In May 2016 Moxie Marlinspike published an article on his company’s blog entitled ‘Reflections: The ecosystem is moving’ where he claims that federated systems are ‘stuck in time’. Since then his blog post has been passed around primarily to support the argument that federated, XMPP based, instant messaging is not working MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. XEP-XXXX: USER AVATAR TO VCARD-BASED AVATARS CONVERSION 1. Introduction. User Avatar (XEP-0084) and vCard-Based Avatars (XEP-0153) are usually considered to stand in competition with each other. XEP-0084 even talks about superseeding XEP-0153 in the future. While XEP-0084 provides a more efficient interface to upload avatars by seperating meta data and data (thus saving the client from having to download its own avatar on every connect) it GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster. CONVERSE.JS LEAKING INFORMATION ABOUT WHICH ROOMS ARE Converse.js leaking information about which rooms are bookmarked. CVE-2018-6591: When storing bookmarks on the server Converse.js does not properly configure the access model to be private. Introduction. The Personal Eventnig Protocol (PEP) is a commonly used extension (XEP) for XMPP. It is a subset of the more powerful Publish-Subscribe (XEP-0060), operating on the user’s account. XEP-0060: PUBLISH-SUBSCRIBE This specification defines an XMPP protocol extension for generic publish-subscribe functionality. The protocol enables XMPP entities to create nodes (topics) at a pubsub service and publish information at those nodes; an event notification (with or without payload) is then broadcasted to all entities that have subscribed to the node. Pubsub therefore adheres to the classic Observer designDANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster.DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. XEP-XXXX: USER AVATAR TO VCARD-BASED AVATARS CONVERSION 1. Introduction. User Avatar (XEP-0084) and vCard-Based Avatars (XEP-0153) are usually considered to stand in competition with each other. XEP-0084 even talks about superseeding XEP-0153 in the future. While XEP-0084 provides a more efficient interface to upload avatars by seperating meta data and data (thus saving the client from having to download its own avatar on every connect) it AN OBJECTION TO THE ECOSYSTEM IS MOVING Daniel Gultsch An Objection to ‘The ecosystem is moving’ In May 2016 Moxie Marlinspike published an article on his company’s blog entitled ‘Reflections: The ecosystem is moving’ where he claims that federated systems are ‘stuck in time’. Since then his blog post has been passed around primarily to support the argument that federated, XMPP based, instant messaging is not working MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. XEP-0363: HTTP FILE UPLOAD 8.1 Server side¶. Note: This section is not normative; it may be updated when general web security recommendations change in the future. It is recommended to run the HTTP upload domain used for GET requests in appropriate isolation from other HTTP based services to avoid user-generated, malicious scripts to be executed in the contextof said services.
CONVERSE.JS LEAKING INFORMATION ABOUT WHICH ROOMS ARE Converse.js leaking information about which rooms are bookmarked. CVE-2018-6591: When storing bookmarks on the server Converse.js does not properly configure the access model to be private. Introduction. The Personal Eventnig Protocol (PEP) is a commonly used extension (XEP) for XMPP. It is a subset of the more powerful Publish-Subscribe (XEP-0060), operating on the user’s account. XEP-0060: PUBLISH-SUBSCRIBE This specification defines an XMPP protocol extension for generic publish-subscribe functionality. The protocol enables XMPP entities to create nodes (topics) at a pubsub service and publish information at those nodes; an event notification (with or without payload) is then broadcasted to all entities that have subscribed to the node. Pubsub therefore adheres to the classic Observer designDANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster.DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. XEP-XXXX: USER AVATAR TO VCARD-BASED AVATARS CONVERSION 1. Introduction. User Avatar (XEP-0084) and vCard-Based Avatars (XEP-0153) are usually considered to stand in competition with each other. XEP-0084 even talks about superseeding XEP-0153 in the future. While XEP-0084 provides a more efficient interface to upload avatars by seperating meta data and data (thus saving the client from having to download its own avatar on every connect) it MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. AN OBJECTION TO THE ECOSYSTEM IS MOVING Daniel Gultsch An Objection to ‘The ecosystem is moving’ In May 2016 Moxie Marlinspike published an article on his company’s blog entitled ‘Reflections: The ecosystem is moving’ where he claims that federated systems are ‘stuck in time’. Since then his blog post has been passed around primarily to support the argument that federated, XMPP based, instant messaging is not working XEP-0363: HTTP FILE UPLOAD 8.1 Server side¶. Note: This section is not normative; it may be updated when general web security recommendations change in the future. It is recommended to run the HTTP upload domain used for GET requests in appropriate isolation from other HTTP based services to avoid user-generated, malicious scripts to be executed in the contextof said services.
CONVERSE.JS LEAKING INFORMATION ABOUT WHICH ROOMS ARE Converse.js leaking information about which rooms are bookmarked. CVE-2018-6591: When storing bookmarks on the server Converse.js does not properly configure the access model to be private. Introduction. The Personal Eventnig Protocol (PEP) is a commonly used extension (XEP) for XMPP. It is a subset of the more powerful Publish-Subscribe (XEP-0060), operating on the user’s account. XEP-0060: PUBLISH-SUBSCRIBE This specification defines an XMPP protocol extension for generic publish-subscribe functionality. The protocol enables XMPP entities to create nodes (topics) at a pubsub service and publish information at those nodes; an event notification (with or without payload) is then broadcasted to all entities that have subscribed to the node. Pubsub therefore adheres to the classic Observer designDANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster.DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. XEP-XXXX: USER AVATAR TO VCARD-BASED AVATARS CONVERSION 1. Introduction. User Avatar (XEP-0084) and vCard-Based Avatars (XEP-0153) are usually considered to stand in competition with each other. XEP-0084 even talks about superseeding XEP-0153 in the future. While XEP-0084 provides a more efficient interface to upload avatars by seperating meta data and data (thus saving the client from having to download its own avatar on every connect) it AN OBJECTION TO THE ECOSYSTEM IS MOVING Daniel Gultsch An Objection to ‘The ecosystem is moving’ In May 2016 Moxie Marlinspike published an article on his company’s blog entitled ‘Reflections: The ecosystem is moving’ where he claims that federated systems are ‘stuck in time’. Since then his blog post has been passed around primarily to support the argument that federated, XMPP based, instant messaging is not working XEP-0384: OMEMO ENCRYPTION Device A communication end point, i.e. a specific client instance OMEMO element An element in the urn:xmpp:omemo:1 namespace Bundle A collection of publicly accessible data used by the X3DH key exchange that can be used to build a session with a device, namely its public IdentityKey, a signed PreKey with corresponding signature, and a list of (single use) PreKeys. XEP-0363: HTTP FILE UPLOAD 8.1 Server side¶. Note: This section is not normative; it may be updated when general web security recommendations change in the future. It is recommended to run the HTTP upload domain used for GET requests in appropriate isolation from other HTTP based services to avoid user-generated, malicious scripts to be executed in the contextof said services.
CONVERSE.JS LEAKING INFORMATION ABOUT WHICH ROOMS ARE Converse.js leaking information about which rooms are bookmarked. CVE-2018-6591: When storing bookmarks on the server Converse.js does not properly configure the access model to be private. Introduction. The Personal Eventnig Protocol (PEP) is a commonly used extension (XEP) for XMPP. It is a subset of the more powerful Publish-Subscribe (XEP-0060), operating on the user’s account. XEP-0060: PUBLISH-SUBSCRIBE This specification defines an XMPP protocol extension for generic publish-subscribe functionality. The protocol enables XMPP entities to create nodes (topics) at a pubsub service and publish information at those nodes; an event notification (with or without payload) is then broadcasted to all entities that have subscribed to the node. Pubsub therefore adheres to the classic Observer designDANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. AN OBJECTION TO THE ECOSYSTEM IS MOVING Daniel Gultsch An Objection to ‘The ecosystem is moving’ In May 2016 Moxie Marlinspike published an article on his company’s blog entitled ‘Reflections: The ecosystem is moving’ where he claims that federated systems are ‘stuck in time’. Since then his blog post has been passed around primarily to support the argument that federated, XMPP based, instant messaging is not working XEP-0384: OMEMO ENCRYPTION Device A communication end point, i.e. a specific client instance OMEMO element An element in the urn:xmpp:omemo:1 namespace Bundle A collection of publicly accessible data used by the X3DH key exchange that can be used to build a session with a device, namely its public IdentityKey, a signed PreKey with corresponding signature, and a list of (single use) PreKeys. GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster. THE STATE OF MOBILE XMPP IN 2016 The State of Mobile XMPP in 2016. XMPP is not suited for mobile devices. That’s a myth that has been around for ages. It is mostly spread by people who want to sell you their own proprietary instantmessaging solution.
CONVERSE.JS LEAKING INFORMATION ABOUT WHICH ROOMS ARE Converse.js leaking information about which rooms are bookmarked. CVE-2018-6591: When storing bookmarks on the server Converse.js does not properly configure the access model to be private. Introduction. The Personal Eventnig Protocol (PEP) is a commonly used extension (XEP) for XMPP. It is a subset of the more powerful Publish-Subscribe (XEP-0060), operating on the user’s account. XEP-0060: PUBLISH-SUBSCRIBE This specification defines an XMPP protocol extension for generic publish-subscribe functionality. The protocol enables XMPP entities to create nodes (topics) at a pubsub service and publish information at those nodes; an event notification (with or without payload) is then broadcasted to all entities that have subscribed to the node. Pubsub therefore adheres to the classic Observer designDANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. AN OBJECTION TO THE ECOSYSTEM IS MOVING Daniel Gultsch An Objection to ‘The ecosystem is moving’ In May 2016 Moxie Marlinspike published an article on his company’s blog entitled ‘Reflections: The ecosystem is moving’ where he claims that federated systems are ‘stuck in time’. Since then his blog post has been passed around primarily to support the argument that federated, XMPP based, instant messaging is not working GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Daniel Gultsch, 2015/12/20. Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim.She has her boyfriend Bob (bob@siacs.eu) saved under Bob in her roster. Gajim shows Bob’s JID only in the XEP-0384: OMEMO ENCRYPTION Device A communication end point, i.e. a specific client instance OMEMO element An element in the urn:xmpp:omemo:1 namespace Bundle A collection of publicly accessible data used by the X3DH key exchange that can be used to build a session with a device, namely its public IdentityKey, a signed PreKey with corresponding signature, and a list of (single use) PreKeys. THE STATE OF MOBILE XMPP IN 2016 The State of Mobile XMPP in 2016. XMPP is not suited for mobile devices. That’s a myth that has been around for ages. It is mostly spread by people who want to sell you their own proprietary instantmessaging solution.
CONVERSE.JS LEAKING INFORMATION ABOUT WHICH ROOMS ARE Converse.js leaking information about which rooms are bookmarked. CVE-2018-6591: When storing bookmarks on the server Converse.js does not properly configure the access model to be private. Introduction. The Personal Eventnig Protocol (PEP) is a commonly used extension (XEP) for XMPP. It is a subset of the more powerful Publish-Subscribe (XEP-0060), operating on the user’s account. XEP-0060: PUBLISH-SUBSCRIBE This specification defines an XMPP protocol extension for generic publish-subscribe functionality. The protocol enables XMPP entities to create nodes (topics) at a pubsub service and publish information at those nodes; an event notification (with or without payload) is then broadcasted to all entities that have subscribed to the node. Pubsub therefore adheres to the classic Observer designDANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster.DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. AN OBJECTION TO THE ECOSYSTEM IS MOVING Daniel Gultsch An Objection to ‘The ecosystem is moving’ In May 2016 Moxie Marlinspike published an article on his company’s blog entitled ‘Reflections: The ecosystem is moving’ where he claims that federated systems are ‘stuck in time’. Since then his blog post has been passed around primarily to support the argument that federated, XMPP based, instant messaging is not working XEP-0384: OMEMO ENCRYPTION Device A communication end point, i.e. a specific client instance OMEMO element An element in the urn:xmpp:omemo:1 namespace Bundle A collection of publicly accessible data used by the X3DH key exchange that can be used to build a session with a device, namely its public IdentityKey, a signed PreKey with corresponding signature, and a list of (single use) PreKeys. MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. XEP-0363: HTTP FILE UPLOAD 8.1 Server side¶. Note: This section is not normative; it may be updated when general web security recommendations change in the future. It is recommended to run the HTTP upload domain used for GET requests in appropriate isolation from other HTTP based services to avoid user-generated, malicious scripts to be executed in the contextof said services.
CONVERSE.JS LEAKING INFORMATION ABOUT WHICH ROOMS ARE Converse.js leaking information about which rooms are bookmarked. CVE-2018-6591: When storing bookmarks on the server Converse.js does not properly configure the access model to be private. Introduction. The Personal Eventnig Protocol (PEP) is a commonly used extension (XEP) for XMPP. It is a subset of the more powerful Publish-Subscribe (XEP-0060), operating on the user’s account. XEP-0060: PUBLISH-SUBSCRIBE This specification defines an XMPP protocol extension for generic publish-subscribe functionality. The protocol enables XMPP entities to create nodes (topics) at a pubsub service and publish information at those nodes; an event notification (with or without payload) is then broadcasted to all entities that have subscribed to the node. Pubsub therefore adheres to the classic Observer designDANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster.DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. AN OBJECTION TO THE ECOSYSTEM IS MOVING Daniel Gultsch An Objection to ‘The ecosystem is moving’ In May 2016 Moxie Marlinspike published an article on his company’s blog entitled ‘Reflections: The ecosystem is moving’ where he claims that federated systems are ‘stuck in time’. Since then his blog post has been passed around primarily to support the argument that federated, XMPP based, instant messaging is not working XEP-0384: OMEMO ENCRYPTION Device A communication end point, i.e. a specific client instance OMEMO element An element in the urn:xmpp:omemo:1 namespace Bundle A collection of publicly accessible data used by the X3DH key exchange that can be used to build a session with a device, namely its public IdentityKey, a signed PreKey with corresponding signature, and a list of (single use) PreKeys. MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. XEP-0363: HTTP FILE UPLOAD 8.1 Server side¶. Note: This section is not normative; it may be updated when general web security recommendations change in the future. It is recommended to run the HTTP upload domain used for GET requests in appropriate isolation from other HTTP based services to avoid user-generated, malicious scripts to be executed in the contextof said services.
CONVERSE.JS LEAKING INFORMATION ABOUT WHICH ROOMS ARE Converse.js leaking information about which rooms are bookmarked. CVE-2018-6591: When storing bookmarks on the server Converse.js does not properly configure the access model to be private. Introduction. The Personal Eventnig Protocol (PEP) is a commonly used extension (XEP) for XMPP. It is a subset of the more powerful Publish-Subscribe (XEP-0060), operating on the user’s account. XEP-0060: PUBLISH-SUBSCRIBE This specification defines an XMPP protocol extension for generic publish-subscribe functionality. The protocol enables XMPP entities to create nodes (topics) at a pubsub service and publish information at those nodes; an event notification (with or without payload) is then broadcasted to all entities that have subscribed to the node. Pubsub therefore adheres to the classic Observer designDANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster.DANIEL GULTSCH
Daniel Gultsch Recent Projects Software. Conversations - an encrypted, mobile friendly XMPP client for Android; XMPP Compliance Tester - checks a given server for compatibility with the compliance levels defined in XEP-0387; XMPP Server Status - Status page and uptime monitor for XMPP servers; Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages BLIND TRUST BEFORE VERIFICATION An introduction to the concept of Blind Trust Before Verification which means to automatically trust all new devices of contacts that haven’t been verified before, and prompt for manual confirmation each time a verified contact adds a new device. DONATIONS - GULTSCH.DE Bank transfer. Europe / SEPA Account holder: Daniel Gultsch IBAN: BE48 9670 1388 6827 BIC: TRWIBEB1XXX USA Account holder: Daniel Gultsch Account number: 8310383171 CONVERSATIONS: A MISSION STATEMENT Daniel Gultsch Conversations: A Mission Statement. Conversations is a messenger for the next decade. Based on already established internet standards that have been around for over ten years Conversations isn’t trying to replace current commercial messengers. THE ROCKY ROAD TO OMEMO BY DEFAULT The rocky road to OMEMO by default Why it took us more than two years to enable End-to-End encryption by default: The first in a series of essays leading up to the release of Conversations 2.0 A PATHWAY TO A WELL REGULATED INSTANT MESSAGING MARKET Daniel Gultsch A pathway to a well regulated instant messaging market. For the last couple of years I have been consulting and doing contract work for various instant messaging companies. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility.OMEMO - GULTSCH
OMEMO. Daniel Gultsch. December 8th 2016 @ XMPP Security Meetup London. Crypto features. Forwared secrecy; Authenticity (Deniability) Security in general and end-to-end encryption in particular is alwaysa tradeoff.
HERE LIES THE SLIDING PANE LAYOUT. RIP Here lies the Sliding Pane Layout. RIP A justification for some of the design choices I made; The second part in a series of essays leading up the release of Conversations 2.0 GAJIM ROSTER PUSH AND MESSAGE INTERCEPTION Gajim Roster Push Attack / Message Interception. CVE-2015-8688: Gajim doesn’t verify the origin of roster pushes thus allowing third parties to modify the roster. Alice is using the latest version of Gajim (0.16.4) and logged in as alice@siacs.eu/Gajim. She has her boyfriend Bob ( bob@siacs.eu) saved under Bob in her roster. XEP-XXXX: OMEMO ENCRYPTION 1.1 Motivation. There are two main end-to-end encryption schemes in common use in the XMPP ecosystem, Off-the-Record (OTR) messaging (Current Off-the-Record Messaging Usage (XEP-0364) ) and OpenPGP (Current Jabber OpenPGP Usage (XEP-0027) ).OTR has significant usability drawbacks for inter-client mobility. AN OBJECTION TO THE ECOSYSTEM IS MOVING Daniel Gultsch An Objection to ‘The ecosystem is moving’ In May 2016 Moxie Marlinspike published an article on his company’s blog entitled ‘Reflections: The ecosystem is moving’ where he claims that federated systems are ‘stuck in time’. Since then his blog post has been passed around primarily to support the argument that federated, XMPP based, instant messaging is not working XEP-0384: OMEMO ENCRYPTION Device A communication end point, i.e. a specific client instance OMEMO element An element in the urn:xmpp:omemo:1 namespace Bundle A collection of publicly accessible data used by the X3DH key exchange that can be used to build a session with a device, namely its public IdentityKey, a signed PreKey with corresponding signature, and a list of (single use) PreKeys. MULTIPLE VULNERABILITIES FOUND IN DINO Multiple Vulnerabilities found in Dino. CVE-2019-16235+: Missing or incorrect sender validations in Dino allow an attacker to spoof messages and inject or remove entries from the user’s roster. Introduction. Dino is a Jabber/XMPP client written in Vala and GTK. On September 10th 2019, while chatting on a public channel, a number of vulnerabilities were discovered in Dino. XEP-0363: HTTP FILE UPLOAD 8.1 Server side¶. Note: This section is not normative; it may be updated when general web security recommendations change in the future. It is recommended to run the HTTP upload domain used for GET requests in appropriate isolation from other HTTP based services to avoid user-generated, malicious scripts to be executed in the contextof said services.
CONVERSE.JS LEAKING INFORMATION ABOUT WHICH ROOMS ARE Converse.js leaking information about which rooms are bookmarked. CVE-2018-6591: When storing bookmarks on the server Converse.js does not properly configure the access model to be private. Introduction. The Personal Eventnig Protocol (PEP) is a commonly used extension (XEP) for XMPP. It is a subset of the more powerful Publish-Subscribe (XEP-0060), operating on the user’s account. XEP-0060: PUBLISH-SUBSCRIBE This specification defines an XMPP protocol extension for generic publish-subscribe functionality. The protocol enables XMPP entities to create nodes (topics) at a pubsub service and publish information at those nodes; an event notification (with or without payload) is then broadcasted to all entities that have subscribed to the node. Pubsub therefore adheres to the classic Observer designDANIEL GULTSCH
RECENT PROJECTS
SOFTWARE
* Conversations - an encrypted, mobile friendly XMPP client for Android * XMPP Compliance Tester- checks a given
server for compatibility with the compliance levels defined inXEP-0387
* XMPP Server Status - Status page and uptime monitor for XMPP servers * Conversations Push Proxy - An XEP-0357: Push Notifications app server that relays push messages between the user’s server and Googles Firebase Cloud Messaging. * Java JMAP library - A Java library for the JSON Meta Application Protocol and Ltt.rs a Proof of concept Email client for Android.SECURITY
* CVE-2015-8688 :
Gajim Roster Push Attack / Message Interception * CVE-2018-6591 : Converse.js leaking information about which rooms are bookmarked * CVE-2019-16235+ : Multiple Vulnerabilitiesfound in Dino
STANDARDIZATION
* OMEMO Multi-End Message andObject Encryption
* HTTP File Upload
* User Avatar to vCard-Based Avatars ConversionESSAYS
* Conversations: A Mission Statement * The State of Mobile XMPP in 2016 * Blind Trust Before Verification * An Objection to ‘The ecosystem is moving’ * A series leading up the release of Conversations 2.0 * The rocky road to OMEMO by default * Here lies the Sliding Pane Layout. RIP * A pathway to a well regulated instant messaging marketTALKS
* Jabber/XMPP: Instant Messaging selber in die Hand nehmen @ MRMCD 2017 (German)DONATIONS
If you like my work you can support me financially (via Liberapay, Github Sponsors, bank transfer, …). COMMERCIAL PRODUCTS & SERVICES* XMPP Consulting
* Server setup - get your own XMPP server up and running * conversations.im - an XMPP provider that also offers Domain Hosting _If you are interested in any of these services or products do not hesitate to contact me._CONTACT
* daniel@gultsch.de (e-mail & xmpp )* Github
* pgp.pub.asc
2C93 2578 ED08 1860 2179 023A F43D 18AD 2A09 82C2 _When contacting me on XMPP please don’t just send a subscription request but start messaging me directly. I won’t blindly accept subscription requests from strangers._Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0