Are you over 18 and want to see adult content?
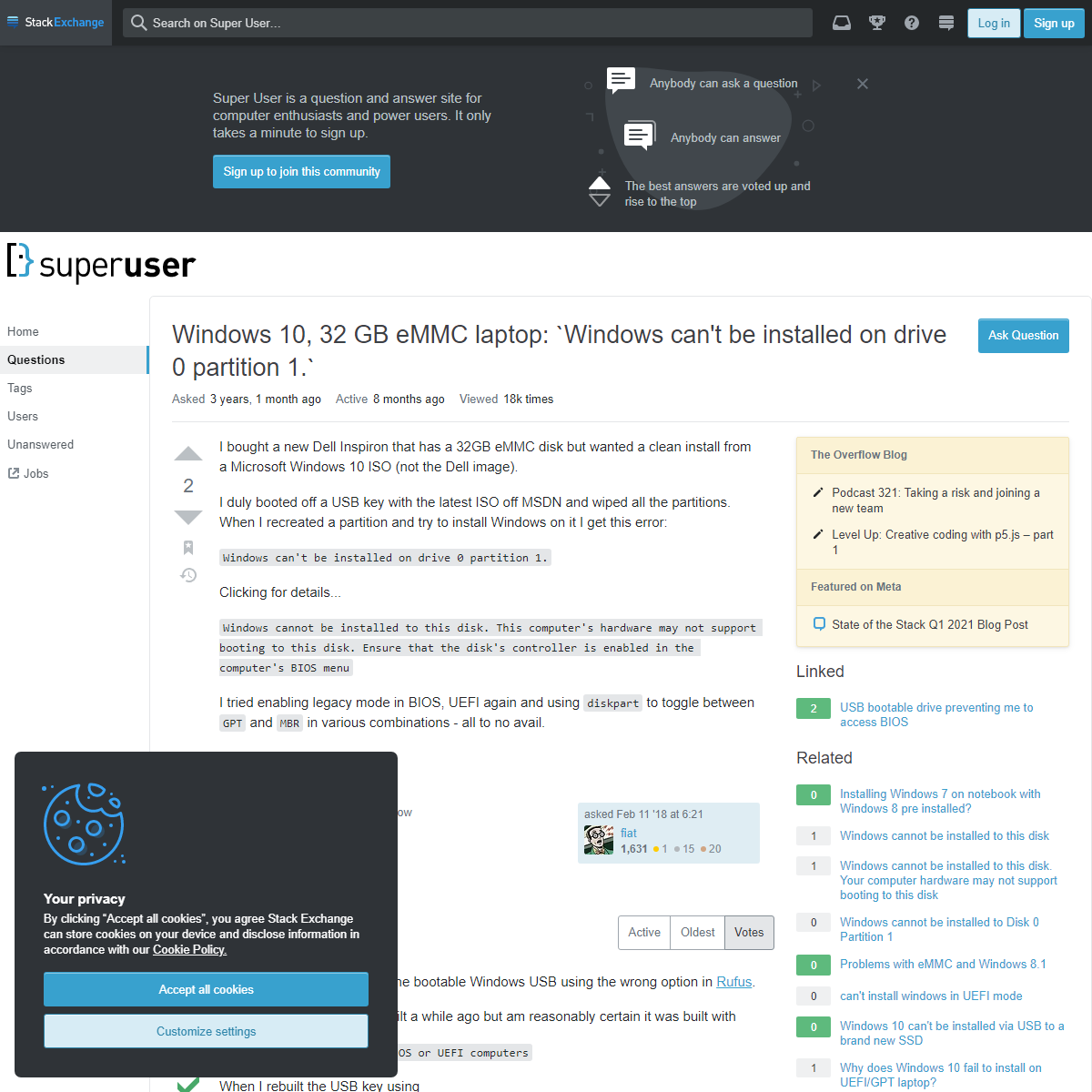
More Annotations

A complete backup of https://www.creta.gr/company/karantinou-pepi/9922
Are you over 18 and want to see adult content?
A complete backup of https://libros.plus/chomsky-esencial/
Are you over 18 and want to see adult content?
A complete backup of https://minuet.biz/ukraine/kiev/9362/ru/
Are you over 18 and want to see adult content?
A complete backup of https://www.kaufmich.com/Wiebke1989
Are you over 18 and want to see adult content?
A complete backup of http://matka.cc/
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://noppies.com
Are you over 18 and want to see adult content?

A complete backup of https://riversidemedicalclinic.com
Are you over 18 and want to see adult content?

A complete backup of https://flyclipart.com
Are you over 18 and want to see adult content?
A complete backup of https://isportsystem.cz
Are you over 18 and want to see adult content?
A complete backup of https://ad-satour.com
Are you over 18 and want to see adult content?

A complete backup of https://wordlidvancnv.nl
Are you over 18 and want to see adult content?
A complete backup of https://progreport.com
Are you over 18 and want to see adult content?
A complete backup of https://libranet.com
Are you over 18 and want to see adult content?

A complete backup of https://presspage.com
Are you over 18 and want to see adult content?
A complete backup of https://diabetesnsw.com.au
Are you over 18 and want to see adult content?
A complete backup of https://unlimited144.com
Are you over 18 and want to see adult content?

A complete backup of https://winstonswish.org
Are you over 18 and want to see adult content?
Text
phishing.”.
HOW CAN PHISHING AFFECT A BUSINESS?ABOUT SEBDB
The challenge faced by security professionals. You face a complex challenge as a security professional. You’re tasked with changing behaviour linked to security risks. The links between security behaviours and risks are not always clear. It’s hard to know which interventions to apply. It’s harder still to explain how interventions reduceWELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. 3 CAUSES OF CYBER ATTACKS 3. Assessing risk. Criminals want us to underestimate the risk of cyber attacks. The more we underestimate, the easier things are for them. Unfortunately, everyone’s ability to calculate risk is poor! Take the example of car accidents and plane crashes. Statistically, flying is far safer than driving. SIX SECURITY ESSENTIALS FOR THOSE WORKING FROM HOME 1. Use company-approved devices. Mental blueprints dictate how we behave in any given situation. Our blueprints might prompt us to use personal laptops when working from home – but that’s rarely a good idea. Most companies fit laptops and devices with inconspicuous defences that improve their security. Plus, devices are portals todata.
7 REASONS WHY SECURITY AWARENESS TRAINING IS IMPORTANT Here are 7 reasons. 1. To prevent breaches and attacks. Starting with the most obvious, security awareness training helps prevent breaches. The precise number of breaches security awareness training prevents is difficult to quantify. In an ideal world, we’d be able to run a controlled trial comparing those who received training and those who LET’S PUNISH PHISHING VICTIMS… ER, YOU WANT TO DO WHAT Why it makes little sense to punish phishing victims. Going a step further, punishing those who misdiagnose simulated phishing emails can cultivate a culture of fear. Think about that for a second: A culture of fear. Fear is a massive hindrance. Fear is why a “Sam” in marketing is yet to report the fact he inadvertently introducedmalware
HOW TO IDENTIFY A PHISHING EMAIL Step 5: Check the sender details. Checking the sender details isn’t foolproof. Email accounts can be hacked and sender details can be spoofed. But, for the most part, it’s possible to identify phishing emails as fraudulent by scrutinising the senders’ details. Emails that claim to be from companies such as Apple might be sent fromdomains
FOUR DIFFERENT TYPES OF SECURITY AWARENESS TRAINING CYBSAFE – UNDERSTAND PEOPLE. PREVENT SECURITY INCIDENTS.WHY CYBSAFEPRODUCTSSEBDBCUSTOMERSPARTNERSCOMPANY It gives us really robust metrics that help us measure where our people are. It shows their behaviours as well as their attitudes.”. “CybSafe has allowed us to identify changes in security behaviour and respond accordingly. We now see and understand aspects of our human cyber risk that we simply couldn’t get from training &phishing.”.
HOW CAN PHISHING AFFECT A BUSINESS?ABOUT SEBDB
The challenge faced by security professionals. You face a complex challenge as a security professional. You’re tasked with changing behaviour linked to security risks. The links between security behaviours and risks are not always clear. It’s hard to know which interventions to apply. It’s harder still to explain how interventions reduceWELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. 3 CAUSES OF CYBER ATTACKS 3. Assessing risk. Criminals want us to underestimate the risk of cyber attacks. The more we underestimate, the easier things are for them. Unfortunately, everyone’s ability to calculate risk is poor! Take the example of car accidents and plane crashes. Statistically, flying is far safer than driving. SIX SECURITY ESSENTIALS FOR THOSE WORKING FROM HOME 1. Use company-approved devices. Mental blueprints dictate how we behave in any given situation. Our blueprints might prompt us to use personal laptops when working from home – but that’s rarely a good idea. Most companies fit laptops and devices with inconspicuous defences that improve their security. Plus, devices are portals todata.
7 REASONS WHY SECURITY AWARENESS TRAINING IS IMPORTANT Here are 7 reasons. 1. To prevent breaches and attacks. Starting with the most obvious, security awareness training helps prevent breaches. The precise number of breaches security awareness training prevents is difficult to quantify. In an ideal world, we’d be able to run a controlled trial comparing those who received training and those who LET’S PUNISH PHISHING VICTIMS… ER, YOU WANT TO DO WHAT Why it makes little sense to punish phishing victims. Going a step further, punishing those who misdiagnose simulated phishing emails can cultivate a culture of fear. Think about that for a second: A culture of fear. Fear is a massive hindrance. Fear is why a “Sam” in marketing is yet to report the fact he inadvertently introducedmalware
HOW TO IDENTIFY A PHISHING EMAIL Step 5: Check the sender details. Checking the sender details isn’t foolproof. Email accounts can be hacked and sender details can be spoofed. But, for the most part, it’s possible to identify phishing emails as fraudulent by scrutinising the senders’ details. Emails that claim to be from companies such as Apple might be sent fromdomains
FOUR DIFFERENT TYPES OF SECURITY AWARENESS TRAININGABOUT CYBSAFE
We are CybSafe. We’re a British cyber security and data analytics company. We build incredible software that makes it easy to manage human cyber risk. We’re on a mission to revolutionise the way society addresses the human aspect of cyber security. Our technology uses science and data to help people when they need it most. In the way that is most effective for them.PRICING – CYBSAFE
Choose the Hub that works for you. CybSafe secures hundreds of organisations around the world. Start making human cyber riskmanagement simple.
WELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes.ALL BEHAVIOURS
Data theft is the intentional stealing of data. Enabling fingerprint or facial login for devices and/or accounts. Reporting security incidents. Blocking pop-ups. Enabling firewalls. Enabling auto-updates. Enabling Google Play Protect. Restricting administrator privileges. Running antivirus if a new icon or desktop pop-up appears. FOUR DIFFERENT TYPES OF SECURITY AWARENESS TRAINING 1. Classroom-based training. 2. Visual aids (including video) 3. Through simulated attacks. 4. Computer-based training. Resource challenges and environmental contexts often force those in security to decide which method or methods to include in awareness campaigns – and in which quantities each should be employed. TEN KEY TOPICS TO COVER IN CYBER SECURITY AWARENESS It should begin by discussing why those taking the training are indeed targets. 2. Preventing identity theft. Identity theft remains the most prevalent form of cybercrime. As such, preventing identity theft is key to any good cyber security awareness training campaign. As well as information on preventing identity theft, cover the warning signs THE ‘ABC’ GUIDE TO IMPROVING INFORMATION SECURITY CybSafe learns individual knowledge levels, behaviour patterns and cultural metrics. It then applies this understanding to protect users online – all the while measuring progress to highlight vulnerabilities, replicate successes and demonstrably reduce human cyber risk. It’s intelligent software that improves informationsecurity ABC.
WHY ARE PHISHING ATTACKS SUCCESSFUL? Fortunately, when you know why phishing attacks are successful, you can begin to reverse the trend – and even use psychology to counter threats such as phishing. CybSafe, for example, is developed in collaboration with psychologists and behavioural scientists. It uses pioneering research from leading academics to ensure people take agenuine
SIMULATED PHISHING EMAILS Occasionally, CybSafe may send you simulated phishing emails. They’re designed to look like real malicious emails used by cyber criminals. These emails are not sent to try and catch you out. ADVANCED SIMULATED PHISHING INFORMATION Tracking Simulated Phishing Emails. CybSafe phishing tracks the "opens" of an email using a unique hidden image pixel to record an open event. This however has some technical limitations: It will vary amongst mail clients and configuration, but if "Automatically download external images" is disabled or blocked, then an open event is notcaptured.
CYBSAFE – UNDERSTAND PEOPLE. PREVENT SECURITY INCIDENTS.WHY CYBSAFEPRODUCTSSEBDBCUSTOMERSPARTNERSCOMPANY It gives us really robust metrics that help us measure where our people are. It shows their behaviours as well as their attitudes.”. “CybSafe has allowed us to identify changes in security behaviour and respond accordingly. We now see and understand aspects of our human cyber risk that we simply couldn’t get from training &phishing.”.
ABOUT CYBSAFE
We are CybSafe. We’re a British cyber security and data analytics company. We build incredible software that makes it easy to manage human cyber risk. We’re on a mission to revolutionise the way society addresses the human aspect of cyber security. Our technology uses science and data to help people when they need it most. In the way that is most effective for them.PRICING – CYBSAFE
Choose the Hub that works for you. CybSafe secures hundreds of organisations around the world. Start making human cyber riskmanagement simple.
HOW CAN PHISHING AFFECT A BUSINESS? LET’S PUNISH PHISHING VICTIMS… ER, YOU WANT TO DO WHAT Why it makes little sense to punish phishing victims. Going a step further, punishing those who misdiagnose simulated phishing emails can cultivate a culture of fear. Think about that for a second: A culture of fear. Fear is a massive hindrance. Fear is why a “Sam” in marketing is yet to report the fact he inadvertently introducedmalware
ABOUT SEBDB
The challenge faced by security professionals. You face a complex challenge as a security professional. You’re tasked with changing behaviour linked to security risks. The links between security behaviours and risks are not always clear. It’s hard to know which interventions to apply. It’s harder still to explain how interventions reduce 3 CAUSES OF CYBER ATTACKS 3. Assessing risk. Criminals want us to underestimate the risk of cyber attacks. The more we underestimate, the easier things are for them. Unfortunately, everyone’s ability to calculate risk is poor! Take the example of car accidents and plane crashes. Statistically, flying is far safer than driving.WELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. HOW TO IDENTIFY A PHISHING EMAIL Step 5: Check the sender details. Checking the sender details isn’t foolproof. Email accounts can be hacked and sender details can be spoofed. But, for the most part, it’s possible to identify phishing emails as fraudulent by scrutinising the senders’ details. Emails that claim to be from companies such as Apple might be sent fromdomains
USING PRIVATE BROWSING WINDOWS Using private browsing windows If workplace devices are shared between colleagues, private browsing should be enabled by default. This means history and cookies are deleted after each session. CYBSAFE – UNDERSTAND PEOPLE. PREVENT SECURITY INCIDENTS.WHY CYBSAFEPRODUCTSSEBDBCUSTOMERSPARTNERSCOMPANY It gives us really robust metrics that help us measure where our people are. It shows their behaviours as well as their attitudes.”. “CybSafe has allowed us to identify changes in security behaviour and respond accordingly. We now see and understand aspects of our human cyber risk that we simply couldn’t get from training &phishing.”.
ABOUT CYBSAFE
We are CybSafe. We’re a British cyber security and data analytics company. We build incredible software that makes it easy to manage human cyber risk. We’re on a mission to revolutionise the way society addresses the human aspect of cyber security. Our technology uses science and data to help people when they need it most. In the way that is most effective for them.PRICING – CYBSAFE
Choose the Hub that works for you. CybSafe secures hundreds of organisations around the world. Start making human cyber riskmanagement simple.
HOW CAN PHISHING AFFECT A BUSINESS? LET’S PUNISH PHISHING VICTIMS… ER, YOU WANT TO DO WHAT Why it makes little sense to punish phishing victims. Going a step further, punishing those who misdiagnose simulated phishing emails can cultivate a culture of fear. Think about that for a second: A culture of fear. Fear is a massive hindrance. Fear is why a “Sam” in marketing is yet to report the fact he inadvertently introducedmalware
ABOUT SEBDB
The challenge faced by security professionals. You face a complex challenge as a security professional. You’re tasked with changing behaviour linked to security risks. The links between security behaviours and risks are not always clear. It’s hard to know which interventions to apply. It’s harder still to explain how interventions reduce 3 CAUSES OF CYBER ATTACKS 3. Assessing risk. Criminals want us to underestimate the risk of cyber attacks. The more we underestimate, the easier things are for them. Unfortunately, everyone’s ability to calculate risk is poor! Take the example of car accidents and plane crashes. Statistically, flying is far safer than driving.WELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. HOW TO IDENTIFY A PHISHING EMAIL Step 5: Check the sender details. Checking the sender details isn’t foolproof. Email accounts can be hacked and sender details can be spoofed. But, for the most part, it’s possible to identify phishing emails as fraudulent by scrutinising the senders’ details. Emails that claim to be from companies such as Apple might be sent fromdomains
USING PRIVATE BROWSING WINDOWS Using private browsing windows If workplace devices are shared between colleagues, private browsing should be enabled by default. This means history and cookies are deleted after each session. CERTIFIED SECURITY AWARENESS TRAINING CybSafe Certified Security Awareness Training is a short, threat-based course that helps develop cyber skills. Contains threat-based modules and separate multi-disciplinary, role-specific content. Short, bite-sized, interactive content. Certified by the UK National Cyber Security Centre (NCSC) & the Chartered Institute of InformationSecurity
WELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. USING PRIVATE BROWSING WINDOWS Using private browsing windows If workplace devices are shared between colleagues, private browsing should be enabled by default. This means history and cookies are deleted after each session. FOUR DIFFERENT TYPES OF SECURITY AWARENESS TRAINING 1. Classroom-based training. 2. Visual aids (including video) 3. Through simulated attacks. 4. Computer-based training. Resource challenges and environmental contexts often force those in security to decide which method or methods to include in awareness campaigns – and in which quantities each should be employed. THE 4 KEY FACTORS FOR A SUCCESSFUL PHISHING SIMULATION A simulated phishing campaign needs to be communicated clearly. Avoid creating a culture of fear. Be positive with those who manage the simulation well, and supportive and helpful when behaviour can be better. 3. Context and beyond. One of the main reasons simulated phishing attacks fail is a lack of context. TEN KEY TOPICS TO COVER IN CYBER SECURITY AWARENESS It should begin by discussing why those taking the training are indeed targets. 2. Preventing identity theft. Identity theft remains the most prevalent form of cybercrime. As such, preventing identity theft is key to any good cyber security awareness training campaign. As well as information on preventing identity theft, cover the warning signs WEBINAR: THE OFFICE OF THE FUTURE The past year has seen dramatic changes to working life. On Monday 19th April, CybSafe’s Oz Alashe MBE (CEO) and Cybersmart’s Jamie Akhtar (CEO) will host a webinar to discuss the office of the future. They’ll explore what remote working has taught us about people and security. The webinar will feature two academic projects from the UK’s leading research networks (SPRITE+ and RISCs BEHAVIOUR CHANGE HUB Intelligently deploy behaviour interventions to reduce risk. CybSafe lets you prioritise certain behaviours for your goals. Nudge-IQ then intelligently presents interventions to people. With 80+ behaviours to choose from, you can focus your efforts and change behaviour easily. WHY ARE PHISHING ATTACKS SUCCESSFUL? Fortunately, when you know why phishing attacks are successful, you can begin to reverse the trend – and even use psychology to counter threats such as phishing. CybSafe, for example, is developed in collaboration with psychologists and behavioural scientists. It uses pioneering research from leading academics to ensure people take agenuine
ADVANCED SIMULATED PHISHING INFORMATION Tracking Simulated Phishing Emails. CybSafe phishing tracks the "opens" of an email using a unique hidden image pixel to record an open event. This however has some technical limitations: It will vary amongst mail clients and configuration, but if "Automatically download external images" is disabled or blocked, then an open event is notcaptured.
CYBSAFE – UNDERSTAND PEOPLE. PREVENT SECURITY INCIDENTS.WHY CYBSAFEPRODUCTSSEBDBCUSTOMERSPARTNERSCOMPANY It gives us really robust metrics that help us measure where our people are. It shows their behaviours as well as their attitudes.”. “CybSafe has allowed us to identify changes in security behaviour and respond accordingly. We now see and understand aspects of our human cyber risk that we simply couldn’t get from training &phishing.”.
ABOUT CYBSAFE
We are CybSafe. We’re a British cyber security and data analytics company. We build incredible software that makes it easy to manage human cyber risk. We’re on a mission to revolutionise the way society addresses the human aspect of cyber security. Our technology uses science and data to help people when they need it most. In the way that is most effective for them.PRICING – CYBSAFE
Choose the Hub that works for you. CybSafe secures hundreds of organisations around the world. Start making human cyber riskmanagement simple.
HOW CAN PHISHING AFFECT A BUSINESS? LET’S PUNISH PHISHING VICTIMS… ER, YOU WANT TO DO WHAT Why it makes little sense to punish phishing victims. Going a step further, punishing those who misdiagnose simulated phishing emails can cultivate a culture of fear. Think about that for a second: A culture of fear. Fear is a massive hindrance. Fear is why a “Sam” in marketing is yet to report the fact he inadvertently introducedmalware
ABOUT SEBDB
The challenge faced by security professionals. You face a complex challenge as a security professional. You’re tasked with changing behaviour linked to security risks. The links between security behaviours and risks are not always clear. It’s hard to know which interventions to apply. It’s harder still to explain how interventions reduce 3 CAUSES OF CYBER ATTACKS 3. Assessing risk. Criminals want us to underestimate the risk of cyber attacks. The more we underestimate, the easier things are for them. Unfortunately, everyone’s ability to calculate risk is poor! Take the example of car accidents and plane crashes. Statistically, flying is far safer than driving.WELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. HOW TO IDENTIFY A PHISHING EMAIL Step 5: Check the sender details. Checking the sender details isn’t foolproof. Email accounts can be hacked and sender details can be spoofed. But, for the most part, it’s possible to identify phishing emails as fraudulent by scrutinising the senders’ details. Emails that claim to be from companies such as Apple might be sent fromdomains
USING PRIVATE BROWSING WINDOWS Using private browsing windows If workplace devices are shared between colleagues, private browsing should be enabled by default. This means history and cookies are deleted after each session. CYBSAFE – UNDERSTAND PEOPLE. PREVENT SECURITY INCIDENTS.WHY CYBSAFEPRODUCTSSEBDBCUSTOMERSPARTNERSCOMPANY It gives us really robust metrics that help us measure where our people are. It shows their behaviours as well as their attitudes.”. “CybSafe has allowed us to identify changes in security behaviour and respond accordingly. We now see and understand aspects of our human cyber risk that we simply couldn’t get from training &phishing.”.
ABOUT CYBSAFE
We are CybSafe. We’re a British cyber security and data analytics company. We build incredible software that makes it easy to manage human cyber risk. We’re on a mission to revolutionise the way society addresses the human aspect of cyber security. Our technology uses science and data to help people when they need it most. In the way that is most effective for them.PRICING – CYBSAFE
Choose the Hub that works for you. CybSafe secures hundreds of organisations around the world. Start making human cyber riskmanagement simple.
HOW CAN PHISHING AFFECT A BUSINESS? LET’S PUNISH PHISHING VICTIMS… ER, YOU WANT TO DO WHAT Why it makes little sense to punish phishing victims. Going a step further, punishing those who misdiagnose simulated phishing emails can cultivate a culture of fear. Think about that for a second: A culture of fear. Fear is a massive hindrance. Fear is why a “Sam” in marketing is yet to report the fact he inadvertently introducedmalware
ABOUT SEBDB
The challenge faced by security professionals. You face a complex challenge as a security professional. You’re tasked with changing behaviour linked to security risks. The links between security behaviours and risks are not always clear. It’s hard to know which interventions to apply. It’s harder still to explain how interventions reduce 3 CAUSES OF CYBER ATTACKS 3. Assessing risk. Criminals want us to underestimate the risk of cyber attacks. The more we underestimate, the easier things are for them. Unfortunately, everyone’s ability to calculate risk is poor! Take the example of car accidents and plane crashes. Statistically, flying is far safer than driving.WELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. HOW TO IDENTIFY A PHISHING EMAIL Step 5: Check the sender details. Checking the sender details isn’t foolproof. Email accounts can be hacked and sender details can be spoofed. But, for the most part, it’s possible to identify phishing emails as fraudulent by scrutinising the senders’ details. Emails that claim to be from companies such as Apple might be sent fromdomains
USING PRIVATE BROWSING WINDOWS Using private browsing windows If workplace devices are shared between colleagues, private browsing should be enabled by default. This means history and cookies are deleted after each session.WELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. CERTIFIED SECURITY AWARENESS TRAINING CybSafe Certified Security Awareness Training is a short, threat-based course that helps develop cyber skills. Contains threat-based modules and separate multi-disciplinary, role-specific content. Short, bite-sized, interactive content. Certified by the UK National Cyber Security Centre (NCSC) & the Chartered Institute of InformationSecurity
USING PRIVATE BROWSING WINDOWS Using private browsing windows If workplace devices are shared between colleagues, private browsing should be enabled by default. This means history and cookies are deleted after each session. THE 4 KEY FACTORS FOR A SUCCESSFUL PHISHING SIMULATION A simulated phishing campaign needs to be communicated clearly. Avoid creating a culture of fear. Be positive with those who manage the simulation well, and supportive and helpful when behaviour can be better. 3. Context and beyond. One of the main reasons simulated phishing attacks fail is a lack of context. WEBINAR: THE OFFICE OF THE FUTURE The past year has seen dramatic changes to working life. On Monday 19th April, CybSafe’s Oz Alashe MBE (CEO) and Cybersmart’s Jamie Akhtar (CEO) will host a webinar to discuss the office of the future. They’ll explore what remote working has taught us about people and security. The webinar will feature two academic projects from the UK’s leading research networks (SPRITE+ and RISCs TEN KEY TOPICS TO COVER IN CYBER SECURITY AWARENESS It should begin by discussing why those taking the training are indeed targets. 2. Preventing identity theft. Identity theft remains the most prevalent form of cybercrime. As such, preventing identity theft is key to any good cyber security awareness training campaign. As well as information on preventing identity theft, cover the warning signs FOUR DIFFERENT TYPES OF SECURITY AWARENESS TRAINING 1. Classroom-based training. 2. Visual aids (including video) 3. Through simulated attacks. 4. Computer-based training. Resource challenges and environmental contexts often force those in security to decide which method or methods to include in awareness campaigns – and in which quantities each should be employed. PUNISHMENT IN CYBER SECURITY WORKSHOP Liz Murray joined HSBC in 2018 following a successful 21 year military career. Her previous experience of human factors and post-graduate study in Education that included examination of the impact of using coaching as a remedial means of improving poor performance underpin her passion for developing a positive cyber security culture. WHY ARE PHISHING ATTACKS SUCCESSFUL? Fortunately, when you know why phishing attacks are successful, you can begin to reverse the trend – and even use psychology to counter threats such as phishing. CybSafe, for example, is developed in collaboration with psychologists and behavioural scientists. It uses pioneering research from leading academics to ensure people take agenuine
ADVANCED SIMULATED PHISHING INFORMATION Tracking Simulated Phishing Emails. CybSafe phishing tracks the "opens" of an email using a unique hidden image pixel to record an open event. This however has some technical limitations: It will vary amongst mail clients and configuration, but if "Automatically download external images" is disabled or blocked, then an open event is notcaptured.
CYBSAFE – UNDERSTAND PEOPLE. PREVENT SECURITY INCIDENTS.WHY CYBSAFEPRODUCTSSEBDBCUSTOMERSPARTNERSCOMPANY It gives us really robust metrics that help us measure where our people are. It shows their behaviours as well as their attitudes.”. “CybSafe has allowed us to identify changes in security behaviour and respond accordingly. We now see and understand aspects of our human cyber risk that we simply couldn’t get from training &phishing.”.
ABOUT CYBSAFE
We are CybSafe. We’re a British cyber security and data analytics company. We build incredible software that makes it easy to manage human cyber risk. We’re on a mission to revolutionise the way society addresses the human aspect of cyber security. Our technology uses science and data to help people when they need it most. In the way that is most effective for them.ABOUT SEBDB
The challenge faced by security professionals. You face a complex challenge as a security professional. You’re tasked with changing behaviour linked to security risks. The links between security behaviours and risks are not always clear. It’s hard to know which interventions to apply. It’s harder still to explain how interventions reduce HOW CAN PHISHING AFFECT A BUSINESS? SIX SECURITY ESSENTIALS FOR THOSE WORKING FROM HOME 1. Use company-approved devices. Mental blueprints dictate how we behave in any given situation. Our blueprints might prompt us to use personal laptops when working from home – but that’s rarely a good idea. Most companies fit laptops and devices with inconspicuous defences that improve their security. Plus, devices are portals todata.
WELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. 7 REASONS WHY SECURITY AWARENESS TRAINING IS IMPORTANT Here are 7 reasons. 1. To prevent breaches and attacks. Starting with the most obvious, security awareness training helps prevent breaches. The precise number of breaches security awareness training prevents is difficult to quantify. In an ideal world, we’d be able to run a controlled trial comparing those who received training and those who LET’S PUNISH PHISHING VICTIMS… ER, YOU WANT TO DO WHAT Why it makes little sense to punish phishing victims. Going a step further, punishing those who misdiagnose simulated phishing emails can cultivate a culture of fear. Think about that for a second: A culture of fear. Fear is a massive hindrance. Fear is why a “Sam” in marketing is yet to report the fact he inadvertently introducedmalware
ALL BEHAVIOURS
Data theft is the intentional stealing of data. Enabling fingerprint or facial login for devices and/or accounts. Reporting security incidents. Blocking pop-ups. Enabling firewalls. Enabling auto-updates. Enabling Google Play Protect. Restricting administrator privileges. Running antivirus if a new icon or desktop pop-up appears. HOW TO IDENTIFY A PHISHING EMAIL Step 5: Check the sender details. Checking the sender details isn’t foolproof. Email accounts can be hacked and sender details can be spoofed. But, for the most part, it’s possible to identify phishing emails as fraudulent by scrutinising the senders’ details. Emails that claim to be from companies such as Apple might be sent fromdomains
CYBSAFE – UNDERSTAND PEOPLE. PREVENT SECURITY INCIDENTS.WHY CYBSAFEPRODUCTSSEBDBCUSTOMERSPARTNERSCOMPANY It gives us really robust metrics that help us measure where our people are. It shows their behaviours as well as their attitudes.”. “CybSafe has allowed us to identify changes in security behaviour and respond accordingly. We now see and understand aspects of our human cyber risk that we simply couldn’t get from training &phishing.”.
ABOUT CYBSAFE
We are CybSafe. We’re a British cyber security and data analytics company. We build incredible software that makes it easy to manage human cyber risk. We’re on a mission to revolutionise the way society addresses the human aspect of cyber security. Our technology uses science and data to help people when they need it most. In the way that is most effective for them.ABOUT SEBDB
The challenge faced by security professionals. You face a complex challenge as a security professional. You’re tasked with changing behaviour linked to security risks. The links between security behaviours and risks are not always clear. It’s hard to know which interventions to apply. It’s harder still to explain how interventions reduce HOW CAN PHISHING AFFECT A BUSINESS? SIX SECURITY ESSENTIALS FOR THOSE WORKING FROM HOME 1. Use company-approved devices. Mental blueprints dictate how we behave in any given situation. Our blueprints might prompt us to use personal laptops when working from home – but that’s rarely a good idea. Most companies fit laptops and devices with inconspicuous defences that improve their security. Plus, devices are portals todata.
WELCOME 👋
Welcome 👋 Welcome to SebDB, the world’s most comprehensive cyber security behaviour database. SebDB maps security behaviours to risks-related outcomes. 7 REASONS WHY SECURITY AWARENESS TRAINING IS IMPORTANT Here are 7 reasons. 1. To prevent breaches and attacks. Starting with the most obvious, security awareness training helps prevent breaches. The precise number of breaches security awareness training prevents is difficult to quantify. In an ideal world, we’d be able to run a controlled trial comparing those who received training and those who LET’S PUNISH PHISHING VICTIMS… ER, YOU WANT TO DO WHAT Why it makes little sense to punish phishing victims. Going a step further, punishing those who misdiagnose simulated phishing emails can cultivate a culture of fear. Think about that for a second: A culture of fear. Fear is a massive hindrance. Fear is why a “Sam” in marketing is yet to report the fact he inadvertently introducedmalware
ALL BEHAVIOURS
Data theft is the intentional stealing of data. Enabling fingerprint or facial login for devices and/or accounts. Reporting security incidents. Blocking pop-ups. Enabling firewalls. Enabling auto-updates. Enabling Google Play Protect. Restricting administrator privileges. Running antivirus if a new icon or desktop pop-up appears. HOW TO IDENTIFY A PHISHING EMAIL Step 5: Check the sender details. Checking the sender details isn’t foolproof. Email accounts can be hacked and sender details can be spoofed. But, for the most part, it’s possible to identify phishing emails as fraudulent by scrutinising the senders’ details. Emails that claim to be from companies such as Apple might be sent fromdomains
ABOUT CYBSAFE
We are CybSafe. We’re a British cyber security and data analytics company. We build incredible software that makes it easy to manage human cyber risk. We’re on a mission to revolutionise the way society addresses the human aspect of cyber security. Our technology uses science and data to help people when they need it most. In the way that is most effective for them. PRODUCTS – CYBSAFE An intelligent software platform to manage human cyber risk. Measure and predict security behaviours. And improve security engagement, attitudes and habits.CYBSAFE CONNECT APP
Comprehensive support for the remote workforce. Take your security awareness programme mobile with the CybSafe Connect app.ASSIST – CYBSAFE
CybSafe Assist is an on-demand resource for the most frequently asked cyber security questions. It provides just-in-time help, cyber advice & guidance for people. Gives people a source of instant advice and guidance for any security queries. Uses positive reinforcement to improve personal confidence inALL BEHAVIOURS
Data theft is the intentional stealing of data. Enabling fingerprint or facial login for devices and/or accounts. Reporting security incidents. Blocking pop-ups. Enabling firewalls. Enabling auto-updates. Enabling Google Play Protect. Restricting administrator privileges. Running antivirus if a new icon or desktop pop-up appears. TEN KEY TOPICS TO COVER IN CYBER SECURITY AWARENESS It should begin by discussing why those taking the training are indeed targets. 2. Preventing identity theft. Identity theft remains the most prevalent form of cybercrime. As such, preventing identity theft is key to any good cyber security awareness training campaign. As well as information on preventing identity theft, cover the warning signs THE 4 KEY FACTORS FOR A SUCCESSFUL PHISHING SIMULATION A simulated phishing campaign needs to be communicated clearly. Avoid creating a culture of fear. Be positive with those who manage the simulation well, and supportive and helpful when behaviour can be better. 3. Context and beyond. One of the main reasons simulated phishing attacks fail is a lack of context. FOUR DIFFERENT TYPES OF SECURITY AWARENESS TRAINING 1. Classroom-based training. 2. Visual aids (including video) 3. Through simulated attacks. 4. Computer-based training. Resource challenges and environmental contexts often force those in security to decide which method or methods to include in awareness campaigns – and in which quantities each should be employed. SIMULATED PHISHING EMAILS Occasionally, CybSafe may send you simulated phishing emails. They’re designed to look like real malicious emails used by cyber criminals. These emails are not sent to try and catch you out. ADVANCED SIMULATED PHISHING INFORMATION Tracking Simulated Phishing Emails. CybSafe phishing tracks the "opens" of an email using a unique hidden image pixel to record an open event. This however has some technical limitations: It will vary amongst mail clients and configuration, but if "Automatically download external images" is disabled or blocked, then an open event is notcaptured.
* Home
* Behaviour-IQ
* CybSafe Connect app* Customers
* Success stories
* Help centre
* Partners
* Resources
* SebDB
* Blog
* Events
* Webinars
* Whitepapers
* Research library
* Demo
* Login
Select Page
* Home
* Behaviour-IQ
* CybSafe Connect app* Customers
* Success stories
* Help centre
* Partners
* Resources
* SebDB
* Blog
* Events
* Webinars
* Whitepapers
* Research library
* Demo
* Login
SECURITY AWARENESS TRAINING DOESN’T CHANGE BEHAVIOUR. CYBSAFEDOES.
Supercharge awareness activities. Improve and measure security behaviour. All in one platform.start free trial
start free trial
Thousands use CybSafe to prevent security incidents: TOOLS TO MAKE SECURITY AWARENESS ACTIVITIES BETTER.N
NAIL THE BASICS
NCSC certified training. Simulated phishing. Security culture assessment. Campaign support suite.N
SAVE TIME
Automated user enrolment, engagement, interventions, and testing. Access anywhere on mobile and desktop.N
GO FURTHER
Support people with a security goal setting tool and a library of home and workplace security tips. Both customisable for richer context.see more
HUMAN RISK DATA, METRICS AND REPORTING YOU CAN’T GET ANYWHERE ELSE.N
UNDERSTAND PEOPLE & RISK See how people’s thoughts and actions affect risk and securityculture.
N
MAKE BETTER DECISIONS Metrics and data show the effectiveness of security controls and awareness activities.N
PROVE RISK REDUCTION, COMPLIANCE & ROI Show the board and regulators you’re reducing risk cost effectively.see more
START IMMEDIATELY WITH: SSO VIA GOOGLE WORKSPACE (FORMERLY G SUITE), AZURE AND OTHERS; SCIM PROVISIONING; AND OUT-OF-THE-BOX AWARENESS TRAINING AND PHISHING. TRY IT YOURSELF OR SEE IT IN ACTIONStart free trial
Watch demo
YOU’RE IN GOOD COMPANY “CybSafe is just another level. It gives us really robust metrics that help us measure where our people are. It shows their behaviours as well as their attitudes.”Caroline Bansraj
Global Cyber Security Education & Awareness “CybSafe has allowed us to identify changes in security behaviour and respond accordingly. We now see and understand aspects of our human cyber risk that we simply couldn’t get from training &phishing.”
Steven Pendleton
CISO
CONTACT US TO GET STARTEDCYBSAFE
Why CybSafe?
Borderless security awarenessPRODUCT
Product
Our technology
Awareness Hub
Behaviour Change HubCulture Hub
Managed Service Hub
Pricing
CUSTOMERS
Our customers
Case studies
Support
PARTNERS
Become a partner
Partner portal
RESOURCES
All resources
Blog
Webinars
Whitepapers
Research library
HELP
Help centre
Contact us
COMPANY
About us
About Research & AnalysisEvents
Press
Careers
Legal
CybStore
* Follow
* Follow
Copyright © 2021 CybSafe Ltd. All Rights Reserved.Privacy policy
| Cookies policy
| Terms of website useDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0