Are you over 18 and want to see adult content?
More Annotations
A complete backup of onlinemmebook.blogspot.com
Are you over 18 and want to see adult content?
A complete backup of lyhealthcare.com
Are you over 18 and want to see adult content?
A complete backup of gtasabusenava.blogspot.com
Are you over 18 and want to see adult content?
A complete backup of fondation-patrimoine.org
Are you over 18 and want to see adult content?
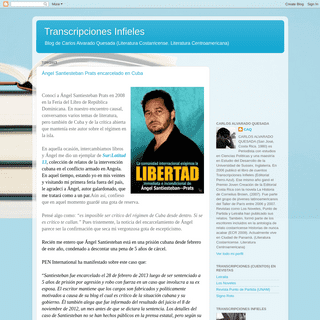
A complete backup of carlosalvaradoquesada.blogspot.com
Are you over 18 and want to see adult content?

A complete backup of strathamtroop185.org
Are you over 18 and want to see adult content?

A complete backup of abom3n.blogspot.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://balkanje.com/marasli-epizoda-17/
Are you over 18 and want to see adult content?
A complete backup of https://balkanje.com/turske-serije/ertugrul-2014/
Are you over 18 and want to see adult content?
A complete backup of https://balkanje.com/turske-serije/moj-dom-2019/
Are you over 18 and want to see adult content?
A complete backup of https://balkanje.com/nada-umire-poslednja-epizoda-18/
Are you over 18 and want to see adult content?

A complete backup of https://balkanje.com/turske-serije/ludo-srce-2017/
Are you over 18 and want to see adult content?
A complete backup of https://balkanje.com/turske-serije/casna-rec-2020/
Are you over 18 and want to see adult content?

A complete backup of https://balkanje.com/latino-serije/znam-ko-si-2017/
Are you over 18 and want to see adult content?
A complete backup of https://balkanje.com/iskupljenje-epizoda-25/
Are you over 18 and want to see adult content?
Text
AWS. 50
COALFIRE FEDERAL
Coalfire Federal’s core capabilities: Cyber program management and operations. Cyber automation, engineering, and orchestration. Security compliance and advisory. Advice on DoD RMF based on our extensive experience. Interpretation of NIST for application to government requirements. Sourcing of staff to meet mission-critical cyber projectneeds.
SOC & SSAE REPORTING SERVICES SOC and SSAE reporting services. A System and Organization Controls report (SOC 1, 2, or 3 report) is a widely recognized way to ensure trust and confidence in your security and financial controls posture. SOC reports follow the guidance from the AICPA’s Statement on Standards for Attestation Engagements No. 18 (SSAE 18, formerly SSAE16).
COALFIREONE ASSESSMENT & PROJECT MANAGEMENT A powerful project management and collaboration portal for managing assessments and compliance projects. To streamline and simplify the assessment experience, you’ll have access to the CoalfireOne assessment and project management portal for the duration of your project. Not only does it allow you and your team to effectively checkstatus and
ATTACK SURFACE MANAGEMENT Attack surface management. Protecting your digital footprint has never been more challenging, or more critical. As your attack surface expands, corporate assets are increasingly exposed to risk, often unbeknownst to security teams. Coalfire’s attack surface management (ASM) solution enables you to take control of your security postureand
CMMC: CYBERSECURITY MATURITY MODEL CERTIFICATION CMMC. Coalfire Federal is among the first to be certified as a Cybersecurity Maturity Model Certification (CMMC) Third Party Assessment Organization (C3PAO) and Registered Provider Organization (RPO) authorized by the CMMC Accreditation Body. We offer a suite of CMMC advisory and assessment services to help organizations preparefor and achieve
PENETRATION TESTING
Penetration testing – whether it’s internal or external, white-box or black-box – uncovers critical issues and demonstrates how well your network and information assets are protected. Because Coalfire Labs thinks and acts like an attacker, you can discover critical APAX PARTNERS COMPLETES COALFIRE ACQUISITION Apax Partners Completes Coalfire Acquisition Investment will fuel growth of services that enable secure cloud migrations and environments WESTMINSTER, CO and NEW YORK – April 23, 2020 – Coalfire, a provider of cybersecurity advisory and assessment services, today announced that its acquisition by Funds advised by Apax Partners has been finalized following full regulatory approval. COALFIRE ACQUIRES DENIM GROUP TO TRANSFORM The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. THE COST OF A FEDRAMP ASSESSMENT FROM A 3PAO Industry estimates place the cost of projects between $75,000 and $3.5 million. It covers at least 325 security test cases as defined by NIST for a “Moderate” system and 421 security test cases for a “High” system. Many of the costs listed by Mr. Goodrich, the Director of FedRAMP, stem from Cloud Service Providers (CSP) owningtheir own
COALFIRE - CLOUD AND CYBERSECURITY CONSULTING AND MANAGEDTOGGLEABOUTINDUSTRIESSOLUTIONSRESOURCESCAREERS The world's biggest and best trust their clouds to us. 7 of the top 10 SaaS providers rely on Coalfire. 75 %. Speed and security. You can have both. Secure compliant environments in 75% less time with our proven approach to cloud automation, developed in partnership withAWS. 50
COALFIRE FEDERAL
Coalfire Federal’s core capabilities: Cyber program management and operations. Cyber automation, engineering, and orchestration. Security compliance and advisory. Advice on DoD RMF based on our extensive experience. Interpretation of NIST for application to government requirements. Sourcing of staff to meet mission-critical cyber projectneeds.
SOC & SSAE REPORTING SERVICES SOC and SSAE reporting services. A System and Organization Controls report (SOC 1, 2, or 3 report) is a widely recognized way to ensure trust and confidence in your security and financial controls posture. SOC reports follow the guidance from the AICPA’s Statement on Standards for Attestation Engagements No. 18 (SSAE 18, formerly SSAE16).
COALFIREONE ASSESSMENT & PROJECT MANAGEMENT A powerful project management and collaboration portal for managing assessments and compliance projects. To streamline and simplify the assessment experience, you’ll have access to the CoalfireOne assessment and project management portal for the duration of your project. Not only does it allow you and your team to effectively checkstatus and
ATTACK SURFACE MANAGEMENT Attack surface management. Protecting your digital footprint has never been more challenging, or more critical. As your attack surface expands, corporate assets are increasingly exposed to risk, often unbeknownst to security teams. Coalfire’s attack surface management (ASM) solution enables you to take control of your security postureand
CMMC: CYBERSECURITY MATURITY MODEL CERTIFICATION CMMC. Coalfire Federal is among the first to be certified as a Cybersecurity Maturity Model Certification (CMMC) Third Party Assessment Organization (C3PAO) and Registered Provider Organization (RPO) authorized by the CMMC Accreditation Body. We offer a suite of CMMC advisory and assessment services to help organizations preparefor and achieve
PENETRATION TESTING
Penetration testing – whether it’s internal or external, white-box or black-box – uncovers critical issues and demonstrates how well your network and information assets are protected. Because Coalfire Labs thinks and acts like an attacker, you can discover critical APAX PARTNERS COMPLETES COALFIRE ACQUISITION Apax Partners Completes Coalfire Acquisition Investment will fuel growth of services that enable secure cloud migrations and environments WESTMINSTER, CO and NEW YORK – April 23, 2020 – Coalfire, a provider of cybersecurity advisory and assessment services, today announced that its acquisition by Funds advised by Apax Partners has been finalized following full regulatory approval. COALFIRE ACQUIRES DENIM GROUP TO TRANSFORM The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. THE COST OF A FEDRAMP ASSESSMENT FROM A 3PAO Industry estimates place the cost of projects between $75,000 and $3.5 million. It covers at least 325 security test cases as defined by NIST for a “Moderate” system and 421 security test cases for a “High” system. Many of the costs listed by Mr. Goodrich, the Director of FedRAMP, stem from Cloud Service Providers (CSP) owningtheir own
COALFIREONE ASSESSMENT & PROJECT MANAGEMENT The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line.CASE STUDIES
Global merchant provider hires Coalfire to investigate a breach and validate cybersecurity. A multinational merchant service provider was breached by a sophisticated international hacking ring that resulted in a $10M global ATM cash-out in 24 hours. Learn how Coalfire helped.case study.
CLOUD SECURITY
Experience: Coalfire is the largest provider of engineering, advisory, and assessment services to the CSP market, serving over 700 unique CSPs. Technical expertise: Coalfire holds 823 major industry cloud and security certifications across its 550+ consultants, engineers, and penetration testers. Proven impact: ACE clients see an average of 429 WHAT YOU NEED TO KNOW: TRANSITIONING CSA STAR FOR CLOUD Resource covering the most important issues in IT security and compliance as well as insights on IT GRC issues that impact the industries that we serve.BLOG ARCHIVE
Resource covering the most important issues in IT security and compliance as well as insights on IT GRC issues that impact the industries that we serve. PCI DSS ASSESSMENTS & ADVISORY PCI DSS assessments and advisory. Coalfire helps organizations address challenges associated with complying with the PCI Data Security Standard (PCI DSS), from scoping uncertainty and gap analysis to assessments, technology validation, and program strategy. As one of the original Qualified Security Assessor (QSA) firms, we haveperformed
PENETRATION TESTING
Penetration testing – whether it’s internal or external, white-box or black-box – uncovers critical issues and demonstrates how well your network and information assets are protected. Because Coalfire Labs thinks and acts like an attacker, you can discover critical APPLICATION SECURITY ASSESSMENTS Securing the design, development, and deployment of your applications. Our dynamic and static application security assessments identify weaknesses in your proprietary or third-party applications and propose fixes that enhance your system’s security posture. By combining the use of leading tools with targeted, expert manual analysis of your THE BASICS OF EXPLOIT DEVELOPMENT 2: SEH OVERFLOWS The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. FEDRAMP 101: HOW TO GET LISTED AS “IN PROCESS” Agency path. To get listed as “FedRAMP In Process” with an agency, there are several key steps to complete before being listed on the Marketplace. The first and arguably most important step is to provide the FedRAMP PMO with an attestation letter from an agency point of contact that should include the following. The CSP name. The CSO name. COALFIRE - CLOUD AND CYBERSECURITY CONSULTING AND MANAGEDTOGGLEABOUTINDUSTRIESSOLUTIONSRESOURCESCAREERS The world's biggest and best trust their clouds to us. 7 of the top 10 SaaS providers rely on Coalfire. 75 %. Speed and security. You can have both. Secure compliant environments in 75% less time with our proven approach to cloud automation, developed in partnership withAWS. 50
COALFIRE FEDERAL
Coalfire Federal’s core capabilities: Cyber program management and operations. Cyber automation, engineering, and orchestration. Security compliance and advisory. Advice on DoD RMF based on our extensive experience. Interpretation of NIST for application to government requirements. Sourcing of staff to meet mission-critical cyber projectneeds.
INDEPENDENT CYBER RISK MANAGEMENT AND COMPLIANCE SERVICES The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line.COALFIREONE
CoalfireOne SM is your hub for proactively managing and automating compliance. You can easily manage the administrative, analytical, and technical aspects of your projects – all in one place. This powerful cloud-based platform delivers technology and insight to help you simplify compliance, reduce risks, and empower your enterprise’ssecurity.
COALFIRE CAREERS IN CYBER RISK AND CYBERSECURITY Careers. A team of relentlessly driven experts and passionate problem-solvers who are hungry to learn, grow, and make a difference. That’s Coalfire. Our strong values and inclusive environment empower us to solve our clients’ toughest cybersecurity challenges and make the world a safer place. If you’re looking to elevate your career,help
SOC & SSAE REPORTING SERVICES SOC and SSAE reporting services. A System and Organization Controls report (SOC 1, 2, or 3 report) is a widely recognized way to ensure trust and confidence in your security and financial controls posture. SOC reports follow the guidance from the AICPA’s Statement on Standards for Attestation Engagements No. 18 (SSAE 18, formerly SSAE16).
APPLICATION SECURITY ASSESSMENTS Securing the design, development, and deployment of your applications. Our dynamic and static application security assessments identify weaknesses in your proprietary or third-party applications and propose fixes that enhance your system’s security posture. By combining the use of leading tools with targeted, expert manual analysis of your DOD RMF CERTIFICATION & ACCREDITATION A shared information security framework across the DoD and its contractors. If you are a DoD contractor, Coalfire’s DoD RMF certification and accreditation service can help you assess your information systems to DoD RMF standards in pursuit of a DoD Agency Authority to Operate (ATO). Using NIST 800-53 Revision 4 guidance, ourRMF approach
THE BASICS OF EXPLOIT DEVELOPMENT 2: SEH OVERFLOWS The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. COALFIRE ACQUIRES DENIM GROUP TO TRANSFORM The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. COALFIRE - CLOUD AND CYBERSECURITY CONSULTING AND MANAGEDTOGGLEABOUTINDUSTRIESSOLUTIONSRESOURCESCAREERS The world's biggest and best trust their clouds to us. 7 of the top 10 SaaS providers rely on Coalfire. 75 %. Speed and security. You can have both. Secure compliant environments in 75% less time with our proven approach to cloud automation, developed in partnership withAWS. 50
COALFIRE FEDERAL
Coalfire Federal’s core capabilities: Cyber program management and operations. Cyber automation, engineering, and orchestration. Security compliance and advisory. Advice on DoD RMF based on our extensive experience. Interpretation of NIST for application to government requirements. Sourcing of staff to meet mission-critical cyber projectneeds.
INDEPENDENT CYBER RISK MANAGEMENT AND COMPLIANCE SERVICES The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line.COALFIREONE
CoalfireOne SM is your hub for proactively managing and automating compliance. You can easily manage the administrative, analytical, and technical aspects of your projects – all in one place. This powerful cloud-based platform delivers technology and insight to help you simplify compliance, reduce risks, and empower your enterprise’ssecurity.
COALFIRE CAREERS IN CYBER RISK AND CYBERSECURITY Careers. A team of relentlessly driven experts and passionate problem-solvers who are hungry to learn, grow, and make a difference. That’s Coalfire. Our strong values and inclusive environment empower us to solve our clients’ toughest cybersecurity challenges and make the world a safer place. If you’re looking to elevate your career,help
SOC & SSAE REPORTING SERVICES SOC and SSAE reporting services. A System and Organization Controls report (SOC 1, 2, or 3 report) is a widely recognized way to ensure trust and confidence in your security and financial controls posture. SOC reports follow the guidance from the AICPA’s Statement on Standards for Attestation Engagements No. 18 (SSAE 18, formerly SSAE16).
APPLICATION SECURITY ASSESSMENTS Securing the design, development, and deployment of your applications. Our dynamic and static application security assessments identify weaknesses in your proprietary or third-party applications and propose fixes that enhance your system’s security posture. By combining the use of leading tools with targeted, expert manual analysis of your DOD RMF CERTIFICATION & ACCREDITATION A shared information security framework across the DoD and its contractors. If you are a DoD contractor, Coalfire’s DoD RMF certification and accreditation service can help you assess your information systems to DoD RMF standards in pursuit of a DoD Agency Authority to Operate (ATO). Using NIST 800-53 Revision 4 guidance, ourRMF approach
THE BASICS OF EXPLOIT DEVELOPMENT 2: SEH OVERFLOWS The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. COALFIRE ACQUIRES DENIM GROUP TO TRANSFORM The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. INDEPENDENT CYBER RISK MANAGEMENT AND COMPLIANCE SERVICES The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. CYBERSECURITY SOLUTIONS Solutions. Accelerate your success with solutions that span the cybersecurity lifecycle. Imperative to business today, digital transformation yields incredible benefits including new revenue streams, faster time to market, and greater efficiencies. Capitalize on these promises by securing your cloud and every aspect of yourenvironment with
COALFIREONE ASSESSMENT & PROJECT MANAGEMENT A powerful project management and collaboration portal for managing assessments and compliance projects. To streamline and simplify the assessment experience, you’ll have access to the CoalfireOne assessment and project management portal for the duration of your project. Not only does it allow you and your team to effectively checkstatus and
CYBERSECURITY COMPLIANCE & ASSESSMENT SERVICES Cybersecurity compliance and assessment services. Make compliance efficient and empowering with services that help reduce risk and demonstrate security posture. Watch the video to learn how Coalfire helps you simplify, strengthen and maintain compliance with expert services and an innovative technology platform solution. Play video. ATTACK SURFACE MANAGEMENT Attack surface management. Protecting your digital footprint has never been more challenging, or more critical. As your attack surface expands, corporate assets are increasingly exposed to risk, often unbeknownst to security teams. Coalfire’s attack surface management (ASM) solution enables you to take control of your security postureand
BLOG ARCHIVE
Resource covering the most important issues in IT security and compliance as well as insights on IT GRC issues that impact the industries that we serve. COALFIREONE SCANNING SERVICES & SUPPORT The CoalfireOne Scanning Services Team manages your vulnerability scans using CoalfireOne, allowing unlimited rescans on demand throughout the subscription. We handle everything including setting up your scans, ensuring your scans are complete, analyzing results, submitting disputes, and providing a passing attestation. APPLICATION SECURITY ASSESSMENTS Securing the design, development, and deployment of your applications. Our dynamic and static application security assessments identify weaknesses in your proprietary or third-party applications and propose fixes that enhance your system’s security posture. By combining the use of leading tools with targeted, expert manual analysis of your THE BASICS OF EXPLOIT DEVELOPMENT 2: SEH OVERFLOWS The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. FEDRAMP 101: HOW TO GET LISTED AS “IN PROCESS” Agency path. To get listed as “FedRAMP In Process” with an agency, there are several key steps to complete before being listed on the Marketplace. The first and arguably most important step is to provide the FedRAMP PMO with an attestation letter from an agency point of contact that should include the following. The CSP name. The CSO name. COALFIRE - CLOUD AND CYBERSECURITY CONSULTING AND MANAGEDTOGGLEABOUTINDUSTRIESSOLUTIONSRESOURCESCAREERS The world's biggest and best trust their clouds to us. 7 of the top 10 SaaS providers rely on Coalfire. 75 %. Speed and security. You can have both. Secure compliant environments in 75% less time with our proven approach to cloud automation, developed in partnership withAWS. 50
COALFIRE FEDERAL
Coalfire Federal’s core capabilities: Cyber program management and operations. Cyber automation, engineering, and orchestration. Security compliance and advisory. Advice on DoD RMF based on our extensive experience. Interpretation of NIST for application to government requirements. Sourcing of staff to meet mission-critical cyber projectneeds.
INDEPENDENT CYBER RISK MANAGEMENT AND COMPLIANCE SERVICES The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line.COALFIREONE
CoalfireOne SM is your hub for proactively managing and automating compliance. You can easily manage the administrative, analytical, and technical aspects of your projects – all in one place. This powerful cloud-based platform delivers technology and insight to help you simplify compliance, reduce risks, and empower your enterprise’ssecurity.
COALFIRE CAREERS IN CYBER RISK AND CYBERSECURITY Careers. A team of relentlessly driven experts and passionate problem-solvers who are hungry to learn, grow, and make a difference. That’s Coalfire. Our strong values and inclusive environment empower us to solve our clients’ toughest cybersecurity challenges and make the world a safer place. If you’re looking to elevate your career,help
SOC & SSAE REPORTING SERVICES SOC and SSAE reporting services. A System and Organization Controls report (SOC 1, 2, or 3 report) is a widely recognized way to ensure trust and confidence in your security and financial controls posture. SOC reports follow the guidance from the AICPA’s Statement on Standards for Attestation Engagements No. 18 (SSAE 18, formerly SSAE16).
APPLICATION SECURITY ASSESSMENTS Securing the design, development, and deployment of your applications. Our dynamic and static application security assessments identify weaknesses in your proprietary or third-party applications and propose fixes that enhance your system’s security posture. By combining the use of leading tools with targeted, expert manual analysis of your DOD RMF CERTIFICATION & ACCREDITATION A shared information security framework across the DoD and its contractors. If you are a DoD contractor, Coalfire’s DoD RMF certification and accreditation service can help you assess your information systems to DoD RMF standards in pursuit of a DoD Agency Authority to Operate (ATO). Using NIST 800-53 Revision 4 guidance, ourRMF approach
THE BASICS OF EXPLOIT DEVELOPMENT 2: SEH OVERFLOWS The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. COALFIRE ACQUIRES DENIM GROUP TO TRANSFORM The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. COALFIRE - CLOUD AND CYBERSECURITY CONSULTING AND MANAGEDTOGGLEABOUTINDUSTRIESSOLUTIONSRESOURCESCAREERS The world's biggest and best trust their clouds to us. 7 of the top 10 SaaS providers rely on Coalfire. 75 %. Speed and security. You can have both. Secure compliant environments in 75% less time with our proven approach to cloud automation, developed in partnership withAWS. 50
COALFIRE FEDERAL
Coalfire Federal’s core capabilities: Cyber program management and operations. Cyber automation, engineering, and orchestration. Security compliance and advisory. Advice on DoD RMF based on our extensive experience. Interpretation of NIST for application to government requirements. Sourcing of staff to meet mission-critical cyber projectneeds.
INDEPENDENT CYBER RISK MANAGEMENT AND COMPLIANCE SERVICES The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line.COALFIREONE
CoalfireOne SM is your hub for proactively managing and automating compliance. You can easily manage the administrative, analytical, and technical aspects of your projects – all in one place. This powerful cloud-based platform delivers technology and insight to help you simplify compliance, reduce risks, and empower your enterprise’ssecurity.
COALFIRE CAREERS IN CYBER RISK AND CYBERSECURITY Careers. A team of relentlessly driven experts and passionate problem-solvers who are hungry to learn, grow, and make a difference. That’s Coalfire. Our strong values and inclusive environment empower us to solve our clients’ toughest cybersecurity challenges and make the world a safer place. If you’re looking to elevate your career,help
SOC & SSAE REPORTING SERVICES SOC and SSAE reporting services. A System and Organization Controls report (SOC 1, 2, or 3 report) is a widely recognized way to ensure trust and confidence in your security and financial controls posture. SOC reports follow the guidance from the AICPA’s Statement on Standards for Attestation Engagements No. 18 (SSAE 18, formerly SSAE16).
APPLICATION SECURITY ASSESSMENTS Securing the design, development, and deployment of your applications. Our dynamic and static application security assessments identify weaknesses in your proprietary or third-party applications and propose fixes that enhance your system’s security posture. By combining the use of leading tools with targeted, expert manual analysis of your DOD RMF CERTIFICATION & ACCREDITATION A shared information security framework across the DoD and its contractors. If you are a DoD contractor, Coalfire’s DoD RMF certification and accreditation service can help you assess your information systems to DoD RMF standards in pursuit of a DoD Agency Authority to Operate (ATO). Using NIST 800-53 Revision 4 guidance, ourRMF approach
THE BASICS OF EXPLOIT DEVELOPMENT 2: SEH OVERFLOWS The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. COALFIRE ACQUIRES DENIM GROUP TO TRANSFORM The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. INDEPENDENT CYBER RISK MANAGEMENT AND COMPLIANCE SERVICES The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. CYBERSECURITY SOLUTIONS Solutions. Accelerate your success with solutions that span the cybersecurity lifecycle. Imperative to business today, digital transformation yields incredible benefits including new revenue streams, faster time to market, and greater efficiencies. Capitalize on these promises by securing your cloud and every aspect of yourenvironment with
COALFIREONE ASSESSMENT & PROJECT MANAGEMENT A powerful project management and collaboration portal for managing assessments and compliance projects. To streamline and simplify the assessment experience, you’ll have access to the CoalfireOne assessment and project management portal for the duration of your project. Not only does it allow you and your team to effectively checkstatus and
CYBERSECURITY COMPLIANCE & ASSESSMENT SERVICES Cybersecurity compliance and assessment services. Make compliance efficient and empowering with services that help reduce risk and demonstrate security posture. Watch the video to learn how Coalfire helps you simplify, strengthen and maintain compliance with expert services and an innovative technology platform solution. Play video. ATTACK SURFACE MANAGEMENT Attack surface management. Protecting your digital footprint has never been more challenging, or more critical. As your attack surface expands, corporate assets are increasingly exposed to risk, often unbeknownst to security teams. Coalfire’s attack surface management (ASM) solution enables you to take control of your security postureand
BLOG ARCHIVE
Resource covering the most important issues in IT security and compliance as well as insights on IT GRC issues that impact the industries that we serve. COALFIREONE SCANNING SERVICES & SUPPORT The CoalfireOne Scanning Services Team manages your vulnerability scans using CoalfireOne, allowing unlimited rescans on demand throughout the subscription. We handle everything including setting up your scans, ensuring your scans are complete, analyzing results, submitting disputes, and providing a passing attestation. APPLICATION SECURITY ASSESSMENTS Securing the design, development, and deployment of your applications. Our dynamic and static application security assessments identify weaknesses in your proprietary or third-party applications and propose fixes that enhance your system’s security posture. By combining the use of leading tools with targeted, expert manual analysis of your THE BASICS OF EXPLOIT DEVELOPMENT 2: SEH OVERFLOWS The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. FEDRAMP 101: HOW TO GET LISTED AS “IN PROCESS” Agency path. To get listed as “FedRAMP In Process” with an agency, there are several key steps to complete before being listed on the Marketplace. The first and arguably most important step is to provide the FedRAMP PMO with an attestation letter from an agency point of contact that should include the following. The CSP name. The CSO name.Close
* Home
* Toggle Solutions
* Toggle Cloud security * Cloud security strategy and maturity assessment * Accelerated Cloud Engineering * Infrastructure as Code development * Cyber performance review * Product applicability guides * Security operations and cyber dashboards * Toggle Threat and vulnerability management * Attack surface management * CoalfireOne scanning * Penetration testing* Red team exercise
* Threat modeling and attack simulation * Vulnerability assessment * Toggle Strategy, privacy, and risk * Strategy+ cybersecurity program assessment * CISO program management* Privacy services
* M&A cyber due diligence * Cyber risk assessment * Healthcare security risk analysis and advisory * Third-party risk management * Cyber breach services * Toggle Cloud managed services * Accelerated Cloud Engineering services * CoalfireOne scanning * Security operations and cyber dashboards * Toggle Secure product development * Application security * Internet of Things security * Toggle Compliance services* CMMC
* DEA EPCS
* DoD RMF
* FedRAMP
* FFIEC
* FISMA
* HIPAA
* HITRUST
* ISO management
* ITAR and EAR
* NIST SP 800-171
* PA-DSS/SSF
* Payments services
* PCI DSS assessments and advisory* PCI in the cloud
* P2PE
* PCI Forensic Investigator * Report on compliance* SOC and SSAE 18
* White paper services * Toggle CoalfireOne� * CoalfireOne overview * CoalfireOne assessment and project management * CoalfireOne scanning * CoalfireOne Compliance Management* Toggle Industries
* Cloud service providers * Federal government * Financial services* Healthcare
* Higher education
* Hospitality
* Retail
* State & local government* Technology
* Utilities
* Toggle About
* Company overview
* Board Advisors and Directors * Diversity and inclusion* Executive Team
* Partners
* Quality management * Richard E. Dakin Fund* Toggle Insights
* Blog
* Resources
* News and events
* Careers
* Contact
* __
Search:
__ Toggle navigation BREAKING NEWS: Coalfire acquires Denim Group to transform DevSecOps and simplify application security. Learn more __ products", "Securing your digital transformation", "Securing the future of your business"]">SECURING YOUR
PRODUCTS
Watch the video
BUSINESS OUTCOMES DELIVERED. YOUR SUCCESS SECURED.*
Realize new revenue streams*
Align your cybersecurity program with the business*
Shorten your time to market*
Reduce your risk in the cloud*
Automate security for efficiency and accuracyExplore solutions
DEMAND EXCELLENCE.
Only Coalfire brings the cloud expertise, technology, and innovative approaches that empower your organization to capitalize on the promise of digital transformation.*
700+
THE BEST IN CLOUD CHOOSE THE BEST IN CLOUD SECURITY. Secured the cloud for more than 700 cloud service providers.#1
FIRST YESTERDAY, TODAY, AND TOMORROW. #1 in compliance with more assessments than anyone else and the leaders in certifying clients on emerging standards.4M
FINDING YOUR VULNERABILITIES BEFORE YOUR ADVERSARIES. 4 million vulnerabilities uncovered each year.*
7 of 10
THE WORLD'S BIGGEST AND BEST TRUST THEIR CLOUDS TO US. 7 of the top 10 SaaS providers rely on Coalfire.75%
SPEED AND SECURITY. YOU CAN HAVE BOTH. Secure compliant environments in 75% less time with our proven approach to cloud automation, developed in partnership with AWS.50+
WE INNOVATE SO YOU CAN DOMINATE. More than 50 open source and purpose-built security tools created andshared.
*
700+
THE BEST IN CLOUD CHOOSE THE BEST IN CLOUD SECURITY. Secured the cloud for more than 700 cloud service providers.#1
FIRST YESTERDAY, TODAY, AND TOMORROW. #1 in compliance with more assessments than anyone else and the leaders in certifying clients on emerging standards.4M
FINDING YOUR VULNERABILITIES BEFORE YOUR ADVERSARIES. 4 million vulnerabilities uncovered each year.*
7 of 10
THE WORLD'S BIGGEST AND BEST TRUST THEIR CLOUDS TO US. 7 of the top 10 SaaS providers rely on Coalfire.75%
SPEED AND SECURITY. YOU CAN HAVE BOTH. Secure compliant environments in 75% less time with our proven approach to cloud automation, developed in partnership with AWS.50+
WE INNOVATE SO YOU CAN DOMINATE. More than 50 open source and purpose-built security tools created andshared.
____
*
JOIN THE WORLD-CLASS ENTERPRISES WHO'VE JOINED US.*
*
*
*
*
*
JOIN THE WORLD-CLASS ENTERPRISES WHO'VE JOINED US.*
*
*
*
*
*
JOIN THE CLOUD LEADERS WHO'VE JOINED US.*
*
*
*
*
*
JOIN THE CUTTING-EDGE SAAS PROVIDERS WHO'VE JOINED US.*
*
*
*
*
*
JOIN THE WORLD-CLASS ENTERPRISES WHO'VE JOINED US.*
*
*
*
*
*
JOIN THE CLOUD LEADERS WHO'VE JOINED US.*
*
*
*
*
*
JOIN THE CLOUD LEADERS WHO'VE JOINED US.*
*
*
*
*
1
2
3
CYBER SOLUTIONS THAT MOVE YOU FORWARD, FASTER.*
CLOUD SECURITY
Unlock the full potential of your cloud – and lock in your success.Get started
*
THREAT AND VULNERABILITY MANAGEMENT Beat them at their game. Partner with the adversary of youradversaries.
Learn how
*
STRATEGY, PRIVACY, AND RISK A business-aligned, modern cybersecurity program. Advantage you.Explore services
*
CLOUD MANAGED SERVICES Get immediate insights and continuous monitoring. Because real time beats point-in-time – every time.See how
*
SECURE PRODUCT DEVELOPMENT No one remembers second place. Get security right from the start – and be first to market.Learn more
*
COMPLIANCE MANAGEMENT From cost center to business generator – you’ll never look at compliance the same way again. Achieve confidence with compliance services See how with CoalfireOne ANSWERING YOUR CYBER QUESTIONS. EVEN THE ONES YOU DIDN’T KNOW TOASK.
From industry-leading research, to in-depth white papers, to timely commentary, find insights to prepare you for what’s now and what’s next in cybersecurity.__
1 / 2
__
*
3rd Annual PENETRATION RISK REPORT 2020Report
Get analysis on several alarming trends and discover the seven steps to overcoming these risks.Download
Compliance in the era of DIGITAL TRANSFORMATIONReport
Learn how to conquer complexity by transforming your compliance strategy and program execution.Download
*
2021 Cloud-native SECURITY TRENDS AND INSIGHTSReport
Confidently navigate the path to your secure cloud with insights and actionable guidance.Download
Smartest path TO YOUR SECURE CLOUDReport
Discover actionable guidance to ensure your success in the cloud.Download
*
3rd Annual PENETRATION RISK REPORT 2020Report
Get analysis on several alarming trends and discover the seven steps to overcoming these risks.Download
Compliance in the era of DIGITAL TRANSFORMATIONReport
Learn how to conquer complexity by transforming your compliance strategy and program execution.Download
*
2021 Cloud-native SECURITY TRENDS AND INSIGHTSReport
Confidently navigate the path to your secure cloud with insights and actionable guidance.Download
Smartest path TO YOUR SECURE CLOUDReport
Discover actionable guidance to ensure your success in the cloud.Download
Explore resources
Solutions
* Cloud security
* Threat and vulnerability management * Strategy, privacy, and risk * Cloud managed services * Secure product development * Compliance services* CoalfireOne�
-------------------------Industries
About
* Company overview
* Board Advisors and Directors * Diversity and inclusion* Executive Team
* Quality management * Richard E. Dakin Fund* Partners
Insights
* Blog
* Resources
* News and events
-------------------------Certificate program
Careers Contact us
Under attack? Take immediate action with our digital forensicsservices
.
* USA/CAN: (877) 224-8077 * FEDERAL: (703) 760-3801 * UK/EMEA: +44 161 537 1280 Copyright © 2021 Coalfire. All Rights Reserved. Privacy Policy and disclaimers Vulnerability discourse policy* __ Facebook
* __ Twitter
* __ LinkedIn
CoalfireOne login
*
Solutions
* Cloud security
* Threat and vulnerability management * Strategy, privacy, and risk * Cloud managed services * Secure product development * Compliance services* CoalfireOne�
Move forward, faster with solutions that span the entire cybersecurity lifecycle. Our experts help you develop a business-aligned strategy, build and operate an effective program, assess its effectiveness, and validate compliance with applicable regulations. * Cloud security strategy and maturity assessment Assess and improve your cloud security posture * Accelerated Cloud Engineering Streamline cloud development with compliant-ready environments * Infrastructure as Code development Build in cybersecurity right from the start * Cyber performance review Secure your cloud and IT perimeter with the latest boundary protectiontechniques
* Product applicability guides Increase customer confidence by promoting your security story * Security operations and cyber dashboards Make smart, strategic, and informed decisions about security events * Attack surface management Providing you unparalleled visibility into your security posture * CoalfireOne scanning Confirm system protection by quickly and easily running internal andexternal scans
* Penetration testing Discover and remediate critical vulnerabilities before they’reexploited
* Red team exercise
Boost your defenses by simulating a real-world attack * Threat modeling and attack simulation Maximize security investments and prove their effectiveness * Vulnerability assessment Strengthen your risk and compliance postures with a proactive approachto security
* Strategy+ cybersecurity program assessment Drive business success through cybersecurity strategy * CISO program management Strengthen your program by putting our experts to work* Privacy services
Turn privacy into a competitive advantage * M&A cyber due diligence Know what risks you’re facing with a merger or acquisition * Cyber risk assessment Uncover the risks present in your organization * Healthcare security risk analysis and advisory Safeguard protected health information and medical devices * Third-party risk management Hold vendors and partners to your security standards * Cyber breach services Don’t waste critical response time. Prepare for incidents beforethey happen.
* Accelerated Cloud Engineering services Reduce the operational burden associated with maintaining your FedRAMPboundary
* CoalfireOne scanning Confirm system protection by quickly and easily running internal andexternal scans
* Security operations and cyber dashboards Make smart, strategic, and informed decisions about security events * Application security Identify weaknesses that make your applications ripe for attacks * Internet of Things security Protect every aspect of your IoT solution* CMMC
Navigate your path to Cybersecurity Maturity Model Certification* DEA EPCS
Simplify and streamline DEA EPCS compliance* DoD RMF
Assess your systems to DoD RMF standards* FedRAMP
Get advisory and assessment services from the leading 3PAO* FFIEC
Reduce IT security risk in financial services* FISMA
Meet your FISMA authorization needs* HIPAA
Protect health data from threats and vulnerabilities* HITRUST
Receive guidance from an original HITRUST CSF Assessor firm* ISO management
Build a management system that complies with ISO standards* ITAR and EAR
Understand and address ITAR and EAR security obligations* NIST SP 800-171
Protect controlled unclassified information* PA-DSS/SSF
Validate the security of your payment applications* Payments services
Shape your overall payments program for current and future security * PCI DSS assessments and advisory Protect cardholder data from cyber attacks and breaches* PCI in the cloud
Simplify and optimize PCI compliance in the cloud* P2PE
Secure data as soon as it’s entered into a point device * PCI Forensic Investigator Suspect a cardholder data breach? Contact us now. * Report on compliance Provide the strongest validation of your PCI program* SOC and SSAE 18
Ensure trust and confidence in your security and financial controls * White paper services Demonstrate your commitment to cybersecurity * CoalfireOne overview Use our cloud-based platform to simplify compliance, reduce risks, and empower your enterprise’s security * CoalfireOne assessment and project management Manage and simplify your compliance projects and assessments with Coalfire through an easy-to-use collaboration portal * CoalfireOne scanning Quickly configure and manage requirements for internal and external vulnerability scanning and PCI ASV scans * CoalfireOne Compliance Management Maintain and improve security with year-round visibility and proactive management of your compliance program*
Industries
* Cloud service providers * Federal government * Financial services* Healthcare
* Higher education
* Hospitality
* Retail
* State & local government* Technology
* Utilities
While cybersecurity is a priority for enterprises worldwide, requirements differ greatly from one industry to the next. Coalfire understands industry nuances; we work with leading organizations in the cloud and technology, financial services, government, healthcare,and retail markets.
Coalfire can help cloud service providers prioritize the cyber risks to the company, and find the right cyber risk management and compliance efforts that keeps customer data secure, and helps differentiate products. "Success" at a government entity looks different at a commercial organization. Create cybersecurity solutions to support your mission goals with a team that understands your unique requirements. The financial services industry was built upon security and privacy. As cyber-attacks become more sophisticated, a strong vault and a guard at the door won’t offer any protection against phishing, DDoS attacks and IT infrastructure breaches. The continuum of care is a concept involving an integrated system of care that guides and tracks patients over time through a comprehensive array of health services spanning all levels of care. Interoperability is the central idea to this care continuum making it possible to have the right information at the right time for the right people to make the right decisions. Maintaining network and data security in any large organization is a major challenge for information systems departments. However, in the higher education environment, the protection of IT assets and sensitive information must be balanced with the need for ‘openness’ and academic freedom; making this a more difficult andcomplex task.
When it comes to cyber threats, the hospitality industry is not a friendly place. Hotels and resorts have proven to be a favorite target for cyber criminals who are looking for high transaction volume, large databases and low barriers to entry. The global retail industry has become the top target for cyber terrorists, and the impact of this onslaught has been staggering to merchants. To secure the complex IT infrastructure of a retail environment, merchants must embrace enterprise-wide cyber risk management practices that reduces risk, minimizes costs and provides security to their customers and their bottom line. Private enterprises serving government and state agencies need to be upheld to the same information management practices and standards as the organizations they serve. Coalfire has over 16 years of experience helping companies navigate increasing complex governance and risk standards for public institutions and their IT vendors. Technology innovations are enabling new methods for corporations and governments to operate and driving changes in consumer behavior. The companies delivering these technology products are facilitating business transformation that provides new operating models, increased efficiency and engagement with consumers as businesses seek a competitive advantage. Cybersecurity has entered the list of the top five concerns for U.S. electric utilities, and with good reason. According to the Department of Homeland Security, attacks on the utilities industry are rising "atan alarming rate".
*
About
* Company overview
* Board Advisors and Directors * Diversity and inclusion* Executive Team
* Partners
* Quality management * Richard E. Dakin Fund Since 2001, Coalfire has worked at the cutting edge of technology to help public and private sector organizations solve their toughest cybersecurity problems and fuel their overall success. Coalfire helps organizations comply with global financial, government, industry and healthcare mandates while helping build the IT infrastructure and security systems that will protect their business from security breaches and data theft. The company is a leading provider of IT advisory services for security in retail, payments, healthcare, financial services, higher education, hospitality, government and utilities. The Coalfire Board of Directors provides invaluable guidance for the organization and reflects Coalfire’s dedication to achieving successfor our customers.
Coalfire is committed to creating a culture that fosters diversity, inclusion, belonging, and equity. Coalfire’s executive leadership team comprises some of the most knowledgeable professionals in cybersecurity, representing many decades of experience leading and developing teams to outperform in meeting the security challenges of commercial and government clients. With diverse backgrounds in IT systems security, governmental security, compliance, and reducing risk while implementing the latest enabling technologies (such as the Cloud and IoT), our leaders understand the challenges customers face. Security is a team game. If your organization values both independence and security, perhaps we should become partners. With a passion for quality, Coalfire uses a process-driven quality approach to improve the customer experience and deliver unparalleledresults.
Created in honor of the late co-founder of Coalfire, the Richard E. Dakin Fund at The Denver Foundation is supporting scholarship programs at several universities for promising college students studying cybersecurity and related fields.*
Insights
* Blog
* Resources
* News and events
Get valuable insight into what matters most in cybersecurity, cloud, and compliance. Here you’ll find resources – including research reports, white papers, case studies, the Coalfire blog, and more – along with recent Coalfire news and upcoming events. Written by Coalfire's leadership team and our security experts, the Coalfire Blog covers the most important issues in cloud security, cybersecurity, and compliance. Find information that can help you approach cybersecurity programmatically. Explore our research reports, white papers, on-demand webinars, videos, case studies, and more. Stay up-to-date with all things Coalfire. Find upcoming events and webinars. See what’s new with your cybersecurity partner. And read the latest media coverage.*
Careers
*
Contact
* Locations
*
Search for:
Close
Top __
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0