Are you over 18 and want to see adult content?
More Annotations
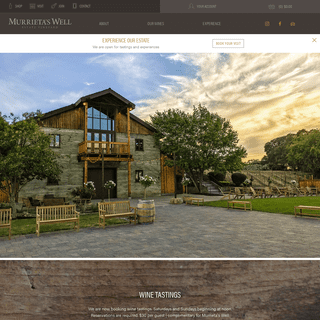
A complete backup of https://murrietaswell.com
Are you over 18 and want to see adult content?

A complete backup of https://myearthcam.com
Are you over 18 and want to see adult content?
A complete backup of https://allergii-bez.ru
Are you over 18 and want to see adult content?

A complete backup of https://ikit.org
Are you over 18 and want to see adult content?

A complete backup of https://caresource.com
Are you over 18 and want to see adult content?
A complete backup of https://mp-newmedia.com
Are you over 18 and want to see adult content?
A complete backup of https://801airsoft.com
Are you over 18 and want to see adult content?
A complete backup of https://boitempoeditorial.com.br
Are you over 18 and want to see adult content?
A complete backup of https://energeticforum.com
Are you over 18 and want to see adult content?
A complete backup of https://capdale.com
Are you over 18 and want to see adult content?
A complete backup of https://label-emmaus.co
Are you over 18 and want to see adult content?

A complete backup of https://xn--12cs3at5bh8htalb.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of thebeatlesrockband.com
Are you over 18 and want to see adult content?

A complete backup of biometricsinstitute.org
Are you over 18 and want to see adult content?
A complete backup of visualcomposer.com
Are you over 18 and want to see adult content?

A complete backup of proudtoserveagain.com
Are you over 18 and want to see adult content?
A complete backup of ilovecolors.com.ar
Are you over 18 and want to see adult content?
A complete backup of chilmarkresearch.com
Are you over 18 and want to see adult content?

A complete backup of dreamgirlsmovie.com
Are you over 18 and want to see adult content?

A complete backup of digicatapult.org.uk
Are you over 18 and want to see adult content?
Text
BAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period. BEST PRACTICES VS INANE PRACTICES or A Full Vindication of the Measures of Security Practitioners, from the Calumnies of their Enemies; In Answer to A Letter, Under the Signature of A. Gwinn. Whereby His Sophistry is exposed, his Cavils confuted, his Artifices detected, and his Wit ridiculed; in a General Address To the public, And A Particular Address To the dedicated members of the security community. Veritas magna est TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the LOOKING FOR VALUE IN EV CERTIFICATES BREAKING THE NEMUCODAES RANSOMWARE EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection. ABOUT - ADAM CAUDILLSEE MORE ON ADAMCAUDILL.COM CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERBAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period. BEST PRACTICES VS INANE PRACTICES or A Full Vindication of the Measures of Security Practitioners, from the Calumnies of their Enemies; In Answer to A Letter, Under the Signature of A. Gwinn. Whereby His Sophistry is exposed, his Cavils confuted, his Artifices detected, and his Wit ridiculed; in a General Address To the public, And A Particular Address To the dedicated members of the security community. Veritas magna est TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the LOOKING FOR VALUE IN EV CERTIFICATES BREAKING THE NEMUCODAES RANSOMWARE EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So afterADAM CAUDILL
Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection. ABOUT - ADAM CAUDILL Who am I? I’m Adam Caudill, a security engineer, a security researcher, a software developer, father, and atheist. I’m a lover of fine Japanese Katanas, a collector of bayonets and something of a technical elitist. I started my career in software development, though I’ve always had a passion for security. From the earliest days of my career, it’s been a focus, one that receives far SPEAKING - ADAM CAUDILL Speaking. I speak at various events on security, development, and related topics; as well as lead training classes. If you would like me to speak at your event or are interesting in training, feel free tocontact me.
30 DAYS OF BRAVE
Brave is a web browser available for multiple platforms that aims to provide additional security and privacy features – plus a novel monetization scheme for publishers. I gave it 30 days to see if it was worth using. I switched on all platforms I use to give it a fair shot, I normally use Chrome which made the switch less painful, though the results were very much mixed. There are some MASKING CREDIT CARDS FOR PCI Masking Credit Cards for PCI. PCI DSS, the security standard for companies that handle credit cards, defines a number of rules as to how credit cards are handled. One of those rules, 3.3, is defined as follows: Mask PAN when displayed (the first six and last four digits are the maximum number of digits to be displayed) PL/SQL DEVELOPER: NONEXISTENT ENCRYPTION (See here for another issue discovered during this research; Updates over HTTP & Command Execution.) PL/SQL Developer by Allround Automations has an option to store the user’s logon history with passwords – the passwords are encrypted with a proprietary algorithm. At this point, you should know how this is going to go. For those that don’t know, PL/SQL Developer is a tool for RESPONSIBLE DISCLOSURE IS WRONG The debate around how, where, and when to disclose a vulnerability – and of course to whom – is nearly as old as the industry that spawned the vulnerabilities. This debate will likely continue as long as humans are writing software. Unfortunately, the debate is hampered by poor terminology. Responsible disclosure is a computer security term describing a vulnerability disclosure model. It GOOGLE CHROME LEAKING CREDIT CARD DATA? While testing ccsrch I noticed a number that looked familiar – my debit card number. Now, being just a little paranoid, I don’t leave such information on my system unencrypted – so seeing it was a real surprise. But, here’s the real kicker: it was on my work PC, where it never should have been. But there it was, plain as day, in clear text. I spent a couple of minutes staring at the VICIDIAL: MULTIPLE VULNERABILITIES VICIDIAL (a.k.a. Asterisk GUI client) is an open-source dialer built on top of the Asterisk PBX. It’s written in PHP, and has a significant number of security issues. In addition to the open-source project, the company behind VICIDIAL, The Vicidial Group, also offers VICIDIAL in a hosted environment. SECURITY DONE WRONG: LEAKY FTP SERVER Update: I’ve just spoken to AMI, and received some very important information; so here are the key points and clarifications: To clarify, the ‘vendor’ I refer to is a customer of AMI; it is this customer’s public FTP server that exposed this information. Per AMI, the signing key included in the ‘Ivy Bridge’ archive is a default test key; AMI instructs customers to change the key ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection. ABOUT - ADAM CAUDILLSEE MORE ON ADAMCAUDILL.COM CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERBAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period. BEST PRACTICES VS INANE PRACTICES or A Full Vindication of the Measures of Security Practitioners, from the Calumnies of their Enemies; In Answer to A Letter, Under the Signature of A. Gwinn. Whereby His Sophistry is exposed, his Cavils confuted, his Artifices detected, and his Wit ridiculed; in a General Address To the public, And A Particular Address To the dedicated members of the security community. Veritas magna est TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the LOOKING FOR VALUE IN EV CERTIFICATES BREAKING THE NEMUCODAES RANSOMWARE EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection. ABOUT - ADAM CAUDILLSEE MORE ON ADAMCAUDILL.COM CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERBAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period. BEST PRACTICES VS INANE PRACTICES or A Full Vindication of the Measures of Security Practitioners, from the Calumnies of their Enemies; In Answer to A Letter, Under the Signature of A. Gwinn. Whereby His Sophistry is exposed, his Cavils confuted, his Artifices detected, and his Wit ridiculed; in a General Address To the public, And A Particular Address To the dedicated members of the security community. Veritas magna est TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the LOOKING FOR VALUE IN EV CERTIFICATES BREAKING THE NEMUCODAES RANSOMWARE EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So afterADAM CAUDILL
Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection. SPEAKING - ADAM CAUDILL Speaking. I speak at various events on security, development, and related topics; as well as lead training classes. If you would like me to speak at your event or are interesting in training, feel free tocontact me.
30 DAYS OF BRAVE
Brave is a web browser available for multiple platforms that aims to provide additional security and privacy features – plus a novel monetization scheme for publishers. I gave it 30 days to see if it was worth using. I switched on all platforms I use to give it a fair shot, I normally use Chrome which made the switch less painful, though the results were very much mixed. There are some PL/SQL DEVELOPER: HTTP TO COMMAND EXECUTION While looking into PL/SQL Developer – a very popular tool for working with Oracle databases, to see how it encrypts passwords I noticed something interesting. When testing Windows applications, I make it a habit to have Fiddler running, to see if there is any interesting traffic – and in this case, there certainly was. PL/SQL Developer has an update mechanism which retrieves a file MASKING CREDIT CARDS FOR PCI Masking Credit Cards for PCI. PCI DSS, the security standard for companies that handle credit cards, defines a number of rules as to how credit cards are handled. One of those rules, 3.3, is defined as follows: Mask PAN when displayed (the first six and last four digits are the maximum number of digits to be displayed) PL/SQL DEVELOPER: NONEXISTENT ENCRYPTION (See here for another issue discovered during this research; Updates over HTTP & Command Execution.) PL/SQL Developer by Allround Automations has an option to store the user’s logon history with passwords – the passwords are encrypted with a proprietary algorithm. At this point, you should know how this is going to go. For those that don’t know, PL/SQL Developer is a tool for RESPONSIBLE DISCLOSURE IS WRONG The debate around how, where, and when to disclose a vulnerability – and of course to whom – is nearly as old as the industry that spawned the vulnerabilities. This debate will likely continue as long as humans are writing software. Unfortunately, the debate is hampered by poor terminology. Responsible disclosure is a computer security term describing a vulnerability disclosure model. It SECURITY DONE WRONG: LEAKY FTP SERVER Update: I’ve just spoken to AMI, and received some very important information; so here are the key points and clarifications: To clarify, the ‘vendor’ I refer to is a customer of AMI; it is this customer’s public FTP server that exposed this information. Per AMI, the signing key included in the ‘Ivy Bridge’ archive is a default test key; AMI instructs customers to change the key VICIDIAL: MULTIPLE VULNERABILITIES VICIDIAL (a.k.a. Asterisk GUI client) is an open-source dialer built on top of the Asterisk PBX. It’s written in PHP, and has a significant number of security issues. In addition to the open-source project, the company behind VICIDIAL, The Vicidial Group, also offers VICIDIAL in a hosted environment. GOOGLE CHROME LEAKING CREDIT CARD DATA? While testing ccsrch I noticed a number that looked familiar – my debit card number. Now, being just a little paranoid, I don’t leave such information on my system unencrypted – so seeing it was a real surprise. But, here’s the real kicker: it was on my work PC, where it never should have been. But there it was, plain as day, in clear text. I spent a couple of minutes staring at the ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection.BLOG - ADAM CAUDILL
May 9, 2021 | 9 minutes read. This is part of the Insane Ideas series. A group of blog posts that detail ideas, possible projects, or concepts that may be of interest. These are ideas that I don’t plan to pursue, and are thus available to any and all that would like to do something with them. I hope you find some inspiration – or at least CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERBAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period. BEST PRACTICES VS INANE PRACTICES or A Full Vindication of the Measures of Security Practitioners, from the Calumnies of their Enemies; In Answer to A Letter, Under the Signature of A. Gwinn. Whereby His Sophistry is exposed, his Cavils confuted, his Artifices detected, and his Wit ridiculed; in a General Address To the public, And A Particular Address To the dedicated members of the security community. Veritas magna est TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around theBITCOIN IS A CULT
BREAKING THE NEMUCODAES RANSOMWARE RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after EXPLOITING THE JACKSON RCE: CVE-2017-7525 ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection.BLOG - ADAM CAUDILL
May 9, 2021 | 9 minutes read. This is part of the Insane Ideas series. A group of blog posts that detail ideas, possible projects, or concepts that may be of interest. These are ideas that I don’t plan to pursue, and are thus available to any and all that would like to do something with them. I hope you find some inspiration – or at least CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERBAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period. BEST PRACTICES VS INANE PRACTICES or A Full Vindication of the Measures of Security Practitioners, from the Calumnies of their Enemies; In Answer to A Letter, Under the Signature of A. Gwinn. Whereby His Sophistry is exposed, his Cavils confuted, his Artifices detected, and his Wit ridiculed; in a General Address To the public, And A Particular Address To the dedicated members of the security community. Veritas magna est TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around theBITCOIN IS A CULT
BREAKING THE NEMUCODAES RANSOMWARE RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after EXPLOITING THE JACKSON RCE: CVE-2017-7525 ABOUT - ADAM CAUDILL Who am I? I’m Adam Caudill, a security engineer, a security researcher, a software developer, father, and atheist. I’m a lover of fine Japanese Katanas, a collector of bayonets and something of a technical elitist. I started my career in software development, though I’ve always had a passion for security. From the earliest days of my career, it’s been a focus, one that receives far ESSAYS - ADAM CAUDILL A friend of mine recently asked for my thoughts on leading people who have more experience or expertise in a topic than they do; this is an important question and one that I felt deserved more thought and exploration. Leading people can be difficult, but when leading people that know more than you do about a given topic, it’s a differentSECURITY RESEARCH
Dovestones Software AD Self Password Reset (CVE-2015-8267) Software AD Self Password Reset v3.0 by Dovestones Software contains a critical vulnerability in the password change functionality, that allows unauthenticated users to change the password of arbitrary accounts. The vendor has been working with customers to upgrade them to a fixedversion.
SPEAKING - ADAM CAUDILL Speaking. I speak at various events on security, development, and related topics; as well as lead training classes. If you would like me to speak at your event or are interesting in training, feel free tocontact me.
PGP & CONTACT INFO
Messaging / Others One of the best ways to get me is via Twitter, @adamcaudill – this or email (see below) gets the fastest response. I’m also available on Signal for those that have my phone number (don’t feel bad if you don’t, not many people do). Email Address: adam@adamcaudill.com Want to validate that I sent an email, or send me something privately? See below for my public PGP key THE (QUESTIONABLE) FUTURE OF YAWAST The last release of YAWAST was on January 1, 2020; while the release history was sometimes unpredictable, the goal was a new release each month with new features and bug fixes. I intentionally took January off from the project. In February, I left the company I was at; the team of penetration testers there had helped to inspire new features while looking for ways to make them more BREAKING THE NEMUCODAES RANSOMWARE The Nemucod ransomware has been around, in various incarnations, for some time. Recently a new variant started spreading via email claiming to be from UPS. This new version changed how files are encrypted, clearly in an attempt to fix its prior issue of being able to decrypt files without paying the ransom, and as this is a new version, no decryptor was available1. My friends at Savage PL/SQL DEVELOPER: NONEXISTENT ENCRYPTION (See here for another issue discovered during this research; Updates over HTTP & Command Execution.) PL/SQL Developer by Allround Automations has an option to store the user’s logon history with passwords – the passwords are encrypted with a proprietary algorithm. At this point, you should know how this is going to go. For those that don’t know, PL/SQL Developer is a tool for SECURITY DONE WRONG: LEAKY FTP SERVER Update: I’ve just spoken to AMI, and received some very important information; so here are the key points and clarifications: To clarify, the ‘vendor’ I refer to is a customer of AMI; it is this customer’s public FTP server that exposed this information. Per AMI, the signing key included in the ‘Ivy Bridge’ archive is a default test key; AMI instructs customers to change the key UPEK WINDOWS PASSWORD DECRYPTION UPEK Windows Password Decryption. On August 28th ElcomSoft announced that they had determined a method to extract Windows passwords from the registry for users of UPEK’s fingerprint readers and Protector Suite software (UPEK is now owned by AuthenTec, which is now owned by Apple). What they didn’t announce was the technical details of how ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection.BLOG - ADAM CAUDILL
May 9, 2021 | 9 minutes read. This is part of the Insane Ideas series. A group of blog posts that detail ideas, possible projects, or concepts that may be of interest. These are ideas that I don’t plan to pursue, and are thus available to any and all that would like to do something with them. I hope you find some inspiration – or at least CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERBAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period. BEST PRACTICES VS INANE PRACTICES or A Full Vindication of the Measures of Security Practitioners, from the Calumnies of their Enemies; In Answer to A Letter, Under the Signature of A. Gwinn. Whereby His Sophistry is exposed, his Cavils confuted, his Artifices detected, and his Wit ridiculed; in a General Address To the public, And A Particular Address To the dedicated members of the security community. Veritas magna est TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around theBITCOIN IS A CULT
BREAKING THE NEMUCODAES RANSOMWARE RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after EXPLOITING THE JACKSON RCE: CVE-2017-7525 ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection.BLOG - ADAM CAUDILL
May 9, 2021 | 9 minutes read. This is part of the Insane Ideas series. A group of blog posts that detail ideas, possible projects, or concepts that may be of interest. These are ideas that I don’t plan to pursue, and are thus available to any and all that would like to do something with them. I hope you find some inspiration – or at least CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERBAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period. BEST PRACTICES VS INANE PRACTICES or A Full Vindication of the Measures of Security Practitioners, from the Calumnies of their Enemies; In Answer to A Letter, Under the Signature of A. Gwinn. Whereby His Sophistry is exposed, his Cavils confuted, his Artifices detected, and his Wit ridiculed; in a General Address To the public, And A Particular Address To the dedicated members of the security community. Veritas magna est TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around theBITCOIN IS A CULT
BREAKING THE NEMUCODAES RANSOMWARE RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after EXPLOITING THE JACKSON RCE: CVE-2017-7525 ABOUT - ADAM CAUDILL Who am I? I’m Adam Caudill, a security engineer, a security researcher, a software developer, father, and atheist. I’m a lover of fine Japanese Katanas, a collector of bayonets and something of a technical elitist. I started my career in software development, though I’ve always had a passion for security. From the earliest days of my career, it’s been a focus, one that receives far ESSAYS - ADAM CAUDILL A friend of mine recently asked for my thoughts on leading people who have more experience or expertise in a topic than they do; this is an important question and one that I felt deserved more thought and exploration. Leading people can be difficult, but when leading people that know more than you do about a given topic, it’s a differentSECURITY RESEARCH
Dovestones Software AD Self Password Reset (CVE-2015-8267) Software AD Self Password Reset v3.0 by Dovestones Software contains a critical vulnerability in the password change functionality, that allows unauthenticated users to change the password of arbitrary accounts. The vendor has been working with customers to upgrade them to a fixedversion.
SPEAKING - ADAM CAUDILL Speaking. I speak at various events on security, development, and related topics; as well as lead training classes. If you would like me to speak at your event or are interesting in training, feel free tocontact me.
PGP & CONTACT INFO
Messaging / Others One of the best ways to get me is via Twitter, @adamcaudill – this or email (see below) gets the fastest response. I’m also available on Signal for those that have my phone number (don’t feel bad if you don’t, not many people do). Email Address: adam@adamcaudill.com Want to validate that I sent an email, or send me something privately? See below for my public PGP key THE (QUESTIONABLE) FUTURE OF YAWAST The last release of YAWAST was on January 1, 2020; while the release history was sometimes unpredictable, the goal was a new release each month with new features and bug fixes. I intentionally took January off from the project. In February, I left the company I was at; the team of penetration testers there had helped to inspire new features while looking for ways to make them more BREAKING THE NEMUCODAES RANSOMWARE The Nemucod ransomware has been around, in various incarnations, for some time. Recently a new variant started spreading via email claiming to be from UPS. This new version changed how files are encrypted, clearly in an attempt to fix its prior issue of being able to decrypt files without paying the ransom, and as this is a new version, no decryptor was available1. My friends at Savage PL/SQL DEVELOPER: NONEXISTENT ENCRYPTION (See here for another issue discovered during this research; Updates over HTTP & Command Execution.) PL/SQL Developer by Allround Automations has an option to store the user’s logon history with passwords – the passwords are encrypted with a proprietary algorithm. At this point, you should know how this is going to go. For those that don’t know, PL/SQL Developer is a tool for SECURITY DONE WRONG: LEAKY FTP SERVER Update: I’ve just spoken to AMI, and received some very important information; so here are the key points and clarifications: To clarify, the ‘vendor’ I refer to is a customer of AMI; it is this customer’s public FTP server that exposed this information. Per AMI, the signing key included in the ‘Ivy Bridge’ archive is a default test key; AMI instructs customers to change the key UPEK WINDOWS PASSWORD DECRYPTION UPEK Windows Password Decryption. On August 28th ElcomSoft announced that they had determined a method to extract Windows passwords from the registry for users of UPEK’s fingerprint readers and Protector Suite software (UPEK is now owned by AuthenTec, which is now owned by Apple). What they didn’t announce was the technical details of how ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection.BLOG - ADAM CAUDILL
May 9, 2021 | 9 minutes read. This is part of the Insane Ideas series. A group of blog posts that detail ideas, possible projects, or concepts that may be of interest. These are ideas that I don’t plan to pursue, and are thus available to any and all that would like to do something with them. I hope you find some inspiration – or at least ABOUT - ADAM CAUDILLSEE MORE ON ADAMCAUDILL.COM CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNER ESSAYS - ADAM CAUDILL A friend of mine recently asked for my thoughts on leading people who have more experience or expertise in a topic than they do; this is an important question and one that I felt deserved more thought and exploration. Leading people can be difficult, but when leading people that know more than you do about a given topic, it’s a differentTHE HIBBING TEST
The idea for “The Hibbing Test” began in 2015 with a documentry on how humans perceive risk, how they would bet or cash out when playing with free money, and what that exposed about how they saw the world. This story sees a world that becomes dominated by that difference, with one group given power, and the other religated due to their view of the world - and how risk perception plays into it. TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the BREAKING THE NEMUCODAES RANSOMWARE EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection.BLOG - ADAM CAUDILL
May 9, 2021 | 9 minutes read. This is part of the Insane Ideas series. A group of blog posts that detail ideas, possible projects, or concepts that may be of interest. These are ideas that I don’t plan to pursue, and are thus available to any and all that would like to do something with them. I hope you find some inspiration – or at least ABOUT - ADAM CAUDILLSEE MORE ON ADAMCAUDILL.COM CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNER ESSAYS - ADAM CAUDILL A friend of mine recently asked for my thoughts on leading people who have more experience or expertise in a topic than they do; this is an important question and one that I felt deserved more thought and exploration. Leading people can be difficult, but when leading people that know more than you do about a given topic, it’s a differentTHE HIBBING TEST
The idea for “The Hibbing Test” began in 2015 with a documentry on how humans perceive risk, how they would bet or cash out when playing with free money, and what that exposed about how they saw the world. This story sees a world that becomes dominated by that difference, with one group given power, and the other religated due to their view of the world - and how risk perception plays into it. TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the BREAKING THE NEMUCODAES RANSOMWARE EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after ESSAYS - ADAM CAUDILL Write Like You Are Running Out of Time. November 28, 2020 | 7 minutes read . The cultural phenomenon that is Hamilton, brought back to the forefront due to its streaming release, is an artistic feat, but it also serves as an opportunity to refresh our memories on the history behind these characters, and look for opportunities to learn lessonsthat apply today.
SECURITY RESEARCH
Dovestones Software AD Self Password Reset (CVE-2015-8267) Software AD Self Password Reset v3.0 by Dovestones Software contains a critical vulnerability in the password change functionality, that allows unauthenticated users to change the password of arbitrary accounts. The vendor has been working with customers to upgrade them to a fixedversion.
PHOTOGRAPHY
The HTML5 Herald. About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if Iget too bored.
SPEAKING - ADAM CAUDILL Speaking. I speak at various events on security, development, and related topics; as well as lead training classes. If you would like me to speak at your event or are interesting in training, feel free tocontact me.
BAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period.PGP & CONTACT INFO
Messaging / Others One of the best ways to get me is via Twitter, @adamcaudill – this or email (see below) gets the fastest response. I’m also available on Signal for those that have my phone number (don’t feel bad if you don’t, not many people do). Email Address: adam@adamcaudill.com Want to validate that I sent an email, or send me something privately? See below for my public PGP key UTILITARIAN NIGHTMARE: OFFENSIVE SECURITY TOOLS The HTML5 Herald. Or: Ethical Decision Making for Security Researchers. There has been much discussion recently on the appropriateness of releasing offensive security tools to the world – while this storm has largely come and gone on Twitter, it’s something I still find myself thinking about. LOOKING FOR VALUE IN EV CERTIFICATES EV (Extended Validation) Finally, we have EV, the most expensive at roughly $300 (though may be as much as $1,000) per year, EV certificates require the most detailed verification process, and extend upon the requirements of OV certificates. Documents such as proof of having a bank account, proof of address, more detailed requirements on proofBITCOIN IS A CULT
Bitcoin is a Cult. June 22, 2018 | 9 minutes read. The Bitcoin community has changed greatly over the years; from technophiles that could explain a Merkle tree in their sleep, to speculators driven by the desire for a quick profit & blockchain startups seeking billion dollar valuations led by people who don’t even know what a Merkletree is.
SECURITY DONE WRONG: LEAKY FTP SERVER Update: I’ve just spoken to AMI, and received some very important information; so here are the key points and clarifications: To clarify, the ‘vendor’ I refer to is a customer of AMI; it is this customer’s public FTP server that exposed this information. Per AMI, the signing key included in the ‘Ivy Bridge’ archive is a default test key; AMI instructs customers to change the key ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE The HTML5 Herald. Exploiting the Jackson RCE: CVE-2017-7525. October 4, 2017 | 4 minutes read . Earlier this year, a vulnerability was discovered in the Jackson data-binding library, a library for Java that allows developers to easily serialize Java objects to JSON and vice versa, that allowed an attacker to exploit deserialization to achieve Remote Code Execution on the server. ESSAYS - ADAM CAUDILL Write Like You Are Running Out of Time. November 28, 2020 | 7 minutes read . The cultural phenomenon that is Hamilton, brought back to the forefront due to its streaming release, is an artistic feat, but it also serves as an opportunity to refresh our memories on the history behind these characters, and look for opportunities to learn lessonsthat apply today.
ABOUT - ADAM CAUDILLSEE MORE ON ADAMCAUDILL.COMBLOG - ADAM CAUDILL
About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if I get too bored. CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERTHE HIBBING TEST
The idea for “The Hibbing Test” began in 2015 with a documentry on how humans perceive risk, how they would bet or cash out when playing with free money, and what that exposed about how they saw the world. This story sees a world that becomes dominated by that difference, with one group given power, and the other religated due to their view of the world - and how risk perception plays into it. BREAKING THE NEMUCODAES RANSOMWARE TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE The HTML5 Herald. Exploiting the Jackson RCE: CVE-2017-7525. October 4, 2017 | 4 minutes read . Earlier this year, a vulnerability was discovered in the Jackson data-binding library, a library for Java that allows developers to easily serialize Java objects to JSON and vice versa, that allowed an attacker to exploit deserialization to achieve Remote Code Execution on the server. ESSAYS - ADAM CAUDILL Write Like You Are Running Out of Time. November 28, 2020 | 7 minutes read . The cultural phenomenon that is Hamilton, brought back to the forefront due to its streaming release, is an artistic feat, but it also serves as an opportunity to refresh our memories on the history behind these characters, and look for opportunities to learn lessonsthat apply today.
ABOUT - ADAM CAUDILLSEE MORE ON ADAMCAUDILL.COMBLOG - ADAM CAUDILL
About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if I get too bored. CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERTHE HIBBING TEST
The idea for “The Hibbing Test” began in 2015 with a documentry on how humans perceive risk, how they would bet or cash out when playing with free money, and what that exposed about how they saw the world. This story sees a world that becomes dominated by that difference, with one group given power, and the other religated due to their view of the world - and how risk perception plays into it. BREAKING THE NEMUCODAES RANSOMWARE TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after ESSAYS - ADAM CAUDILL Write Like You Are Running Out of Time. November 28, 2020 | 7 minutes read . The cultural phenomenon that is Hamilton, brought back to the forefront due to its streaming release, is an artistic feat, but it also serves as an opportunity to refresh our memories on the history behind these characters, and look for opportunities to learn lessonsthat apply today.
SPEAKING - ADAM CAUDILL About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if I get too bored.PHOTOGRAPHY
The HTML5 Herald. About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if Iget too bored.
SECURITY RESEARCH
Exploiting the Jackson RCE: CVE-2017-7525. October 4, 2017 | 4 minutes read . Earlier this year, a vulnerability was discovered in the Jackson data-binding library, a library for Java that allows developers to easily serialize Java objects to JSON and vice versa, that allowed an attacker to exploit deserialization to achieve Remote Code Execution on the server.BAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period.PGP & CONTACT INFO
Messaging / Others One of the best ways to get me is via Twitter, @adamcaudill – this or email (see below) gets the fastest response. I’m also available on Signal for those that have my phone number (don’t feel bad if you don’t, not many people do). Email Address: adam@adamcaudill.com Want to validate that I sent an email, or send me something privately? See below for my public PGP key UTILITARIAN NIGHTMARE: OFFENSIVE SECURITY TOOLS The HTML5 Herald. Or: Ethical Decision Making for Security Researchers. There has been much discussion recently on the appropriateness of releasing offensive security tools to the world – while this storm has largely come and gone on Twitter, it’s something I still find myself thinking about. LOOKING FOR VALUE IN EV CERTIFICATES About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if I get too bored.BITCOIN IS A CULT
The HTML5 Herald. The Bitcoin community has changed greatly over the years; from technophiles that could explain a Merkle tree in their sleep, to speculators driven by the desire for a quick profit & blockchain startups seeking billion dollar valuations led by people who don’t even know what a Merkle tree is. As the years have gone on, a zealotry has been building around Bitcoin and other SECURITY DONE WRONG: LEAKY FTP SERVER Update: I’ve just spoken to AMI, and received some very important information; so here are the key points and clarifications: To clarify, the ‘vendor’ I refer to is a customer of AMI; it is this customer’s public FTP server that exposed this information. Per AMI, the signing key included in the ‘Ivy Bridge’ archive is a default test key; AMI instructs customers to change the key ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE The HTML5 Herald. Exploiting the Jackson RCE: CVE-2017-7525. October 4, 2017 | 4 minutes read . Earlier this year, a vulnerability was discovered in the Jackson data-binding library, a library for Java that allows developers to easily serialize Java objects to JSON and vice versa, that allowed an attacker to exploit deserialization to achieve Remote Code Execution on the server. ESSAYS - ADAM CAUDILL Write Like You Are Running Out of Time. November 28, 2020 | 7 minutes read . The cultural phenomenon that is Hamilton, brought back to the forefront due to its streaming release, is an artistic feat, but it also serves as an opportunity to refresh our memories on the history behind these characters, and look for opportunities to learn lessonsthat apply today.
ABOUT - ADAM CAUDILLSEE MORE ON ADAMCAUDILL.COMBLOG - ADAM CAUDILL
About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if I get too bored. CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERTHE HIBBING TEST
The idea for “The Hibbing Test” began in 2015 with a documentry on how humans perceive risk, how they would bet or cash out when playing with free money, and what that exposed about how they saw the world. This story sees a world that becomes dominated by that difference, with one group given power, and the other religated due to their view of the world - and how risk perception plays into it. BREAKING THE NEMUCODAES RANSOMWARE TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after ADAM CAUDILLBLOGESSAYSRESEARCHSPEAKINGABOUTARCHIVE The HTML5 Herald. Exploiting the Jackson RCE: CVE-2017-7525. October 4, 2017 | 4 minutes read . Earlier this year, a vulnerability was discovered in the Jackson data-binding library, a library for Java that allows developers to easily serialize Java objects to JSON and vice versa, that allowed an attacker to exploit deserialization to achieve Remote Code Execution on the server. ESSAYS - ADAM CAUDILL Write Like You Are Running Out of Time. November 28, 2020 | 7 minutes read . The cultural phenomenon that is Hamilton, brought back to the forefront due to its streaming release, is an artistic feat, but it also serves as an opportunity to refresh our memories on the history behind these characters, and look for opportunities to learn lessonsthat apply today.
ABOUT - ADAM CAUDILLSEE MORE ON ADAMCAUDILL.COMBLOG - ADAM CAUDILL
About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if I get too bored. CCSRCH – OPEN SOURCE PAN / CREDIT CARD SCANNERTHE HIBBING TEST
The idea for “The Hibbing Test” began in 2015 with a documentry on how humans perceive risk, how they would bet or cash out when playing with free money, and what that exposed about how they saw the world. This story sees a world that becomes dominated by that difference, with one group given power, and the other religated due to their view of the world - and how risk perception plays into it. BREAKING THE NEMUCODAES RANSOMWARE TESTING FOR SWEET32 WITH YAWAST Testing for SWEET32 isn’t simple – when the vulnerability was announced, some argued that the best solution was to assume that if a TLS server supported any of the 3DES cipher suites, consider it vulnerable. The problem is, it’s not that simple. On my employer’s corporate blog, I wrote about practical advice for dealing with SWEET32 – and pointed out that there are ways around the EXPLOITING THE JACKSON RCE: CVE-2017-7525 RUNNING REGEDIT AS SYSTEM While facing an interesting research challenge, digging into the inner working of Windows, I realized that I needed to change a registry value. That’s simple enough, I fire up RegEdit, make the change, then politely as RegEdit knows how, it told me that I couldn’t change the value! Being one that hates when my computer tells me I can’t do something, I had to find another option. So after ESSAYS - ADAM CAUDILL Write Like You Are Running Out of Time. November 28, 2020 | 7 minutes read . The cultural phenomenon that is Hamilton, brought back to the forefront due to its streaming release, is an artistic feat, but it also serves as an opportunity to refresh our memories on the history behind these characters, and look for opportunities to learn lessonsthat apply today.
SPEAKING - ADAM CAUDILL About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if I get too bored.PHOTOGRAPHY
The HTML5 Herald. About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if Iget too bored.
SECURITY RESEARCH
Exploiting the Jackson RCE: CVE-2017-7525. October 4, 2017 | 4 minutes read . Earlier this year, a vulnerability was discovered in the Jackson data-binding library, a library for Java that allows developers to easily serialize Java objects to JSON and vice versa, that allowed an attacker to exploit deserialization to achieve Remote Code Execution on the server.BAYONET COLLECTION
This is a new hobby that I picked up recently after my father gave me a bayonet as a surprise gift. I’ve been rather hooked since then. Here you’ll find the gallery for my small but growing collection. Turkish M1935 This is my first bayonet, a Turkish Model 1935, in a rather impressive condition. Czech VZ24 I believe this is a Czech VZ24 bayonet, which would place in in the WWII time period.PGP & CONTACT INFO
Messaging / Others One of the best ways to get me is via Twitter, @adamcaudill – this or email (see below) gets the fastest response. I’m also available on Signal for those that have my phone number (don’t feel bad if you don’t, not many people do). Email Address: adam@adamcaudill.com Want to validate that I sent an email, or send me something privately? See below for my public PGP key UTILITARIAN NIGHTMARE: OFFENSIVE SECURITY TOOLS The HTML5 Herald. Or: Ethical Decision Making for Security Researchers. There has been much discussion recently on the appropriateness of releasing offensive security tools to the world – while this storm has largely come and gone on Twitter, it’s something I still find myself thinking about. LOOKING FOR VALUE IN EV CERTIFICATES About Me. I am a Principal Security Engineer at 1Password, researcher and software developer with more than 20 years of experience.. I primarily focus on application security, secure communications, and cryptography, though often research new areas if I get too bored.BITCOIN IS A CULT
The HTML5 Herald. The Bitcoin community has changed greatly over the years; from technophiles that could explain a Merkle tree in their sleep, to speculators driven by the desire for a quick profit & blockchain startups seeking billion dollar valuations led by people who don’t even know what a Merkle tree is. As the years have gone on, a zealotry has been building around Bitcoin and other SECURITY DONE WRONG: LEAKY FTP SERVER Update: I’ve just spoken to AMI, and received some very important information; so here are the key points and clarifications: To clarify, the ‘vendor’ I refer to is a customer of AMI; it is this customer’s public FTP server that exposed this information. Per AMI, the signing key included in the ‘Ivy Bridge’ archive is a default test key; AMI instructs customers to change the keyADAM CAUDILL
* __
* __
_Security Engineer, Researcher, & Developer_* __Blog
* __Essays
* __Research
* __Speaking
* __Photography
* __Writing
* __About
RECENT BLOG POSTS
*
BEST PRACTICES VS INANE PRACTICES May 18, 2021 | 16 minutes read or A Full Vindication of the Measures of Security Practitioners, from the Calumnies of their Enemies; In Answer to A Letter, Under the Signature of A. Gwinn. Whereby His Sophistry is exposed, his Cavils confuted, his Artifices detected, and his Wit ridiculed; in a General Address To the public, And A Particular Address To the dedicated members of the security community. Veritas magna est & prœvalebit. Friends and Colleagues, It was hardly to be expected that any man could be so presumptuous as to openly controvert the equity, wisdom, and authority of the measures, adopted by the practitioners of information security: a group truly dedicated to the protection of business and individuals around the world!Read more…
-------------------------*
INSANE IDEAS: STOCK IN PEOPLE May 9, 2021 | 9 minutes read This is part of the Insane Ideas series. A group of blog posts that detail ideas, possible projects, or concepts that may be of interest. These are ideas that I don’t plan to pursue, and are thus available to any and all that would like to do something with them. I hope you find some inspiration – or at least some amusement in this. There are many ways to invest in a variety of things, though there is one hugely promising front that has barely begun to emerge, that could have massive potential for profit, and incredible ramifications: the ability to invest in individuals.Read more…
-------------------------*
PROPOSAL: ASSOCIATION OF SECURITY RESEARCHERS December 23, 2020 | 6 minutes read Security researchers play an important role in the industry, though one that doesn’t always receive the support needed. In this post, I am proposing the creation of a new non-profit entity, the International Association of Information Security Research Professionals (IAISRP), as a supporting group to push research forward, and provide the tools and resources to improve the quality of work, and the quality of life for those involved in this vital work.Read more…
------------------------- All Blog Posts | Archive RECENT SECURITY RESEARCH*
EXPLOITING THE JACKSON RCE: CVE-2017-7525 October 4, 2017 | 4 minutes read Earlier this year, a vulnerability was discovered in the Jackson data-binding library, a library for Java that allows developers to easily serialize Java objects to JSON and vice versa, that allowed an attacker to exploit deserialization to achieve Remote Code Execution on the server. This vulnerability didn’t seem to get much attention, and even less documentation. Given that this is an easily exploited Remote Code Execution vulnerability with little documentation, I’m sharing my notes on it.Read more…
-------------------------*
BREAKING THE NEMUCODAES RANSOMWARE July 13, 2017 | 5 minutes read The Nemucod ransomware has been around, in various incarnations, for some time. Recently a new variant started spreading via email claiming to be from UPS. This new version changed how files are encrypted, clearly in an attempt to fix its prior issue of being able to decrypt files without paying the ransom, and as this is a new version, no decryptor was available1. My friends at Savage Security contacted me to help save the data of one of their clients; I immediately began studying the cryptography related portions of the software, while the Savage Security team was busy looking at other portions.Read more…
-------------------------*
PL/SQL DEVELOPER: HTTP TO COMMAND EXECUTION May 1, 2016 | 4 minutes read While looking into PL/SQL Developer – a very popular tool for working with Oracle databases, to see how it encrypts passwords I noticed something interesting. When testing Windows applications, I make it a habit to have Fiddler running, to see if there is any interesting traffic – and in this case, there certainly was. PL/SQL Developer has an update mechanism which retrieves a file containing information about available updates to PL/SQL Developer and other components; this file is retrieved via HTTP, meaning that an attacker in a privileged network position could modify this file.Read more…
-------------------------PROJECTS
* YAWAST – The YAWAST Antecedent Web Application Security Toolkit. * libsodium-net – The .NET library for libsodium ; a modern and easy-to-usecrypto library.
* ccsrch – Cross-platform credit card (PAN) search tool for security assessments. * Underhanded Crypto Contest – A competition to write or modify crypto code that appears to be secure, but actually does something evil.INSANE IDEAS
The _Insane Ideas_ series is a group of blog posts the detail various ideas that I found interesting, but didn’t pursue due to time restrictions or other factors. The goal of publishing these ideas is to make the concept available to others, in hopes that they will pursue the idea – or at least find amusement in it.*
INSANE IDEAS: STOCK IN PEOPLE May 9, 2021 | 9 minutes read This is part of the Insane Ideas series. A group of blog posts that detail ideas, possible projects, or concepts that may be of interest. These are ideas that I don’t plan to pursue, and are thus available to any and all that would like to do something with them. I hope you find some inspiration – or at least some amusement in this. There are many ways to invest in a variety of things, though there is one hugely promising front that has barely begun to emerge, that could have massive potential for profit, and incredible ramifications: the ability to invest in individuals.Read more…
-------------------------*
INSANE IDEAS: BLOCKCHAIN-BASED AUTOMATED INVESTMENT SYSTEM September 10, 2019 | 12 minutes read This is part of the Insane Ideas series. A group of blog posts that detail ideas, possible projects, or concepts that may be of interest. These are ideas that I don’t plan to pursue, and are thus available to any and all that would like to do something with them. I hope you find some inspiration – or at least some amusement in this. A few months ago I was reading about high-frequency trading (HFT) – algorithms that allow investors to make money essentially out of nothing by executing trades at high speed, and leveraging the natural (and artificial) volatility of the market.Read more…
-------------------------ABOUT ADAM CAUDILL
Adam Caudill is a security consultant with over 20 years of experience in security and software development; with a focus on application security, secure communications, and cryptography. Active blogger, open source contributor, and advocate for user privacy and protection. His work has been cited by many media outlets and publications around the world, from CNN to Wired and countless others.ABOUT ME
I am a Principal Security Engineer at 1Password , researcher and software developer with more than 20 years of experience. I primarily focus on application security, secure communications, and cryptography, though often research new areas if I get too bored. I write about my research and security in general, development and software design, and whatever hobby has my attention at the moment.Contact
DISCLAIMER
Opinions expressed here are solely those of Adam Caudill, and do not represent the views of his employer, or any other person or entity.CONTACT & MEDIA
If you have any questions, please feel free to contact me , I will try to respond as quickly as possible.COPYRIGHT
Copyright © 2003 – 2021 Adam Caudill. Fair use is respected; though please provide proper attribution.Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0