Are you over 18 and want to see adult content?
More Annotations
A complete backup of boldcommerce.com
Are you over 18 and want to see adult content?

A complete backup of trouconulohgal.gq
Are you over 18 and want to see adult content?

A complete backup of siteworthchecker.com
Are you over 18 and want to see adult content?

A complete backup of stadt-waldkirch.de
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://muskegonartmuseum.org
Are you over 18 and want to see adult content?
A complete backup of https://graphics-illustrations.com
Are you over 18 and want to see adult content?
A complete backup of https://muzey-factov.ru
Are you over 18 and want to see adult content?

A complete backup of https://pokerfirma.com
Are you over 18 and want to see adult content?
A complete backup of https://photographerstory.com
Are you over 18 and want to see adult content?
A complete backup of https://energieforschung.de
Are you over 18 and want to see adult content?
A complete backup of https://droidapp.nl
Are you over 18 and want to see adult content?
A complete backup of https://infraredtraining.com
Are you over 18 and want to see adult content?
A complete backup of https://erektionstabletter-se.eu
Are you over 18 and want to see adult content?
A complete backup of https://nightclub.com
Are you over 18 and want to see adult content?

A complete backup of https://enterprisetech.com
Are you over 18 and want to see adult content?
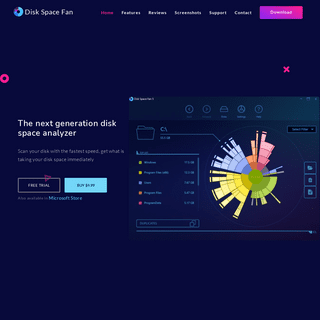
A complete backup of https://diskspacefan.com
Are you over 18 and want to see adult content?
Text
(manually) control
AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS TEMPLATE INHERITANCE Introduction Previously we looked at template class syntax and semantics. In this article we’ll extend this to look at inheritance of template classes. Inheriting from a template class It is possible to inherit from a template class. All the usual rules for inheritance and polymorphism apply. If we want the new, derived class to be generic it should also be a template class; and pass its SCOPE AND LIFETIME OF VARIABLES IN C In a previous posting we looked at the principles (and peculiarities) of declarations and definitions. Here I would like to address the concepts of scope and lifetime of variables (program objects to be precise). In the general case: The placement of the declaration affects scope The placement of the definition affects lifetime Lifetime The lifetime of an object is the time in which memory is WEAK LINKAGE IN C PROGRAMMING At some time later we can add another file with the same function signature to the project. // foo.c. int foo (void) {. // override weak function. return 2; } If we rebuild, normally we would get the “multiply defined” symbols error, however with weak linkage the linker will now bind the new “strong” function to the call inmain.
SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTION An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but in DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the C++11: THE RULE OF THE BIG FIVE Resource Management The dynamic creation and destruction of objects was always one of the bugbears of C. It required the programmer to(manually) control
AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS TEMPLATE INHERITANCE Introduction Previously we looked at template class syntax and semantics. In this article we’ll extend this to look at inheritance of template classes. Inheriting from a template class It is possible to inherit from a template class. All the usual rules for inheritance and polymorphism apply. If we want the new, derived class to be generic it should also be a template class; and pass its SCOPE AND LIFETIME OF VARIABLES IN C In a previous posting we looked at the principles (and peculiarities) of declarations and definitions. Here I would like to address the concepts of scope and lifetime of variables (program objects to be precise). In the general case: The placement of the declaration affects scope The placement of the definition affects lifetime Lifetime The lifetime of an object is the time in which memory is WEAK LINKAGE IN C PROGRAMMING At some time later we can add another file with the same function signature to the project. // foo.c. int foo (void) {. // override weak function. return 2; } If we rebuild, normally we would get the “multiply defined” symbols error, however with weak linkage the linker will now bind the new “strong” function to the call inmain.
SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTION An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but in DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with INTRODUCTION TO THE ARM® CORTEX®-M7 CACHE Caches – Why do we miss? Cold Start As stated, both data and instruction caches are required to be invalidated on system start. Therefore, the first load of any object (code or data) cannot be in cache (thus the cold start condition). One available technique to help with cold-start conditions is the ability to pre-load data into the cache. The ARMv7-M instruction set adds the Preload Data C++11: THE RULE OF THE BIG FIVE Resource Management The dynamic creation and destruction of objects was always one of the bugbears of C. It required the programmer to(manually) control
TDD WITH COMPILER EXPLORER Compiler Explorer (CE) has been around for several years now. When it first appeared on the scene, it immediately became an invaluable tool. Its ability to show generated assembler from given source code across many different compilers and ISAs (Instruction Set Architectures) is “mind-blowing”. We use it extensively when teaching as it allows you to clarify the effect your code can have on BRACE INITIALIZATION OF USER-DEFINED TYPES Uniform initialization syntax is one of my favourite features of Modern C++. I think it’s important, in good quality code, to clearly distinguish between initialization and assignment. When it comes to user-defined types – structures and classes – brace initialization can throw up a few unexpected issues, and some counter-intuitive results (and errors!). In this article, I want to have a AN INTRODUCTION TO C++ TEMPLATES Introduction. Templates are a very powerful – but often very confusing – mechanism within C++. However, approached in stages, templates can be readily understood (despite their heinous syntax). The aim of this series of articles is to guide beginners through the syntax and semantics of the foundation concepts in C++ templateprogramming.
DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with PYTHON 3 UNICODE AND BYTE STRINGS A notable difference between Python 2 and Python 3 is that character data is stored using Unicode instead of bytes. It is quite likely that when migrating existing code and writing new code you may be unaware of this change as most string algorithms will work with either type of representation; but you cannot intermix the two. If you are working with web service libraries such as urllib SETTING UP SUBLIME TEXT TO BUILD YOUR PROJECT For many years embedded development was dominated by complex integrated development environments (IDEs) that hide away all the nasty, messy details of a typical embedded software project. Recently, with the rapidly accelerating adoption of agile techniques in embedded systems, there has been a move away from integrated development environments towards smaller, TEMPLATE MEMBER FUNCTIONS Introduction Previously we’ve looked at template functions and we’ve looked at template classes. This time, let’s look at what happens when you combine them. Template member functions A non-template class can have template member functions, if required. Notice the syntax. Unlike a member function for a template class, a template member function is just like a free template function butCONFIGURATION ITEMS
Configuration Items. A Configuration Item (sometimes referred to as a Computer System Configuration Item, or CSCI) is an artefact (hardware and/or software) that has an end-user purpose – that is, it contributes, in some way, towards the attributes of a system or product, or the development processes followed to produce the systemor product.
HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the C++11: THE RULE OF THE BIG FIVE Resource Management The dynamic creation and destruction of objects was always one of the bugbears of C. It required the programmer to(manually) control
AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS TEMPLATE INHERITANCE Introduction Previously we looked at template class syntax and semantics. In this article we’ll extend this to look at inheritance of template classes. Inheriting from a template class It is possible to inherit from a template class. All the usual rules for inheritance and polymorphism apply. If we want the new, derived class to be generic it should also be a template class; and pass its SCOPE AND LIFETIME OF VARIABLES IN C In a previous posting we looked at the principles (and peculiarities) of declarations and definitions. Here I would like to address the concepts of scope and lifetime of variables (program objects to be precise). In the general case: The placement of the declaration affects scope The placement of the definition affects lifetime Lifetime The lifetime of an object is the time in which memory is WEAK LINKAGE IN C PROGRAMMING At some time later we can add another file with the same function signature to the project. // foo.c. int foo (void) {. // override weak function. return 2; } If we rebuild, normally we would get the “multiply defined” symbols error, however with weak linkage the linker will now bind the new “strong” function to the call inmain.
SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTION An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but in DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the C++11: THE RULE OF THE BIG FIVE Resource Management The dynamic creation and destruction of objects was always one of the bugbears of C. It required the programmer to(manually) control
AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS TEMPLATE INHERITANCE Introduction Previously we looked at template class syntax and semantics. In this article we’ll extend this to look at inheritance of template classes. Inheriting from a template class It is possible to inherit from a template class. All the usual rules for inheritance and polymorphism apply. If we want the new, derived class to be generic it should also be a template class; and pass its SCOPE AND LIFETIME OF VARIABLES IN C In a previous posting we looked at the principles (and peculiarities) of declarations and definitions. Here I would like to address the concepts of scope and lifetime of variables (program objects to be precise). In the general case: The placement of the declaration affects scope The placement of the definition affects lifetime Lifetime The lifetime of an object is the time in which memory is WEAK LINKAGE IN C PROGRAMMING At some time later we can add another file with the same function signature to the project. // foo.c. int foo (void) {. // override weak function. return 2; } If we rebuild, normally we would get the “multiply defined” symbols error, however with weak linkage the linker will now bind the new “strong” function to the call inmain.
SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTION An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but in DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with INTRODUCTION TO THE ARM® CORTEX®-M7 CACHE Caches – Why do we miss? Cold Start As stated, both data and instruction caches are required to be invalidated on system start. Therefore, the first load of any object (code or data) cannot be in cache (thus the cold start condition). One available technique to help with cold-start conditions is the ability to pre-load data into the cache. The ARMv7-M instruction set adds the Preload Data C++11: THE RULE OF THE BIG FIVE Resource Management The dynamic creation and destruction of objects was always one of the bugbears of C. It required the programmer to(manually) control
TDD WITH COMPILER EXPLORER Compiler Explorer (CE) has been around for several years now. When it first appeared on the scene, it immediately became an invaluable tool. Its ability to show generated assembler from given source code across many different compilers and ISAs (Instruction Set Architectures) is “mind-blowing”. We use it extensively when teaching as it allows you to clarify the effect your code can have on BRACE INITIALIZATION OF USER-DEFINED TYPES Uniform initialization syntax is one of my favourite features of Modern C++. I think it’s important, in good quality code, to clearly distinguish between initialization and assignment. When it comes to user-defined types – structures and classes – brace initialization can throw up a few unexpected issues, and some counter-intuitive results (and errors!). In this article, I want to have a AN INTRODUCTION TO C++ TEMPLATES Introduction. Templates are a very powerful – but often very confusing – mechanism within C++. However, approached in stages, templates can be readily understood (despite their heinous syntax). The aim of this series of articles is to guide beginners through the syntax and semantics of the foundation concepts in C++ templateprogramming.
DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with PYTHON 3 UNICODE AND BYTE STRINGS A notable difference between Python 2 and Python 3 is that character data is stored using Unicode instead of bytes. It is quite likely that when migrating existing code and writing new code you may be unaware of this change as most string algorithms will work with either type of representation; but you cannot intermix the two. If you are working with web service libraries such as urllib SETTING UP SUBLIME TEXT TO BUILD YOUR PROJECT For many years embedded development was dominated by complex integrated development environments (IDEs) that hide away all the nasty, messy details of a typical embedded software project. Recently, with the rapidly accelerating adoption of agile techniques in embedded systems, there has been a move away from integrated development environments towards smaller, TEMPLATE MEMBER FUNCTIONS Introduction Previously we’ve looked at template functions and we’ve looked at template classes. This time, let’s look at what happens when you combine them. Template member functions A non-template class can have template member functions, if required. Notice the syntax. Unlike a member function for a template class, a template member function is just like a free template function butCONFIGURATION ITEMS
Configuration Items. A Configuration Item (sometimes referred to as a Computer System Configuration Item, or CSCI) is an artefact (hardware and/or software) that has an end-user purpose – that is, it contributes, in some way, towards the attributes of a system or product, or the development processes followed to produce the systemor product.
HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the TDD WITH COMPILER EXPLORER AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS DYSON OUR AGILE JOURNEY 04/05/2017 1 Dyson –our Agile journey Rod Sinclair Ian Jordan Introductions Ian Jordan Technical Lead •Motorola Systems Group •Alcatel-Lucent •Dyson AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS AN INTRODUCTION TO C++ TEMPLATES RAPID APPLICATION DEVELOPMENT WITH PYTHON WEAK LINKAGE IN C PROGRAMMING At some time later we can add another file with the same function signature to the project. // foo.c. int foo (void) {. // override weak function. return 2; } If we rebuild, normally we would get the “multiply defined” symbols error, however with weak linkage the linker will now bind the new “strong” function to the call inmain.
HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the TDD WITH COMPILER EXPLORER DYSON OUR AGILE JOURNEY 04/05/2017 1 Dyson –our Agile journey Rod Sinclair Ian Jordan Introductions Ian Jordan Technical Lead •Motorola Systems Group •Alcatel-Lucent •Dyson AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS BRACE INITIALIZATION OF USER-DEFINED TYPES AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS RAPID APPLICATION DEVELOPMENT WITH PYTHON WEAK LINKAGE IN C PROGRAMMING At some time later we can add another file with the same function signature to the project. // foo.c. int foo (void) {. // override weak function. return 2; } If we rebuild, normally we would get the “multiply defined” symbols error, however with weak linkage the linker will now bind the new “strong” function to the call inmain.
COURSE LIST
Feabhas provides world-class on-site and public training courses, and consultancy to improve real-time embedded software development skills.TDD FOR EMBEDDED C
The course covers testing embedded C software across host, emulated and target environments. Attendees perform practical TDD exercises based on real-world embedded requirements. The course utilises the C based test framework Unity and CMock for test doubles. Course objectives: To understand the principles of Test-Driven Development. C FOR REAL-TIME EMBEDDED DEVELOPERS This is an intensive five day course covering C in the context of real-time embedded application development. Approximately 50% of the course consists of writing code for a real target. During the week, attendees will build up a complete solution to a case study A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM COMPLYING WITH MISRA-C: WHY AND HOW Authors: Chris Hills Complying with MISRA-C has been a bug bear for many programmers. This presentation will look at why you should use coding standards in general and then MISRA-C in particular. It will address how to apply a coding standard, both in general and with focus on MISRA-C, what are some of the common problems and how to avoidthem.
INTRODUCTION TO THE ARM® CORTEX®-M7 CACHE Instruction Cache Replacement Policy Starting with the simpler instruction cache case; when we encounter a cache miss the normal policy is to evict the current cache line and replace it with the new cache line. This is known as a read-allocate policy and is the default on all instruction caches. Cold start (first read) It should also be noted that on system power-up the initial state of the INTRODUCTION TO THE ARM® CORTEX®-M7 CACHE For many years, the majority of smaller microprocessor-based systems have typically not used caches. With the launch of the ARMv7 architectures, caches were supported in the ARMv7-A family (e.g. Cortex-A8, etc.) but not supported in the core design of the ARMv7-M micro-controllers such as the Cortex-M3 and Cortex-M4. However, when the Cortex-M7 was announced, it broke that mould by AN INTRODUCTION TO C++ TEMPLATES Introduction. Templates are a very powerful – but often very confusing – mechanism within C++. However, approached in stages, templates can be readily understood (despite their heinous syntax). The aim of this series of articles is to guide beginners through the syntax and semantics of the foundation concepts in C++ templateprogramming.
SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTION An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but in DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the TDD WITH COMPILER EXPLORER C++11: THE RULE OF THE BIG FIVE Resource Management The dynamic creation and destruction of objects was always one of the bugbears of C. It required the programmer to(manually) control
AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS SCOPE AND LIFETIME OF VARIABLES IN C In a previous posting we looked at the principles (and peculiarities) of declarations and definitions. Here I would like to address the concepts of scope and lifetime of variables (program objects to be precise). In the general case: The placement of the declaration affects scope The placement of the definition affects lifetime Lifetime The lifetime of an object is the time in which memory is PYTHON 3 UNICODE AND BYTE STRINGS SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTION An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but in DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the TDD WITH COMPILER EXPLORER C++11: THE RULE OF THE BIG FIVE Resource Management The dynamic creation and destruction of objects was always one of the bugbears of C. It required the programmer to(manually) control
AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS SCOPE AND LIFETIME OF VARIABLES IN C In a previous posting we looked at the principles (and peculiarities) of declarations and definitions. Here I would like to address the concepts of scope and lifetime of variables (program objects to be precise). In the general case: The placement of the declaration affects scope The placement of the definition affects lifetime Lifetime The lifetime of an object is the time in which memory is PYTHON 3 UNICODE AND BYTE STRINGS SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTION An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but in DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with INTRODUCTION TO THE ARM® CORTEX®-M7 CACHE Caches – Why do we miss? Cold Start As stated, both data and instruction caches are required to be invalidated on system start. Therefore, the first load of any object (code or data) cannot be in cache (thus the cold start condition). One available technique to help with cold-start conditions is the ability to pre-load data into the cache. The ARMv7-M instruction set adds the Preload Data TDD WITH COMPILER EXPLORER Compiler Explorer (CE) has been around for several years now. When it first appeared on the scene, it immediately became an invaluable tool. Its ability to show generated assembler from given source code across many different compilers and ISAs (Instruction Set Architectures) is “mind-blowing”. We use it extensively when teaching as it allows you to clarify the effect your code can have on C++11: THE RULE OF THE BIG FIVE Resource Management The dynamic creation and destruction of objects was always one of the bugbears of C. It required the programmer to(manually) control
INTRODUCTION TO THE ARM® CORTEX®-M7 CACHE For many years, the majority of smaller microprocessor-based systems have typically not used caches. With the launch of the ARMv7 architectures, caches were supported in the ARMv7-A family (e.g. Cortex-A8, etc.) but not supported in the core design of the ARMv7-M micro-controllers such as the Cortex-M3 and Cortex-M4. However, when the Cortex-M7 was announced, it broke that mould by BRACE INITIALIZATION OF USER-DEFINED TYPES Uniform initialization syntax is one of my favourite features of Modern C++. I think it’s important, in good quality code, to clearly distinguish between initialization and assignment. When it comes to user-defined types – structures and classes – brace initialization can throw up a few unexpected issues, and some counter-intuitive results (and errors!). In this article, I want to have a AN INTRODUCTION TO C++ TEMPLATES Introduction. Templates are a very powerful – but often very confusing – mechanism within C++. However, approached in stages, templates can be readily understood (despite their heinous syntax). The aim of this series of articles is to guide beginners through the syntax and semantics of the foundation concepts in C++ templateprogramming.
WEAK LINKAGE IN C PROGRAMMING At some time later we can add another file with the same function signature to the project. // foo.c. int foo (void) {. // override weak function. return 2; } If we rebuild, normally we would get the “multiply defined” symbols error, however with weak linkage the linker will now bind the new “strong” function to the call inmain.
PYTHON 3 UNICODE AND BYTE STRINGS A notable difference between Python 2 and Python 3 is that character data is stored using Unicode instead of bytes. It is quite likely that when migrating existing code and writing new code you may be unaware of this change as most string algorithms will work with either type of representation; but you cannot intermix the two. If you are working with web service libraries such as urllibCONFIGURATION ITEMS
Configuration Items. A Configuration Item (sometimes referred to as a Computer System Configuration Item, or CSCI) is an artefact (hardware and/or software) that has an end-user purpose – that is, it contributes, in some way, towards the attributes of a system or product, or the development processes followed to produce the systemor product.
SETTING UP SUBLIME TEXT TO BUILD YOUR PROJECT For many years embedded development was dominated by complex integrated development environments (IDEs) that hide away all the nasty, messy details of a typical embedded software project. Recently, with the rapidly accelerating adoption of agile techniques in embedded systems, there has been a move away from integrated development environments towards smaller, HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the TDD WITH COMPILER EXPLORER AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS DYSON OUR AGILE JOURNEY 04/05/2017 1 Dyson –our Agile journey Rod Sinclair Ian Jordan Introductions Ian Jordan Technical Lead •Motorola Systems Group •Alcatel-Lucent •Dyson AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS AN INTRODUCTION TO C++ TEMPLATES RAPID APPLICATION DEVELOPMENT WITH PYTHON WEAK LINKAGE IN C PROGRAMMING At some time later we can add another file with the same function signature to the project. // foo.c. int foo (void) {. // override weak function. return 2; } If we rebuild, normally we would get the “multiply defined” symbols error, however with weak linkage the linker will now bind the new “strong” function to the call inmain.
HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the TDD WITH COMPILER EXPLORER AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS DYSON OUR AGILE JOURNEY 04/05/2017 1 Dyson –our Agile journey Rod Sinclair Ian Jordan Introductions Ian Jordan Technical Lead •Motorola Systems Group •Alcatel-Lucent •Dyson AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS AN INTRODUCTION TO C++ TEMPLATES RAPID APPLICATION DEVELOPMENT WITH PYTHON WEAK LINKAGE IN C PROGRAMMING At some time later we can add another file with the same function signature to the project. // foo.c. int foo (void) {. // override weak function. return 2; } If we rebuild, normally we would get the “multiply defined” symbols error, however with weak linkage the linker will now bind the new “strong” function to the call inmain.
COURSE LIST
Feabhas provides world-class on-site and public training courses, and consultancy to improve real-time embedded software development skills.TDD FOR EMBEDDED C
The course covers testing embedded C software across host, emulated and target environments. Attendees perform practical TDD exercises based on real-world embedded requirements. The course utilises the C based test framework Unity and CMock for test doubles. Course objectives: To understand the principles of Test-Driven Development. C FOR REAL-TIME EMBEDDED DEVELOPERS This is an intensive five day course covering C in the context of real-time embedded application development. Approximately 50% of the course consists of writing code for a real target. During the week, attendees will build up a complete solution to a case study A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM COMPLYING WITH MISRA-C: WHY AND HOW Authors: Chris Hills Complying with MISRA-C has been a bug bear for many programmers. This presentation will look at why you should use coding standards in general and then MISRA-C in particular. It will address how to apply a coding standard, both in general and with focus on MISRA-C, what are some of the common problems and how to avoidthem.
INTRODUCTION TO THE ARM® CORTEX®-M7 CACHE Instruction Cache Replacement Policy Starting with the simpler instruction cache case; when we encounter a cache miss the normal policy is to evict the current cache line and replace it with the new cache line. This is known as a read-allocate policy and is the default on all instruction caches. Cold start (first read) It should also be noted that on system power-up the initial state of the INTRODUCTION TO THE ARM® CORTEX®-M7 CACHE For many years, the majority of smaller microprocessor-based systems have typically not used caches. With the launch of the ARMv7 architectures, caches were supported in the ARMv7-A family (e.g. Cortex-A8, etc.) but not supported in the core design of the ARMv7-M micro-controllers such as the Cortex-M3 and Cortex-M4. However, when the Cortex-M7 was announced, it broke that mould by AN INTRODUCTION TO C++ TEMPLATES Introduction. Templates are a very powerful – but often very confusing – mechanism within C++. However, approached in stages, templates can be readily understood (despite their heinous syntax). The aim of this series of articles is to guide beginners through the syntax and semantics of the foundation concepts in C++ templateprogramming.
SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTION An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but in DEVELOPING A GENERIC HARD FAULT HANDLER FOR ARM CORTEX-M3 Greetings, Excellent Post nice work sir, May i know what is hardware break point and software breakpoints as well as hardware watch point and software watch point in cortex m3, how could i set those things with a clear explanation,i searched alot but most of the websites and arm technical manual. all are saying that there are comparators existed which will compare the program counter with HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy.COURSE LIST
Feabhas provides world-class on-site and public training courses, and consultancy to improve real-time embedded software development skills. COMPLYING WITH MISRA-C: WHY AND HOW Authors: Chris Hills Complying with MISRA-C has been a bug bear for many programmers. This presentation will look at why you should use coding standards in general and then MISRA-C in particular. It will address how to apply a coding standard, both in general and with focus on MISRA-C, what are some of the common problems and how to avoidthem.
RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the MODERN C++ WHITE PAPER: MAKING THINGS DO STUFF � Feabhas Ltd. August 2017 Modern C++ White paper: Making things do stuff Glennan Carnie Technical consultant, Feabhas AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS BRACE INITIALIZATION OF USER-DEFINED TYPESPYTHON 3 FILE PATHS
SCOPE AND LIFETIME OF VARIABLES IN C In a previous posting we looked at the principles (and peculiarities) of declarations and definitions. Here I would like to address the concepts of scope and lifetime of variables (program objects to be precise). In the general case: The placement of the declaration affects scope The placement of the definition affects lifetime Lifetime The lifetime of an object is the time in which memory is SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTIONCORTEX M MPU An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but in HOMEPAGE | FEABHASABOUTTRAININGBLOGNEWSKNOWLEDGE CENTRECONTACT Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts. Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy.COURSE LIST
Feabhas provides world-class on-site and public training courses, and consultancy to improve real-time embedded software development skills. COMPLYING WITH MISRA-C: WHY AND HOW Authors: Chris Hills Complying with MISRA-C has been a bug bear for many programmers. This presentation will look at why you should use coding standards in general and then MISRA-C in particular. It will address how to apply a coding standard, both in general and with focus on MISRA-C, what are some of the common problems and how to avoidthem.
RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER I first wrote about MQTT and IoT back in 2012, when I developed a simple C based library to publish and subscribe Quality of Service (QoS) level 0 MQTT messages. Subsequently, MQTT has grown to be one of the most widely used IoT connectivity protocols with direct support from service such as AWS. Back in 2010, the first open-source MQTT Broker was Mosquitto. Mosquitto is now part of the MODERN C++ WHITE PAPER: MAKING THINGS DO STUFF � Feabhas Ltd. August 2017 Modern C++ White paper: Making things do stuff Glennan Carnie Technical consultant, Feabhas AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS BRACE INITIALIZATION OF USER-DEFINED TYPESPYTHON 3 FILE PATHS
SCOPE AND LIFETIME OF VARIABLES IN C In a previous posting we looked at the principles (and peculiarities) of declarations and definitions. Here I would like to address the concepts of scope and lifetime of variables (program objects to be precise). In the general case: The placement of the declaration affects scope The placement of the definition affects lifetime Lifetime The lifetime of an object is the time in which memory is SETTING UP THE CORTEX-M3/4 (ARMV7-M) MEMORY PROTECTIONCORTEX M MPU An optional part of the ARMv7-M architecture is the support of a Memory Protection Unit (MPU). This is a fairly simplistic device (compared to a fully blow Memory Management Unit (MMU) as found on the Cortex-A family), but if available can be programmed to help capture illegal or dangerous memory accesses. When first looking at programming the MPU it may seem rather daunting, but inCOURSE LIST
Feabhas provides world-class on-site and public training courses, and consultancy to improve real-time embedded software development skills. FEABHAS - A QUICK GUIDE TO ISO 26262 Find out all about ISO 26262. ISO 26262 is an international standard focussing on the safety of automotive electrical / electronic systems. That is, ISO 26262 is designed to ensure that embedded systems developed for road vehicles – cars, lorries motorbikes, etc – are designed with an appropriate level of rigour for their intendedapplication.
C FOR REAL-TIME EMBEDDED DEVELOPERS This is an intensive five day course covering C in the context of real-time embedded application development. Approximately 50% of the course consists of writing code for a real target. During the week, attendees will build up a complete solution to a case study A QUICK GUIDE TO ISO 26262 Title: Microsoft Word - A quick guide to ISO 26262.docx Author: Jo.Cooling Created Date: 1/25/2012 8:06:00 PM WHY WE NEED BUILD SYSTEMS Build systems were developed to simplify and automate running the compiler and linker and are an essential part of modern software development. This blog post is a precursor to future posts discussing our experiences refactoring the training projects to use the CMake build generator. Using Build Systems Build systems can be standalone command line applications such as Make, Scons and Ninja; INTRODUCTION TO THE ARM® CORTEX®-M7 CACHE Caches – Why do we miss? Cold Start As stated, both data and instruction caches are required to be invalidated on system start. Therefore, the first load of any object (code or data) cannot be in cache (thus the cold start condition). One available technique to help with cold-start conditions is the ability to pre-load data into the cache. The ARMv7-M instruction set adds the Preload Data TDD WITH COMPILER EXPLORER Compiler Explorer (CE) has been around for several years now. When it first appeared on the scene, it immediately became an invaluable tool. Its ability to show generated assembler from given source code across many different compilers and ISAs (Instruction Set Architectures) is “mind-blowing”. We use it extensively when teaching as it allows you to clarify the effect your code can have on BUILD-SYSTEMS ARCHIVES An independent IT trainer Martin has over 40 years academic and commercial experience in open systems software engineering. He has worked with a range of technologies from real time process controllers, through compilers, to large scale parallel processing systems; and across multiple sectors including industrial systems, semi-conductor manufacturing, telecomms, banking, MoD, and government. AN INTRODUCTION TO DOCKER FOR EMBEDDED DEVELOPERS In the previous posting we looked at defining a custom Dockerfile where we can add specific tools (and their dependencies). From that we created a Docker image and this allowed us to build C/C++ code in a Docker container, ensuring a consistent build environment. So far we have to build all our code using the native GCC toolchain which is part of the base Docker image (gcc:7.2). However, I AN INTRODUCTION TO C++ TEMPLATES Introduction. Templates are a very powerful – but often very confusing – mechanism within C++. However, approached in stages, templates can be readily understood (despite their heinous syntax). The aim of this series of articles is to guide beginners through the syntax and semantics of the foundation concepts in C++ templateprogramming.
Skip to main contentFeabhas
Menu
MAIN NAVIGATION
* About
* Our management
* Our customers
* DebMed case study
* Leonardo case study* Newsletter
* Training
* Course list
* Course calendar
* Booking form
* Course road map
* Assessments & Audits* FastTrack
* Modern C++ for Embedded Development * Consultancy and mentoring * Why choose Feabhas?* Blog
* News
* Knowledge centre
* Contact
* Events
info@feabhas.com
HOMEPAGE
About FeabhasDeveloping YourselfDeveloping Your TeamDeveloping YourBusiness
THE JOURNEY TO IMPROVING YOUR EMBEDDED SOFTWARE DEVELOPMENT SKILLSSTARTS HERE...
Feabhas training and consultancy improves the embedded software development skills within the world’s leading electronic companies, such as Samsung, Arm, HP and Intel. DURING THE COVID-19 CRISIS, FEABHAS COURSES ARE ONLY AVAILABLE FOR REMOTE DELIVERY. DELEGATES CONNECT INDIVIDUALLY VIA THE INTERNET AND GET FULL INTERACTION WITH THE LECTURER, INCLUDING A LIVE VIDEO STREAM, LIVE ANNOTATION OF PRESENTATIONS, WHITEBOARD SESSIONS AND INTERACTION FOR PRACTICAL EXERCISES. EMULATION IS USED FOR LAB SESSIONS INVOLVING TARGET HARDWARE. CONTACT US FOR MORE INFORMATION.Find out more
About
Feabhas
DEVELOPING YOURSELF
Learning new embedded software development skills and processes not only helps to deliver better quality products; it also supports continuing professional development. Feabhas training courses will help you to improve your knowledge of Embedded Linux, C, C++ , Python, software design or testing, with practical exercises and face-to-face lectures from industry experts.Find out more
Developing
Yourself
DEVELOPING YOUR TEAM Help your team to gain valuable new skills in embedded software development with Feabhas onsite-training and consultancy. Courses are delivered world-wide by industry experts and the practical exercises enable rapid adoption back in the workplace.Find out more
Developing
Your Team
YOUR PARTNER FOR IMPROVING EMBEDDED SOFTWARE DEVELOPMENT SKILLS Feabhas can help you improve your embedded software developers' competency and the processes they use. Many leading companies already use our consultancy, onsite-training and competency assessments, to help them develop better quality products, more efficiently.Find out more
Developing
Your Business
* ABOUTFeabhas
* DEVELOPINGYourself * DEVELOPINGYour Team * DEVELOPINGYour BusinessWidgets
POPULAR COURSES
Learn more about
*
Modern C++ for Embedded Systems*
C for Real-Time Embedded Developers*
Real-Time Software Design with UMLCOURSE SELECTOR
Find a course to suit your needs - Course category - Agile for Embedded Programming Languages Design Techniques Operating Systems Quality - Course name - Robust Software for Embedded Systems Software Modelling with UML Design Patterns in C++ for Embedded Systems Developing for Embedded Linux Guidelines for Writing High Integrity Software in C (The MISRA-C:2012 Guidelines) C for Real-Time Embedded Developers Advanced C Programming The Value of Verification and Validation Real-Time Design Patterns for Embedded Systems Real-Time Software Design with UML Python for Test Engineers Developing Linux Device Drivers C Software Testing Fundamentals Embedded Software Testing with C Systems Engineering using SysML Embedded Software Testing with C++ Transitioning to C++11/C++14 Robust Software Development Modern C++ for Embedded Systems C++ Software Testing Fundamentals Agile for Embedded C Agile for Embedded C++ TDD for Embedded C TDD for Embedded C++ Introduction to Agile Real-Time Modern C++ Developing for Real-Time Operating Systems with FreeRTOS Design Patterns in Modern C++ Advanced Real-Time Modern C++ Advanced Modern C++ for Embedded Developers Real-Time Design Patterns in Modern C++ - Course code - RB-201 OO-302 DP-403 EL-503 MC-102 C-501 AC-401 T-101 DP-303 OO-504 PY-404 EL-504 TC-201 TC-401 SE-401 TC++-401 AC++11-401 RBC-201 C++11-501 TC++-201 AEC-401 AEC++-401 TDDC-201 TDDC++-201 AE-101 C++11-502 RTOS-301 DP11-403 AC++11-502 AC++11-501 DP11-404WATCH OUR VIDEO
Why Feabhas stands out from the crowdOUR BLOG
SIDE EFFECTS AND SEQUENCE POINTS; WHY VOLATILE MATTERS Introduction Most embedded programmers, and indeed anyone who has attended a Feabhas programming course, is familiar with using the volatile directive when accessing registers. But it is not alwaysobvious
* February 27th, 2020 PRACTICE MAKES PERFECT, PART 3 – IDIOMATIC KATA * February 20th, 2020 RUNNING THE ECLIPSE-MOSQUITTO MQTT BROKER IN A DOCKER CONTAINER * February 13th, 2020 PRACTICE MAKES PERFECT, PART 2 – FOUNDATION KATA View more on blog.feabhas.comLATEST NEWS
FEABHAS INTRODUCES TRAINING BY REMOTE DELIVERY We are pleased to announce that Feabhas courses are now available for remote delivery During the Covid-19 crisis we will only be offering remote delivery of training. This is available... * Press release: Agile for Embedded Conference, Innovative ‘Lunch and Learn’ Sessions and ‘Agile Springboard’ Workshop * Springboard into Agile for EmbeddedView more stories
SIGNUP TO RECEIVE OUR NEWSLETTER Please subscribe me: Name: Email: Get the latest technical know-how from Feabhas and information on our embedded software training, events, products and services. We won’t bombard your inbox and you can opt-out at anytime. PrivacyPolicy
FOOTER MENU
* Contact
* Privacy
* Cookies
SOCIAL
* Linked In
* Youtube
* FEABHAS LTD - UK OFFICE * 15-17 Lotmead Business Park, Wanborough, Swindon, SN4 0UY, UK* info@feabhas.com
* www.feabhas.com
* About
* Our management
* Our customers
* DebMed case study
* Leonardo case study* Newsletter
* Training
* Course list
* Course calendar
* Booking form
* Course road map
* Assessments & Audits* FastTrack
* Modern C++ for Embedded Development * Consultancy and mentoring * Why choose Feabhas?* Blog
* News
* Knowledge centre
* Contact
* Events
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0