Are you over 18 and want to see adult content?
More Annotations

Big Bear's Wife - Easy Recipes, Fun Travels, & Real Life Southern Days
Are you over 18 and want to see adult content?
The Business School for the World | INSEAD
Are you over 18 and want to see adult content?
A complete backup of therealmyroyals.com
Are you over 18 and want to see adult content?
Nalogcity.ru — просто и доступно о налогах и налоговых вычетах.
Are you over 18 and want to see adult content?

Window Shutters | Plantation Shutters | Window Replacements | Window Design Group
Are you over 18 and want to see adult content?
A complete backup of slm-solution.com.ua
Are you over 18 and want to see adult content?

Смотреть фильмы, сериалы онлайн! Новинки кинопроката, трейлеры и море разных фильмов
Are you over 18 and want to see adult content?
![ASIAN GRUP - Portal Infotainment Selebritis Asia [TERUPDATE]](https://www.archivebay.com/archive/9f1fc802-31c8-45d6-b384-39a926bad034.png)
ASIAN GRUP - Portal Infotainment Selebritis Asia [TERUPDATE]
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of www.tv8.com.tr/survivor-panorama/yasin-ile-erman-arasindaki-gerilimin-perde-arkasinda-ne-var-hakan-hatipogl
Are you over 18 and want to see adult content?

A complete backup of topick.hket.com/article/2576268
Are you over 18 and want to see adult content?

A complete backup of www.chip.de/news/Real-Madrid-vs.-Manchester-City-im-Live-Stream-Champions-League-Kracher-online-sehen-so-ge
Are you over 18 and want to see adult content?
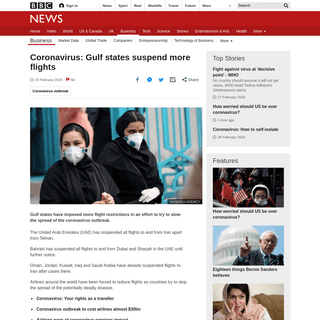
A complete backup of www.bbc.com/news/business-51626803
Are you over 18 and want to see adult content?

A complete backup of www.diariolaprovinciasj.com/espectaculos/2020/2/26/grego-rossello-confeso-que-debuto-con-lali-esposito-no-s
Are you over 18 and want to see adult content?
Text
ecosystem.
CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
SECURITY RISKS OF CONTACTLESS PAYMENT Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
RANSOMWARE, PHISHING AND BOTNETS Ransomware is any malware that holds your data ransom. These days it usually involves encrypting a victim’s data before asking for cash (typically crypto-currency) to decrypt it. Ransomware ruled the malware world since late 2013, but finally saw a decline last year. The general drop in malware numbers, along with defensive improvementsby
RESILIENCE CYBER INSURANCE SOLUTIONS Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SENTRYO - CYBER SECURITY INTELLIGENCE Sentryo. Sentryo is pioneering the market for cybersecurity protection for M2M networks and critical industrial systems. Sentryo ICS CyberVision is a two tier monitoring platform made up of sensors and central data visualization and analytics software. It enables organisations to perform OT monitoring: asset tracking, control systemintegrity
INDUSTRY 5.0 WILL TRANSFORM THE WORKPLACE The key difference is that Industry 5.0 refers to a combination of advanced Industry 4.0 technologies, creating a digital assistant for humans to easily connect. The workplace is evolving at tremendous speed, and it is an exciting time for many industries. This ongoing change is expected to continue in the coming years, as developmentsprogress.
THE EFFECTS OF THE INTERNET ON SOCIETY The Negative Impacts of the Internet on Society include: Easy availability of illegal or inappropriate materials online that isn’t age-suitable. It can be addicting and it can hurt our communication skills. Extended screen time can result in health ramifications like insomnia, eyestrain, and increased anxiety and depression. PHILIPPINE NATIONAL POLICE ANTI-CYBERCRIME GROUP (PNP-ACG) Philippine National Police Anti-Cybercrime Group (PNP-ACG) The mission of the PNP Anti-Cybercrime Group is to implement and enforce pertinent laws on cybercrime and other cyber related crimes and pursue an effective anti-cybercrime campaign. RWANDA INFORMATION SOCIETY AUTHORITY (RISA) Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution to TRACEPOINT - CYBER SECURITY INTELLIGENCE TracePoint. TracePoint provide full-service cyber incident response, remediation and recovery solutions for the most time-sensitive situation your company may ever face. Founded by incident response, cyber security and insurance leaders, TracePoint was built on decades of experience working at the epicenter of the cyber securityecosystem.
CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
SECURITY RISKS OF CONTACTLESS PAYMENT Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
RANSOMWARE, PHISHING AND BOTNETS Ransomware is any malware that holds your data ransom. These days it usually involves encrypting a victim’s data before asking for cash (typically crypto-currency) to decrypt it. Ransomware ruled the malware world since late 2013, but finally saw a decline last year. The general drop in malware numbers, along with defensive improvementsby
RESILIENCE CYBER INSURANCE SOLUTIONS Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SENTRYO - CYBER SECURITY INTELLIGENCE Sentryo. Sentryo is pioneering the market for cybersecurity protection for M2M networks and critical industrial systems. Sentryo ICS CyberVision is a two tier monitoring platform made up of sensors and central data visualization and analytics software. It enables organisations to perform OT monitoring: asset tracking, control systemintegrity
INDUSTRY 5.0 WILL TRANSFORM THE WORKPLACE The key difference is that Industry 5.0 refers to a combination of advanced Industry 4.0 technologies, creating a digital assistant for humans to easily connect. The workplace is evolving at tremendous speed, and it is an exciting time for many industries. This ongoing change is expected to continue in the coming years, as developmentsprogress.
THE EFFECTS OF THE INTERNET ON SOCIETY The Negative Impacts of the Internet on Society include: Easy availability of illegal or inappropriate materials online that isn’t age-suitable. It can be addicting and it can hurt our communication skills. Extended screen time can result in health ramifications like insomnia, eyestrain, and increased anxiety and depression. PHILIPPINE NATIONAL POLICE ANTI-CYBERCRIME GROUP (PNP-ACG) Philippine National Police Anti-Cybercrime Group (PNP-ACG) The mission of the PNP Anti-Cybercrime Group is to implement and enforce pertinent laws on cybercrime and other cyber related crimes and pursue an effective anti-cybercrime campaign. RWANDA INFORMATION SOCIETY AUTHORITY (RISA) Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution toUNBOUND SECURITY
1 day ago · Unbound Security. Our vision at Unbound Security is to be the global cryptographic platform of choice for the enterprise. At Unbound Security we apply revolutionary breakthroughs in cryptography to empower enterprises to confidently secure and manage all their critical business transactions, information, and digital assets –anywhere, anytime.
FUTURE THREATS ARE GROWING CLOSER Future generations may look back at our time as one of intense change. In a few short decades, we have morphed from a machine-based society to an information-based society and society has been forced to develop a new and intimate familiarity with data-driven and algorithmic systems and two of the most interesting topics on the Internet today are Artificial Intelligence (AI) and Cyber Security. EQUALITY GOES MISSING IN THE DIGITAL INDUSTRY 5 hours ago · In many organisations in many different locations women have not always been welcome. The catalyst for change was World War II, when women took work in factories to replace conscripted male workers. Since then, women have been fighting for CLOSING THE SPACE BETWEEN CYBERCRIME & CYBERSECURITY 1 day ago · Siloed thinking on cybersecurity and cybercrime leaves blind spots ready to be exploited by anyone - a critical weakness for both governments and corporations. Although nothing new, ransomware attacks on critical national infrastructure have recently been held under a microscope due to a series of THE CYBER REVOLUTION’S EFFECTS ON INTERNATIONAL TRADE Practice Labs. Practice Labs is an IT competency hub, where live-lab environments give access to real equipment for hands-on practice of essential cybersecurity skills.REGULATIV.AI
1 day ago · Regulativ.ai is an innovative and comprehensive platform, driven by AI, to address the regulatory and compliance needs of Cyber Security Regulatory compliance and reporting. The platform provides integrated aggregation, analytical, compliance and reporting for all your Cyber Security needs CRIMINAL MESSAGING APP LEADS TO WIDESPREAD ARRESTS A massive international sting, involving at least 17 countries, including the US, has arrested suspects, the seizure of 8 tons of cocaine and more than $48 million and over 800 suspected criminals have been arrested after being hoodwinked into using an FBI-run encrypted messaging app says the FBI and this is a continuation of Operation Trojan Shield. FAKE FINANCE APPS FOCUS ON THEFT Criminals have published hundreds of bogus banking, finance, and crypto-currency apps that steal your money. A team of researchers at Sophos say they have identified as many as 167 fake banking, trading and crypto-currency apps that criminals are using to steal money and financial information from unsuspecting users.. These fraudulent applications are aimed at exploiting the ONLINE FRAUD COSTS BRITISH INVESTORS £63M Online Fraud Costs British Investors £63m. Uploaded on 2021-06-02 in GOVERNMENT-Law Enforcement, FREE TO VIEW, BUSINESS-Services-Financial. Over £63m was lost nationally by victims of investment fraud who referred to a social media platform in their report to Action Fraud, the national reporting centre for fraud and cyber crime. MICROSOFT’S DEFENSIVE PLAYBOOK Many company leaders, especially those leading SMEs, have little knowledge on how to defend their businesses from cyber attacks or how to respond if their company is hacked. Microsoft is now offering organisations advice on how to protect their cyber networks and it TRACEPOINT - CYBER SECURITY INTELLIGENCE TracePoint. TracePoint provide full-service cyber incident response, remediation and recovery solutions for the most time-sensitive situation your company may ever face. Founded by incident response, cyber security and insurance leaders, TracePoint was built on decades of experience working at the epicenter of the cyber securityecosystem.
CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
SECURITY RISKS OF CONTACTLESS PAYMENT Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
RANSOMWARE, PHISHING AND BOTNETS Ransomware is any malware that holds your data ransom. These days it usually involves encrypting a victim’s data before asking for cash (typically crypto-currency) to decrypt it. Ransomware ruled the malware world since late 2013, but finally saw a decline last year. The general drop in malware numbers, along with defensive improvementsby
RESILIENCE CYBER INSURANCE SOLUTIONS Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SENTRYO - CYBER SECURITY INTELLIGENCE Sentryo. Sentryo is pioneering the market for cybersecurity protection for M2M networks and critical industrial systems. Sentryo ICS CyberVision is a two tier monitoring platform made up of sensors and central data visualization and analytics software. It enables organisations to perform OT monitoring: asset tracking, control systemintegrity
INDUSTRY 5.0 WILL TRANSFORM THE WORKPLACE The key difference is that Industry 5.0 refers to a combination of advanced Industry 4.0 technologies, creating a digital assistant for humans to easily connect. The workplace is evolving at tremendous speed, and it is an exciting time for many industries. This ongoing change is expected to continue in the coming years, as developmentsprogress.
THE EFFECTS OF THE INTERNET ON SOCIETY The Negative Impacts of the Internet on Society include: Easy availability of illegal or inappropriate materials online that isn’t age-suitable. It can be addicting and it can hurt our communication skills. Extended screen time can result in health ramifications like insomnia, eyestrain, and increased anxiety and depression. PHILIPPINE NATIONAL POLICE ANTI-CYBERCRIME GROUP (PNP-ACG) Philippine National Police Anti-Cybercrime Group (PNP-ACG) The mission of the PNP Anti-Cybercrime Group is to implement and enforce pertinent laws on cybercrime and other cyber related crimes and pursue an effective anti-cybercrime campaign. RWANDA INFORMATION SOCIETY AUTHORITY (RISA) Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution to TRACEPOINT - CYBER SECURITY INTELLIGENCE TracePoint. TracePoint provide full-service cyber incident response, remediation and recovery solutions for the most time-sensitive situation your company may ever face. Founded by incident response, cyber security and insurance leaders, TracePoint was built on decades of experience working at the epicenter of the cyber securityecosystem.
CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
SECURITY RISKS OF CONTACTLESS PAYMENT Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
RANSOMWARE, PHISHING AND BOTNETS Ransomware is any malware that holds your data ransom. These days it usually involves encrypting a victim’s data before asking for cash (typically crypto-currency) to decrypt it. Ransomware ruled the malware world since late 2013, but finally saw a decline last year. The general drop in malware numbers, along with defensive improvementsby
RESILIENCE CYBER INSURANCE SOLUTIONS Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SENTRYO - CYBER SECURITY INTELLIGENCE Sentryo. Sentryo is pioneering the market for cybersecurity protection for M2M networks and critical industrial systems. Sentryo ICS CyberVision is a two tier monitoring platform made up of sensors and central data visualization and analytics software. It enables organisations to perform OT monitoring: asset tracking, control systemintegrity
INDUSTRY 5.0 WILL TRANSFORM THE WORKPLACE The key difference is that Industry 5.0 refers to a combination of advanced Industry 4.0 technologies, creating a digital assistant for humans to easily connect. The workplace is evolving at tremendous speed, and it is an exciting time for many industries. This ongoing change is expected to continue in the coming years, as developmentsprogress.
THE EFFECTS OF THE INTERNET ON SOCIETY The Negative Impacts of the Internet on Society include: Easy availability of illegal or inappropriate materials online that isn’t age-suitable. It can be addicting and it can hurt our communication skills. Extended screen time can result in health ramifications like insomnia, eyestrain, and increased anxiety and depression. PHILIPPINE NATIONAL POLICE ANTI-CYBERCRIME GROUP (PNP-ACG) Philippine National Police Anti-Cybercrime Group (PNP-ACG) The mission of the PNP Anti-Cybercrime Group is to implement and enforce pertinent laws on cybercrime and other cyber related crimes and pursue an effective anti-cybercrime campaign. RWANDA INFORMATION SOCIETY AUTHORITY (RISA) Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution toUNBOUND SECURITY
1 day ago · Unbound Security. Our vision at Unbound Security is to be the global cryptographic platform of choice for the enterprise. At Unbound Security we apply revolutionary breakthroughs in cryptography to empower enterprises to confidently secure and manage all their critical business transactions, information, and digital assets –anywhere, anytime.
CLOSING THE SPACE BETWEEN CYBERCRIME & CYBERSECURITY 18 hours ago · Siloed thinking on cybersecurity and cybercrime leaves blind spots ready to be exploited by anyone - a critical weakness for both governments and corporations. Although nothing new, ransomware attacks on critical national infrastructure have FUTURE THREATS ARE GROWING CLOSER Future generations may look back at our time as one of intense change. In a few short decades, we have morphed from a machine-based society to an information-based society and society has been forced to develop a new and intimate familiarity with data-driven and algorithmic systems and two of the most interesting topics on the Internet today are Artificial Intelligence (AI) and Cyber Security. THE CYBER REVOLUTION’S EFFECTS ON INTERNATIONAL TRADE 1 day ago · Practice Labs. Practice Labs is an IT competency hub, where live-lab environments give access to real equipment for hands-on practice of essential cybersecurity skills. FAKE FINANCE APPS FOCUS ON THEFT Criminals have published hundreds of bogus banking, finance, and crypto-currency apps that steal your money. A team of researchers at Sophos say they have identified as many as 167 fake banking, trading and crypto-currency apps that criminals are using to steal money and financial information from unsuspecting users.. These fraudulent applications are aimed at exploiting the CRIMINAL MESSAGING APP LEADS TO WIDESPREAD ARRESTS A massive international sting, involving at least 17 countries, including the US, has arrested suspects, the seizure of 8 tons of cocaine and more than $48 million and over 800 suspected criminals have been arrested after being hoodwinked into using an FBI-run encrypted messaging app says the FBI and this is a continuation of Operation Trojan Shield. MICROSOFT’S DEFENSIVE PLAYBOOK Many company leaders, especially those leading SMEs, have little knowledge on how to defend their businesses from cyber attacks or how to respond if their company is hacked. Microsoft is now offering organisations advice on how to protect their cyber networks and itREGULATIV.AI
1 day ago · Regulativ.ai is an innovative and comprehensive platform, driven by AI, to address the regulatory and compliance needs of Cyber Security Regulatory compliance and reporting. The platform provides integrated aggregation, analytical, compliance and reporting for all your Cyber Security needs ONLINE FRAUD COSTS BRITISH INVESTORS £63M Online Fraud Costs British Investors £63m. Uploaded on 2021-06-02 in GOVERNMENT-Law Enforcement, FREE TO VIEW, BUSINESS-Services-Financial. Over £63m was lost nationally by victims of investment fraud who referred to a social media platform in their report to Action Fraud, the national reporting centre for fraud and cyber crime. THE FBI CAN COVERTLY ACCESS YOUR COMPUTER As fallout from the devastating and extensive breach of Microsoft's Exchange email suite of email software, the FBI now has the authority to access privately owned computers without their owners’ knowledge or consent and to delete software. This is part of the US government's effort to contain the continuing attacks on corporate networks running Microsoft Exchange and it’s raising legal CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
CYBER SECURITY IN HIGHER EDUCATION Cyber Security In Higher Education. In response to the Coronavirus onslaught, higher education is rapidly migrating to remote and online learning and academic and IT leaders in the sector have faced an onslaught of challenges. Perhaps the greatest of these is the need for heightened cyber security, at the same time as budgets and resourcesare
RESILIENCE CYBER INSURANCE SOLUTIONS Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SECURITY RISKS OF CONTACTLESS PAYMENT Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
DFI - CYBER SECURITY INTELLIGENCE DFI. DFI is a global leading provider of high-performance computing technology across multiple embedded industries. With its innovative design and premium quality management system, DFI’s industrial-grade solutions enable customers to optimize their equipment and ensure high reliability, long-term life cycle, and 24/7 durability in a breadth of markets including factory automation, medical CRITICAL PIPELINE NETWORK SHUT DOWN BY HACKERS Critical Pipeline Network Shut Down By Hackers. A critical oil pipeline which supplies 45 percent of the east coast fuel supply has shut-down all pipeline operations after being hacked. Colonial Pipeline has said that it was the victim of “a cybersecurity attack. In response, we proactively took certain systems offline to containthe
PETRI IT KNOWLEDGEBASE First launched by IT expert Daniel Petri in 1999, the Petri IT Knowledgebase has always been focused on serving the needs of IT professionals by providing information to help them solve problems, do their jobs more effectively, and to advance their careers. The Petri IT Knowledgebase is an independent website owned by Blue Whale WebInc.
NATIONAL AGENCY FOR INFORMATION & COMMUNICATION ANTIC is responsible for regulating the activities of electronic security and regulation of the Internet in Cameroon. The tasks of the Agency are to ensure, on behalf of the State: - the promotion and monitoring of government action in the field of Information and Communication Technologies (ICT AFCERT - CYBER SECURITY INTELLIGENCE AFCERT. AFCERT is the national Computer Emergency Response Team for Afghanistan. AFCERT operates as first responder to cyber and computer incidents in Afghanistan. RWANDA INFORMATION SOCIETY AUTHORITY (RISA) Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution to CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
CYBER SECURITY IN HIGHER EDUCATION Cyber Security In Higher Education. In response to the Coronavirus onslaught, higher education is rapidly migrating to remote and online learning and academic and IT leaders in the sector have faced an onslaught of challenges. Perhaps the greatest of these is the need for heightened cyber security, at the same time as budgets and resourcesare
RESILIENCE CYBER INSURANCE SOLUTIONS Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SECURITY RISKS OF CONTACTLESS PAYMENT Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
DFI - CYBER SECURITY INTELLIGENCE DFI. DFI is a global leading provider of high-performance computing technology across multiple embedded industries. With its innovative design and premium quality management system, DFI’s industrial-grade solutions enable customers to optimize their equipment and ensure high reliability, long-term life cycle, and 24/7 durability in a breadth of markets including factory automation, medical CRITICAL PIPELINE NETWORK SHUT DOWN BY HACKERS Critical Pipeline Network Shut Down By Hackers. A critical oil pipeline which supplies 45 percent of the east coast fuel supply has shut-down all pipeline operations after being hacked. Colonial Pipeline has said that it was the victim of “a cybersecurity attack. In response, we proactively took certain systems offline to containthe
PETRI IT KNOWLEDGEBASE First launched by IT expert Daniel Petri in 1999, the Petri IT Knowledgebase has always been focused on serving the needs of IT professionals by providing information to help them solve problems, do their jobs more effectively, and to advance their careers. The Petri IT Knowledgebase is an independent website owned by Blue Whale WebInc.
NATIONAL AGENCY FOR INFORMATION & COMMUNICATION ANTIC is responsible for regulating the activities of electronic security and regulation of the Internet in Cameroon. The tasks of the Agency are to ensure, on behalf of the State: - the promotion and monitoring of government action in the field of Information and Communication Technologies (ICT AFCERT - CYBER SECURITY INTELLIGENCE AFCERT. AFCERT is the national Computer Emergency Response Team for Afghanistan. AFCERT operates as first responder to cyber and computer incidents in Afghanistan. RWANDA INFORMATION SOCIETY AUTHORITY (RISA) Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution to THE CYBER REVOLUTION’S EFFECTS ON INTERNATIONAL TRADE 14 hours ago · Practice Labs. Practice Labs is an IT competency hub, where live-lab environments give access to real equipment for hands-on practice of essential cybersecurity skills.UNBOUND SECURITY
9 hours ago · Unbound Security. Our vision at Unbound Security is to be the global cryptographic platform of choice for the enterprise. At Unbound Security we apply revolutionary breakthroughs in cryptography to empower enterprises to confidently secure and manage all their critical business transactions, information, and digital assets –anywhere, anytime.
CRIMINAL MESSAGING APP LEADS TO WIDESPREAD ARRESTS 1 day ago · A massive international sting, involving at least 17 countries, including the US, has arrested suspects, the seizure of 8 tons of cocaine and more than $48 million and over 800 suspected criminals have been arrested after being hoodwinked into using an FBI-run encrypted messaging app says the FBI and this is a continuation of Operation Trojan Shield. FUTURE THREATS ARE GROWING CLOSER 1 day ago · Future generations may look back at our time as one of intense change. In a few short decades, we have morphed from a machine-based society to an information-based society and society has been forced to develop a new and intimate familiarity with data-driven and algorithmic systems and two of the most interesting topics on the Internet today are Artificial Intelligence (AI) and Cyber Security. HOW HAS A YEAR OF PANDEMIC CHANGED CYBER SECURITY? The virus has impacted cyber in a major way. During the pandemic, “cyber criminals ditched many of their old tactics, placing a new emphasis on gathering intelligence, and exploiting and preying upon fears with targeted and sophisticated attacks.”. There was “a notable shift in the devices targeted and strategies deployed by cyber FAKE FINANCE APPS FOCUS ON THEFT Criminals have published hundreds of bogus banking, finance, and crypto-currency apps that steal your money. A team of researchers at Sophos say they have identified as many as 167 fake banking, trading and crypto-currency apps that criminals are using to steal money and financial information from unsuspecting users.. These fraudulent applications are aimed at exploiting the increased interest US MEDIA GROUP IN LATEST RANSOM ATTACK Live streams for radio and TV stations owned by the Cox Media Group, one of the largest media conglomerates in the US are the target of a ransomware attack.. The attack affected the internal networks and live streaming capabilities for Cox media properties, such as web streamsand mobile apps
REGULATIV.AI
9 hours ago · Regulativ.ai is an innovative and comprehensive platform, driven by AI, to address the regulatory and compliance needs of Cyber Security Regulatory compliance and reporting. The platform provides integrated aggregation, analytical, compliance and reporting for all your Cyber Security needs MICROSOFT’S DEFENSIVE PLAYBOOK Many company leaders, especially those leading SMEs, have little knowledge on how to defend their businesses from cyber attacks or how to respond if their company is hacked. Microsoft is now offering organisations advice on how to protect their cyber networks and it SAFE SECURITY (LUCIDEUS) Safe Security (previously Lucideus) provides Cyber risk assessment services and platforms to multiple Fortune 500 companies and governments across the globe. Security Assessment Framework for Enterprise (SAFE) - A dynamic & self evolving enterprise cyber security and risk management platform that integrates with your existing IT Infrastructure CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
CYBER SECURITY IN HIGHER EDUCATION Cyber Security In Higher Education. In response to the Coronavirus onslaught, higher education is rapidly migrating to remote and online learning and academic and IT leaders in the sector have faced an onslaught of challenges. Perhaps the greatest of these is the need for heightened cyber security, at the same time as budgets and resourcesare
RESILIENCE CYBER INSURANCE SOLUTIONS Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SECURITY RISKS OF CONTACTLESS PAYMENT Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
DFI - CYBER SECURITY INTELLIGENCE DFI. DFI is a global leading provider of high-performance computing technology across multiple embedded industries. With its innovative design and premium quality management system, DFI’s industrial-grade solutions enable customers to optimize their equipment and ensure high reliability, long-term life cycle, and 24/7 durability in a breadth of markets including factory automation, medical CRITICAL PIPELINE NETWORK SHUT DOWN BY HACKERS Critical Pipeline Network Shut Down By Hackers. A critical oil pipeline which supplies 45 percent of the east coast fuel supply has shut-down all pipeline operations after being hacked. Colonial Pipeline has said that it was the victim of “a cybersecurity attack. In response, we proactively took certain systems offline to containthe
PETRI IT KNOWLEDGEBASE First launched by IT expert Daniel Petri in 1999, the Petri IT Knowledgebase has always been focused on serving the needs of IT professionals by providing information to help them solve problems, do their jobs more effectively, and to advance their careers. The Petri IT Knowledgebase is an independent website owned by Blue Whale WebInc.
NATIONAL AGENCY FOR INFORMATION & COMMUNICATION ANTIC is responsible for regulating the activities of electronic security and regulation of the Internet in Cameroon. The tasks of the Agency are to ensure, on behalf of the State: - the promotion and monitoring of government action in the field of Information and Communication Technologies (ICT AFCERT - CYBER SECURITY INTELLIGENCE AFCERT. AFCERT is the national Computer Emergency Response Team for Afghanistan. AFCERT operates as first responder to cyber and computer incidents in Afghanistan. RWANDA INFORMATION SOCIETY AUTHORITY (RISA) Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution to CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
CYBER SECURITY IN HIGHER EDUCATION Cyber Security In Higher Education. In response to the Coronavirus onslaught, higher education is rapidly migrating to remote and online learning and academic and IT leaders in the sector have faced an onslaught of challenges. Perhaps the greatest of these is the need for heightened cyber security, at the same time as budgets and resourcesare
RESILIENCE CYBER INSURANCE SOLUTIONS Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SECURITY RISKS OF CONTACTLESS PAYMENT Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
DFI - CYBER SECURITY INTELLIGENCE DFI. DFI is a global leading provider of high-performance computing technology across multiple embedded industries. With its innovative design and premium quality management system, DFI’s industrial-grade solutions enable customers to optimize their equipment and ensure high reliability, long-term life cycle, and 24/7 durability in a breadth of markets including factory automation, medical CRITICAL PIPELINE NETWORK SHUT DOWN BY HACKERS Critical Pipeline Network Shut Down By Hackers. A critical oil pipeline which supplies 45 percent of the east coast fuel supply has shut-down all pipeline operations after being hacked. Colonial Pipeline has said that it was the victim of “a cybersecurity attack. In response, we proactively took certain systems offline to containthe
PETRI IT KNOWLEDGEBASE First launched by IT expert Daniel Petri in 1999, the Petri IT Knowledgebase has always been focused on serving the needs of IT professionals by providing information to help them solve problems, do their jobs more effectively, and to advance their careers. The Petri IT Knowledgebase is an independent website owned by Blue Whale WebInc.
NATIONAL AGENCY FOR INFORMATION & COMMUNICATION ANTIC is responsible for regulating the activities of electronic security and regulation of the Internet in Cameroon. The tasks of the Agency are to ensure, on behalf of the State: - the promotion and monitoring of government action in the field of Information and Communication Technologies (ICT AFCERT - CYBER SECURITY INTELLIGENCE AFCERT. AFCERT is the national Computer Emergency Response Team for Afghanistan. AFCERT operates as first responder to cyber and computer incidents in Afghanistan. RWANDA INFORMATION SOCIETY AUTHORITY (RISA) Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution to THE CYBER REVOLUTION’S EFFECTS ON INTERNATIONAL TRADE 11 hours ago · Practice Labs. Practice Labs is an IT competency hub, where live-lab environments give access to real equipment for hands-on practice of essential cybersecurity skills.UNBOUND SECURITY
7 hours ago · Unbound Security. Our vision at Unbound Security is to be the global cryptographic platform of choice for the enterprise. At Unbound Security we apply revolutionary breakthroughs in cryptography to empower enterprises to confidently secure and manage all their critical business transactions, information, and digital assets –anywhere, anytime.
CRIMINAL MESSAGING APP LEADS TO WIDESPREAD ARRESTS 1 day ago · A massive international sting, involving at least 17 countries, including the US, has arrested suspects, the seizure of 8 tons of cocaine and more than $48 million and over 800 suspected criminals have been arrested after being hoodwinked into using an FBI-run encrypted messaging app says the FBI and this is a continuation of Operation Trojan Shield. FUTURE THREATS ARE GROWING CLOSER 1 day ago · Future generations may look back at our time as one of intense change. In a few short decades, we have morphed from a machine-based society to an information-based society and society has been forced to develop a new and intimate familiarity with data-driven and algorithmic systems and two of the most interesting topics on the Internet today are Artificial Intelligence (AI) and Cyber Security. HOW HAS A YEAR OF PANDEMIC CHANGED CYBER SECURITY? The virus has impacted cyber in a major way. During the pandemic, “cyber criminals ditched many of their old tactics, placing a new emphasis on gathering intelligence, and exploiting and preying upon fears with targeted and sophisticated attacks.”. There was “a notable shift in the devices targeted and strategies deployed by cyber FAKE FINANCE APPS FOCUS ON THEFT Criminals have published hundreds of bogus banking, finance, and crypto-currency apps that steal your money. A team of researchers at Sophos say they have identified as many as 167 fake banking, trading and crypto-currency apps that criminals are using to steal money and financial information from unsuspecting users.. These fraudulent applications are aimed at exploiting the increased interest US MEDIA GROUP IN LATEST RANSOM ATTACK Live streams for radio and TV stations owned by the Cox Media Group, one of the largest media conglomerates in the US are the target of a ransomware attack.. The attack affected the internal networks and live streaming capabilities for Cox media properties, such as web streamsand mobile apps
REGULATIV.AI
6 hours ago · Regulativ.ai is an innovative and comprehensive platform, driven by AI, to address the regulatory and compliance needs of Cyber Security Regulatory compliance and reporting. The platform provides integrated aggregation, analytical, compliance and reporting for all your Cyber Security needs MICROSOFT’S DEFENSIVE PLAYBOOK Many company leaders, especially those leading SMEs, have little knowledge on how to defend their businesses from cyber attacks or how to respond if their company is hacked. Microsoft is now offering organisations advice on how to protect their cyber networks and it SAFE SECURITY (LUCIDEUS) Safe Security (previously Lucideus) provides Cyber risk assessment services and platforms to multiple Fortune 500 companies and governments across the globe. Security Assessment Framework for Enterprise (SAFE) - A dynamic & self evolving enterprise cyber security and risk management platform that integrates with your existing IT Infrastructure 2020: TOP ISSUES IN CYBER SECURITY 2020: Top Issues In Cyber Security. The pace of change in cybersecurity is quickening as technologies like 5G and artificial intelligence enable new services, products and modes of communication. Most medium and large organisations are coming to terms with the fact that a cyber security incident is not a factor of ‘if’, but rather‘when
CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
RESILIENCE CYBER INSURANCE SOLUTIONSCYBER RESILIENCE DEFINITIONCYBER RESILIENCE REVIEWDOD CYBER RESILIENCECYBER RESILIENCE FRAMEWORKNIST CYBER RESILIENCECYBER RESILIENCE PPT Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SECURITY RISKS OF CONTACTLESS PAYMENTHOW TO USE CONTACTLESS PAYMENTRISKS OF CONTACTLESS CREDIT CARDSCONTACTLESS PAYMENT COMPANIESCONTACTLESS PAYMENT HISTORYLEADERS IN CONTACTLESS PAYMENTSSQUARE CONTACTLESS PAYMENTS Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
HOW DO CYBER CRIMINALS OPERATE? Cyber security incidents have become more numerous and diverse and more damaging, with new types of cyber security attacks frequently emerging.Cyber crime should be a fairly open and shut case - cyber criminals execute a crime and then law enforcement should step in and catch the criminals and so the case should be closed. CRITICAL PIPELINE NETWORK SHUT DOWN BY HACKERS Critical Pipeline Network Shut Down By Hackers. A critical oil pipeline which supplies 45 percent of the east coast fuel supply has shut-down all pipeline operations after being hacked. Colonial Pipeline has said that it was the victim of “a cybersecurity attack. In response, we proactively took certain systems offline to containthe
BEECHERMADDEN
BeecherMadden. BeecherMadden is a leading UK and US cyber security recruitment business. Leveraging our long-held relationships, industry knowledge and data driven approach, we help candidates and clients make better hiring decisions. As one of the only niche recruitment businesses to house a dedicated cyber recruitment practice,experienced
90% OF BREACHES ARE CAUSED BY HUMAN ERROR ZenGRC. ZenGRC - the first, easy-to-use, enterprise-grade information security solution for compliance and risk management - offers businesses efficient control tracking, testing, and enforcement. IS SLACK SECURE FOR YOUR BUSINESS?IS SLACK SECURE AND PRIVATEIS SLACK SAFE TO USEIS SLACK PRIVATESLACK FOR PERSONALSLACK SECURITY CONCERNSISSLACK ENCRYPTED
Slack is used by 65 of the top Fortune 100 companies and over 85,000 businesses, from SMBs to large enterprises, are using the paid tier of Slack within their business. Slack is a great place to have secure conversations, but that doesn't mean you should treat it like it's watertight. Never use Slack to share secrets such as passwords RWANDA INFORMATION SOCIETY AUTHORITY (RISA)RWANDA EMBASSY VISARWANDA VISA AT AIRPORTRWANDA VISA ON ARRIVALLAND INFORMATION RWANDARWANDA COUNTRY INFORMATIONRWANDA VISA FOR US CITIZENS Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution to 2020: TOP ISSUES IN CYBER SECURITY 2020: Top Issues In Cyber Security. The pace of change in cybersecurity is quickening as technologies like 5G and artificial intelligence enable new services, products and modes of communication. Most medium and large organisations are coming to terms with the fact that a cyber security incident is not a factor of ‘if’, but rather‘when
CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. Designed for organizations that demand a clear and immediate return on investment, CYRISMA simplifies the process of identifying, assessing, and mitigating technical risks, allwhile
RESILIENCE CYBER INSURANCE SOLUTIONSCYBER RESILIENCE DEFINITIONCYBER RESILIENCE REVIEWDOD CYBER RESILIENCECYBER RESILIENCE FRAMEWORKNIST CYBER RESILIENCECYBER RESILIENCE PPT Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance and claims—all supported bysuperior data
SECURITY RISKS OF CONTACTLESS PAYMENTHOW TO USE CONTACTLESS PAYMENTRISKS OF CONTACTLESS CREDIT CARDSCONTACTLESS PAYMENT COMPANIESCONTACTLESS PAYMENT HISTORYLEADERS IN CONTACTLESS PAYMENTSSQUARE CONTACTLESS PAYMENTS Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
HOW DO CYBER CRIMINALS OPERATE? Cyber security incidents have become more numerous and diverse and more damaging, with new types of cyber security attacks frequently emerging.Cyber crime should be a fairly open and shut case - cyber criminals execute a crime and then law enforcement should step in and catch the criminals and so the case should be closed. CRITICAL PIPELINE NETWORK SHUT DOWN BY HACKERS Critical Pipeline Network Shut Down By Hackers. A critical oil pipeline which supplies 45 percent of the east coast fuel supply has shut-down all pipeline operations after being hacked. Colonial Pipeline has said that it was the victim of “a cybersecurity attack. In response, we proactively took certain systems offline to containthe
BEECHERMADDEN
BeecherMadden. BeecherMadden is a leading UK and US cyber security recruitment business. Leveraging our long-held relationships, industry knowledge and data driven approach, we help candidates and clients make better hiring decisions. As one of the only niche recruitment businesses to house a dedicated cyber recruitment practice,experienced
90% OF BREACHES ARE CAUSED BY HUMAN ERROR ZenGRC. ZenGRC - the first, easy-to-use, enterprise-grade information security solution for compliance and risk management - offers businesses efficient control tracking, testing, and enforcement. IS SLACK SECURE FOR YOUR BUSINESS?IS SLACK SECURE AND PRIVATEIS SLACK SAFE TO USEIS SLACK PRIVATESLACK FOR PERSONALSLACK SECURITY CONCERNSISSLACK ENCRYPTED
Slack is used by 65 of the top Fortune 100 companies and over 85,000 businesses, from SMBs to large enterprises, are using the paid tier of Slack within their business. Slack is a great place to have secure conversations, but that doesn't mean you should treat it like it's watertight. Never use Slack to share secrets such as passwords RWANDA INFORMATION SOCIETY AUTHORITY (RISA)RWANDA EMBASSY VISARWANDA VISA AT AIRPORTRWANDA VISA ON ARRIVALLAND INFORMATION RWANDARWANDA COUNTRY INFORMATIONRWANDA VISA FOR US CITIZENS Rwanda Information Society Authority (RISA) RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution to IDENTIFYING & MINIMIZING SECURITY VULNERABILITIES FOR YOUR 7 hours ago · When organizations are exposed to these vulnerabilities, bad actors can gain access to confidential company and client information. They can also acquire intellectual property, which poses a huge threat to the organization’s growth and credibility. Therefore, it is important for an organization FUTURE THREATS ARE GROWING CLOSER 6 hours ago · Future generations may look back at our time as one of intense change. In a few short decades, we have morphed from a machine-based society to an information-based society and society has been forced to develop a new and intimate familiarity with data-driven and algorithmic systems and two of the most interesting topics on the Internet today are Artificial Intelligence (AI) and Cyber Security. US MEDIA GROUP IN LATEST RANSOM ATTACK 1 day ago · Live streams for radio and TV stations owned by the Cox Media Group, one of the largest media conglomerates in the US are the target of a ransomware attack.. The attack affected the internal networks and live streaming capabilities for Cox media properties, such as web streams and mobile apps CYBER SECURITY MERGERS & ACQUISITIONS Cybersecurity mergers and acquisitions activity continued at a high rate in May with 35 deals involving companies from 12 countries including the USA, Canada, UK, Ireland, France, Germany, Switzerland, Netherlands, Croatia, Israel, India and New Zealand. Belcan has acquired VICTOR42, a FAKE FINANCE APPS FOCUS ON THEFT 1 day ago · Criminals have published hundreds of bogus banking, finance, and crypto-currency apps that steal your money. A team of researchers at Sophos say they have identified as many as 167 fake banking, trading and crypto-currency apps that criminals are using to steal money and financial information from unsuspecting users.. These fraudulent applications are aimed at exploiting the increased interest MICROSOFT’S DEFENSIVE PLAYBOOK 1 day ago · Many company leaders, especially those leading SMEs, have little knowledge on how to defend their businesses from cyber attacks or how to respond if their company is hacked. Microsoft is now offering organisations advice on how to protect their cyber networksand it
ONI LTD - CYBERSECURITYINTELLIGENCE.COM 1 day ago · ONI Ltd is a leading provider of IT solutions and services to both public sector and commercial markets. We offer a comprehensive range of on-site, cloud and hybrid technology solutions. Our expertise already spans core network infrastructure, unified communications and collaboration, contact centre GATEKEEPER ENTERPRISE GateKeeper Enterprise. GateKeeper Enterprise is a proximity enterprise identity and access management technology, servicing the enterprise security and access control markets. It provides automated privileged access management solutions for a wide range of industries including healthcare, MSP/MSSPs, law enforcement, manufacturing, and finance. RANSOMWARE AND ITS CRIMINAL USE Ransomware is a type of malicious software cyber criminals use to block you from accessing your own data. The digital extortionists encrypt the files on your system and add extensions to the attacked data and hold them ‘hostage’ until the demanded ransom is paid. MORGANFRANKLIN CONSULTING MorganFranklin Consulting is a management advisory firm that works with leading businesses and government to address complex and transformational technology and business objectives including cybersecurity. Our services provide a comprehensive and robust approach to solving your most critical 2020: TOP ISSUES IN CYBER SECURITY Cyber Security in 2020 will be defined by increasing connectivity. Business leaders and decision-makers need to think about the risks. CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. RESILIENCE CYBER INSURANCE SOLUTIONSCYBER RESILIENCE DEFINITIONCYBER RESILIENCE REVIEWDOD CYBER RESILIENCECYBER RESILIENCE FRAMEWORKNIST CYBER RESILIENCECYBER RESILIENCE PPT Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance SECURITY RISKS OF CONTACTLESS PAYMENTHOW TO USE CONTACTLESS PAYMENTRISKS OF CONTACTLESS CREDIT CARDSCONTACTLESS PAYMENT COMPANIESCONTACTLESS PAYMENT HISTORYLEADERS IN CONTACTLESS PAYMENTSSQUARE CONTACTLESS PAYMENTS Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
CRITICAL PIPELINE NETWORK SHUT DOWN BY HACKERS A critical oil pipeline which supplies 45 percent of the east coast fuel supply has shut-down all pipeline operations after being hacked. Colonial Pipeline has said that it was the victim of “a cybersecurity attack. In response, we proactively took certain systems offline to contain the threat, which has temporarily halted all pipeline operations, and affected some of our IT system."BEECHERMADDEN
BeecherMadden. BeecherMadden is a leading UK and US cyber security recruitment business. Leveraging our long-held relationships, industry knowledge and data driven approach, we help candidates and clients make better hiring decisions. 90% OF BREACHES ARE CAUSED BY HUMAN ERROR ZenGRC. ZenGRC - the first, easy-to-use, enterprise-grade information security solution for compliance and risk management - offers businesses efficient control tracking, testing, and enforcement. RWANDA INFORMATION SOCIETY AUTHORITY (RISA)RWANDA EMBASSY VISARWANDA VISA AT AIRPORTRWANDA VISA ON ARRIVALLAND INFORMATION RWANDARWANDA COUNTRY INFORMATIONRWANDA VISA FOR US CITIZENS RISA is at the forefront of all ICT project implementation, research, infrastructure and innovation within the ICT sector in Rwanda. RISA derives from the former IT department of Rwanda Development Board, RDB. Currently, it is an affiliated institution to the Ministry of Technology. It implements IS SLACK SECURE FOR YOUR BUSINESS?IS SLACK SECURE AND PRIVATEIS SLACK SAFE TO USEIS SLACK PRIVATESLACK FOR PERSONALSLACK SECURITY CONCERNSISSLACK ENCRYPTED
Slack is used as a communal discussion center for businesses and it has increased in popularity in the last few years. Slack now has 10 million daily active users, making it the leading platform for live discussions within organisations. Slack is used by 65 of the top Fortune 100 companies and over 85,000 businesses, from SMBs to large enterprises, are using the paid tier of Slack within their CRIME HAS GONE HIGH-TECH AND THE LAW HASN’T When most people hear the word “criminal,” they probably picture some dim-witted thug. But a security expert, Marc Goodman, has been fighting crime for more than 20 years and he’s learned the hard way that crime is increasingly going high-tech, leaving law enforcement struggling to keep up. 2020: TOP ISSUES IN CYBER SECURITY Cyber Security in 2020 will be defined by increasing connectivity. Business leaders and decision-makers need to think about the risks. CYRISMA - CYBER SECURITY INTELLIGENCE CYRISMA is a revolutionary cybersecurity platform that helps organizations manage risk without the usual headaches associated with enterprise cybersecurity tools. RESILIENCE CYBER INSURANCE SOLUTIONSCYBER RESILIENCE DEFINITIONCYBER RESILIENCE REVIEWDOD CYBER RESILIENCECYBER RESILIENCE FRAMEWORKNIST CYBER RESILIENCECYBER RESILIENCE PPT Resilience Cyber Insurance combines insurance expertise with cybersecurity and data talent to deliver clear, effective solutions to protect you for the cyberrisks of today—and tomorrow. Fighting cyberattacks demands a holistic approach. We bring together this full complement of security, insurance SECURITY RISKS OF CONTACTLESS PAYMENTHOW TO USE CONTACTLESS PAYMENTRISKS OF CONTACTLESS CREDIT CARDSCONTACTLESS PAYMENT COMPANIESCONTACTLESS PAYMENT HISTORYLEADERS IN CONTACTLESS PAYMENTSSQUARE CONTACTLESS PAYMENTS Consumers are driving the push towards contactless payment, with credit card companies revealing double-digit increases in its use during the first quarter of 2020.Contactless payment was first used in the 1990s and currently with Covid companies and consumers are looking for ways to conduct business with as little physical interaction aspossible.
US MEDIA GROUP IN LATEST RANSOM ATTACK 15 hours ago · Live streams for radio and TV stations owned by the Cox Media Group, one of the largest media conglomerates in the US are the target of a ransomware attack.. The attack affected the internal networks and live streaming capabilities for Cox media properties, such as web streams and mobile apps CYBER SECURITY MERGERS & ACQUISITIONS Cybersecurity mergers and acquisitions activity continued at a high rate in May with 35 deals involving companies from 12 countries including the USA, Canada, UK, Ireland, France, Germany, Switzerland, Netherlands, Croatia, Israel, India and New Zealand. Belcan has acquired VICTOR42, a FAKE FINANCE APPS FOCUS ON THEFT 12 hours ago · Criminals have published hundreds of bogus banking, finance, and crypto-currency apps that steal your money. A team of researchers at Sophos say they have identified as many as 167 fake banking, trading and crypto-currency apps that criminals are using to steal money and financial information from unsuspecting users.. These fraudulent applications are aimed at exploiting the CYBER SECURITY: ITS GOOD TO TALK The future of cyber security for all organisations lies in a more proactive approach with management and employees. A proactive security approach is designed to prevent attacks rather than react after an attack has happened. The days of waiting for an attack to be detected, then taking steps to MICROSOFT’S DEFENSIVE PLAYBOOK 13 hours ago · Many company leaders, especially those leading SMEs, have little knowledge on how to defend their businesses from cyber attacks or how to respond if their company is hacked. Microsoft is now offering organisations advice on how to protect their cyber networksand it
ELECTRONIC ESPIONAGE WILL USE AI INSTEAD OF SPIES In our latest Directors Report, Cyber Security Intelligence goes into depth to look at important past history concerning intelligence and spying. The British spy agency, GCHQ, has developing innovation ion the fields of cyber technology and electronic data ONI LTD - CYBERSECURITYINTELLIGENCE.COM 12 hours ago · ONI Ltd is a leading provider of IT solutions and services to both public sector and commercial markets. We offer a comprehensive range of on-site, cloud and hybrid technology solutions. Our expertise already spans core network infrastructure, unified communications and collaboration, contact centre RANSOMWARE AND ITS CRIMINAL USE Ransomware is a type of malicious software cyber criminals use to block you from accessing your own data. The digital extortionists encrypt the files on your system and add extensions to the attacked data and hold them ‘hostage’ until the demanded ransom is paid. VODAFONE USING GOOGLE CLOUD TO RETAIN CUSTOMERS Currently Vodafone is working with Google to develop a cloud-based data platform to help telcos, (telecoms companies), find new opportunities and improve relationships with their customers.Recent studies have shown that telcos are increasingly struggling to find new revenue streams, despite investing heavily into 4G and 5G networks. MORGANFRANKLIN CONSULTING 1 day ago · MorganFranklin Consulting is a management advisory firm that works with leading businesses and government to address complex and transformational technology and business objectives including cybersecurity. Our services provide a comprehensive and robust approach to solving your most criticalMenu
* NEWS ►
* News Analysis
* Newsletter Archive* BUSINESS ►
* Production
* Energy
* Manufacturing
* Utilities
* Services
* Consulting
* Financial
* Health & Welfare
* IT & Telecoms
* Law
* Transport & Travel* GOVERNMENT ►
* Defence
* Local
* National
* Police
* TECHNOLOGY ►
* Forensics
* Hackers
* New
* Reports
* Social Media
* INTELLIGENCE ►
* Europe
* International
* US
* JOBS ►
* Careers
* Education
* DIRECTORY ►
* Browse Categories
* Browse Locations
* Advanced Search
* SUBSCRIBER AREA ►* My Account
* Directors Reports
Subscribe
Login
* HOME
* NEWS
* News Analysis
* Newsletter Archive* BUSINESS
* Production
* Energy
* Manufacturing
* Utilities
* Services
* Consulting
* Financial
* Health & Welfare
* IT & Telecoms
* Law
* Transport & Travel* GOVERNMENT
* Defence
* Local
* National
* Police
* TECHNOLOGY
* Forensics
* Hackers
* New
* Reports
* Social Media
* INTELLIGENCE
* Europe
* International
* US
* JOBS
* Careers
* Education
* DIRECTORY
* Browse Categories
* Browse Locations
* Advanced Search
* SUBSCRIBER AREA
* My Account
* Directors Reports
* ABOUT
* Who We Are
* Contact
* Commercial Terms
For continued FREE access to Articles and Directory Listings please Login to your Account or Sign Up.Subscribe
Login
2020-11-23
SANS BOOK: PRACTICAL GUIDE TO SECURITY IN THE AWS CLOUD SANS' Practical Guide to Security in the AWS Cloud. Tactics, techniques and procedures for securely operating in the cloud.Download Now
Read More
2020-12-01
BRITAIN BANS HUAWEI 5G The UK government will ban new Huawei technology from the national telecoms network from September of 2021 - much earlier expected.Read More
2020-12-01
AMAZON WEB SERVICES OUTAGE AWS is a giant cloud services provider and a recent outage has rippled across the web services and apps of numerous companies affected.Read More
2020-11-30
DIVING INTO THE DARK WEB Sensitive information often ends up for sale on the black market in the Dark Web, compromising the security of businesses and theiremployees.
Read More
2020-11-30
NEW BRITISH TELECOMS SECURITY LAW Britain will take new national security powers to issue directions to public telecoms providers to manage the threat from 'high-risk'vendors.
Read More
2020-11-27
NCSC COME OFF BENCH TO HELP MANCHESTER UNITED The British National Cyber Security Centre (NCSC) is assisting Manchester United to recover after a cyber attack, which has left somesystems offline.
Read More
2020-11-27
A ‘FUNNYDREAM’ FROM CHINA Some senior corporate executives have been having nightmares about being hacked on their business trips in Asia. They're not justdreaming.
Read More
2020-11-27
CYBER SECURITY HAS BECOME CRITICAL FOR NATIONAL SECURITY Critical national infrastructure, both public and private, is increasingly interconnected and has become susceptible to predatorycyberattacks.
Read More
2020-11-26
DONALD TRUMP HAD HIS TWITTER ACCOUNT HACKED A Dutch cyber investigator has claimed he gained access to Donald Trump's Twitter account with the password 'MAGA2020!' Police areinvestigating.
Read More
2020-11-26
HOW THE INTERNET HAS TRANSFORMED OUR LIVES Those born after 1990 may not realise the profound effects of the Internet on almost every aspect of modern life. Both good and bad.Read More
Real Attacks. Real Tools. Real Scenarios.Schedule a demo
SIGN UP: Cyber Security Intelligence Newsletter DIRECTORY OF SUPPLIERS CYBER SECURITY SERVICE SUPPLIER DIRECTORY Free Access: Cyber Security Service Supplier Directory listing 5,000+ specialist service providers.MIRACL
MIRACL provides the world’s only single step Multi-Factor Authentication (MFA) which can replace passwords on 100% of mobiles, desktops or even Smart TVs.CLAYDEN LAW
Clayden Law are experts in information technology, data privacy andcybersecurity law.
BACKUPVAULT
BackupVault is a leading provider of completely automatic, fully encrypted online, cloud backup.CYRIN
CYRIN® Cyber Range. Real Tools, Real Attacks, Real Scenarios. See why leading educational institutions and companies in the U.S. have begun to adopt the CYRIN® system. CSI CONSULTING SERVICES Get Advice From The Experts: * Training * Penetration Testing * Data Governance * GDPR Compliance. Connecting you to the best in thebusiness.
DIGITALSTAKEOUT
A simple and cost-effective solution to monitor, investigate and analyze data from the web, social media and cyber sources to identify threats and make better security decisions.IT GOVERNANCE
IT Governance is a leading global provider of information security solutions. Download our free guide and find out how ISO 27001 can help protect your organisation's information.JOOBLE
Jooble is a job search aggregator operating in 71 countries worldwide. We simplify the job search process by displaying active job ads from major job boards and career sites across the internet. EBOOK: PRACTICAL GUIDE TO SECURITY IN THE AWS CLOUD AWS Marketplace would like to present you with a digital copy of the new book, Practical Guide to Security in the AWS Cloud, by the SANSInstitute.
HSI CYBER CRIMES CENTER HSI's Cyber Crimes Center delivers computer-based technical services to support domestic and international investigations into cross-bordercrime.
STMICROELECTRONICS
ST is a global semiconductor company serving customers across the spectrum of electronics applications including Smart Cars and theInternet of Things.
TRUSTAR TECHNOLOGY
TruSTAR is a threat intelligence exchange platform built to protect and incentivize information sharing.ZETTASET
Zettaset’s XCrypt Data Encryption Platform delivers proven protection for Object, Relational/SQL, NoSQL, and Hadoop data stores…in the cloud and on-premises.CALIAN GROUP
Calian is a diverse Canadian company offering professional services in areas including IT Consulting, Cyber Security and IT Products.EXEIN
Exein provide security software and middleware that can be injected like a vaccine into existing hardware and defend it from inside, working directly into the firmware at a lower level.VILNIUS TECH PARK
The region‘s most complex and integrated ICT hub, Vilnius Tech Park aims to attract and unite innovative talent from big data, cyber security, smart solutions, fintech and digital design.USTELS
Ustels provides brand protection strategy, intelligence, monitoring and enforcement services.* BUSINESS
* Energy
* Manufacturing
* Utilities
* Consulting
* Financial
* Health & Welfare
* IT & Communications* Law
* Transport & Travel* GOVERNMENT
* Defence
* Local
* National
* Police
* TECHNOLOGY
* Forensics
* Hackers
* New
* Reports
* Social Media
* INTELLIGENCE
* Europe
* International
* US
* DIRECTORY
* Browse Categories
* Browse Locations
* Advanced Search
*
* ABOUT US
* Contact
* Who We Are
* Commercial Terms
* Register / Subscribe* Legal
CAPTURED ORGANISED ACCESSIBLE All content © 2020 Cyber Security Intelligence site by pixel concepts / redwaxShare
Tweet
Share
Share
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0