Are you over 18 and want to see adult content?
More Annotations
A complete backup of www.blick.ch/people-tv/international/im-kreuzverhoer-waehrend-vergewaltigungs-prozess-weinstein-zeugin-bric
Are you over 18 and want to see adult content?
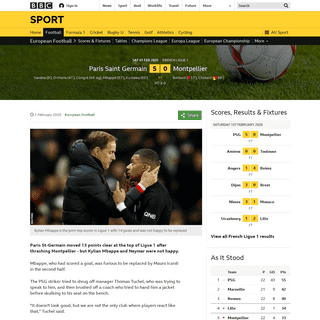
A complete backup of www.bbc.co.uk/sport/football/51344588
Are you over 18 and want to see adult content?
A complete backup of www.ladepeche.fr/2020/02/01/amber-heard-reconnait-avoir-frappe-johnny-depp-je-suis-tellement-en-colere-que-
Are you over 18 and want to see adult content?

A complete backup of orf.at/stories/3153143/
Are you over 18 and want to see adult content?

A complete backup of www.krone.at/2090138
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://baixartorrent.net/
Are you over 18 and want to see adult content?
A complete backup of https://www.msn.com/zh-tw/
Are you over 18 and want to see adult content?
A complete backup of https://www.pandora.com/artist/free/ARdjfpxjpcrKrfg
Are you over 18 and want to see adult content?
A complete backup of https://libros.plus/la-santa-biblia-2/
Are you over 18 and want to see adult content?
A complete backup of https://potasio-remix.yump3.me/
Are you over 18 and want to see adult content?
A complete backup of https://www.mundotecnico.info/viewtopic.php?t=2186
Are you over 18 and want to see adult content?
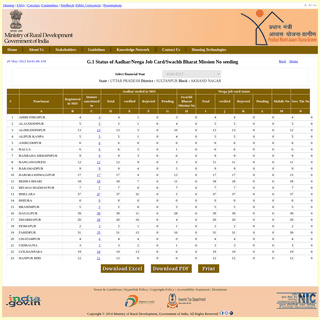
A complete backup of https://rhreporting.nic.in/netiay/ConvergenceReport/Aadhar_seeded.aspx?page1=b&state_code=31&state_name=UTT
Are you over 18 and want to see adult content?
A complete backup of https://chinaq.tv/horse-doctor/
Are you over 18 and want to see adult content?
A complete backup of https://kbcliv.in/
Are you over 18 and want to see adult content?
A complete backup of https://www.blogger.com/profile/17206596968156648538
Are you over 18 and want to see adult content?
A complete backup of https://www.pinterest.ca/dianes2420/beer-history/
Are you over 18 and want to see adult content?
Text
product.
OPEN BANKING: OPEN FOR BUSINESS Open Banking: Open for Business. Context have worked with a number of organisations to help them integrate securely with the Open Banking ecosystem, both banks (ASPSPs) and third party providers (TPPs). This post is the first in a series of articles where we will share some of the knowledge accumulated in the process. MANUALLY TESTING SSL/TLS WEAKNESSES Manually Testing SSL/TLS Weaknesses. The Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols aim to provide client and server systems with a means of establishing an encrypted communication channel. Though best known for putting the "S" in HTTPS, their use is not limited to web-based systems; they are also commonly used as a WIRELESS PHISHING WITH CAPTIVE PORTALS Wireless phishing is any technique by which an attacker attempts to convince wireless network users to divulge sensitive information. As we previously mentioned the associated wireless network is generally open and access to network resources is mediated by a web application known as a captive portal. Typically the attacker creates their own PUSH TO HACK: REVERSE ENGINEERING AN IP CAMERA 02 Feb 2016. Reverse Engineering. The Motorola Focus 73 outdoor security camera is packed with features and quite a few surprises - it's not made by Motorola for starters. It's the outdoor variant of a family of Blink and Motorola IP cameras manufactured by Binatone which includes baby monitors. All these products boast cloud connectivityvia
HACKING INTO INTERNET CONNECTED LIGHT BULBS DEMYSTIFYING THE EXPLOIT KIT 301 Moved Permanently. nginx CONTEXT INFORMATION SECURITY We are a certified cyber security consultancy helping clients avoid potential breaches and to deter, detect and respond to the most sophisticated cyber-attacks. Now a part of Accenture Security, our services include a comprehensive portfolio of advisory and advanced technical cyber security services. View Our CONTACT US | CONTEXT INFORMATION SECURITY General Enquiries. +44 (0)20 7537 7515. +44 (0)20 7537 1071. info@contextis.com. recruitment@contextis.com. Context Information Security works with a Preferred Suppliers List when partnering with recruitment agencies. The selection and briefing of recruitment agencies is always at the instigation of the Company. RANSOMWARE - IDENTIFYING PATIENT ZERO This file ownership information can assist in identifying the user and computers on which the ransomware is running. This step is mostly conducted on the file server on which the files are being encrypted. The quickest way to identify the owner is to open the file properties of an encrypted file and view the owner in the “Details” tab. PRODUCT SECURITY ASSESSMENT, IOT PENETRATION TESTING Product security testing. This service is designed to deliver the level of assurance for the appropriate threats. It is not a full product assurance process, which can take many weeks (if you do want that, or want to sell to UK Government, look into CPA or CTAS), but a way of achieving a pragmatic measure of assurance in the security of aproduct.
OPEN BANKING: OPEN FOR BUSINESS Open Banking: Open for Business. Context have worked with a number of organisations to help them integrate securely with the Open Banking ecosystem, both banks (ASPSPs) and third party providers (TPPs). This post is the first in a series of articles where we will share some of the knowledge accumulated in the process. MANUALLY TESTING SSL/TLS WEAKNESSES Manually Testing SSL/TLS Weaknesses. The Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols aim to provide client and server systems with a means of establishing an encrypted communication channel. Though best known for putting the "S" in HTTPS, their use is not limited to web-based systems; they are also commonly used as a WIRELESS PHISHING WITH CAPTIVE PORTALS Wireless phishing is any technique by which an attacker attempts to convince wireless network users to divulge sensitive information. As we previously mentioned the associated wireless network is generally open and access to network resources is mediated by a web application known as a captive portal. Typically the attacker creates their own PUSH TO HACK: REVERSE ENGINEERING AN IP CAMERA 02 Feb 2016. Reverse Engineering. The Motorola Focus 73 outdoor security camera is packed with features and quite a few surprises - it's not made by Motorola for starters. It's the outdoor variant of a family of Blink and Motorola IP cameras manufactured by Binatone which includes baby monitors. All these products boast cloud connectivityvia
HACKING INTO INTERNET CONNECTED LIGHT BULBS DEMYSTIFYING THE EXPLOIT KIT 301 Moved Permanently. nginxCAREERS AT CONTEXT
0800 082 0822 response@contextis.com. Exploit your potential. Apply your skills. Work with some of the best in the industry, on prestigious projects with the world’s most high profile blue chip companies and enjoy the benefits of being a part of AccentureSecurity.
CONDUCTING ONSITE SECURITY TESTING REMOTELY Our solution – called TRigER (Testing Rig for Engaging Remotely) – allows us to support our clients and deliver comprehensive security assessment remotely. TRigER is a physical appliance that, once installed on your network, allows Context security consultants to securely access your internal estate and perform routine securityassessments
CVES & ADVISORIES
CVEs & Advisories. At Context we are committed to ensuring and improving the security of our clients. Whether for clients or our own purposes, we regularly carry out independent security audits and vulnerability research against third-party software and hardware products. Identifier. PENETRATION TESTING SERVICES What is Penetration testing? A penetration test (also known as a pentest) is a security assessment aimed at identifying technical vulnerabilities in IT and communications systems that could leave your organisation open to attack should they be exploited by a potential threat actor. Once identified, these weak points – which can bewithin
WIRELESS PHISHING WITH CAPTIVE PORTALS Wireless phishing is any technique by which an attacker attempts to convince wireless network users to divulge sensitive information. As we previously mentioned the associated wireless network is generally open and access to network resources is mediated by a web application known as a captive portal. Typically the attacker creates their own HARDWARE ENCRYPTION WEAKNESSES AND BITLOCKER This allows traditional hard drives and SSDs that don’t support hardware encryption to provide full disk encryption. Some of the disadvantages of software encryption include: Encryption software has to be supported by the operating system. Encryption key is cached in the host's memory. There is a performance overhead.DYNAMICWRAPPEREX
Once the Automation controller knows that the function or property exists, the Invoke method is called to execute a function, modify, or read a property. The first parameter dispIdMember is the dispatch ID, the second parameter riid must be null, and the third parameter lcid is the local identifier.. To understand the remaining parameters, it is important to understand that Invoke is a generic A CODE SIGNING BYPASS FOR THE VW POLO A code signing bypass for the VW Polo. Focusing on the infotainment system of the Volkswagen® Polo®, and will reveal how the security checks which prevent modifications to its firmware can be circumvented by an attacker in order to allow privileged execution and unrestricted access to the infotainment system’s internals. INCIDENT RESPONSE PLANNING A cyber Incident Response Plan (IRP) prepares the organisation so that a coherent and coordinated response can be managed, regardless of the situation, and thereby limit the impact that an incident could have on ongoing operations. To think of this in terms that might be easier to relate to, every organisation will have a fire evacuation plan. DON'T FEED THEM AFTER MIDNIGHT: REVERSE-ENGINEERING THE The first 30 bytes here seem to form the word "FURBY" as a unicode string. This turned out to be true of all DLC files we observed, and appears to be the file signature for Furby Connect DLC files. Next, we see a couple of lines which clearly contain the word "DLC" followed by CONTEXT INFORMATION SECURITY We are a certified cyber security consultancy helping clients avoid potential breaches and to deter, detect and respond to the most sophisticated cyber-attacks. Now a part of Accenture Security, our services include a comprehensive portfolio of advisory and advanced technical cyber security services. View Our CONTACT US | CONTEXT INFORMATION SECURITY General Enquiries. +44 (0)20 7537 7515. +44 (0)20 7537 1071. info@contextis.com. recruitment@contextis.com. Context Information Security works with a Preferred Suppliers List when partnering with recruitment agencies. The selection and briefing of recruitment agencies is always at the instigation of the Company. PRODUCT SECURITY ASSESSMENT, IOT PENETRATION TESTING Product security testing. This service is designed to deliver the level of assurance for the appropriate threats. It is not a full product assurance process, which can take many weeks (if you do want that, or want to sell to UK Government, look into CPA or CTAS), but a way of achieving a pragmatic measure of assurance in the security of aproduct.
RANSOMWARE - IDENTIFYING PATIENT ZERO This file ownership information can assist in identifying the user and computers on which the ransomware is running. This step is mostly conducted on the file server on which the files are being encrypted. The quickest way to identify the owner is to open the file properties of an encrypted file and view the owner in the “Details” tab. PENETRATION TESTING SERVICES What is Penetration testing? A penetration test (also known as a pentest) is a security assessment aimed at identifying technical vulnerabilities in IT and communications systems that could leave your organisation open to attack should they be exploited by a potential threat actor. Once identified, these weak points – which can bewithin
HARDWARE ENCRYPTION WEAKNESSES AND BITLOCKER PUSH TO HACK: REVERSE ENGINEERING AN IP CAMERA 02 Feb 2016. Reverse Engineering. The Motorola Focus 73 outdoor security camera is packed with features and quite a few surprises - it's not made by Motorola for starters. It's the outdoor variant of a family of Blink and Motorola IP cameras manufactured by Binatone which includes baby monitors. All these products boast cloud connectivityvia
MANUALLY TESTING SSL/TLS WEAKNESSES Manually Testing SSL/TLS Weaknesses. The Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols aim to provide client and server systems with a means of establishing an encrypted communication channel. Though best known for putting the "S" in HTTPS, their use is not limited to web-based systems; they are also commonly used as a WIRELESS PHISHING WITH CAPTIVE PORTALS Wireless phishing is any technique by which an attacker attempts to convince wireless network users to divulge sensitive information. As we previously mentioned the associated wireless network is generally open and access to network resources is mediated by a web application known as a captive portal. Typically the attacker creates their own DEMYSTIFYING THE EXPLOIT KIT 301 Moved Permanently. nginx CONTEXT INFORMATION SECURITY We are a certified cyber security consultancy helping clients avoid potential breaches and to deter, detect and respond to the most sophisticated cyber-attacks. Now a part of Accenture Security, our services include a comprehensive portfolio of advisory and advanced technical cyber security services. View Our CONTACT US | CONTEXT INFORMATION SECURITY General Enquiries. +44 (0)20 7537 7515. +44 (0)20 7537 1071. info@contextis.com. recruitment@contextis.com. Context Information Security works with a Preferred Suppliers List when partnering with recruitment agencies. The selection and briefing of recruitment agencies is always at the instigation of the Company. PRODUCT SECURITY ASSESSMENT, IOT PENETRATION TESTING Product security testing. This service is designed to deliver the level of assurance for the appropriate threats. It is not a full product assurance process, which can take many weeks (if you do want that, or want to sell to UK Government, look into CPA or CTAS), but a way of achieving a pragmatic measure of assurance in the security of aproduct.
RANSOMWARE - IDENTIFYING PATIENT ZERO This file ownership information can assist in identifying the user and computers on which the ransomware is running. This step is mostly conducted on the file server on which the files are being encrypted. The quickest way to identify the owner is to open the file properties of an encrypted file and view the owner in the “Details” tab. PENETRATION TESTING SERVICES What is Penetration testing? A penetration test (also known as a pentest) is a security assessment aimed at identifying technical vulnerabilities in IT and communications systems that could leave your organisation open to attack should they be exploited by a potential threat actor. Once identified, these weak points – which can bewithin
HARDWARE ENCRYPTION WEAKNESSES AND BITLOCKER PUSH TO HACK: REVERSE ENGINEERING AN IP CAMERA 02 Feb 2016. Reverse Engineering. The Motorola Focus 73 outdoor security camera is packed with features and quite a few surprises - it's not made by Motorola for starters. It's the outdoor variant of a family of Blink and Motorola IP cameras manufactured by Binatone which includes baby monitors. All these products boast cloud connectivityvia
MANUALLY TESTING SSL/TLS WEAKNESSES Manually Testing SSL/TLS Weaknesses. The Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols aim to provide client and server systems with a means of establishing an encrypted communication channel. Though best known for putting the "S" in HTTPS, their use is not limited to web-based systems; they are also commonly used as a WIRELESS PHISHING WITH CAPTIVE PORTALS Wireless phishing is any technique by which an attacker attempts to convince wireless network users to divulge sensitive information. As we previously mentioned the associated wireless network is generally open and access to network resources is mediated by a web application known as a captive portal. Typically the attacker creates their own DEMYSTIFYING THE EXPLOIT KIT 301 Moved Permanently. nginx PENETRATION TESTING SERVICES What is Penetration testing? A penetration test (also known as a pentest) is a security assessment aimed at identifying technical vulnerabilities in IT and communications systems that could leave your organisation open to attack should they be exploited by a potential threat actor. Once identified, these weak points – which can bewithin
CONDUCTING ONSITE SECURITY TESTING REMOTELY Our solution – called TRigER (Testing Rig for Engaging Remotely) – allows us to support our clients and deliver comprehensive security assessment remotely. TRigER is a physical appliance that, once installed on your network, allows Context security consultants to securely access your internal estate and perform routine securityassessments
TESTTRACKER
TestTracker is a workflow management solution which allows organisations to easily procure and track their security assessments from start to finish. It helps to streamline this process so that the teams involved in the process can spend less time performi OPEN BANKING: READ/WRITE API & TOOLING We conclude our Open Banking blog series with an overview of the Read/Write API permission model, technical workflow and tooling required for a successful security assessment.ICS SECURITY
IT – Information Technology. This is the hardware and software used for storing, retrieving, or transmitting information; OT – Operational Technology. This is hardware and software that monitors or triggers changes in physical devices, and will be used in this post to refer to the component devices of ICS systems; WAN – Wide AreaNetwork.
COST EFFECTIVE DRONE DETECTION COPTHORNE. For the last few years Context have invested substantial effort into cost effective drone detection in partnership with a leading radio manufacturer. The outcome is a lightweight, passive, cloud-based RF survey system based upon their compact SDRs. WIRELESS PHISHING WITH CAPTIVE PORTALS Wireless phishing is any technique by which an attacker attempts to convince wireless network users to divulge sensitive information. As we previously mentioned the associated wireless network is generally open and access to network resources is mediated by a web application known as a captive portal. Typically the attacker creates their own RANSOMWARE - FIRST STEPS TO TAKE AFTER IDENTIFYING AN Secondary Tasks. With the spread of infection limited and the source host isolated, the following tasks can be taken at a slower pace: Identify the ransomware family. Analyse with a sandbox; Identifying the strain or type of ransomware can be a complex process, however, there are lots of tools and information to assist in this. INCIDENT RESPONSE PLANNING A cyber Incident Response Plan (IRP) prepares the organisation so that a coherent and coordinated response can be managed, regardless of the situation, and thereby limit the impact that an incident could have on ongoing operations. To think of this in terms that might be easier to relate to, every organisation will have a fire evacuation plan. LINUX PRIVILEGE ESCALATION VIA DYNAMICALLY LINKED SHARED Linux applications may make use of dynamically linked shared object libraries (let’s just call them shared libraries from now on) to provide application functionality without having to re-write the same code over and over - a bit like a .DLL in Windows applications. CONTEXT INFORMATION SECURITY We are a certified cyber security consultancy helping clients avoid potential breaches and to deter, detect and respond to the most sophisticated cyber-attacks. Now a part of Accenture Security, our services include a comprehensive portfolio of advisory and advanced technical cyber security services. View Our PRODUCT SECURITY ASSESSMENT, IOT PENETRATION TESTING Product security testing. This service is designed to deliver the level of assurance for the appropriate threats. It is not a full product assurance process, which can take many weeks (if you do want that, or want to sell to UK Government, look into CPA or CTAS), but a way of achieving a pragmatic measure of assurance in the security of aproduct.
RANSOMWARE - IDENTIFYING PATIENT ZERO This file ownership information can assist in identifying the user and computers on which the ransomware is running. This step is mostly conducted on the file server on which the files are being encrypted. The quickest way to identify the owner is to open the file properties of an encrypted file and view the owner in the “Details” tab. OPEN BANKING: READ/WRITE API & TOOLING OPEN BANKING: OPEN FOR BUSINESS Open Banking: Open for Business. Context have worked with a number of organisations to help them integrate securely with the Open Banking ecosystem, both banks (ASPSPs) and third party providers (TPPs). This post is the first in a series of articles where we will share some of the knowledge accumulated in the process. WIRELESS PHISHING WITH CAPTIVE PORTALS Wireless phishing is any technique by which an attacker attempts to convince wireless network users to divulge sensitive information. As we previously mentioned the associated wireless network is generally open and access to network resources is mediated by a web application known as a captive portal. Typically the attacker creates their own PUSH TO HACK: REVERSE ENGINEERING AN IP CAMERA 02 Feb 2016. Reverse Engineering. The Motorola Focus 73 outdoor security camera is packed with features and quite a few surprises - it's not made by Motorola for starters. It's the outdoor variant of a family of Blink and Motorola IP cameras manufactured by Binatone which includes baby monitors. All these products boast cloud connectivityvia
MANUALLY TESTING SSL/TLS WEAKNESSES Manually Testing SSL/TLS Weaknesses. The Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols aim to provide client and server systems with a means of establishing an encrypted communication channel. Though best known for putting the "S" in HTTPS, their use is not limited to web-based systems; they are also commonly used as a HACKING INTO INTERNET CONNECTED LIGHT BULBS XSLT SERVER SIDE INJECTION ATTACKS XSLT Server Side Injection Attacks. Extensible Stylesheet Language Transformations (XSLT) vulnerabilities can have serious consequences for the affected applications, often resulting in remote code execution. Examples of XSLT remote code execution vulnerabilities with public exploits are CVE-2012-5357 affecting the .Net Ektron CMS;CVE-2012
CONTEXT INFORMATION SECURITY We are a certified cyber security consultancy helping clients avoid potential breaches and to deter, detect and respond to the most sophisticated cyber-attacks. Now a part of Accenture Security, our services include a comprehensive portfolio of advisory and advanced technical cyber security services. View Our PRODUCT SECURITY ASSESSMENT, IOT PENETRATION TESTING Product security testing. This service is designed to deliver the level of assurance for the appropriate threats. It is not a full product assurance process, which can take many weeks (if you do want that, or want to sell to UK Government, look into CPA or CTAS), but a way of achieving a pragmatic measure of assurance in the security of aproduct.
RANSOMWARE - IDENTIFYING PATIENT ZERO This file ownership information can assist in identifying the user and computers on which the ransomware is running. This step is mostly conducted on the file server on which the files are being encrypted. The quickest way to identify the owner is to open the file properties of an encrypted file and view the owner in the “Details” tab. OPEN BANKING: READ/WRITE API & TOOLING OPEN BANKING: OPEN FOR BUSINESS Open Banking: Open for Business. Context have worked with a number of organisations to help them integrate securely with the Open Banking ecosystem, both banks (ASPSPs) and third party providers (TPPs). This post is the first in a series of articles where we will share some of the knowledge accumulated in the process. WIRELESS PHISHING WITH CAPTIVE PORTALS Wireless phishing is any technique by which an attacker attempts to convince wireless network users to divulge sensitive information. As we previously mentioned the associated wireless network is generally open and access to network resources is mediated by a web application known as a captive portal. Typically the attacker creates their own PUSH TO HACK: REVERSE ENGINEERING AN IP CAMERA 02 Feb 2016. Reverse Engineering. The Motorola Focus 73 outdoor security camera is packed with features and quite a few surprises - it's not made by Motorola for starters. It's the outdoor variant of a family of Blink and Motorola IP cameras manufactured by Binatone which includes baby monitors. All these products boast cloud connectivityvia
MANUALLY TESTING SSL/TLS WEAKNESSES Manually Testing SSL/TLS Weaknesses. The Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols aim to provide client and server systems with a means of establishing an encrypted communication channel. Though best known for putting the "S" in HTTPS, their use is not limited to web-based systems; they are also commonly used as a HACKING INTO INTERNET CONNECTED LIGHT BULBS XSLT SERVER SIDE INJECTION ATTACKS XSLT Server Side Injection Attacks. Extensible Stylesheet Language Transformations (XSLT) vulnerabilities can have serious consequences for the affected applications, often resulting in remote code execution. Examples of XSLT remote code execution vulnerabilities with public exploits are CVE-2012-5357 affecting the .Net Ektron CMS;CVE-2012
CAREERS AT CONTEXT
0800 082 0822 response@contextis.com. Exploit your potential. Apply your skills. Work with some of the best in the industry, on prestigious projects with the world’s most high profile blue chip companies and enjoy the benefits of being a part of AccentureSecurity.
MANAGED PHISHING SIMULATION SERVICE Benefits of Context's managed phishing simulation service: Send targeted simulated phishing emails to your employees/users in a controlled manner. Design a range of targeted phishing emails varying from mass-emailed messages to highly targeted emails. Track user actions in a safe and non-intrusive way; anonymized if required. CONDUCTING ONSITE SECURITY TESTING REMOTELY Our solution – called TRigER (Testing Rig for Engaging Remotely) – allows us to support our clients and deliver comprehensive security assessment remotely. TRigER is a physical appliance that, once installed on your network, allows Context security consultants to securely access your internal estate and perform routine securityassessments
CYBER SECURITY USER AWARENESS TRAINING Context’s cyber security end user training sessions demonstrate to staff why their organisation is a target for cyber-attacks and how attackers will seek to target them as a way to steal sensitive data or funds. The briefing examines the major cyber threat groupings, givingrelevant and
MANUALLY TESTING SSL/TLS WEAKNESSES Manually Testing SSL/TLS Weaknesses. The Secure Sockets Layer (SSL) and Transport Layer Security (TLS) protocols aim to provide client and server systems with a means of establishing an encrypted communication channel. Though best known for putting the "S" in HTTPS, their use is not limited to web-based systems; they are also commonly used as a HARDWARE ENCRYPTION WEAKNESSES AND BITLOCKER This allows traditional hard drives and SSDs that don’t support hardware encryption to provide full disk encryption. Some of the disadvantages of software encryption include: Encryption software has to be supported by the operating system. Encryption key is cached in the host's memory. There is a performance overhead.ICS SECURITY
IT – Information Technology. This is the hardware and software used for storing, retrieving, or transmitting information; OT – Operational Technology. This is hardware and software that monitors or triggers changes in physical devices, and will be used in this post to refer to the component devices of ICS systems; WAN – Wide AreaNetwork.
RANSOMWARE - FIRST STEPS TO TAKE AFTER IDENTIFYING AN Secondary Tasks. With the spread of infection limited and the source host isolated, the following tasks can be taken at a slower pace: Identify the ransomware family. Analyse with a sandbox; Identifying the strain or type of ransomware can be a complex process, however, there are lots of tools and information to assist in this. WEBGL – MORE WEBGL SECURITY FLAWS WebGL – More WebGL Security Flaws. In this blog post Context demonstrates how to steal user data through web browsers using a vulnerability in Firefox’s implementation of WebGL. This is a continuation of our research into serious design flaws that could affect any browser which implements WebGL, currently Chrome andFirefox.
A CODE SIGNING BYPASS FOR THE VW POLO A code signing bypass for the VW Polo. Focusing on the infotainment system of the Volkswagen® Polo®, and will reveal how the security checks which prevent modifications to its firmware can be circumvented by an attacker in order to allow privileged execution and unrestricted access to the infotainment system’s internals. CONTEXT INFORMATION SECURITY Penetration Testing, Red Teaming, Cyber Incident Response. Context helps your business to manage cyber risk, and to deter, detect and respond to the most sophisticated cyber-attacks. CONDUCTING ONSITE SECURITY TESTING REMOTELY Blog post updated on 21 April 2020 with information about our additional solution for remote testing using virtual devices. From a cyber-security perspective, it is as important as ever to ensure that your infrastructure and applications are secure. PRODUCT SECURITY ASSESSMENT, IOT PENETRATION TESTING Our product security assessment service is designed to help you ascertain how well a product has been developed from a security perspective and the level to which it might stand up to relevant cyberthreats.
RANSOMWARE - IDENTIFYING PATIENT ZERO This blog post aims to provide IT teams with a guide to combat on-going ransomware infections and highlight the source of an infection where it is not immediately obvious, and has not been flagged by an end user. OPEN BANKING: OPEN FOR BUSINESS Before we begin, let’s define a few acronyms: ASPSP Account Servicing Payment Service Provider (let’s call it a bank); TPP Third Party Provider (e.g. a FinTech startup); PSD2 Revised Payment Services Directive (new rules created by the European Union to foster integrated, safer and open banking); A full glossary is available here.. An Introduction to Open Banking PUSH TO HACK: REVERSE ENGINEERING AN IP CAMERA For our most recent IoT adventure, we've examined an outdoor cloud security camera which like many devices of its generation a) has an associated mobile app b) is quick to setup and c) presents new security threats to your network.ICS SECURITY
WIRELESS PHISHING WITH CAPTIVE PORTALS It is trivial for an attacker to harvest information about a wireless network and to copy the entirety of the access control application andthen use this to
MANUALLY TESTING SSL/TLS WEAKNESSES SSL/TLS flaws are widespread; SSL Pulse estimates that over three-quarters of the SSL/TLS deployments currently in use by the top one million websites are inadequately configured. XSLT SERVER SIDE INJECTION ATTACKS From the examples above it is clear that XSLT vulnerabilities have been around for a long time and, although they are less common than other similar vulnerabilities such as XML Injection, we regularly find them in our security assessments. CONTEXT INFORMATION SECURITY Penetration Testing, Red Teaming, Cyber Incident Response. Context helps your business to manage cyber risk, and to deter, detect and respond to the most sophisticated cyber-attacks. CONDUCTING ONSITE SECURITY TESTING REMOTELY Blog post updated on 21 April 2020 with information about our additional solution for remote testing using virtual devices. From a cyber-security perspective, it is as important as ever to ensure that your infrastructure and applications are secure. PRODUCT SECURITY ASSESSMENT, IOT PENETRATION TESTING Our product security assessment service is designed to help you ascertain how well a product has been developed from a security perspective and the level to which it might stand up to relevant cyberthreats.
RANSOMWARE - IDENTIFYING PATIENT ZERO This blog post aims to provide IT teams with a guide to combat on-going ransomware infections and highlight the source of an infection where it is not immediately obvious, and has not been flagged by an end user. OPEN BANKING: OPEN FOR BUSINESS Before we begin, let’s define a few acronyms: ASPSP Account Servicing Payment Service Provider (let’s call it a bank); TPP Third Party Provider (e.g. a FinTech startup); PSD2 Revised Payment Services Directive (new rules created by the European Union to foster integrated, safer and open banking); A full glossary is available here.. An Introduction to Open Banking PUSH TO HACK: REVERSE ENGINEERING AN IP CAMERA For our most recent IoT adventure, we've examined an outdoor cloud security camera which like many devices of its generation a) has an associated mobile app b) is quick to setup and c) presents new security threats to your network.ICS SECURITY
WIRELESS PHISHING WITH CAPTIVE PORTALS It is trivial for an attacker to harvest information about a wireless network and to copy the entirety of the access control application andthen use this to
MANUALLY TESTING SSL/TLS WEAKNESSES SSL/TLS flaws are widespread; SSL Pulse estimates that over three-quarters of the SSL/TLS deployments currently in use by the top one million websites are inadequately configured. XSLT SERVER SIDE INJECTION ATTACKS From the examples above it is clear that XSLT vulnerabilities have been around for a long time and, although they are less common than other similar vulnerabilities such as XML Injection, we regularly find them in our security assessments. EVENTS | CONTEXT INFORMATION SECURITY Virtual Event, United States. Black Hat USA 2020. Context Consultant Rohan Durve, will present Dynamic Labs - an open source solution for creating lab environments for practising penetration testing tools, techniques and procedures (TTPs). CONDUCTING ONSITE SECURITY TESTING REMOTELY Blog post updated on 21 April 2020 with information about our additional solution for remote testing using virtual devices. From a cyber-security perspective, it is as important as ever to ensure that your infrastructure and applications are secure. CONTACT US | CONTEXT INFORMATION SECURITY Context Information Security works with a Preferred Suppliers List when partnering with recruitment agencies. The selection and briefing of recruitment agencies is always at the instigation of the Company.TESTTRACKER
TestTracker is a workflow management solution which allows organisations to easily procure and track their security assessments from start to finish. It helps to streamline this process so that the teams involved in the process can spend less time performi PENETRATION TESTING SERVICES What is Penetration testing? A penetration test (also known as a pentest) is a security assessment aimed at identifying technical vulnerabilities in IT and communications systems that could leave your organisation open to attack should they be exploited by a potentialthreat actor.
WIRELESS PHISHING WITH CAPTIVE PORTALS It is trivial for an attacker to harvest information about a wireless network and to copy the entirety of the access control application andthen use this to
WHAT IS EFFECTIVE CYBER SECURITY RISK MANAGEMENT Traditional cyber services revolved around providing some basic anti-malware tools to prevent an attacker from gaining access to networks, and then, when things went wrong, dealing with the aftermath of an attack, investigating what happened and how the attackers were able to gain access. HACKING INTO INTERNET CONNECTED LIGHT BULBS WiFi and 802.15.4 6LoWPAN Mesh Network. In the event of the master bulb being turned off or disconnected from the network, one of the remaining bulbs elects to take its position as the master and connects to the WiFi network ready to relay commands to any further remainingbulbs.
A CODE SIGNING BYPASS FOR THE VW POLO Focusing on the infotainment system of the Volkswagen® Polo®, and will reveal how the security checks which prevent modifications to its firmware can be circumvented by an attacker in order to allow privileged execution and unrestricted access to the infotainment system’s internals. SNIFFING HTTPS URLS WITH MALICIOUS PAC FILES If an attacker can get your browser to use a malicious PAC file (for example via a rogue access point or WPAD injection attacks), they can use JavaScript code to monitor the full HTTPS URL of every web requestyour browser makes.
THIS WEBSITE USES COOKIES We use cookies to personalise content and ads, to provide social media features and to analyse our traffic. We also share information about your use of our site with our social media, advertising and analytics partners who may combine it with other information that you’ve provided to them or that they’ve collected from your use of their services. You consent to our cookies if you continue to use ourwebsite.
Use necessary cookies only Allow all cookies Show detailsOK
Use necessary cookies only Allow selection Allow all cookiesNecessary
Preferences
Statistics
Marketing
Show details
Cookie declaration About cookies Necessary (7) Preferences (0) Statistics (7) Marketing (12) Unclassified (5) Necessary cookies help make a website usable by enabling basic functions like page navigation and access to secure areas of the website. The website cannot function properly without these cookies.NAME
PROVIDER
PURPOSE
EXPIRY
TYPE
BIGipServer#
Marketo, INC
Used to distribute traffic to the website on several servers in order to optimise response times.Session
HTTP
__cf_bm
Marketo
Githack
This cookie is used to distinguish between humans and bots. This is beneficial for the website, in order to make valid reports on the useof their website.
1 day
HTTP
__cfduid
www.contextis.com
Used by the content network, Cloudflare, to identify trusted webtraffic.
29 days
HTTP
CookieConsent
Cookiebot
Stores the user's cookie consent state for the current domain1 year
HTTP
exp_csrf_token
www.contextis.com
Ensures visitor browsing-security by preventing cross-site request forgery. This cookie is essential for the security of the website andvisitor.
1 day
HTTP
PHPSESSID
www.contextis.com
Preserves user session state across page requests.Session
HTTP
Preference cookies enable a website to remember information that changes the way the website behaves or looks, like your preferred language or the region that you are in. We do not use cookies of this type. Statistic cookies help website owners to understand how visitors interact with websites by collecting and reporting informationanonymously.
NAME
PROVIDER
PURPOSE
EXPIRY
TYPE
_ga
Google Tag Manager
Registers a unique ID that is used to generate statistical data on how the visitor uses the website.2 years
HTTP
_gat
Google Tag Manager
Used by Google Analytics to throttle request rate1 day
HTTP
_gid
Google Tag Manager
Registers a unique ID that is used to generate statistical data on how the visitor uses the website.1 day
HTTP
exp_last_activity
www.contextis.com
Contains information on what date the user last visited the website. Used to generate statistical data.1 year
HTTP
exp_last_visit
www.contextis.com
Contains information on what date the user last visited the website. Used to generate statistical data.1 year
HTTP
exp_tracker
www.contextis.com
Contains information on what date the user last visited the website. Used to generate statistical data.Session
HTTP
collect
Session
Pixel
Marketing cookies are used to track visitors across websites. The intention is to display ads that are relevant and engaging for the individual user and thereby more valuable for publishers and thirdparty advertisers.
NAME
PROVIDER
PURPOSE
EXPIRY
TYPE
_mkto_trk
www.contextis.com
Contains data on visitor behaviour and website interaction. This is used in context with the email marketing service Marketo.com, which allows the website to target visitors via email.2 years
HTTP
IDE
to the user.
1 year
HTTP
test_cookie
1 day
HTTP
GPS
YouTube
Registers a unique ID on mobile devices to enable tracking based on geographical GPS location.1 day
HTTP
VISITOR_INFO1_LIVE
YouTube
Tries to estimate the users' bandwidth on pages with integratedYouTube videos.
179 days
HTTP
YSC
YouTube
Registers a unique ID to keep statistics of what videos from YouTubethe user has seen.
Session
HTTP
yt-remote-cast-installedYouTube
Stores the user's video player preferences using embedded YouTubevideo
Session
HTML
yt-remote-connected-devicesYouTube
Stores the user's video player preferences using embedded YouTubevideo
Persistent
HTML
yt-remote-device-id
YouTube
Stores the user's video player preferences using embedded YouTubevideo
Persistent
HTML
yt-remote-fast-check-periodYouTube
Stores the user's video player preferences using embedded YouTubevideo
Session
HTML
yt-remote-session-appYouTube
Stores the user's video player preferences using embedded YouTubevideo
Session
HTML
yt-remote-session-nameYouTube
Stores the user's video player preferences using embedded YouTubevideo
Session
HTML
Unclassified cookies are cookies that we are in the process of classifying, together with the providers of individual cookies.NAME
PROVIDER
PURPOSE
EXPIRY
TYPE
RSMKTO1
Marketo
Pending
Session
HTTP
exp_context_languagewww.contextis.com
Pending
1 year
HTTP
exp_stashid
www.contextis.com
Pending
Session
HTTP
oktgid
Oktopost
Pending
1 year
HTTP
oktsid
Oktopost
Pending
Session
HTTP
Cookies are small text files that can be used by websites to make a user's experience more efficient. The law states that we can store cookies on your device if they are strictly necessary for the operation of this site. For all other types of cookies we need your permission. This site uses different types of cookies. Some cookies are placed by third party services that appear on our pages. You can at any time change or withdraw your consent from the Cookie Declaration on our website. Learn more about who we are, how you can contact us and how we process personal data in our Privacy Policy. Cookie declaration last updated on 03/05/2020 by Cookiebot
Toggle navigation
* Services
* Industries
* Events
* Resources
* Blog
* Contact
* Search
* Home
* About
* News
* Careers
*
* Change Language
* GLOBAL
* GERMANY
* USA
*
SUSPECTED SECURITY BREACH? If you are an IRIS customer, contact us 24/7 for immediate support 0800 082 0822 response@contextis.comSEARCH
* Back View All Services * Penetration Testing* Red Teaming
* Cyber Incident Response Services * Product Security Evaluation * Active Directory Attack Resistance * Mobile Application and Device Security * Vulnerability Assessment * Build and Configuration Reviews * Source Code Review Services * Cyber Threat Hunting CERTIFIED CYBER SECURITY CONSULTANCY Whether you have a specific cyber security problem, or just want some general help with improving the security posture of your organisation,we can help.
View All Services
SUSPECTED SECURITY BREACH? If you are an IRIS customer, contact us 24/7 for immediate support 0800 082 0822 response@contextis.com * Back All Industries * Financial services * Legal and professional services* Technology
* Telecommunications * Civil Nuclear and Critical Infrastructure* Public Sector
* Defence, Security & Law Enforcement * Retail, Hospitality & Leisure* Other
COMMITTED TO ENSURING YOUR SECURITY We have worked with a wide range of organisations of different types and sizes, across many different sectors. Find out how we can help your business become more secure.View All Industries
EVENTS
Join us at our upcoming events* Back All Events
*
May 07 2020
SIMULATED ATTACK AND RESPONSE TRAINING In diesem Webinar stellt Context vor, wie unsere Kunden simulierte Angriffs- und Response-Trainingszenarien nutzen, um Prozesse und das eigene technische Team zu trainieren.*
Oct 23 2020
SECURITY BSIDES LONDON 2020 BSides is a community-driven event built for and by information security community members. It creates opportunities for individuals to both present and participate in an intimate atmosphere that encourages collaboration. Be sure to to drop by our stand to have a chat with us, pick up some great swag or attempt to solve our puzzle games!View All Events
SECURI-TAY 2020
Paul Laîné will be talking at the upcoming Securi-Tay conference, taking place on 28th February 2020 at Abertay University. WEBINAR: DEFENDING AGAINST NEW AVIVORE THREAT GROUP This webinar will provide an overview of AVIVORE, outlining the techniques and tactics used and highlight ways that organisations can develop their detection capability and response plans to deal with thethreat.
* Back All Resources* Tools
* White Papers and Ebooks* CVEs & Advisories
* Other downloads
RESOURCES
Download our tools from recent research projects, read our latest white papers or browse the list of vulnerabilities we have discovered and disclosed to manufacturers.View All Resources
BLOGS
Read our security findings and insights* Back All Blogs
* Behind the Screen: An insight into Context’s testing data * Don’t compromise your security during the COVID-19 crisis * Your car is just the casing for a complex computer * Conducting Onsite Security Testing - Remotely?View All Blogs
A VIEW FROM THE SOC; MAINTAINING DETECTION CAPABILITIES DURINGCHALLENGING TIMES
The exponential growth in working from home as a result of COVID-19 has presented a number of challenges for SOC teams. OPEN BANKING: THE CHALLENGES In this second blog in our Open Banking series, we delve deeper into the challenges Open Banking brings.Back All Locations
CONTACT
Our headquarters are in the UK. Head Office : LondonUnited Kingdom
T: +44 (0)20 7537 7515 info@contextis.com ContactUs
OFFICES
Our international office locations.Basingstoke
United Kingdom T: +44 (0)20 7537 7515Bad Nauheim
Germany T: +49 (0)6032 949 7917Cheltenham
United Kingdom T: +44 (0)20 7537 7515Essen Germany
T: +49 (0)201 87778550Melbourne
Australia T: +61 1300 565 352Sydney
Australia T: +61 1300 565 352Cambridge
United Kingdom T: +44 (0)20 7537 7515New York
United States T: +1 917 880 3130Edinburgh
United Kingdom T: +44 (0)131 285 1505Brisbane
Australia T: +61 1300 565 352 SUSPECTED SECURITY BREACH? If you are an IRIS customer, contact us 24/7 for immediate support 0800 082 0822 response@contextis.com SUSPECTED SECURITY BREACH? If you are an IRIS customer, contact us 24/7 for immediate support 0800 082 0822 response@contextis.com LEADING CYBER SECURITY CONSULTANCY We are a certified cyber security consultancyhelping
businesses to manage their cyber risk, and detect and respond to sophisticated cyber-attacks. We provide specialist cyber security services including penetrationtesting
and red teaming
,
cyber incident responseand threat hunting
,
and product security testing.
View Our Services
SUSPECTED SECURITY BREACH? If you are an IRIS customer, contact us 24/7 for immediate support response@contextis.com 0800 082 0822 What is IRIS?We are recruiting
Blog
28 Apr 2020
A VIEW FROM THE SOC; MAINTAINING DETECTION CAPABILITIES DURINGCHALLENGING TIMES
The exponential growth in working from home as a result of COVID-19 has pre...Read Article
NEW BLOGS
Read our security findings and insights * Open Banking: The Challenges This post is the second in a series of articles... * Behind the Screen: An insight into Context’s testing data One of our Context Account Managers, Alexander Roxon, took a...Read The Blog
09 Apr 2020
News
CONNECTED CARS ARE JUST COMPUTERS ON WHEELS, WARNS CONTEXT09 Apr 2020
Read More
01 Apr 2020
News
CONTEXT APPOINTED AS CERTIFYING BODY FOR CYBER ESSENTIALS01 Apr 2020
Read More
careers
CAREERS AT CONTEXT
Work with some of the best in the industry, in a collaborative and supportive environment....Read More
Events
SIMULATED ATTACK AND RESPONSE TRAININGMay 2020 07
Event Information
INDUSTRY EVENTS
Join us at upcoming events and conferencesOct 23 2020
SECURITY BSIDES LONDON 2020 London, United KingdomDec 01 2020
ITS.CONNECT
Bochum, Germany
View All Events
SIGN UP FOR OUR
NEWS & RESEARCH
PAGES
* Services
* Industries
* Resources
* Contact
RESEARCH & TOOLS
* Blog
* Tools
* White Papers and EbooksCOMPANY
* Events
* Recent News
SOCIAL MEDIA
* Blog RSS Feed
* News RSS Feed
CONTACT
Head Office : London United Kingdom T: +44 (0)20 7537 7515 General Enquiries : info@contextis.com Recruitment : recruitment@contextis.com Contact UsOUR OFFICES
Basingstoke United Kingdom T: +44 (0)20 7537 7515 Bad Nauheim Germany T: +49 (0)6032 949 7917 Cheltenham United Kingdom T: +44 (0)20 7537 7515 Essen Germany T: +49 (0)201 87778550 Melbourne Australia T: +61 1300 565 352 Sydney Australia T: +61 1300 565 352 Cambridge United Kingdom T: +44 (0)20 7537 7515 New York United States T: +1 917 880 3130 Edinburgh United Kingdom T: +44 (0)131 285 1505 Brisbane Australia T: +61 1300 565 352 � 2020 Context Information Security Cookies and PrivacyTerms & Conditions
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0