Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://gongwer.com
Are you over 18 and want to see adult content?

A complete backup of https://fcsamerica.com
Are you over 18 and want to see adult content?

A complete backup of https://umarkets.website
Are you over 18 and want to see adult content?
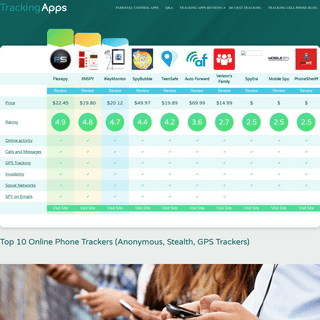
A complete backup of https://trackingapps.org
Are you over 18 and want to see adult content?
A complete backup of https://cryptominingfarm.pw
Are you over 18 and want to see adult content?
A complete backup of https://xpi.com.br
Are you over 18 and want to see adult content?
A complete backup of https://largo-la.com
Are you over 18 and want to see adult content?

A complete backup of https://strefalamp.pl
Are you over 18 and want to see adult content?

A complete backup of https://rabatol.pl
Are you over 18 and want to see adult content?

A complete backup of https://fightsaga.com
Are you over 18 and want to see adult content?

A complete backup of https://alfredobernardini.com
Are you over 18 and want to see adult content?

A complete backup of https://sureoak.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of faceofmalawi.com
Are you over 18 and want to see adult content?
A complete backup of arrendadoraeconomica.com
Are you over 18 and want to see adult content?
A complete backup of diablo-technologies.com
Are you over 18 and want to see adult content?

A complete backup of wattwaybycolas.com
Are you over 18 and want to see adult content?

A complete backup of huntingandfishing.co.nz
Are you over 18 and want to see adult content?
A complete backup of charlestonforge.com
Are you over 18 and want to see adult content?

A complete backup of thenationaldc.com
Are you over 18 and want to see adult content?
Text
HACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes. 11 PROTOCOLS YOU’VE GOT TO KNOW SSH and FTP are often mentioned in the same breath. Invented in 1995 Secure Shell’s definition is “a cryptographic network protocol for secure data communication”. SSH allows for remote command-line login and remote execution. It has many of the functions of FTP but is more secure. The latest versions are referred to as SSH-1 and SSH-2.IS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools then TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform used WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
SN1PER TUTORIAL BASICS Sn1per Recommended Hacking Tutorial. Sn1per is one of the most exciting hacking software to come out in recent years. In fact, it’s been out for a while now – but in any event, if you’re a serious pentester/ethical hacker, then I’d strongly suggest that you learn how to use this hacking tool.HACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes. 11 PROTOCOLS YOU’VE GOT TO KNOW SSH and FTP are often mentioned in the same breath. Invented in 1995 Secure Shell’s definition is “a cryptographic network protocol for secure data communication”. SSH allows for remote command-line login and remote execution. It has many of the functions of FTP but is more secure. The latest versions are referred to as SSH-1 and SSH-2.IS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools then TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform used WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
SN1PER TUTORIAL BASICS Sn1per Recommended Hacking Tutorial. Sn1per is one of the most exciting hacking software to come out in recent years. In fact, it’s been out for a while now – but in any event, if you’re a serious pentester/ethical hacker, then I’d strongly suggest that you learn how to use this hacking tool.HACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes. BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the BEST KEYLOGGERS FOR 2020! Keylogger Mini USB 3.0. This one definitely looks the best. If you don’t want to get messy with configuring the device remotely, i.e. with hidden WiFi networks, Bluetooth, etc, then this is for you! This would suit the Ethical Hacker that is able to have physical access to the targets machine at will. The device works on Windows 7,8 and 10 SLIDER CALCULATOR TO SHOW BENEFITS Let potential customers validate your service themselves. There is nothing better than a prospect self-validating and self-convincing themselves that your product or service will genuinely HIDE RETARGETING COOKIES FOR 45 SECONDS Stop retargeting people who bounced immediately from your site. Use a little bit of javascript to hide retargeting cookies for 45 seconds to ensure you’re only retargeting users MY RECOMMENDED SEO & GROWTH HACKER TOOLS FOR 2021 Rating: 4.5 out of 5. A really powerful tool for automation; Decent community and a lot of folks on Legiit, Fiverr and UpWork can help you out if you get stuck. It’s FREE! This really is an incredible tool. If you spend anytime doing any form of SEO, Growth Marketing or HANDWRITTEN LETTER SAYING THANKS As ever, it’s the human touch and the details that often make all the difference. It doesn’t matter what you sell or do when you acquire a new customer, send them a handwritten note, a postcard, i.e. something informal, relaxed, and personal. HOW TO GET SOMEONE’S IP ADDRESS AND TRACE THEIR LOCATION Step 1: Upload any old image or file and get the URL. You could upload a file to Dropbox, Google drive, or even your FTP server. Next, just copy and paste that URL. Nice and simple. Step 2: We head over to a service called IPLogger via this site. Click on the “URL and Image Shortner” option, and go ahead and paste your link in there. FIREWALL SOFTWARE & TOOLS Netfilter. Netfilter is a classic Firewall hacking tool used by many within the cybersecurity industry. The tool (framework) essentially filters packets inside Linux 2.4.x and later kernels. Netfilter is a series of hooks inside the Linux kernel that allows kernel modulesHACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes. 11 PROTOCOLS YOU’VE GOT TO KNOW SSH and FTP are often mentioned in the same breath. Invented in 1995 Secure Shell’s definition is “a cryptographic network protocol for secure data communication”. SSH allows for remote command-line login and remote execution. It has many of the functions of FTP but is more secure. The latest versions are referred to as SSH-1 and SSH-2.IS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools then TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform used WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
SN1PER TUTORIAL BASICS Sn1per Recommended Hacking Tutorial. Sn1per is one of the most exciting hacking software to come out in recent years. In fact, it’s been out for a while now – but in any event, if you’re a serious pentester/ethical hacker, then I’d strongly suggest that you learn how to use this hacking tool.HACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes. 11 PROTOCOLS YOU’VE GOT TO KNOW SSH and FTP are often mentioned in the same breath. Invented in 1995 Secure Shell’s definition is “a cryptographic network protocol for secure data communication”. SSH allows for remote command-line login and remote execution. It has many of the functions of FTP but is more secure. The latest versions are referred to as SSH-1 and SSH-2.IS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools then TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform used WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
SN1PER TUTORIAL BASICS Sn1per Recommended Hacking Tutorial. Sn1per is one of the most exciting hacking software to come out in recent years. In fact, it’s been out for a while now – but in any event, if you’re a serious pentester/ethical hacker, then I’d strongly suggest that you learn how to use this hacking tool.HACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes. BEST KEYLOGGERS FOR 2020! Keylogger Mini USB 3.0. This one definitely looks the best. If you don’t want to get messy with configuring the device remotely, i.e. with hidden WiFi networks, Bluetooth, etc, then this is for you! This would suit the Ethical Hacker that is able to have physical access to the targets machine at will. The device works on Windows 7,8 and 10 SLIDER CALCULATOR TO SHOW BENEFITS Let potential customers validate your service themselves. There is nothing better than a prospect self-validating and self-convincing themselves that your product or service will genuinely HIDE RETARGETING COOKIES FOR 45 SECONDS Stop retargeting people who bounced immediately from your site. Use a little bit of javascript to hide retargeting cookies for 45 seconds to ensure you’re only retargeting users PORT SCANNING HACKING TOOLS Port Scanner Tools For 2021. Port Scanning is one of the initial steps that a Penetration Tester (‘Ethical Hacker’) will take to determine how secure a network or web application is from black hat hackers. Port Scanning Software, of which there is plenty, is a ‘must-learn’ if you are serious about becoming a CybersecurityProfessional.
HANDWRITTEN LETTER SAYING THANKS As ever, it’s the human touch and the details that often make all the difference. It doesn’t matter what you sell or do when you acquire a new customer, send them a handwritten note, a postcard, i.e. something informal, relaxed, and personal. HOW TO GET SOMEONE’S IP ADDRESS AND TRACE THEIR LOCATION Step 1: Upload any old image or file and get the URL. You could upload a file to Dropbox, Google drive, or even your FTP server. Next, just copy and paste that URL. Nice and simple. Step 2: We head over to a service called IPLogger via this site. Click on the “URL and Image Shortner” option, and go ahead and paste your link in there. FIREWALL SOFTWARE & TOOLS Netfilter. Netfilter is a classic Firewall hacking tool used by many within the cybersecurity industry. The tool (framework) essentially filters packets inside Linux 2.4.x and later kernels. Netfilter is a series of hooks inside the Linux kernel that allows kernel modulesHACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools thenIS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. METASPLOIT FOR BEGINNERS Metasploit For Beginners: A Concise Introduction. Having recently blogged about the world’s most scary pentest tools we thought we should write something about the importance of learning the Metasploit Framework for penetration testers.. Metasploit is an incredibly good framework and if your new to the world of penetration testing then we’d certainly recommend this tool. WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes.SHODAN EXPLAINED
SHODAN will tell the hacker (be they white or black hat) things like banner information, HTTP, SSH, FTP, and SNMP services. The most basic SHODAN search will render results by country, network, operating system (s), and port (s). If you wanted to execute a more specific search you’d use a string like this: port:121 country:US hyper-v.Port
TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform usedHACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools thenIS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. METASPLOIT FOR BEGINNERS Metasploit For Beginners: A Concise Introduction. Having recently blogged about the world’s most scary pentest tools we thought we should write something about the importance of learning the Metasploit Framework for penetration testers.. Metasploit is an incredibly good framework and if your new to the world of penetration testing then we’d certainly recommend this tool. WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes.SHODAN EXPLAINED
SHODAN will tell the hacker (be they white or black hat) things like banner information, HTTP, SSH, FTP, and SNMP services. The most basic SHODAN search will render results by country, network, operating system (s), and port (s). If you wanted to execute a more specific search you’d use a string like this: port:121 country:US hyper-v.Port
TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform usedHACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes. BEST KEYLOGGERS FOR 2020! Keylogger Mini USB 3.0. This one definitely looks the best. If you don’t want to get messy with configuring the device remotely, i.e. with hidden WiFi networks, Bluetooth, etc, then this is for you! This would suit the Ethical Hacker that is able to have physical access to the targets machine at will. The device works on Windows 7,8 and 10 METASPLOIT FOR BEGINNERS Metasploit For Beginners: A Concise Introduction. Having recently blogged about the world’s most scary pentest tools we thought we should write something about the importance of learning the Metasploit Framework for penetration testers.. Metasploit is an incredibly good framework and if your new to the world of penetration testing then we’d certainly recommend this tool. PORT SCANNING HACKING TOOLS Port Scanner Tools For 2021. Port Scanning is one of the initial steps that a Penetration Tester (‘Ethical Hacker’) will take to determine how secure a network or web application is from black hat hackers. Port Scanning Software, of which there is plenty, is a ‘must-learn’ if you are serious about becoming a CybersecurityProfessional.
HOW TO GET SOMEONE’S IP ADDRESS AND TRACE THEIR LOCATION Step 1: Upload any old image or file and get the URL. You could upload a file to Dropbox, Google drive, or even your FTP server. Next, just copy and paste that URL. Nice and simple. Step 2: We head over to a service called IPLogger via this site. Click on the “URL and Image Shortner” option, and go ahead and paste your link in there. WIFI / WIRELESS HACKING TOOLS Wifiphisher. Wifiphisher is a WiFi hacking tool that can execute speedy automated phishing attacks against Wireless/WiFi networks with the intention of discovering user and password credentials The difference with this wireless tool (compared with the others) is that it launches a Social Engineering attack which is a completely different attack vector to take when attempting to breach WiFi CHROME VS VIVALDI VS BRAVE VS SPHERE Growth (Computer) Hacking Browser Purposes. I do two things to earn a living: Growth Hacking (in the “Automation” and White-Grey-Black-Hat sense of the term); Penetration Testing and WordPress Hacking; Both of these disciplines require a ton of different hacking software and growth hacking tools. Aside from the multitude of tools out there – one “tool” remains utterlyindispensable
5 MAJOR TYPES OF DOS ATTACK A SYN flood is a type of DOS attack in which an attacker sends a series of SYN requests to a target’s system in an attempt to use vast amounts of server resources to make the system unresponsive to legitimate traffic. 2. Teardrop Attacks. A teardrop attack involves the hacker sending broken and disorganized IP fragments withoverlapping, over
WEB VULNERABILITY SCANNING TOOLS AND SOFTWARE Acunetix WVS. Acunetix is a web vulnerability scanner that automatically checks web applications. This tool is particularly good at scanning for vulnerabilities such as cross-site scripting, SQL injections, weak password strength on authentication pages and arbitrary file creation.HACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools thenIS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. METASPLOIT FOR BEGINNERS Metasploit For Beginners: A Concise Introduction. Having recently blogged about the world’s most scary pentest tools we thought we should write something about the importance of learning the Metasploit Framework for penetration testers.. Metasploit is an incredibly good framework and if your new to the world of penetration testing then we’d certainly recommend this tool. WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes.SHODAN EXPLAINED
SHODAN will tell the hacker (be they white or black hat) things like banner information, HTTP, SSH, FTP, and SNMP services. The most basic SHODAN search will render results by country, network, operating system (s), and port (s). If you wanted to execute a more specific search you’d use a string like this: port:121 country:US hyper-v.Port
TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform usedHACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools thenIS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. METASPLOIT FOR BEGINNERS Metasploit For Beginners: A Concise Introduction. Having recently blogged about the world’s most scary pentest tools we thought we should write something about the importance of learning the Metasploit Framework for penetration testers.. Metasploit is an incredibly good framework and if your new to the world of penetration testing then we’d certainly recommend this tool. WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes.SHODAN EXPLAINED
SHODAN will tell the hacker (be they white or black hat) things like banner information, HTTP, SSH, FTP, and SNMP services. The most basic SHODAN search will render results by country, network, operating system (s), and port (s). If you wanted to execute a more specific search you’d use a string like this: port:121 country:US hyper-v.Port
TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform usedHACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes.IS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. BEST KEYLOGGERS FOR 2020! Keylogger Mini USB 3.0. This one definitely looks the best. If you don’t want to get messy with configuring the device remotely, i.e. with hidden WiFi networks, Bluetooth, etc, then this is for you! This would suit the Ethical Hacker that is able to have physical access to the targets machine at will. The device works on Windows 7,8 and 10 METASPLOIT FOR BEGINNERS Metasploit For Beginners: A Concise Introduction. Having recently blogged about the world’s most scary pentest tools we thought we should write something about the importance of learning the Metasploit Framework for penetration testers.. Metasploit is an incredibly good framework and if your new to the world of penetration testing then we’d certainly recommend this tool.HACKING TOOLS
Netfilter is a classic Firewall hacking tool used by many within the cybersecurity industry. The tool (framework) essentially filters packets inside Linux 2.4.x and later kernels. Netfilter is a series of hooks inside the Linux kernel that allows kernel modules to perform callback functions within the network stack. PASSWORD HACKING TOOLS & SOFTWARE Aircrack-ng is a network hacking tool that consists of a packet sniffer, detector, WPA/WPA2-PSK cracker, WEP and an analysis tool for 802.11 wireless LANs. This tool works with a wireless network interface controller whose driver supports raw monitoring mode and CHROME VS VIVALDI VS BRAVE VS SPHERE Growth (Computer) Hacking Browser Purposes. I do two things to earn a living: Growth Hacking (in the “Automation” and White-Grey-Black-Hat sense of the term); Penetration Testing and WordPress Hacking; Both of these disciplines require a ton of different hacking software and growth hacking tools. Aside from the multitude of tools out there – one “tool” remains utterlyindispensable
5 MAJOR TYPES OF DOS ATTACK A SYN flood is a type of DOS attack in which an attacker sends a series of SYN requests to a target’s system in an attempt to use vast amounts of server resources to make the system unresponsive to legitimate traffic. 2. Teardrop Attacks. A teardrop attack involves the hacker sending broken and disorganized IP fragments withoverlapping, over
WIFI / WIRELESS HACKING TOOLS Wifiphisher. Wifiphisher is a WiFi hacking tool that can execute speedy automated phishing attacks against Wireless/WiFi networks with the intention of discovering user and password credentials The difference with this wireless tool (compared with the others) is that it launches a Social Engineering attack which is a completely different attack vector to take when attempting to breach WiFiHACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes. 11 PROTOCOLS YOU’VE GOT TO KNOW SSH and FTP are often mentioned in the same breath. Invented in 1995 Secure Shell’s definition is “a cryptographic network protocol for secure data communication”. SSH allows for remote command-line login and remote execution. It has many of the functions of FTP but is more secure. The latest versions are referred to as SSH-1 and SSH-2.IS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools then TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform used WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
SN1PER TUTORIAL BASICS Sn1per Recommended Hacking Tutorial. Sn1per is one of the most exciting hacking software to come out in recent years. In fact, it’s been out for a while now – but in any event, if you’re a serious pentester/ethical hacker, then I’d strongly suggest that you learn how to use this hacking tool.HACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the HOW TO START A CAREER IN CYBERSECURITY IN 2021 At the start of your career, I would suggest that you spend time understanding the Networking, OS, Basic Programming, Tools, Cyber Law, IT/ Evidence Act, Hacking modules and more for additional skills. Try to use all opensource, shareware’s tools and benchmark as per efficiency and learning purposes. 11 PROTOCOLS YOU’VE GOT TO KNOW SSH and FTP are often mentioned in the same breath. Invented in 1995 Secure Shell’s definition is “a cryptographic network protocol for secure data communication”. SSH allows for remote command-line login and remote execution. It has many of the functions of FTP but is more secure. The latest versions are referred to as SSH-1 and SSH-2.IS CEH DIFFICULT?
The main point is this: YES – it is 100% achievable. TL;DR #1. CEH is multiple choice, so you need to master multiple-choice answering as well. TL;DR #2. The feedback is (so far) that to pass CEH you’re best to use as much courseware as possible as provided by EC Council. WHAT IS THC HYDRA? BASIC OVERVIEW What Is THC Hydra? Basic Overview. Hydra or THC Hydra is a popular and respected network logon cracker (password cracking tool) that can support many different services. Update! I interviewed the developer of THC Hydra! If you’d like to see other tools then TABLE OF CONTENTS FOR SEO LONG FORM Facebook is the largest social network in the world with approximately over 2 billion monthly active users. While this may come as a surprise to some people, the biggest social network platform used WIFI HACKING HARDWARE Alfa AWUS036NH RT3070L WIFI Adapter Complete Kit. See Prices on Amazon. If the WiFi Pineapple is the absolute classic “Rogue Access Point” hacking hardware tool, then we can consider the Alfa AWUS036NH is the quintessential “old-school” WiFi hacking tool that has been around for years! The Alfa AWUS036NH works superbly wellwith the
SN1PER TUTORIAL BASICS Sn1per Recommended Hacking Tutorial. Sn1per is one of the most exciting hacking software to come out in recent years. In fact, it’s been out for a while now – but in any event, if you’re a serious pentester/ethical hacker, then I’d strongly suggest that you learn how to use this hacking tool.HACKING TOOLS
Crunchbase For Funded Companies Contact CEO. The "official" purpose of Crunchbase, is that it is a platform for finding business information about private and public companies. The growth hackers use of Crunchbase is that it tells you who View Post. link to Power Of Old School Set Up Group.ABOUT THIS SITE
About This Site. I’ve been actively involved in two areas for the last fifteen years: Cybersecurity, specifically Penetration Testing, and Growth Marketing. I built this site as a resource to share my experience with particular reference to the tools that I’ve used along the journey. The “ key ” takeaway I’d love for you to takefrom
USE EMOJIS. ALWAYS AND OFTEN OK, this is probably one of the more basic five-minute growth hacks I explain but it is worth including nonetheless because it works. The use of Emojis in subject lines will increase your open rates and reply rates when placed within the text. BEST HACKER TOOLS OF 2021! If you had to learn one tool to use in 2021 we’d definitely push you to learn Metasploit. The Metasploit Project is a hugely popular pentesting or hacking framework. Metasploit, along with Nmap (see below) and Wireshark (see below) and probably the BEST KEYLOGGERS FOR 2020! Keylogger Mini USB 3.0. This one definitely looks the best. If you don’t want to get messy with configuring the device remotely, i.e. with hidden WiFi networks, Bluetooth, etc, then this is for you! This would suit the Ethical Hacker that is able to have physical access to the targets machine at will. The device works on Windows 7,8 and 10 METASPLOIT FOR BEGINNERS Metasploit For Beginners: A Concise Introduction. Having recently blogged about the world’s most scary pentest tools we thought we should write something about the importance of learning the Metasploit Framework for penetration testers.. Metasploit is an incredibly good framework and if your new to the world of penetration testing then we’d certainly recommend this tool. ARCHIVE POSTS (BLOG) An Overview Of This Interview Roundup The point of this resource is to discover and establish just how difficult the OSCP, and we ask those that have passed it. IS PASSING CISSP DIFFICULT? 70% of respondents so far answered that “Yes”, CISSP is a ‘difficult’ Certification. Of course, the real answer to this question is: ‘it depends.’. Whether or not you find CISSP hard to pass the first time depends greatly on your experience and ability to learn. CISSP is a senior IT Security Cert and it does require in-depthknowledge.
MY RECOMMENDED SEO & GROWTH HACKER TOOLS FOR 2021 Rating: 4.5 out of 5. A really powerful tool for automation; Decent community and a lot of folks on Legiit, Fiverr and UpWork can help you out if you get stuck. It’s FREE! This really is an incredible tool. If you spend anytime doing any form of SEO, Growth Marketing or HANDWRITTEN LETTER SAYING THANKS As ever, it’s the human touch and the details that often make all the difference. It doesn’t matter what you sell or do when you acquire a new customer, send them a handwritten note, a postcard, i.e. something informal, relaxed, and personal.HACKING TOOLS
Site Dedicated To Intrepid Explorers . I'm Henry, aka "HMFIC" ~ the guy behind this site. In the last few years, I've become obsessed with digital marketing processes and automation, especially within SEO. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! WHAT IS THC HYDRA? BASIC OVERVIEW How does Hydra work? Hydra is a brute force password cracking tool. In information security (IT security), password cracking is the methodology of guessing passwords from databases that have been stored in or are in transit within a computer system or network. BEST HACKER TOOLS OF 2021! WTF Is This Post? I list my favorite Hacking Tools and Hacker Software of 2021 that I extensively use. Why? I’ve been updating this resource since 2012, yep, that long, and I thought it would be a shame to break with this tradition. The list originally started by a vote and this list haven’t really much changed since then. HOW TO START A CAREER IN CYBERSECURITY IN 2021 Three years ago, I play counter-strike a lot, and some players do hacker things on it, so I became really curious about it, and Googled “How to hack counter strike”, then after several months, I want to learn how to hack a Facebook account, and at that point, I discovered that Facebook has a bug bounty program, and research about “what is bug bounty and all” and now I am here. 11 PROTOCOLS YOU’VE GOT TO KNOW OK, so let’s start by asking: What exactly are Protocols? Protocols are rules. Think of protocols as ‘accepted standards’ – which weall agree to.
TABLE OF CONTENTS FOR SEO LONG FORM Google loves well-written, informative and helpful content and this is one of my “must-do” and “easy to understand” hacks that will absolutely help with yourSHODAN EXPLAINED
What Is SHODAN, How Does It Work? Commonly referred to as the world’s most scary search engine – SHODAN is here to stay and is getting better and better at what it is designed to do.IS CEH DIFFICULT?
There was a period when CEH exam questions appeared on the Internet and other sources. These question banks were easy to obtain and some people swot up and pass the exam by this method and don’t even prepare with the course materials. 5 MAJOR TYPES OF DOS ATTACKHACKING TOOLS
Site Dedicated To Intrepid Explorers . I'm Henry, aka "HMFIC" ~ the guy behind this site. In the last few years, I've become obsessed with digital marketing processes and automation, especially within SEO. HOW TO HACK WORDPRESS IN 2021 Being Able To Hack WordPress Makes You A Better Developer. There’s no doubt. WordPress is a massive, in fact mega, target for hackers. The key thing to understand about anything to do with hacking is this: the typical hack goes unnoticed for 174 days! WHAT IS THC HYDRA? BASIC OVERVIEW How does Hydra work? Hydra is a brute force password cracking tool. In information security (IT security), password cracking is the methodology of guessing passwords from databases that have been stored in or are in transit within a computer system or network. BEST HACKER TOOLS OF 2021! WTF Is This Post? I list my favorite Hacking Tools and Hacker Software of 2021 that I extensively use. Why? I’ve been updating this resource since 2012, yep, that long, and I thought it would be a shame to break with this tradition. The list originally started by a vote and this list haven’t really much changed since then. HOW TO START A CAREER IN CYBERSECURITY IN 2021 Three years ago, I play counter-strike a lot, and some players do hacker things on it, so I became really curious about it, and Googled “How to hack counter strike”, then after several months, I want to learn how to hack a Facebook account, and at that point, I discovered that Facebook has a bug bounty program, and research about “what is bug bounty and all” and now I am here. 11 PROTOCOLS YOU’VE GOT TO KNOW OK, so let’s start by asking: What exactly are Protocols? Protocols are rules. Think of protocols as ‘accepted standards’ – which weall agree to.
TABLE OF CONTENTS FOR SEO LONG FORM Google loves well-written, informative and helpful content and this is one of my “must-do” and “easy to understand” hacks that will absolutely help with yourSHODAN EXPLAINED
What Is SHODAN, How Does It Work? Commonly referred to as the world’s most scary search engine – SHODAN is here to stay and is getting better and better at what it is designed to do.IS CEH DIFFICULT?
There was a period when CEH exam questions appeared on the Internet and other sources. These question banks were easy to obtain and some people swot up and pass the exam by this method and don’t even prepare with the course materials. 5 MAJOR TYPES OF DOS ATTACKHACKING TOOLS
Site Dedicated To Intrepid Explorers . I'm Henry, aka "HMFIC" ~ the guy behind this site. In the last few years, I've become obsessed with digital marketing processes and automation, especially within SEO. HOW TO START A CAREER IN CYBERSECURITY IN 2021 Three years ago, I play counter-strike a lot, and some players do hacker things on it, so I became really curious about it, and Googled “How to hack counter strike”, then after several months, I want to learn how to hack a Facebook account, and at that point, I discovered that Facebook has a bug bounty program, and research about “what is bug bounty and all” and now I am here. DEBUGGING TOOLS & SOFTWARE (FIND BUGS) GDB: The GNU Project Debugger. GDB, or, the GNU Project debugger, is a cybersecurity pentesting/ hacker tool that allows the user to audit and discover what is being executed within a web app or program.. GDB is especially helpful for developers or programmers that are keen to understand why their application or program is crashing or whether their code has any vulnerabilities. HACKER SOFTWARE DEVELOPERS My favorite hacking tool is SN1PER. I interviewed the developer at the end of last year, 2019, and listed as being one of the Best Hacker Tools Of 2020.. Other noteworthy mentions in this ever-growing list include SIPViscious, WPScan for WordPress Hacking, CowPAtty for WiFi Hacking and theHarvester for Email Scraping and Reconnaissance.. All these tools are used daily by Penetration Testers METASPLOIT FOR BEGINNERS Metasploit For Beginners: A Concise Introduction. Having recently blogged about the world’s most scary pentest tools we thought we should write something about the importance of learning the Metasploit Framework for penetration testers.. Metasploit is an incredibly good framework and if your new to the world of penetration testing then we’d certainly recommend this tool. WIFI HACKING BASIC ATTACKS Cracking WiFi networks seems to be a rite of passage. In fact, our most popular directory dedicated to hack tools is the WiFi Hacking list here.. Currently, as of 2021, we have the following tools listed in the Wireless Hacking section: PORT SCANNING HACKING TOOLS Netscan Tools. NetScanTools is really a collection of different pentesting tools that a system admin would find particularly useful. The range of network toolkits is designed for those who work in network engineering, network security, network administration, network WIFI / WIRELESS HACKING TOOLS Wifiphisher. Wifiphisher is a WiFi hacking tool that can execute speedy automated phishing attacks against Wireless/WiFi networks with the intention of discovering user and password credentials The difference with this wireless tool (compared with the others) is that it launches a Social Engineering attack which is a completely different attack vector to take when attempting to breach WiFi PACKET SNIFFERS & CRAFTING TOOLS Wireshark. Wireshark is an absolute classic and probably the best-known network analyzer and password cracking tool. Of course, the password must be sent via an encrypted format for Wireshark. This tool is a network packet analyzer and this kind of tool will try to capture network packets used for analysis, network troubleshooting, education, software, and communications protocol development THAT FEELING YOU GET HACKING WIFI FOR FIRST TIME Why Do Hackers Do It? Good question and one that is quite difficult to answer. Sure, there are reasons like hacktivism and personal vendettas, heck there’s even state-sponsored hacking which is on steroids at the moment – but I’m referring to the individual, i.e. the “self-taught” n00b who is interested in IT Security and wants to get into the industry: what is it that makes themSkip to content
MENU
Search Search for:
* Hacker Tools
* Growth Marketing Tools * 20 Second Overview A SITE DEDICATED TO GROWTH HACKING TOOLS AND CYBER CRACKS HOW TO FIND ANYONE'S IP ADDRESS & LOCATIONLearn How
MY EXPERIENCE OF SEO BACK IN 2002! MY RECOMMENDED WORDPRESS PLUGINS FOR 2021 POWERFUL PASSWORD CRACKING TOOLS BEST HACKING TOOLS OF 2020! RECENT GROWTH AND HACKING ARTICLES link to Using Kali Linux For SEO Using Kali Linux For SEO The two things are extremely closely related in my mind. Growth Hacking (which also includes SEO for me) and "Hacking" in an IT/Computer sense (like a Penetration Tester or Ethical Hacker") havethe...
View Post
link to What’s Hong Kong Like? What’s Hong Kong Like? I live in Hong Kong where I manage a growth hacking and SEO agency. I've been here for five years and I thought it would be helpful to post this resource for those that are thinking of coming out...View Post
link to How To Get Someone’s IP Address And Trace Their Location How To Get Someone’s IP Address And Trace Their Location This is a clever little hack to discover someone's IP address and location. It requires some free tools that I list below in this post. Why Would You Want To Know Someone's IP? OK...I agree, it...View Post
link to How To Improve Crappy Facebook Leads For eCommerce How To Improve Crappy Facebook Leads For eCommerce Has anyone else noticed recently that Facebook leads are getting worse and worse, or at least they are for me? In this post, I take a look at some options to improve your Facebook advertising...View Post
link to 6 Domain Drop-Catching Platforms You Can Use 6 Domain Drop-Catching Platforms You Can Use Deciding on which domain drop-catching platform to use is a challenge and of vital importance relating to which one you should invest time in using. Hopefully, I've helped you out by listing 6...View Post
link to 13 Ways To Increase A Site’s Position on Google (CheckList) 13 Ways To Increase A Site’s Position on Google (CheckList) In this SEO post, I'm going to highlight a quick "Best Ways To Increase A Site's Ranking" in 13 steps that have helped me, which I hope helps you in return. I've been in the game for a long time now...View Post
Page 1 Page 2 Page 3 … Page 7NEXT »
ABOUT THIS SITE
I'm Henry, the guy behind this site. I live in Hong Kong and I'm a "Growth Marketer" and Cybersecurity Professional, working as a freelancer for the last decade. I wrote a post on what its like to live in Hong Kongif you're
interested.
In the last few years, I've become obsessed with digital marketing processes. Since 2013 "Concise Courses" has grown into a valuable resource for many folks starting out their careers in Cybersecurity and Growth Marketing with thousands of site visitors each month. This site lists a bunch of information on Cybersecurity "Ethical Hacking" Tips 'n Tricks. Please be responsible and remember that doing anything without permission is a crime! And - importantly, in this difficult time - stay safe! GROWTH HACKING & CYBER CRACKING In my mind, the two things are very closely related. The best Growth Hackers I have ever met (and also SEO professionals) were programmers and had a "hacking mindset". Indeed, I work alongside a bunch of Growth Hackers and SEO experts that use Kali Linux and even hackingtools when
they execute their tasks. If you're interested in either skill then thanks for dropping by and I hope you learn something.SEE POST
* Privacy Policy
* About This Site
* Sitemap
� 2020 Concise AC | UK Registered CompanyDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0