Are you over 18 and want to see adult content?
More Annotations
A complete backup of capogirogelato.com
Are you over 18 and want to see adult content?

A complete backup of easterngraphics.com
Are you over 18 and want to see adult content?
A complete backup of touristsherpa.com
Are you over 18 and want to see adult content?
Favourite Annotations
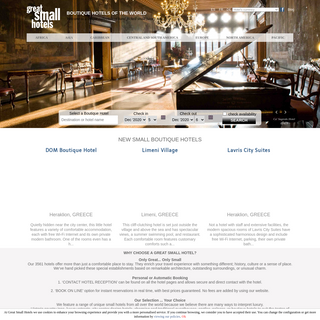
A complete backup of greatsmallhotels.com
Are you over 18 and want to see adult content?
A complete backup of connect2builder.com
Are you over 18 and want to see adult content?

A complete backup of vesuvioinrete.it
Are you over 18 and want to see adult content?
Text
THE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Introduction Wi-Fi has come a long way over the years. From devices to access points (APs) to antennas to management software, there are numerous aspects of the technology that are just plain better thanthey were before.
SEAN SHERMAN, CISSP, CISA, CCSK DEFINING AND PLANNING 2 Defining and Planning Continuous Monitoring for NIST Requirements EXECUTIVE SUMMARY Continuous monitoring is the practice of focused monitoring of systems to better VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . COMMVAULT SIMPANA INTELLISNAP SNAPSHOT MANAGEMENT CommVault Simpana IntelliSnap Snapshot Management and ® EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and isTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Introduction Wi-Fi has come a long way over the years. From devices to access points (APs) to antennas to management software, there are numerous aspects of the technology that are just plain better thanthey were before.
SEAN SHERMAN, CISSP, CISA, CCSK DEFINING AND PLANNING 2 Defining and Planning Continuous Monitoring for NIST Requirements EXECUTIVE SUMMARY Continuous monitoring is the practice of focused monitoring of systems to better VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . COMMVAULT SIMPANA INTELLISNAP SNAPSHOT MANAGEMENT CommVault Simpana IntelliSnap Snapshot Management and ® CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, VORMETRIC DATA SECURITY ARCHITECTURE OVERVIEW White Paper Vormetric Data Security Architecture Overview ® Page | 6 Vormetric.com Big Data, database separation and results access controls The ability to analyze multiple databases and data sets with Big Data techniques can be invaluable. DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Introduction Wi-Fi has come a long way over the years. From devices to access points (APs) to antennas to management software, there are numerous aspects of the technology that are just plain better thanthey were before.
SEAN SHERMAN, CISSP, CISA, CCSK DEFINING AND PLANNING 2 Defining and Planning Continuous Monitoring for NIST Requirements EXECUTIVE SUMMARY Continuous monitoring is the practice of focused monitoring of systems to better VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . THE ESSENTIAL GUIDE TO BLOCKING MALWARE WITHOUT A SOC TH SSTIA I T BCI MAA ITHT A SC 4 INTRODUCTION 2 They prefer using your tools to theirs. If you’ve been following along recent evolu-tions in attack techniques, you may have noticed a VMWARE WORKSPACE OFFICE 365 ENABLING MORE SECURE … WHITE PAPER | 3 ENABLING MORE SECURE COLLABORATION Introduction As a cloud-based business services suite, Microsoft® Office 365™ provides organizations with access to web, mobile and desktop versions of traditional Office THREAT INTELLIGENCE PLATFORMS 3 © 2015 ThreatConnect, Inc. All Rights Reserved CHAPTER ONE: WHY THREAT INTELLIGENCE MATTERS ACTIVE DIRECTORY INTEGRATION WITH OKTA Okta nc. 301 Brannan Street, Suite 300 San Francisco CA, 94107 info@okta.com 1-888-722-7871 OTA HITE APER Active Directory Integration with Okta HOW TO BLOCK MALICIOUS FILE UPLOADS WITH OPSWAT APIS 8.16.17 How to Block Malicious File Uploads with OPSWAT APIs 6 Best Practices Only allow certain types of le formats. This is a simple but necessarystep.
CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and is SEAN SHERMAN, CISSP, CISA, CCSK DEFINING AND PLANNING 2 Defining and Planning Continuous Monitoring for NIST Requirements EXECUTIVE SUMMARY Continuous monitoring is the practice of focused monitoring of systems to betterTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Introduction Wi-Fi has come a long way over the years. From devices to access points (APs) to antennas to management software, there are numerous aspects of the technology that are just plain better thanthey were before.
EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and isTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Introduction Wi-Fi has come a long way over the years. From devices to access points (APs) to antennas to management software, there are numerous aspects of the technology that are just plain better thanthey were before.
SEAN SHERMAN, CISSP, CISA, CCSK DEFINING AND PLANNING 2 Defining and Planning Continuous Monitoring for NIST Requirements EXECUTIVE SUMMARY Continuous monitoring is the practice of focused monitoring of systems to better VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . COMMVAULT SIMPANA INTELLISNAP SNAPSHOT MANAGEMENT CommVault Simpana IntelliSnap Snapshot Management and ® SEAN SHERMAN, CISSP, CISA, CCSK DEFINING AND PLANNING 4 Defining and Planning Continuous Monitoring for NIST Requirements It affords enterprise protection against adversaries by correlating the data from multiple systems to identify a coordi-nated external penetration attack or CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . THE ESSENTIAL GUIDE TO BLOCKING MALWARE WITHOUT A SOC TH SSTIA I T BCI MAA ITHT A SC 4 INTRODUCTION 2 They prefer using your tools to theirs. If you’ve been following along recent evolu-tions in attack techniques, you may have noticed a BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
MAGIC QUADRANT FOR SECURE E-MAIL GATEWAYS Magic Quadrant for Secure E-Mail Gateways Gartner RAS Core Research Note G00175396, Peter Firstbrook, Eric Ouellet, 27 April 2010, RA504302011
VMWARE WORKSPACE OFFICE 365 ENABLING MORE SECURE … WHITE PAPER | 3 ENABLING MORE SECURE COLLABORATION Introduction As a cloud-based business services suite, Microsoft® Office 365™ provides organizations with access to web, mobile and desktop versions of traditional Office THREAT INTELLIGENCE PLATFORMS 3 © 2015 ThreatConnect, Inc. All Rights Reserved CHAPTER ONE: WHY THREAT INTELLIGENCE MATTERS ACTIVE DIRECTORY INTEGRATION WITH OKTA Okta nc. 301 Brannan Street, Suite 300 San Francisco CA, 94107 info@okta.com 1-888-722-7871 OTA HITE APER Active Directory Integration with Okta HOW TO BLOCK MALICIOUS FILE UPLOADS WITH OPSWAT APIS 8.16.17 How to Block Malicious File Uploads with OPSWAT APIs 6 Best Practices Only allow certain types of le formats. This is a simple but necessarystep.
EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
THE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques.THE SECOPS PLAYBOOK
THE SECOPS PLAYBOOK • InTrOduCTIOn 2 The Present and Future: SecOps While we didn’t coin the term alone, Threat Stack has argued for introducing security into the DevOps BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Wi-Fi is very much a location-specific networking technology. Neighbors and interference and all of the other things that affect Wi-Fi performance really only matter NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and is VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
THE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques.THE SECOPS PLAYBOOK
THE SECOPS PLAYBOOK • InTrOduCTIOn 2 The Present and Future: SecOps While we didn’t coin the term alone, Threat Stack has argued for introducing security into the DevOps BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Wi-Fi is very much a location-specific networking technology. Neighbors and interference and all of the other things that affect Wi-Fi performance really only matter NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and is VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and is VORMETRIC DATA SECURITY ARCHITECTURE OVERVIEW White Paper Vormetric Data Security Architecture Overview ® Page | 6 Vormetric.com Big Data, database separation and results access controls The ability to analyze multiple databases and data sets with Big Data techniques can be invaluable. THE ESSENTIAL GUIDE TO BLOCKING MALWARE WITHOUT A SOC TH SSTIA I T BCI MAA ITHT A SC 4 INTRODUCTION 2 They prefer using your tools to theirs. If you’ve been following along recent evolu-tions in attack techniques, you may have noticed a CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, THE 2018 STATE OF ENDPOINT SECURITY RISK PONEMON INSTITUTE© RESEARCH REPORT 2 The 2018 State of Endpoint Security Risk PONEMON INSTITUTE, SEPTEMBER 2018 Part 1: Introduction The 2018 State of Endpoint Security Risk, sponsored by Barkly, reveals that organizations are being attacked at an ACTIVE DIRECTORY INTEGRATION WITH OKTA Okta nc. 301 Brannan Street, Suite 300 San Francisco CA, 94107 info@okta.com 1-888-722-7871 OTA HITE APER Active Directory Integration with OktaJON FRIEDMAN
Jon Friedman Mark Bouchard, CISSP Foreword by John P. Watters to Cyber Threat Intelligence DefinitiveGuide TM Contributions by Jonathan Couchand Matt Hartley
THREAT INTELLIGENCE PLATFORMS 3 © 2015 ThreatConnect, Inc. All Rights Reserved CHAPTER ONE: WHY THREAT INTELLIGENCE MATTERS AVEKSA SOLUTIONS OVERVIEW n Reporting – Ad hoc reporting, together with an extensive set of built-in reports, delivers detailed, summary analyses of users, applications, entitlements, roles and compliance status. n Controls automation – Easy-to-use business rules enable security and THE KEYS TO THE KINGDOM: LIMITING ACTIVE DIRECTORY Sponsored by Quest Software The KeyS To The KingDom: LimiTing AcTive DirecTory ADminiSTrATorS 3 basic security premise is at the heart of microsoft’s domain controller security model, and is the most difficult aspect of designing your own implemen- CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and is SEAN SHERMAN, CISSP, CISA, CCSK DEFINING AND PLANNING 2 Defining and Planning Continuous Monitoring for NIST Requirements EXECUTIVE SUMMARY Continuous monitoring is the practice of focused monitoring of systems to betterTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Introduction Wi-Fi has come a long way over the years. From devices to access points (APs) to antennas to management software, there are numerous aspects of the technology that are just plain better thanthey were before.
COMMVAULT SIMPANA INTELLISNAP SNAPSHOT MANAGEMENT CommVault Simpana IntelliSnap Snapshot Management and ® VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and is SEAN SHERMAN, CISSP, CISA, CCSK DEFINING AND PLANNING 2 Defining and Planning Continuous Monitoring for NIST Requirements EXECUTIVE SUMMARY Continuous monitoring is the practice of focused monitoring of systems to betterTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Introduction Wi-Fi has come a long way over the years. From devices to access points (APs) to antennas to management software, there are numerous aspects of the technology that are just plain better thanthey were before.
COMMVAULT SIMPANA INTELLISNAP SNAPSHOT MANAGEMENT CommVault Simpana IntelliSnap Snapshot Management and ® VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
SEAN SHERMAN, CISSP, CISA, CCSK DEFINING AND PLANNING 4 Defining and Planning Continuous Monitoring for NIST Requirements It affords enterprise protection against adversaries by correlating the data from multiple systems to identify a coordi-nated external penetration attack or CLOUD PLATFORM SECURITY AND MONITORING Step 1: Configuration that maximizes security of cloud platform architecture Most cloud platforms include some built-in security features and applications to ensure proper data protection, VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . THE ESSENTIAL GUIDE TO BLOCKING MALWARE WITHOUT A SOC TH SSTIA I T BCI MAA ITHT A SC 4 INTRODUCTION 2 They prefer using your tools to theirs. If you’ve been following along recent evolu-tions in attack techniques, you may have noticed a BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
MAGIC QUADRANT FOR SECURE E-MAIL GATEWAYS Magic Quadrant for Secure E-Mail Gateways Gartner RAS Core Research Note G00175396, Peter Firstbrook, Eric Ouellet, 27 April 2010, RA504302011
VMWARE WORKSPACE OFFICE 365 ENABLING MORE SECURE … WHITE PAPER | 3 ENABLING MORE SECURE COLLABORATION Introduction As a cloud-based business services suite, Microsoft® Office 365™ provides organizations with access to web, mobile and desktop versions of traditional Office THREAT INTELLIGENCE PLATFORMS 3 © 2015 ThreatConnect, Inc. All Rights Reserved CHAPTER ONE: WHY THREAT INTELLIGENCE MATTERS ACTIVE DIRECTORY INTEGRATION WITH OKTA Okta nc. 301 Brannan Street, Suite 300 San Francisco CA, 94107 info@okta.com 1-888-722-7871 OTA HITE APER Active Directory Integration with Okta HOW TO BLOCK MALICIOUS FILE UPLOADS WITH OPSWAT APIS 8.16.17 How to Block Malicious File Uploads with OPSWAT APIs 6 Best Practices Only allow certain types of le formats. This is a simple but necessarystep.
EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and isTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques.THE SECOPS PLAYBOOK
THE SECOPS PLAYBOOK • InTrOduCTIOn 2 The Present and Future: SecOps While we didn’t coin the term alone, Threat Stack has argued for introducing security into the DevOps VORMETRIC DATA SECURITY ARCHITECTURE OVERVIEW White Paper Vormetric Data Security Architecture Overview ® Page | 6 Vormetric.com Big Data, database separation and results access controls The ability to analyze multiple databases and data sets with Big Data techniques can be invaluable. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Wi-Fi is very much a location-specific networking technology. Neighbors and interference and all of the other things that affect Wi-Fi performance really only matter EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and isTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques.THE SECOPS PLAYBOOK
THE SECOPS PLAYBOOK • InTrOduCTIOn 2 The Present and Future: SecOps While we didn’t coin the term alone, Threat Stack has argued for introducing security into the DevOps VORMETRIC DATA SECURITY ARCHITECTURE OVERVIEW White Paper Vormetric Data Security Architecture Overview ® Page | 6 Vormetric.com Big Data, database separation and results access controls The ability to analyze multiple databases and data sets with Big Data techniques can be invaluable. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Wi-Fi is very much a location-specific networking technology. Neighbors and interference and all of the other things that affect Wi-Fi performance really only matterTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. VORMETRIC DATA SECURITY ARCHITECTURE OVERVIEW White Paper Vormetric Data Security Architecture Overview ® Page | 6 Vormetric.com Big Data, database separation and results access controls The ability to analyze multiple databases and data sets with Big Data techniques can be invaluable. STRATEGIC OPPORTUNITY ANALYSIS OF THE GLOBAL SMART CITY MARKET Executive Summary—Key Findings of the Study Smart City Market: Key Take Aways, Global, 2011–2025 1 Around 26 global cities and more than 90 sustainable cities are to developed by 2025.Around 50% VMWARE WORKSPACE OFFICE 365 ENABLING MORE SECURE … WHITE PAPER | 3 ENABLING MORE SECURE COLLABORATION Introduction As a cloud-based business services suite, Microsoft® Office 365™ provides organizations with access to web, mobile and desktop versions of traditional Office ACTIVE DIRECTORY INTEGRATION WITH OKTA Okta nc. 301 Brannan Street, Suite 300 San Francisco CA, 94107 info@okta.com 1-888-722-7871 OTA HITE APER Active Directory Integration with Okta THREAT INTELLIGENCE PLATFORMS 3 © 2015 ThreatConnect, Inc. All Rights Reserved CHAPTER ONE: WHY THREAT INTELLIGENCE MATTERS OUTSYSTEMS PLATFORM AND FORCE OutSystems Platform and Force.com different PaaS for different players An InComparison Paper by Bloor Research Author : David Norfolk Publishdate : October 2013
MEETING COMPLIANCE OBJECTIVES IN SHAREPOINT® Meeting Compliance Objectives in SharePoint® February 2009 white paper Unleashing the Power of SharePoint™ This document is intended to aid IT administrators and other COMPARING ACCELLION AND EGNYTE Egnyte Inc. | 1350 W. Middlefield Road | Mountain View, CA 94043, USA | Phone: 877-7EGNYTE (877-734-6983) www.egnyte.com | © 2014 by EgnyteInc.
THE KEYS TO THE KINGDOM: LIMITING ACTIVE DIRECTORY Sponsored by Quest Software The KeyS To The KingDom: LimiTing AcTive DirecTory ADminiSTrATorS 3 basic security premise is at the heart of microsoft’s domain controller security model, and is the most difficult aspect of designing your own implemen- EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and isTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
THE SECOPS PLAYBOOK
THE SECOPS PLAYBOOK • InTrOduCTIOn 2 The Present and Future: SecOps While we didn’t coin the term alone, Threat Stack has argued for introducing security into the DevOps CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and isTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
THE SECOPS PLAYBOOK
THE SECOPS PLAYBOOK • InTrOduCTIOn 2 The Present and Future: SecOps While we didn’t coin the term alone, Threat Stack has argued for introducing security into the DevOps CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
NETAPP STORAGE BEST PRACTICES FOR MICROSOFT VIRTUALIZATION 5 NetApp Storage Best Practices for Microsoft Virtualization 1 SERVER CONFIGURATION 1.1 MICROSOFT HYPER-V R2 CONFIGURATION Microsoft Hyper-V is the latest server virtualization product from Microsoft, featuring a 64-bit hypervisor, and isTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. VORMETRIC DATA SECURITY ARCHITECTURE OVERVIEW White Paper Vormetric Data Security Architecture Overview ® Page | 6 Vormetric.com Big Data, database separation and results access controls The ability to analyze multiple databases and data sets with Big Data techniques can be invaluable. STRATEGIC OPPORTUNITY ANALYSIS OF THE GLOBAL SMART CITY MARKET Executive Summary—Key Findings of the Study Smart City Market: Key Take Aways, Global, 2011–2025 1 Around 26 global cities and more than 90 sustainable cities are to developed by 2025.Around 50% VMWARE WORKSPACE OFFICE 365 ENABLING MORE SECURE … WHITE PAPER | 3 ENABLING MORE SECURE COLLABORATION Introduction As a cloud-based business services suite, Microsoft® Office 365™ provides organizations with access to web, mobile and desktop versions of traditional Office ACTIVE DIRECTORY INTEGRATION WITH OKTA Okta nc. 301 Brannan Street, Suite 300 San Francisco CA, 94107 info@okta.com 1-888-722-7871 OTA HITE APER Active Directory Integration with Okta MEETING COMPLIANCE OBJECTIVES IN SHAREPOINT® Meeting Compliance Objectives in SharePoint® February 2009 white paper Unleashing the Power of SharePoint™ This document is intended to aid IT administrators and other OUTSYSTEMS PLATFORM AND FORCE OutSystems Platform and Force.com different PaaS for different players An InComparison Paper by Bloor Research Author : David Norfolk Publishdate : October 2013
COMPARING ACCELLION AND EGNYTE Egnyte Inc. | 1350 W. Middlefield Road | Mountain View, CA 94043, USA | Phone: 877-7EGNYTE (877-734-6983) www.egnyte.com | © 2014 by EgnyteInc.
THE KEYS TO THE KINGDOM: LIMITING ACTIVE DIRECTORY Sponsored by Quest Software The KeyS To The KingDom: LimiTing AcTive DirecTory ADminiSTrATorS 3 basic security premise is at the heart of microsoft’s domain controller security model, and is the most difficult aspect of designing your own implemen- EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. VORMETRIC DATA SECURITY ARCHITECTURE OVERVIEW White Paper Vormetric Data Security Architecture Overview ® Page | 6 Vormetric.com Big Data, database separation and results access controls The ability to analyze multiple databases and data sets with Big Data techniques can be invaluable.THE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
THE SECOPS PLAYBOOK
THE SECOPS PLAYBOOK • InTrOduCTIOn 2 The Present and Future: SecOps While we didn’t coin the term alone, Threat Stack has argued for introducing security into the DevOps CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
AVEKSA SOLUTIONS OVERVIEW n Reporting – Ad hoc reporting, together with an extensive set of built-in reports, delivers detailed, summary analyses of users, applications, entitlements, roles and compliance status. n Controls automation – Easy-to-use business rules enable security and DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Wi-Fi is very much a location-specific networking technology. Neighbors and interference and all of the other things that affect Wi-Fi performance really only matter EMC NETWORKER DESIGN BEST PRACTICES WITH DATA DOMAIN 7 significant differentiator from competitive products which perform deduplication at the file level or at a block level, resulting in more efficient deduplication capabilities. VORMETRIC DATA SECURITY ARCHITECTURE OVERVIEW White Paper Vormetric Data Security Architecture Overview ® Page | 6 Vormetric.com Big Data, database separation and results access controls The ability to analyze multiple databases and data sets with Big Data techniques can be invaluable.THE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. BUILDING A UNIFIED COMMUNICATIONS AND COLLABORATION ROADMAP 2 ©Nemertes Research 2013 www.nemertes.com 1-888-241-2685 DN2569 Agenda Introductions and Overview What is a Roadmap? Unified Communications Architecture Key Roadmap Components: Voice VideoIM/presence
THE SECOPS PLAYBOOK
THE SECOPS PLAYBOOK • InTrOduCTIOn 2 The Present and Future: SecOps While we didn’t coin the term alone, Threat Stack has argued for introducing security into the DevOps CONTINUOUS MONITORING: WHAT IT IS, WHY IT IS NEEDED, AND Continuous Monitoring: What It Is, Why It Is Needed, and How to Use It June 2011 A SANS Whitepaper Written by: E. Eugene Schultz, Ph.D. Advisor: Marcus H. Sachs, Director Emiratis, SANS Internet Storm Center Benefits of Continuous Monitoring PAge 2 What, How, and Whereto
VEEAM AVAILABILITY SUITE AND SAP ON ORACLE Veeam Availability Suite and SAP on Oracle Deployment Guide 2016 Veeam Software 6 The challenge Enterprise organizations today are under incredible pressure to keep Availability levels high . BRING YOUR OWN DEVICE (BYOD)—KEY TRENDS AND CONSIDERATIONS #9838-65 ©2013 Frost & Sullivan www.frost.com 2 Exhibit 1 shows the percent of organizations with BYOD activity in the United States from2011 to 2018.
AVEKSA SOLUTIONS OVERVIEW n Reporting – Ad hoc reporting, together with an extensive set of built-in reports, delivers detailed, summary analyses of users, applications, entitlements, roles and compliance status. n Controls automation – Easy-to-use business rules enable security and DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Wi-Fi is very much a location-specific networking technology. Neighbors and interference and all of the other things that affect Wi-Fi performance really only matterTHE FILELESS ATTACK
E FILELESS AACK SUIAL UIE 3 Executive Summary Attacks are constantly evolving. One of the most damaging trends we’ve seen of late is the increasingly widespread adoption of fileless attack techniques. OUTSYSTEMS PLATFORM AND FORCE OutSystems Platform and Force.com different PaaS for different players An InComparison Paper by Bloor Research Author : David Norfolk Publishdate : October 2013
VMWARE WORKSPACE OFFICE 365 ENABLING MORE SECURE … WHITE PAPER | 3 ENABLING MORE SECURE COLLABORATION Introduction As a cloud-based business services suite, Microsoft® Office 365™ provides organizations with access to web, mobile and desktop versions of traditional Office COMPARING ACCELLION AND EGNYTE Egnyte Inc. | 1350 W. Middlefield Road | Mountain View, CA 94043, USA | Phone: 877-7EGNYTE (877-734-6983) www.egnyte.com | © 2014 by EgnyteInc.
2019 STATE OF DEVOPS Previous Next Table of Contents interop.com May 2019 3 AUTHOR Salvatore Salamone is the managing editor of Network Computing. After working as a research physicist, he became a writer and edi- ACTIVE DIRECTORY INTEGRATION WITH OKTA Okta nc. 301 Brannan Street, Suite 300 San Francisco CA, 94107 info@okta.com 1-888-722-7871 OTA HITE APER Active Directory Integration with Okta MEETING COMPLIANCE OBJECTIVES IN SHAREPOINT® Meeting Compliance Objectives in SharePoint® February 2009 white paper Unleashing the Power of SharePoint™ This document is intended to aid IT administrators and other DETERMINING THE CAUSE OF A HIGH RETRY PERCENTAGE Wi-Fi is very much a location-specific networking technology. Neighbors and interference and all of the other things that affect Wi-Fi performance really only matter ECCOLO MEDIA 2010 B2B TECHNOLOGY COLLATERAL SURVEY REPORT 2. EXECUTIVE SUMMARY. Welcome to the third annual . Eccolo Media B2B Technology Collateral Survey Report. Conducting a survey of this detail, analyzing the data, and writing this report takes THE KEYS TO THE KINGDOM: LIMITING ACTIVE DIRECTORY Sponsored by Quest Software The KeyS To The KingDom: LimiTing AcTive DirecTory ADminiSTrATorS 3 basic security premise is at the heart of microsoft’s domain controller security model, and is the most difficult aspect of designing your own implemen- Skip to main content This site is part of the Informa Markets Division of Informa PLC* __INFORMA PLC
* __ABOUT US
* __INVESTOR RELATIONS* __TALENT
This site is operated by a business or businesses owned by Informa PLC and all copyright resides with them. Informa PLC's registered office is 5 Howick Place, London SW1P 1WG. Registered in England and Wales.Number 8860726.
This site
Search
__
* Events |
* Careers |
* Contact Us
* About Us
* Senior Management Team* Our History
* Sustainability
* Contact Us
* Regions
* Asia
* Europe
* Middle East & Africa* North America
* South America
* Upcoming Events
* Markets
* Agriculture
* Aviation & Aerospace * Beauty & Aesthetics * Culture & Lifestyle * Design & Furniture * Energy, Utilities & Resources* Fashion & Apparel
* Health & Nutrition * Healthcare & Pharmaceuticals * Hospitality, Food & Beverage * Infrastructure, Construction & Real Estate* Jewellery
* Manufacturing, Machinery & Equipment * Maritime, Transportation & Logistics * Media & Entertainment* People
* Careers
* Office Locations
* Press
* Media Contacts
* Informa Plc
*
*
Toggle navigation
Navigation Toggle navigation CREATING GLOBAL PLATFORMS FOR INDUSTRIES, SPECIALIST MARKETS AND CUSTOMERS TO TRADE, INNOVATE AND GROW. HELPING COMMUNITIES THRIVE 365 DAYS A YEAR.About Us
test
NEWS
PERFORMING TO PLAN: INFORMA’S HALF YEAR RESULTS INDUSTRY RECOGNITION: INFORMA MARKETS CONTINUES TO LEAD MEET COTERIE: THE PREMIER GLOBAL EVENT WITHIN THE NEW YORK FASHIONMARKETPLACE
WHO WE ARE
Informa Markets creates global platforms and opportunities for industries, specialist markets and communities to trade, innovateand grow.
As the world’s leading exhibitions organiser, we deliver over 550 international market-leading events, brands and experiences annually through face-to-face exhibitions, specialist digital content and actionable data solutions. People are at the heart of Informa Markets. Our 4,400+ talented colleagues work across a variety of markets and use their industryinsight to
create environments that enable our customers to connect and businesses to flourish.#1
EXHIBITIONS ORGANISER550+
B2B BRANDS
4,400+
COLLEAGUES GLOBALLY
40+
COUNTRIES
UPCOMING EVENTS
CPHI WORLDWIDE
05 - 07 November, 2019Frankurt, Germany
LEARN MORE
FUTURECOM
28 - 31 October, 2019|São Paulo, BrazilLearn More
-------------------------TOC AMERICAS
29 - 31 October, 2019|Cartagena, ColombiaLearn More
-------------------------DENTECH CHINA
30 October - 02 November, 2019|Shanghai, ChinaLearn More
------------------------- FORT LAUDERDALE INTERNATIONAL BOAT SHOW 30 October - 03 November, 2019|Fort Lauderdale, USALearn More
-------------------------FIREX EGYPT
03 - 05 November, 2019|Cairo, EgyptLearn More
VIEW ALL UPCOMING EVENTS » OUR SPECIALIST MARKETS We bring a diverse range of industry sectors and specialist markets to life, unlocking opportunities and helping them to thrive 365 days of the year. Discover all the markets we serve and keep up with our latest news and events.CULTURE & LIFESTYLE
JEWELLERY
ENERGY, UTILITIES & RESOURCES MANUFACTURING, MACHINERY & EQUIPMENTFASHION & APPAREL
MEDIA & ENTERTAINMENT EXPLORE OUR SPECIALIST MARKETS »OUR PEOPLE
People are at the heart of Informa Markets. Our 4,400+ colleagues deliver over 550 international events and brands in more than 40 countries, working across a variety of specialist markets, industries and continents. Using our industry insight, comprehensive portfolio of events, and digital resources, we create platforms for our customers to connect, and shape environments that enable businesses to flourish. Get to know the talented individuals responsible for bringing Informa Markets to life.Join Us
CONTACT US
OFFICE LOCATIONS
UPCOMING EVENTS
* __
* __
* Home |
* About Us |
* Regions |
* Markets |
* People |
* Press
Copyright © 2019. All rights reserved. Informa Markets, a trading division of Informa PLC.* Accessibility|
* Privacy Policy |
* Cookie Policy|
* Terms of Use|
* Visitor Terms And Conditions We use cookies to help provide you with the best possible online experience. Please read our Privacy Policyand Cookie Policy
for information about which cookies we use and what information we collect on our site. By continuing to use this site, you agree that we may store and access cookies on your device.I Agree
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0