Are you over 18 and want to see adult content?
More Annotations

A complete backup of www.veinsensor.pl
Are you over 18 and want to see adult content?
A complete backup of 131458934.keywordblocks.com
Are you over 18 and want to see adult content?

A complete backup of markkavanagh.com
Are you over 18 and want to see adult content?

A complete backup of azscers.000webhostapp.com
Are you over 18 and want to see adult content?

A complete backup of abc12.onesignal.com
Are you over 18 and want to see adult content?

A complete backup of sp-active.adsrvr.org
Are you over 18 and want to see adult content?

A complete backup of services.runescape.com-api.top
Are you over 18 and want to see adult content?
A complete backup of cb1.dev.rtb.owneriq.net
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of spectrumlocalnews.com
Are you over 18 and want to see adult content?

A complete backup of ardatradexport.com
Are you over 18 and want to see adult content?
A complete backup of mobilenations.com
Are you over 18 and want to see adult content?
A complete backup of csharp-station.com
Are you over 18 and want to see adult content?
A complete backup of nosy-paradise.com
Are you over 18 and want to see adult content?
A complete backup of allterraincycles.co.uk
Are you over 18 and want to see adult content?
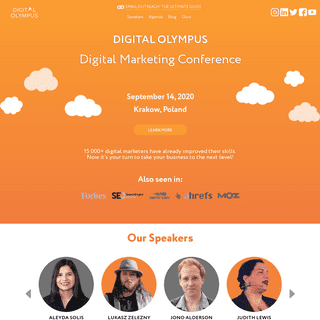
A complete backup of digitalolympus.net
Are you over 18 and want to see adult content?

A complete backup of russian-gamer.ru
Are you over 18 and want to see adult content?
Text
SSH
SET THE ILO PASSWORD FROM LINUX USING HPONCFG To load the xml file into the iLO, the hponcfg command with the “-f filename” option is used. The “-f” option instructs hponcfg to set Management Processor (iLO) configuration from “filename”. After the command has been executed successfully, the Administrator’s password is set to the new value. To find out aboutother settings
SETUP POSTFIX FOR MULTIPLE DOMAINS You can configure postfix for more than one domain via the use of a hash file. This file contains the list of domains postfix will accept for local delivery. To configure postfix to read the destination domains from a hash file, open the /etc/postfix/main.cf configuration file and add the following setting. The configuration is similar tothe
CHANGE SSH PORT IN CENTOS WITH SELINUX Since version 4 of CentOS, SELinux is providing an additional layer of security to the Linux distribution. As of SELinux in combination with sshd, changing the port or even listening on 2 ports is not as easy as just changing the sshd configuration file. SHOW NETWORK ROUTES ON MACOSX In OS X, to specify a route for network 10.0.0.0/24 to be routed to gateway 10.0.0.1 you use the following command. $ route -n add 10.0.0.0/24 10.0.0.1. But if you are on a Linux system you will have to use the following command to do the same: $ route -n add -net 10.0.0.0/24 gw 10.0.0.1. The syntax is very close to the syntax of OSX but it is
RESTRICT SSH LOGIN USING SSH KEYS TO A PARTICULAR IP The SSH connection to your server is one of the most important way of accessing and managing your server, because of this, it is a target for any attacker that wants access to your server. MERGE TWO SVN REPOSITORIES UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. INSTALL HP PROLIANT MANAGEMENT UTILITIES This command will download the GPG-Key from the HP website and install it on the system in order for apt to verify the package signatures. To retrieve the package list containing the packages from the newly added repository, run the the following command as usual. $ apt-get update. With the package list loaded, the packages provided in the SDR SETUP DOVECOT WITH PAM AUTHENTICATION AND SSL ON CENTOS Apply Configuration. After the configuration changes we need to restart dovecot to load the changed configuration. $ /etc/init.d/dovecot restart. Check the startup configuration as you might want this service to start at boot time. This can be done via the following command. $ chkconfig dovecot on. GENERATE PUBLIC SSH KEY FROM PRIVATE SSH KEY To generate the missing public key again from the private key, the following command will generate the public key of the private key provided with the -f option. $ ssh-keygen -y -f ~/.ssh/id_rsa > ~/.ssh/id_rsa.pub Enter passphrase: The -y option will read a privateSSH
SET THE ILO PASSWORD FROM LINUX USING HPONCFG To load the xml file into the iLO, the hponcfg command with the “-f filename” option is used. The “-f” option instructs hponcfg to set Management Processor (iLO) configuration from “filename”. After the command has been executed successfully, the Administrator’s password is set to the new value. To find out aboutother settings
SETUP POSTFIX FOR MULTIPLE DOMAINS You can configure postfix for more than one domain via the use of a hash file. This file contains the list of domains postfix will accept for local delivery. To configure postfix to read the destination domains from a hash file, open the /etc/postfix/main.cf configuration file and add the following setting. The configuration is similar tothe
CHANGE SSH PORT IN CENTOS WITH SELINUX Since version 4 of CentOS, SELinux is providing an additional layer of security to the Linux distribution. As of SELinux in combination with sshd, changing the port or even listening on 2 ports is not as easy as just changing the sshd configuration file. SHOW NETWORK ROUTES ON MACOSX In OS X, to specify a route for network 10.0.0.0/24 to be routed to gateway 10.0.0.1 you use the following command. $ route -n add 10.0.0.0/24 10.0.0.1. But if you are on a Linux system you will have to use the following command to do the same: $ route -n add -net 10.0.0.0/24 gw 10.0.0.1. The syntax is very close to the syntax of OSX but it is
RESTRICT SSH LOGIN USING SSH KEYS TO A PARTICULAR IP The SSH connection to your server is one of the most important way of accessing and managing your server, because of this, it is a target for any attacker that wants access to your server. MERGE TWO SVN REPOSITORIES INSTALL HP PROLIANT MANAGEMENT UTILITIES This command will download the GPG-Key from the HP website and install it on the system in order for apt to verify the package signatures. To retrieve the package list containing the packages from the newly added repository, run the the following command as usual. $ apt-get update. With the package list loaded, the packages provided in the SDR UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. FIND AND EXTRACT ONE FILE FROM RPM PACKAGE Option 1: cpio. Propably the more elegant way of extracting a file, at least in my opinion, is the use of cpio (1). Cpio is an archive utility which allows to extract files from a few archive formats and needs to be installed as separate package. $ yum install cpio. Combined with the rpm2cpio (8) utility, which comes pre-installed aspart of
SETUP POSTFIX FOR MULTIPLE DOMAINS You can configure postfix for more than one domain via the use of a hash file. This file contains the list of domains postfix will accept for local delivery. To configure postfix to read the destination domains from a hash file, open the /etc/postfix/main.cf configuration file and add the following setting. The configuration is similar tothe
MANAGE SSH-KEYS WITH THE SSH-AGENT Many webservices generate ssh keys to access their service. With the amount of services the number of SSH keys grows. To avoid dealing with the keys in the command line and the ssh_config(5), you can simply add the ssh-key to the local ssh-agent(1) to manage them.. The ssh-agent(1) is a program used to hold ssh private keys used to authenticate to remote systems via ssh SELINUX ALLOW WEBSERVER TO SEND EMAIL As already shown in my Migrate WordPress site with minimal downtime article, SELinux provides predefined rulesets for some functionality. These can be enabled with boolean switches. The boolean switch to allow apache to send emails is called “httpd_can_sendmail”: $ setsebool -P httpd_can_sendmail=on. This command will enable the rulesto
REMOVE STUCK EMAILS FROM POSTFIX MAIL QUEUE If a huge number of emails is clogging the mail queue, it makes sense to remove them manually from the queue. If there are only one or two emails which should be removed, you can just use their Queue ID from the mailq (1) output and delete them with the following command. $ postsuper -d CB7E5B0067 postsuper: CB7E5B0067: removed postsuper LVM REMOVE PHYSICAL VOLUME FROM VOLUME GROUP LVM Remove physical volume from volume group. LVM provides flexibility to organize logical volumes without being bound to inflexible partitioning. If set-up correctly, the LVM can grow as the disk/raid might grow. To allow the LVM to grow, the block device needs to be added as a physical volume to LVM without any partitioning on it. AUTOMOUNT A LUKS ENCRYPTED VOLUME ON SYSTEM START Linux supports encrypted volumes with luks. When a luks encrypted volume is set up during installation to be booted from, the volume is already configured and set up. MERGE TWO SVN REPOSITORIES There was a point in time when i created a copy of a project and it was then committed into another repository. This as such is not a big problem, but merging those repositories back together while keeping all the complete changes in the history is a challenge. INSTALL HP PROLIANT MANAGEMENT UTILITIES This command will download the GPG-Key from the HP website and install it on the system in order for apt to verify the package signatures. To retrieve the package list containing the packages from the newly added repository, run the the following command as usual. $ apt-get update. With the package list loaded, the packages provided in the SDR UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. SETUP DOVECOT WITH PAM AUTHENTICATION AND SSL ON CENTOS Apply Configuration. After the configuration changes we need to restart dovecot to load the changed configuration. $ /etc/init.d/dovecot restart. Check the startup configuration as you might want this service to start at boot time. This can be done via the following command. $ chkconfig dovecot on. SET THE ILO PASSWORD FROM LINUX USING HPONCFG To load the xml file into the iLO, the hponcfg command with the “-f filename” option is used. The “-f” option instructs hponcfg to set Management Processor (iLO) configuration from “filename”. After the command has been executed successfully, the Administrator’s password is set to the new value. To find out aboutother settings
GENERATE PUBLIC SSH KEY FROM PRIVATE SSH KEY To generate the missing public key again from the private key, the following command will generate the public key of the private key provided with the -f option. $ ssh-keygen -y -f ~/.ssh/id_rsa > ~/.ssh/id_rsa.pub Enter passphrase: The -y option will read a privateSSH
INSTALL HP PROLIANT MANAGEMENT UTILITIES This command will download the GPG-Key from the HP website and install it on the system in order for apt to verify the package signatures. To retrieve the package list containing the packages from the newly added repository, run the the following command as usual. $ apt-get update. With the package list loaded, the packages provided in the SDR UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. SETUP DOVECOT WITH PAM AUTHENTICATION AND SSL ON CENTOS Apply Configuration. After the configuration changes we need to restart dovecot to load the changed configuration. $ /etc/init.d/dovecot restart. Check the startup configuration as you might want this service to start at boot time. This can be done via the following command. $ chkconfig dovecot on. SET THE ILO PASSWORD FROM LINUX USING HPONCFG To load the xml file into the iLO, the hponcfg command with the “-f filename” option is used. The “-f” option instructs hponcfg to set Management Processor (iLO) configuration from “filename”. After the command has been executed successfully, the Administrator’s password is set to the new value. To find out aboutother settings
GENERATE PUBLIC SSH KEY FROM PRIVATE SSH KEY To generate the missing public key again from the private key, the following command will generate the public key of the private key provided with the -f option. $ ssh-keygen -y -f ~/.ssh/id_rsa > ~/.ssh/id_rsa.pub Enter passphrase: The -y option will read a privateSSH
HARDEN SSH SERVER SETTINGS Before sshd is restarted, check the sshd config to be valid (-t) and show debug infos (-d) where the -d can be provided multiple times to show more details. If the sshd configuration is not valid, the output will tell exactly which option and even the value that is invalid. RECOMPRESS GIT REPOSITORY The git command ‘gc’ (garbage collection) will cleanup unnecessary files and optimize the local repository. It runs a number of housekeeping tasks within the repository, such as compressing file revisions to reduce disk space, and more. The option ‘–prune=now’ is set to remove loose objects older than the specified date (in this case PERMANENTLY REJECT A SPECIFIC EMAIL SENDER ADDRESS USING Postfix generally accepts all sender addresses. It might be needed in some rare cases to reject one sender addresses for some reason. With postfix, there is the possibility to use the “check_sender_access” to set individual actions per sender address. SELINUX ALLOW WEBSERVER TO SEND EMAIL As already shown in my Migrate WordPress site with minimal downtime article, SELinux provides predefined rulesets for some functionality. These can be enabled with boolean switches. The boolean switch to allow apache to send emails is called “httpd_can_sendmail”: $ setsebool -P httpd_can_sendmail=on. This command will enable the rulesto
SHRINK SPARSE CQOW2 DISC IMAGE The following procedure will show how it is possible to shrink a qcow2 disk image after it has been expanded to its maximum size. The following output shows the disk image of the VM being expanded to the maximum. $ qemu-img info vm-106-disk-1.qcow2 image: vm-106-disk-1.qcow2 file format: qcow2 virtual size: 80G (85899345920bytes) disk size
DOWNLOAD A COMPLETE WEBSITE USING WGET In some rare cases you might run into the need to download a complete website onto your local machine for offline usage. There are many GUI tools to do this with loads of options.MULTIMEDIA ARCHIVES
Sometimes it can be helpful to inspect videos or sections of a video frame by frame. The simplest way to do this might be using ffplay. Although with its minimalistic user interface, the controls requiregetting used to.
UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. FIND AND EXTRACT ONE FILE FROM RPM PACKAGE Option 1: cpio. Propably the more elegant way of extracting a file, at least in my opinion, is the use of cpio (1). Cpio is an archive utility which allows to extract files from a few archive formats and needs to be installed as separate package. $ yum install cpio. Combined with the rpm2cpio (8) utility, which comes pre-installed aspart of
SPLITTING UP AN SVN REPOSITORY The first step is quite simple but must be run directly on the machine where the repository is located. The command “svnadmin dump” requires direct access to the repository directory. svnadmin dump /path/to/repository/ >repository.dump. After that is finished, you will find the file ‘repository.dump’ containing a full dump of the SETUP SFTP ONLY ACCOUNT USING OPENSSH AND SSH-KEY Preparing the Account. A new sftp only account can now be created and prepared. As described above, the user needs to be assigned to the group used in the Match block. $ useradd -G sftponly -s /sbin/nologin user1. The “-G” option adds “sftponly” as a supplementary group to the user “user1”. With the “-s” option, the user gets SETUP SIEVE MAIL FILTER WITH POSTFIX AND DOVECOT A mailbox can get flooded with many emails, some are automatically generated, others are related to orders. Sorting through emails on a daily basis can be a tedious task. SELINUX ALLOW WEBSERVER TO SEND EMAIL As already shown in my Migrate WordPress site with minimal downtime article, SELinux provides predefined rulesets for some functionality. These can be enabled with boolean switches. The boolean switch to allow apache to send emails is called “httpd_can_sendmail”: $ setsebool -P httpd_can_sendmail=on. This command will enable the rulesto
REMOVE STUCK EMAILS FROM POSTFIX MAIL QUEUE If a huge number of emails is clogging the mail queue, it makes sense to remove them manually from the queue. If there are only one or two emails which should be removed, you can just use their Queue ID from the mailq (1) output and delete them with the following command. $ postsuper -d CB7E5B0067 postsuper: CB7E5B0067: removed postsuper LVM REMOVE PHYSICAL VOLUME FROM VOLUME GROUP LVM Remove physical volume from volume group. LVM provides flexibility to organize logical volumes without being bound to inflexible partitioning. If set-up correctly, the LVM can grow as the disk/raid might grow. To allow the LVM to grow, the block device needs to be added as a physical volume to LVM without any partitioning on it. UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. INSTALL HP PROLIANT MANAGEMENT UTILITIES This command will download the GPG-Key from the HP website and install it on the system in order for apt to verify the package signatures. To retrieve the package list containing the packages from the newly added repository, run the the following command as usual. $ apt-get update. With the package list loaded, the packages provided in the SDR CREATE GNUPG KEY WITH SUB-KEYS TO SIGN, ENCRYPTSEE MORE ON BLOG.TINNED-SOFTWARE.NET SETUP DOVECOT WITH PAM AUTHENTICATION AND SSL ON CENTOS Apply Configuration. After the configuration changes we need to restart dovecot to load the changed configuration. $ /etc/init.d/dovecot restart. Check the startup configuration as you might want this service to start at boot time. This can be done via the following command. $ chkconfig dovecot on. GENERATE PUBLIC SSH KEY FROM PRIVATE SSH KEY To generate the missing public key again from the private key, the following command will generate the public key of the private key provided with the -f option. $ ssh-keygen -y -f ~/.ssh/id_rsa > ~/.ssh/id_rsa.pub Enter passphrase: The -y option will read a privateSSH
FIND AND EXTRACT ONE FILE FROM RPM PACKAGE Option 1: cpio. Propably the more elegant way of extracting a file, at least in my opinion, is the use of cpio (1). Cpio is an archive utility which allows to extract files from a few archive formats and needs to be installed as separate package. $ yum install cpio. Combined with the rpm2cpio (8) utility, which comes pre-installed aspart of
SET THE ILO PASSWORD FROM LINUX USING HPONCFG To load the xml file into the iLO, the hponcfg command with the “-f filename” option is used. The “-f” option instructs hponcfg to set Management Processor (iLO) configuration from “filename”. After the command has been executed successfully, the Administrator’s password is set to the new value. To find out aboutother settings
SELINUX ALLOW WEBSERVER TO SEND EMAIL As already shown in my Migrate WordPress site with minimal downtime article, SELinux provides predefined rulesets for some functionality. These can be enabled with boolean switches. The boolean switch to allow apache to send emails is called “httpd_can_sendmail”: $ setsebool -P httpd_can_sendmail=on. This command will enable the rulesto
LVM REMOVE PHYSICAL VOLUME FROM VOLUME GROUP LVM Remove physical volume from volume group. LVM provides flexibility to organize logical volumes without being bound to inflexible partitioning. If set-up correctly, the LVM can grow as the disk/raid might grow. To allow the LVM to grow, the block device needs to be added as a physical volume to LVM without any partitioning on it. SETUP AMAVISD-NEW WITH SPAMASSASSIN AND CLAMAV WITH In the here described setup, postfix passes the incoming mails on to amavisd-new. There, the emails get checked for viruses and spam. After the email is checked, it UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. INSTALL HP PROLIANT MANAGEMENT UTILITIES This command will download the GPG-Key from the HP website and install it on the system in order for apt to verify the package signatures. To retrieve the package list containing the packages from the newly added repository, run the the following command as usual. $ apt-get update. With the package list loaded, the packages provided in the SDR CREATE GNUPG KEY WITH SUB-KEYS TO SIGN, ENCRYPTSEE MORE ON BLOG.TINNED-SOFTWARE.NET SETUP DOVECOT WITH PAM AUTHENTICATION AND SSL ON CENTOS Apply Configuration. After the configuration changes we need to restart dovecot to load the changed configuration. $ /etc/init.d/dovecot restart. Check the startup configuration as you might want this service to start at boot time. This can be done via the following command. $ chkconfig dovecot on. GENERATE PUBLIC SSH KEY FROM PRIVATE SSH KEY To generate the missing public key again from the private key, the following command will generate the public key of the private key provided with the -f option. $ ssh-keygen -y -f ~/.ssh/id_rsa > ~/.ssh/id_rsa.pub Enter passphrase: The -y option will read a privateSSH
FIND AND EXTRACT ONE FILE FROM RPM PACKAGE Option 1: cpio. Propably the more elegant way of extracting a file, at least in my opinion, is the use of cpio (1). Cpio is an archive utility which allows to extract files from a few archive formats and needs to be installed as separate package. $ yum install cpio. Combined with the rpm2cpio (8) utility, which comes pre-installed aspart of
SET THE ILO PASSWORD FROM LINUX USING HPONCFG To load the xml file into the iLO, the hponcfg command with the “-f filename” option is used. The “-f” option instructs hponcfg to set Management Processor (iLO) configuration from “filename”. After the command has been executed successfully, the Administrator’s password is set to the new value. To find out aboutother settings
SELINUX ALLOW WEBSERVER TO SEND EMAIL As already shown in my Migrate WordPress site with minimal downtime article, SELinux provides predefined rulesets for some functionality. These can be enabled with boolean switches. The boolean switch to allow apache to send emails is called “httpd_can_sendmail”: $ setsebool -P httpd_can_sendmail=on. This command will enable the rulesto
LVM REMOVE PHYSICAL VOLUME FROM VOLUME GROUP LVM Remove physical volume from volume group. LVM provides flexibility to organize logical volumes without being bound to inflexible partitioning. If set-up correctly, the LVM can grow as the disk/raid might grow. To allow the LVM to grow, the block device needs to be added as a physical volume to LVM without any partitioning on it. SETUP AMAVISD-NEW WITH SPAMASSASSIN AND CLAMAV WITH In the here described setup, postfix passes the incoming mails on to amavisd-new. There, the emails get checked for viruses and spam. After the email is checked, it INSTALL HP PROLIANT MANAGEMENT UTILITIES This command will download the GPG-Key from the HP website and install it on the system in order for apt to verify the package signatures. To retrieve the package list containing the packages from the newly added repository, run the the following command as usual. $ apt-get update. With the package list loaded, the packages provided in the SDR CREATE GNUPG KEY WITH SUB-KEYS TO SIGN, ENCRYPT To start the guided process of creating a sub-key the command is “addkey”. After the passphrase is entered, the type of sub-key must be entered. For a signing key, the “ (4) RSA (sign only)” is used. The key size should match the size fitting on the smartcard or Yubikey. While GnuPG version 1 will ask for the passphrase at thebeginning
UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. FIND AND EXTRACT ONE FILE FROM RPM PACKAGE Option 1: cpio. Propably the more elegant way of extracting a file, at least in my opinion, is the use of cpio (1). Cpio is an archive utility which allows to extract files from a few archive formats and needs to be installed as separate package. $ yum install cpio. Combined with the rpm2cpio (8) utility, which comes pre-installed aspart of
MANAGE SSH-KEYS WITH THE SSH-AGENT Many webservices generate ssh keys to access their service. With the amount of services the number of SSH keys grows. To avoid dealing with the keys in the command line and the ssh_config(5), you can simply add the ssh-key to the local ssh-agent(1) to manage them.. The ssh-agent(1) is a program used to hold ssh private keys used to authenticate to remote systems via ssh SPLITTING UP AN SVN REPOSITORY The first step is quite simple but must be run directly on the machine where the repository is located. The command “svnadmin dump” requires direct access to the repository directory. svnadmin dump /path/to/repository/ >repository.dump. After that is finished, you will find the file ‘repository.dump’ containing a full dump of the RESTRICT SSH LOGIN USING SSH KEYS TO A PARTICULAR IP When you use the following option, you can restrict where a user is allowed to login from using the SSH-key. To do so, add the option shown below to the line of the SSH-key. If you need multiple options, they should be separated by a “,”. from="pattern-list". The IP addresses or hostnames can be specified as a list in the ‘from’pattern
SHOW NETWORK ROUTES ON MACOSX In OS X, to specify a route for network 10.0.0.0/24 to be routed to gateway 10.0.0.1 you use the following command. $ route -n add 10.0.0.0/24 10.0.0.1. But if you are on a Linux system you will have to use the following command to do the same: $ route -n add -net 10.0.0.0/24 gw 10.0.0.1. The syntax is very close to the syntax of OSX but it is
REMOVE FILES FROM GIT HISTORY Rewrite affected commits. Rewriting the history is done with “git filter-branch” by walking through the complete history. For each commit, filters are applied after which the changes are re-committed. The different filters allow modifying different parts of the commit. REMOVE STUCK EMAILS FROM POSTFIX MAIL QUEUE If a huge number of emails is clogging the mail queue, it makes sense to remove them manually from the queue. If there are only one or two emails which should be removed, you can just use their Queue ID from the mailq (1) output and delete them with the following command. $ postsuper -d CB7E5B0067 postsuper: CB7E5B0067: removed postsuper UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. CREATE GNUPG KEY WITH SUB-KEYS TO SIGN, ENCRYPTSEE MORE ON BLOG.TINNED-SOFTWARE.NET GENERATE PUBLIC SSH KEY FROM PRIVATE SSH KEY A lost SSH public-key or a web service generates an SSH key but does not provide the public-key part to you. What to do now? There is a solution for this situation. CHANGE SSH PORT IN CENTOS WITH SELINUX Since version 4 of CentOS, SELinux is providing an additional layer of security to the Linux distribution. As of SELinux in combination with sshd, changing the port or even listening on 2 ports is not as easy as just changing the sshd configuration file. INSTALL HP PROLIANT MANAGEMENT UTILITIES The HP ProLiant Support Pack (PSP) for Linux allows reading out hardware details from a HP ProLiant server. this set of tools can be used to read out hardware information, state and logs. FIND AND EXTRACT ONE FILE FROM RPM PACKAGE Extracting a configuration file (or any other single file) from a package which is not installed is not a standard operation on rpm based systems, but with the following few steps, a file can be extracted without installing the package on the system. LVM REMOVE PHYSICAL VOLUME FROM VOLUME GROUP The now unused physical volumes /dev/vdb1 and /dev/vdc1 can be removed from the lvm. To do so, the physical volume needs to be removed fromthe volume group.
SET THE ILO PASSWORD FROM LINUX USING HPONCFG No matter if you are looking for a way to manage the iLO settings from the Linux command line or just have lost or forgotten the iLO password, as long as you have access to the Linux system running on the server, HP’s management utilities allows you to configure the iLO even without knowing the password for it. SETUP AMAVISD-NEW WITH SPAMASSASSIN AND CLAMAV WITHCONFIGURE SPAMASSASSIN POSTFIXINSTALL SPAMASSASSIN UBUNTU POSTFIXPOSTFIX AND DOVECOTDEBIAN CLAMAVPOSTFIX CLAMAV CONFIG In the here described setup, postfix passes the incoming mails on to amavisd-new. There, the emails get checked for viruses and spam. After the email is checked, it SELINUX ALLOW WEBSERVER TO SEND EMAIL When Wordpress tries to send email and you see "your host may have disabled the mail() function" it might be that SELinux is blocking it. Here is how to enable it. UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. CREATE GNUPG KEY WITH SUB-KEYS TO SIGN, ENCRYPTSEE MORE ON BLOG.TINNED-SOFTWARE.NET GENERATE PUBLIC SSH KEY FROM PRIVATE SSH KEY A lost SSH public-key or a web service generates an SSH key but does not provide the public-key part to you. What to do now? There is a solution for this situation. CHANGE SSH PORT IN CENTOS WITH SELINUX Since version 4 of CentOS, SELinux is providing an additional layer of security to the Linux distribution. As of SELinux in combination with sshd, changing the port or even listening on 2 ports is not as easy as just changing the sshd configuration file. INSTALL HP PROLIANT MANAGEMENT UTILITIES The HP ProLiant Support Pack (PSP) for Linux allows reading out hardware details from a HP ProLiant server. this set of tools can be used to read out hardware information, state and logs. FIND AND EXTRACT ONE FILE FROM RPM PACKAGE Extracting a configuration file (or any other single file) from a package which is not installed is not a standard operation on rpm based systems, but with the following few steps, a file can be extracted without installing the package on the system. LVM REMOVE PHYSICAL VOLUME FROM VOLUME GROUP The now unused physical volumes /dev/vdb1 and /dev/vdc1 can be removed from the lvm. To do so, the physical volume needs to be removed fromthe volume group.
SET THE ILO PASSWORD FROM LINUX USING HPONCFG No matter if you are looking for a way to manage the iLO settings from the Linux command line or just have lost or forgotten the iLO password, as long as you have access to the Linux system running on the server, HP’s management utilities allows you to configure the iLO even without knowing the password for it. SETUP AMAVISD-NEW WITH SPAMASSASSIN AND CLAMAV WITHCONFIGURE SPAMASSASSIN POSTFIXINSTALL SPAMASSASSIN UBUNTU POSTFIXPOSTFIX AND DOVECOTDEBIAN CLAMAVPOSTFIX CLAMAV CONFIG In the here described setup, postfix passes the incoming mails on to amavisd-new. There, the emails get checked for viruses and spam. After the email is checked, it SELINUX ALLOW WEBSERVER TO SEND EMAIL When Wordpress tries to send email and you see "your host may have disabled the mail() function" it might be that SELinux is blocking it. Here is how to enable it. UNDERSTAND THE BASICS OF RRDTOOL TO CREATE A SIMPLE GRAPH rrdtool is a powerful tool to store time series data and create graphs. It is very easy to create your first simple graph. This how-to will show the quickest way to generating your first graphs while explaining the options used. CREATE GNUPG KEY WITH SUB-KEYS TO SIGN, ENCRYPT Generating the random data needed for the key generation might take a long time. To speed up the process, use the rngd(8) to feed random data into the random number pool of the kernel. This can be done by installing the rng-tools package. # Debian / Ubuntu $ sudo apt-get install rng-tools # RedHat / CentOS $ yum install rng-tools FIND AND EXTRACT ONE FILE FROM RPM PACKAGE Extracting a configuration file (or any other single file) from a package which is not installed is not a standard operation on rpm based systems, but with the following few steps, a file can be extracted without installing the package on the system. INSTALL HP PROLIANT MANAGEMENT UTILITIES The HP ProLiant Support Pack (PSP) for Linux allows reading out hardware details from a HP ProLiant server. this set of tools can be used to read out hardware information, state and logs. MANAGE SSH-KEYS WITH THE SSH-AGENT Many webservices generate ssh keys to access their service. With the amount of services the number of SSH keys grows. To avoid dealing with the keys in the command line and the ssh_config(5), you can simply add the ssh-key to the local ssh-agent(1) to manage them.. The ssh-agent(1) is a program used to hold ssh private keys used to authenticate to remote systems via ssh RESTRICT SSH LOGIN USING SSH KEYS TO A PARTICULAR IP The SSH connection to your server is one of the most important way of accessing and managing your server, because of this, it is a target for any attacker that wants access to your server. REMOVE FILES FROM GIT HISTORY Rewrite affected commits. Rewriting the history is done with “git filter-branch” by walking through the complete history. For each commit, filters are applied after which the changes are re-committed. The different filters allow modifying different parts of the commit. SHOW NETWORK ROUTES ON MACOSX When working with Linux you get used to the way Linux is handling things. But when you switch from Linux to Mac OS X you notice that things are handled differently. One of these differences I came across recently. Its about the way you read out the routes you currently havecurrently active.
SPLITTING UP AN SVN REPOSITORY When I was creating my SVN repository I was lazy and created just one repository for all my projects. This was easy to administrate and to use; only one repository to configure with user names and passwords, only one URL to remember, but over time this repository has grown, and at some point the whole thing has got quite messy. REMOVE STUCK EMAILS FROM POSTFIX MAIL QUEUE Sometimes mails queue up in the postfix mail queue for some reason, maybe the destination mailserver does not exist or some emails have a recipient address that is incorrect.Home
* Tinned-Mail
*
* News
* History
* Download
* Screenshots
* Requirements
* References
* Tinned-Bug
*
* History
* Download
* Screenshots
* Requirements
* Tinned-RFC
*
* Download
* Screenshots
* Requirements
* Demo
* Tinned-TreeNotes
*
* History
* Download
* Screenshots
* Requirements
* Roadmap
* Demo (read only)
* PHP-Liphono
*
* Download
* Requirements
* Shell Scripts
*
* Simple-Backup
* Directory-Transfer* Tunnel-Manager
* Mailserver-Test
* Tinned-Software Blog* Privacy Policy
* Contact
* Partner & Support
*
*
TINNED-SOFTWARE
At the beginning we searched for a small and easy program fitting our needs but without a lot of requirements. Because we couldn't find such a program, we developed it by ourselves. The resulting program has little requirements and provides as many features as possible combined with an easy and comfortable user interface. In this spirit ... Have fun with our program set and help us to enhance it with your ideas.TINNED-MAIL
It is our first php project, designed to need as less requirements as possible providing as much features and comfort as possible. It offers many features to manage your mails from everywhere without taking care of the environment, operating system, browser or installed add-on's.TINNED-BUG
A low requirement bug tracking system written in php. With this program you can manage all you bugs, errors, changes and new ideas of all your different projects.TINNED-RFC
A small and simple rfc document converter. It presents each rfc text document as an html page with links to the referenced rfc documents and links in the table of contents for easy navigation through thedocuments.
TINNED-TREENOTES
A webbased application to store notes and text sniplets in a hirachically structured database. Its main functionality is similar to applications like TreeDBNotes, JreePad or TreePad. The database uses the well known sqlite database.PHP-LIBPHONO
A PHP library used for E.164 phone number normalization. It is intended to be a mall, fast way to work with telephone numbers. The library allows an input number to be converted into a variety ofdifferent formats.
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0