Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://emutalk.net
Are you over 18 and want to see adult content?
A complete backup of https://countryman.com
Are you over 18 and want to see adult content?
A complete backup of https://4sonrus.com
Are you over 18 and want to see adult content?

A complete backup of https://playboyrussia.com
Are you over 18 and want to see adult content?
A complete backup of https://cialisviagraonline.com
Are you over 18 and want to see adult content?

A complete backup of https://refrapide.com
Are you over 18 and want to see adult content?

A complete backup of https://overstuffedlife.com
Are you over 18 and want to see adult content?

A complete backup of https://anniesnoms.com
Are you over 18 and want to see adult content?

A complete backup of https://geocv.com
Are you over 18 and want to see adult content?
A complete backup of https://profi-forex.by
Are you over 18 and want to see adult content?

A complete backup of https://sildenafilreg.com
Are you over 18 and want to see adult content?
A complete backup of https://coie.com.au
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of https://prestonbailey.com
Are you over 18 and want to see adult content?
A complete backup of https://studium.at
Are you over 18 and want to see adult content?
A complete backup of https://ligna.de
Are you over 18 and want to see adult content?
A complete backup of https://adkernel.com
Are you over 18 and want to see adult content?

A complete backup of https://getakka.net
Are you over 18 and want to see adult content?
A complete backup of https://madden-school.com
Are you over 18 and want to see adult content?

A complete backup of https://ytjajx.com
Are you over 18 and want to see adult content?
A complete backup of https://worldhepatitisday.org
Are you over 18 and want to see adult content?

A complete backup of https://agrotimes.ua
Are you over 18 and want to see adult content?
A complete backup of https://cafebazaar.ir
Are you over 18 and want to see adult content?

A complete backup of https://rohama.org
Are you over 18 and want to see adult content?
A complete backup of https://knomobags.com
Are you over 18 and want to see adult content?
Text
accounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. SPYCLOUD | TAKE ACTION BEFORE CRIMINALS DO SpyCloud uses cookies and similar technologies to ensure the functionality of our site, recognize repeat visits and preferences, and measure the effectiveness of our campaigns and site content.SPYCLOUD API
Power Your Products with SpyCloud Data. Partner with the industry leader in breach data recovery. SpyCloud provides product teams with fast, easy access to the world’s most comprehensive breach database, enabling you to create offerings that protect your consumers and bring them to market quickly.. By integrating SpyCloud data into dark web monitoring, identity theft, security, and payments WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.ATO PREVENTION
Immediately after a breach, attackers keep stolen credentials contained to a small group of associates while they monetize stolen data, often engaging in highly targeted, manual account takeover attempts against high-value accounts. Once the attackers finally allow the credentials to leak to a broader criminal audience, often 18 to 24 months after the initial breach, advanced crimeware makes WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is. PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW Password security is a persistent challenge stemming from password reuse but can be solved with SpyCloud automated account takeover prevention solutions. WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Account takeover attempts may be highly targeted, particularly early in the breach timeline, making early detection critical. The earlier username and password breaches are flagged, the sooner action can be taken to force a password reset. SIMPLIFY NIST PASSWORD GUIDELINES WITH SPYCLOUD ACTIVE To help organizations mitigate the risk posed by users’ bad password habits, the National Institute of Standards and Technology (NIST) designed a set of password guidelines with human behavior in mind. SPYCLOUD | PREVENT ACCOUNT TAKEOVERSIGN INWHAT WE OFFEROUR DATACOMPANYBECOME A PARTNERRESOURCES SpyCloud helps businesses prevent account takeover and fraud stemming from stolen credentials. We secure billions of employee & consumeraccounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. SPYCLOUD | TAKE ACTION BEFORE CRIMINALS DO SpyCloud uses cookies and similar technologies to ensure the functionality of our site, recognize repeat visits and preferences, and measure the effectiveness of our campaigns and site content.SPYCLOUD API
Power Your Products with SpyCloud Data. Partner with the industry leader in breach data recovery. SpyCloud provides product teams with fast, easy access to the world’s most comprehensive breach database, enabling you to create offerings that protect your consumers and bring them to market quickly.. By integrating SpyCloud data into dark web monitoring, identity theft, security, and payments WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.ATO PREVENTION
Immediately after a breach, attackers keep stolen credentials contained to a small group of associates while they monetize stolen data, often engaging in highly targeted, manual account takeover attempts against high-value accounts. Once the attackers finally allow the credentials to leak to a broader criminal audience, often 18 to 24 months after the initial breach, advanced crimeware makes WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is. PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW Password security is a persistent challenge stemming from password reuse but can be solved with SpyCloud automated account takeover prevention solutions. WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Account takeover attempts may be highly targeted, particularly early in the breach timeline, making early detection critical. The earlier username and password breaches are flagged, the sooner action can be taken to force a password reset. SIMPLIFY NIST PASSWORD GUIDELINES WITH SPYCLOUD ACTIVE To help organizations mitigate the risk posed by users’ bad password habits, the National Institute of Standards and Technology (NIST) designed a set of password guidelines with human behavior in mind. SPYCLOUD | TAKE ACTION BEFORE CRIMINALS DO SpyCloud uses cookies and similar technologies to ensure the functionality of our site, recognize repeat visits and preferences, and measure the effectiveness of our campaigns and site content. DARK WEB DATA PARTNERSHIPS Human Intelligence and Rock-Solid Data. SpyCloud offers the most comprehensive, cleansed data available to make your product effective at mitigating the harm that can be caused by exposed credentials and empowering your customer to take immediate action if a breach isdiscovered.
WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Account takeover attempts may be highly targeted, particularly early in the breach timeline, making early detection critical. The earlier username and password breaches are flagged, the sooner action can be taken to force a password reset. 2020 ANNUAL CREDENTIAL EXPOSURE REPORT (1) More data than ever available to criminals. 2019 was a record year for cybercriminals. During the first half of the year alone, data breaches increased 54 percent, compared to the first half of 2018.In line with that early 2019 statistic, our researchers observed a noticeable uptick in the amount of data available on the criminal underground over the last year; anecdotally, they noticed SPYCLOUD | LEADERSHIP TEAM & BOARD OF DIRECTORS Our team consists of seasoned information security veterans hailing from Fortune 500 companies, threat intelligence vendors, and the U.S. Department of Defense. BREAKING DOWN THE SOLARWINDS SUPPLY CHAIN ATTACK 1. Compromise While the initial entrypoint that attackers used to gain a foothold within SolarWinds’ network is still under investigation, media outlets and security experts have speculated that it may have been an exposed server, unpatched software, or even simple account takeover using password spraying or stolen credentials.Once inside, the attackers were able to modify the build process HOW TO PREVENT ACCOUNT TAKEOVER Stopping Account Takeover. Account Takeover, or ATO, is a term that has become all too familiar. Credentials exposed in 3rd party breaches are now routinely used by criminals to perpetrate fraud, steal intellectual property and sell it on underground markets. NEW NIST GUIDELINES ACKNOWLEDGE WE’RE ONLY HUMAN Passwords need not be hard to remember. They just need to be hard to guess. NIST sets forth new guidelines to make creating strong passwords a bit easier. OUR PERSPECTIVE ON THE 'COLLECTION' COMBO LISTS February 2021 Update: A few major combo lists have been re-released as the COMB combo list.This appears to be a sorted and deduped version of previously leaked combo lists, not new information. That said, this is a good reminder that old data can still be useful to criminals; threat actors are no doubt running credential stuffing attacks with the COMB list, so any accounts using the sameBOB LYLE | SPYCLOUD
Bob brings over 25 years of technology industry experience to SpyCloud’s leadership team. With a background in the device security and IP licensing spaces, he leads SpyCloud’s efforts to engage with key market verticals, including telecommunications and e-commerce, to best serve enterprises and consumers globally and protect them from account takeover (ATO). SPYCLOUD | PREVENT ACCOUNT TAKEOVERSIGN INWHAT WE OFFEROUR DATACOMPANYBECOME A PARTNERRESOURCES SpyCloud helps businesses prevent account takeover and fraud stemming from stolen credentials. We secure billions of employee & consumeraccounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.SPYCLOUD API
SpyCloud provides product teams with fast, easy access to the world’s most comprehensive breach database, enabling you to create offerings that protect your consumers and bring them to market quickly. By integrating SpyCloud data into dark web monitoring, identity theft, security, and payments solutions, you can acceleratecustomer
SPYCLOUD | LEADERSHIP TEAM & BOARD OF DIRECTORS The SpyCloud Team. Our team consists of seasoned information security veterans hailing from Fortune 500 companies, threat intelligence vendors, and the U.S. Department of Defense. We’ve dealt with cyber crime of all types and are confident that our solutions and vast dataset are the foundation of your proactive defense.ATO PREVENTION
Criminals frequently exploit their illicit access by making fraudulent purchases, stealing sensitive data, or moving laterally within a target organization. SpyCloud’s ATO prevention solutions can help you protect your employees and consumers from account takeover by alerting you to stolen passwords before criminals have a chance to usethem.
PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW A password policy best practice is to follow the latest NIST password guidelines, which call for enterprises to check for “commonly-used, expected, or compromised” passwords that make account takeover easy for criminals. Security leaders can enforce NIST guidelines using the built-in controls in SpyCloud Active Directory Guardian to prevent WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Dark Web Monitoring Is Not Enough. The “dark web” refers to the section of the internet that requires additional privacy support from visitors that can be provided by services like Tor and I2P. Entities (including websites) within the “dark web” are known as hidden services, and due to the access requirements for these services, theyCASSIO MELLO
Cassio Mello. Cassio has more than twenty-five years of experience in security, fraud and identity, technology, financial services, and management consulting. He is passionate about developing the growth of a team and business through a creative and intentional approach. Prior to joining SpyCloud, Cassio was the Chief Strategy Officer at SIMPLIFY NIST PASSWORD GUIDELINES WITH SPYCLOUD ACTIVE Read this solution brief to understand the benefits of using SpyCloud to align with NIST password guidelines: Reduce your team’s workload with “set it and forget it” automation. Stay ahead of criminals with early access to breach data. Protect your organization from Account Takeover (ATO) attacks. SPYCLOUD | PREVENT ACCOUNT TAKEOVERSIGN INWHAT WE OFFEROUR DATACOMPANYBECOME A PARTNERRESOURCES SpyCloud helps businesses prevent account takeover and fraud stemming from stolen credentials. We secure billions of employee & consumeraccounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.SPYCLOUD API
SpyCloud provides product teams with fast, easy access to the world’s most comprehensive breach database, enabling you to create offerings that protect your consumers and bring them to market quickly. By integrating SpyCloud data into dark web monitoring, identity theft, security, and payments solutions, you can acceleratecustomer
SPYCLOUD | LEADERSHIP TEAM & BOARD OF DIRECTORS The SpyCloud Team. Our team consists of seasoned information security veterans hailing from Fortune 500 companies, threat intelligence vendors, and the U.S. Department of Defense. We’ve dealt with cyber crime of all types and are confident that our solutions and vast dataset are the foundation of your proactive defense.ATO PREVENTION
Criminals frequently exploit their illicit access by making fraudulent purchases, stealing sensitive data, or moving laterally within a target organization. SpyCloud’s ATO prevention solutions can help you protect your employees and consumers from account takeover by alerting you to stolen passwords before criminals have a chance to usethem.
PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW A password policy best practice is to follow the latest NIST password guidelines, which call for enterprises to check for “commonly-used, expected, or compromised” passwords that make account takeover easy for criminals. Security leaders can enforce NIST guidelines using the built-in controls in SpyCloud Active Directory Guardian to prevent WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Dark Web Monitoring Is Not Enough. The “dark web” refers to the section of the internet that requires additional privacy support from visitors that can be provided by services like Tor and I2P. Entities (including websites) within the “dark web” are known as hidden services, and due to the access requirements for these services, theyCASSIO MELLO
Cassio Mello. Cassio has more than twenty-five years of experience in security, fraud and identity, technology, financial services, and management consulting. He is passionate about developing the growth of a team and business through a creative and intentional approach. Prior to joining SpyCloud, Cassio was the Chief Strategy Officer at SIMPLIFY NIST PASSWORD GUIDELINES WITH SPYCLOUD ACTIVE Read this solution brief to understand the benefits of using SpyCloud to align with NIST password guidelines: Reduce your team’s workload with “set it and forget it” automation. Stay ahead of criminals with early access to breach data. Protect your organization from Account Takeover (ATO) attacks. SPYCLOUD | TAKE ACTION BEFORE CRIMINALS DO Take Action Before Criminals Do. After a data breach, criminals quickly monetize the data, often by using stolen credentials to gain easy access to consumer accounts and corporate systems. If your employees, consumers, or third-parties have credentials or PII exposed in a data breach, they are at high risk of account takeover fraud.SPYCLOUD API
Power Your Products with SpyCloud Data. Partner with the industry leader in breach data recovery. SpyCloud provides product teams with fast, easy access to the world’s most comprehensive breach database, enabling you to create offerings that protect your consumers and bring them to market quickly.. By integrating SpyCloud data into dark web monitoring, identity theft, security, and payments DARK WEB DATA PARTNERSHIPS With monthly ingests of ~1B breach assets, SpyCloud is continually adding valuable data that is immediately available to you. We are the only ones who crack passwords and update our data sets with real-time data straight from the dark web. Develop your solutions with the bestdata possible.
ONE FOR THE MONEY, TWO FOR THE SHOW, $4.4M FOR THE According to Bloomberg, the attack last month on Colonial Pipeline – the largest fuel pipeline in the U.S. – was “the result of a single compromised password.”On April 29, attackers gained access into the company’s networks through an employee’s virtual private network account. The employee’s password was discovered in a batch of leaked passwords available on the dark web, which BREAKING DOWN THE SOLARWINDS SUPPLY CHAIN ATTACK Breaking Down the SolarWinds Supply Chain Attack. When the public became aware of an advanced persistent threat (APT) responsible for compromising the SolarWinds Orion software supply chain in December 2020, experts were quick to warn it would likely be years – maybe decades – before the fallout could be fully accounted for.SPYCLOUD | LOGIN
Login Please enter your email address and password below. Email.Password
SIMPLIFY NIST PASSWORD GUIDELINES WITH SPYCLOUD ACTIVE Read this solution brief to understand the benefits of using SpyCloud to align with NIST password guidelines: Reduce your team’s workload with “set it and forget it” automation. Stay ahead of criminals with early access to breach data. Protect your organization from Account Takeover (ATO) attacks. WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is. HOW TO PREVENT ACCOUNT TAKEOVER Stopping Account Takeover. Account Takeover, or ATO, is a term that has become all too familiar. Credentials exposed in 3rd party breaches are now routinely used by criminals to perpetrate fraud, steal intellectual property and sell it on underground markets.BOB LYLE | SPYCLOUD
Bob brings over 25 years of technology industry experience to SpyCloud’s leadership team. With a background in the device security and IP licensing spaces, he leads SpyCloud’s efforts to engage with key market verticals, including telecommunications and e-commerce, to best serve enterprises and consumers globally and protect them from account takeover (ATO). SPYCLOUD | PREVENT ACCOUNT TAKEOVERSIGN INWHAT WE OFFEROUR DATACOMPANYBECOME A PARTNERRESOURCES SpyCloud helps businesses prevent account takeover and fraud stemming from stolen credentials. We secure billions of employee & consumeraccounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. DARK WEB DATA PARTNERSHIPS With monthly ingests of ~1B breach assets, SpyCloud is continually adding valuable data that is immediately available to you. We are the only ones who crack passwords and update our data sets with real-time data straight from the dark web. Develop your solutions with the bestdata possible.
SPYCLOUD API
SpyCloud provides product teams with fast, easy access to the world’s most comprehensive breach database, enabling you to create offerings that protect your consumers and bring them to market quickly. By integrating SpyCloud data into dark web monitoring, identity theft, security, and payments solutions, you can acceleratecustomer
PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW A password policy best practice is to follow the latest NIST password guidelines, which call for enterprises to check for “commonly-used, expected, or compromised” passwords that make account takeover easy for criminals. Security leaders can enforce NIST guidelines using the built-in controls in SpyCloud Active Directory Guardian to prevent WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Dark Web Monitoring Is Not Enough. The “dark web” refers to the section of the internet that requires additional privacy support from visitors that can be provided by services like Tor and I2P. Entities (including websites) within the “dark web” are known as hidden services, and due to the access requirements for these services, they HOW TO PREVENT ACCOUNT TAKEOVER Stopping Account Takeover. Account Takeover, or ATO, is a term that has become all too familiar. Credentials exposed in 3rd party breaches are now routinely used by criminals to perpetrate fraud, steal intellectual property and sell it on underground markets.BOB LYLE | SPYCLOUD
Bob brings over 25 years of technology industry experience to SpyCloud’s leadership team. With a background in the device security and IP licensing spaces, he leads SpyCloud’s efforts to engage with key market verticals, including telecommunications and e-commerce, to best serve enterprises and consumers globally and protect them from account takeover (ATO). WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is. SPYCLOUD | PRIVACY POLICY SpyCloud is the leader in account takeover and fraud prevention, with solutions backed by the world’s largest database of recovered stolen credentials and PII. SPYCLOUD | PREVENT ACCOUNT TAKEOVERSIGN INWHAT WE OFFEROUR DATACOMPANYBECOME A PARTNERRESOURCES SpyCloud helps businesses prevent account takeover and fraud stemming from stolen credentials. We secure billions of employee & consumeraccounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. DARK WEB DATA PARTNERSHIPS With monthly ingests of ~1B breach assets, SpyCloud is continually adding valuable data that is immediately available to you. We are the only ones who crack passwords and update our data sets with real-time data straight from the dark web. Develop your solutions with the bestdata possible.
SPYCLOUD API
SpyCloud provides product teams with fast, easy access to the world’s most comprehensive breach database, enabling you to create offerings that protect your consumers and bring them to market quickly. By integrating SpyCloud data into dark web monitoring, identity theft, security, and payments solutions, you can acceleratecustomer
PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW A password policy best practice is to follow the latest NIST password guidelines, which call for enterprises to check for “commonly-used, expected, or compromised” passwords that make account takeover easy for criminals. Security leaders can enforce NIST guidelines using the built-in controls in SpyCloud Active Directory Guardian to prevent WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Dark Web Monitoring Is Not Enough. The “dark web” refers to the section of the internet that requires additional privacy support from visitors that can be provided by services like Tor and I2P. Entities (including websites) within the “dark web” are known as hidden services, and due to the access requirements for these services, they HOW TO PREVENT ACCOUNT TAKEOVER Stopping Account Takeover. Account Takeover, or ATO, is a term that has become all too familiar. Credentials exposed in 3rd party breaches are now routinely used by criminals to perpetrate fraud, steal intellectual property and sell it on underground markets.BOB LYLE | SPYCLOUD
Bob brings over 25 years of technology industry experience to SpyCloud’s leadership team. With a background in the device security and IP licensing spaces, he leads SpyCloud’s efforts to engage with key market verticals, including telecommunications and e-commerce, to best serve enterprises and consumers globally and protect them from account takeover (ATO). WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is. SPYCLOUD | PRIVACY POLICY SpyCloud is the leader in account takeover and fraud prevention, with solutions backed by the world’s largest database of recovered stolen credentials and PII. SPYCLOUD | TAKE ACTION BEFORE CRIMINALS DO Take Action Before Criminals Do. After a data breach, criminals quickly monetize the data, often by using stolen credentials to gain easy access to consumer accounts and corporate systems. If your employees, consumers, or third-parties have credentials or PII exposed in a data breach, they are at high risk of account takeover fraud. SPYCLOUD | WHAT WE OFFER SpyCloud offers powerful solutions to prevent online fraud by stopping account takeover (ATO) attacks. Our solutions enable enterprises to validate logins against the world’s largest database of credentials and PII recovered from third-party breaches, reset exposed passwords, and trust that employees, consumers, and vendors logging in aren ONE FOR THE MONEY, TWO FOR THE SHOW, $4.4M FOR THE According to Bloomberg, the attack last month on Colonial Pipeline – the largest fuel pipeline in the U.S. – was “the result of a single compromised password.”On April 29, attackers gained access into the company’s networks through an employee’s virtual private network account. The employee’s password was discovered in a batch of leaked passwords available on the dark web, which WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.SPYCLOUD CAREERS
SpyCloud is a fast-paced, growing cybersecurity company that’s driven to make the internet a safer place. SpyCloud is used by 4 of the Fortune 10, as well as some of the most well-known ecommerce, financial, telecommunications, and tech companies in the world. We’ve been winning awards since day 1, and Gartner recently named usa 2020
SPYCLOUD | LOGIN
Login Please enter your email address and password below. Email.Password
WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is. WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Dark Web Monitoring Is Not Enough. The “dark web” refers to the section of the internet that requires additional privacy support from visitors that can be provided by services like Tor and I2P. Entities (including websites) within the “dark web” are known as hidden services, and due to the access requirements for these services, they SIMPLIFY NIST PASSWORD GUIDELINES WITH SPYCLOUD ACTIVE Read this solution brief to understand the benefits of using SpyCloud to align with NIST password guidelines: Reduce your team’s workload with “set it and forget it” automation. Stay ahead of criminals with early access to breach data. Protect your organization from Account Takeover (ATO) attacks. NEW NIST GUIDELINES ACKNOWLEDGE WE’RE ONLY HUMAN In contrast, the new guidelines recommend that passwords should be “easy to remember” but “hard to guess.”. According to the new guidance, usability and security go hand-in-hand. In short, the new NIST guidance recommends the following for passwords: A minimum of eight characters and a maximum length of at least 64 characters. SPYCLOUD | PREVENT ACCOUNT TAKEOVERSIGN INWHAT WE OFFEROUR DATACOMPANYBECOME A PARTNERRESOURCES SpyCloud helps businesses prevent account takeover and fraud stemming from stolen credentials. We secure billions of employee & consumeraccounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. SPYCLOUD | TAKE ACTION BEFORE CRIMINALS DO Take Action Before Criminals Do. After a data breach, criminals quickly monetize the data, often by using stolen credentials to gain easy access to consumer accounts and corporate systems. If your employees, consumers, or third-parties have credentials or PII exposed in a data breach, they are at high risk of account takeover fraud. DARK WEB DATA PARTNERSHIPS With monthly ingests of ~1B breach assets, SpyCloud is continually adding valuable data that is immediately available to you. We are the only ones who crack passwords and update our data sets with real-time data straight from the dark web. Develop your solutions with the bestdata possible.
WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.ATO PREVENTION
Criminals frequently exploit their illicit access by making fraudulent purchases, stealing sensitive data, or moving laterally within a target organization. SpyCloud’s ATO prevention solutions can help you protect your employees and consumers from account takeover by alerting you to stolen passwords before criminals have a chance to usethem.
WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Dark Web Monitoring Is Not Enough. The “dark web” refers to the section of the internet that requires additional privacy support from visitors that can be provided by services like Tor and I2P. Entities (including websites) within the “dark web” are known as hidden services, and due to the access requirements for these services, they PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW A password policy best practice is to follow the latest NIST password guidelines, which call for enterprises to check for “commonly-used, expected, or compromised” passwords that make account takeover easy for criminals. Security leaders can enforce NIST guidelines using the built-in controls in SpyCloud Active Directory Guardian to prevent WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is.BOB LYLE | SPYCLOUD
Bob brings over 25 years of technology industry experience to SpyCloud’s leadership team. With a background in the device security and IP licensing spaces, he leads SpyCloud’s efforts to engage with key market verticals, including telecommunications and e-commerce, to best serve enterprises and consumers globally and protect them from account takeover (ATO). SPYCLOUD | PREVENT ACCOUNT TAKEOVERSIGN INWHAT WE OFFEROUR DATACOMPANYBECOME A PARTNERRESOURCES SpyCloud helps businesses prevent account takeover and fraud stemming from stolen credentials. We secure billions of employee & consumeraccounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. SPYCLOUD | TAKE ACTION BEFORE CRIMINALS DO Take Action Before Criminals Do. After a data breach, criminals quickly monetize the data, often by using stolen credentials to gain easy access to consumer accounts and corporate systems. If your employees, consumers, or third-parties have credentials or PII exposed in a data breach, they are at high risk of account takeover fraud. DARK WEB DATA PARTNERSHIPS With monthly ingests of ~1B breach assets, SpyCloud is continually adding valuable data that is immediately available to you. We are the only ones who crack passwords and update our data sets with real-time data straight from the dark web. Develop your solutions with the bestdata possible.
WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.ATO PREVENTION
Criminals frequently exploit their illicit access by making fraudulent purchases, stealing sensitive data, or moving laterally within a target organization. SpyCloud’s ATO prevention solutions can help you protect your employees and consumers from account takeover by alerting you to stolen passwords before criminals have a chance to usethem.
WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGH Dark Web Monitoring Is Not Enough. The “dark web” refers to the section of the internet that requires additional privacy support from visitors that can be provided by services like Tor and I2P. Entities (including websites) within the “dark web” are known as hidden services, and due to the access requirements for these services, they PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW A password policy best practice is to follow the latest NIST password guidelines, which call for enterprises to check for “commonly-used, expected, or compromised” passwords that make account takeover easy for criminals. Security leaders can enforce NIST guidelines using the built-in controls in SpyCloud Active Directory Guardian to prevent WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is.BOB LYLE | SPYCLOUD
Bob brings over 25 years of technology industry experience to SpyCloud’s leadership team. With a background in the device security and IP licensing spaces, he leads SpyCloud’s efforts to engage with key market verticals, including telecommunications and e-commerce, to best serve enterprises and consumers globally and protect them from account takeover (ATO).SPYCLOUD PRODUCTS
SpyCloud is on a mission to disrupt the cybercriminal economy by preventing account takeover and reducing online fraud. Account Takeover (ATO) attacks have become an extremely lucrative business for cybercriminals, and the use of weak or stolen credentials remains the #1 hacking technique. Criminals steal credentials in third-partybreaches
ONE FOR THE MONEY, TWO FOR THE SHOW, $4.4M FOR THE According to Bloomberg, the attack last month on Colonial Pipeline – the largest fuel pipeline in the U.S. – was “the result of a single compromised password.”On April 29, attackers gained access into the company’s networks through an employee’s virtual private network account. The employee’s password was discovered in a batch of leaked passwords available on the dark web, which WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.SPYCLOUD API
SpyCloud provides product teams with fast, easy access to the world’s most comprehensive breach database, enabling you to create offerings that protect your consumers and bring them to market quickly. By integrating SpyCloud data into dark web monitoring, identity theft, security, and payments solutions, you can acceleratecustomer
SPYCLOUD | LEADERSHIP TEAM & BOARD OF DIRECTORS The SpyCloud Team. Our team consists of seasoned information security veterans hailing from Fortune 500 companies, threat intelligence vendors, and the U.S. Department of Defense. We’ve dealt with cyber crime of all types and are confident that our solutions and vast dataset are the foundation of your proactive defense. SIMPLIFY NIST PASSWORD GUIDELINES WITH SPYCLOUD ACTIVE Read this solution brief to understand the benefits of using SpyCloud to align with NIST password guidelines: Reduce your team’s workload with “set it and forget it” automation. Stay ahead of criminals with early access to breach data. Protect your organization from Account Takeover (ATO) attacks.SPYCLOUD | LOGIN
Login Please enter your email address and password below. Email.Password
HOW TO PREVENT ACCOUNT TAKEOVER Stopping Account Takeover. Account Takeover, or ATO, is a term that has become all too familiar. Credentials exposed in 3rd party breaches are now routinely used by criminals to perpetrate fraud, steal intellectual property and sell it on underground markets. WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is. NEW NIST GUIDELINES ACKNOWLEDGE WE’RE ONLY HUMAN In contrast, the new guidelines recommend that passwords should be “easy to remember” but “hard to guess.”. According to the new guidance, usability and security go hand-in-hand. In short, the new NIST guidance recommends the following for passwords: A minimum of eight characters and a maximum length of at least 64 characters. SPYCLOUD | PREVENT ACCOUNT TAKEOVERSIGN INWHAT WE OFFEROUR DATACOMPANYBECOME A PARTNERRESOURCES SpyCloud helps businesses prevent account takeover and fraud stemming from stolen credentials. We secure billions of employee & consumeraccounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. SPYCLOUD | TAKE ACTION BEFORE CRIMINALS DOSPYCLOUD AUSTINSPYCLOUD GLASSDOORSPYCLOUD PRICINGSPYCLOUD REVIEWSPYCLOUD SCAMSPYCLOUD STOCK Take Action Before Criminals Do. After a data breach, criminals quickly monetize the data, often by using stolen credentials to gain easy access to consumer accounts and corporate systems. If your employees, consumers, or third-parties have credentials or PII exposed in a data breach, they are at high risk of account takeover fraud. DARK WEB DATA PARTNERSHIPS With monthly ingests of ~1B breach assets, SpyCloud is continually adding valuable data that is immediately available to you. We are the only ones who crack passwords and update our data sets with real-time data straight from the dark web. Develop your solutions with the bestdata possible.
WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.ATO PREVENTION
Criminals frequently exploit their illicit access by making fraudulent purchases, stealing sensitive data, or moving laterally within a target organization. SpyCloud’s ATO prevention solutions can help you protect your employees and consumers from account takeover by alerting you to stolen passwords before criminals have a chance to usethem.
WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGHFREE WEB MONITORINGWEB MONITOR TOOLWEB PAGE MONITORING TOOLS Dark Web Monitoring Is Not Enough. The “dark web” refers to the section of the internet that requires additional privacy support from visitors that can be provided by services like Tor and I2P. Entities (including websites) within the “dark web” are known as hidden services, and due to the access requirements for these services, they PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW A password policy best practice is to follow the latest NIST password guidelines, which call for enterprises to check for “commonly-used, expected, or compromised” passwords that make account takeover easy for criminals. Security leaders can enforce NIST guidelines using the built-in controls in SpyCloud Active Directory Guardian to prevent WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is.BOB LYLE | SPYCLOUD
Bob brings over 25 years of technology industry experience to SpyCloud’s leadership team. With a background in the device security and IP licensing spaces, he leads SpyCloud’s efforts to engage with key market verticals, including telecommunications and e-commerce, to best serve enterprises and consumers globally and protect them from account takeover (ATO). SPYCLOUD | PREVENT ACCOUNT TAKEOVERSIGN INWHAT WE OFFEROUR DATACOMPANYBECOME A PARTNERRESOURCES SpyCloud helps businesses prevent account takeover and fraud stemming from stolen credentials. We secure billions of employee & consumeraccounts worldwide.
ABOUT SPYCLOUD
Early Data Recovery. SpyCloud is able to access breached records within hours or days of the breach occurring and share it with customers before it is used to cause harm, typically months or even years before it becomes available anywhere else. SPYCLOUD | TAKE ACTION BEFORE CRIMINALS DOSPYCLOUD AUSTINSPYCLOUD GLASSDOORSPYCLOUD PRICINGSPYCLOUD REVIEWSPYCLOUD SCAMSPYCLOUD STOCK Take Action Before Criminals Do. After a data breach, criminals quickly monetize the data, often by using stolen credentials to gain easy access to consumer accounts and corporate systems. If your employees, consumers, or third-parties have credentials or PII exposed in a data breach, they are at high risk of account takeover fraud. DARK WEB DATA PARTNERSHIPS With monthly ingests of ~1B breach assets, SpyCloud is continually adding valuable data that is immediately available to you. We are the only ones who crack passwords and update our data sets with real-time data straight from the dark web. Develop your solutions with the bestdata possible.
WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.ATO PREVENTION
Criminals frequently exploit their illicit access by making fraudulent purchases, stealing sensitive data, or moving laterally within a target organization. SpyCloud’s ATO prevention solutions can help you protect your employees and consumers from account takeover by alerting you to stolen passwords before criminals have a chance to usethem.
WHAT IS DARK WEB MONITORING? AND WHY IT'S NOT ENOUGHFREE WEB MONITORINGWEB MONITOR TOOLWEB PAGE MONITORING TOOLS Dark Web Monitoring Is Not Enough. The “dark web” refers to the section of the internet that requires additional privacy support from visitors that can be provided by services like Tor and I2P. Entities (including websites) within the “dark web” are known as hidden services, and due to the access requirements for these services, they PASSWORD SECURITY GUIDELINES: EVERYTHING YOU NEED TO KNOW A password policy best practice is to follow the latest NIST password guidelines, which call for enterprises to check for “commonly-used, expected, or compromised” passwords that make account takeover easy for criminals. Security leaders can enforce NIST guidelines using the built-in controls in SpyCloud Active Directory Guardian to prevent WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is.BOB LYLE | SPYCLOUD
Bob brings over 25 years of technology industry experience to SpyCloud’s leadership team. With a background in the device security and IP licensing spaces, he leads SpyCloud’s efforts to engage with key market verticals, including telecommunications and e-commerce, to best serve enterprises and consumers globally and protect them from account takeover (ATO).SPYCLOUD PRODUCTS
SpyCloud is on a mission to disrupt the cybercriminal economy by preventing account takeover and reducing online fraud. Account Takeover (ATO) attacks have become an extremely lucrative business for cybercriminals, and the use of weak or stolen credentials remains the #1 hacking technique. Criminals steal credentials in third-partybreaches
WHAT IS ACCOUNT TAKEOVER (ATO)? ACCOUNT TAKEOVER FRAUD Targeted Account Takeover Attacks. What: Highly effective, difficult to detect manual attacks like phishing, social engineering, SIM swapping, extortion, blackmail. When: Occur early in the breach timeline, usually in the first 18-24 months after the breach.During this time, criminals keep the stolen data within a small group that monetizes the credentials before selling them on the dark web.SPYCLOUD API
SpyCloud provides product teams with fast, easy access to the world’s most comprehensive breach database, enabling you to create offerings that protect your consumers and bring them to market quickly. By integrating SpyCloud data into dark web monitoring, identity theft, security, and payments solutions, you can acceleratecustomer
SPYCLOUD | LEADERSHIP TEAM & BOARD OF DIRECTORS The SpyCloud Team. Our team consists of seasoned information security veterans hailing from Fortune 500 companies, threat intelligence vendors, and the U.S. Department of Defense. We’ve dealt with cyber crime of all types and are confident that our solutions and vast dataset are the foundation of your proactive defense. SIMPLIFY NIST PASSWORD GUIDELINES WITH SPYCLOUD ACTIVE Read this solution brief to understand the benefits of using SpyCloud to align with NIST password guidelines: Reduce your team’s workload with “set it and forget it” automation. Stay ahead of criminals with early access to breach data. Protect your organization from Account Takeover (ATO) attacks. HOW TO PREVENT ACCOUNT TAKEOVER Stopping Account Takeover. Account Takeover, or ATO, is a term that has become all too familiar. Credentials exposed in 3rd party breaches are now routinely used by criminals to perpetrate fraud, steal intellectual property and sell it on underground markets.SPYCLOUD CAREERS
SpyCloud is a fast-paced, growing cybersecurity company that’s driven to make the internet a safer place. SpyCloud is used by 4 of the Fortune 10, as well as some of the most well-known ecommerce, financial, telecommunications, and tech companies in the world. We’ve been winning awards since day 1, and Gartner recently named usa 2020
SPYCLOUD | LOGIN
Login Please enter your email address and password below. Email.Password
WHAT IS CORPORATE ACCOUNT TAKEOVER AND WHAT CAN YOU DO TO Multi-factor authentication is an effective extra step companies can take to make sure the person logging into an app, system or network is who they say they are. There’s only one problem: 63 percent of companies say employees won’t use it. It adds friction to the login process and employees avoid it. Some don’t even know what it is. NEW NIST GUIDELINES ACKNOWLEDGE WE’RE ONLY HUMAN In contrast, the new guidelines recommend that passwords should be “easy to remember” but “hard to guess.”. According to the new guidance, usability and security go hand-in-hand. In short, the new NIST guidance recommends the following for passwords: A minimum of eight characters and a maximum length of at least 64 characters.* Sign in
_Check Your Exposure_ _Request a Demo_* What We Offer__
*
*
*
WHAT WE OFFER
Powerful, easy-to-use solutions to prevent account takeover and thwartonline fraud.
*
_Request a Demo _ Learn More About What We Offer__*
* Solutions
* Account Takeover Solutions Reset stolen passwords before criminals can use them to defraud your users or access sensitive corporate data. * Fraud Investigations Draw on decades-worth of digital breadcrumbs to locate, unmask, and catch criminals as they attempt to defraud your business and yourcustomers.
* Third Party Risk Management Monitor your critical third party relationships for supply chain breach exposures that could endanger your enterprise.*
View All Solutions__*
* Products
* Consumer ATO Prevention * Employee ATO Prevention * Active Directory Guardian * Fraud Investigations * Third Party Insight* SpyCloud API
*
View All Products__
* Our Data__
* Our Data
* Request a Data Test* Company__
* Overview
* Targeted Attacks
* Our Team
* News & Press
* Events
* Careers
* Become A Partner__* Become A Partner
* Technology Partners* Channel Partners
* Our Data
* Resources__
* Blog
* Case Studies
* Research Reports
* Solution Briefs
* Webinars
* Whitepapers
* Contact__
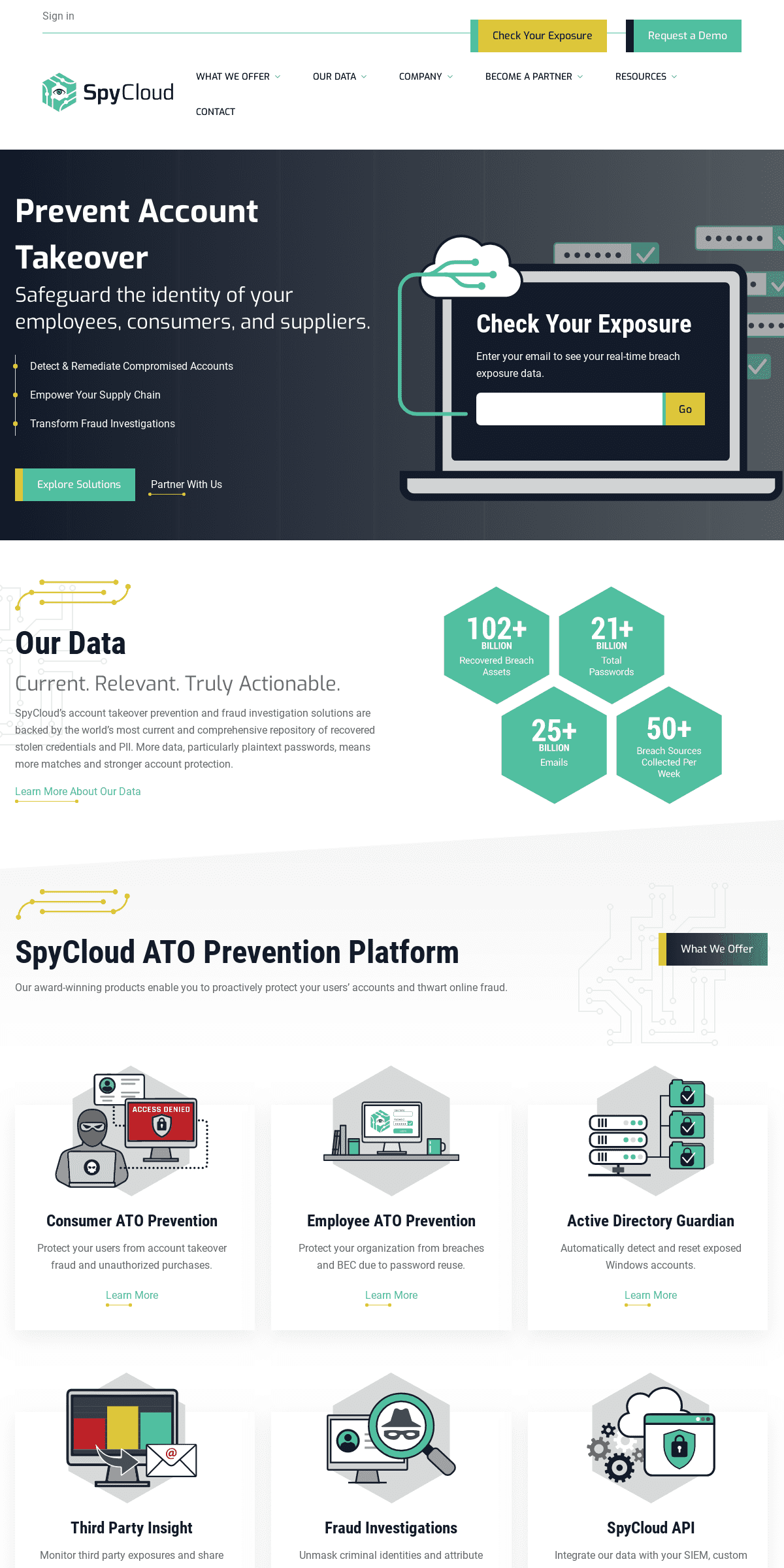
PREVENT ACCOUNT TAKEOVER Safeguard the identity of your employees, consumers, and suppliers. * Detect & Remediate Compromised Accounts * Empower Your Supply Chain * Transform Fraud Investigations _ Explore Solutions _ Partner With Us __CHECK YOUR EXPOSURE
Enter your email to see your real-time breach exposure data.OUR DATA
Current. Relevant. Truly Actionable. SpyCloud’s account takeover prevention and fraud investigation solutions are backed by the world’s most current and comprehensive repository of recovered stolen credentials and PII. More data, particularly plaintext passwords, means more matches and strongeraccount protection.
Learn More About Our Data __ SPYCLOUD ATO PREVENTION PLATFORM Our award-winning products enable you to proactively protect your users’ accounts and thwart online fraud._What We Offer_
CONSUMER ATO PREVENTION Protect your users from account takeover fraud and unauthorizedpurchases.
Learn More__
EMPLOYEE ATO PREVENTION Protect your organization from breaches and BEC due to password reuse.Learn More__
ACTIVE DIRECTORY GUARDIAN Automatically detect and reset exposed Windows accounts.Learn More__
THIRD PARTY INSIGHT
Monitor third party exposures and share data to aid in remediation.Learn More__
FRAUD INVESTIGATIONS Unmask criminal identities and attribute crimes to specificindividuals.
Learn More__
SPYCLOUD API
Integrate our data with your SIEM, custom app, or security offering.Learn More__
SPYCLOUD IS UNLIKE ANY OTHER CYBERSECURITY FIRM.Learn More__
WHO USES SPYCLOUD?
Hundreds of global enterprises, including 4 of the Fortune 10, are using to SpyCloud to prevent account takeover without having to hire additional intel staff. They’re seeing ROI in a matter of days. Check out some of our success stories: _See All Case Studies_Higher Education
Technology
Ecommerce
Chemical
Higher Education
OKLAHOMA UNIVERSITY
Higher Education
“In a matter of hours, 1,000 accounts were secured. Using SpyCloud and the ingenuity of our student employees, we are legitimately preventing bad guys from compromising accounts.” Read the Case Study__Technology
AUTOMATTIC
Technology“Now that we have SpyCloud, we can protect hundreds of millions of people and prevent them from choosing passwords that have already been exposed.” Read the Case Study__Ecommerce
TOP 10 TRAVEL BOOKING SITEEcommerce
“Using the SpyCloud data, we discover anywhere from 3,000 to 11,000 direct matches per hour. Every one of those exposed accounts could have led to account takeover.” Read the Case Study__Chemical
BUCKMAN
Chemical“The SpyCloud data is more specific and actionable than any other solution we’ve found, giving us employee, account-level and source detail we need to mitigate the threat and take immediateaction.”
Read the Case Study__FEATURED RESOURCES
_See All Resources_
Report
2020 REPORT: BREACH EXPOSURE OF THE FORTUNE 1000 Our extensive 2020 report examines the breach exposure of Fortune 1000enterprises.
Read More
Webinar
I PUT A KEYLOGGER ON YOU, AND NOW YOU’RE MINE: WHAT CYBERCRIMINALS SEE WHEN THEY INFECT A HOST WITH MALWARE See malware from the criminal perspective, including how the data collected from infected machines gets monetized. Learn how to shield your organization from the damage caused by credential-stealingmalware.
Read More
Webinar
HOW CREDENTIAL STUFFING TOOLS ARE MADE Learn how credential stuffing works and get insights into the tools of the trade (including some very sophisticated custom Nintendo crimeware). Discover why stolen accounts that don’t have obvious monetary value can be profitable for cybercriminals.Read More
Stop exposures from becoming account breaches._Request a Demo_
SOLUTIONS
* Account Takeover Solutions * Business Email Compromise * Credential Stuffing * Dark Web Monitoring * NIST Password Screening * Online Fraud Detection* Password Security
* SIM Swapping
* VIP Monitoring
* Zero Trust
PRODUCTS
* Consumer ATO Prevention * Employee ATO Prevention * Active Directory Guardian * Fraud Investigations * Third Party Insight* SpyCloud API
RESOURCES
* Blog
* Case Studies
* Research Reports
* Solution Briefs
* Webinars
* Whitepapers
COMPANY
* Why SpyCloud
* Targeted Attacks
* Our Team
* News & Press
* Events
* Careers
* Contact
_Check Your Exposure_ _Request a Demo_* __
* __
* __
SPYCLOUD INC.
2130 S Congress Ave
Austin, Texas 78704
Call: 1-800-513-2502�2020 SpyCloud Inc.
All Rights Reserved
Terms | Privacy | Cookies* What We Offer
▼
* Solutions
▼
* Account Takeover Solutions Reset stolen passwords before criminals can use them to defraud your users or access sensitive corporate data. * Fraud Investigations Draw on decades-worth of digital breadcrumbs to locate, unmask, and catch criminals as they attempt to defraud your business and yourcustomers.
* Third Party Risk Management Monitor your critical third party relationships for supply chain breach exposures that could endanger your enterprise.* Products
▼
* Consumer ATO Prevention * Employee ATO Prevention * Active Directory Guardian * Fraud Investigations * Third Party Insight* SpyCloud API
* Our Data
▼
* Our Data
* Request a Data Test* Company
▼
* Overview
* Targeted Attacks
* Our Team
* News & Press
* Events
* Careers
* Become A Partner
▼
* Become A Partner
* Technology Partners* Channel Partners
* Our Data
* Resources
▼
* Blog
* Case Studies
* Research Reports
* Solution Briefs
* Webinars
* Whitepapers
* Contact
_Check Your Exposure_ _Request a Demo_Sign In
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0