Are you over 18 and want to see adult content?
More Annotations

A complete backup of www.veinsensor.pl
Are you over 18 and want to see adult content?
A complete backup of 131458934.keywordblocks.com
Are you over 18 and want to see adult content?

A complete backup of markkavanagh.com
Are you over 18 and want to see adult content?

A complete backup of azscers.000webhostapp.com
Are you over 18 and want to see adult content?

A complete backup of abc12.onesignal.com
Are you over 18 and want to see adult content?

A complete backup of sp-active.adsrvr.org
Are you over 18 and want to see adult content?

A complete backup of services.runescape.com-api.top
Are you over 18 and want to see adult content?
A complete backup of cb1.dev.rtb.owneriq.net
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of theweereview.com
Are you over 18 and want to see adult content?

A complete backup of geraardsbergen.be
Are you over 18 and want to see adult content?

A complete backup of handcraftedmodelships.com
Are you over 18 and want to see adult content?
A complete backup of pastoralninezyjuventud.org
Are you over 18 and want to see adult content?

A complete backup of blackandmissinginc.com
Are you over 18 and want to see adult content?
Text
SECURITYTRAILS
1. Krebs on Security. Krebs on Security is one of the most influential blogs in the field, and its author Brian Krebs has already been included in our list of 10 cybersecurity legends. Krebs is a well-known investigative journalist who covers computer security and cyber crime, earning himself many awards through the years; mostrecently, he was
DKIM: WHAT IS IT AND SHOULD YOU CONFIGURE IT? This is where DKIM, an established form of sender authentication, comes into play. DKIM, or DomainKeys Identified Mail, is an email authentication standard created to allow senders to connect to their domain with an email, through cryptographic authentication which, in turn, proves the legitimacy of said email to the receiver. COMMON CYBER SECURITY RISKS TO WATCH OUT FOR 1. No backup and recovery plan. Surprisingly or not, our followers did say that the lack of a backup and recovery plan is the number one risk for organizations today. Statistics support this claim, too: a survey of SMEs by Riverbank IT Management found that 46% of SMEs don’t have a backup and recovery plan, and for those that do have it, 23% have never actually tested it. RECON-NG: AN OPEN SOURCE RECONNAISSANCE TOOL The OSINT tools arsenal is now filled with more pieces of code that help “get things done” better, faster and more effectively than ever before. And Recon-ng, with its modular design, brings you a familiar way to operate a command line while its similar syntax to the Metasploit framework allows you to mount different purpose modules and configure them independently. TOP 16 NMAP COMMANDS TO SCAN REMOTE HOSTS 3. Scan specific ports or scan entire port ranges on a local or remote server. nmap -p 1-65535 localhost. In this example, we scanned all 65535 ports for our localhost computer. Nmap is able to scan all possible ports, but you can also scan specific ports, which will report faster results. See below: THE WORLD'S LARGEST REPOSITORY OF HISTORICAL DNS DATAPRODUCTSWHY USCUSTOMERSPRICINGBLOGSUPPORT The World's Largest Repository of Historical DNS data. The Total. Internet Inventory. Powerful tools for third-party risk, attack surface management, and total intel. Get your Free Attack Surface Report. Company Search. 30. Acquisitions. 3.2K. THE WORLD'S LARGEST REPOSITORY OF HISTORICAL DNS DATA The World's Largest Repository of historical DNS data. Data for security companies, researchers and teams who need to drill down, find suspicious changes toSECURITYTRAILS
1. Krebs on Security. Krebs on Security is one of the most influential blogs in the field, and its author Brian Krebs has already been included in our list of 10 cybersecurity legends. Krebs is a well-known investigative journalist who covers computer security and cyber crime, earning himself many awards through the years; mostrecently, he was
DKIM: WHAT IS IT AND SHOULD YOU CONFIGURE IT? This is where DKIM, an established form of sender authentication, comes into play. DKIM, or DomainKeys Identified Mail, is an email authentication standard created to allow senders to connect to their domain with an email, through cryptographic authentication which, in turn, proves the legitimacy of said email to the receiver. COMMON CYBER SECURITY RISKS TO WATCH OUT FOR 1. No backup and recovery plan. Surprisingly or not, our followers did say that the lack of a backup and recovery plan is the number one risk for organizations today. Statistics support this claim, too: a survey of SMEs by Riverbank IT Management found that 46% of SMEs don’t have a backup and recovery plan, and for those that do have it, 23% have never actually tested it. RECON-NG: AN OPEN SOURCE RECONNAISSANCE TOOL The OSINT tools arsenal is now filled with more pieces of code that help “get things done” better, faster and more effectively than ever before. And Recon-ng, with its modular design, brings you a familiar way to operate a command line while its similar syntax to the Metasploit framework allows you to mount different purpose modules and configure them independently. TOP 16 NMAP COMMANDS TO SCAN REMOTE HOSTS 3. Scan specific ports or scan entire port ranges on a local or remote server. nmap -p 1-65535 localhost. In this example, we scanned all 65535 ports for our localhost computer. Nmap is able to scan all possible ports, but you can also scan specific ports, which will report faster results. See below: THEHARVESTER: A CLASSIC OPEN SOURCE INTELLIGENCE TOOL theHarvester (purposely spelt with a lower-case ‘t’ at the beginning) is a commandline-based tool made by the team at Edge-Security. It is a Python-based tool meant to be used in the initial stages of an investigation by leveraging open source Intelligence ( OSINT) to help determine a company’s external threat landscape on the internet. FRONT-END SECURITY: 10 POPULAR TYPES OF ATTACKS AND BEST Top 10 Front-End Security Risks and Best Practices to Prevent Them. Let’s look at some popular front-end security issues, and how you can prevent them with the industry’s best practices. 1. Preventing cross-site scripting (XSS) attacks. XSS attacksSECURITYTRAILS
DMitry: Its name stands for Deepmagic Information Gathering Tool, and is one of the top terminal-based tools when it comes to intel reconnaissance tasks. It will allow you to get any available data from any host, such as subdomains, email addresses, open TOP 25 OSINT TOOLS FOR PENETRATION TESTING Without any doubt, it is a very good open source intelligence tool to gather all the possible technical details about any website. 7. Google Dorks. While investigating people or companies, a lot of IT security newbies forget the importance of using traditional search engines for recon and intel gathering. TOP 12 VULNERABLE WEBSITES FOR PENETRATION TESTING AND 1. bWAPP. Created by Malik Messelem, bWAPP (short for “buggy web application”) is a free and open source application that is, just as the name implies, deliberately vulnerable. It’s one of the best—if not the best—buggy websites available for practising and sharpening your hacking skills. Whether you’re a security enthusiastSECURITYTRAILS
Without any doubts, a pretty cool GUI interface for WPScan, which is the core scanner behind this tool. 5. FirstSiteGuide WP Scanner. This scanner is one of the best free online security scanners for Wordpress. It performs a big number of security checks to determine if your WP installation is vulnerable or not. LIST OF ALL CYBERSECURITY CONFERENCES TO ATTEND IN 2021 The most popular cybersecurity and infosec conferences in 2021. 1. DEF CON 29. Date: August 5–9, 2021. Location: Bally’s Las Vegas and Paris Las Vegas Las Vegas, Nevada, USA. It wasn’t hard to predict that DEF CON would be mentioned first—it’s the most famous and longest-running entry on the list. We are big fans of DEFCON,attending
THE EQUINIX ATTACK: UNDERSTANDING RANSOMWARE BEHAVIOUR The Equinix attack. According to an unknown source that reported to BleepingComputer, this attack was perpetrated by the infamous Netwalker ransomware. Despite this claim, we haven’t found any official statements about it. The source also shared that there was a message sent to Equinix with the usual ransom note as well as ascreenshot
PREVENTING DOMAIN HIJACKING 3. Always enable domain locking. Domain locking is a common security enhancement offered by all domain name registrars: it allows you to prevent unauthorized domain name transfers to another registrar. This is one of the oldest and most popular ways to protect domain names from hijacking activities.SECURITYTRAILS
Curl. One of the oldest and most classic Unix tools available for retrieving information from any website is the curl command ¹, which can also be used to extract data from any SSL certificate. In this case, there are a few ways to use it: curl -vvI https: //securitytrails.com. THE WORLD'S LARGEST REPOSITORY OF HISTORICAL DNS DATAPRODUCTSWHY USCUSTOMERSPRICINGBLOGSUPPORT The World's Largest Repository of Historical DNS data. The Total. Internet Inventory. Powerful tools for third-party risk, attack surface management, and total intel. Get your Free Attack Surface Report. Company Search. 30. Acquisitions. 3.2K. THE WORLD'S LARGEST REPOSITORY OF HISTORICAL DNS DATA The World's Largest Repository of historical DNS data. Data for security companies, researchers and teams who need to drill down, find suspicious changes toSECURITYTRAILS
1. Krebs on Security. Krebs on Security is one of the most influential blogs in the field, and its author Brian Krebs has already been included in our list of 10 cybersecurity legends. Krebs is a well-known investigative journalist who covers computer security and cyber crime, earning himself many awards through the years; mostrecently, he was
SECURITYTRAILS
DKIM: WHAT IS IT AND SHOULD YOU CONFIGURE IT? This is where DKIM, an established form of sender authentication, comes into play. DKIM, or DomainKeys Identified Mail, is an email authentication standard created to allow senders to connect to their domain with an email, through cryptographic authentication which, in turn, proves the legitimacy of said email to the receiver. RECON-NG: AN OPEN SOURCE RECONNAISSANCE TOOL The OSINT tools arsenal is now filled with more pieces of code that help “get things done” better, faster and more effectively than ever before. And Recon-ng, with its modular design, brings you a familiar way to operate a command line while its similar syntax to the Metasploit framework allows you to mount different purpose modules and configure them independently. TOP 16 NMAP COMMANDS TO SCAN REMOTE HOSTS 3. Scan specific ports or scan entire port ranges on a local or remote server. nmap -p 1-65535 localhost. In this example, we scanned all 65535 ports for our localhost computer. Nmap is able to scan all possible ports, but you can also scan specific ports, which will report faster results. See below: PREVENTING DOMAIN HIJACKING 3. Always enable domain locking. Domain locking is a common security enhancement offered by all domain name registrars: it allows you to prevent unauthorized domain name transfers to another registrar. This is one of the oldest and most popular ways to protect domain names from hijacking activities. TOP 10 CLOUD MIGRATION MISTAKES AND HOW TO AVOID THEM Some of the most common cloud security threats and risks are misconfigurations, insider threats, lack of IAM, exposure of dev and staging environments, poor regulatory compliance, insecure APIs, lack of visibility, and more. These threats might require non-traditional approaches when it comes to cloud environments. HOW TO FIND IP ADDRESSES OWNED BY A COMPANY One of the most traditional ways to get the IP address of a company is to use the ping command, which allows you to get the main IP address of the webserver behind the webpage. But that doesn’t give you the full company’s public network address range. It’s only a singleisolated IP.
THE WORLD'S LARGEST REPOSITORY OF HISTORICAL DNS DATAPRODUCTSWHY USCUSTOMERSPRICINGBLOGSUPPORT The World's Largest Repository of Historical DNS data. The Total. Internet Inventory. Powerful tools for third-party risk, attack surface management, and total intel. Get your Free Attack Surface Report. Company Search. 30. Acquisitions. 3.2K. THE WORLD'S LARGEST REPOSITORY OF HISTORICAL DNS DATA The World's Largest Repository of historical DNS data. Data for security companies, researchers and teams who need to drill down, find suspicious changes toSECURITYTRAILS
1. Krebs on Security. Krebs on Security is one of the most influential blogs in the field, and its author Brian Krebs has already been included in our list of 10 cybersecurity legends. Krebs is a well-known investigative journalist who covers computer security and cyber crime, earning himself many awards through the years; mostrecently, he was
SECURITYTRAILS
DKIM: WHAT IS IT AND SHOULD YOU CONFIGURE IT? This is where DKIM, an established form of sender authentication, comes into play. DKIM, or DomainKeys Identified Mail, is an email authentication standard created to allow senders to connect to their domain with an email, through cryptographic authentication which, in turn, proves the legitimacy of said email to the receiver. RECON-NG: AN OPEN SOURCE RECONNAISSANCE TOOL The OSINT tools arsenal is now filled with more pieces of code that help “get things done” better, faster and more effectively than ever before. And Recon-ng, with its modular design, brings you a familiar way to operate a command line while its similar syntax to the Metasploit framework allows you to mount different purpose modules and configure them independently. TOP 16 NMAP COMMANDS TO SCAN REMOTE HOSTS 3. Scan specific ports or scan entire port ranges on a local or remote server. nmap -p 1-65535 localhost. In this example, we scanned all 65535 ports for our localhost computer. Nmap is able to scan all possible ports, but you can also scan specific ports, which will report faster results. See below: PREVENTING DOMAIN HIJACKING 3. Always enable domain locking. Domain locking is a common security enhancement offered by all domain name registrars: it allows you to prevent unauthorized domain name transfers to another registrar. This is one of the oldest and most popular ways to protect domain names from hijacking activities. TOP 10 CLOUD MIGRATION MISTAKES AND HOW TO AVOID THEM Some of the most common cloud security threats and risks are misconfigurations, insider threats, lack of IAM, exposure of dev and staging environments, poor regulatory compliance, insecure APIs, lack of visibility, and more. These threats might require non-traditional approaches when it comes to cloud environments. HOW TO FIND IP ADDRESSES OWNED BY A COMPANY One of the most traditional ways to get the IP address of a company is to use the ping command, which allows you to get the main IP address of the webserver behind the webpage. But that doesn’t give you the full company’s public network address range. It’s only a singleisolated IP.
FRONT-END SECURITY: 10 POPULAR TYPES OF ATTACKS AND BEST Top 10 Front-End Security Risks and Best Practices to Prevent Them. Let’s look at some popular front-end security issues, and how you can prevent them with the industry’s best practices. 1. Preventing cross-site scripting (XSS) attacks. XSS attacksSECURITYTRAILS
Curl. One of the oldest and most classic Unix tools available for retrieving information from any website is the curl command ¹, which can also be used to extract data from any SSL certificate. In this case, there are a few ways to use it: curl -vvI https: //securitytrails.com. PREVENTING DOMAIN HIJACKING 3. Always enable domain locking. Domain locking is a common security enhancement offered by all domain name registrars: it allows you to prevent unauthorized domain name transfers to another registrar. This is one of the oldest and most popular ways to protect domain names from hijacking activities. LIST OF ALL CYBERSECURITY CONFERENCES TO ATTEND IN 2021 The most popular cybersecurity and infosec conferences in 2021. 1. DEF CON 29. Date: August 5–9, 2021. Location: Bally’s Las Vegas and Paris Las Vegas Las Vegas, Nevada, USA. It wasn’t hard to predict that DEF CON would be mentioned first—it’s the most famous and longest-running entry on the list. We are big fans of DEFCON,attending
THE EQUINIX ATTACK: UNDERSTANDING RANSOMWARE BEHAVIOUR The Equinix attack. According to an unknown source that reported to BleepingComputer, this attack was perpetrated by the infamous Netwalker ransomware. Despite this claim, we haven’t found any official statements about it. The source also shared that there was a message sent to Equinix with the usual ransom note as well as ascreenshot
SECURITYTRAILS
Without any doubts, a pretty cool GUI interface for WPScan, which is the core scanner behind this tool. 5. FirstSiteGuide WP Scanner. This scanner is one of the best free online security scanners for Wordpress. It performs a big number of security checks to determine if your WP installation is vulnerable or not. NEW FEATURE: FIND EVERY DOMAIN SOMEONE OWNS AUTOMATICALLY Step 1: Open up DNSTrails.com. Step 2: Search for any domain name, for example: godaddy.com. Step 3: After you get the results for the domain name, locate the Whois information block as you see below: Step 4: You will notice there is a phone number and email address associated with the domain name. Step 5: Click on the links at the right, you DNS ROOT SERVERS: WHAT ARE THEY AND IS THERE REALLY ONLY 13? Root servers, or DNS root servers, are name servers that are responsible for the functionality of the DNS as well as the entire Internet. They’re the first step in the name resolution of any domain name, meaning they translate domain names into IP addresses. The mapping of domain names to IP addresses works in a hierarchicalorder using DNS
HOW TO FIND IP ADDRESSES OWNED BY A COMPANY One of the most traditional ways to get the IP address of a company is to use the ping command, which allows you to get the main IP address of the webserver behind the webpage. But that doesn’t give you the full company’s public network address range. It’s only a singleisolated IP.
HOW TO PERFORM A NMAP VULNERABILITY SCAN USING NSE SCRIPTS The syntax we’ll be using is pretty simple, calling the script by using –script and specifying the vulners engine, as shown here: nmap --script nmap-vulners -sV 11 .22.33.44. If you want to target specific posts, you simply need to add -p80 at the end, and replace “80” with the port you want to scan. THE WORLD'S LARGEST REPOSITORY OF HISTORICAL DNS DATAPRODUCTSWHY USCUSTOMERSPRICINGBLOGSUPPORT The World's Largest Repository of Historical DNS data. The Total. Internet Inventory. Powerful tools for third-party risk, attack surface management, and total intel. Get your Free Attack Surface Report. Company Search. 30. Acquisitions. 3.2K. DKIM: WHAT IS IT AND SHOULD YOU CONFIGURE IT? This is where DKIM, an established form of sender authentication, comes into play. DKIM, or DomainKeys Identified Mail, is an email authentication standard created to allow senders to connect to their domain with an email, through cryptographic authentication which, in turn, proves the legitimacy of said email to the receiver.SECURITYTRAILS
1. Krebs on Security. Krebs on Security is one of the most influential blogs in the field, and its author Brian Krebs has already been included in our list of 10 cybersecurity legends. Krebs is a well-known investigative journalist who covers computer security and cyber crime, earning himself many awards through the years; mostrecently, he was
TOP 20 AND 200 MOST SCANNED PORTS IN THE CYBERSECURITYSEE MORE ONSECURITYTRAILS.COM
DNS ROOT SERVERS: WHAT ARE THEY AND IS THERE REALLY ONLY 13? Root servers, or DNS root servers, are name servers that are responsible for the functionality of the DNS as well as the entire Internet. They’re the first step in the name resolution of any domain name, meaning they translate domain names into IP addresses. The mapping of domain names to IP addresses works in a hierarchicalorder using DNS
THE TOP 5 DNS SERVERS FOR IMPROVING ONLINE PRIVACY & SECURITY 3. OpenDNS. Founded in 2005 and owned by Cisco since 2016, OpenDNS is a free, public and cloud-based service that provides DNS servers. It’s one of the most popular, but surprisingly, our Twitter poll showed it in third place. OpenDNS is a great choice for TOP 16 NMAP COMMANDS TO SCAN REMOTE HOSTS 3. Scan specific ports or scan entire port ranges on a local or remote server. nmap -p 1-65535 localhost. In this example, we scanned all 65535 ports for our localhost computer. Nmap is able to scan all possible ports, but you can also scan specific ports, which will report faster results. See below: PREVENTING DOMAIN HIJACKING 3. Always enable domain locking. Domain locking is a common security enhancement offered by all domain name registrars: it allows you to prevent unauthorized domain name transfers to another registrar. This is one of the oldest and most popular ways to protect domain names from hijacking activities. HOW TO FIND IP ADDRESSES OWNED BY A COMPANY One of the most traditional ways to get the IP address of a company is to use the ping command, which allows you to get the main IP address of the webserver behind the webpage. But that doesn’t give you the full company’s public network address range. It’s only a singleisolated IP.
HOW TO PERFORM A NMAP VULNERABILITY SCAN USING NSE SCRIPTS The syntax we’ll be using is pretty simple, calling the script by using –script and specifying the vulners engine, as shown here: nmap --script nmap-vulners -sV 11 .22.33.44. If you want to target specific posts, you simply need to add -p80 at the end, and replace “80” with the port you want to scan. THE WORLD'S LARGEST REPOSITORY OF HISTORICAL DNS DATAPRODUCTSWHY USCUSTOMERSPRICINGBLOGSUPPORT The World's Largest Repository of Historical DNS data. The Total. Internet Inventory. Powerful tools for third-party risk, attack surface management, and total intel. Get your Free Attack Surface Report. Company Search. 30. Acquisitions. 3.2K. DKIM: WHAT IS IT AND SHOULD YOU CONFIGURE IT? This is where DKIM, an established form of sender authentication, comes into play. DKIM, or DomainKeys Identified Mail, is an email authentication standard created to allow senders to connect to their domain with an email, through cryptographic authentication which, in turn, proves the legitimacy of said email to the receiver.SECURITYTRAILS
1. Krebs on Security. Krebs on Security is one of the most influential blogs in the field, and its author Brian Krebs has already been included in our list of 10 cybersecurity legends. Krebs is a well-known investigative journalist who covers computer security and cyber crime, earning himself many awards through the years; mostrecently, he was
TOP 20 AND 200 MOST SCANNED PORTS IN THE CYBERSECURITYSEE MORE ONSECURITYTRAILS.COM
DNS ROOT SERVERS: WHAT ARE THEY AND IS THERE REALLY ONLY 13? Root servers, or DNS root servers, are name servers that are responsible for the functionality of the DNS as well as the entire Internet. They’re the first step in the name resolution of any domain name, meaning they translate domain names into IP addresses. The mapping of domain names to IP addresses works in a hierarchicalorder using DNS
THE TOP 5 DNS SERVERS FOR IMPROVING ONLINE PRIVACY & SECURITY 3. OpenDNS. Founded in 2005 and owned by Cisco since 2016, OpenDNS is a free, public and cloud-based service that provides DNS servers. It’s one of the most popular, but surprisingly, our Twitter poll showed it in third place. OpenDNS is a great choice for TOP 16 NMAP COMMANDS TO SCAN REMOTE HOSTS 3. Scan specific ports or scan entire port ranges on a local or remote server. nmap -p 1-65535 localhost. In this example, we scanned all 65535 ports for our localhost computer. Nmap is able to scan all possible ports, but you can also scan specific ports, which will report faster results. See below: PREVENTING DOMAIN HIJACKING 3. Always enable domain locking. Domain locking is a common security enhancement offered by all domain name registrars: it allows you to prevent unauthorized domain name transfers to another registrar. This is one of the oldest and most popular ways to protect domain names from hijacking activities. HOW TO FIND IP ADDRESSES OWNED BY A COMPANY One of the most traditional ways to get the IP address of a company is to use the ping command, which allows you to get the main IP address of the webserver behind the webpage. But that doesn’t give you the full company’s public network address range. It’s only a singleisolated IP.
HOW TO PERFORM A NMAP VULNERABILITY SCAN USING NSE SCRIPTS The syntax we’ll be using is pretty simple, calling the script by using –script and specifying the vulners engine, as shown here: nmap --script nmap-vulners -sV 11 .22.33.44. If you want to target specific posts, you simply need to add -p80 at the end, and replace “80” with the port you want to scan. THE WORLD'S LARGEST REPOSITORY OF HISTORICAL DNS DATA The World's Largest Repository of historical DNS data. Data for security companies, researchers and teams who need to drill down, find suspicious changes to DNS PREVENTING DOMAIN HIJACKING 3. Always enable domain locking. Domain locking is a common security enhancement offered by all domain name registrars: it allows you to prevent unauthorized domain name transfers to another registrar. This is one of the oldest and most popular ways to protect domain names from hijacking activities. TOP 20 AND 200 MOST SCANNED PORTS IN THE CYBERSECURITY Top 200 most scanned ports. In the same way that we scanned the top 20 ports, you can literally request any port range from the available 65535 ports. So, if you want to get the full UDP and TCP top 200 ports, this can be achieved by simply running: nmap -sTU --top-ports 200 localhost -v -oG -.SECURITYTRAILS
Without any doubts, a pretty cool GUI interface for WPScan, which is the core scanner behind this tool. 5. FirstSiteGuide WP Scanner. This scanner is one of the best free online security scanners for Wordpress. It performs a big number of security checks to determine if your WP installation is vulnerable or not. RECON-NG: AN OPEN SOURCE RECONNAISSANCE TOOL The OSINT tools arsenal is now filled with more pieces of code that help “get things done” better, faster and more effectively than ever before. And Recon-ng, with its modular design, brings you a familiar way to operate a command line while its similar syntax to the Metasploit framework allows you to mount different purpose modules and configure them independently. WHAT IS REVERSE DNS? HOW TO PERFORM A REVERSE DNS LOOKUP? When it comes to cybersecurity investigations, every single point in your attack surface area counts, and that includes the so-called rDNS or reverse DNS records. which is often a forgotten key by new penetration testers and researchers.. Today we’re going to learn more about reverse DNS, what it is, what it’s used for, how to perform quick rDNS lookups from the terminal using several CYBER CRIME INVESTIGATION: TOOLS AND TECHNIQUES EXPLAINED Cyber Crime Investigation Tools and Techniques Explained. Reading time: 15 minutes. Investigating a crime scene is not an easy job. It requires years of study to learn how to deal with hard cases, and most importantly, get those cases resolved. This applies not only to real-world crime scenes, but also to those in the digital world. EXPLORING GOOGLE HACKING TECHNIQUES The following Google hacking techniques can help you fetch live camera web pages that are not restricted by IP. Here’s the dork to fetch various IP based cameras: inurl:top.htm inurl:currenttime. To find WebcamXP-based transmissions: intitle:"webcamXP 5". And another one WHAT IS BANNER GRABBING? BEST TOOLS AND TECHNIQUES EXPLAINED Active banner grabbing. This is the most popular type of banner grabbing, basically the act of sending packets to the remote host and waiting for their response to analyze the data. Active banner grabbing techniques involve opening a TCP (or similar) connection between an origin host and a remote host. It can be considered active, as your TYPES OF CYBERCRIME AND HOW TO PROTECT AGAINST THEM In plain English, cybercrime is crime committed on the Internet, on local networks, or even against isolated computers. It can affect any of your digital devices (including PCs, notebooks, smart TVs, tablets, smartphones, home electronic systems, etc). Cybercrime also refers to any activity where crime is committed using any computer system.Products
* __ API
* __ Feeds
* SurfaceBrowser
* __ Attack Surface ReductionWhy us
Pricing
Blog
Support
* __ FAQ
* __ API Docs
* __ API Integrations* __ Contact
Login
Signup for free
API Feeds ASR™
SurfaceBrowser Why
us Pricing Blog FAQ API Docs API Integrations Contact*
ATTACK
SURFACE
REDUCTION
Find known and unknown exposed data from any of your assets in seconds. Analyze weak network points on your attack surface and prevent threats before they become a real risk, thanks to our proactive monitoring services.Learn more
*
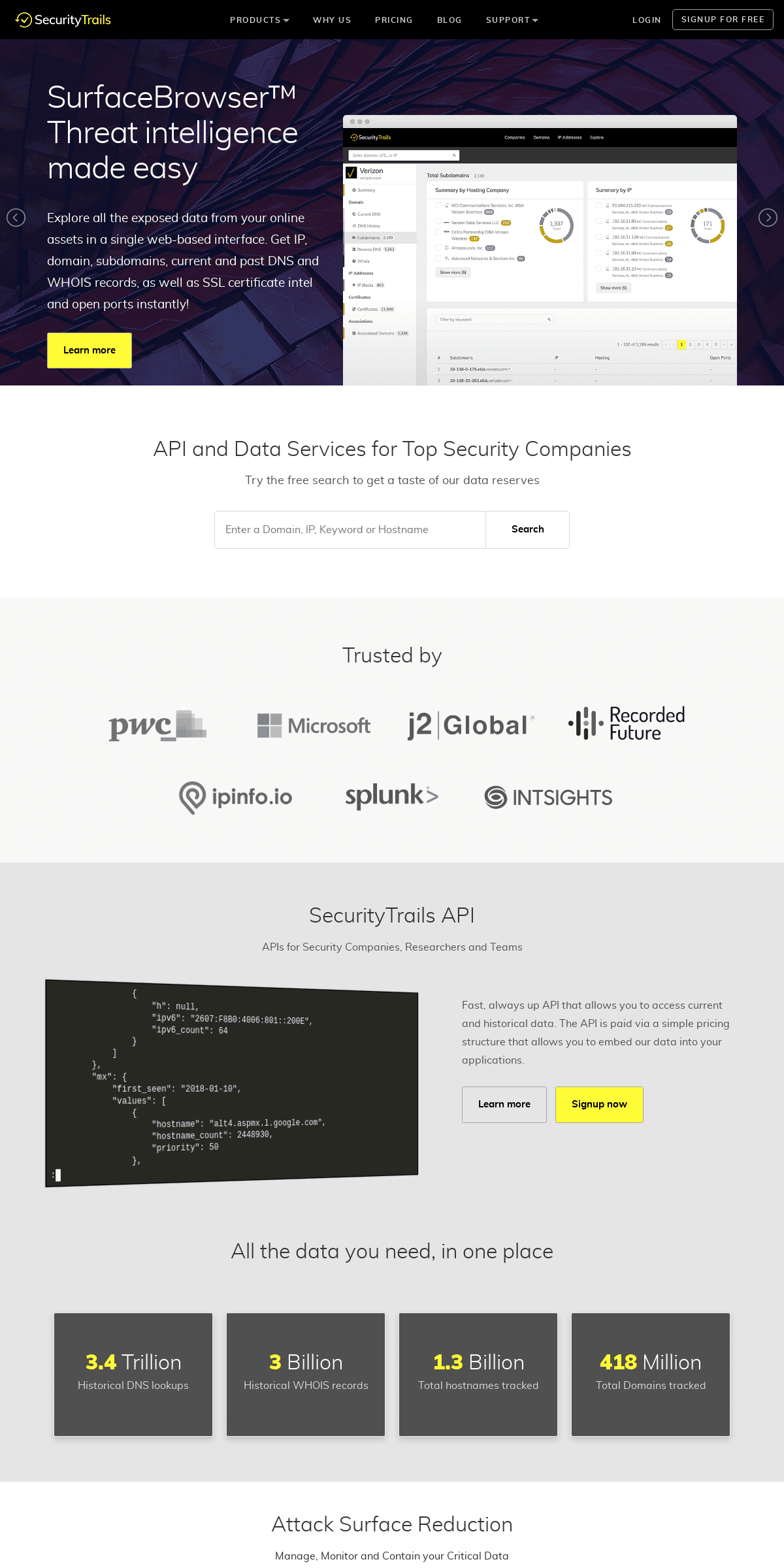
SURFACEBROWSER™ THREAT INTELLIGENCE MADE EASY Explore all the exposed data from your online assets in a single web-based interface. Get IP, domain, subdomains, current and past DNS and WHOIS records, as well as SSL certificate intel and open portsinstantly!
Learn more
*
SECURITY DATA FOR TOP SECURITY TEAMS AND COMPANIES Tap into a treasure-trove of cyber security gold for info you can’t find anywhere else. We’re proud to offer security analysts and developers the most current DNS and domain intel with our powerfulAPI.
Signup now Run A Free Search*
ATTACK
SURFACE
REDUCTION
Find known and unknown exposed data from any of your assets in seconds. Analyze weak network points on your attack surface and prevent threats before they become a real risk, thanks to our proactive monitoring services.Learn more
*
SURFACEBROWSER™ THREAT INTELLIGENCE MADE EASY Explore all the exposed data from your online assets in a single web-based interface. Get IP, domain, subdomains, current and past DNS and WHOIS records, as well as SSL certificate intel and open portsinstantly!
Learn more
API AND DATA SERVICES FOR TOP SECURITY COMPANIES Try the free search to get a taste of our data reservesSearch
TRUSTED BY
SECURITYTRAILS API
APIs for Security Companies, Researchers and Teams "hostname": "alt4.aspmx.l.google.com", "hostname_count": 2448930, "priority": 50 }, { "hostname": "alt3.aspmx.l.google.com", "hostname_count": 2517350, "priority": 40 }, { "hostname": "alt2.aspmx.l.google.com", "hostname_count": 7774606, "priority": 30 }, { :00:07-00:14
Fast, always up API that allows you to access current and historical data. The API is paid via a simple pricing structure that allows you to embed our data into your applications. Learn more Signup now ALL THE DATA YOU NEED, IN ONE PLACE3.4 TRILLION
Historical DNS lookups3 BILLION
Historical WHOIS records1.3 BILLION
Total hostnames tracked418 MILLION
Total Domains tracked Attack Surface Reduction Manage, Monitor and Contain your Critical Data As your organization infrastructure grows day by day, your attack surface becomes more difficult to manage. Attack Surface Reduction solves this problem. Get full control of all your online assets:* Find open ports
* Explore vulnerabilities* Build your IP map
* Perform a full domain enumeration * Discover all your subdomains * Extract SSL data from all your domainsLearn more
SurfaceBrowser
Security health from a distance Instantly click through the external internet surface area of any company from a single unified web interface. Discover all your exposed data before the bad guys do. Main features include: * DNS Time Machine™* Reverse IP data
* IP intelligence
* Full internet scans * SSL transparency logs * WhoWas™ smart WHOIS historyLearn more
Domain Intelligence Feeds High-quality domain feeds for data enrichment Our daily updated and curated domain, IP and DNS data feeds are available in CSV format or API and easily integrated into your ownapps.
Jump to the next level of cybersecurity feeds instantly. Includes full access to:* Port scans
* Domain attribution * List of all domains * List of subdomains* SPF + DMARC scans
* Certificate transparency logsLearn more
SEE WHAT OUR CUSTOMERS ARE SAYING ABOUT US "We spent a ton of time and effort building out our own domain lists, but we gave up when we found SecurityTrails – the data was better than anything else we've seen, and allowed us to focus on our coreproduct."
BEN DOWLING
IPINFO.IO
"SecurityTrails solves the headache of accurately mapping a company's footprint with data you can't find anywhere else. If you are a security analyst or developer, you will get tremendous value from the most current domain intel through their API."BILL LADD
RECORDEDFUTURE
"SecurityTrails is my source of truth when it comes to threat hunting and research. The speed of the API is crazy and the integrations with automation tools and SIEM tools makes it an easy choice."MICKEY PERRE
SPLUNK
GET STARTED NOW!
Use SecurityTrails API to fetch any domain and whois related data: Our easy to use API can help you enriching your datasets or adding value to your service. Signup for an API key×
7 DAYS. 49 DOLLARS. FULL ACCESS. 7-day trial gives you full access to all tools and features ofSurfaceBrowser.
__ SURFACEBROWSER™ Start 7-day trial for $49. Then $499/month I accept SecurityTrails'Terms of use .
You can cancel your subscription anytime. No contracts, nohidden charges.
PRODUCTS
DNS History
API
API Pricing
API Documentation
Feeds
Attack Surface ReductionCOMPANY
Blog __
Our Story
Careers
Press
Contact us
Product Manifesto
RESOURCES
Domain Stats
Integrations
Fortune 500 Domains
Developer Hub
Service Status
LATEST FROM OUR BLOG NEWAsset Discovery: Stay Ahead of Your Digital Fingerprint Top 30+ Most Popular Red Team Tools All Things Quantum - Quantum Security Series -Part 3 New
SurfaceBrowser™ Features: Company Activity & New AssociationsGOSINT: A
Framework for Collecting, Processing, and Exporting Indicators ofCompromise (IoC)
SecurityTrails © 2020·Privacy Policy ·Terms ofService ·DMCA
__ __
__
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0