Are you over 18 and want to see adult content?
More Annotations

A complete backup of www.model-kartei.de
Are you over 18 and want to see adult content?

A complete backup of dirtyhomeclips.com
Are you over 18 and want to see adult content?
A complete backup of sonovinhasbr.com
Are you over 18 and want to see adult content?

A complete backup of webcamsdolls.com
Are you over 18 and want to see adult content?
A complete backup of www.www.petticoated.com
Are you over 18 and want to see adult content?

A complete backup of www.www.millionairematch.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of championhomes.com
Are you over 18 and want to see adult content?

A complete backup of kismetswritings.com
Are you over 18 and want to see adult content?
A complete backup of collectif-lubrizol.org
Are you over 18 and want to see adult content?

A complete backup of americancollegeofphysicalmedicine.org
Are you over 18 and want to see adult content?
A complete backup of activemomsaz.com
Are you over 18 and want to see adult content?
Text
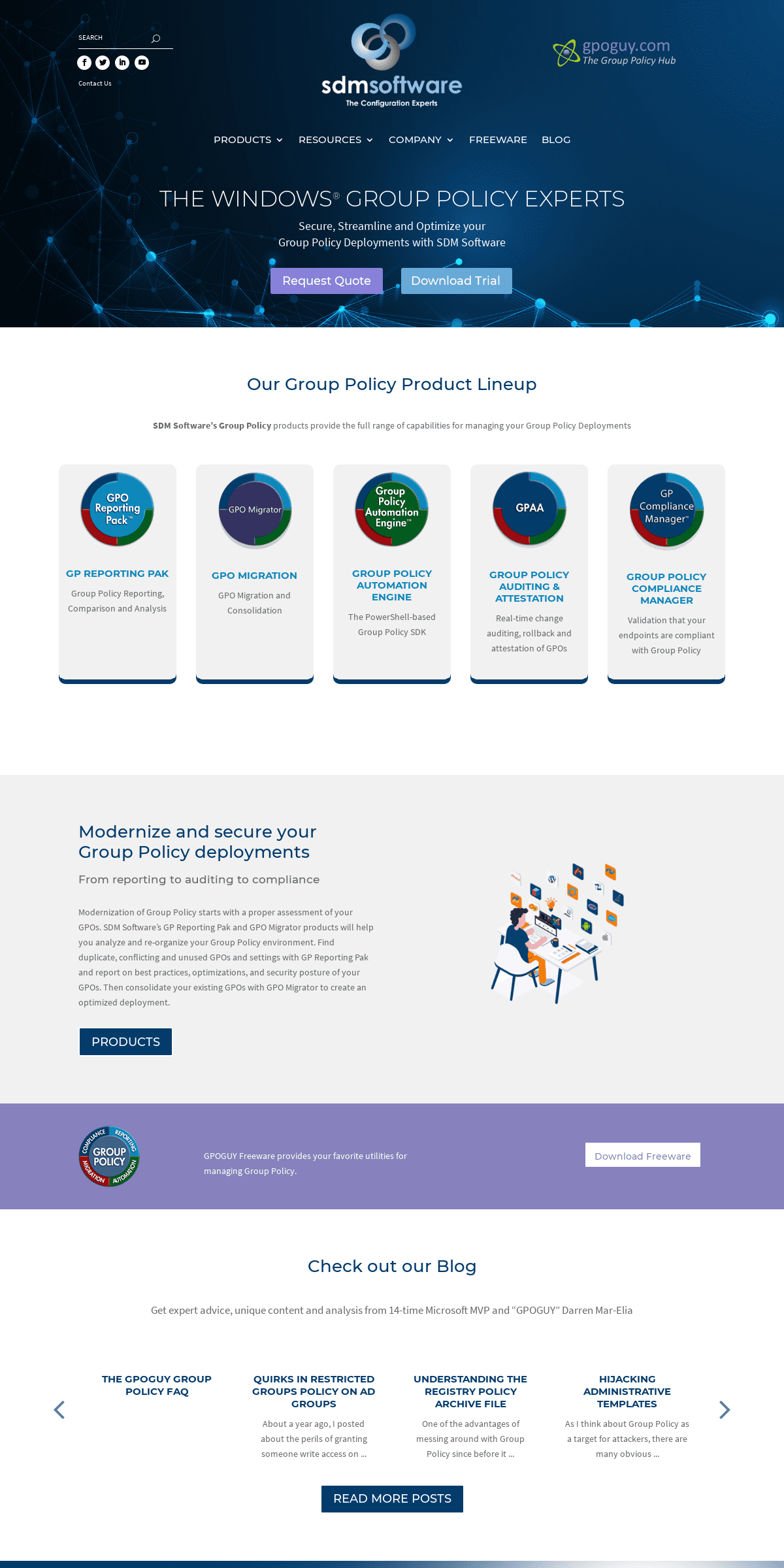
SDM SOFTWARE
SDM Software’s GP Reporting Pak and GPO Migrator products will help you analyze and re-organize your Group Policy environment. Find duplicate, conflicting and unused GPOs and settings with GP Reporting Pak and report on best practices, optimizations, and security posture of your GPOs. Then consolidate your existing GPOs with GPO Migrator to REMOVING EXTRA REGISTRY SETTINGS FROM GPOS Namely, I can use this syntax: Remove-GPRegistryValue -Name "OfficeDeployment" -Key
"HKCU\Software\Policies\Microsoft\Office\11.0\Word\Disable. dCmdBarItemsCheckBoxes". And by leaving off the -ValueName parameter, the cmdlet removes all entries under that key, within the GPO. This leaves me with quite a few less extra registry settings, as you DEALING WITH THE ACCOUNTEXPIRES DATE IN ACTIVE DIRECTORY Accessing this data from PowerShell is a useful technique to master. If you have yet to dive deep into dates it is time. Just one quick date scenario/comment in this post. In Working with the AccountExpires attribute in AD there is a strange experience that is not super intuitive. Not overly complex, just may have you shaking your head. UNDERSTANDING GROUP POLICY “TATTOOING” Policies & Preferences You’ve probably vaguely heard of registry tattooing as it relates to the old NT 4 system policy. Tattooing was the effect that you saw whenever you applied REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. FIND GROUP POLICY (GPO) SETTING CONFLICTS USING POWERSHELL The output of this command looks like that shown here: Finding Conflicting Group Policy Settings using GPO Exporter and PowerShell. As you can see in this listing, it becomes much easier to find conflicting settings when you can see exactly which GPO (s) contain a particular setting. Another cool by-product of this cmdlet is theability to find
EVALUATING OU MEMBERSHIP USING WMI FILTERS WMI Query for OU Membership. Note that the namespace field has to reflect the correct namespace, which is root\RSOP\Computer rather than the default root\cimV2. In addition, this query above: Select * From RSOP_Session Where SOM = 'OU=SDM,DC=cpandl,DC=com'. Evaluates to true if the computer processing the GPO that has this filter is in the WHAT DOES GROUP POLICY DO WHEN IT CAN’T CONTACT A DC During the core phase of processing, when the machine (or user) goes to resolve itself in AD, it will make 4 attempts (Windows 10) to contact a DC to get it’s account information. If it fails to do that, it will generate event ID 7320 in the GP Operations Event Log, as shown here: A client failing to find a DC during GP processing. HELPING WITH A SQL CE CHALLENGE USING HERE-STRINGS While working through a challenge I stumbled through a few interesting items that are worth jotting down. I’ve used both of these constructs before but I had to re-search for some assistance. GHOSTS IN THE GPO MACHINE–LOCAL SECURITY POLICY CHANGES ON But there are other ways to affect change to the local security policy outside of GP editor. In the simplest case, the good old command-line net.exe command can make changes to password policy. For example, if I run the following command on a DC: net accounts /minpwlen:9. This will change the minimum password length policy to 9 characters.SDM SOFTWARE
SDM Software’s GP Reporting Pak and GPO Migrator products will help you analyze and re-organize your Group Policy environment. Find duplicate, conflicting and unused GPOs and settings with GP Reporting Pak and report on best practices, optimizations, and security posture of your GPOs. Then consolidate your existing GPOs with GPO Migrator to REMOVING EXTRA REGISTRY SETTINGS FROM GPOS Namely, I can use this syntax: Remove-GPRegistryValue -Name "OfficeDeployment" -Key
"HKCU\Software\Policies\Microsoft\Office\11.0\Word\Disable. dCmdBarItemsCheckBoxes". And by leaving off the -ValueName parameter, the cmdlet removes all entries under that key, within the GPO. This leaves me with quite a few less extra registry settings, as you DEALING WITH THE ACCOUNTEXPIRES DATE IN ACTIVE DIRECTORY Accessing this data from PowerShell is a useful technique to master. If you have yet to dive deep into dates it is time. Just one quick date scenario/comment in this post. In Working with the AccountExpires attribute in AD there is a strange experience that is not super intuitive. Not overly complex, just may have you shaking your head. UNDERSTANDING GROUP POLICY “TATTOOING” Policies & Preferences You’ve probably vaguely heard of registry tattooing as it relates to the old NT 4 system policy. Tattooing was the effect that you saw whenever you applied REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. FIND GROUP POLICY (GPO) SETTING CONFLICTS USING POWERSHELL The output of this command looks like that shown here: Finding Conflicting Group Policy Settings using GPO Exporter and PowerShell. As you can see in this listing, it becomes much easier to find conflicting settings when you can see exactly which GPO (s) contain a particular setting. Another cool by-product of this cmdlet is theability to find
EVALUATING OU MEMBERSHIP USING WMI FILTERS WMI Query for OU Membership. Note that the namespace field has to reflect the correct namespace, which is root\RSOP\Computer rather than the default root\cimV2. In addition, this query above: Select * From RSOP_Session Where SOM = 'OU=SDM,DC=cpandl,DC=com'. Evaluates to true if the computer processing the GPO that has this filter is in the WHAT DOES GROUP POLICY DO WHEN IT CAN’T CONTACT A DC During the core phase of processing, when the machine (or user) goes to resolve itself in AD, it will make 4 attempts (Windows 10) to contact a DC to get it’s account information. If it fails to do that, it will generate event ID 7320 in the GP Operations Event Log, as shown here: A client failing to find a DC during GP processing. HELPING WITH A SQL CE CHALLENGE USING HERE-STRINGS While working through a challenge I stumbled through a few interesting items that are worth jotting down. I’ve used both of these constructs before but I had to re-search for some assistance. GHOSTS IN THE GPO MACHINE–LOCAL SECURITY POLICY CHANGES ON But there are other ways to affect change to the local security policy outside of GP editor. In the simplest case, the good old command-line net.exe command can make changes to password policy. For example, if I run the following command on a DC: net accounts /minpwlen:9. This will change the minimum password length policy to 9 characters. SDM SOFTWARE SUPPORT At SDM Software we strive to provide timely support to all of our customers. To open a support case with our team please email support@sdmsoftware.com. This ensures we are tracking the incident in our system and keeps us accountable. REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. UNDERSTANDING GROUP POLICY PRIVILEGE ESCALATION IN CVE Understanding Group Policy Privilege Escalation in CVE-2020-1317. Earlier this month, Microsoft released an advisory for CVE-2020-1317 which describes a privilege escalation vulnerability in Group Policy. This was further detailed by the discoverer of the vulnerability on the Cyberark website. The nature of this issue is interesting andworth
FIND ALL REGISTRY SETTINGS MANAGED IN A GPO Here is an example of using Microsoft’s native Group Policy cmdlets to find registry settings in a GPO. This example looks at the Registry.pol file in the GPO which contains settings from Administrative Templates as well as other settings that write to the registry.pol file. In this video I will go through finding managedAdministrative
RETRIEVING GPO LINKS WITH POWERSHELL Paul-With our cmdlets, you either feed get-sdmgplink GPO names or scopes (i.e. sites, domains, OUs). So the only way to get links across the entire domain is to use get-sdmGPO to retrieve all GPOs and then pass each one to get-sdmgplink, or use AD cmdlets to retrieve the DNs of all site, domain and OUs and then feed that to get-sdmgplink. COMPARING GROUP POLICY (GPO) SETTINGS FROM POWERSHELL GPO Compare 2.0 is all about letting you compare GPO settings across two live or backed up GPOs. The PowerShell interface lets you perform these comparisons in bulk! The product ships with a cmdlet called Compare-SDMGPO which, in the simplest form, lets you do something like this: Compare-SDMGPO -GPONameA “Default Domain Policy” -GPONameB GETTING GROUP POLICY COUNTS WITH POWERSHELL Powershell provides a way to do this quickly and easily. Earlier today I tweeted about the way to do this in Windows 7 or Server 2008-R2, using the Microsoft-provided “GroupPolicy” PowerShell Module. Its as simple as: (Get-GPO -All).Count. However, if you are not yet on these newer OS versions, you can still get this information from CLEANING GROUP POLICY WHEN REMOVING A MACHINE FROM THE A recent thread on Mark Minasi’s forum site reminded me of a topic that comes up every once in a while–namely, how do you cleanly remove Group Policy settings from a machine that has been removed from an AD domain. The answer is to avoid the problem in the first place :). The challenge here is that, once a machine is removed from the domain, you don’t have any control over the policy UNDERSTANDING THE REGISTRY POLICY ARCHIVE FILE The Archive File. The job of the registry archive file is simple. When GP is processed (e.g. you type gpupdate from the command line, or a user logs into a workstation) the GP engine consults the archive file to determine what registry settings have been delivered to the computer or user. It first removes the registry values found in the NEW VERSION OF GPMC POWERSHELL CMDLETS RELEASED! Well, we’ve released a new version of our GPMC PowerShell cmdlets–version 1.2. This new version represents a significant updgrade to the existing cmdlets. The biggest change is that we incorporated new functionality that became available in the version of GPMC that shipped with Vista, SP1 and Windows Server 2008.SDM SOFTWARE
SDM Software’s GP Reporting Pak and GPO Migrator products will help you analyze and re-organize your Group Policy environment. Find duplicate, conflicting and unused GPOs and settings with GP Reporting Pak and report on best practices, optimizations, and security posture of your GPOs. Then consolidate your existing GPOs with GPO Migrator to REMOVING EXTRA REGISTRY SETTINGS FROM GPOS Namely, I can use this syntax: Remove-GPRegistryValue -Name "OfficeDeployment" -Key
"HKCU\Software\Policies\Microsoft\Office\11.0\Word\Disable. dCmdBarItemsCheckBoxes". And by leaving off the -ValueName parameter, the cmdlet removes all entries under that key, within the GPO. This leaves me with quite a few less extra registry settings, as you REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. THE TYPE ACCELERATOR It is a System.Management.ManagementObjectSearcher type and you can execute the query, find the options on the object, execute the query with the get () method. You can also manipulate this object on the fly. Super helpful in scripts and automation. This is an interesting item to have in your back pocket for sure. WMI and type RETRIEVING GPO LINKS WITH POWERSHELL Paul-With our cmdlets, you either feed get-sdmgplink GPO names or scopes (i.e. sites, domains, OUs). So the only way to get links across the entire domain is to use get-sdmGPO to retrieve all GPOs and then pass each one to get-sdmgplink, or use AD cmdlets to retrieve the DNs of all site, domain and OUs and then feed that to get-sdmgplink. GETTING GROUP POLICY COUNTS WITH POWERSHELL Powershell provides a way to do this quickly and easily. Earlier today I tweeted about the way to do this in Windows 7 or Server 2008-R2, using the Microsoft-provided “GroupPolicy” PowerShell Module. Its as simple as: (Get-GPO -All).Count. However, if you are not yet on these newer OS versions, you can still get this information from DEALING WITH THE ACCOUNTEXPIRES DATE IN ACTIVE DIRECTORY Accessing this data from PowerShell is a useful technique to master. If you have yet to dive deep into dates it is time. Just one quick date scenario/comment in this post. In Working with the AccountExpires attribute in AD there is a strange experience that is not super intuitive. Not overly complex, just may have you shaking your head. UNDERSTANDING GROUP POLICY “TATTOOING” Policies & Preferences You’ve probably vaguely heard of registry tattooing as it relates to the old NT 4 system policy. Tattooing was the effect that you saw whenever you applied EVALUATING OU MEMBERSHIP USING WMI FILTERS WMI Query for OU Membership. Note that the namespace field has to reflect the correct namespace, which is root\RSOP\Computer rather than the default root\cimV2. In addition, this query above: Select * From RSOP_Session Where SOM = 'OU=SDM,DC=cpandl,DC=com'. Evaluates to true if the computer processing the GPO that has this filter is in the BEST PRACTICES FOR DESIGNING AND CONSOLIDATING GROUP POLICY Best Practices for Designing and Consolidating Group Policy August 2012 Darren Mar-Elia CTO & Founder, SDM Software, Inc. (www.sdmsoftware.com)SDM SOFTWARE
SDM Software’s GP Reporting Pak and GPO Migrator products will help you analyze and re-organize your Group Policy environment. Find duplicate, conflicting and unused GPOs and settings with GP Reporting Pak and report on best practices, optimizations, and security posture of your GPOs. Then consolidate your existing GPOs with GPO Migrator to REMOVING EXTRA REGISTRY SETTINGS FROM GPOS Namely, I can use this syntax: Remove-GPRegistryValue -Name "OfficeDeployment" -Key
"HKCU\Software\Policies\Microsoft\Office\11.0\Word\Disable. dCmdBarItemsCheckBoxes". And by leaving off the -ValueName parameter, the cmdlet removes all entries under that key, within the GPO. This leaves me with quite a few less extra registry settings, as you REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. THE TYPE ACCELERATOR It is a System.Management.ManagementObjectSearcher type and you can execute the query, find the options on the object, execute the query with the get () method. You can also manipulate this object on the fly. Super helpful in scripts and automation. This is an interesting item to have in your back pocket for sure. WMI and type RETRIEVING GPO LINKS WITH POWERSHELL Paul-With our cmdlets, you either feed get-sdmgplink GPO names or scopes (i.e. sites, domains, OUs). So the only way to get links across the entire domain is to use get-sdmGPO to retrieve all GPOs and then pass each one to get-sdmgplink, or use AD cmdlets to retrieve the DNs of all site, domain and OUs and then feed that to get-sdmgplink. GETTING GROUP POLICY COUNTS WITH POWERSHELL Powershell provides a way to do this quickly and easily. Earlier today I tweeted about the way to do this in Windows 7 or Server 2008-R2, using the Microsoft-provided “GroupPolicy” PowerShell Module. Its as simple as: (Get-GPO -All).Count. However, if you are not yet on these newer OS versions, you can still get this information from DEALING WITH THE ACCOUNTEXPIRES DATE IN ACTIVE DIRECTORY Accessing this data from PowerShell is a useful technique to master. If you have yet to dive deep into dates it is time. Just one quick date scenario/comment in this post. In Working with the AccountExpires attribute in AD there is a strange experience that is not super intuitive. Not overly complex, just may have you shaking your head. UNDERSTANDING GROUP POLICY “TATTOOING” Policies & Preferences You’ve probably vaguely heard of registry tattooing as it relates to the old NT 4 system policy. Tattooing was the effect that you saw whenever you applied EVALUATING OU MEMBERSHIP USING WMI FILTERS WMI Query for OU Membership. Note that the namespace field has to reflect the correct namespace, which is root\RSOP\Computer rather than the default root\cimV2. In addition, this query above: Select * From RSOP_Session Where SOM = 'OU=SDM,DC=cpandl,DC=com'. Evaluates to true if the computer processing the GPO that has this filter is in the BEST PRACTICES FOR DESIGNING AND CONSOLIDATING GROUP POLICY Best Practices for Designing and Consolidating Group Policy August 2012 Darren Mar-Elia CTO & Founder, SDM Software, Inc. (www.sdmsoftware.com) GROUP POLICY REPORTING PAK SDM Software’s GP Reporting Pak 3.0 is the industry-leading Group Policy reporting and analysis tool. Whether you are preparing to migrate to Microsoft Endpoint Manager (MEM), or just need to report on the health and security of your GPOs, quickly find settings within your environment, find differences in settings across individual GPOs or analyze your entire Group Policy deployment for GETTING GROUP POLICY COUNTS WITH POWERSHELL Powershell provides a way to do this quickly and easily. Earlier today I tweeted about the way to do this in Windows 7 or Server 2008-R2, using the Microsoft-provided “GroupPolicy” PowerShell Module. Its as simple as: (Get-GPO -All).Count. However, if you are not yet on these newer OS versions, you can still get this information from RETRIEVING GPO LINKS WITH POWERSHELL Paul-With our cmdlets, you either feed get-sdmgplink GPO names or scopes (i.e. sites, domains, OUs). So the only way to get links across the entire domain is to use get-sdmGPO to retrieve all GPOs and then pass each one to get-sdmgplink, or use AD cmdlets to retrieve the DNs of all site, domain and OUs and then feed that to get-sdmgplink. COMPARING GROUP POLICY (GPO) SETTINGS FROM GPO Compare 2.0 is all about letting you compare GPO settings across two live or backed up GPOs. The PowerShell interface lets you perform these comparisons in bulk! The product ships with a cmdlet called Compare-SDMGPO which, in the simplest form, lets you do something like this: Compare-SDMGPO -GPONameA “Default Domain Policy” -GPONameB FIND ALL REGISTRY SETTINGS MANAGED IN A GPO Here is an example of using Microsoft’s native Group Policy cmdlets to find registry settings in a GPO. This example looks at the Registry.pol file in the GPO which contains settings from Administrative Templates as well as other settings that write to the registry.pol file. In this video I will go through finding managedAdministrative
FIND GROUP POLICY (GPO) SETTING CONFLICTS USING POWERSHELL The output of this command looks like that shown here: Finding Conflicting Group Policy Settings using GPO Exporter and PowerShell. As you can see in this listing, it becomes much easier to find conflicting settings when you can see exactly which GPO (s) contain a particular setting. Another cool by-product of this cmdlet is theability to find
CONFIGURING EVENT LOGS WITH GROUP POLICY Prior to those OS releases, if you want to configure Windows Event Logs for things like maximum log size or retention behavior, you traditionally did that from within Security Settings–specifically under Computer Configuration\Policies\Windows Settings\Security Settings\Event Log. However Microsoft added a new AdministrativeTemplate way of
CLEANING GROUP POLICY WHEN REMOVING A MACHINE FROM THE A recent thread on Mark Minasi’s forum site reminded me of a topic that comes up every once in a while–namely, how do you cleanly remove Group Policy settings from a machine that has been removed from an AD domain. The answer is to avoid the problem in the first place :). The challenge here is that, once a machine is removed from the domain, you don’t have any control over the policy GHOSTS IN THE GPO MACHINE–LOCAL SECURITY POLICY CHANGES ON But there are other ways to affect change to the local security policy outside of GP editor. In the simplest case, the good old command-line net.exe command can make changes to password policy. For example, if I run the following command on a DC: net accounts /minpwlen:9. This will change the minimum password length policy to 9 characters. HELPING WITH A SQL CE CHALLENGE USING HERE-STRINGS While working through a challenge I stumbled through a few interesting items that are worth jotting down. I’ve used both of these constructs before but I had to re-search for some assistance.SDM SOFTWARE
SDM Software’s GP Reporting Pak and GPO Migrator products will help you analyze and re-organize your Group Policy environment. Find duplicate, conflicting and unused GPOs and settings with GP Reporting Pak and report on best practices, optimizations, and security posture of your GPOs. Then consolidate your existing GPOs with GPO Migrator to DEALING WITH THE ACCOUNTEXPIRES DATE IN ACTIVE DIRECTORY Accessing this data from PowerShell is a useful technique to master. If you have yet to dive deep into dates it is time. Just one quick date scenario/comment in this post. In Working with the AccountExpires attribute in AD there is a strange experience that is not super intuitive. Not overly complex, just may have you shaking your head. REMOVING EXTRA REGISTRY SETTINGS FROM GPOS Namely, I can use this syntax: Remove-GPRegistryValue -Name "OfficeDeployment" -Key
"HKCU\Software\Policies\Microsoft\Office\11.0\Word\Disable. dCmdBarItemsCheckBoxes". And by leaving off the -ValueName parameter, the cmdlet removes all entries under that key, within the GPO. This leaves me with quite a few less extra registry settings, as you REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. GETTING GROUP POLICY COUNTS WITH POWERSHELL Powershell provides a way to do this quickly and easily. Earlier today I tweeted about the way to do this in Windows 7 or Server 2008-R2, using the Microsoft-provided “GroupPolicy” PowerShell Module. Its as simple as: (Get-GPO -All).Count. However, if you are not yet on these newer OS versions, you can still get this information from FIND GROUP POLICY (GPO) SETTING CONFLICTS USING POWERSHELL The output of this command looks like that shown here: Finding Conflicting Group Policy Settings using GPO Exporter and PowerShell. As you can see in this listing, it becomes much easier to find conflicting settings when you can see exactly which GPO (s) contain a particular setting. Another cool by-product of this cmdlet is theability to find
UNDERSTANDING GROUP POLICY “TATTOOING” Policies & Preferences You’ve probably vaguely heard of registry tattooing as it relates to the old NT 4 system policy. Tattooing was the effect that you saw whenever you applied EVALUATING OU MEMBERSHIP USING WMI FILTERS WMI Query for OU Membership. Note that the namespace field has to reflect the correct namespace, which is root\RSOP\Computer rather than the default root\cimV2. In addition, this query above: Select * From RSOP_Session Where SOM = 'OU=SDM,DC=cpandl,DC=com'. Evaluates to true if the computer processing the GPO that has this filter is in the WHAT DOES GROUP POLICY DO WHEN IT CAN’T CONTACT A DC During the core phase of processing, when the machine (or user) goes to resolve itself in AD, it will make 4 attempts (Windows 10) to contact a DC to get it’s account information. If it fails to do that, it will generate event ID 7320 in the GP Operations Event Log, as shown here: A client failing to find a DC during GP processing. HELPING WITH A SQL CE CHALLENGE USING HERE-STRINGS While working through a challenge I stumbled through a few interesting items that are worth jotting down. I’ve used both of these constructs before but I had to re-search for some assistance.SDM SOFTWARE
SDM Software’s GP Reporting Pak and GPO Migrator products will help you analyze and re-organize your Group Policy environment. Find duplicate, conflicting and unused GPOs and settings with GP Reporting Pak and report on best practices, optimizations, and security posture of your GPOs. Then consolidate your existing GPOs with GPO Migrator to DEALING WITH THE ACCOUNTEXPIRES DATE IN ACTIVE DIRECTORY Accessing this data from PowerShell is a useful technique to master. If you have yet to dive deep into dates it is time. Just one quick date scenario/comment in this post. In Working with the AccountExpires attribute in AD there is a strange experience that is not super intuitive. Not overly complex, just may have you shaking your head. REMOVING EXTRA REGISTRY SETTINGS FROM GPOS Namely, I can use this syntax: Remove-GPRegistryValue -Name "OfficeDeployment" -Key
"HKCU\Software\Policies\Microsoft\Office\11.0\Word\Disable. dCmdBarItemsCheckBoxes". And by leaving off the -ValueName parameter, the cmdlet removes all entries under that key, within the GPO. This leaves me with quite a few less extra registry settings, as you REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. GETTING GROUP POLICY COUNTS WITH POWERSHELL Powershell provides a way to do this quickly and easily. Earlier today I tweeted about the way to do this in Windows 7 or Server 2008-R2, using the Microsoft-provided “GroupPolicy” PowerShell Module. Its as simple as: (Get-GPO -All).Count. However, if you are not yet on these newer OS versions, you can still get this information from FIND GROUP POLICY (GPO) SETTING CONFLICTS USING POWERSHELL The output of this command looks like that shown here: Finding Conflicting Group Policy Settings using GPO Exporter and PowerShell. As you can see in this listing, it becomes much easier to find conflicting settings when you can see exactly which GPO (s) contain a particular setting. Another cool by-product of this cmdlet is theability to find
UNDERSTANDING GROUP POLICY “TATTOOING” Policies & Preferences You’ve probably vaguely heard of registry tattooing as it relates to the old NT 4 system policy. Tattooing was the effect that you saw whenever you applied EVALUATING OU MEMBERSHIP USING WMI FILTERS WMI Query for OU Membership. Note that the namespace field has to reflect the correct namespace, which is root\RSOP\Computer rather than the default root\cimV2. In addition, this query above: Select * From RSOP_Session Where SOM = 'OU=SDM,DC=cpandl,DC=com'. Evaluates to true if the computer processing the GPO that has this filter is in the WHAT DOES GROUP POLICY DO WHEN IT CAN’T CONTACT A DC During the core phase of processing, when the machine (or user) goes to resolve itself in AD, it will make 4 attempts (Windows 10) to contact a DC to get it’s account information. If it fails to do that, it will generate event ID 7320 in the GP Operations Event Log, as shown here: A client failing to find a DC during GP processing. HELPING WITH A SQL CE CHALLENGE USING HERE-STRINGS While working through a challenge I stumbled through a few interesting items that are worth jotting down. I’ve used both of these constructs before but I had to re-search for some assistance. SDM SOFTWARE SUPPORT At SDM Software we strive to provide timely support to all of our customers. To open a support case with our team please email support@sdmsoftware.com. This ensures we are tracking the incident in our system and keeps us accountable. REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. FIND ALL REGISTRY SETTINGS MANAGED IN A GPO Here is an example of using Microsoft’s native Group Policy cmdlets to find registry settings in a GPO. This example looks at the Registry.pol file in the GPO which contains settings from Administrative Templates as well as other settings that write to the registry.pol file. In this video I will go through finding managedAdministrative
GROUP POLICY AUTOMATION ENGINE The SDM Group Policy Automation Engine provides a PowerShell interface for getting and setting configuration in Group Policy Objects (GPOs). We utilize a single cmdlet called Get-SDMGPObject. This single cmdlet provides all the secret sauce that makes the magic happen. With that said, this cmdlet has some complexities. GETTING GROUP POLICY COUNTS WITH POWERSHELL Powershell provides a way to do this quickly and easily. Earlier today I tweeted about the way to do this in Windows 7 or Server 2008-R2, using the Microsoft-provided “GroupPolicy” PowerShell Module. Its as simple as: (Get-GPO -All).Count. However, if you are not yet on these newer OS versions, you can still get this information from UNDERSTANDING GROUP POLICY PRIVILEGE ESCALATION IN CVE Understanding Group Policy Privilege Escalation in CVE-2020-1317. Earlier this month, Microsoft released an advisory for CVE-2020-1317 which describes a privilege escalation vulnerability in Group Policy. This was further detailed by the discoverer of the vulnerability on the Cyberark website. The nature of this issue is interesting andworth
COMPARING GROUP POLICY (GPO) SETTINGS FROM GPO Compare 2.0 is all about letting you compare GPO settings across two live or backed up GPOs. The PowerShell interface lets you perform these comparisons in bulk! The product ships with a cmdlet called Compare-SDMGPO which, in the simplest form, lets you do something like this: Compare-SDMGPO -GPONameA “Default Domain Policy” -GPONameB FIND GROUP POLICY (GPO) SETTING CONFLICTS USING POWERSHELL The output of this command looks like that shown here: Finding Conflicting Group Policy Settings using GPO Exporter and PowerShell. As you can see in this listing, it becomes much easier to find conflicting settings when you can see exactly which GPO (s) contain a particular setting. Another cool by-product of this cmdlet is theability to find
RETRIEVING GPO LINKS WITH POWERSHELL Paul-With our cmdlets, you either feed get-sdmgplink GPO names or scopes (i.e. sites, domains, OUs). So the only way to get links across the entire domain is to use get-sdmGPO to retrieve all GPOs and then pass each one to get-sdmgplink, or use AD cmdlets to retrieve the DNs of all site, domain and OUs and then feed that to get-sdmgplink. CLEANING GROUP POLICY WHEN REMOVING A MACHINE FROM THE A recent thread on Mark Minasi’s forum site reminded me of a topic that comes up every once in a while–namely, how do you cleanly remove Group Policy settings from a machine that has been removed from an AD domain. The answer is to avoid the problem in the first place :). The challenge here is that, once a machine is removed from the domain, you don’t have any control over the policySDM SOFTWARE
SDM Software’s GP Reporting Pak and GPO Migrator products will help you analyze and re-organize your Group Policy environment. Find duplicate, conflicting and unused GPOs and settings with GP Reporting Pak and report on best practices, optimizations, and security posture of your GPOs. Then consolidate your existing GPOs with GPO Migrator to SDM SOFTWARE SUPPORT At SDM Software we strive to provide timely support to all of our customers. To open a support case with our team please email support@sdmsoftware.com. This ensures we are tracking the incident in our system and keeps us accountable. GROUP POLICY COMPLIANCE MANAGER Operating Systems Supported for Installation: Microsoft® Windows 7, 8.x, 10, Windows Server 2008-R2, 2012-R2, 2016 or 2019..Net Framework 4.5.2 and Microsoft® Group Policy Management Console (GPMC) installed on the system where you install the product. GROUP POLICY REPORTING PAK SDM Software’s GP Reporting Pak 3.0 is the industry-leading Group Policy reporting and analysis tool. Whether you are preparing to migrate to Microsoft Endpoint Manager (MEM), or just need to report on the health and security of your GPOs, quickly find settings within your environment, find differences in settings across individual GPOs or analyze your entire Group Policy deployment for REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. REMOVING EXTRA REGISTRY SETTINGS FROM GPOS Namely, I can use this syntax: Remove-GPRegistryValue -Name "OfficeDeployment" -Key
"HKCU\Software\Policies\Microsoft\Office\11.0\Word\Disable. dCmdBarItemsCheckBoxes". And by leaving off the -ValueName parameter, the cmdlet removes all entries under that key, within the GPO. This leaves me with quite a few less extra registry settings, as you THE TYPE ACCELERATOR It is a System.Management.ManagementObjectSearcher type and you can execute the query, find the options on the object, execute the query with the get () method. You can also manipulate this object on the fly. Super helpful in scripts and automation. This is an interesting item to have in your back pocket for sure. WMI and type DEALING WITH THE ACCOUNTEXPIRES DATE IN ACTIVE DIRECTORY Accessing this data from PowerShell is a useful technique to master. If you have yet to dive deep into dates it is time. Just one quick date scenario/comment in this post. In Working with the AccountExpires attribute in AD there is a strange experience that is not super intuitive. Not overly complex, just may have you shaking your head. UNDERSTANDING GROUP POLICY “TATTOOING” Policies & Preferences You’ve probably vaguely heard of registry tattooing as it relates to the old NT 4 system policy. Tattooing was the effect that you saw whenever you applied HELPING WITH A SQL CE CHALLENGE USING HERE-STRINGS While working through a challenge I stumbled through a few interesting items that are worth jotting down. I’ve used both of these constructs before but I had to re-search for some assistance.SDM SOFTWARE
SDM Software’s GP Reporting Pak and GPO Migrator products will help you analyze and re-organize your Group Policy environment. Find duplicate, conflicting and unused GPOs and settings with GP Reporting Pak and report on best practices, optimizations, and security posture of your GPOs. Then consolidate your existing GPOs with GPO Migrator to SDM SOFTWARE SUPPORT At SDM Software we strive to provide timely support to all of our customers. To open a support case with our team please email support@sdmsoftware.com. This ensures we are tracking the incident in our system and keeps us accountable. GROUP POLICY COMPLIANCE MANAGER Operating Systems Supported for Installation: Microsoft® Windows 7, 8.x, 10, Windows Server 2008-R2, 2012-R2, 2016 or 2019..Net Framework 4.5.2 and Microsoft® Group Policy Management Console (GPMC) installed on the system where you install the product. GROUP POLICY REPORTING PAK SDM Software’s GP Reporting Pak 3.0 is the industry-leading Group Policy reporting and analysis tool. Whether you are preparing to migrate to Microsoft Endpoint Manager (MEM), or just need to report on the health and security of your GPOs, quickly find settings within your environment, find differences in settings across individual GPOs or analyze your entire Group Policy deployment for REGISTRY.POL VIEWER UTILITY This utility provides read-only access into the registry.pol file (or any other .pol file). Registry.pol is the file that GP uses to store registry-based policy settings made by Administrative Template, Windows Firewall, Application Control Policies (AppLocker), Software Restriction Policy or Disk Quota policy. REMOVING EXTRA REGISTRY SETTINGS FROM GPOS Namely, I can use this syntax: Remove-GPRegistryValue -Name "OfficeDeployment" -Key
"HKCU\Software\Policies\Microsoft\Office\11.0\Word\Disable. dCmdBarItemsCheckBoxes". And by leaving off the -ValueName parameter, the cmdlet removes all entries under that key, within the GPO. This leaves me with quite a few less extra registry settings, as you THE TYPE ACCELERATOR It is a System.Management.ManagementObjectSearcher type and you can execute the query, find the options on the object, execute the query with the get () method. You can also manipulate this object on the fly. Super helpful in scripts and automation. This is an interesting item to have in your back pocket for sure. WMI and type DEALING WITH THE ACCOUNTEXPIRES DATE IN ACTIVE DIRECTORY Accessing this data from PowerShell is a useful technique to master. If you have yet to dive deep into dates it is time. Just one quick date scenario/comment in this post. In Working with the AccountExpires attribute in AD there is a strange experience that is not super intuitive. Not overly complex, just may have you shaking your head. UNDERSTANDING GROUP POLICY “TATTOOING” Policies & Preferences You’ve probably vaguely heard of registry tattooing as it relates to the old NT 4 system policy. Tattooing was the effect that you saw whenever you applied HELPING WITH A SQL CE CHALLENGE USING HERE-STRINGS While working through a challenge I stumbled through a few interesting items that are worth jotting down. I’ve used both of these constructs before but I had to re-search for some assistance. GROUP POLICY AUTOMATION ENGINE SDM Software’s Group Policy Automation Engine (GPAE) provides the industry’s only PowerShell interface for automating the reads and writes of Group Policy settings. If automating changes to GPOs is your requirement, GPAE is the answer! With support for most policy areas in GP, including Admin Templates, most security settings, GP OVERRIDE THE GROUP POLICY ADMX CENTRAL STORE If you set the value to 1, then your GP editor tools will use the ADMX/ADML files found under c:\windows\policydefinitions instead of the Central Store. If the value is set to 0, or removed, then the Central Store is used again. Note that you will need to restart GP editor in between changes to this value. (see figure below) GETTING GROUP POLICY COUNTS WITH POWERSHELL Powershell provides a way to do this quickly and easily. Earlier today I tweeted about the way to do this in Windows 7 or Server 2008-R2, using the Microsoft-provided “GroupPolicy” PowerShell Module. Its as simple as: (Get-GPO -All).Count. However, if you are not yet on these newer OS versions, you can still get this information from FIND ALL REGISTRY SETTINGS MANAGED IN A GPO Here is an example of using Microsoft’s native Group Policy cmdlets to find registry settings in a GPO. This example looks at the Registry.pol file in the GPO which contains settings from Administrative Templates as well as other settings that write to the registry.pol file. In this video I will go through finding managedAdministrative
EVALUATING OU MEMBERSHIP USING WMI FILTERS WMI Query for OU Membership. Note that the namespace field has to reflect the correct namespace, which is root\RSOP\Computer rather than the default root\cimV2. In addition, this query above: Select * From RSOP_Session Where SOM = 'OU=SDM,DC=cpandl,DC=com'. Evaluates to true if the computer processing the GPO that has this filter is in the GROUP POLICY AUDITING & ATTESTATION 2.0 HITS WITH NEW AD Last month we at SDM Software shipped the 2.0 version of our Group Policy Auditing & Attestation product. GPAA is our flagship product for helping you perform real-time compliance auditing, alerting, rollback and attestation of Group Policy Objects (GPOs). The product provides in-depth auditing of GPO changes on everything from new GPOcreation
HELPING WITH A SQL CE CHALLENGE USING HERE-STRINGS While working through a challenge I stumbled through a few interesting items that are worth jotting down. I’ve used both of these constructs before but I had to re-search for some assistance. UNDERSTANDING THE ROLE OF ADMX (AND ADM) FILES IN GROUP Recently I’ve been answering a few questions about the role of ADMX files (Administrative Templates) in Group Policy. For those who are new to Group Policy or haven’t spent a lot of time with it, I have seen some misunderstanding around what these template files actually do, and their role in CLEANING GROUP POLICY WHEN REMOVING A MACHINE FROM THE A recent thread on Mark Minasi’s forum site reminded me of a topic that comes up every once in a while–namely, how do you cleanly remove Group Policy settings from a machine that has been removed from an AD domain. The answer is to avoid the problem in the first place :). The challenge here is that, once a machine is removed from the domain, you don’t have any control over the policy GHOSTS IN THE GPO MACHINE–LOCAL SECURITY POLICY CHANGES ON But there are other ways to affect change to the local security policy outside of GP editor. In the simplest case, the good old command-line net.exe command can make changes to password policy. For example, if I run the following command on a DC: net accounts /minpwlen:9. This will change the minimum password length policy to 9 characters. • • • • • •Search for:
* Follow
* Follow
* Follow
* Follow
Contact Us
* Products
* Product Overview
* GPO Migrator
* Group Policy Reporting Pak * Group Policy Auditing & Attestation (GPAA) * Group Policy Compliance Manager * Group Policy Automation Engine* Resources
* Newsletter Signup
* Whitepapers
* SDM Software Support* Company
* About Us
* Connect
* Freeware
* Blog
* Products
* Product Overview
* GPO Migrator
* Group Policy Reporting Pak * Group Policy Auditing & Attestation (GPAA) * Group Policy Compliance Manager * Group Policy Automation Engine* Resources
* Newsletter Signup
* Whitepapers
* SDM Software Support* Company
* About Us
* Connect
* Freeware
* Blog
Search for:
* Follow
* Follow
* Follow
* Follow
* Products
* Product Overview
* GPO Migrator
* Group Policy Reporting Pak * Group Policy Auditing & Attestation (GPAA) * Group Policy Compliance Manager * Group Policy Automation Engine* Resources
* Newsletter Signup
* Whitepapers
* SDM Software Support* Company
* About Us
* Connect
* Freeware
* Blog
* Products
* Product Overview
* GPO Migrator
* Group Policy Reporting Pak * Group Policy Auditing & Attestation (GPAA) * Group Policy Compliance Manager * Group Policy Automation Engine* Resources
* Newsletter Signup
* Whitepapers
* SDM Software Support* Company
* About Us
* Connect
* Freeware
* Blog
Contact Us
* Home
* About Us
* Case Studies
* Case Study: Annese & Associates, Inc. * Case Study: PacStar* Contact
* Thank You For Contacting Us* Disclaimer
* Download A Trial
* End User License Agreement * GPO Freeware Downloads * GPO Deny Finder 1.0 * GPO Version Powershell Cmdlets * Group Policy Health Reporter 1.91 * Group Policy Preference Password Remediation Utility * Registry.Pol Viewer Utility * SDM GPMC 1.5 Cmdlets * SDM GPMC 2.0 Module * WMI Filter Validation Utility* GPO Whitepapers
* Understanding Group Policy Storage* Group Policy Blog
* Group Policy Products* GPO Migrator
* Group Policy Auditing & Attestation (GPAA) * Group Policy Automation Engine * Group Policy Compliance Manager * Group Policy Reporting Pak * Group Policy Software Trial Downloads* Home
* Newsletter Signup
* Privacy Policy
* SDM Software
* SDM Software Support* Terms of Service
* Test Page
* AD
* Azure
* Bugs
* Cloud
* Conferences
* Cool New Products
* Desired State Configuration* Event Logs
* Folder Redirection* Freeware
* General
* General Stuff
* GP Troubleshooting* GPMC
* GPO Attestation
* GPO Compare
* GPOGUY.COM
* GPSI
* Group Policy
* Group Policy Automation* Group Policy Blog
* Group Policy Change Auditing * Group Policy Cleanup * Group Policy Compliance * Group Policy Consulting * Group Policy Design * Group Policy Management* Group Policy News
* Group Policy Performance * Group Policy Preferences * Group Policy Reporting * Group Policy Tools * IE Maintenance Policy* IE Policy
* Ignite
* iPad
* Microsoft-Related
* MMS 2012
* MSTeched
* Office
* PowerShell
* Presentations
* registry policy
* RSOP
* sdm software
* Security Policy
* Security-related
* Server 2012
* SQL CE
* TechEd
* Teched 2012
* TechEd 2013
* Technology Futures* Tips & Tricks
* Training
* Uncategorized
* VDI
* Videos
* Vista-2008 stuff
* Webinar
* Whitepaper
* whitepapers
* Windows 10
* Windows 8
* Windows 8.1
* Windows Intune
* Windows RT
* WMI
* WMI Filters
Select Page
* Home
* About Us
* Case Studies
* Case Study: Annese & Associates, Inc. * Case Study: PacStar* Contact
* Thank You For Contacting Us* Disclaimer
* Download A Trial
* End User License Agreement * GPO Freeware Downloads * GPO Deny Finder 1.0 * GPO Version Powershell Cmdlets * Group Policy Health Reporter 1.91 * Group Policy Preference Password Remediation Utility * Registry.Pol Viewer Utility * SDM GPMC 1.5 Cmdlets * SDM GPMC 2.0 Module * WMI Filter Validation Utility* GPO Whitepapers
* Understanding Group Policy Storage* Group Policy Blog
* Group Policy Products* GPO Migrator
* Group Policy Auditing & Attestation (GPAA) * Group Policy Automation Engine * Group Policy Compliance Manager * Group Policy Reporting Pak * Group Policy Software Trial Downloads* Home
* Newsletter Signup
* Privacy Policy
* SDM Software
* SDM Software Support* Terms of Service
* Test Page
* AD
* Azure
* Bugs
* Cloud
* Conferences
* Cool New Products
* Desired State Configuration* Event Logs
* Folder Redirection* Freeware
* General
* General Stuff
* GP Troubleshooting* GPMC
* GPO Attestation
* GPO Compare
* GPOGUY.COM
* GPSI
* Group Policy
* Group Policy Automation* Group Policy Blog
* Group Policy Change Auditing * Group Policy Cleanup * Group Policy Compliance * Group Policy Consulting * Group Policy Design * Group Policy Management* Group Policy News
* Group Policy Performance * Group Policy Preferences * Group Policy Reporting * Group Policy Tools * IE Maintenance Policy* IE Policy
* Ignite
* iPad
* Microsoft-Related
* MMS 2012
* MSTeched
* Office
* PowerShell
* Presentations
* registry policy
* RSOP
* sdm software
* Security Policy
* Security-related
* Server 2012
* SQL CE
* TechEd
* Teched 2012
* TechEd 2013
* Technology Futures* Tips & Tricks
* Training
* Uncategorized
* VDI
* Videos
* Vista-2008 stuff
* Webinar
* Whitepaper
* whitepapers
* Windows 10
* Windows 8
* Windows 8.1
* Windows Intune
* Windows RT
* WMI
* WMI Filters
Search for:
* Follow
* Follow
* Follow
* Follow
Contact Us
* Products
* Product Overview
* GPO Migrator
* Group Policy Reporting Pak * Group Policy Auditing & Attestation (GPAA) * Group Policy Compliance Manager * Group Policy Automation Engine* Resources
* Newsletter Signup
* Whitepapers
* SDM Software Support* Company
* About Us
* Connect
* Freeware
* Blog
* Products
* Product Overview
* GPO Migrator
* Group Policy Reporting Pak * Group Policy Auditing & Attestation (GPAA) * Group Policy Compliance Manager * Group Policy Automation Engine* Resources
* Newsletter Signup
* Whitepapers
* SDM Software Support* Company
* About Us
* Connect
* Freeware
* Blog
Search for:
* Follow
* Follow
* Follow
* Follow
* Products
* Product Overview
* GPO Migrator
* Group Policy Reporting Pak * Group Policy Auditing & Attestation (GPAA) * Group Policy Compliance Manager * Group Policy Automation Engine* Resources
* Newsletter Signup
* Whitepapers
* SDM Software Support* Company
* About Us
* Connect
* Freeware
* Blog
* Products
* Product Overview
* GPO Migrator
* Group Policy Reporting Pak * Group Policy Auditing & Attestation (GPAA) * Group Policy Compliance Manager * Group Policy Automation Engine* Resources
* Newsletter Signup
* Whitepapers
* SDM Software Support* Company
* About Us
* Connect
* Freeware
* Blog
THE WINDOWS® GROUP POLICY EXPERTS Secure, Streamline and Optimize your Group Policy Deployments with SDM SoftwareRequest Quote
Download Trial
OUR GROUP POLICY PRODUCT LINEUP SDM SOFTWARE’S GROUP POLICY products provide the full range of capabilities for managing your Group Policy DeploymentsGP REPORTING PAK
Group Policy Reporting, Comparison and AnalysisGPO MIGRATION
GPO Migration and Consolidation GROUP POLICY AUTOMATION ENGINE The PowerShell-based Group Policy SDK GROUP POLICY AUDITING & ATTESTATION Real-time change auditing, rollback and attestation of GPOs GROUP POLICY COMPLIANCE MANAGER Validation that your endpoints are compliant with Group Policy MODERNIZE AND SECURE YOUR GROUP POLICY DEPLOYMENTS From reporting to auditing to compliance Modernization of Group Policy starts with a proper assessment of your GPOs. SDM Software’s GP Reporting Pak and GPO Migrator products will help you analyze and re-organize your Group Policy environment. Find duplicate, conflicting and unused GPOs and settings with GP Reporting Pak and report on best practices, optimizations, and security posture of your GPOs. Then consolidate your existing GPOs with GPO Migrator to create an optimized deployment.PRODUCTS
GPOGUY Freeware provides your favorite utilities for managing Group Policy.Download Freeware
CHECK OUT OUR BLOG
Get expert advice, unique content and analysis from 14-time Microsoft MVP and “GPOGUY” Darren Mar-Elia__
WHAT DOES GROUP POLICY DO WHEN IT CAN’T ... The title of this blog tells it all. I got asked the question–whathappens ...
SENDING GPOS DOWN THE WRONG ... At this blog title implies, this is a bit of a science experiment.Many years ...
GROUP POLICY SECURITY– TINKERING WITH ... If you’ve been following this blog, you know that about 2 and halfyears ...
SPEAKING IN CHICAGO NEXT MONTH! Hey folks! Just a quick note that I’m giving a talk next month inChicago. ...
THE GPOGUY GROUP POLICY FAQ QUIRKS IN RESTRICTED GROUPS POLICY ON AD GROUPS About a year ago, I posted about the perils of granting someone writeaccess on ...
UNDERSTANDING THE REGISTRY POLICY ARCHIVE FILE One of the advantages of messing around with Group Policy since beforeit ...
HIJACKING ADMINISTRATIVE TEMPLATES As I think about Group Policy as a target for attackers, there aremany obvious ...
WHAT DOES GROUP POLICY DO WHEN IT CAN’T ... The title of this blog tells it all. I got asked the question–whathappens ...
SENDING GPOS DOWN THE WRONG ... At this blog title implies, this is a bit of a science experiment.Many years ...
GROUP POLICY SECURITY– TINKERING WITH ... If you’ve been following this blog, you know that about 2 and halfyears ...
SPEAKING IN CHICAGO NEXT MONTH! Hey folks! Just a quick note that I’m giving a talk next month inChicago. ...
THE GPOGUY GROUP POLICY FAQ QUIRKS IN RESTRICTED GROUPS POLICY ON AD GROUPS About a year ago, I posted about the perils of granting someone writeaccess on ...
UNDERSTANDING THE REGISTRY POLICY ARCHIVE FILE One of the advantages of messing around with Group Policy since beforeit ...
HIJACKING ADMINISTRATIVE TEMPLATES As I think about Group Policy as a target for attackers, there aremany obvious ...
WHAT DOES GROUP POLICY DO WHEN IT CAN’T ... The title of this blog tells it all. I got asked the question–whathappens ...
SENDING GPOS DOWN THE WRONG ... At this blog title implies, this is a bit of a science experiment.Many years ...
GROUP POLICY SECURITY– TINKERING WITH ... If you’ve been following this blog, you know that about 2 and halfyears ...
SPEAKING IN CHICAGO NEXT MONTH! Hey folks! Just a quick note that I’m giving a talk next month inChicago. ...
__
READ MORE POSTS
415.226.1308
sales@sdmsoftware.com2100 4th St. #132
San Rafael, CA 94901 Contact Us Get Newsletter Copyright @ SDM Software 2020. All Rights Reserved. Website by Social Media Ninjas | Terms of Service | Privacy Policy | Disclaimer| EULA
╳
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0