Are you over 18 and want to see adult content?
More Annotations
A complete backup of indietheaternow.com
Are you over 18 and want to see adult content?
A complete backup of epal-pallets.org
Are you over 18 and want to see adult content?
A complete backup of fridaymagazine.ae
Are you over 18 and want to see adult content?
A complete backup of crime-prevention-intl.org
Are you over 18 and want to see adult content?

A complete backup of badinstallmentonline.com
Are you over 18 and want to see adult content?

A complete backup of investiraucameroun.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://ibjapan.com
Are you over 18 and want to see adult content?
A complete backup of https://flashgamesnexus.com
Are you over 18 and want to see adult content?

A complete backup of https://rolex-watch.me.uk
Are you over 18 and want to see adult content?
A complete backup of https://wilftek.com
Are you over 18 and want to see adult content?

A complete backup of https://haikyo.co.jp
Are you over 18 and want to see adult content?

A complete backup of https://krkonose.eu
Are you over 18 and want to see adult content?
A complete backup of https://inten.to
Are you over 18 and want to see adult content?
A complete backup of https://lifestylecombining.com
Are you over 18 and want to see adult content?

A complete backup of https://oxfordeagle.info
Are you over 18 and want to see adult content?

A complete backup of https://royalgreenwich.gov.uk
Are you over 18 and want to see adult content?
Text
UPRECENT
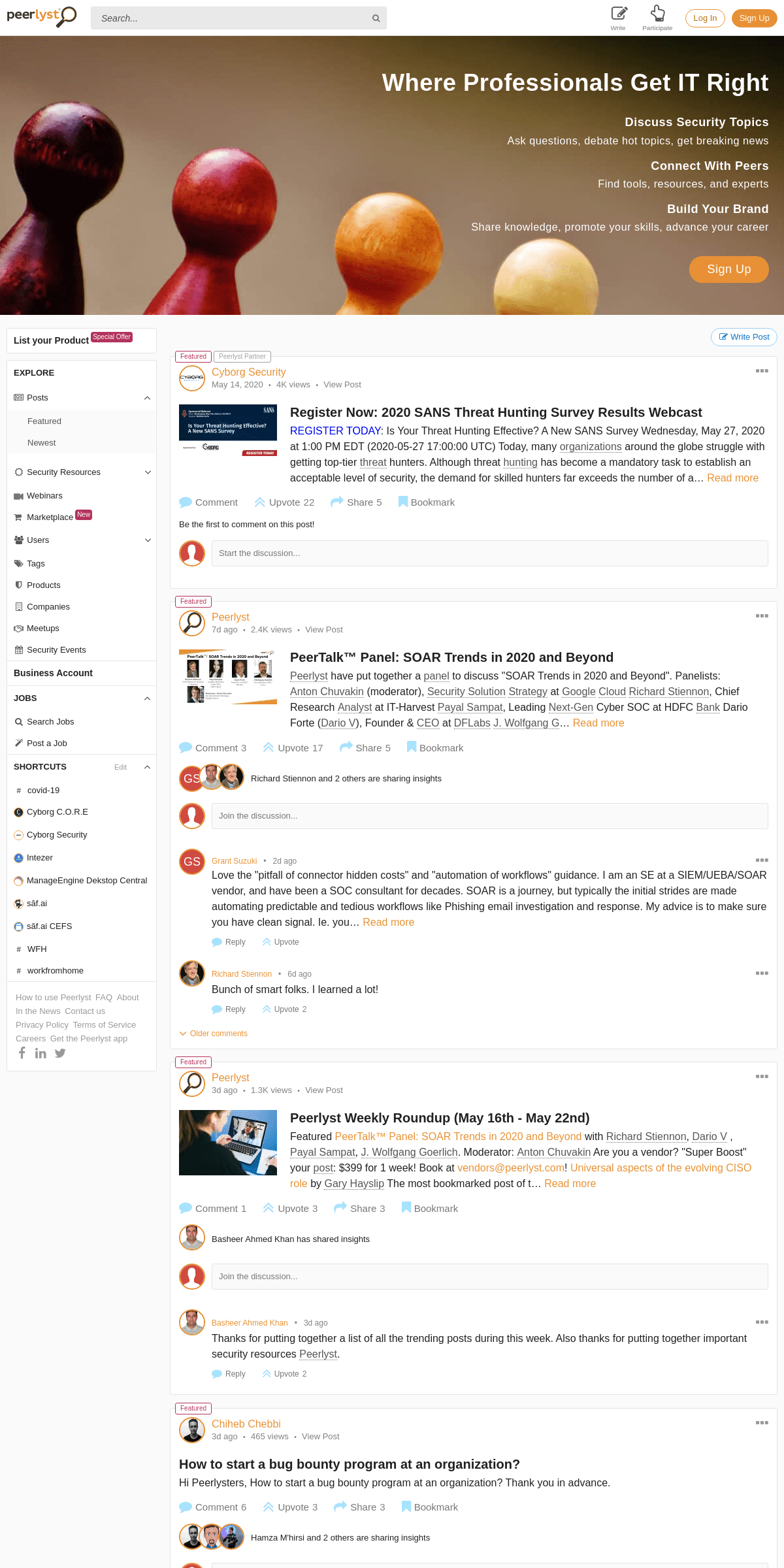
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami men POWERSHELL FOR PENETRATION TESTERS about_Execution_Policies •Execution Policy is present to stop a user from accidently running scripts. •There are numerous ways to bypassit:
RED TEAMING DEVOPS
Red teaming Devops - hypothesis / adv sim - Is the target organization aware of Devops CI/CD attack surface? - Is this being addressed or just dismissed as another 3rd party (pre cloud CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length BECOMING VIRTUALLY UNTRACEABLE (EPS1.0 B4S!C T3CHN1QU3S.ONION) Becoming Virtually Untraceable (Eps1.0_B4s!c_T3chn1qu3s.onion) Ian Barwise Aug 10, 2018 Liam Neeson in “Taken 3” image courtesy ofFandango
PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS ANDSIGNUPRECENT
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami men POWERSHELL FOR PENETRATION TESTERS about_Execution_Policies •Execution Policy is present to stop a user from accidently running scripts. •There are numerous ways to bypassit:
RED TEAMING DEVOPS
Red teaming Devops - hypothesis / adv sim - Is the target organization aware of Devops CI/CD attack surface? - Is this being addressed or just dismissed as another 3rd party (pre cloud CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length BECOMING VIRTUALLY UNTRACEABLE (EPS1.0 B4S!C T3CHN1QU3S.ONION) Becoming Virtually Untraceable (Eps1.0_B4s!c_T3chn1qu3s.onion) Ian Barwise Aug 10, 2018 Liam Neeson in “Taken 3” image courtesy ofFandango
TOP "CHINA" POSTS
Read about "china" wiki, training, posts, blogs, discussions, overview, Q&A, vendors, products, and events. TRAINING MATERIALS, COURSES, E-BOOKS, ETC FOR INFOSEC Continuously updated resources on trainings, courses, certifications, etc on various information-security topics, for different paths and stages of an InfoSec career ATTACK VECTORS FOR VEHICLES AND CONNECTED CARS Download This Resource as PDF:Attack Vectors for Vehicles and Connected CarsThe moderncarsandvehiclesuse electronic devices to transfer messages inreal time, operate thecarfrom remote locations,wifiaccess, andapplicationinstallation. The modern vehicGNNGI I R B IT HOME
knowledgementsiii Ac 1 Introduction: Critical Infrastructure and Your Business 9 Energy Sector 13 Chemical Sector (including Research & Biotech) 19 Commercial Facilities Sector (including Tourism & Public Venues) 23 Communications Sector PRODUCT INFORMATION FOR STEALTHWATCH UDP BY LANCOPE The UDP Director™ (formerly known as the StealthWatch FlowReplicator) is a high-speed, high-performance appliance that receives essential network and security i PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS ANDSIGNUPRECENT
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami men POWERSHELL FOR PENETRATION TESTERS about_Execution_Policies •Execution Policy is present to stop a user from accidently running scripts. •There are numerous ways to bypassit:
RED TEAMING DEVOPS
Red teaming Devops - hypothesis / adv sim - Is the target organization aware of Devops CI/CD attack surface? - Is this being addressed or just dismissed as another 3rd party (pre cloud CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length BECOMING VIRTUALLY UNTRACEABLE (EPS1.0 B4S!C T3CHN1QU3S.ONION) Becoming Virtually Untraceable (Eps1.0_B4s!c_T3chn1qu3s.onion) Ian Barwise Aug 10, 2018 Liam Neeson in “Taken 3” image courtesy ofFandango
PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS ANDSIGNUPRECENT
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami men POWERSHELL FOR PENETRATION TESTERS about_Execution_Policies •Execution Policy is present to stop a user from accidently running scripts. •There are numerous ways to bypassit:
RED TEAMING DEVOPS
Red teaming Devops - hypothesis / adv sim - Is the target organization aware of Devops CI/CD attack surface? - Is this being addressed or just dismissed as another 3rd party (pre cloud CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length BECOMING VIRTUALLY UNTRACEABLE (EPS1.0 B4S!C T3CHN1QU3S.ONION) Becoming Virtually Untraceable (Eps1.0_B4s!c_T3chn1qu3s.onion) Ian Barwise Aug 10, 2018 Liam Neeson in “Taken 3” image courtesy ofFandango
TOP "CHINA" POSTS
Read about "china" wiki, training, posts, blogs, discussions, overview, Q&A, vendors, products, and events. TRAINING MATERIALS, COURSES, E-BOOKS, ETC FOR INFOSEC Continuously updated resources on trainings, courses, certifications, etc on various information-security topics, for different paths and stages of an InfoSec career ATTACK VECTORS FOR VEHICLES AND CONNECTED CARS Download This Resource as PDF:Attack Vectors for Vehicles and Connected CarsThe moderncarsandvehiclesuse electronic devices to transfer messages inreal time, operate thecarfrom remote locations,wifiaccess, andapplicationinstallation. The modern vehicGNNGI I R B IT HOME
knowledgementsiii Ac 1 Introduction: Critical Infrastructure and Your Business 9 Energy Sector 13 Chemical Sector (including Research & Biotech) 19 Commercial Facilities Sector (including Tourism & Public Venues) 23 Communications Sector PRODUCT INFORMATION FOR STEALTHWATCH UDP BY LANCOPE The UDP Director™ (formerly known as the StealthWatch FlowReplicator) is a high-speed, high-performance appliance that receives essential network and security i PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS ANDSIGNUPRECENT
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami men ATTACK VECTORS FOR VEHICLES AND CONNECTED CARS Download This Resource as PDF:Attack Vectors for Vehicles and Connected CarsThe moderncarsandvehiclesuse electronic devices to transfer messages inreal time, operate thecarfrom remote locations,wifiaccess, andapplicationinstallation. The modern vehic POWERSHELL FOR PENETRATION TESTERS about_Execution_Policies •Execution Policy is present to stop a user from accidently running scripts. •There are numerous ways to bypassit:
RED TEAMING DEVOPS
Red teaming Devops - hypothesis / adv sim - Is the target organization aware of Devops CI/CD attack surface? - Is this being addressed or just dismissed as another 3rd party (pre cloud CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS ANDSIGNUPRECENT
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami men ATTACK VECTORS FOR VEHICLES AND CONNECTED CARS Download This Resource as PDF:Attack Vectors for Vehicles and Connected CarsThe moderncarsandvehiclesuse electronic devices to transfer messages inreal time, operate thecarfrom remote locations,wifiaccess, andapplicationinstallation. The modern vehic POWERSHELL FOR PENETRATION TESTERS about_Execution_Policies •Execution Policy is present to stop a user from accidently running scripts. •There are numerous ways to bypassit:
RED TEAMING DEVOPS
Red teaming Devops - hypothesis / adv sim - Is the target organization aware of Devops CI/CD attack surface? - Is this being addressed or just dismissed as another 3rd party (pre cloud CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS AND Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
TRAINING MATERIALS, COURSES, E-BOOKS, ETC FOR INFOSEC Continuously updated resources on trainings, courses, certifications, etc on various information-security topics, for different paths and stages of an InfoSec career PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS ANDSIGNUPRECENT
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce ATTACK VECTORS FOR VEHICLES AND CONNECTED CARS Download This Resource as PDF:Attack Vectors for Vehicles and Connected CarsThe moderncarsandvehiclesuse electronic devices to transfer messages inreal time, operate thecarfrom remote locations,wifiaccess, andapplicationinstallation. The modern vehic JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami menTOP "CHINA" POSTS
Read about "china" wiki, training, posts, blogs, discussions, overview, Q&A, vendors, products, and events. CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length BECOMING VIRTUALLY UNTRACEABLE (EPS1.0 B4S!C T3CHN1QU3S.ONION) Becoming Virtually Untraceable (Eps1.0_B4s!c_T3chn1qu3s.onion) Ian Barwise Aug 10, 2018 Liam Neeson in “Taken 3” image courtesy ofFandango
PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS ANDSIGNUPRECENT
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce ATTACK VECTORS FOR VEHICLES AND CONNECTED CARS Download This Resource as PDF:Attack Vectors for Vehicles and Connected CarsThe moderncarsandvehiclesuse electronic devices to transfer messages inreal time, operate thecarfrom remote locations,wifiaccess, andapplicationinstallation. The modern vehic JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami menTOP "CHINA" POSTS
Read about "china" wiki, training, posts, blogs, discussions, overview, Q&A, vendors, products, and events. CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length BECOMING VIRTUALLY UNTRACEABLE (EPS1.0 B4S!C T3CHN1QU3S.ONION) Becoming Virtually Untraceable (Eps1.0_B4s!c_T3chn1qu3s.onion) Ian Barwise Aug 10, 2018 Liam Neeson in “Taken 3” image courtesy ofFandango
PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS AND Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst. Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from 191 countries. We were really proud to build a place where anyone could learn, share knowledge, and advance their career. The site hosted ~150,000 resources, wikis and blogs insecurity, all
TRAINING MATERIALS, COURSES, E-BOOKS, ETC FOR INFOSEC Continuously updated resources on trainings, courses, certifications, etc on various information-security topics, for different paths and stages of an InfoSec career PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS ANDSIGNUPRECENT
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from191 countries.
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce ATTACK VECTORS FOR VEHICLES AND CONNECTED CARS Download This Resource as PDF:Attack Vectors for Vehicles and Connected CarsThe moderncarsandvehiclesuse electronic devices to transfer messages inreal time, operate thecarfrom remote locations,wifiaccess, andapplicationinstallation. The modern vehic JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami menTOP "CHINA" POSTS
Read about "china" wiki, training, posts, blogs, discussions, overview, Q&A, vendors, products, and events. CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length BECOMING VIRTUALLY UNTRACEABLE (EPS1.0 B4S!C T3CHN1QU3S.ONION) Becoming Virtually Untraceable (Eps1.0_B4s!c_T3chn1qu3s.onion) Ian Barwise Aug 10, 2018 Liam Neeson in “Taken 3” image courtesy ofFandango
PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS ANDSIGNUPRECENT
Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from191 countries.
HOW TO USE PEERLYST
How To Use Peerlyst. Peerlyst combines familiar social network capabilities with proprietary search technologies to connect you with peers and experts who can help you stay up to date and master the challenges of your job. POSTS ABOUT FIREWALL ANALYZER BY MANAGEENGINE ITOM Firewall Analyzer is a firewall policy, configuration management and log analytics software. SECURING REMOTE WORKSPACE DURI NG COVID-19 S e cu r i t y I n ci d e n t M o n i t o r i n g R e m o t e C o n n e ct i vi t y C o mmu n i ca t i o n C o l l a b o ra t i o n To o l s P h ysi ca l Wo rksp a ce ATTACK VECTORS FOR VEHICLES AND CONNECTED CARS Download This Resource as PDF:Attack Vectors for Vehicles and Connected CarsThe moderncarsandvehiclesuse electronic devices to transfer messages inreal time, operate thecarfrom remote locations,wifiaccess, andapplicationinstallation. The modern vehic JUNIPER NETWORKS COMPLETES AGREEMENT TO ACQUIRE MIST I am thrilled to announce that Juniper Networks’ acquisition of Mist Systems is now complete! Mist has a highly differentiated wireless solution that will strengthen and complement Juniper’s existing software-defined enterprise portfolio.As Rami menTOP "CHINA" POSTS
Read about "china" wiki, training, posts, blogs, discussions, overview, Q&A, vendors, products, and events. CREDIT SESAME ACCOUNT TAKEOVER If any of you folks use Credit Sesame, please read on.FYI, I just had my Credit Sesame account taken over yesterday. I received an email from them telling me my email had been changed to a Yahoo account I don't own. Based on the complexity and length BECOMING VIRTUALLY UNTRACEABLE (EPS1.0 B4S!C T3CHN1QU3S.ONION) Becoming Virtually Untraceable (Eps1.0_B4s!c_T3chn1qu3s.onion) Ian Barwise Aug 10, 2018 Liam Neeson in “Taken 3” image courtesy ofFandango
PEERLYST – A COMMUNITY OF INFORMATION SECURITY EXPERTS AND Peerlyst is the largest community of information security experts serving a million security professionals. Learn, share knowledge and advance your career.PEERLYST
Peerlyst was built as an open community for security professionals and was within 5 years served over 1 million cyber security experts from191 countries.
TRAINING MATERIALS, COURSES, E-BOOKS, ETC FOR INFOSEC Continuously updated resources on trainings, courses, certifications, etc on various information-security topics, for different paths and stages of an InfoSec career You need to enable JavaScript to run this app.Invite to discuss
__
__
Log In Sign Up
__
__
__
Write
__
Participate
Log In Sign Up
__
PARTICIPATE
__
Share your knowledge Write a post, ask a question. Use #tags to gain reputation for expertise. Review a @product/@vendor.__ Join experts on a panel Peerlyst have put together a panel to discuss "SOAR TRENDS IN 2020 ANDBEYOND"__
Add skills
Add areas of expertise to get personalized content and careeropportunities__
Personalize feed
Add your interests for a better experience__List a product
Get your product in front of 700,000+ cybersecurity professionals__Post a job
Find candidates from the 60,000+ information security professionalsactive on Peerlyst
__
__Edit
SHORTCUTS
_#_
covid-19
Cyborg C.O.R.E
Cyborg Security
Intezer
ManageEngine Dekstop Centralsāf.ai
sāf.ai CEFS
_#_
WFH
_#_
workfromhome
__
Home
__
Shortcuts
__
Write
__
Participate
WHERE PROFESSIONALS GET IT RIGHT DISCUSS SECURITY TOPICS Ask questions, debate hot topics, get breaking newsCONNECT WITH PEERS
Find tools, resources, and expertsBUILD YOUR BRAND
Share knowledge, promote your skills, advance your careerSign Up
__
LIST YOUR PRODUCT SPECIAL OFFERExplore
__Posts__
Featured Newest
__Security Resources__Newest How-to's
Wikis
Tools
Trainings
eBooks
Webinars
__MarketplaceNew
__Users__
Featured Newest
Popular
__Tags
__Products
__Companies
Meetups
__Security Events
BUSINESS ACCOUNT
Jobs__
__Search Jobs
__Post a Job
Shortcuts__Edit
_#_
covid-19
Cyborg C.O.R.E
Cyborg Security
Intezer
ManageEngine Dekstop Centralsāf.ai
sāf.ai CEFS
_#_
WFH
_#_
workfromhome
How to use Peerlyst FAQAbout In the News
Contact us Privacy
Policy Terms of ServiceCareers Get the
Peerlyst app
__ __
__
__Write Post
Featured
Peerlyst Partner
Cyborg Security
May 14, 20204K viewsView Post__
REGISTER NOW: 2020 SANS THREAT HUNTING SURVEY RESULTS WEBCASTREGISTER TODAY
:
Is Your Threat Hunting Effective? A New SANS Survey Wednesday, May 27, 2020 at 1:00 PM EDT (2020-05-27 17:00:00 UTC) Today, many organizations around the globe struggle with getting top-tier threat hunters. Although threat hunting has become a mandatory task to establish an acceptable level of security, the demand for skilled hunters far exceeds the number of a… Read more__Comment
__Upvote
22
__Share
5
__Bookmark
Be the first to comment on this post! Start the discussion...Featured
Peerlyst
7d ago2.4K viewsView Post__
PEERTALK™ PANEL: SOAR TRENDS IN 2020 AND BEYOND Peerlyst have put together a panel to discuss "SOAR Trends in 2020 and Beyond". Panelists: Anton Chuvakin (moderator), Security SolutionStrategy at Google
Cloud Richard Stiennon , Chief Research Analyst at IT-Harvest Payal Sampat , Leading Next-Gen Cyber SOC at HDFC Bank Dario Forte (Dario V ), Founder & CEO at DFLabs J. Wolfgang G… Read more
__Comment
3
__Upvote
17
__Share
5
__Bookmark
*
*
* GS
Richard Stiennon and 2 others are sharing insights Join the discussion...GS
Grant Suzuki 2d ago
__
Love the "pitfall of connector hidden costs" and "automation of workflows" guidance. I am an SE at a SIEM/UEBA/SOAR vendor, and have been a SOC consultant for decades. SOAR is a journey, but typically the initial strides are made automating predictable and tedious workflows like Phishing email investigation and response. My advice is to make sure you have clean signal. Ie. you… Read more__Reply
__Upvote
Richard Stiennon 6d ago__
Bunch of smart folks. I learned a lot!__Reply
__Upvote
2
__Older comments
Featured
Peerlyst
3d ago1.3K viewsView Post__
PEERLYST WEEKLY ROUNDUP (MAY 16TH - MAY 22ND) Featured PeerTalk™ Panel: SOAR Trends in 2020 and Beyond with Richard Stiennon , Dario V , Payal Sampat , J. Wolfgang Goerlich . Moderator: Anton Chuvakin Are you a vendor? "Super Boost" your post : $399 for 1 week! Book at vendors@peerlyst.com! Universal aspects of the evolving CISO roleby Gary Hayslip
The
most bookmarked post of t… Read more__Comment
1
__Upvote
3
__Share
3
__Bookmark
*
Basheer Ahmed Khan has shared insights Join the discussion... Basheer Ahmed Khan 3d ago__
Thanks for putting together a list of all the trending posts during this week. Also thanks for putting together important security resources Peerlyst .__Reply
__Upvote
2
Featured
Chiheb Chebbi
3d ago465 viewsView Post__
HOW TO START A BUG BOUNTY PROGRAM AT AN ORGANIZATION? Hi Peerlysters, How to start a bug bounty program at an organization? Thank you in advance.__Comment
6
__Upvote
3
__Share
3
__Bookmark
*
*
*
Hamza M'hirsi and 2 others are sharing insights Join the discussion... Chiheb Chebbi 1d ago__
Thank you for the resources J Geno __Reply
__Upvote
1
J Geno 3d ago
__
The download link from my previous favorite guide from hackerone no longer works. I am attaching my old copy; I dont think I'm violating any copright laws by doing so. To cover myself and Peerlyst: This is not my intellectual property, all rights belong to Hackerone. bug-bounty-field-manual__Reply
__Upvote
2
__1 reply
__Older comments
Featured
Peerlyst Partner
Cymulate
16h ago151 viewsView Post__
AUTOMATED PEN TESTING VS BREACH AND ATTACK SIMULATION Determine which solution is best for your organization! Basically, organizations want to know "can an attacker get in?" One approach to answer the question is to use pen-testing teams to attempt to breach your defenses. A second approach is to use Breach and Attack Simulation (BAS) tools to test the effectiveness of each security control and the combined effectiveness of you… Read more__Comment
__Upvote
1
__Share
3
__Bookmark
Be the first to comment on this post! Start the discussion...Featured
Jay W (NO53LF)
7h ago82 viewsView Post__
BRAINSTORM WALKTHROUGH, BUFFER OVERFLOW So I signed up for TryHackMe last week to compliment my studies for the eCPPT from eLearnSecurity , as I just finished the buffer overflow section I thought I'd tackle "Brainstorm"..... This was good fun so I did a write-up, it's in pdf on my GitHub here: buffer overflow pentest offense andexploitation
https://github.com/UbuntuStrike/H…
Read more
__Comment
1
__Upvote
3
__Share
2
__Bookmark
*
Tim Meyers has shared insights Join the discussion...Tim Meyers 21m ago
__
Good work Jay, keep it up and before you know it you will be doing ROP and JOP without Mona plugins 😁__Reply
__Upvote
Featured
Joseph Dunn
4d ago275 viewsView Post__
ENCRYPTION BACKDOORS: A PHYSICAL WORLD ANALOGY The topic of forcing tech companies to deliberately add backdoors in their encryption implementation for law enforcement is a common and recurring theme. I thought I would put this concept into a physical world (non cyber) scenario as a thought-provoking exercise. I will set the scene. A tragic act has occurred within a private residence in a small town which causes gr… Read more__Comment
3
__Upvote
4
__Share
3
__Bookmark
*
*
* IT
z3ro Trust and 2 others are sharing insights Join the discussion...z3ro Trust 8h ago
__
This article pretty much sums up my thoughts on the subject. https://www.peerlyst.com/posts/hacking-privacy-5-20-encryption-backdoors-in-the-name-of-national-security-z3ro-trust-1?trk=activity_feed__Reply
__Upvote
1
Dave Howe 3d ago
__
I usually go with "law enforcement only holes in encryption are like law enforcement only holes in body armour. the people you need to worry most about aren't going to respect the label"__Reply
__Upvote
__Older comments
Featured
Kapil Awasthi
9h ago59 viewsView Post__
ICS
Hi Experts I am setting up Cyber Security Monitoring System for a ICS Network Level 0 to level 5 . What are the Top Priorities for ICS system which should get reflected on dashboard . What information Our Weekly Report carry which makes sense to ICS people What all use cases we should depict on the Dashboard Feed back will be appreciated Regards kapil kapilawasthi@… Read more__Comment
__Upvote
__Share
3
__Bookmark
Be the first to comment on this post! Start the discussion...Featured
z3ro Trust
8h ago118 viewsView Post__
HACKING PRIVACY #5.20: ENCRYPTION BACKDOORS IN THE NAME OF NATIONALSECURITY
This article was originally published on Medium.com on May 24, 2020,here
.
If you enjoyed the read, please consider "clapping" for the article at the link above to support the furtherance of my security research. What happens when the citizens who elected the politicians finally decide that enough is enough and hit the delete button on their government? “The superior man, when … Read more__Comment
__Upvote
3
__Share
4
__Bookmark
Be the first to comment on this post! Start the discussion...Ender Pérez
9h ago57 viewsView Post__
TOP 10 BEST OPEN SOURCE INTELLIGENCE TOOLS (OSINT TOOLS) FOR PENETRATION TESTING – 2020 #CyberSecurity #infosec #OSINT #datasecurity #socialnetwork cybersecurity skills #CyberSecurity #infosec #OSINT #datasecurity #socialnetwork #CyberSec. https://cybersecuritynews-com.cdn.ampproject.org/c/s/cybersecuritynews.com/osint-tools/?amp__Comment
__Upvote
1
__Share
__Bookmark
Be the first to comment on this post! Start the discussion...Peerlyst Partner
Cymulate
16h ago184 viewsView Post__
16 WAYS BREACH AND ATTACK SIMULATION INCREASES CYBERSECURITY ROI Cyber defense costs rise year over year. According to CMS WiRE, costs associated with cyber crime have increased by 21%. With increasing costs, how can you make sure your security controls are producing a return on investment? In this whitepaper, we explore 16 ways of how breach and attack simulation technology can improve your cybersecurity ROI, including reducing penetration testing costs, impr… Read more__Comment
__Upvote
1
__Share
3
__Bookmark
Be the first to comment on this post! Start the discussion...Featured
Monsur M N Karim
15h ago193 viewsView Post__
THE ROLE OF PHYSICAL SECURITY IN 2020 According to Wikipedia, Physical security describes the security measures that are subject to save the services, equipment, assets, people, and possessions from damage or disruptions. In the below discussion we will discuss some important physical security trends in 2020: AI: Artificial Intelligence will gather serious momentum in 2020. In the coming days, the idea will become a reality. Through …Read more
__Comment
1
__Upvote
2
__Share
3
__Bookmark
*
Basheer Ahmed Khan has shared insights Join the discussion... Basheer Ahmed Khan 15h ago__
Thanks for sharing an excellent article Monsur M N Karim.
__Reply
__Upvote
Scroll Top
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0