Are you over 18 and want to see adult content?
More Annotations

A complete backup of http://yuinyan.net/
Are you over 18 and want to see adult content?
A complete backup of https://www.songtexte.com/
Are you over 18 and want to see adult content?

A complete backup of https://www.kaufmich.com/Latexmausi
Are you over 18 and want to see adult content?
A complete backup of http://onetouchscripter.com/support/
Are you over 18 and want to see adult content?

A complete backup of https://visionfornonviolence.weebly.com/
Are you over 18 and want to see adult content?
A complete backup of https://www.nekosubs.net/nekos/charlotte/watch/3639
Are you over 18 and want to see adult content?
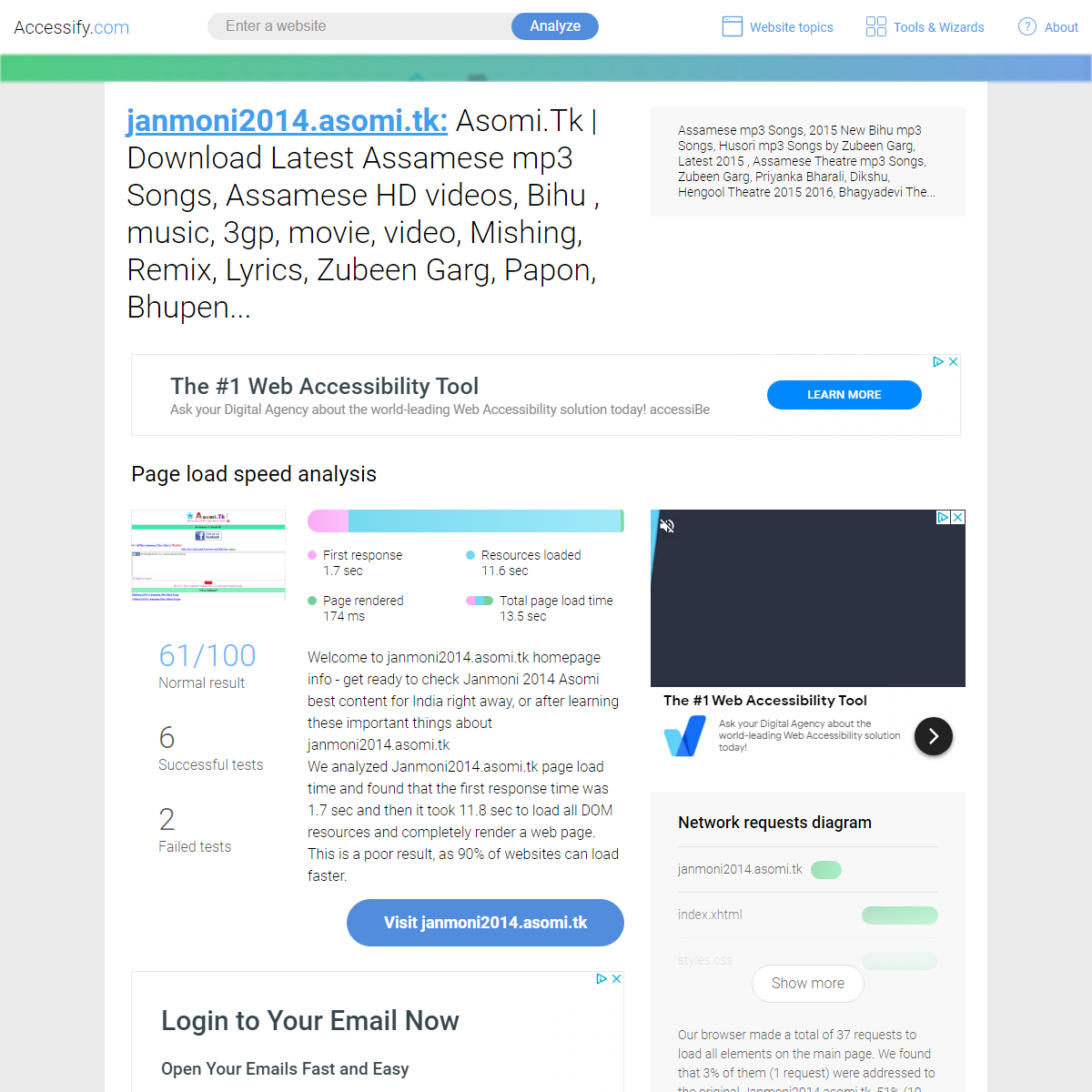
A complete backup of https://www.accessify.com/a/janmoni2014.asomi.tk
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of wanderlusttours.com
Are you over 18 and want to see adult content?
A complete backup of oscilloscope.net
Are you over 18 and want to see adult content?
A complete backup of das-erlebnisbad.de
Are you over 18 and want to see adult content?
Text
complete.
COME RIMUOVERE MAILTO RANSOMWARE DAI PC …TRANSLATE THIS PAGE Metodi facili e semplici per eliminare Mailto ransomware e recuperare file Hai mai visto il virus Mailto ransomware sul tuo sistema? Questo virus dannoso non è sicuro per la privacy online e le impostazioni di sistema. Secondo i cyber ricercatori, sono molto noti i malware e le infezioni del computer che appartengono alla famiglia dei ransomware. SO ENTFERNEN BUGSPLAT VIRUS (SCHRITTE GELÖSTE) Anleitung zur Beseitigen BugSplat virus Wenn Sie nach einer Lösung suchen, um durch BugSplat virus verursachte Probleme zu beheben, sind Sie hier richtig. Die hier beschriebene Lösung hilft Ihnen, lästige Probleme mühelos und mit minimalem Aufwand zu lösen. Es wird empfohlen, die gegebenen Anweisungen zu befolgen, indem Sie diesen Artikel sorgfältig lesen. RIMUOVERE ADWARE.RELEVANTKNOWLEDGE.DI: …TRANSLATE THIS PAGE Suggerimenti sicuri per eliminare Adware.RelevantKnowledge.DI Se stai cercando una soluzione per eliminare Adware.RelevantKnowledge.DI, hai raggiunto il posto giusto. Con la soluzione fornita in questa guida, sarete in grado di sbarazzarvi di fastidiosi problemi con facilità e il minimo sforzo. Si consiglia di seguire le istruzioni fornite leggendo attentamente questo articolo. USUŃ BOOKING.COM VIRUS (JAK ODINSTALOWAĆ BOOKING.COM VIRUS Łatwy proces, aby usunąć booking.com virus (proces ręczny) booking.com virus jest śmiertelną przeglądarka-porywacz, który jest bardzo zmanipulowana przez wygląd. To wygląda na portalu rezerwacji online, gdzie użytkownicy mogą zarezerwować hotele, bilety lotnicze i tak dalej. Funkcje te mogą być prawdziwe i jest pomocny, ale problem leży po stronie przekierowań internetowej i УДАЛИТЬ TROJAN:WIN32/OCCAMY.C: ЭФФЕКТИВНЫЙ …TRANSLATE THIS PAGE Легкие советы по устранению Trojan:Win32/Occamy.C Решение, приведенное в этой статье, поможет полностью удалить Trojan:Win32/Occamy.C и другие связанные с ним файлы. Это позволяет избавиться от этой угрозы со всех версий Windows, таких как JAK USUNĄĆ WEB COMPANION Z KOMPUTERA Czy Web companion jest bezpieczny? Web companion to aplikacja bezpieczeństwa dla komputerów PC, opracowana przez Lavasoft. Jest dostępny w postaci wtyczek do przeglądarek. W przeglądarce możesz zobaczyć dowolne wtyczki, takie jak "Ochrona sieci z uwzględnieniem reklam", "Wyszukiwanie bezpieczeństwa uwzględniające reklamy", "Blokada reklam ad-aware" i tak dalej. HOW TO REMOVE POWERSHELL.EXE (SOLVED GUIDE) Steps to eliminate Powershell.exe If you're seeking for solution caused by Powershell.exe file on your computer then you are at right place. The solution as given here in this article will help you fix troubles caused by this file. It allows you to solve this problem from all Windows versions such as XP, vista, 7, 8, 8.1, 10 and others. You just required following instruction by reading this CÓMO QUITAR ZPEVDO.A TROJAN (PROCESO RESUELTO) Pasos para eliminar Zpevdo.a virus Si su PC con Windows queda atrapada con la amenaza Zpevdo.a y está buscando su guía de eliminación, entonces ha llegado al lugar correcto. Con la solución dada en esta guía, podrá librarse de problemas molestos con facilidad y con un mínimo esfuerzo. Se recomienda seguir las instrucciones dadas leyendo este artículo cuidadosamente. USUŃ SSOPTION Z KOMPUTERA (PROSTE KROKI) Ssoption to wspierany przez reklamy potencjalnie niechciany program, który potajemnie dostaje się do docelowego komputera i powoduje wiele problemów dla jego użytkowników. Może łatwo dodać powiązane nieprzyjemne wtyczki i dodatki w popularnych przeglądarkach, takich jak Google Chrome, Mozilla Firefox i Internet Explorer i tak dalej. RIMUOVERE AA.ONLINE-METRIX.NET: PROCESSO DI …TRANSLATE THIS PAGE Conosci Aa.online-metrix.net Aa.online-metrix.net è stato rilevato come un virus deludente di reindirizzamento che attacca segretamente il computer mirato attraverso diversi modi ingannevoli e colpisce male la sua funzionalità di lavoro. Porta la capacità di reindirizzarti a vari portali web maligni e ridurre gravemente le sessioni webcomplete.
COME RIMUOVERE MAILTO RANSOMWARE DAI PC …TRANSLATE THIS PAGE Metodi facili e semplici per eliminare Mailto ransomware e recuperare file Hai mai visto il virus Mailto ransomware sul tuo sistema? Questo virus dannoso non è sicuro per la privacy online e le impostazioni di sistema. Secondo i cyber ricercatori, sono molto noti i malware e le infezioni del computer che appartengono alla famiglia dei ransomware. SO ENTFERNEN BUGSPLAT VIRUS (SCHRITTE GELÖSTE) Anleitung zur Beseitigen BugSplat virus Wenn Sie nach einer Lösung suchen, um durch BugSplat virus verursachte Probleme zu beheben, sind Sie hier richtig. Die hier beschriebene Lösung hilft Ihnen, lästige Probleme mühelos und mit minimalem Aufwand zu lösen. Es wird empfohlen, die gegebenen Anweisungen zu befolgen, indem Sie diesen Artikel sorgfältig lesen. RIMUOVERE ADWARE.RELEVANTKNOWLEDGE.DI: …TRANSLATE THIS PAGE Suggerimenti sicuri per eliminare Adware.RelevantKnowledge.DI Se stai cercando una soluzione per eliminare Adware.RelevantKnowledge.DI, hai raggiunto il posto giusto. Con la soluzione fornita in questa guida, sarete in grado di sbarazzarvi di fastidiosi problemi con facilità e il minimo sforzo. Si consiglia di seguire le istruzioni fornite leggendo attentamente questo articolo. USUŃ BOOKING.COM VIRUS (JAK ODINSTALOWAĆ BOOKING.COM VIRUS Łatwy proces, aby usunąć booking.com virus (proces ręczny) booking.com virus jest śmiertelną przeglądarka-porywacz, który jest bardzo zmanipulowana przez wygląd. To wygląda na portalu rezerwacji online, gdzie użytkownicy mogą zarezerwować hotele, bilety lotnicze i tak dalej. Funkcje te mogą być prawdziwe i jest pomocny, ale problem leży po stronie przekierowań internetowej i УДАЛИТЬ TROJAN:WIN32/OCCAMY.C: ЭФФЕКТИВНЫЙ …TRANSLATE THIS PAGE Легкие советы по устранению Trojan:Win32/Occamy.C Решение, приведенное в этой статье, поможет полностью удалить Trojan:Win32/Occamy.C и другие связанные с ним файлы. Это позволяет избавиться от этой угрозы со всех версий Windows, таких как JAK USUNĄĆ WEB COMPANION Z KOMPUTERA Czy Web companion jest bezpieczny? Web companion to aplikacja bezpieczeństwa dla komputerów PC, opracowana przez Lavasoft. Jest dostępny w postaci wtyczek do przeglądarek. W przeglądarce możesz zobaczyć dowolne wtyczki, takie jak "Ochrona sieci z uwzględnieniem reklam", "Wyszukiwanie bezpieczeństwa uwzględniające reklamy", "Blokada reklam ad-aware" i tak dalej. HOW TO REMOVE QAAGENT.EXE (SOLVED GUIDE) Steps to delete QAAgent.exe using Windows Scanner. Step 1: In first step, you need to download and save scanner software. Next open this application and click on run to start. Step 2: Follow the gives installation to complete its installation and finally click on finish button to exit from installation. HOW TO REMOVE HACKTOOL:WIN32/AUTOKMS TROJAN Effective Guide To Delete HackTool:Win32/AutoKMS HackTool:Win32/AutoKMS is a highly dangerous computer infection that belongs to Trojan horse's family. It has been discovered by the team of malware hacker with the main intention to damage the target System very badly and makes the System totally useless to perform any task. It is able to infect all kind of Windows based Operating System RIMUOVERE ADWARE.RELEVANTKNOWLEDGE.DI: …TRANSLATE THIS PAGE Suggerimenti sicuri per eliminare Adware.RelevantKnowledge.DI Se stai cercando una soluzione per eliminare Adware.RelevantKnowledge.DI, hai raggiunto il posto giusto. Con la soluzione fornita in questa guida, sarete in grado di sbarazzarvi di fastidiosi problemi con facilità e il minimo sforzo. Si consiglia di seguire le istruzioni fornite leggendo attentamente questo articolo. RIMUOVERE TROJAN.SCRIPT.AGENT.GEN (SOLVED GUIDE) Punti per eliminare Trojan.script.agent.gen Le informazioni qui fornite vi aiuteranno ad eliminare Trojan.script.agent.gen e tutti i suoi altri file correlati. Permette di sbarazzarsi di questa infezione brutto da tutte le versioni di Windows. Si consiglia di seguire le istruzioni fornite leggendo questo post. Trojan.script.agent.gen è un'infezione infettiva che segue segretamente tutti i SO ENTFERNEN BUGSPLAT VIRUS (SCHRITTE GELÖSTE) Anleitung zur Beseitigen BugSplat virus Wenn Sie nach einer Lösung suchen, um durch BugSplat virus verursachte Probleme zu beheben, sind Sie hier richtig. Die hier beschriebene Lösung hilft Ihnen, lästige Probleme mühelos und mit minimalem Aufwand zu lösen. Es wird empfohlen, die gegebenen Anweisungen zu befolgen, indem Sie diesen Artikel sorgfältig lesen. QUITAR TROJAN:WIN32/SKEEYAH.A!RFN Proceso manual para eliminar Trojan:Win32/Skeeyah.A!rfn. Trojan:Win32/Skeeyah.A!rfn es una infección de troyana desagradable que funciona también como un keyloggers. COME RIMUOVERE BEHAVIOR:WIN32/CEPROLAD.A …TRANSLATE THIS PAGE Passo 1: Innanzitutto è necessario scaricare e installare MacKeeper cliccando sul seguito dato link. Passo 2: Poi vai a trovare & difficoltà opzione per controllare lo stato corrente del Mac e quindi fare clic su elementi di correzione in modo sicuro per eliminare tutti i file infetti. Passo 3: Se trova & Fix opzione non risolve tutti i vostri problemi, è può fare uso di Geek funzionalit� JAK USUNĄĆ GOOGLE CRASH HANDLER VIRUS (WŁAŚCIWETRANSLATE THIS PAGE Google Crash Handler Virus to fałszywa aplikacja, która przedstawia się jako prawdziwy i uzasadniony Google Crash Handler. Na komputerze, na którym jest zainstalowany Google Chrome, bardzo ważna jest funkcja Google Crash Handler. Zawsze działa w tle podczas korzystania z Google Chrome i wysyła raporty do serwera Google dotyczące wszelkich problemów z awariami przeglądarki. USUŃ BOOKING.COM VIRUS (JAK ODINSTALOWAĆ BOOKING.COM VIRUS Łatwy proces, aby usunąć booking.com virus (proces ręczny) booking.com virus jest śmiertelną przeglądarka-porywacz, który jest bardzo zmanipulowana przez wygląd. To wygląda na portalu rezerwacji online, gdzie użytkownicy mogą zarezerwować hotele, bilety lotnicze i tak dalej. Funkcje te mogą być prawdziwe i jest pomocny, ale problem leży po stronie przekierowań internetowej i JAK USUNĄĆ WEB COMPANION Z KOMPUTERA Czy Web companion jest bezpieczny? Web companion to aplikacja bezpieczeństwa dla komputerów PC, opracowana przez Lavasoft. Jest dostępny w postaci wtyczek do przeglądarek. W przeglądarce możesz zobaczyć dowolne wtyczki, takie jak "Ochrona sieci z uwzględnieniem reklam", "Wyszukiwanie bezpieczeństwa uwzględniające reklamy", "Blokada reklam ad-aware" i tak dalej. Go to ... Go to ... HomeHow Spyhunter WorksBuy NowContact UsCookie PolicyMalware NewsUpdatesLatest ThreatSoftwareVideosSpyhunter 5: Efficient Malware Detection & Removal ToolMac User Guide* Home
* How Spyhunter Works* Buy Now
* Contact Us
* Cookie Policy
* Malware News
* Updates
* Latest Threat
* Software
* Videos
* Spyhunter 5: Efficient Malware Detection & Removal Tool* Mac User Guide
CATEGORIES
* Adware
* Application
* Backdoor
* Browser Hijacker
* Mac
* News
* PC Worms
* PUP
* Ransomware
* Rootkits
* Security news
* Trojan
* Uncategorized
* Updates
ARCHIVES
Archives Select Month March 2020 February 2020 January 2020 December 2019 November 2019 October 2019 September 2019 August 2019 July 2019 June 2019 May 2019 April 2019 March 2019 February 2019 January 2019 December 2018 November 2018 October 2018 September 2018 August 2018 July 2018 June 2018 May 2018 April 2018 March 2018 February 2018 January 2018 December 2017 November 2017 October 2017 September 2017 August 2017 July 2017 June 2017 May 2017 April 2017 March 2017 February 2017 January 2017 December 2016 November 2016 October 2016September 2016
RECENT POSTS
* Remove CoronaVirus Ransomware (How to restore files) * Remove Domainht5.cf: Working Tips * Remove Andapprovidej.info: Easy Instructions * Remove COVID-19 Cases Surpassed 300,000 Email Scam * Remove .vhd file virus (Recover Encrypted Files) * Remove Redfunchicken ads: Easy Instructions * How To Remove Pdo7e.com * Remove Trocarpment.info: Working Guidelines * Remove Isitedelirium.info: Easy Working Guide * How To Remove Pushmoder.com REMOVE CORONAVIRUS RANSOMWARE (HOW TO RESTORE FILES) March 26, 2020, Posted in Ransomware| No comments
GUIDE TO REMOVE CORONAVIRUS RANSOMWARE & RESTORE FILES EASILY A new and creepy ransomware is recently detected that seems to be very scary and drastic if affects a machine somehow. That ransomware is named as CoronaVirus Ransomware which can encrypt all files stored on computer using strong algorithms and lock down all files on computer using its own norms, and extensions. The victims can notice such files to be inaccessible and appended with a new suffix. The files in such cases get actually suffixed by an Email address that is coronaVi2022@protonmail.ch, and clicking such files probably opens a scary ransom note on screen. This ransom note basically includes details through which the victims are urged to contact hackers and seek developer’s help to restore their files. For an instance, take a look through the ransom note message here: CORONAVIRUS is there All your file are encrypted. Your computer is temporarily blocked on several levels. Applying strong military secret encryption algorithm. To assist in decrypting your files, you must do the following: 1. Pay 0.008 btc to Bitcoin wallet bc1q6ryyex33jxgr946u3jyre66uey07e2xy3v2cah or purchase the receipt Bitcoin; 2. Contact us by e-mail: coronaVi2022@protonmail.ch and tell us this yourunique ID:
and send the link to Bitcoin transaction generated or Bitcoin check number. After all this, you get in your email the following: 1. Instructions and software to unlock your computer 2. Program - decryptor of your files. Donations to the US presidential elections are accepted around the clock. Desine sperare qui hic intras! As the ransom note message justifies about CoronaVirus Ransomware, it’s technically just a developed creation of criminals through which they intend to extort innocent PC users based on their locked files. The criminals claim that such files can only be recovered or restored by receiving a valid decryption key and tools from hackers, and in order to get the same, paying demanded ransom fee or money to hackers is necessary. The victims can contact the hackers through provided email details included under the ransom note, in which they require to mention the assigned unique ID to them, through which the hackers can identity them and provide further help. Since the CoronaVirus Ransomware uses a very strong and powerful cryptography to lock down your files, you can hardly expect those affected files to be restored, but still you should not contact the criminals to seek theirhelp.
As per the researchers, although, the criminals may claim to provide you all help once they receive their demanded ransom amount, but this measure is technically unsafe and may lead victims to be financially scammed. The better thing the users can go is to take some suggested measures to identify and remove CoronaVirus Ransomware from their infected computers somehow, and attempt to restore their files with a lately created backup or some other possible file recovery measures. TECHNICAL SPECIFICATIONS ABOUT CORONAVIRUS RANSOMWARE Name: CoronaVirus Ransomware Type: Ransomware, cryptovirus Description: CoronaVirus Ransomware is another new vicious computer infection or ransomware that encrypts all stored files on machine and demands the victims to pay a hefty fee to hackers so as files can berestored back.
Distribution: Infected email attachments, torrent websites, maliciousadvertisements
Removal (File Restoration): For more information about detection and removal of CoronaVirus Ransomware, get through the guidelines sectionbelow
ABOUT INTRUSION OF CORONAVIRUS RANSOMWARE AND ITS REMOVAL MEASURES As per the researchers, CoronaVirus Ransomware mostly sneak on targeted computers through a number of hectic methods employed by cyber criminals. Some of such sources can be spam/junk email attachments, suspicious websites, freeware or shareware installer, bundled free applications, cracked software, malicious links, porn sites, and many more. Once this malicious code manage to enter, it will disable all security ends to compromise the system and its security aspects. Also, the malware will change computer’s desktop wallpaper that shows ransom message on screen. According to ransom message, the user if not pay demanded sum to hackers and get not the decryption key within specified time limit, the malware will delete all stored files completely. So, the overall impacts are really scary and the malware should be treated, but not through the instructions as recommended by ransom note, but through methods suggested by experts. If you got your machine infected by CoronaVirus Ransomware, then you should instantly treat your computer as quick as possible. Paying ransom money to hackers will just lead you to suffer high potential losses in terms of data as well as financial status too. To keep the hassle and risks away, we suggest you to try here included automatic method that will assist you cleaning your machine against CoronaVirus Ransomware and all associated files, processes and leftovers. Also, you can attempt to clean your machine manually with the guidelines included that may also assist you to clean your machine through yourself. Once the threat is completely removed, the victims can choose their own lately created backup files to restore their files. Alternatively, some other methods can also be helpful which are included under this article later.Read More
REMOVE DOMAINHT5.CF: WORKING TIPS March 26, 2020, Posted in Browser Hijacker| No
comments
QUICK & EASY GUIDELINES TO REMOVE DOMAINHT5.CF Domainht5.cf is a vicious domain that may appear helpful to users at first sight however its reality is very harsh because it’s one of the malicious one aims only to hijack all pre-installed browser settings on Windows. The site actually enforce users to subscribe its push notification spam service by claiming that it’s necessary in order to view content of the webpage. And once the user clicks to subscribe the push notification service powered by Domainht5.cf, all their browsing sessions start to get filled with regular spamming pop ups or banners throughout the day. The problems related to Domainht5.cf hijacking may appear on all popular browsers whether you are using Chrome, Firefox, Opera, Safari, IE, Edge, or whatever you have installed. So, it’s technically obvious and expected for victims to face off tons of problems while surfing the web and that makes it essential to detect and terminate Domainht5.cf out of yourmachine in no time.
THREAT SUMMARY
Name: Domainht5.cf
Type: Browser hijacker, adware Description: Domainht5.cf is discovered as a new vicious computer infection that mostly get assail on computers without any prior notice and affects all your online sessions further to bring intolerable chaos. Therefore, it’s necessary to detect and terminate Domainht5.cf out of a machine completely for which here included guidelines can be helpful. Distribution: Malicious file downloads, clicking links or ads on suspicious websites, spam email attachments, social engineering attacks, and many more. Removal: For more information about detection and removal of Domainht5.cf, follow the guidelines here included under this article. HOW DOMAINHT5.CF INTRUDES AND WORKS? HOW IT SHOULD BE TACKLED? So, the problems related to Domainht5.cf will begin to appear on your machine only after the user clicks Allow button as the site recommends at very initial. And clicking the same allows the site to throw push notifications further on screen which makes the online sessions bombarded with endless of fake or unwanted advertisements. Even such pop ups may appear when the browsers are not launched but system is connected to web, which also makes the PC usage annoying. If we speak about its intrusion on a targeted computer, potentially, there are various possible methods through which Domainht5.cf may get intruded on targeted computers without any prior notice, while some common of them includes third party software bundling, freeware or shareware installer packages, visiting porn sites, playing or installing free online games, and so on. If you are addicted to do these aforementioned interaction, then you should be very careful every time as these stuffs often comes with additional offers which are never disclosed to users in prior, and further leads to unwanted installation of Domainht5.cf on victim computers. If you have got your machine infected by Domainht5.cf after you have clicked on push notification button then you can easily disallow the same in browser settings to get rid of such unwanted eruptions on screen in no time. However, the same can be disturbing for normal or non technical users. Also, the overall removal process may become complex if an adware or PUP associated with Domainht5.cf gets installed. In such instances, we recommend to choose and follow here mentioned guidelines to remove Domainht5.cf from your compromisedmachine.
Read More
REMOVE ANDAPPROVIDEJ.INFO: EASY INSTRUCTIONS March 26, 2020, Posted in Browser Hijacker| No
comments
QUICK MEASURES TO REMOVE ANDAPPROVIDEJ.INFO Have you just started to see Andapprovidej.info pop ups and redirect issues while browsing the web? Are you unable to surf the web safely as this nasty hijacker keeps redirecting you to unwanted pages throughout the day? In case if your computer seems facing problems due to this website, then reading this article is strongly recommended. According to experts, the term Andapprovidej.info is just a piece of hectic browser hijacker or redirect virus that tends to hijack all web browser variants installed on computer such as Chrome, Firefox, Opera, Safari, IE, Edge and so on without any prior notice, and redirects almost all your browsing preferences to its own sponsored websites or pages. The malware can modify homepage, search engine defaults, new tab settings, and many other critical settings which turns the PC access terrible specially while the system is being used for online sessions. This website actually used by cyber criminals to promote its own sponsored contents on targeted browsers through which the criminals tend to earn cyber crime profit. However the impacts caused by this redirect virus on a computer leads users to suffer high potential issues or loss as well if not controlled in real time.THREAT SUMMARY
Name: Andapprovidej.info Type: Browser hijacker, redirect virus Description: Andapprovidej.info is said to be a creepy redirect virus or browser hijacker that modiofies all active browsers on targeted computer to show up tons of irritating advertisements throughout the web surfing sessions. Distribution: Spam/junk email attachments, freeware or shareware installers, malicious file downloads, and many more. Removal: For detailed information about detection and removal of Andapprovidej.info, we suggest you to follow here mentioned guidelines HOW ANDAPPROVIDEJ.INFO MOSTLY INTRUDES AND CAN BE RISKY? The malicious codes of browser hijacker often spread over web in form of bundled free software downloads, pirated software copies, cracks or patches, suspicious file downloads, and many more. The criminals use to spread these embedded objects using various social engineering techniques or file sharing methods, which causes victims to download and install these vicious things on their system without consent of hidden malicious objects. As a result, they start to face off hecitc issues on their browsers. Also, those unintentionally modified settings can hardly be restored unless the victims follow a set of recommended instructions carefully. And in order to accomplish this task, the victims must know some possible measures or details which are included under this article. In order to remove Andapprovidej.info from an infected computer completely, it’s suggested to detect and remove Andapprovidej.info along with all its associated files, processes and leftovers completely. Although, doing this taks on a compromised computer is not an easy task, still if the victims follow a few set of suggested instructions or steps carefully, they might end up cleaning their machine easily. Well, in case if you are one among the victims and seeking some helpful measures or guidelines that can help cleaning your machine, we suggest you to follow the steps included. In alternative conditions, the non technical users can also check and try suggested automatic solution to justify if the app can helpful to clean malware strikes easily.Read More
REMOVE COVID-19 CASES SURPASSED 300,000 EMAIL SCAM March 26, 2020, Posted in PUP| No comments
MEASURES TO REMOVE COVID-19 CASES SURPASSED 300,000 EMAIL SCAM SAFELY Since the world now suffering panicking conditions caused due to Corona Virus effect, a number of fake emails are being circulated that appears to be from Centers for Disease Control and Prevention (CDC) organization and pretends to share information about the virus its growth these days. The attackers who actually circulating these phishing emails just want to trick users into clicking some links through which the victims are supposed to open a website that allows them to track all recent Covid-19 cases. As per the researchers when they checked the email scam, they found the link has opened a fake Microsoft Outlook login page, and the scammers are intended to let users feeding their details into login form. Speaking about the facts related to COVID-19 Cases Surpassed 300,000 Email Scam, this email is no connection with actual Centers for Disease Control and Prevention organization, and it’s very common for cyber crime master minds to disguise their emails to appear as official and important. In order to do so, they may use of various well known and reputed companies, organizations and other possible structures as well. Since it’s already mentioned that researchers have found the email and its link opening a fake Outlook login page, it just want users to feed their login credentials and details into a form. Doing these, the hackers intend to steal your personal outlook details. They can further manage to hijack your other accounts too as the users often use those same details for their own personalaccounts.
Through collecting details feed by users into fake outlook login page, the hackers can also utilize such information to spread more other scams, send people more emails with malicious attachments and contents, access your sensitive information, and even may install some rogue trojans or malware on system to steal more data to turn you into paying them money. Therefore, the overall impacts of COVID-19 Cases Surpassed 300,000 Email Scam is really terrible and should not be left ignored. The very essential thing you can do is to avoid clicking or interacting with COVID-19 Cases Surpassed 300,000 Email Scam if you are receiving the same through your email Ids. However, in case if you somehow managed to interact with those emails, you should clean your system against any malicious entries that might slipped down on your machine without your consent.THREAT SUMMARY
Name: COVID-19 Cases Surpassed 300,000 Email Scam Type: Browser hijacker, redirect virus Description: COVID-19 Cases Surpassed 300,000 Email Scam is said to be a nothing more than a scam technique utilized by cyber crime master minds to circulate malware terms on global basis. It’s mostly utilized to steal secret credentials or data through which more cyber crimes can be committed. Distribution: Spam/junk email attachments, freeware or shareware installers, malicious file downloads, and many more. Removal: For detailed information about detection and removal of COVID-19 Cases Surpassed 300,000 Email Scam, we suggest you to follow here mentioned guidelines HOW DO COVID-19 CASES SURPASSED 300,000 EMAIL SCAM CAN AFFECT A COMPUTER AND SHOULD BE SORTED OUT? The system and its OS may get affected through COVID-19 Cases Surpassed 300,000 Email Scam messages when the victims end up opening files or downloading them through provided links or attachment. As noticed in most of the instances, the criminals use to send emails containing MS Office documents, PDF documents, java script files, exe files, and so on, which if get executed on a machine, may bring serious chaos to users without any prior notice. Therefore, the victims must be cautious against these intruders and scams, also, they should avoid interacting with any such hectic resources that may drive just bunch of issues on targeted machine. If your system started to throw some issues as well after interaction with COVID-19 Cases Surpassed 300,000 Email Scam, we suggest you to clean your machine against malicious entries or malware with help of guidelines includedunder this article.
Read More
REMOVE .VHD FILE VIRUS (RECOVER ENCRYPTED FILES) March 25, 2020, Posted in Ransomware| No comments
REMOVE .VHD FILE VIRUS AND RESTORE ENCRYPTED FILES .vhd file virus is discovered as a highly precarious ransomware infection that is prone of locking down all your files completely and demands a hefty ransom amount to pay to hackers. This hectic ransomware is created by cyber crime master minds with sole intention to harass users tactically and cheat their hard earned money as extortion profit. The malware usually gets installed on targeted computers without seeking any permission in prior, following which it starts to lock down all your personal and important files using a powerful encryption algorithm and adds its own extension (.vhd) to those affected files after which such files become inaccessible to users in real time, and every time they try accessing those, a ransom note is thrown on screen. This note states that users about the ransomware and how they can seek restoration of their personal files by contacting hackers and pay them with their demanded ransom fee. Here comes the message which .vhd file virus included under itsransom note:
All data on your pc were encrypted with strongest encryption method. The only way to get your data back is to purchase unique key for you. * You can get cheaper price if you contact us as soon as possible. * After three days from now, it will be difficult to recover your data.Good Luck.
contact address:
miclejaps@msgden.net stevenjoker@msgden.net As per the ransom note, all files on computer are encrypted by with the strongest ciphers and those files can only be restored by using a valid decryption key and software provided by developers of this ransomware. The victims need to purchase the key and tool by contacting them as soon as possible. The ransom note also includes that victims have only 3 days to accomplish file restoration, following which the decryption key specific to a user will be destroyed. And the users can’t restore their files in such cases. In order to contact the hackers, the ransom note also includes two email IDs which are miclejaps@msgden.net and stevenjoker@msgden.net. So, the victims are required to contact hackers and seek their help in order to overcome issues caused by encryption of this creepy ransomware. Although, the criminals claim to provide users with decryption tool or software to allow users restoring files, the victims should never believe those messages to be true. Even after the victims end up paying demanded ransom fee to hackers, they will get no help from those and may get scammed. So, it’s better for users to avoid contacting criminals to seek their help, rather, the users should try some alternative measures to remove .vhd file virus and restore their files, the guidelines are explained under this article. THREAT SPECIFICATIONS Name: .vhd file virus Type: Ransomware, cryptovirus Description: .vhd file virus is another new vicious computer infection or ransomware that encrypts all stored files on machine and demands the victims to pay a hefty fee to hackers so as files can berestored back.
Distribution: Infected email attachments, torrent websites, maliciousadvertisements
Removal (File Restoration): For more information about detection and removal of .vhd file virus, get through the guidelines section below HOW .VHD FILE VIRUS ASSAILS ON TARGETED COMPUTER AND SHOULD BETREATED?
The vicious computer infection .vhd file virus is really a notorious piece and silently sneaks on targeted computers without any prior notice. This threat is presumed to be carried through bundled third party applications, spam or junk email attachments, suspicious websites, and through other possible tricks as well. So, once the threat is installed on targeted computer, will block all installed security apps like antivirus or firewall, following which the malware manage to execute all its malignant activities on targeted computers. Therefore, the users should be protective while interacting various risky online web sources that includes porn sites, data sharing networks, P2P networks, and so on. Even transferring data using contaminated USB drives may also be risky at all. To treat a ransomware infections on targeted computers, the victims should never choose what the hackers actually suggest through deployed ransom note. They actually suggest victims to pay the hefty demanded sum and buy a decryption key which can be utilized for decryption of files. However, this is just a trap created by cyber criminals to earn profit and leave infected files intact. To overcome the issues caused by .vhd file virus on a targeted computer, we suggest you to follow here included guidelines or method which will assist you cleaning as well as restoring your files either with a lately created backup file or through some other data recovery solutions.Read More
REMOVE REDFUNCHICKEN ADS: EASY INSTRUCTIONS March 25, 2020, Posted in Adware| No comments
TECHNICAL ASSISTANCE TO REMOVE REDFUNCHICKEN ADS SAFELY Are you facing Redfunchicken ads pop ups or commercial banners on screen that redirects you often to malicious or phishing websites? Are you got fed up with those problematic eruption on screen caused by Redfunchicken ads and needs these eruptions to be terminated permanently? Well, in case your answer to these interrogations are yes, then you must read this article to learn some effective guidelines or methods following which the removal of Redfunchicken ads can easily be perceived in no time. Also, you can assure your system being safe against all massive intruders with some prevention tips that allows you to identify and avoid interacting with any such web sources which often promote the objects like Redfunchicken ads on web. These sources are basically the main cause through which a user end up having the adware objects like Redfunchicken ads installed on their machine following which their overall system performance gets drastic. So, if you are facing hassles caused by Redfunchicken ads, then you must read this article to learn how to sort out the issues completely.THREAT SUMMARY
Name: Redfunchicken ads Type: Browser hijacker, redirect virus Description: Redfunchicken ads simply indicates to an adware that is residing on targeted computer somehow and may bring you to face off various fake or deceptive adverts that may cause your system to suffer high potential loss in no time if remains untreated. Distribution: Spam/junk email attachments, freeware or shareware installers, malicious file downloads, and many more. Removal: For detailed information about detection and removal of Redfunchicken ads, we suggest you to follow here mentioned guidelines DETAILED INFORMATION ABOUT REDFUNCHICKEN ADS The term Redfunchicken ads is technically a way for malware creators to attack and invade targeted computers globally and to deceive users and their personal values through showing spam notifications on screen. Based on its attributes, the experts also call this hectic program as an adware or browser hijacker that configures all active browser settings on Windows and keep users redirected to a number of malicious of phishing pages which are either loaded with tons of irritating advertisements, or some hectic techniques which can intrude system with more malware or enforce users into clicking some links. Although, these problems may appear not much harmful to affect overall computer system and its related aspects initially. But the risks associated with a browser hijacker is still very high that makes the detection and removal of Redfunchicken ads mandatory from targeted computers. In most of the circumstances, the unintentional presence of Redfunchicken ads mostly takes place due to user’s own mistakes as they often visit a number of web sources which offers tons of free options with false proclaims. Some commonly known such sources can be a freeware or shareware distribution sites, torrent based networks, free gaming sources, and many more. To assure your system security and data consistency, it’s strongly recommended to be strictly cautious while interacting with those mostly interacted sources as they often provide you with freebies to help you, but such objects may even come hidden with other hectic source codes which will destroy your PC usage disastrously. To overcome such issues completely and to remove Redfunchicken ads from a compromised system, we suggest you to identify and terminate all associated files, processes and leftovers with this adware. In order to accomplish this task, the victims can try following here included guidelines under this article.Read More
HOW TO REMOVE PDO7E.COM March 25, 2020, Posted in Browser Hijacker| No
comments
QUICK MEASURES TO REMOVE PDO7E.COM As per the researchers, the term Pdo7e.com is nothing more than a browser hijacker or an ad supported application interacting with which may lead you to a number of advertising websites. Most of such redirected websites can be identified as questionable or misleading ones that may cause hectic issues on computer. The experts have to say, the users often get redirected to Pdo7e.com to open this website due to some adware or PUP which usually get installed on computer while installing some questionable applications or browser extensions. Technically, an adware is just an application which leads to numerous advertisements which are somehow scam and is just meant to redirect to Pdo7e.com and similar nasty websites, which also affects your online sessions further. Since Pdo7e.com belongs to category of browser hijackers, the victims can expect to have their browser settings like homepage, search engine, new tab url, and other possible defaults are modified by Pdo7e.com. So, every time they attempt to access web sessions, they will get redirected to more nasty or unsafe websites sponsored by Pdo7e.com. Although, browser hijackers may technically appear not much harmful like other vicious malware objects, but still its overall potential may cause serious issues if not treated in real time. Its longer term presence can modify registry settings, MBR, administrative values, and so on. Thus, the system is really expected to suffer more hectic issues as its present vulnerabilities will be exposed to morecriminals.
In addition to these issues, the Pdo7e.com may also create some hidden security loophole or backdoor taking advantage of which more malware intruders may affect the system. Also, the cyber crime master minds may intrude such machine with their RAT or other malicious objects which altogether can manage to keep a keen eye over all your personal information, browsing details, financial information and so on. Such details can also be stolen and misused for cyber crime purposes. Therefore, the term Pdo7e.com should not be underestimated, and should be eliminated from infected computers as quick as possible once its presence is noticed.THREAT SUMMARY
Name: Pdo7e.com
Type: Browser hijacker, redirect virus Description: Pdo7e.com is said to be a creepy redirect virus or browser hijacker that modifies all active browsers on targeted computer to show up tons of irritating advertisements throughout the web surfing sessions. Distribution: Spam/junk email attachments, freeware or shareware installers, malicious file downloads, and many more. Removal: For detailed information about detection and removal of Pdo7e.com, we suggest you to follow here mentioned guidelines HOW PDO7E.COM ADWARE OR BROWSER HIJACKER GET INSTALLED? HOW TO TERMINATE THIS INFECTION? As noticed in most of the instances, the adware or browser hijacker like Pdo7e.com get installed on computer while installing certain freeware or shareware objects like email checker, PDF converter, video codecs, and many more. These free installer often come bundled or packed with more third party installers which are never disclosed to users in prior. Even some reliable download sources may also promote such freebies which often get interacted by global users. And this kind of online interaction simply risks the system unless the user is technically capable of identifying and blocking such unwanted installers in real time. To do so, the users should be cautious while downloading/installing any freebies. However, in case if a system get infected, the users should remove Pdo7e.com sooner from infected machine, for which here mentioned instructions or steps will easilyhelp.
Read More
REMOVE TROCARPMENT.INFO: WORKING GUIDELINES March 25, 2020, Posted in Browser Hijacker| No
comments
STEP BY STEP MEASURES TO REMOVE TROCARPMENT.INFO Researchers have identified a new and misleading website url Trocarpment.info that is designed with sole intention to make users allowing its spam notifications. Once the site is allowed, it starts to throw tons of irritating pop up banners or adverts on screen throughout the web surfing sessions. When this site is opened for first time somehow, it display users to Confirm notification pop up on screen and tells that allowing the same is mandatory in order to download a file from the site, enable flash player, watch its content, or just access any of its content, and many more. Employing all these tricks on targeted computer, the Trocarpment.info simply intends the users to click allow button somehow, following which the site starts to throw promotional contents. Means, in case if a user somehow clicks to allow push notifications from Trocarpment.info, the victims can expect to see notification pop ups in the right bottom corner of the screen that includes annoying advertisements, leading to misleading websites or spamming online sources. In technical terms, Push Notification is a genuine browser option that allows users to be notified about new posts and updates from the site they want to subscribe. Allowing this feature for a page simply keeps the webpage url into allowed list and ad-blocker of browser simply allows those notifications to appear without beingblocked.
But the Trocarpment.info is just a scamming website created for illicit intentions and any of its advertisements is just to deceive users and their values. Such ads may be related to scamming websites, enforcing users to install some browser extensions, and so on. If you have accidentally subscribed to push notifications from Trocarpment.info, then you can easily get rid of the same by modifying some settings in browsers. For more information about removal of Trocarpment.info pop ups or related adware out of your machine, follow the guidelines included under this article.THREAT SUMMARY
Name: Trocarpment.info Type: Browser hijacker, redirect virus Description: Trocarpment.info is said to be a creepy website that brings nasty notifications or pop ups on screen that will turn your overall online sessions to be extremely drastic. Distribution: Spam/junk email attachments, freeware or shareware installers, malicious file downloads, and many more. Removal: For detailed information about detection and removal of Trocarpment.info, we suggest you to follow here mentioned guidelines. HOW A SYSTEM MAY GET INFECTED BY TROCARPMENT.INFO? HOW IT SHOULD BEREMOVED?
As per the researchers, none of the users will intend themselves to visit or interact with Trocarpment.info through their own, rather than clicking some shady advertisements or due to secret installation of some adware or PUPs inside their machine. This kind of nasty objects often come packed or bundled with various freeware or shareware objects, suspicious websites, porn contents, installing some browser extensions or addons, and many more. To keep such hassles away, the victims should be very cautious while doing any such online interactions. Also, they should choose Advanced/Custom installation mode while installing some freebies to find and de-select any such options which are unwanted or unsafe. In order to learn how to detect and eradicate Trocarpment.info out of an infected computer completely, get through the guidelines section included under this article.Read More
REMOVE ISITEDELIRIUM.INFO: EASY WORKING GUIDE March 24, 2020, Posted in Browser Hijacker| No
comments
STEP BY STEP GUIDELINES TO REMOVE ISITEDELIRIUM.INFO Researchers have identified another new vicious computer infection by name Isitedelirium.info that makes your whole internet surfing sessions disastrous by promoting fake or scamming adverts on screen. No matters you have what browsers installed and activated, the malware is capable to work with all well known browser variants such as Chrome, Firefox, Opera, Safari, Ie, Edge, and so on. However, the installation of such vicious objects hardly takes place on its own unless the user somehow interact with some online sources or free of cost shared objects which have embedded codes with them. As a result, once such vicious objects are installed or executed on a system once, the hidden malicious programs also runs in background and manipulate with all browsers’s settings such as homepage, search engine, proxy, DNS, and other critical values as well. In addition, the Isitedelirium.info also alters some Windows administrative areas of settings like MBR, registry settings, control panel settings, etc as well to keep itself undetected for long time. This is why the overall detection and removal of Isitedelirium.info becomes a hard task and require users to follow some recommended removal measures. The vicious terms like Isitedelirium.info are mostly referred as hectic browser hijackers because it actually hijacks all web browser settings with sole intention to help its creators to promote third party malicious stuffs on targeted computers. The hackers are actually partnered with many third party advertisers who never care about user’s benefits rather than just promoting scam campaigns and other destructive product. However, the Isitedelirium.info once manage to configure your browser settings according to its own, the victims are expected to face of such vicious online sources while surfing the web, and the same can cause them to have more malware installed, increased chances of hacker’s attack, unwanted increment in present system vulnerabilities, and so on.THREAT SUMMARY
Name: Isitedelirium.info Type: Browser hijacker, redirect virus Description: Isitedelirium.info is another vicious computer infection which mostly assail on targeted computers without any prior notice and affects overall online sessions terribly. Distribution: Spam/junk email attachments, freeware or shareware installers, malicious file downloads, and many more. Removal: For detailed information about detection and removal of Isitedelirium.info, we suggest you to follow here mentioned guidelines HOW ISITEDELIRIUM.INFO IS SPREAD OVER WEB? HOW TO TREAT INFECTEDCOMPUTER?
In order to spread the vicious code related to Isitedelirium.info over web, the malware creators use a number of tactical methods like software bundling, data distribution through network sharing, email spamming, social engineering attacks, and many more. Even using an infected external media for data transfer can be equally responsible for such malware distribution if not used properly. This is why, it’s often recommended by experts to be careful about these intruders and used terms by its creators to distribute them. Although accomplishing the protection on a machine without technical skill is really very hard, choosing some right and appropriate solutions can easily work to prevent malware impacts as far as possible. In case your system got affected by Isitedelirium.info, then you might be worried about its removal from your infected machine, the best procedure we recommend you is to choose a powerful automatic solution which will easily detect all present malware intruder on your machine hassle free. Rather, some technically recommended manual steps can also be helpful, but following these instructions require users to be very proper while following the guidelines. Doing something improperly may cause more problems that can hardly be reverted back. So, the users can also try automatic solution here to check if the app can clean their machine hassle free.Read More
HOW TO REMOVE PUSHMODER.COM March 24, 2020, Posted in Browser Hijacker| No
comments
QUICK MEASURES TO REMOVE PUSHMODER.COM Pushmoder.com is found as a new malicious computer infection that can be categorized as a browser hijacker or a redirect virus. This kind of malicious programs are tactically developed by cyber crime master minds with sole intention to display tons of irritating spam advertisements, and cause redirects to various spamming websites or pages which altogether makes the PC usage disastrous. In some cases, such adverts will even enforce you to download and install some free software options like fake security apps, software updates, media player updates, and many more. However, the users are strongly recommended to click or interact with such elements because such objects may have hidden malicious source codes which can affect your computer’s overall performance, speed, data consistency, and even your personal privacy as well. The very first thing you will come to notice after having Pushmoder.com installed on your machine is modified browser settings. Actually a browser hijacker like Pushmoder.com mostly use to affect all pre-installed browser settings like homepage, search engine defaults, new tabs, proxy defaults, and many more. So, the victims can expect their online sessions to be completely modified and keeping them affected throughout the day. Although, browser hijackers are not like typical viruses or malware kinds such as Trojans or ransomware, but still its way to hijack browsers and enforcing users to visit malicious pages, might end up installing vicious things on targetedcomputers.
As a result, the system may even throw such issues which are technically not caused by a hijacker application. Such issues can be slow PC performance, corrupted or unintentionally deleted files, non functioning web applications, failure of system due to lack of system resources, and so on. Also, your personal details like IP addresses, bank details, login credentials, etc can be misused by third parties. Therefore, the detection and removal of Pushmoder.com is highly recommended and in order to do so, we suggest you take some suggested removal measures in practice as quick as possible.THREAT SUMMARY
Name: Pushmoder.com
Type: Browser hijacker, redirect virus Description: Pushmoder.com is said to be a creepy computer infection or a browser hijacker that mainly assails on targeted computers withou any prior notice, and display tons or irritating advertisements, and even redirect based issues throughout the web surfing sessions. Distribution: Spam/junk email attachments, freeware or shareware installers, malicious file downloads, and many more. Removal: For detailed information about detection and removal of Pushmoder.com, we suggest you to follow here mentioned guidelines HOW PUSHMODER.COM ASSAILS AND SHOULD BE TREATED? As seen in most of the circumstances, the malware term like Pushmoder.com will easily assail on targeted computers without seeking user’s permission in prior. This mostly comes in form of bundled freeware or shareware installer, malicious attachments with spam or junk emails, scripts or links on malicious websites, and many more. In all these instances, the users are mostly shown with various proclaims which appears to be helpful for users, but as soon as they end up interacting with those, their system starts to throw tons or irritating problems in form of hijacked browser settings. Also, the malware replicates its presence through affecting other critical settings as well like Windows registry files, MBR, and so on. Thus, in case if your machine is behaving abnormal due to unintentional presence of Pushmoder.com, then you should terminate Pushmoder.com from your compromised system completely. Here included methods or guidelines might assist you to accomplish the removal in easy manner.Read More
Next Page
*
*
*
* Share
Copyright © 2020 PC Virus Care - Complete Caring Tips To Eliminate PC Viruses Designed by coque iphone 5 , thanks to: coque ipad , motorcycle fairingsand r4 3ds
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0