Are you over 18 and want to see adult content?
More Annotations

A complete backup of wspolnoty-jerozolimskie.pl
Are you over 18 and want to see adult content?

A complete backup of monkeybreadsoftware.de
Are you over 18 and want to see adult content?

A complete backup of helpcomputerguides.com
Are you over 18 and want to see adult content?

A complete backup of communityamerica.com
Are you over 18 and want to see adult content?

A complete backup of virtualfinalabraham.blogspot.com
Are you over 18 and want to see adult content?
A complete backup of becomeablogger.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of creditform.co.kr
Are you over 18 and want to see adult content?
A complete backup of brasilcard.com.br
Are you over 18 and want to see adult content?
A complete backup of technologywatchpost.com
Are you over 18 and want to see adult content?

A complete backup of pointschauds.info
Are you over 18 and want to see adult content?
A complete backup of lakotaonline.com
Are you over 18 and want to see adult content?

A complete backup of galleria-mall.jp
Are you over 18 and want to see adult content?

A complete backup of erisay-traiteur.fr
Are you over 18 and want to see adult content?
Text
FREE LEARNING
Free Forever. On top of your daily Free Learning eBook, you can access over 30 premium titles that we've handpicked for quality across a diverse range of tech. These are yours to access online forever with a free account. Create powerful data visualizations and unlock intelligent business insights with Tableau. LIMITLESS ANALYTICS WITH AZURE SYNAPSE Limitless Analytics with Azure Synapse. By Prashant Kumar Mishra. $5 for 5 months Subscribe Access now. Print. $34.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. MASTERING EMBEDDED LINUX PROGRAMMING Mastering Embedded Linux Programming - Third Edition. By Frank Vasquez , Chris Simmonds. Start FREE trial Subscribe Access now. Print. $34.99 eBook Buy. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. ASP.NET CORE SECURE CODING COOKBOOK ASP.NET Core Secure Coding Cookbook. By Roman Canlas. $5 for 5 months Subscribe Access now. Print. $27.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. Breadth and depth in over 1,000+ technologies. PRACTICAL DISCRETE MATHEMATICS "A set is a Many that allows itself to be thought of as a One." – Georg Cantor. In mathematics, set theory is the study of collections of objects, which is prerequisite knowledge for studying discrete mathematics.. Definition–Sets and set notation. A set is a collection of objects. If a set A is made up of objects a1, a2, , we write it as A = {a1, a2, }. BECOME A PACKT AUTHOR Writing with Packt. So you want to write a tech book but you don’t know where to begin. Founded in 2004, Packt’s mission is to help the world put software to work in new ways. Working towards that vision, we have published over 8,000 books and videos, providing developers with the actionable knowledge they need to innovate and deliver WIRESHARK FOR ANALYZING ISSUES AND MALICIOUS EMAILS IN POP The normal behavior of IMAP communication is as follows: Open the email client and enter the username and password for the relevant account. Compose a new message and send it from any email account. Retrieve the email on the client that is using IMAP. Different clients may have different ways of retrieving the email. CROSS-VALIDATION STRATEGIES FOR TIME SERIES FORECASTINGSEE MORE ONHUB.PACKTPUB.COM
HOW TO USE ARRAYS, LISTS, AND DICTIONARIES IN UNITY FOR 3DSEE MORE ONHUB.PACKTPUB.COM
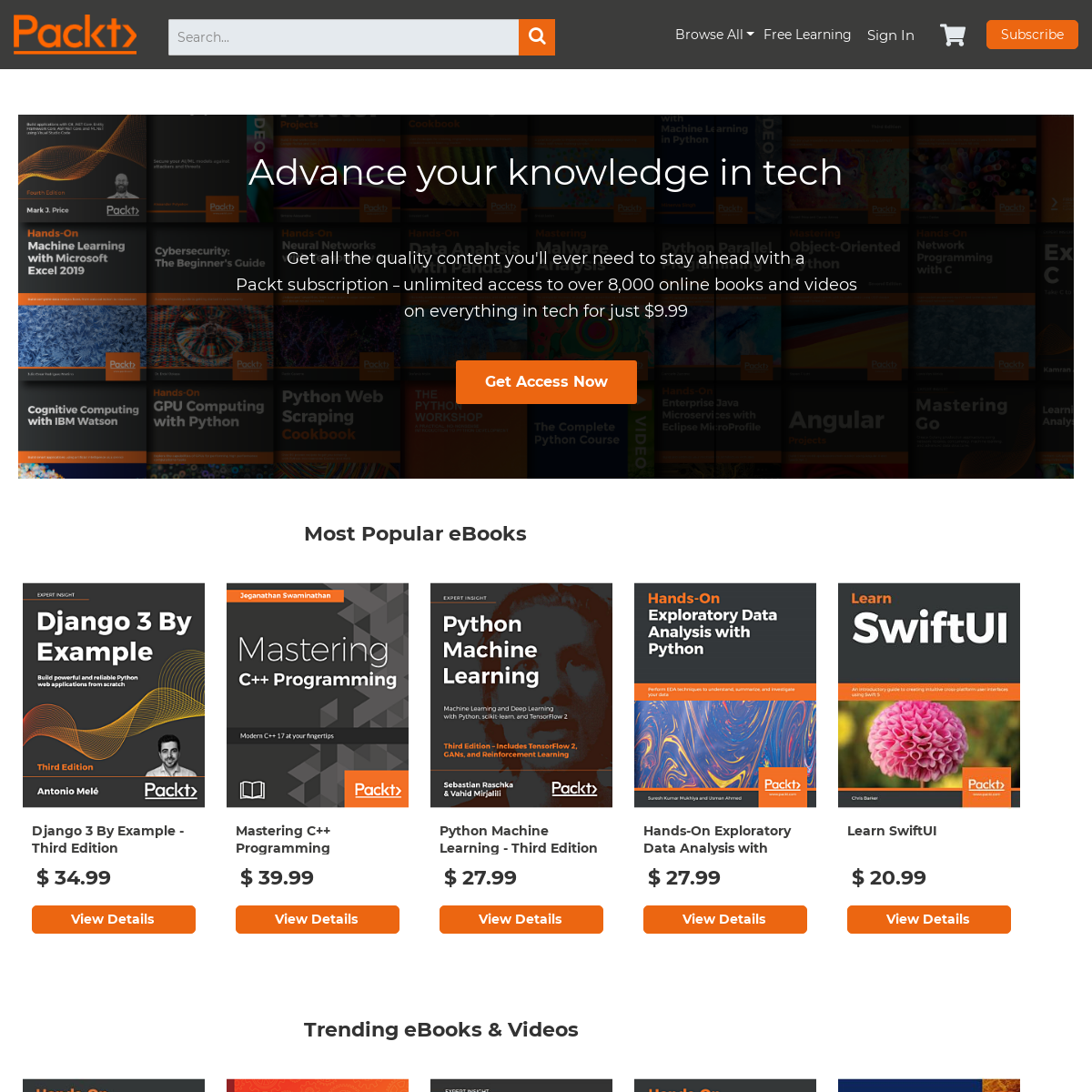
PACKT | PROGRAMMING BOOKS, EBOOKS & VIDEOS FOR DEVELOPERSSIGN INFREE LEARNINGWEB DEVELOPMENTPROGRAMMINGDATACLOUD & NETWORKING Packt | Programming Books, eBooks & Videos for Developers. Advance your knowledge in tech. Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited. access to over 8,000 online books and videos on everything in tech for just £9.99. Unlock for just $9.99.FREE LEARNING
Free Forever. On top of your daily Free Learning eBook, you can access over 30 premium titles that we've handpicked for quality across a diverse range of tech. These are yours to access online forever with a free account. Create powerful data visualizations and unlock intelligent business insights with Tableau. LIMITLESS ANALYTICS WITH AZURE SYNAPSE Limitless Analytics with Azure Synapse. By Prashant Kumar Mishra. $5 for 5 months Subscribe Access now. Print. $34.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. MASTERING EMBEDDED LINUX PROGRAMMING Mastering Embedded Linux Programming - Third Edition. By Frank Vasquez , Chris Simmonds. Start FREE trial Subscribe Access now. Print. $34.99 eBook Buy. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. ASP.NET CORE SECURE CODING COOKBOOK ASP.NET Core Secure Coding Cookbook. By Roman Canlas. $5 for 5 months Subscribe Access now. Print. $27.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. Breadth and depth in over 1,000+ technologies. PRACTICAL DISCRETE MATHEMATICS "A set is a Many that allows itself to be thought of as a One." – Georg Cantor. In mathematics, set theory is the study of collections of objects, which is prerequisite knowledge for studying discrete mathematics.. Definition–Sets and set notation. A set is a collection of objects. If a set A is made up of objects a1, a2, , we write it as A = {a1, a2, }. BECOME A PACKT AUTHOR Writing with Packt. So you want to write a tech book but you don’t know where to begin. Founded in 2004, Packt’s mission is to help the world put software to work in new ways. Working towards that vision, we have published over 8,000 books and videos, providing developers with the actionable knowledge they need to innovate and deliver WIRESHARK FOR ANALYZING ISSUES AND MALICIOUS EMAILS IN POP The normal behavior of IMAP communication is as follows: Open the email client and enter the username and password for the relevant account. Compose a new message and send it from any email account. Retrieve the email on the client that is using IMAP. Different clients may have different ways of retrieving the email. CROSS-VALIDATION STRATEGIES FOR TIME SERIES FORECASTINGSEE MORE ONHUB.PACKTPUB.COM
HOW TO USE ARRAYS, LISTS, AND DICTIONARIES IN UNITY FOR 3DSEE MORE ONHUB.PACKTPUB.COM
LOGIN | PACKT SUBSCRIPTION So that we can easily apply your past purchases, free eBooks and Packt reports to your full account, we've sent you a confirmation email. Please check your inbox and click on the activation link.ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
BECOME A PACKT AUTHOR Writing with Packt. So you want to write a tech book but you don’t know where to begin. Founded in 2004, Packt’s mission is to help the world put software to work in new ways. Working towards that vision, we have published over 8,000 books and videos, providing developers with the actionable knowledge they need to innovate and deliverDOCKER COOKBOOK
For flexible deployments, and i n order to better utilize the resources of the host system, virtualization was invented. With hypervisors, such as KVM, XEN, ESX, Hyper-V, and so on, we emulated the hardware for virtual machines (VMs) and deployed a guest OS on each virtual machine. VMs can have a different OS than their host; this means that we are responsible for managing patches, security CROSS-VALIDATION STRATEGIES FOR TIME SERIES FORECASTING Cross-validation is a well-established methodology for choosing the best model by tuning hyper-parameters or performing feature selection. There are a plethora of strategies for implementing optimal cross-validation. K-fold cross-validation is a time-proven example of such techniques. However, it is not robust in handling time series VULNERABILITY ANALYSIS OF VSFTPD 2.3.4 BACKDOOR We can use a great utility called msfvenom to generate a meterpreter payload, as shown in the preceding screenshot. The -p switch defines the payload to use, while LHOST and LPORT define our IP address and port number that ourbackdoor.elf file will connect to in order to provide us meterpreter access to the target. The -f switch defines the output type, and elf is the default extension for the 4 POWERFUL CUSTOM VISUALS IN POWER BI: WHY, WHEN, AND HOW Power BI report authors and BI teams are well-served to remain conscience of both the advantages and limitations of custom visuals. For example, when several measures or dimension columns need to be displayed within the same visual, custom visuals such as the Impact Bubble Chart and the Dot Plot by Maq Software may exclusively addressthis need.
USING HANDLEBARS WITH EXPRESS Node.js. What Le Sacre du Printemps by Stravinsky did to the world of classical music, Node.js may have done to the world of web development. At its introduction, it shocked the world. By now, Node.js is considered by many as the coolest thing. Just like Le Sacre is a totally different kind of music—but by now every child who has seen Fantasia has heard it—Node.js is a different way of MINING WITH BITCOIN CORE The Bitcoin Core wallet has built-in capabilities for mining; therefore, it is really easy to use the wallet to mine on your machine. The wallet will use your CPU to mine. As you might recall, mining is basically hashing of a candidate block over and over againuntil the
INSTALLING METASPLOIT ON WINDOWS Metasploit Framework can be easily installed on a Windows based operating system. However, Windows is usually not the platform of choice for deploying Metasploit Framework, the reason being, that many of the supporting tools and utilities are not available for Windowsplatform.
PACKT | PROGRAMMING BOOKS, EBOOKS & VIDEOS FOR DEVELOPERSSIGN INFREE LEARNINGWEB DEVELOPMENTPROGRAMMINGDATACLOUD & NETWORKING Packt | Programming Books, eBooks & Videos for Developers. Advance your knowledge in tech. Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited. access to over 8,000 online books and videos on everything in tech for just £9.99. Unlock for just $9.99. LIMITLESS ANALYTICS WITH AZURE SYNAPSE Limitless Analytics with Azure Synapse. By Prashant Kumar Mishra. $5 for 5 months Subscribe Access now. Print. $34.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. LOGIN | PACKT SUBSCRIPTION So that we can easily apply your past purchases, free eBooks and Packt reports to your full account, we've sent you a confirmation email. Please check your inbox and click on the activation link.ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
PRACTICAL DISCRETE MATHEMATICS "A set is a Many that allows itself to be thought of as a One." – Georg Cantor. In mathematics, set theory is the study of collections of objects, which is prerequisite knowledge for studying discrete mathematics.. Definition–Sets and set notation. A set is a collection of objects. If a set A is made up of objects a1, a2, , we write it as A = {a1, a2, }. WIRESHARK FOR ANALYZING ISSUES AND MALICIOUS EMAILS IN POP The normal behavior of IMAP communication is as follows: Open the email client and enter the username and password for the relevant account. Compose a new message and send it from any email account. Retrieve the email on the client that is using IMAP. Different clients may have different ways of retrieving the email. HOW TO CREATE A CONVERSATIONAL ASSISTANT OR CHATBOT USING This article is an excerpt taken from a book Natural Language Processing with Python Cookbook written by Krishna Bhavsar, Naresh Kumar, and Pratap Dangeti. This book includes unique recipes to teach various aspects of performing Natural Language Processing with NLTK—the leading Python platform for the task. DOWNLOADING TEMPLATES Templates are available directly through the Proxmox VE management interface, which offers both OS templates and virtual appliancetemplates.
CONVERTING A PYSPARK DATAFRAME TO AN ARRAY Converting a PySpark dataframe to an array - Apache Spark Deep Learning Cookbook. Setting Up Spark for Deep Learning Development. Setting Up Spark for Deep Learning Development. Introduction. Downloading an Ubuntu Desktop image. Installing and configuring Ubuntu with VMWare Fusion on macOS. Installing and configuring Ubuntu withOracle
ENABLING CLIENT-TO-CLIENT TRAFFIC The first option is the fastest option, both in terms of configuration and in terms of performance. If there are no restrictions on the traffic between VPN clients, add the line client-to-client to the configuration file tap-udp-server.conf, save it as movpn-06-01-server.conf, and restart the OpenVPN server using thisconfiguration file:
PACKT | PROGRAMMING BOOKS, EBOOKS & VIDEOS FOR DEVELOPERSSIGN INFREE LEARNINGWEB DEVELOPMENTPROGRAMMINGDATACLOUD & NETWORKING Packt | Programming Books, eBooks & Videos for Developers. Advance your knowledge in tech. Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited. access to over 8,000 online books and videos on everything in tech for just £9.99. Unlock for just $9.99. LIMITLESS ANALYTICS WITH AZURE SYNAPSE Limitless Analytics with Azure Synapse. By Prashant Kumar Mishra. $5 for 5 months Subscribe Access now. Print. $34.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. LOGIN | PACKT SUBSCRIPTION So that we can easily apply your past purchases, free eBooks and Packt reports to your full account, we've sent you a confirmation email. Please check your inbox and click on the activation link.ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
PRACTICAL DISCRETE MATHEMATICS "A set is a Many that allows itself to be thought of as a One." – Georg Cantor. In mathematics, set theory is the study of collections of objects, which is prerequisite knowledge for studying discrete mathematics.. Definition–Sets and set notation. A set is a collection of objects. If a set A is made up of objects a1, a2, , we write it as A = {a1, a2, }. WIRESHARK FOR ANALYZING ISSUES AND MALICIOUS EMAILS IN POP The normal behavior of IMAP communication is as follows: Open the email client and enter the username and password for the relevant account. Compose a new message and send it from any email account. Retrieve the email on the client that is using IMAP. Different clients may have different ways of retrieving the email. HOW TO CREATE A CONVERSATIONAL ASSISTANT OR CHATBOT USING This article is an excerpt taken from a book Natural Language Processing with Python Cookbook written by Krishna Bhavsar, Naresh Kumar, and Pratap Dangeti. This book includes unique recipes to teach various aspects of performing Natural Language Processing with NLTK—the leading Python platform for the task. DOWNLOADING TEMPLATES Templates are available directly through the Proxmox VE management interface, which offers both OS templates and virtual appliancetemplates.
CONVERTING A PYSPARK DATAFRAME TO AN ARRAY Converting a PySpark dataframe to an array - Apache Spark Deep Learning Cookbook. Setting Up Spark for Deep Learning Development. Setting Up Spark for Deep Learning Development. Introduction. Downloading an Ubuntu Desktop image. Installing and configuring Ubuntu with VMWare Fusion on macOS. Installing and configuring Ubuntu withOracle
ENABLING CLIENT-TO-CLIENT TRAFFIC The first option is the fastest option, both in terms of configuration and in terms of performance. If there are no restrictions on the traffic between VPN clients, add the line client-to-client to the configuration file tap-udp-server.conf, save it as movpn-06-01-server.conf, and restart the OpenVPN server using thisconfiguration file:
ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
PRICING AND PLANS
Annual. was $120. $99.99. billed annually. Start now. Unlimited access to entire Packt eBook and Video library. Constantly refreshed with 100+ new titles a month. Build your skills with Learning Paths. Manage content by building Playlists. EXPERT PYTHON PROGRAMMING Developers often consider multithreading to be a very complex topic. While this statement is totally true, Python provides high-level classes and functions that greatly help in using threads. CPython has some inconvenient implementation details that make threads less effective than in other programming languages like C or Java. PACKT | PROGRAMMING BOOKS, EBOOKS & VIDEOS FOR DEVELOPERS Packt | Programming Books, eBooks & Videos for Developers. Advance your knowledge in tech. Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited. access to over 8,000 online books and videos on everything in tech for just £9.99. Unlock for just $9.99. CHAPTER 3: SOCKET PROGRAMMING Socket Programming. Technical requirements. Introduction to sockets. Creating a simple TCP client and TCP server. Creating a simple UDP client and UDP server. Resolving IP addresses and domains. Practical use cases for sockets. Summary. HOW TO PERFORM SENTIMENT ANALYSIS USING PYTHON [TUTORIAL Step 11: Print the output: print "Predicted sentiment:", pred_sentiment print "Probability:", round ( probdist. prob ( pred_sentiment), 2) Copy. If you run this code, you will see three main things printed on the Terminal. The first is the accuracy, as shown in the following image: The next is a list of most informative words: The last is the CLONING YOUR REPOSITORY AND PUSHING CODE TO IT Go to the newly created repository. Select the URL in the top-right section. Go to the folder where you want to check out the project in the terminal. No need to create a new folder for the project. Enter the Git clone command, and change the URL to the URL you just copied:$ git clone URL.
THE ROUTING TABLE
A routing table lists all of the preferred routes known to a router. It is viewable in two ways, one using the inspect tool of packet tracer and the other using the show ip route Cisco IOS command. With each way, you'll see a table with lots of columns and information. TOKENIZING TEXT INTO SENTENCES First we need to import the sentence tokenization function, and then we can call it with the paragraph as an argument: >>> from nltk.tokenize import sent_tokenize >>> sent_tokenize (para) So now we have a list of sentences that we can use for furtherprocessing.
INSTALLING METASPLOIT ON WINDOWS Metasploit Framework can be easily installed on a Windows based operating system. However, Windows is usually not the platform of choice for deploying Metasploit Framework, the reason being, that many of the supporting tools and utilities are not available for Windowsplatform.
PACKT | PROGRAMMING BOOKS, EBOOKS & VIDEOS FOR DEVELOPERSSIGN INFREE LEARNINGWEB DEVELOPMENTPROGRAMMINGDATACLOUD & NETWORKING Packt | Programming Books, eBooks & Videos for Developers. Advance your knowledge in tech. Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited. access to over 8,000 online books and videos on everything in tech for just £9.99. Unlock for just $9.99. LIMITLESS ANALYTICS WITH AZURE SYNAPSE Limitless Analytics with Azure Synapse. By Prashant Kumar Mishra. $5 for 5 months Subscribe Access now. Print. $34.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. LOGIN | PACKT SUBSCRIPTION So that we can easily apply your past purchases, free eBooks and Packt reports to your full account, we've sent you a confirmation email. Please check your inbox and click on the activation link.ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
PRACTICAL DISCRETE MATHEMATICS "A set is a Many that allows itself to be thought of as a One." – Georg Cantor. In mathematics, set theory is the study of collections of objects, which is prerequisite knowledge for studying discrete mathematics.. Definition–Sets and set notation. A set is a collection of objects. If a set A is made up of objects a1, a2, , we write it as A = {a1, a2, }. WIRESHARK FOR ANALYZING ISSUES AND MALICIOUS EMAILS IN POP The normal behavior of IMAP communication is as follows: Open the email client and enter the username and password for the relevant account. Compose a new message and send it from any email account. Retrieve the email on the client that is using IMAP. Different clients may have different ways of retrieving the email. HOW TO CREATE A CONVERSATIONAL ASSISTANT OR CHATBOT USING This article is an excerpt taken from a book Natural Language Processing with Python Cookbook written by Krishna Bhavsar, Naresh Kumar, and Pratap Dangeti. This book includes unique recipes to teach various aspects of performing Natural Language Processing with NLTK—the leading Python platform for the task. DOWNLOADING TEMPLATES Templates are available directly through the Proxmox VE management interface, which offers both OS templates and virtual appliancetemplates.
CONVERTING A PYSPARK DATAFRAME TO AN ARRAY Converting a PySpark dataframe to an array - Apache Spark Deep Learning Cookbook. Setting Up Spark for Deep Learning Development. Setting Up Spark for Deep Learning Development. Introduction. Downloading an Ubuntu Desktop image. Installing and configuring Ubuntu with VMWare Fusion on macOS. Installing and configuring Ubuntu withOracle
ENABLING CLIENT-TO-CLIENT TRAFFIC The first option is the fastest option, both in terms of configuration and in terms of performance. If there are no restrictions on the traffic between VPN clients, add the line client-to-client to the configuration file tap-udp-server.conf, save it as movpn-06-01-server.conf, and restart the OpenVPN server using thisconfiguration file:
PACKT | PROGRAMMING BOOKS, EBOOKS & VIDEOS FOR DEVELOPERSSIGN INFREE LEARNINGWEB DEVELOPMENTPROGRAMMINGDATACLOUD & NETWORKING Packt | Programming Books, eBooks & Videos for Developers. Advance your knowledge in tech. Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited. access to over 8,000 online books and videos on everything in tech for just £9.99. Unlock for just $9.99. LIMITLESS ANALYTICS WITH AZURE SYNAPSE Limitless Analytics with Azure Synapse. By Prashant Kumar Mishra. $5 for 5 months Subscribe Access now. Print. $34.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. LOGIN | PACKT SUBSCRIPTION So that we can easily apply your past purchases, free eBooks and Packt reports to your full account, we've sent you a confirmation email. Please check your inbox and click on the activation link.ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
PRACTICAL DISCRETE MATHEMATICS "A set is a Many that allows itself to be thought of as a One." – Georg Cantor. In mathematics, set theory is the study of collections of objects, which is prerequisite knowledge for studying discrete mathematics.. Definition–Sets and set notation. A set is a collection of objects. If a set A is made up of objects a1, a2, , we write it as A = {a1, a2, }. WIRESHARK FOR ANALYZING ISSUES AND MALICIOUS EMAILS IN POP The normal behavior of IMAP communication is as follows: Open the email client and enter the username and password for the relevant account. Compose a new message and send it from any email account. Retrieve the email on the client that is using IMAP. Different clients may have different ways of retrieving the email. HOW TO CREATE A CONVERSATIONAL ASSISTANT OR CHATBOT USING This article is an excerpt taken from a book Natural Language Processing with Python Cookbook written by Krishna Bhavsar, Naresh Kumar, and Pratap Dangeti. This book includes unique recipes to teach various aspects of performing Natural Language Processing with NLTK—the leading Python platform for the task. DOWNLOADING TEMPLATES Templates are available directly through the Proxmox VE management interface, which offers both OS templates and virtual appliancetemplates.
CONVERTING A PYSPARK DATAFRAME TO AN ARRAY Converting a PySpark dataframe to an array - Apache Spark Deep Learning Cookbook. Setting Up Spark for Deep Learning Development. Setting Up Spark for Deep Learning Development. Introduction. Downloading an Ubuntu Desktop image. Installing and configuring Ubuntu with VMWare Fusion on macOS. Installing and configuring Ubuntu withOracle
ENABLING CLIENT-TO-CLIENT TRAFFIC The first option is the fastest option, both in terms of configuration and in terms of performance. If there are no restrictions on the traffic between VPN clients, add the line client-to-client to the configuration file tap-udp-server.conf, save it as movpn-06-01-server.conf, and restart the OpenVPN server using thisconfiguration file:
ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
PRICING AND PLANS
Annual. was $120. $99.99. billed annually. Start now. Unlimited access to entire Packt eBook and Video library. Constantly refreshed with 100+ new titles a month. Build your skills with Learning Paths. Manage content by building Playlists. EXPERT PYTHON PROGRAMMING Developers often consider multithreading to be a very complex topic. While this statement is totally true, Python provides high-level classes and functions that greatly help in using threads. CPython has some inconvenient implementation details that make threads less effective than in other programming languages like C or Java. PACKT | PROGRAMMING BOOKS, EBOOKS & VIDEOS FOR DEVELOPERS Packt | Programming Books, eBooks & Videos for Developers. Advance your knowledge in tech. Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited. access to over 8,000 online books and videos on everything in tech for just £9.99. Unlock for just $9.99. CHAPTER 3: SOCKET PROGRAMMING Socket Programming. Technical requirements. Introduction to sockets. Creating a simple TCP client and TCP server. Creating a simple UDP client and UDP server. Resolving IP addresses and domains. Practical use cases for sockets. Summary. HOW TO PERFORM SENTIMENT ANALYSIS USING PYTHON [TUTORIAL Step 11: Print the output: print "Predicted sentiment:", pred_sentiment print "Probability:", round ( probdist. prob ( pred_sentiment), 2) Copy. If you run this code, you will see three main things printed on the Terminal. The first is the accuracy, as shown in the following image: The next is a list of most informative words: The last is the CLONING YOUR REPOSITORY AND PUSHING CODE TO IT Go to the newly created repository. Select the URL in the top-right section. Go to the folder where you want to check out the project in the terminal. No need to create a new folder for the project. Enter the Git clone command, and change the URL to the URL you just copied:$ git clone URL.
THE ROUTING TABLE
A routing table lists all of the preferred routes known to a router. It is viewable in two ways, one using the inspect tool of packet tracer and the other using the show ip route Cisco IOS command. With each way, you'll see a table with lots of columns and information. TOKENIZING TEXT INTO SENTENCES First we need to import the sentence tokenization function, and then we can call it with the paragraph as an argument: >>> from nltk.tokenize import sent_tokenize >>> sent_tokenize (para) So now we have a list of sentences that we can use for furtherprocessing.
INSTALLING METASPLOIT ON WINDOWS Metasploit Framework can be easily installed on a Windows based operating system. However, Windows is usually not the platform of choice for deploying Metasploit Framework, the reason being, that many of the supporting tools and utilities are not available for Windowsplatform.
PACKT | PROGRAMMING BOOKS, EBOOKS & VIDEOS FOR DEVELOPERSSIGN INFREE LEARNINGWEB DEVELOPMENTPROGRAMMINGDATACLOUD & NETWORKING Packt | Programming Books, eBooks & Videos for Developers. Advance your knowledge in tech. Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited. access to over 8,000 online books and videos on everything in tech for just £9.99. Unlock for just $9.99. LIMITLESS ANALYTICS WITH AZURE SYNAPSE Limitless Analytics with Azure Synapse. By Prashant Kumar Mishra. $5 for 5 months Subscribe Access now. Print. $34.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. LOGIN | PACKT SUBSCRIPTION So that we can easily apply your past purchases, free eBooks and Packt reports to your full account, we've sent you a confirmation email. Please check your inbox and click on the activation link.ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
PRICING AND PLANS
Offline learning on the mobile app. Choose a DRM-free eBook or Video every month to keep. PLUS own as many other DRM-free eBooks or Videos as you like for just $5 each. Exclusive print book purchases. Unlimited access to entire Packt eBook and Video library. Constantly refreshed with 100+ new titles a month. Build your skills withLearning Paths.
HOW TO PERFORM SENTIMENT ANALYSIS USING PYTHON [TUTORIAL Step 11: Print the output: print "Predicted sentiment:", pred_sentiment print "Probability:", round ( probdist. prob ( pred_sentiment), 2) Copy. If you run this code, you will see three main things printed on the Terminal. The first is the accuracy, as shown in the following image: The next is a list of most informative words: The last is the WIRESHARK FOR ANALYZING ISSUES AND MALICIOUS EMAILS IN POP The normal behavior of IMAP communication is as follows: Open the email client and enter the username and password for the relevant account. Compose a new message and send it from any email account. Retrieve the email on the client that is using IMAP. Different clients may have different ways of retrieving the email. BUILDING A WIX INSTALLER FROM THE COMMAND LINE When we installed the WiX toolset, it gave us the WiX compiler, which is candle.exe, and linker, which is light.exe.These are the only tools we need to create an MSI from our WiX source file, Product.wxs.From the command line, we navigated to the directory where our source file was and then used Candle and Light to compile and link the file to create an MSI installer. CLONING YOUR REPOSITORY AND PUSHING CODE TO IT Go to the newly created repository. Select the URL in the top-right section. Go to the folder where you want to check out the project in the terminal. No need to create a new folder for the project. Enter the Git clone command, and change the URL to the URL you just copied:$ git clone URL.
INSTALLING METASPLOIT ON WINDOWS Metasploit Framework can be easily installed on a Windows based operating system. However, Windows is usually not the platform of choice for deploying Metasploit Framework, the reason being, that many of the supporting tools and utilities are not available for Windowsplatform.
PACKT | PROGRAMMING BOOKS, EBOOKS & VIDEOS FOR DEVELOPERSSIGN INFREE LEARNINGWEB DEVELOPMENTPROGRAMMINGDATACLOUD & NETWORKING Packt | Programming Books, eBooks & Videos for Developers. Advance your knowledge in tech. Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited. access to over 8,000 online books and videos on everything in tech for just £9.99. Unlock for just $9.99. LIMITLESS ANALYTICS WITH AZURE SYNAPSE Limitless Analytics with Azure Synapse. By Prashant Kumar Mishra. $5 for 5 months Subscribe Access now. Print. $34.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. LOGIN | PACKT SUBSCRIPTION So that we can easily apply your past purchases, free eBooks and Packt reports to your full account, we've sent you a confirmation email. Please check your inbox and click on the activation link.ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
PRICING AND PLANS
Offline learning on the mobile app. Choose a DRM-free eBook or Video every month to keep. PLUS own as many other DRM-free eBooks or Videos as you like for just $5 each. Exclusive print book purchases. Unlimited access to entire Packt eBook and Video library. Constantly refreshed with 100+ new titles a month. Build your skills withLearning Paths.
HOW TO PERFORM SENTIMENT ANALYSIS USING PYTHON [TUTORIAL Step 11: Print the output: print "Predicted sentiment:", pred_sentiment print "Probability:", round ( probdist. prob ( pred_sentiment), 2) Copy. If you run this code, you will see three main things printed on the Terminal. The first is the accuracy, as shown in the following image: The next is a list of most informative words: The last is the WIRESHARK FOR ANALYZING ISSUES AND MALICIOUS EMAILS IN POP The normal behavior of IMAP communication is as follows: Open the email client and enter the username and password for the relevant account. Compose a new message and send it from any email account. Retrieve the email on the client that is using IMAP. Different clients may have different ways of retrieving the email. BUILDING A WIX INSTALLER FROM THE COMMAND LINE When we installed the WiX toolset, it gave us the WiX compiler, which is candle.exe, and linker, which is light.exe.These are the only tools we need to create an MSI from our WiX source file, Product.wxs.From the command line, we navigated to the directory where our source file was and then used Candle and Light to compile and link the file to create an MSI installer. CLONING YOUR REPOSITORY AND PUSHING CODE TO IT Go to the newly created repository. Select the URL in the top-right section. Go to the folder where you want to check out the project in the terminal. No need to create a new folder for the project. Enter the Git clone command, and change the URL to the URL you just copied:$ git clone URL.
INSTALLING METASPLOIT ON WINDOWS Metasploit Framework can be easily installed on a Windows based operating system. However, Windows is usually not the platform of choice for deploying Metasploit Framework, the reason being, that many of the supporting tools and utilities are not available for Windowsplatform.
ACCOUNT PORTAL
Manage your Packt account, where you can update your address, review your purchases, update your subscription and change your emailpreferences
LOGIN | PACKT SUBSCRIPTION So that we can easily apply your past purchases, free eBooks and Packt reports to your full account, we've sent you a confirmation email. Please check your inbox and click on the activation link.PACKT CAREERS
Packt is a developer skills platform that supports software professionals in learning the skills they need to stay relevant in their field. From web development to data science, Packt delivers practical content on what's important in the tech world, helping developers solve today's - and tomorrow's challenges. EXPERT DATA MODELING WITH POWER BI Expert Data Modeling with Power BI. By Soheil Bakhshi. $5 for 5 months Subscribe Access now. Print. $34.99 eBook Pre-Order. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titleseach month.
PRACTICAL MICROSERVICES WITH DAPR AND .NET Practical Microservices with Dapr and .NET. 5 (1 reviews total) By Davide Bedin. $5 for 5 months Subscribe Access now. Print. $31.99 eBook Buy. Advance your knowledge in tech with a Packt subscription. Instant online access to over 7,500+ books and videos. Constantly updated with 100+ new titles each month. HANDS-ON MATHEMATICS FOR DEEP LEARNING Here, shows the vector is in n-dimensional real space, which results from taking the Cartesian product of n times; shows each element is a real number; i is the position of each element; and, finally, is a natural number, telling us how many elements are in the vector. As with regular numbers, you can add and subtract vectors. However, there are some limitations.PACKT SUBSCRIPTION
Interacting with Wireshark with pyshark. This section will help you update the basics of Wireshark to capture packets, filter them, and inspect them. You can use Wireshark to analyze the network traffic of a suspicious program, analyze the traffic flow in your network, or solve network problems. We will also review the pyshark module for COMMON BIG DATA DESIGN PATTERNS These big data design patterns aim to reduce complexity, boost the performance of integration and improve the results of working with new and larger forms of data. This article intends to introduce readers to the common big data design patterns based on various data layers such as data sources and ingestion layer, data storage layer and dataFINDING OPEN PORTS
Let's begin the process of finding the open ports by opening a terminal window: To begin, launch a terminal window and enter the following command: nmap 192.168.56.101. We can also explicitly specify the ports to scan (in this case, we are specifying 1000 ports): nmap -p 1-1000 192.168.56.101. TOKENIZING TEXT INTO SENTENCES First we need to import the sentence tokenization function, and then we can call it with the paragraph as an argument: >>> from nltk.tokenize import sent_tokenize >>> sent_tokenize (para) So now we have a list of sentences that we can use for furtherprocessing.
JAVASCRIPT SEEMS TO BE DISABLED IN YOUR BROWSER. For the best experience on our site, be sure to turn on Javascript in your browser. Choose another country or region to see content specific to yourlocation
United Kingdom Europe India AustraliaContinue >
X
SEARCH
Search:
__
_ _ _ _ Skip to ContentBrowse All
Browse Categories
Web Development
Programming
Data
Cloud & Networking
Mobile
Security
IOT & Hardware
Business
* Browse Categories
* Web Development
* Programming
* Data
* Cloud & Networking* Mobile
* Security
* IOT & Hardware
* Business
Browse By
All Products
All Books
All Videos
Best Sellers
Latest Releases
* Browse By
* All Products
* All Books
* All Videos
* Best Sellers
* Latest Releases
Trending
Python
C#
C++
Javascript
Java
AWS
React
Azure
Angular
PHP
* Trending
* Python
* C#
* C++
* Javascript
* Java
* AWS
* React
* Azure
* Angular
* PHP
Free Learning
Sign In
Subscribe
-------------------------* Browse All
Browse Categories
Web Development
Programming
Data
Cloud & Networking
Mobile
Security
IOT & Hardware
Business
* Browse Categories
* Web Development
* Programming
* Data
* Cloud & Networking* Mobile
* Security
* IOT & Hardware
* Business
Browse By
All Products
All Books
All Videos
Best Sellers
Latest Releases
* Browse By
* All Products
* All Books
* All Videos
* Best Sellers
* Latest Releases
Trending
Python
C#
C++
Javascript
Java
AWS
React
Azure
Angular
PHP
* Trending
* Python
* C#
* C++
* Javascript
* Java
* AWS
* React
* Azure
* Angular
* PHP
-------------------------Free Learning
-------------------------_ _ _ _
Sign In
My Cart 0
MY CART 0
Close YOU HAVE NO ITEMS IN YOUR SHOPPING CART.Proceed to Checkout
Subscribe
Sign In Register
Menu
ADVANCE YOUR KNOWLEDGE IN TECH Get all the quality content you'll ever need to stay ahead with a Packt subscription – unlimited access to over 8,000 online books andvideos
on everything in tech for just $9.99Get Access Now
MOST POPULAR EBOOKS
Django 3 By Example - Third Edition$ 34.99
View Details
Mastering C++ Programming$ 39.99
View Details
Python Machine Learning - Third Edition$ 27.99
View Details
Hands-On Exploratory Data Analysis with Python$ 27.99
View Details
Learn SwiftUI
$ 20.99
View Details
TRENDING EBOOKS & VIDEOS Hands-On Neuroevolution with Python$ 31.99
View Details
The JavaScript Workshop$ 27.99
View Details
Mastering Go - Second Edition$ 39.99
View Details
Hands-On RESTful Web Services with ASP.NET...$ 27.99
View Details
The Complete Python Course$ 161.99
View Details
ASP.NET Core 3 and Angular 9 - Third Edition$ 27.99
View Details
Deep Learning with TensorFlow 2 and Keras -...$ 27.99
View Details
Advanced Deep Learning with TensorFlow 2...$ 27.99
View Details
Mastering Azure Machine Learning$ 31.99
View Details
Hands-On Machine Learning with ML.NET$ 31.99
View Details
Whether you’re after the latest tech news, our newest offers or just updates about your subscription, stay right up to date with what we’re up to at Packt with our email updates.NEWSLETTER
Sign Up for Our Newsletter:Submit
USEFUL LINKS
* About Us
* Our Authors
* Press
* Careers
* Privacy Policy
* View our Cookie PolicyHELP & SUPPORT
* Support Home
* Frequently Asked Questions * Orders & Purchases * Code Download & Errata* Submit Errata
* Contact Us
SOCIAL
*
*
*
*
*
*
The word 'Packt' and the Packt logo are registered trademarks belonging to Packt Publishing Limited. All rights reservedUnited States
This website uses cookies and other tracking technology to analyse traffic, personalise ads and learn how we can improve the experience for our visitors and customers. We may also share information with trusted third-party providers. For an optimal-browsing experience please click 'Accept'. Learn moreMore Info Accept
×
Privacy Centre
* 1. Your Privacy
* 2. Strictly Necessary Cookies * 3. Performance Cookies * 4. Targeting CookiesYour Privacy
When you visit any website, it may store or retrieve information on your browser,usually in the form of cookies. This information does not usually identify you, but it does help companies to learn how their users are interacting with the site. We respect your right to privacy, so you can choose not to accept some of these cookies. Choose from the different category headers to find out more and change your default settings. Please note if you have arrived at our site via a cashback website, turning off targeting or performance cookies will mean we cannot verify your transaction with the referrer and you may not receive yourcashback.
Strictly Necessary Cookies Always active These cookies are essential for the website to function and they cannot be turned off. They are usually only set in response to actions made by you on our site, such as logging in, adding items to your cart or filling in forms. If you browse our website, you accept thesecookies.
Cookies are used by
* Packt Publishing
* Google Analytics
* Heap
Performance Cookies
These cookies allow us to keep track of how many people have visited our website, how they discovered us, and how they interact with the site.All the information used is aggregated, and completely anonymous. If you do not allow these cookies we won’t know you have visited us.Cookies are used by
* Facebook Pixel
* Google Adwords
Targeting Cookies
These cookies are placed on our site by our trusted third-party providers.They help us to personalise our adverts and provide services to our customers such as live chat. If you have arrived at our site via a cashback website, turning off Targeting Cookies will mean we cannot verify your transaction with the referrer and you may not receive your cashback.Cookies are used by
* Maxymiser
* Criteo
* Get site control
* Hotjar
* Rakuten
Allow all Save
Reviews
4.2/5
_ __ __ __ __ _
_ __ __ __ __ _
based on Customer Feedback_ _
__
Close
CHECKOUT AS A NEW CUSTOMER Creating an account has many benefits: * See order and shipping status * Track order history* Check out faster
Create an Account
CHECKOUT USING YOUR ACCOUNTEmail Address
Password
Sign In
Forgot Your Password?Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0