Are you over 18 and want to see adult content?
More Annotations
A complete backup of ashevillelist.com
Are you over 18 and want to see adult content?

eHungry: Online Ordering System for Restaurants
Are you over 18 and want to see adult content?

Catatan Seorang Guru Muda
Are you over 18 and want to see adult content?
Luminárias Exclusivas e Personalizadas | Boutique dos Lustres
Are you over 18 and want to see adult content?
The Crick Code – because everyone deserves the right to choose
Are you over 18 and want to see adult content?
کاهش وزن | آموزش تغذیه سالم و روانشناسی تغذیه و چاقی | لاغری بدون رژیم غذایی | مشاوره و برنامه تخصصی لاغری
Are you over 18 and want to see adult content?
Favourite Annotations

Ubezpieczenia online dla dzieci i dorosłych - Bezpieczny.pl
Are you over 18 and want to see adult content?
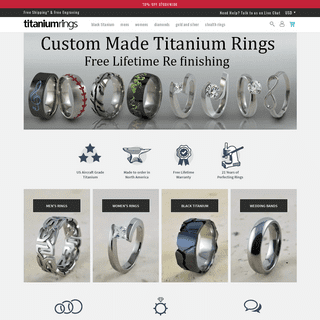
Titanium Rings - Custom Crafted In North America
Are you over 18 and want to see adult content?
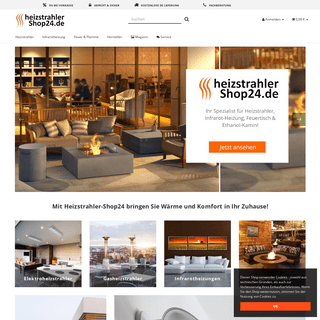
A complete backup of heizstrahler-shop24.de
Are you over 18 and want to see adult content?
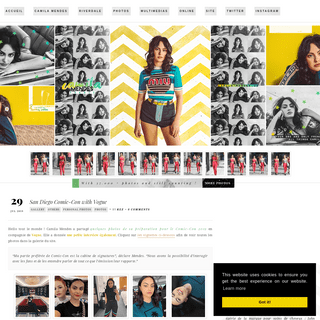
Camila Mendes France • www.camila-mendes.us | A fansite about Camila Mendes
Are you over 18 and want to see adult content?

Home | Lucky Dog Animal Rescue
Are you over 18 and want to see adult content?
Text
goto.
XSS WITH UTF-7
UTF-7 is an encoding of Unicode that only uses 7-bit characters, for use in email transmission. In a nutshell, many characters are used as-is, but some characters require encoding, in the form of a plus-sign, a modified base-64 encoding of the character code, and a minus-sign. For example, our script snippet can be represented inUTF-7 as:
RUNNING A DATABASE FROM A RAMDISK Running a database from a ramdisk. Thursday 12 May 2011. One project I’m working on these days is a large test suite for a Django project, in particular, trying to make it go faster. In one subset of 16 tests, total execution time is about 250 seconds! The tests clearly spend a lot of time in the database: 50% of the time is creating thetest
TODAY’S KENKEN
Today’s KenKen. Sunday 11 October 2009. The raging success of Sudoku has created demand for more abstract analytical puzzles, and KenKen seems to fit the bill nicely. Like Sudoku, completing the puzzle requires satisfying a number of overlapping constraints. For KenKen, the rows and columns must have each number only once, and the outlined BAD WEB TYPE: GEORGIA’S NUMERALS Bad web type: georgia’s numerals. Typography is an ancient and fascinating subject, with many facets: artistic, historic, and technological. At the intersection of these is how technology has shaped the art over time. The design of typefaces has always been shaped both by what the technology was capable of, and what the technology required. NED BATCHELDERCODETEXTSITEPYTHONCOVERAGEAUDIO Cherry-picking a pull request. 16 May. At work, we work in GitHub pull requests that get merged to the main branch.We also have twice-yearly community release branches, and a small fraction of the main-branch changes need to be copied onto the current release branch. » more.. CHERRY-PICKING A PULL REQUEST In the case of a merged pull request, the answer is easy: cherry-pick the two original commits in the pull request. We can tell the pull request was merged because the merge commit (with a thicker outline) has two parents (it’s actually a merge): But for rebased and squashed pull requests, the answer is PICKLE’S NINE FLAWS It needs no schema, and can handle arbitrary Python objects. But it has problems. This post briefly explains the problems. Some people will tell you to never use pickle because it’s bad. I won’t go that far. I’ll say, only use pickle if you are OK with its nine flaws: Insecure. Old pickles look like old code. Implicit. STATEMENT COVERAGE FOR PYTHON STATEMENT COVERAGE FOR PYTHON: DESIGN AND ANALYSIS Statement coverage for Python: design and analysis. Gareth Rees , Ravenbrook Limited , 2001-12-04. 1. Introduction. This document lists the requirements for a statement coverage tool for Python, describes some issues in design and implementation, and compares coverage.py with other statement coverage implementations. 2. BREAKING OUT OF TWO LOOPS Put the loops into a function, and return from the function to break the loops. This is unsatisfying because the loops might not be a natural place to refactor into a new function, and maybe you need access to other locals during the loops. Raise an exception and catch it outside the double loop. This is using exceptions as a form ofgoto.
XSS WITH UTF-7
UTF-7 is an encoding of Unicode that only uses 7-bit characters, for use in email transmission. In a nutshell, many characters are used as-is, but some characters require encoding, in the form of a plus-sign, a modified base-64 encoding of the character code, and a minus-sign. For example, our script snippet can be represented inUTF-7 as:
RUNNING A DATABASE FROM A RAMDISK Running a database from a ramdisk. Thursday 12 May 2011. One project I’m working on these days is a large test suite for a Django project, in particular, trying to make it go faster. In one subset of 16 tests, total execution time is about 250 seconds! The tests clearly spend a lot of time in the database: 50% of the time is creating thetest
TODAY’S KENKEN
Today’s KenKen. Sunday 11 October 2009. The raging success of Sudoku has created demand for more abstract analytical puzzles, and KenKen seems to fit the bill nicely. Like Sudoku, completing the puzzle requires satisfying a number of overlapping constraints. For KenKen, the rows and columns must have each number only once, and the outlined BAD WEB TYPE: GEORGIA’S NUMERALS Bad web type: georgia’s numerals. Typography is an ancient and fascinating subject, with many facets: artistic, historic, and technological. At the intersection of these is how technology has shaped the art over time. The design of typefaces has always been shaped both by what the technology was capable of, and what the technology required. STATEMENT COVERAGE FOR PYTHON Statement coverage for Python. 1. Introduction. The coverage.py Python module provides statement coverage for Python. It accumulates coverage data over many runs; generates coverage reports; and annotates Python source showing which statements have been covered. To use it, download coverage.py and add it to your Python library (for example, inLETTER BOXED
Letter boxed. Saturday 18 April 2020. With more time on my hands during this quarantine time, I started doing the Letter Boxed puzzle . You are given a square with three letters on each side: You form words by choosing letters in sequence.XSS WITH UTF-7
UTF-7 is an encoding of Unicode that only uses 7-bit characters, for use in email transmission. In a nutshell, many characters are used as-is, but some characters require encoding, in the form of a plus-sign, a modified base-64 encoding of the character code, and a minus-sign. For example, our script snippet can be represented inUTF-7 as:
C# AND OUTPUTDEBUGSTRING First, use the .NET Debug.WriteLine () method. This calls the Win32 OutputDebugString () function. The good thing about this technique is that because it is a native Windows facility, there are tools available to help. Most developers know that these methods write STANDARDS MISCONCEPTIONS Standards misconceptions. Created 21 September 2003. There seem to be widely-held misconceptions about software standards. People treat them as if they were laws, or moral commandments, or guarantees of success. They’re not. They’re just shorthands. LEAD IN POWER CORDS? Thursday 12 January 2006. I got a Toshiba port replicator today, and packed in the box was a small slip of yellow paper with tiny print that read: WARNING: Handling the cord on this product will expose you to lead, a chemical known to the State of California to cause birth defects or other reproducive harm.Wash hands after handling. STEPHEN WOLFRAM’S UNFORTUNATE EGO Stephen Wolfram’s unfortunate ego. Sunday 21 July 2002. I’ve started reading Stephen Wolfram’s landmark book, A New Kind Of Science . Much has already been said about Wolfram’s high opinion of himself, and his presentation style. Even knowing these things beforehand, my breath was taken away by the sheer size of Wolfram’sego.
POLITICAL COMPASS
Of course, the authors of the site have a political view as well. The problem with trying to identify anything as left or right is that the placement of the center is subjective. EXTRACTING JPGS FROM PDFS Python3 code: # coding=utf-8 # Extract jpg's from pdf's. Quick and dirty. import sys with open(sys.argv, "rb") as file: pdf = file.read() startmark = b"\xff\xd8" startfix = 0 endmark = b"\xff\xd9" endfix = 2 i = 0 njpg = 0 while True: istream = pdf.find(b"stream", i) if istream 0: break istart = pdf.find(startmark, istream, istream + 20) if istart 0: i = istream + 20 continue iend = pdf BOB’S QUICK GUIDE TO THE APOSTROPHE, YOU IDIOTS Yes, "dependant" is a real word. But it's always a noun, never a verb. As in: on my tax form I claim deductions for three dependants. "Independant" is not a word at all. If, like me, incorrect grammar and punctuation drive you crazy, then you'll enjoy reading "Eat, Shoots and Leaves" by Lynne Truss. The U.K. edition was released some timeago
NED BATCHELDERCODETEXTSITEPYTHONCOVERAGEAUDIO Cherry-picking a pull request. 16 May. At work, we work in GitHub pull requests that get merged to the main branch.We also have twice-yearly community release branches, and a small fraction of the main-branch changes need to be copied onto the current release branch. » more.. CHERRY-PICKING A PULL REQUEST In the case of a merged pull request, the answer is easy: cherry-pick the two original commits in the pull request. We can tell the pull request was merged because the merge commit (with a thicker outline) has two parents (it’s actually a merge): But for rebased and squashed pull requests, the answer is PICKLE’S NINE FLAWS It needs no schema, and can handle arbitrary Python objects. But it has problems. This post briefly explains the problems. Some people will tell you to never use pickle because it’s bad. I won’t go that far. I’ll say, only use pickle if you are OK with its nine flaws: Insecure. Old pickles look like old code. Implicit. STATEMENT COVERAGE FOR PYTHON STATEMENT COVERAGE FOR PYTHON: DESIGN AND ANALYSIS 1. Introduction. This document lists the requirements for a statement coverage tool for Python, describes some issues in design and implementation, and compares coverage.py with other statement coverage implementations.. 2. BREAKING OUT OF TWO LOOPS Put the loops into a function, and return from the function to break the loops. This is unsatisfying because the loops might not be a natural place to refactor into a new function, and maybe you need access to other locals during the loops. Raise an exception and catch it outside the double loop. This is using exceptions as a form ofgoto.
STEPHEN WOLFRAM’S UNFORTUNATE EGO Stephen Wolfram’s unfortunate ego. Sunday 21 July 2002. I’ve started reading Stephen Wolfram’s landmark book, A New Kind Of Science . Much has already been said about Wolfram’s high opinion of himself, and his presentation style. Even knowing these things beforehand, my breath was taken away by the sheer size of Wolfram’sego.
RUNNING A DATABASE FROM A RAMDISK Running a database from a ramdisk. Thursday 12 May 2011. One project I’m working on these days is a large test suite for a Django project, in particular, trying to make it go faster. In one subset of 16 tests, total execution time is about 250 seconds! The tests clearly spend a lot of time in the database: 50% of the time is creating thetest
TODAY’S KENKEN
Today’s KenKen. Sunday 11 October 2009. The raging success of Sudoku has created demand for more abstract analytical puzzles, and KenKen seems to fit the bill nicely. Like Sudoku, completing the puzzle requires satisfying a number of overlapping constraints. For KenKen, the rows and columns must have each number only once, and the outlined BAD WEB TYPE: GEORGIA’S NUMERALS Bad web type: georgia’s numerals. Typography is an ancient and fascinating subject, with many facets: artistic, historic, and technological. At the intersection of these is how technology has shaped the art over time. The design of typefaces has always been shaped both by what the technology was capable of, and what the technology required. NED BATCHELDERCODETEXTSITEPYTHONCOVERAGEAUDIO Cherry-picking a pull request. 16 May. At work, we work in GitHub pull requests that get merged to the main branch.We also have twice-yearly community release branches, and a small fraction of the main-branch changes need to be copied onto the current release branch. » more.. CHERRY-PICKING A PULL REQUEST In the case of a merged pull request, the answer is easy: cherry-pick the two original commits in the pull request. We can tell the pull request was merged because the merge commit (with a thicker outline) has two parents (it’s actually a merge): But for rebased and squashed pull requests, the answer is PICKLE’S NINE FLAWS It needs no schema, and can handle arbitrary Python objects. But it has problems. This post briefly explains the problems. Some people will tell you to never use pickle because it’s bad. I won’t go that far. I’ll say, only use pickle if you are OK with its nine flaws: Insecure. Old pickles look like old code. Implicit. STATEMENT COVERAGE FOR PYTHON STATEMENT COVERAGE FOR PYTHON: DESIGN AND ANALYSIS 1. Introduction. This document lists the requirements for a statement coverage tool for Python, describes some issues in design and implementation, and compares coverage.py with other statement coverage implementations.. 2. BREAKING OUT OF TWO LOOPS Put the loops into a function, and return from the function to break the loops. This is unsatisfying because the loops might not be a natural place to refactor into a new function, and maybe you need access to other locals during the loops. Raise an exception and catch it outside the double loop. This is using exceptions as a form ofgoto.
STEPHEN WOLFRAM’S UNFORTUNATE EGO Stephen Wolfram’s unfortunate ego. Sunday 21 July 2002. I’ve started reading Stephen Wolfram’s landmark book, A New Kind Of Science . Much has already been said about Wolfram’s high opinion of himself, and his presentation style. Even knowing these things beforehand, my breath was taken away by the sheer size of Wolfram’sego.
RUNNING A DATABASE FROM A RAMDISK Running a database from a ramdisk. Thursday 12 May 2011. One project I’m working on these days is a large test suite for a Django project, in particular, trying to make it go faster. In one subset of 16 tests, total execution time is about 250 seconds! The tests clearly spend a lot of time in the database: 50% of the time is creating thetest
TODAY’S KENKEN
Today’s KenKen. Sunday 11 October 2009. The raging success of Sudoku has created demand for more abstract analytical puzzles, and KenKen seems to fit the bill nicely. Like Sudoku, completing the puzzle requires satisfying a number of overlapping constraints. For KenKen, the rows and columns must have each number only once, and the outlined BAD WEB TYPE: GEORGIA’S NUMERALS Bad web type: georgia’s numerals. Typography is an ancient and fascinating subject, with many facets: artistic, historic, and technological. At the intersection of these is how technology has shaped the art over time. The design of typefaces has always been shaped both by what the technology was capable of, and what the technology required. CHERRY-PICKING A PULL REQUEST In the case of a merged pull request, the answer is easy: cherry-pick the two original commits in the pull request. We can tell the pull request was merged because the merge commit (with a thicker outline) has two parents (it’s actually a merge): But for rebased and squashed pull requests, the answer is BREAKING OUT OF TWO LOOPS Put the loops into a function, and return from the function to break the loops. This is unsatisfying because the loops might not be a natural place to refactor into a new function, and maybe you need access to other locals during the loops. Raise an exception and catch it outside the double loop. This is using exceptions as a form ofgoto.
LETTER BOXED
Letter boxed. Saturday 18 April 2020. With more time on my hands during this quarantine time, I started doing the Letter Boxed puzzle . You are given a square with three letters on each side: You form words by choosing letters in sequence. STATEMENT COVERAGE FOR PYTHON Statement coverage for Python. 1. Introduction. The coverage.py Python module provides statement coverage for Python. It accumulates coverage data over many runs; generates coverage reports; and annotates Python source showing which statements have been covered. To use it, download coverage.py and add it to your Python library (for example, in HOW TO MAKE COFFEE STIRRER STARS Add a third stick crossing the other two. Each of the three stirrers should go over one and under one. The fourth stick makes the star shape. Make sure the crossing at the apex is correct: it shouldn’t hold the whole star together yet, though if you grip the star at that crossing, the star will hold. The last stirrer is the hardest. 30% OF PEOPLE CAN JUGGLE What percent of people can juggle three balls? — Ned Batchelder (@nedbat) October 31, 2020. There’s a nice symmetry to the idea that about 70% of people are surprised that about 30% of people can juggle! If you have a better source of data about the general public, let meknow.
XSS WITH UTF-7
UTF-7 is an encoding of Unicode that only uses 7-bit characters, for use in email transmission. In a nutshell, many characters are used as-is, but some characters require encoding, in the form of a plus-sign, a modified base-64 encoding of the character code, and a minus-sign. For example, our script snippet can be represented inUTF-7 as:
LEAD IN POWER CORDS? Thursday 12 January 2006. I got a Toshiba port replicator today, and packed in the box was a small slip of yellow paper with tiny print that read: WARNING: Handling the cord on this product will expose you to lead, a chemical known to the State of California to cause birth defects or other reproducive harm.Wash hands after handling. EXTRACTING JPGS FROM PDFS Python3 code: # coding=utf-8 # Extract jpg's from pdf's. Quick and dirty. import sys with open(sys.argv, "rb") as file: pdf = file.read() startmark = b"\xff\xd8" startfix = 0 endmark = b"\xff\xd9" endfix = 2 i = 0 njpg = 0 while True: istream = pdf.find(b"stream", i) if istream 0: break istart = pdf.find(startmark, istream, istream + 20) if istart 0: i = istream + 20 continue iend = pdf KEYED LOOKUPS IN XSLT 1.0 I write a lot of XSLT for a variety of reasons, but somehow the “key” function has always baffled me. Every time I need to use it, I scour Google, and re-read my own XSLT code, trying to find examples that will help me, once again, understand how it works.NED BATCHELDER
Blog · Code · Text · Site HOW LONG DID IT TAKE YOU TO LEARN PYTHON?27 March
Wait, don’t answer that. It doesn’t matter. » more.. FUNCTIONAL STRATEGIES IN PYTHON13 March
I got into a debate about Python’s support for functional programming (FP) with a friend. One of the challenging parts was listening to him say, “Python is broken” a number of times.� more..
GETTING STARTED TESTING WITH PYTEST20 February
Next week I am presenting Getting Started Testing: pytest edition at Boston Python (event page). » more..
RE-USING MY PRESENTATIONS13 February
Yesterday I got an email saying that someone in Turkey had stolen one of my presentations. The email included a YouTube link. » more.. MORE BLOG ·· audio · autism� boston · cakes
� coding · coverage� debugging ·
dev-mindset · development� education ·
friends-&-family · git� help · history
� juggling ·
linters · math · obituaries · online� open-source
� parenting
� presentations
� puzzles
� pycon · python
� swimming · testing � typography · 2020� 19 ·
18 · 17
� 16 ·
15 · 14
� 13 ·
12 · 11
� 10 ·
09 · 08
� 07 ·
06 · 05
� 04 ·
03 · 02
� » more
topics..
CODE
software I made
* APTUS ·· a Mandelbrot set explorer * COVERAGE.PY ·· for measuring Python codecoverage
* HYPHENATE ·· for hyphenating words with the Liang/Knuth algorithm� more code..
TEXT
words I wrote
* PYTHON NAMES AND VALUES ·· how assignmentworks
* KINDLING PROJECTS ·· small projects fornew programmers
* PRAGMATIC UNICODE ·· how to stop the pain� more text..
ABOUT ME
I'm a software developer with a long career , a wife and three boys, one autistic. I help organize Boston Python . » more..SEARCH ME
ALSO ME
twitter · github
� sponsor
� work · resume
� irc ·
� 2002–2020
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0