Are you over 18 and want to see adult content?
More Annotations

A complete backup of televisionando.it
Are you over 18 and want to see adult content?
A complete backup of hudsonvalleyfoiegras.com
Are you over 18 and want to see adult content?

A complete backup of honke-owariya.co.jp
Are you over 18 and want to see adult content?

A complete backup of i95exitguide.com
Are you over 18 and want to see adult content?
A complete backup of shorttalkclub.com
Are you over 18 and want to see adult content?
A complete backup of profootballweekly.com
Are you over 18 and want to see adult content?

A complete backup of mobiledragway.com
Are you over 18 and want to see adult content?
A complete backup of bestsportsgames.xyz
Are you over 18 and want to see adult content?
Favourite Annotations

Nexeon: Managed Hosting & Infrastructure-as-a-Service Solutions (IaaS)
Are you over 18 and want to see adult content?

Search for homes in BC | Realtylink.org
Are you over 18 and want to see adult content?
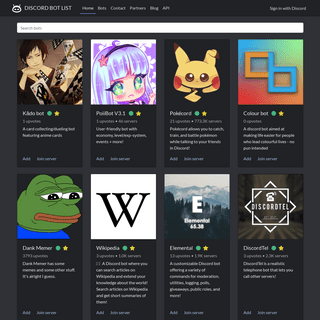
A complete backup of discordbotlist.com
Are you over 18 and want to see adult content?

Forum - Digi-TV.ch - Das grösste Forum rund um digitales Fernsehen
Are you over 18 and want to see adult content?

A complete backup of mozilla.github.io
Are you over 18 and want to see adult content?

Home - Your Application Builder
Are you over 18 and want to see adult content?
Text
AUTHINTERFACE
Generate an authentication URI for the app with the given permissions and optional parameters. HOME - DOCUMENTATION Recommended to build basic Electron app, while referencing this documentation. Our web API exposed in SAFE Browser, nearly identical to this library with just one variation, is an easy way to start exploring operations. Recommended to either follow the web APItutorial
CLASS NATIVEHANDLE
Handle to a complex object held in the SafeApp object cache. Complex objects are not moved across FFI boundary, instead a reference to theobject is used.
CIPHEROPTINTERFACE
Example // Assumes SAFEApp interface has been obtained const asyncFn = async => { // For this example you're encrypting data with our own public encryption key, // which only you will be able to deciper, however, // the use case is for encrypting with the intended recipient's public encryption key. const pubEncKey = await app.crypto.getAppPubEncKey(); const cipherOpt = await app.cipherOpt MAIDSAFE DISTRIBUTED FILE SYSTEM IRVINE: MAIDSAFE DISTRIBUTED FILE SYSTEM 2 II. OVERVIEW To enable a huge amount of data to be organised into a directory structure (as we are used to) then a new method of DHT-BASED NAT TRAVERSAL IRVINE: DHT-BASED NAT TRAVERSAL 3 On threads 2 and 3 the router negotiations protocols should be attempted (one on each thread). If 5 above passes then all thread should be stopped and the MAIDSAFE DISTRIBUTED HASH TABLE IRVINE: MAIDSAFE DISTRIBUTED HASH TABLE 3 network address in bits. For a SHA1 based addressing scheme this is 159 buckets. Taking a traditional set-up for of 20 thisCRYPTOINTERFACE
Example // Assumes SAFEApp interface has been obtained const asyncFn = async => { try { const nonce = await app.crypto.generateNonce(); } catch (err) { throw err; } }; 'PEER TO PEER' PUBLIC KEY INFRASTRUCTURE IRVINE: "PEER TO PEER" PUBLIC KEY INFRASTRUCTURE 3 A. Linking identity to key-pairs We wish to create an identity that is inherently connected to the key-pair we will use for communication, rather thanDOCS.MAIDSAFE.NET
Redirecting to https://docs.maidsafe.net/Reader.htmlAUTHINTERFACE
Generate an authentication URI for the app with the given permissions and optional parameters. HOME - DOCUMENTATION Recommended to build basic Electron app, while referencing this documentation. Our web API exposed in SAFE Browser, nearly identical to this library with just one variation, is an easy way to start exploring operations. Recommended to either follow the web APItutorial
CLASS NATIVEHANDLE
Handle to a complex object held in the SafeApp object cache. Complex objects are not moved across FFI boundary, instead a reference to theobject is used.
CIPHEROPTINTERFACE
Example // Assumes SAFEApp interface has been obtained const asyncFn = async => { // For this example you're encrypting data with our own public encryption key, // which only you will be able to deciper, however, // the use case is for encrypting with the intended recipient's public encryption key. const pubEncKey = await app.crypto.getAppPubEncKey(); const cipherOpt = await app.cipherOpt MAIDSAFE DISTRIBUTED FILE SYSTEM IRVINE: MAIDSAFE DISTRIBUTED FILE SYSTEM 2 II. OVERVIEW To enable a huge amount of data to be organised into a directory structure (as we are used to) then a new method of DHT-BASED NAT TRAVERSAL IRVINE: DHT-BASED NAT TRAVERSAL 3 On threads 2 and 3 the router negotiations protocols should be attempted (one on each thread). If 5 above passes then all thread should be stopped and the MAIDSAFE DISTRIBUTED HASH TABLE IRVINE: MAIDSAFE DISTRIBUTED HASH TABLE 3 network address in bits. For a SHA1 based addressing scheme this is 159 buckets. Taking a traditional set-up for of 20 thisCRYPTOINTERFACE
Example // Assumes SAFEApp interface has been obtained const asyncFn = async => { try { const nonce = await app.crypto.generateNonce(); } catch (err) { throw err; } }; 'PEER TO PEER' PUBLIC KEY INFRASTRUCTURE IRVINE: "PEER TO PEER" PUBLIC KEY INFRASTRUCTURE 3 A. Linking identity to key-pairs We wish to create an identity that is inherently connected to the key-pair we will use for communication, rather thanDOCS.MAIDSAFE.NET
Redirecting to https://docs.maidsafe.net/Reader.htmlWWW.MAIDSAFE.NET
Redirecting to https://maidsafe.net/products.aspWWW.MAIDSAFE.NET
Redirecting to https://maidsafe.net/contact.jspCLASS NATIVEHANDLE
Handle to a complex object held in the SafeApp object cache. Complex objects are not moved across FFI boundary, instead a reference to theobject is used.
STRUCT MDATAINFO
Mutable Data shell. Information allowing to locate and access Mutable Data on the network. STRUCT CONTAINERPERMISSIONS Namespace: System.Dynamic.ExpandoObject Assembly: SafeApp.Utilities.dll Syntax. public struct ContainerPermissions. Fields AccessWWW.MAIDSAFE.NET
Redirecting to https://maidsafe.net/libraries-network-file-system DHT-BASED NAT TRAVERSAL IRVINE: DHT-BASED NAT TRAVERSAL 2 Algorithm 1 Let A and B be the two hosts, each in its own private network; N1 and N2 are the two NATdevices; S is a
SELF ENCRYPTING DATA IRVINE: SELF ENCRYPTING DATA 1 Self Encrypting Data David Irvine MaidSafe.net, 72 Templehill, Troon, South Ayrshire, Scotland, UK. KA10 6BE. david.irvine@maidsafe.net IRVINE ET AL: AUTONOMOUS NETWORK 1 AUTONOMOUS IRVINE ET AL: AUTONOMOUS NETWORK 3 2) A method of validation of Nodes as described in Peer to Peer Public Key Infrastructure . 3) The ability to randomly select Nodes based on a math-DOCS.MAIDSAFE.NET
Redirecting to https://docs.maidsafe.net/Reader.html PROVIDING PRIVACY, SECURITY AND FREEDOM Based in Ayr, Scotland, MaidSafe have drawn talents from many cultures and countries, reflecting the users that we serve. Despite this variety, we all share a mission: a desire to provide security and privacy for everyone on the planet. This has been our unwavering ambition since we started on thisWWW.MAIDSAFE.NET
Redirecting to https://maidsafe.net/products.aspAUTHINTERFACE
Generate an authentication URI for the app with the given permissions and optional parameters. MAIDSAFE DISTRIBUTED FILE SYSTEM IRVINE: MAIDSAFE DISTRIBUTED FILE SYSTEM 2 II. OVERVIEW To enable a huge amount of data to be organised into a directory structure (as we are used to) then a new method of DHT-BASED NAT TRAVERSAL IRVINE: DHT-BASED NAT TRAVERSAL 2 Algorithm 1 Let A and B be the two hosts, each in its own private network; N1 and N2 are the two NATdevices; S is a
SELF ENCRYPTING DATA IRVINE: SELF ENCRYPTING DATA 1 Self Encrypting Data David Irvine MaidSafe.net, 72 Templehill, Troon, South Ayrshire, Scotland, UK. KA10 6BE. david.irvine@maidsafe.net SAFECOIN: THE DECENTRALISED NETWORK TOKEN Safecoin: The Decentralised Network Token Nick Lambert, Qi Ma and David Irvine January 2015 Abstract There are many examples of tokens(coins) be-
THE SAFE NETWORK ANEW,DECENTRALISEDINTERNET The SAFE Network aNew,DecentralisedInternet Nick Lambert⇤and Benjamin Bollen† October 2-3, 2014 Paper for the final symposium of the ADAM project Abstract IRVINE: SELF-AUTHENTICATION 1 SELF-AUTHENTICATION IRVINE: SELF-AUTHENTICATION 2 This is a reasonable request from people to make from their technology, but so far has been regarded asimpossible
'PEER TO PEER' PUBLIC KEY INFRASTRUCTURE IRVINE: "PEER TO PEER" PUBLIC KEY INFRASTRUCTURE 3 A. Linking identity to key-pairs We wish to create an identity that is inherently connected to the key-pair we will use for communication, rather than PROVIDING PRIVACY, SECURITY AND FREEDOM Based in Ayr, Scotland, MaidSafe have drawn talents from many cultures and countries, reflecting the users that we serve. Despite this variety, we all share a mission: a desire to provide security and privacy for everyone on the planet. This has been our unwavering ambition since we started on thisWWW.MAIDSAFE.NET
Redirecting to https://maidsafe.net/products.aspAUTHINTERFACE
Generate an authentication URI for the app with the given permissions and optional parameters. MAIDSAFE DISTRIBUTED FILE SYSTEM IRVINE: MAIDSAFE DISTRIBUTED FILE SYSTEM 2 II. OVERVIEW To enable a huge amount of data to be organised into a directory structure (as we are used to) then a new method of DHT-BASED NAT TRAVERSAL IRVINE: DHT-BASED NAT TRAVERSAL 2 Algorithm 1 Let A and B be the two hosts, each in its own private network; N1 and N2 are the two NATdevices; S is a
SELF ENCRYPTING DATA IRVINE: SELF ENCRYPTING DATA 1 Self Encrypting Data David Irvine MaidSafe.net, 72 Templehill, Troon, South Ayrshire, Scotland, UK. KA10 6BE. david.irvine@maidsafe.net SAFECOIN: THE DECENTRALISED NETWORK TOKEN Safecoin: The Decentralised Network Token Nick Lambert, Qi Ma and David Irvine January 2015 Abstract There are many examples of tokens(coins) be-
THE SAFE NETWORK ANEW,DECENTRALISEDINTERNET The SAFE Network aNew,DecentralisedInternet Nick Lambert⇤and Benjamin Bollen† October 2-3, 2014 Paper for the final symposium of the ADAM project Abstract IRVINE: SELF-AUTHENTICATION 1 SELF-AUTHENTICATION IRVINE: SELF-AUTHENTICATION 2 This is a reasonable request from people to make from their technology, but so far has been regarded asimpossible
'PEER TO PEER' PUBLIC KEY INFRASTRUCTURE IRVINE: "PEER TO PEER" PUBLIC KEY INFRASTRUCTURE 3 A. Linking identity to key-pairs We wish to create an identity that is inherently connected to the key-pair we will use for communication, rather than PROVIDING PRIVACY, SECURITY AND FREEDOM Based in Ayr, Scotland, MaidSafe have drawn talents from many cultures and countries, reflecting the users that we serve. Despite this variety, we all share a mission: a desire to provide security and privacy for everyone on the planet. This has been our unwavering ambition since we started on thisWWW.MAIDSAFE.NET
Redirecting to https://maidsafe.net/products.aspMUTABLEDATA
The metadata is particularly used by the Authenticator when another application has requested mutation permissions on this MutableData , displaying this information to the user, so the user can make a better decision to either allow or deny such a request based on it. Parameters: Name. Type. Description.STRUCT MDATAINFO
Mutable Data shell. Information allowing to locate and access Mutable Data on the network.NFS - DOCUMENTATION
Find the file of the given filename (aka keyName in the MutableData)CLASS CRYPTO
public Task DecryptSealedBoxAsync(List cipherText, NativeHandle pkHandle, NativeHandle skHandle) MAIDSAFE DISTRIBUTED HASH TABLE IRVINE: MAIDSAFE DISTRIBUTED HASH TABLE 3 network address in bits. For a SHA1 based addressing scheme this is 159 buckets. Taking a traditional set-up for of 20 thisCRYPTOINTERFACE
Example // Assumes SAFEApp interface has been obtained const asyncFn = async => { try { const nonce = await app.crypto.generateNonce(); } catch (err) { throw err; } }; IRVINE ET AL: AUTONOMOUS NETWORK 1 AUTONOMOUS IRVINE ET AL: AUTONOMOUS NETWORK 3 2) A method of validation of Nodes as described in Peer to Peer Public Key Infrastructure . 3) The ability to randomly select Nodes based on a math-DOCS.MAIDSAFE.NET
Redirecting to https://docs.maidsafe.net/Reader.htmlWWW.MAIDSAFE.NET
Redirecting to https://maidsafe.net/products.aspAUTHINTERFACE
Generate an authentication URI for the app with the given permissions and optional parameters. HOME - DOCUMENTATION Recommended to build basic Electron app, while referencing this documentation. Our web API exposed in SAFE Browser, nearly identical to this library with just one variation, is an easy way to start exploring operations. Recommended to either follow the web APItutorial
CLASS NATIVEHANDLE
Handle to a complex object held in the SafeApp object cache. Complex objects are not moved across FFI boundary, instead a reference to theobject is used.
MAIDSAFE DISTRIBUTED FILE SYSTEM IRVINE: MAIDSAFE DISTRIBUTED FILE SYSTEM 2 II. OVERVIEW To enable a huge amount of data to be organised into a directory structure (as we are used to) then a new method of DHT-BASED NAT TRAVERSAL IRVINE: DHT-BASED NAT TRAVERSAL 3 On threads 2 and 3 the router negotiations protocols should be attempted (one on each thread). If 5 above passes then all thread should be stopped and theCRYPTOINTERFACE
Example // Assumes SAFEApp interface has been obtained const asyncFn = async => { try { const nonce = await app.crypto.generateNonce(); } catch (err) { throw err; } }; MAIDSAFE DISTRIBUTED HASH TABLE IRVINE: MAIDSAFE DISTRIBUTED HASH TABLE 3 network address in bits. For a SHA1 based addressing scheme this is 159 buckets. Taking a traditional set-up for of 20 this 'PEER TO PEER' PUBLIC KEY INFRASTRUCTURE IRVINE: "PEER TO PEER" PUBLIC KEY INFRASTRUCTURE 3 A. Linking identity to key-pairs We wish to create an identity that is inherently connected to the key-pair we will use for communication, rather thanDOCS.MAIDSAFE.NET
Redirecting to https://docs.maidsafe.net/Reader.htmlWWW.MAIDSAFE.NET
Redirecting to https://maidsafe.net/products.aspAUTHINTERFACE
Generate an authentication URI for the app with the given permissions and optional parameters. HOME - DOCUMENTATION Recommended to build basic Electron app, while referencing this documentation. Our web API exposed in SAFE Browser, nearly identical to this library with just one variation, is an easy way to start exploring operations. Recommended to either follow the web APItutorial
CLASS NATIVEHANDLE
Handle to a complex object held in the SafeApp object cache. Complex objects are not moved across FFI boundary, instead a reference to theobject is used.
MAIDSAFE DISTRIBUTED FILE SYSTEM IRVINE: MAIDSAFE DISTRIBUTED FILE SYSTEM 2 II. OVERVIEW To enable a huge amount of data to be organised into a directory structure (as we are used to) then a new method of DHT-BASED NAT TRAVERSAL IRVINE: DHT-BASED NAT TRAVERSAL 3 On threads 2 and 3 the router negotiations protocols should be attempted (one on each thread). If 5 above passes then all thread should be stopped and theCRYPTOINTERFACE
Example // Assumes SAFEApp interface has been obtained const asyncFn = async => { try { const nonce = await app.crypto.generateNonce(); } catch (err) { throw err; } }; MAIDSAFE DISTRIBUTED HASH TABLE IRVINE: MAIDSAFE DISTRIBUTED HASH TABLE 3 network address in bits. For a SHA1 based addressing scheme this is 159 buckets. Taking a traditional set-up for of 20 this 'PEER TO PEER' PUBLIC KEY INFRASTRUCTURE IRVINE: "PEER TO PEER" PUBLIC KEY INFRASTRUCTURE 3 A. Linking identity to key-pairs We wish to create an identity that is inherently connected to the key-pair we will use for communication, rather thanDOCS.MAIDSAFE.NET
Redirecting to https://docs.maidsafe.net/Reader.html PROVIDING PRIVACY, SECURITY AND FREEDOM Based in Ayr, Scotland, MaidSafe have drawn talents from many cultures and countries, reflecting the users that we serve. Despite this variety, we all share a mission: a desire to provide security and privacy for everyone on the planet. This has been our unwavering ambition since we started on thisJOIN THE TEAM
Join our team. We are an eclectic and multicultural group of passionate, focussed and genuine individuals determined to release great software while making a hugely positive impact on the world. We are always interested to hear from those who have a passion for making a positive impact through the creation of software, especially expertsin Rust.
MUTABLEDATA
The metadata is particularly used by the Authenticator when another application has requested mutation permissions on this MutableData , displaying this information to the user, so the user can make a better decision to either allow or deny such a request based on it. Parameters: Name. Type. Description. GLOBAL - DOCUMENTATION Name Type Description; range: Object range of bytes to be retrieved. The start attribute is expected to be the start offset, while the end attribute of the range object the end position (both inclusive) to be retrieved, e.g. with range: { start: 2, end: 3 } the 3rd and 4th bytes of data will be retrieved. If end is not specified, the bytes retrived will be from the start offset untill the end SELF ENCRYPTING DATA IRVINE: SELF ENCRYPTING DATA 1 Self Encrypting Data David Irvine MaidSafe.net, 72 Templehill, Troon, South Ayrshire, Scotland, UK. KA10 6BE. david.irvine@maidsafe.net INDEX.JS - DOCUMENTATION index.js // Copyright 2018 MaidSafe.net limited. // // This SAFE Network Software is licensed to you under // the MIT license { // For this example you're encrypting data with our own public encryption key, // which only you will be able to deciper, however, // the use case is for encrypting with the intended recipient's public encryption key. const pubEncKey = await app.crypto.getAppPubEncKey(); const cipherOpt = await app.cipherOpt DHT-BASED NAT TRAVERSAL IRVINE: DHT-BASED NAT TRAVERSAL 2 Algorithm 1 Let A and B be the two hosts, each in its own private network; N1 and N2 are the two NATdevices; S is a
IRVINE ET AL: AUTONOMOUS NETWORK 1 AUTONOMOUS IRVINE ET AL: AUTONOMOUS NETWORK 3 2) A method of validation of Nodes as described in Peer to Peer Public Key Infrastructure . 3) The ability to randomly select Nodes based on a math-DOCS.MAIDSAFE.NET
Redirecting to https://docs.maidsafe.net/Reader.html MenuAbout Us Careers Contact MaidSafe, builders of the SAFE Network , are a small team of: thinkers, inventors, tinkerers, engineers and designers started by Scottish engineer David Irvine in 2006.INTRO TO MAIDSAFE
Based in Ayr, Scotland, MaidSafe have drawn talents from many cultures and countries, reflecting the users that we serve. Despite this variety, we all share a mission: a desire to provide security and privacy for everyone on the planet. This has been our unwavering ambition since we started on this journey in 2006, and it remains our driving force today. We will do so by building the SAFE Network, the world’s first autonomous and decentralised data network. Be part of creating this new Internet, for the people by the people; visit safenetwork.techto join us today.
* Cookies
* Disclaimer
* Privacy
* Credits
*
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0