Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://ablissfulnest.com
Are you over 18 and want to see adult content?

A complete backup of https://dynavax.com
Are you over 18 and want to see adult content?

A complete backup of https://linuxcenter.ru
Are you over 18 and want to see adult content?
A complete backup of https://antiragging.in
Are you over 18 and want to see adult content?

A complete backup of https://modocuidado.com
Are you over 18 and want to see adult content?

A complete backup of https://aidsvu.org
Are you over 18 and want to see adult content?

A complete backup of https://openfarmpet.com
Are you over 18 and want to see adult content?
A complete backup of https://stboy.net
Are you over 18 and want to see adult content?
A complete backup of https://lexilogos.com
Are you over 18 and want to see adult content?

A complete backup of https://wfscorp.com
Are you over 18 and want to see adult content?
A complete backup of https://artsmanagement.net
Are you over 18 and want to see adult content?
A complete backup of https://configurationsapien.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of serienjunkies.org
Are you over 18 and want to see adult content?

A complete backup of tysonsreporter.com
Are you over 18 and want to see adult content?
Text
more than
IVAN RISTIĆ: SECOND EDITION OF BULLETPROOF SSL AND TLS NOW November 01, 2020. I am happy to announce that the second edition of Bulletproof SSL and TLS is now available in preview. As I write this, it’s November 2020 and roughly six years since we released the first edition. I am happy to say that things have worked out approximately how I thought they would. The first edition came out in 2014, but IVAN RISTIĆ: OPENSSL COOKBOOK 3RD EDITION NOW AVAILABLE The third edition of OpenSSL Cookbook, my free book that covers command-line usage of OpenSSL, is now available for your pleasure. Although the structure of the book remains the same, it’s been significantly updated with the help of Matt Caswell, a member of the OpenSSL development team. The largest change, of course, is that thematerial is
IVAN RISTIĆ: TAG: SSL LABS SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. SSL Pulse: 49% vulnerable to CVE-2014-0224, 14% exploitable. June 13, 2014. SSL Labs test for the Heartbleed attack. IVAN RISTIĆ: DEPLOYING FORWARD SECRECYSEE MORE ON BLOG.IVANRISTIC.COM IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: HOWTO: CREATE A ROGUE CA CERTIFICATE FOR $2000 An international group of researchers—speaking at the 25th Chaos Communication Club conference—published details on how they had managed to construct a rogue Certificate Authority (CA) certificate (!) using a weakness in the MD5 hashing algorithm. They estimate the attack costs $20,000 to execute today, but that the cost can be reduced to as little as $2000. IVAN RISTIĆ: ANNOUNCING BULLETPROOF SSL AND TLS, THE 2017 July 11, 2017. I am very happy to announce Bulletproof SSL and TLS, the 2017 revision. The manuscript is complete and it’s now undergoing copyediting. We expect that the revision will be fully done by the end of July. Get your updates now if you can’t wait, or in August if you can. As with all full revisions, this means that we wentthrough
IVAN RISTIĆ: TESTING FOR SSL RENEGOTIATION Testing is easy provided you have access to an un-patched version of OpenSSL. To test, you will use the s_client tool (you'll type the bits in blue): The idea is that you connect to an SSL server and start by typing the first line of a request. You then type a single uppercase letter R on a single line, which tells OpenSSL to ask forrenegotiation.
IVAN RISTIĆ: INCREASING DHE STRENGTH ON APACHE 2.4.X Increasing DHE strength on Apache 2.4.x. August 15, 2013. Update (13 May 2015): Apache 2.2.30 (not yet released at the time of writing) will also support configurable DH parameter strength, in the same way Apache 2.4.x does. Update (26 Nov 2013): Apache 2.4.7, released today, has been improved to automatically select appropriate DH parameters IVAN RISTIĆLIBHTPSSL LABSLUABLOGBREACHMODSECURITY BLOG CAA Mandated by CA/Browser Forum. March 13, 2017. Certification Authority Authorization (CAA), specified in RFC 6844 in 2013, is a proposal to improve the strength of the PKI ecosystem with a new control to restrict which CAs can issue certificates for a particular domain name. Although CAA had been in the proposed-standard state formore than
IVAN RISTIĆ: SECOND EDITION OF BULLETPROOF SSL AND TLS NOW November 01, 2020. I am happy to announce that the second edition of Bulletproof SSL and TLS is now available in preview. As I write this, it’s November 2020 and roughly six years since we released the first edition. I am happy to say that things have worked out approximately how I thought they would. The first edition came out in 2014, but IVAN RISTIĆ: OPENSSL COOKBOOK 3RD EDITION NOW AVAILABLE The third edition of OpenSSL Cookbook, my free book that covers command-line usage of OpenSSL, is now available for your pleasure. Although the structure of the book remains the same, it’s been significantly updated with the help of Matt Caswell, a member of the OpenSSL development team. The largest change, of course, is that thematerial is
IVAN RISTIĆ: TAG: SSL LABS SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. SSL Pulse: 49% vulnerable to CVE-2014-0224, 14% exploitable. June 13, 2014. SSL Labs test for the Heartbleed attack. IVAN RISTIĆ: DEPLOYING FORWARD SECRECYSEE MORE ON BLOG.IVANRISTIC.COM IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: HOWTO: CREATE A ROGUE CA CERTIFICATE FOR $2000 An international group of researchers—speaking at the 25th Chaos Communication Club conference—published details on how they had managed to construct a rogue Certificate Authority (CA) certificate (!) using a weakness in the MD5 hashing algorithm. They estimate the attack costs $20,000 to execute today, but that the cost can be reduced to as little as $2000. IVAN RISTIĆ: ANNOUNCING BULLETPROOF SSL AND TLS, THE 2017 July 11, 2017. I am very happy to announce Bulletproof SSL and TLS, the 2017 revision. The manuscript is complete and it’s now undergoing copyediting. We expect that the revision will be fully done by the end of July. Get your updates now if you can’t wait, or in August if you can. As with all full revisions, this means that we wentthrough
IVAN RISTIĆ: TESTING FOR SSL RENEGOTIATION Testing is easy provided you have access to an un-patched version of OpenSSL. To test, you will use the s_client tool (you'll type the bits in blue): The idea is that you connect to an SSL server and start by typing the first line of a request. You then type a single uppercase letter R on a single line, which tells OpenSSL to ask forrenegotiation.
IVAN RISTIĆ: INCREASING DHE STRENGTH ON APACHE 2.4.X Increasing DHE strength on Apache 2.4.x. August 15, 2013. Update (13 May 2015): Apache 2.2.30 (not yet released at the time of writing) will also support configurable DH parameter strength, in the same way Apache 2.4.x does. Update (26 Nov 2013): Apache 2.4.7, released today, has been improved to automatically select appropriate DH parameters IVAN RISTIĆ: OPENSSL COOKBOOK 3RD EDITION NOW AVAILABLE The third edition of OpenSSL Cookbook, my free book that covers command-line usage of OpenSSL, is now available for your pleasure. Although the structure of the book remains the same, it’s been significantly updated with the help of Matt Caswell, a member of the OpenSSL development team. The largest change, of course, is that thematerial is
IVAN RISTIĆ: HTTP CLIENT FINGERPRINTING USING SSL HTTP client fingerprinting using SSL handshake analysis. June 17, 2009. My first SSL Labs project is about HTTP client fingerprinting when SSL is used. A cipher suite, in SSL, is a collection of cryptographic techniques that defines a secure communication channel. There are hundreds of cipher suites, and they are all built out of adozen or so
IVAN RISTIĆ: SSL PULSE NOW TRACKING FORWARD SECRECY AND RC4 In October we made several changes to how we produce our monthly SSL Pulse reports. They include starting tracking Forward Secrecy and RC4, and removing the requirement to mitigate BEAST server side.. Forward Secrecy. Given the increased importance of Forward Secrecy (FS) in SSL/TLS server configuration, SSL Pulse now tracks support for it among the servers in our data sample. IVAN RISTIĆ: HOWTO: CREATE A ROGUE CA CERTIFICATE FOR $2000 An international group of researchers—speaking at the 25th Chaos Communication Club conference—published details on how they had managed to construct a rogue Certificate Authority (CA) certificate (!) using a weakness in the MD5 hashing algorithm. They estimate the attack costs $20,000 to execute today, but that the cost can be reduced to as little as $2000. IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: HOW BULLETPROOF SSL AND TLS IS A LIVING BOOK August 31, 2015. I often say that Bulletproof SSL and TLS is a living book, but what does that mean exactly? It's now been one full year since the initial release, so what better time to look back to understand the process. It turns out there is a lot of work producing a living book that covers a turbulent field such as SSL/TLS and PKI. IVAN RISTIĆ: TAG: OPENSSL Tag: OpenSSL 2013 Configuring Apache, Nginx, and OpenSSL for Forward Secrecy August 05, 2013 IVAN RISTIĆ: EXAMPLES OF THE INFORMATION COLLECTED FROM I've received an email or two asking me about the information I collected using mod_sslhaf, so I decided to make it available for everyone.Here it is: sslhaf-20090709-2.txt.gz; The file contains a list of unique user agents seen on SSL Labs, each with information on the handshake they used and the protocols and cipher suites they offered to use.For example: IVAN RISTIĆ: SECURE RENEGOTIATION TEST ADDED TO SSL LABS Secure renegotiation test added to SSL Labs. May 25, 2010. When the SSL and TLS authentication gap problem was initially discovered (in November 2009), there wasn't much anyone could do about the vulnerability. You could disable renegotiation altogether, which only worked if your site did not depend on the feature. INTERNET SSL SURVEY 2010 Internet SSL Survey 2010! Black Hat USA 2010 Ivan Ristic Director of Engineering, Web Application Firewall and SSL iristic@qualys.com /@ivanristic
IVAN RISTIĆLIBHTPSSL LABSLUABLOGBREACHMODSECURITY BLOG CAA Mandated by CA/Browser Forum. March 13, 2017. Certification Authority Authorization (CAA), specified in RFC 6844 in 2013, is a proposal to improve the strength of the PKI ecosystem with a new control to restrict which CAs can issue certificates for a particular domain name. Although CAA had been in the proposed-standard state formore than
IVAN RISTIĆ: OPENSSL COOKBOOK 3RD EDITION NOW AVAILABLE The third edition of OpenSSL Cookbook, my free book that covers command-line usage of OpenSSL, is now available for your pleasure. Although the structure of the book remains the same, it’s been significantly updated with the help of Matt Caswell, a member of the OpenSSL development team. The largest change, of course, is that thematerial is
IVAN RISTIĆ: TAG: SSL LABS SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. SSL Pulse: 49% vulnerable to CVE-2014-0224, 14% exploitable. June 13, 2014. SSL Labs test for the Heartbleed attack. IVAN RISTIĆ: TAG: SSL September 09, 2014. Bulletproof SSL and TLS proofs on my desk. August 12, 2014. Bulletproof SSL and TLS has been released! August 05, 2014. Bulletproof SSL and TLS June Update: Cryptography, Protocol, and PKI. June 24, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. IVAN RISTIĆ: TAG: LUA Tag: Lua 2010 Programming in Lua 2ed now sold by Feisty Duck (PDF only) January 19, 2010 IVAN RISTIĆ: TAG: BREACH Tag: BREACH 2013 Defending against the BREACH attack August 07, 2013 IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: TESTING FOR SSL RENEGOTIATION Testing is easy provided you have access to an un-patched version of OpenSSL. To test, you will use the s_client tool (you'll type the bits in blue): The idea is that you connect to an SSL server and start by typing the first line of a request. You then type a single uppercase letter R on a single line, which tells OpenSSL to ask forrenegotiation.
IVAN RISTIĆ: ANNOUNCING BULLETPROOF SSL AND TLS, THE 2017 July 11, 2017. I am very happy to announce Bulletproof SSL and TLS, the 2017 revision. The manuscript is complete and it’s now undergoing copyediting. We expect that the revision will be fully done by the end of July. Get your updates now if you can’t wait, or in August if you can. As with all full revisions, this means that we wentthrough
IVAN RISTIĆ: INCREASING DHE STRENGTH ON APACHE 2.4.X Increasing DHE strength on Apache 2.4.x. August 15, 2013. Update (13 May 2015): Apache 2.2.30 (not yet released at the time of writing) will also support configurable DH parameter strength, in the same way Apache 2.4.x does. Update (26 Nov 2013): Apache 2.4.7, released today, has been improved to automatically select appropriate DH parameters IVAN RISTIĆLIBHTPSSL LABSLUABLOGBREACHMODSECURITY BLOG CAA Mandated by CA/Browser Forum. March 13, 2017. Certification Authority Authorization (CAA), specified in RFC 6844 in 2013, is a proposal to improve the strength of the PKI ecosystem with a new control to restrict which CAs can issue certificates for a particular domain name. Although CAA had been in the proposed-standard state formore than
IVAN RISTIĆ: OPENSSL COOKBOOK 3RD EDITION NOW AVAILABLE The third edition of OpenSSL Cookbook, my free book that covers command-line usage of OpenSSL, is now available for your pleasure. Although the structure of the book remains the same, it’s been significantly updated with the help of Matt Caswell, a member of the OpenSSL development team. The largest change, of course, is that thematerial is
IVAN RISTIĆ: TAG: SSL LABS SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. SSL Pulse: 49% vulnerable to CVE-2014-0224, 14% exploitable. June 13, 2014. SSL Labs test for the Heartbleed attack. IVAN RISTIĆ: TAG: SSL September 09, 2014. Bulletproof SSL and TLS proofs on my desk. August 12, 2014. Bulletproof SSL and TLS has been released! August 05, 2014. Bulletproof SSL and TLS June Update: Cryptography, Protocol, and PKI. June 24, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. IVAN RISTIĆ: TAG: LUA Tag: Lua 2010 Programming in Lua 2ed now sold by Feisty Duck (PDF only) January 19, 2010 IVAN RISTIĆ: TAG: BREACH Tag: BREACH 2013 Defending against the BREACH attack August 07, 2013 IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: TESTING FOR SSL RENEGOTIATION Testing is easy provided you have access to an un-patched version of OpenSSL. To test, you will use the s_client tool (you'll type the bits in blue): The idea is that you connect to an SSL server and start by typing the first line of a request. You then type a single uppercase letter R on a single line, which tells OpenSSL to ask forrenegotiation.
IVAN RISTIĆ: ANNOUNCING BULLETPROOF SSL AND TLS, THE 2017 July 11, 2017. I am very happy to announce Bulletproof SSL and TLS, the 2017 revision. The manuscript is complete and it’s now undergoing copyediting. We expect that the revision will be fully done by the end of July. Get your updates now if you can’t wait, or in August if you can. As with all full revisions, this means that we wentthrough
IVAN RISTIĆ: INCREASING DHE STRENGTH ON APACHE 2.4.X Increasing DHE strength on Apache 2.4.x. August 15, 2013. Update (13 May 2015): Apache 2.2.30 (not yet released at the time of writing) will also support configurable DH parameter strength, in the same way Apache 2.4.x does. Update (26 Nov 2013): Apache 2.4.7, released today, has been improved to automatically select appropriate DH parameters IVAN RISTIĆ: SECOND EDITION OF BULLETPROOF SSL AND TLS NOW November 01, 2020. I am happy to announce that the second edition of Bulletproof SSL and TLS is now available in preview. As I write this, it’s November 2020 and roughly six years since we released the first edition. I am happy to say that things have worked out approximately how I thought they would. The first edition came out in 2014, but IVAN RISTIĆ: ARCHIVE SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. Bulletproof SSL and TLS proofs on my desk. August 12, 2014. Bulletproof SSL and TLS has been released! August 05, 2014. Bulletproof SSL and TLS June Update: Cryptography, Protocol, and PKI. IVAN RISTIĆ: TAG: LUA Tag: Lua 2010 Programming in Lua 2ed now sold by Feisty Duck (PDF only) January 19, 2010 IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: TAG: BREACH Tag: BREACH 2013 Defending against the BREACH attack August 07, 2013 IVAN RISTIĆ: SSL PULSE NOW TRACKING FORWARD SECRECY AND RC4 In October we made several changes to how we produce our monthly SSL Pulse reports. They include starting tracking Forward Secrecy and RC4, and removing the requirement to mitigate BEAST server side.. Forward Secrecy. Given the increased importance of Forward Secrecy (FS) in SSL/TLS server configuration, SSL Pulse now tracks support for it among the servers in our data sample. IVAN RISTIĆ: DEPLOYING FORWARD SECRECY Configuring Forward Secrecy. Enabling Forward Secrecy can be done in two steps: Configure your server to actively select the most desirable suite from the list offered by SSL clients. Place ECDHE and DHE suites at the top of your list. (The order is important; because ECDHE suites are faster, you want to use them whenever clients supports them.) IVAN RISTIĆ: SSL THREAT MODEL SSL Threat Model. September 09, 2009. SSL is easy to use but also very easy to use incorrectly. The ecosystem, which is built of the specifications, the implementations, the CAs and the PKI, is full of traps, each of which is very easy to fall into. Once I started to spend significant time thinking about SSL I set out to build a modelof the
IVAN RISTIĆ: SSL AND TLS AUTHENTICATION GAP VULNERABILITY A serious vulnerability has been discovered in the way web servers utilise SSL (and TLS, up to the most recent version, 1.2), effectively allowing an active man-in-the-middle attacker to inject arbitrary content into an encrypted data stream.Both the Apache web server andthe IIS
INTERNET SSL SURVEY 2010 Internet SSL Survey 2010! Black Hat USA 2010 Ivan Ristic Director of Engineering, Web Application Firewall and SSL iristic@qualys.com /@ivanristic
IVAN RISTIĆLIBHTPSSL LABSLUABLOGBREACHMODSECURITY BLOG CAA Mandated by CA/Browser Forum. March 13, 2017. Certification Authority Authorization (CAA), specified in RFC 6844 in 2013, is a proposal to improve the strength of the PKI ecosystem with a new control to restrict which CAs can issue certificates for a particular domain name. Although CAA had been in the proposed-standard state formore than
IVAN RISTIĆ: ARCHIVE SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. Bulletproof SSL and TLS proofs on my desk. August 12, 2014. Bulletproof SSL and TLS has been released! August 05, 2014. Bulletproof SSL and TLS June Update: Cryptography, Protocol, and PKI. IVAN RISTIĆ: TAG: SSL LABSQUALYS SSLSSL LABS SSL CHECKER SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. SSL Pulse: 49% vulnerable to CVE-2014-0224, 14% exploitable. June 13, 2014. SSL Labs test for the Heartbleed attack. IVAN RISTIĆ: TAG: BREACH Tag: BREACH 2013 Defending against the BREACH attack August 07, 2013 IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: TAG: LUA Tag: Lua 2010 Programming in Lua 2ed now sold by Feisty Duck (PDF only) January 19, 2010 IVAN RISTIĆ: TAG: OPENSSL Tag: OpenSSL 2013 Configuring Apache, Nginx, and OpenSSL for Forward Secrecy August 05, 2013 IVAN RISTIĆ: ANNOUNCING BULLETPROOF SSL AND TLS, THE 2017BULLETPROOF SSL AND TLS PDFSSL TLS CERTIFICATESSL TLS CHECKERSSL TLS SETTINGSSSL V3 TLSTLS AND SSL PROTOCOLS July 11, 2017. I am very happy to announce Bulletproof SSL and TLS, the 2017 revision. The manuscript is complete and it’s now undergoing copyediting. We expect that the revision will be fully done by the end of July. Get your updates now if you can’t wait, or in August if you can. As with all full revisions, this means that we wentthrough
IVAN RISTIĆ: TESTING FOR SSL RENEGOTIATIONDISABLE SSL RENEGOTIATIONSECURE CLIENT INITIATED RENEGOTIATIONSSL RENEGOTIATION VULNERABILITYTLS CLIENT INITIATED RENEGOTIATIONSSL RENEGOTIATION DISABLETEST SSL SERVER Testing is easy provided you have access to an un-patched version of OpenSSL. To test, you will use the s_client tool (you'll type the bits in blue): The idea is that you connect to an SSL server and start by typing the first line of a request. You then type a single uppercase letter R on a single line, which tells OpenSSL to ask forrenegotiation.
INTERNET SSL SURVEY 2010 Internet SSL Survey 2010! Black Hat USA 2010 Ivan Ristic Director of Engineering, Web Application Firewall and SSL iristic@qualys.com /@ivanristic
IVAN RISTIĆLIBHTPSSL LABSLUABLOGBREACHMODSECURITY BLOG CAA Mandated by CA/Browser Forum. March 13, 2017. Certification Authority Authorization (CAA), specified in RFC 6844 in 2013, is a proposal to improve the strength of the PKI ecosystem with a new control to restrict which CAs can issue certificates for a particular domain name. Although CAA had been in the proposed-standard state formore than
IVAN RISTIĆ: ARCHIVE SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. Bulletproof SSL and TLS proofs on my desk. August 12, 2014. Bulletproof SSL and TLS has been released! August 05, 2014. Bulletproof SSL and TLS June Update: Cryptography, Protocol, and PKI. IVAN RISTIĆ: TAG: SSL LABSQUALYS SSLSSL LABS SSL CHECKER SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. SSL Pulse: 49% vulnerable to CVE-2014-0224, 14% exploitable. June 13, 2014. SSL Labs test for the Heartbleed attack. IVAN RISTIĆ: TAG: BREACH Tag: BREACH 2013 Defending against the BREACH attack August 07, 2013 IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: TAG: LUA Tag: Lua 2010 Programming in Lua 2ed now sold by Feisty Duck (PDF only) January 19, 2010 IVAN RISTIĆ: TAG: OPENSSL Tag: OpenSSL 2013 Configuring Apache, Nginx, and OpenSSL for Forward Secrecy August 05, 2013 IVAN RISTIĆ: ANNOUNCING BULLETPROOF SSL AND TLS, THE 2017BULLETPROOF SSL AND TLS PDFSSL TLS CERTIFICATESSL TLS CHECKERSSL TLS SETTINGSSSL V3 TLSTLS AND SSL PROTOCOLS July 11, 2017. I am very happy to announce Bulletproof SSL and TLS, the 2017 revision. The manuscript is complete and it’s now undergoing copyediting. We expect that the revision will be fully done by the end of July. Get your updates now if you can’t wait, or in August if you can. As with all full revisions, this means that we wentthrough
IVAN RISTIĆ: TESTING FOR SSL RENEGOTIATIONDISABLE SSL RENEGOTIATIONSECURE CLIENT INITIATED RENEGOTIATIONSSL RENEGOTIATION VULNERABILITYTLS CLIENT INITIATED RENEGOTIATIONSSL RENEGOTIATION DISABLETEST SSL SERVER Testing is easy provided you have access to an un-patched version of OpenSSL. To test, you will use the s_client tool (you'll type the bits in blue): The idea is that you connect to an SSL server and start by typing the first line of a request. You then type a single uppercase letter R on a single line, which tells OpenSSL to ask forrenegotiation.
INTERNET SSL SURVEY 2010 Internet SSL Survey 2010! Black Hat USA 2010 Ivan Ristic Director of Engineering, Web Application Firewall and SSL iristic@qualys.com /@ivanristic
IVAN RISTIĆ: TAG: SSL September 09, 2014. Bulletproof SSL and TLS proofs on my desk. August 12, 2014. Bulletproof SSL and TLS has been released! August 05, 2014. Bulletproof SSL and TLS June Update: Cryptography, Protocol, and PKI. June 24, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. IVAN RISTIĆ: BULLETPROOF SSL AND TLS, THREE YEARS LATER Bulletproof SSL and TLS, three years later. July 04, 2017. The last time I wrote about my book Bulleproof SSL and TLS was two years ago, just after publishing the first full revision. Although two years is a long time to go without a blog post, throughout this period I continued to work on the book, keeping it nearly-always up to date. IVAN RISTIĆ: SSL PULSE NOW TRACKING FORWARD SECRECY AND RC4 In October we made several changes to how we produce our monthly SSL Pulse reports. They include starting tracking Forward Secrecy and RC4, and removing the requirement to mitigate BEAST server side.. Forward Secrecy. Given the increased importance of Forward Secrecy (FS) in SSL/TLS server configuration, SSL Pulse now tracks support for it among the servers in our data sample. IVAN RISTIĆ: HOW BULLETPROOF SSL AND TLS IS A LIVING BOOK August 31, 2015. I often say that Bulletproof SSL and TLS is a living book, but what does that mean exactly? It's now been one full year since the initial release, so what better time to look back to understand the process. It turns out there is a lot of work producing a living book that covers a turbulent field such as SSL/TLS and PKI. IVAN RISTIĆ: DEPLOYING FORWARD SECRECY Configuring Forward Secrecy. Enabling Forward Secrecy can be done in two steps: Configure your server to actively select the most desirable suite from the list offered by SSL clients. Place ECDHE and DHE suites at the top of your list. (The order is important; because ECDHE suites are faster, you want to use them whenever clients supports them.) IVAN RISTIĆ: TAG: MYSQL Tag: MySQL 2009 The death of dual-licensing as a commercial open source strategy May 15, 2009 How did MySQL become so successful? May15, 2009
IVAN RISTIĆ: TAG: SSLHAF Tag: sslhaf 2013 Introducing the SSL Client Test October 02, 2013 2012 Improved passive SSL fingerprinting in sslhaf October 18, 2012 2009Two bugs in
IVAN RISTIĆ: TAG: APACHE SECURITY 2005. The PHP chapter from Apache Security available for download. June 13, 2005. The public life of Apache Security begins. April 26, 2005. Apache Security A STUDY OF WHAT REALLY BREAKS SSL About Ivan Ristic 2 Ivan is a compulsive builder, usually attracted to problems no one else is working on Apache Security, O’Reilly (2005) ModSecurity, open source web application firewall INTERNET SSL SURVEY 2010 Internet SSL Survey 2010! Black Hat USA 2010 Ivan Ristic Director of Engineering, Web Application Firewall and SSL iristic@qualys.com /@ivanristic
IVAN RISTIĆLIBHTPSSL LABSLUABLOGBREACHMODSECURITY BLOG CAA Mandated by CA/Browser Forum. March 13, 2017. Certification Authority Authorization (CAA), specified in RFC 6844 in 2013, is a proposal to improve the strength of the PKI ecosystem with a new control to restrict which CAs can issue certificates for a particular domain name. Although CAA had been in the proposed-standard state formore than
IVAN RISTIĆ: ARCHIVE SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. Bulletproof SSL and TLS proofs on my desk. August 12, 2014. Bulletproof SSL and TLS has been released! August 05, 2014. Bulletproof SSL and TLS June Update: Cryptography, Protocol, and PKI. IVAN RISTIĆ: TAG: SSL LABSQUALYS SSLSSL LABS SSL CHECKER SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. SSL Pulse: 49% vulnerable to CVE-2014-0224, 14% exploitable. June 13, 2014. SSL Labs test for the Heartbleed attack. IVAN RISTIĆ: TAG: BREACH Tag: BREACH 2013 Defending against the BREACH attack August 07, 2013 IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: TAG: LUA Tag: Lua 2010 Programming in Lua 2ed now sold by Feisty Duck (PDF only) January 19, 2010 IVAN RISTIĆ: TAG: OPENSSL Tag: OpenSSL 2013 Configuring Apache, Nginx, and OpenSSL for Forward Secrecy August 05, 2013 IVAN RISTIĆ: ANNOUNCING BULLETPROOF SSL AND TLS, THE 2017BULLETPROOF SSL AND TLS PDFSSL TLS CERTIFICATESSL TLS CHECKERSSL TLS SETTINGSSSL V3 TLSTLS AND SSL PROTOCOLS July 11, 2017. I am very happy to announce Bulletproof SSL and TLS, the 2017 revision. The manuscript is complete and it’s now undergoing copyediting. We expect that the revision will be fully done by the end of July. Get your updates now if you can’t wait, or in August if you can. As with all full revisions, this means that we wentthrough
IVAN RISTIĆ: TESTING FOR SSL RENEGOTIATIONDISABLE SSL RENEGOTIATIONSECURE CLIENT INITIATED RENEGOTIATIONSSL RENEGOTIATION VULNERABILITYTLS CLIENT INITIATED RENEGOTIATIONSSL RENEGOTIATION DISABLETEST SSL SERVER Testing is easy provided you have access to an un-patched version of OpenSSL. To test, you will use the s_client tool (you'll type the bits in blue): The idea is that you connect to an SSL server and start by typing the first line of a request. You then type a single uppercase letter R on a single line, which tells OpenSSL to ask forrenegotiation.
INTERNET SSL SURVEY 2010 Internet SSL Survey 2010! Black Hat USA 2010 Ivan Ristic Director of Engineering, Web Application Firewall and SSL iristic@qualys.com /@ivanristic
IVAN RISTIĆLIBHTPSSL LABSLUABLOGBREACHMODSECURITY BLOG CAA Mandated by CA/Browser Forum. March 13, 2017. Certification Authority Authorization (CAA), specified in RFC 6844 in 2013, is a proposal to improve the strength of the PKI ecosystem with a new control to restrict which CAs can issue certificates for a particular domain name. Although CAA had been in the proposed-standard state formore than
IVAN RISTIĆ: ARCHIVE SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. Bulletproof SSL and TLS proofs on my desk. August 12, 2014. Bulletproof SSL and TLS has been released! August 05, 2014. Bulletproof SSL and TLS June Update: Cryptography, Protocol, and PKI. IVAN RISTIĆ: TAG: SSL LABSQUALYS SSLSSL LABS SSL CHECKER SSL 3 is dead, killed by the POODLE attack. October 15, 2014. SHA1 deprecation: what you need to know. September 09, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. SSL Pulse: 49% vulnerable to CVE-2014-0224, 14% exploitable. June 13, 2014. SSL Labs test for the Heartbleed attack. IVAN RISTIĆ: TAG: BREACH Tag: BREACH 2013 Defending against the BREACH attack August 07, 2013 IVAN RISTIĆ: TAG: LIBHTP Tag: LibHTP 2009 HTTP parser for intrusion detection and web application firewalls November 30, 2009 IVAN RISTIĆ: TAG: LUA Tag: Lua 2010 Programming in Lua 2ed now sold by Feisty Duck (PDF only) January 19, 2010 IVAN RISTIĆ: TAG: OPENSSL Tag: OpenSSL 2013 Configuring Apache, Nginx, and OpenSSL for Forward Secrecy August 05, 2013 IVAN RISTIĆ: ANNOUNCING BULLETPROOF SSL AND TLS, THE 2017BULLETPROOF SSL AND TLS PDFSSL TLS CERTIFICATESSL TLS CHECKERSSL TLS SETTINGSSSL V3 TLSTLS AND SSL PROTOCOLS July 11, 2017. I am very happy to announce Bulletproof SSL and TLS, the 2017 revision. The manuscript is complete and it’s now undergoing copyediting. We expect that the revision will be fully done by the end of July. Get your updates now if you can’t wait, or in August if you can. As with all full revisions, this means that we wentthrough
IVAN RISTIĆ: TESTING FOR SSL RENEGOTIATIONDISABLE SSL RENEGOTIATIONSECURE CLIENT INITIATED RENEGOTIATIONSSL RENEGOTIATION VULNERABILITYTLS CLIENT INITIATED RENEGOTIATIONSSL RENEGOTIATION DISABLETEST SSL SERVER Testing is easy provided you have access to an un-patched version of OpenSSL. To test, you will use the s_client tool (you'll type the bits in blue): The idea is that you connect to an SSL server and start by typing the first line of a request. You then type a single uppercase letter R on a single line, which tells OpenSSL to ask forrenegotiation.
INTERNET SSL SURVEY 2010 Internet SSL Survey 2010! Black Hat USA 2010 Ivan Ristic Director of Engineering, Web Application Firewall and SSL iristic@qualys.com /@ivanristic
IVAN RISTIĆ: TAG: SSL September 09, 2014. Bulletproof SSL and TLS proofs on my desk. August 12, 2014. Bulletproof SSL and TLS has been released! August 05, 2014. Bulletproof SSL and TLS June Update: Cryptography, Protocol, and PKI. June 24, 2014. SSL Labs: New grades for trust (T) and mismatch (M) issues. June 17, 2014. IVAN RISTIĆ: BULLETPROOF SSL AND TLS, THREE YEARS LATER Bulletproof SSL and TLS, three years later. July 04, 2017. The last time I wrote about my book Bulleproof SSL and TLS was two years ago, just after publishing the first full revision. Although two years is a long time to go without a blog post, throughout this period I continued to work on the book, keeping it nearly-always up to date. IVAN RISTIĆ: SSL PULSE NOW TRACKING FORWARD SECRECY AND RC4 In October we made several changes to how we produce our monthly SSL Pulse reports. They include starting tracking Forward Secrecy and RC4, and removing the requirement to mitigate BEAST server side.. Forward Secrecy. Given the increased importance of Forward Secrecy (FS) in SSL/TLS server configuration, SSL Pulse now tracks support for it among the servers in our data sample. IVAN RISTIĆ: HOW BULLETPROOF SSL AND TLS IS A LIVING BOOK August 31, 2015. I often say that Bulletproof SSL and TLS is a living book, but what does that mean exactly? It's now been one full year since the initial release, so what better time to look back to understand the process. It turns out there is a lot of work producing a living book that covers a turbulent field such as SSL/TLS and PKI. IVAN RISTIĆ: DEPLOYING FORWARD SECRECY Configuring Forward Secrecy. Enabling Forward Secrecy can be done in two steps: Configure your server to actively select the most desirable suite from the list offered by SSL clients. Place ECDHE and DHE suites at the top of your list. (The order is important; because ECDHE suites are faster, you want to use them whenever clients supports them.) IVAN RISTIĆ: TAG: MYSQL Tag: MySQL 2009 The death of dual-licensing as a commercial open source strategy May 15, 2009 How did MySQL become so successful? May15, 2009
IVAN RISTIĆ: TAG: SSLHAF Tag: sslhaf 2013 Introducing the SSL Client Test October 02, 2013 2012 Improved passive SSL fingerprinting in sslhaf October 18, 2012 2009Two bugs in
IVAN RISTIĆ: TAG: APACHE SECURITY 2005. The PHP chapter from Apache Security available for download. June 13, 2005. The public life of Apache Security begins. April 26, 2005. Apache Security A STUDY OF WHAT REALLY BREAKS SSL About Ivan Ristic 2 Ivan is a compulsive builder, usually attracted to problems no one else is working on Apache Security, O’Reilly (2005) ModSecurity, open source web application firewall INTERNET SSL SURVEY 2010 Internet SSL Survey 2010! Black Hat USA 2010 Ivan Ristic Director of Engineering, Web Application Firewall and SSL iristic@qualys.com /@ivanristic
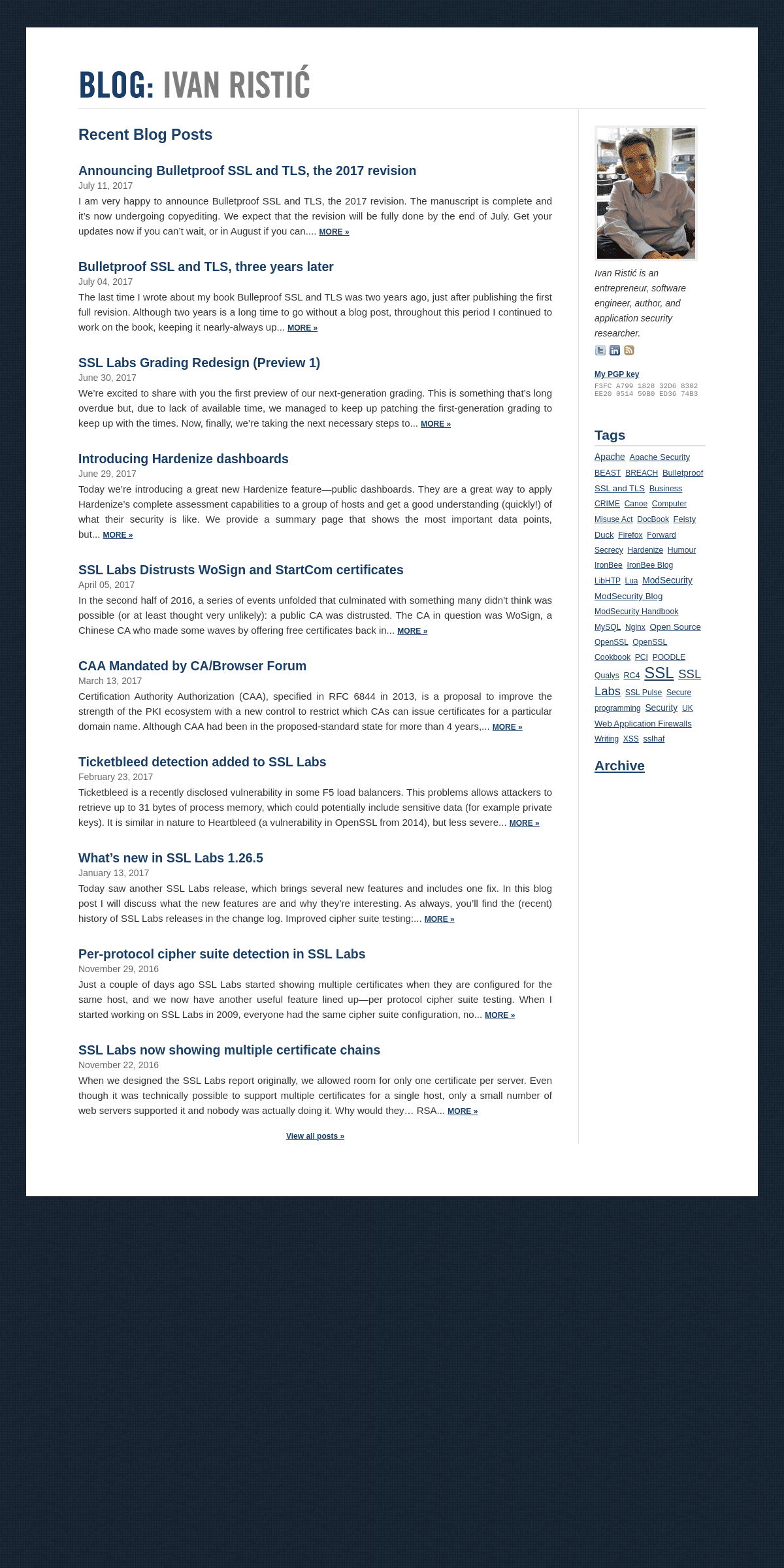
RECENT BLOG POSTS
ANNOUNCING BULLETPROOF SSL AND TLS, THE 2017 REVISIONJuly 11, 2017
I am very happy to announce Bulletproof SSL and TLS, the 2017 revision. The manuscript is complete and it’s now undergoing copyediting. We expect that the revision will be fully done by the end of July. Get your updates now if you can’t wait, or in August if youcan.... MORE »
BULLETPROOF SSL AND TLS, THREE YEARS LATERJuly 04, 2017
The last time I wrote about my book Bulleproof SSL and TLS was two years ago, just after publishing the first full revision. Although two years is a long time to go without a blog post, throughout this period I continued to work on the book, keeping it nearly-alwaysup... MORE »
SSL LABS GRADING REDESIGN (PREVIEW 1)June 30, 2017
We’re excited to share with you the first preview of our next-generation grading. This is something that’s long overdue but, due to lack of available time, we managed to keep up patching the first-generation grading to keep up with the times. Now, finally, we’re taking the next necessary steps to... MORE » INTRODUCING HARDENIZE DASHBOARDSJune 29, 2017
Today we’re introducing a great new Hardenize feature—public dashboards. They are a great way to apply Hardenize’s complete assessment capabilities to a group of hosts and get a good understanding (quickly!) of what their security is like. We provide a summary page that shows the most important data points,but... MORE »
SSL LABS DISTRUSTS WOSIGN AND STARTCOM CERTIFICATESApril 05, 2017
In the second half of 2016, a series of events unfolded that culminated with something many didn’t think was possible (or at least thought very unlikely): a public CA was distrusted. The CA in question was WoSign, a Chinese CA who made some waves by offering free certificates back in... MORE » CAA MANDATED BY CA/BROWSER FORUMMarch 13, 2017
Certification Authority Authorization (CAA), specified in RFC 6844 in 2013, is a proposal to improve the strength of the PKI ecosystem with a new control to restrict which CAs can issue certificates for a particular domain name. Although CAA had been in the proposed-standard state for more than 4 years,... MORE » TICKETBLEED DETECTION ADDED TO SSL LABSFebruary 23, 2017
Ticketbleed is a recently disclosed vulnerability in some F5 load balancers. This problems allows attackers to retrieve up to 31 bytes of process memory, which could potentially include sensitive data (for example private keys). It is similar in nature to Heartbleed (a vulnerability in OpenSSL from 2014), but less severe... MORE » WHAT’S NEW IN SSL LABS 1.26.5January 13, 2017
Today saw another SSL Labs release, which brings several new features and includes one fix. In this blog post I will discuss what the new features are and why they’re interesting. As always, you’ll find the (recent) history of SSL Labs releases in the change log. Improved cipher suite testing:... MORE » PER-PROTOCOL CIPHER SUITE DETECTION IN SSL LABSNovember 29, 2016
Just a couple of days ago SSL Labs started showing multiple certificates when they are configured for the same host, and we now have another useful feature lined up—per protocol cipher suite testing. When I started working on SSL Labs in 2009, everyone had the same cipher suite configuration, no... MORE » SSL LABS NOW SHOWING MULTIPLE CERTIFICATE CHAINSNovember 22, 2016
When we designed the SSL Labs report originally, we allowed room for only one certificate per server. Even though it was technically possible to support multiple certificates for a single host, only a small number of web servers supported it and nobody was actually doing it. Why would they… RSA... MORE »VIEW ALL POSTS »
_Ivan Ristić is an entrepreneur, software engineer, author, and application security researcher._MY PGP KEY
F3FC A799 1828 32D6 8302 EE20 0514 59B0 ED36 74B3TAGS
Apache Apache Security BEAST BREACH Bulletproof SSL and TLSBusiness CRIME
Canoe Computer Misuse Act DocBook Feisty Duck Firefox Forward Secrecy Hardenize Humour IronBee IronBee Blog LibHTP Lua ModSecurity ModSecurity Blog ModSecurity Handbook MySQL Nginx Open Source OpenSSL OpenSSL Cookbook PCI POODLE Qualys RC4 SSL SSL Labs SSL Pulse Secure programming Security UK Web Application FirewallsWriting XSS
sslhaf
ARCHIVE
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0