Are you over 18 and want to see adult content?
More Annotations
A complete backup of theinnmazatlan.com
Are you over 18 and want to see adult content?

A complete backup of santacruzpowerfitness.com
Are you over 18 and want to see adult content?
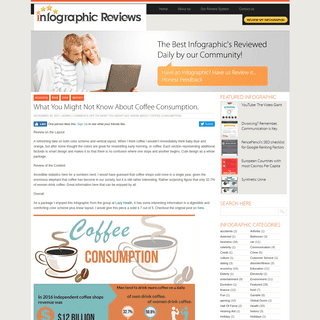
A complete backup of infographicreviews.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://pole-prepa.fr
Are you over 18 and want to see adult content?

A complete backup of https://premier.it
Are you over 18 and want to see adult content?
A complete backup of https://siebel.com
Are you over 18 and want to see adult content?

A complete backup of https://cadilapharma.com
Are you over 18 and want to see adult content?

A complete backup of https://digiro.ir
Are you over 18 and want to see adult content?

A complete backup of https://nedvizhka-buy.com.ua
Are you over 18 and want to see adult content?
A complete backup of https://pmctire.com
Are you over 18 and want to see adult content?

A complete backup of https://mobilane.com
Are you over 18 and want to see adult content?

A complete backup of https://splendidtable.org
Are you over 18 and want to see adult content?

A complete backup of https://vaccinespotter.org
Are you over 18 and want to see adult content?
A complete backup of https://radio-shalom-dijon.com
Are you over 18 and want to see adult content?

A complete backup of https://symphonic.com
Are you over 18 and want to see adult content?
Text
COLLAPSING FIND
Collapsing Find Unfortunately, using the Join algorithm given in Program can result in particularly bad trees. E.g., Figure shows the worst possible tree that can be obtained. Such a tree is bad because its height is O(N).In such a tree both the worst case and the average case running time for the Find operation is O(N).. Figure: A Degenerate Tree There is an interesting trick we can play that ORDERED LISTS AND SORTED LISTS Ordered Lists and Sorted Lists The most simple, yet one of the most versatile containers is the list .In this chapter we consider lists as abstract data types.A list is a series of items. PC ARCHITECTURE. CHAPTER 22. CHIPSETS AND HUBS. A BOOK BY Chapter 22. Chipsets and hubs Since 1997, there has been more and more focus on refinement of the chipset, and not least the north bridge, which looks after data transfer to and from RAM. GNU OCTAVE - RANDOM MATRICES - HUIHOO 16.5 Random Matrices. This section describes the basic generators for random matrices in Octave. Additional random distributions can be found in section 24.7 Random Number Generation.. Loadable Function: rand (x) Loadable Function: rand (n, m) Loadable Function: rand ("state", x) Loadable Function: rand ("seed", x) Return a matrix with random elements uniformly distributed on the interval (0, 1). KAFKA: THE DEFINITIVE GUIDE Neha Narkhede, Gwen Shapira, and Todd Palino Kafka: The Definitive Guide Real-Time Data and Stream Processing at Scale Beijing Boston Farnham Sebastopol Tokyo DESIGN OF VLSI SYSTEMS 4.3 MOSFET Capacitances. The first component of capacitive parasitics we will examine is the MOSFET capacitances. These parasitic components are mainly responsible for the intrinsic delay of logic gates, and they can be modeled with fairly high accuracy for gate delayestimation.
UNSUCCESSFUL SEARCH
Unsuccessful Search. All successful searches terminate when the object of the search is found. Therefore, all successful searches terminate at an internal node.CONNMARK TARGET
CONNMARK target. The CONNMARK target is used to set a mark on a whole connection, much the same way as the MARK target does. It can then be used together with the connmark match to match the connection in thefuture.
JEFF ERICKSON'S CS 373: COMBINATORIAL ALGORITHMS Administrivia. Prerequisites: Students are assumed to have working knowledge of the material taught in CS 225 and CS 273.This is not the same as merely having passed! In particular, I assume that all students have a gut-level understanding of induction and recursion. GUIDE TO HDL CODING STYLES FOR SYNTHESIS: 3. CODING STYLES HOME CONTENTS / 3-6 v2000.05 Guide to HDL Coding Styles for Synthesis Figure 3-3 Decoder Compile Times Versus Address Width In conclusion, Example 3-1 and Example 3-2, using indexing, areCOLLAPSING FIND
Collapsing Find Unfortunately, using the Join algorithm given in Program can result in particularly bad trees. E.g., Figure shows the worst possible tree that can be obtained. Such a tree is bad because its height is O(N).In such a tree both the worst case and the average case running time for the Find operation is O(N).. Figure: A Degenerate Tree There is an interesting trick we can play that ORDERED LISTS AND SORTED LISTS Ordered Lists and Sorted Lists The most simple, yet one of the most versatile containers is the list .In this chapter we consider lists as abstract data types.A list is a series of items. PC ARCHITECTURE. CHAPTER 22. CHIPSETS AND HUBS. A BOOK BY Chapter 22. Chipsets and hubs Since 1997, there has been more and more focus on refinement of the chipset, and not least the north bridge, which looks after data transfer to and from RAM. GNU OCTAVE - RANDOM MATRICES - HUIHOO 16.5 Random Matrices. This section describes the basic generators for random matrices in Octave. Additional random distributions can be found in section 24.7 Random Number Generation.. Loadable Function: rand (x) Loadable Function: rand (n, m) Loadable Function: rand ("state", x) Loadable Function: rand ("seed", x) Return a matrix with random elements uniformly distributed on the interval (0, 1). KAFKA: THE DEFINITIVE GUIDE Neha Narkhede, Gwen Shapira, and Todd Palino Kafka: The Definitive Guide Real-Time Data and Stream Processing at Scale Beijing Boston Farnham Sebastopol Tokyo DESIGN OF VLSI SYSTEMS 4.3 MOSFET Capacitances. The first component of capacitive parasitics we will examine is the MOSFET capacitances. These parasitic components are mainly responsible for the intrinsic delay of logic gates, and they can be modeled with fairly high accuracy for gate delayestimation.
UNSUCCESSFUL SEARCH
Unsuccessful Search. All successful searches terminate when the object of the search is found. Therefore, all successful searches terminate at an internal node.CONNMARK TARGET
CONNMARK target. The CONNMARK target is used to set a mark on a whole connection, much the same way as the MARK target does. It can then be used together with the connmark match to match the connection in thefuture.
JEFF ERICKSON'S CS 373: COMBINATORIAL ALGORITHMS Administrivia. Prerequisites: Students are assumed to have working knowledge of the material taught in CS 225 and CS 273.This is not the same as merely having passed! In particular, I assume that all students have a gut-level understanding of induction and recursion. GUIDE TO HDL CODING STYLES FOR SYNTHESIS: 3. CODING STYLES HOME CONTENTS / 3-6 v2000.05 Guide to HDL Coding Styles for Synthesis Figure 3-3 Decoder Compile Times Versus Address Width In conclusion, Example 3-1 and Example 3-2, using indexing, are BRUTE-FORCE AND GREEDY ALGORITHMS Brute-Force and Greedy Algorithms In this section we consider two closely related algorithm types--brute-force and greedy. Brute-force algorithms are distinguished not by their structure or form, but by the way in which the problem to be solved is approached. A brute-force algorithm solves a problem in the most simple, direct or obvious way. A DETAILED MODEL OF THE COMPUTER A Detailed Model of the Computer In this section we develop a detailed model of the running time performance of C++ programs. The model developed is independent of the underlying hardware and systemsoftware.
DESIGN OF VLSI SYSTEMS 4.3 MOSFET Capacitances. The first component of capacitive parasitics we will examine is the MOSFET capacitances. These parasitic components are mainly responsible for the intrinsic delay of logic gates, and they can be modeled with fairly high accuracy for gate delayestimation.
COMPLETE N -ARY TREES Complete N-ary Trees. The definition for complete binary trees can be easily extended to trees with arbitrary fixed degree as follows: . Definition (Complete N-ary Tree) A complete N-ary tree of height , is an N-ary tree with the following properties.. If h=0, for all i, .; For h>0 there exists a j, such that . is a perfect binary tree of height h-1 for all ; HDL COMPILER DIRECTIVES 9 HOME CONTENTS INDEX / 9-3 v2000.05 HDL Compiler for Verilog Reference Manual Example 9-1 analyze Command With List of Defines analyze -f verilog -d { RIPPLE, SIMPLE } mydesign.v DATA MINING SURVIVOR: INTRODUCTION An alternative that seems to work quite well is to get everything installed by running an R script that also installs the rggobi package. You can start up R and then type the command: NODE.JS NOTES FOR PROFESSIONALS Node.js Node.js Notes for Professionals Notes for Professionals GoalKicker.com Free Programming Books Disclaimer This is an uno cial free book created for educational purposes and isSCTP HEADERS
SCTP Headers. This will be a very brief introduction to the SCTP headers. SCTP has a lot of different types of packets, and hence I will try to follow the RFC's as close as possible and how they depict the different headers, starting with a general overview of the headers applicable to all SCTP packets. 3.7. JOINTURE DE LISTES ET DÉCOUPAGE DE CHAÎNESTRANSLATE THIS PAGE 3.7. Jointure de listes et découpage de chaînes. 3.7.1. Note historique sur les méthodes de chaînes. Nous avons une liste de paires clé-valeur sous la forme clé=valeur et nous voulons les assembler au sein d'une même chaîne. Pour joindre une liste de chaînes en une seule, nous LABORATORY: XV6 PROJECTS 2 LABORATORY: XV6 PROJECTS H.4 Copy-on-write Mappings This project adds the ability to perform a lightweight fork(), called vfork(), to xv6. This new call doesn’t simply copy the mappings butCOLLAPSING FIND
Collapsing Find Unfortunately, using the Join algorithm given in Program can result in particularly bad trees. E.g., Figure shows the worst possible tree that can be obtained. Such a tree is bad because its height is O(N).In such a tree both the worst case and the average case running time for the Find operation is O(N).. Figure: A Degenerate Tree There is an interesting trick we can play that A DETAILED MODEL OF THE COMPUTER A Detailed Model of the Computer In this section we develop a detailed model of the running time performance of C++ programs. The model developed is independent of the underlying hardware and systemsoftware.
PC ARCHITECTURE. CHAPTER 22. CHIPSETS AND HUBS. A BOOK BY Chapter 22. Chipsets and hubs Since 1997, there has been more and more focus on refinement of the chipset, and not least the north bridge, which looks after data transfer to and from RAM.ORDERED LISTS
Ordered Lists Figure: Object Class Hierarchy The most basic of the searchable containers is an ordered list .In Chapter we defined a searchable container as a container which supports the following additional operations: Insert used to put objects into a thecontainer; Withdraw
KAFKA: THE DEFINITIVE GUIDE Neha Narkhede, Gwen Shapira, and Todd Palino Kafka: The Definitive Guide Real-Time Data and Stream Processing at Scale Beijing Boston Farnham Sebastopol Tokyo CONNECTEDNESS OF A DIRECTED GRAPH Connectedness of a Directed Graph. When dealing with directed graphs, we define two kinds of connectedness, strong and weak.Strong connectedness of a directed graph is defined as follows: MIDDLE SQUARE METHOD Middle Square Method. In this section we consider a hashing method which avoids the use of division. Since integer division is usually slower than integer multiplication, by avoiding division we can potentially improve the running time of the hashing algorithm.UNSUCCESSFUL SEARCH
Unsuccessful Search. All successful searches terminate when the object of the search is found. Therefore, all successful searches terminate at an internal node.CONNMARK TARGET
CONNMARK target. The CONNMARK target is used to set a mark on a whole connection, much the same way as the MARK target does. It can then be used together with the connmark match to match the connection in thefuture.
NODE.JS NOTES FOR PROFESSIONALS Node.js Node.js Notes for Professionals Notes for Professionals GoalKicker.com Free Programming Books Disclaimer This is an uno cial free book created for educational purposes and isCOLLAPSING FIND
Collapsing Find Unfortunately, using the Join algorithm given in Program can result in particularly bad trees. E.g., Figure shows the worst possible tree that can be obtained. Such a tree is bad because its height is O(N).In such a tree both the worst case and the average case running time for the Find operation is O(N).. Figure: A Degenerate Tree There is an interesting trick we can play that A DETAILED MODEL OF THE COMPUTER A Detailed Model of the Computer In this section we develop a detailed model of the running time performance of C++ programs. The model developed is independent of the underlying hardware and systemsoftware.
PC ARCHITECTURE. CHAPTER 22. CHIPSETS AND HUBS. A BOOK BY Chapter 22. Chipsets and hubs Since 1997, there has been more and more focus on refinement of the chipset, and not least the north bridge, which looks after data transfer to and from RAM.ORDERED LISTS
Ordered Lists Figure: Object Class Hierarchy The most basic of the searchable containers is an ordered list .In Chapter we defined a searchable container as a container which supports the following additional operations: Insert used to put objects into a thecontainer; Withdraw
KAFKA: THE DEFINITIVE GUIDE Neha Narkhede, Gwen Shapira, and Todd Palino Kafka: The Definitive Guide Real-Time Data and Stream Processing at Scale Beijing Boston Farnham Sebastopol Tokyo CONNECTEDNESS OF A DIRECTED GRAPH Connectedness of a Directed Graph. When dealing with directed graphs, we define two kinds of connectedness, strong and weak.Strong connectedness of a directed graph is defined as follows: MIDDLE SQUARE METHOD Middle Square Method. In this section we consider a hashing method which avoids the use of division. Since integer division is usually slower than integer multiplication, by avoiding division we can potentially improve the running time of the hashing algorithm.UNSUCCESSFUL SEARCH
Unsuccessful Search. All successful searches terminate when the object of the search is found. Therefore, all successful searches terminate at an internal node.CONNMARK TARGET
CONNMARK target. The CONNMARK target is used to set a mark on a whole connection, much the same way as the MARK target does. It can then be used together with the connmark match to match the connection in thefuture.
NODE.JS NOTES FOR PROFESSIONALS Node.js Node.js Notes for Professionals Notes for Professionals GoalKicker.com Free Programming Books Disclaimer This is an uno cial free book created for educational purposes and is GNU OCTAVE - RANDOM MATRICES - HUIHOO 16.5 Random Matrices. This section describes the basic generators for random matrices in Octave. Additional random distributions can be found in section 24.7 Random Number Generation.. Loadable Function: rand (x) Loadable Function: rand (n, m) Loadable Function: rand ("state", x) Loadable Function: rand ("seed", x) Return a matrix with random elements uniformly distributed on the interval (0, 1). DESIGN OF VLSI SYSTEMS 5.1 On-Chip Clock Generation and Distribution. Clock signals are the heartbeats of digital systems. Hence, the stability of clock signals is highly important.UNSUCCESSFUL SEARCH
Unsuccessful Search. All successful searches terminate when the object of the search is found. Therefore, all successful searches terminate at an internal node. HDL COMPILER DIRECTIVES 9 HOME CONTENTS INDEX / 9-3 v2000.05 HDL Compiler for Verilog Reference Manual Example 9-1 analyze Command With List of Defines analyze -f verilog -d { RIPPLE, SIMPLE } mydesign.v CONNECTEDNESS OF A DIRECTED GRAPH Connectedness of a Directed Graph. When dealing with directed graphs, we define two kinds of connectedness, strong and weak.Strong connectedness of a directed graph is defined as follows:THE MAIN LOOP
Main Loop Basics. The main loop is primarily implemented by glib, which has a generic main loop abstraction. GTK+ attaches the glib main loop to GDK's X server connection, and presents a convenient interface (the glib loop is slightly lower-level than the GTK+ loop). IPTABLES TUTORIAL 1.2.2 Permission is granted to copy, distribute and/or modify this document under the terms of the GNU Free Documentation License, Version 1.1; with the Invariant Sections being "Introduction" and all sub-sections, with the Front-Cover Texts being "Original Author: Oskar Andreasson", and with no Back-Cover Texts.FIBONACCI HASHING
Fibonacci Hashing. The final variation of hashing to be considered here is called the Fibonacci hashing method .In fact, Fibonacci hashing is exactly the multiplication hashing method discussed in the preceding section using a very special value for a.The value we choose is closely related to the number called the golden ratio. CHANGING CYGWIN'S MAXIMUM MEMORY By default no Cygwin program can allocate more than 384 MB of memory (program+data). You should not need to change this default in mostcircumstances.
8.2. TROVARE IL PERCORSO 8.2. Trovare il percorso. Quando lanciate gli script Python da linea di comando, qualche volta torna utile sapere dov'è localizzato lo script corrente sul disco fisso. Questo è uno degli oscuri e piccoli trucchi che sono virtualmente impossibili da imparare da soli, ma semplici da ricordare una volta visti.项目 文档
博客 图书
灰狐和他的朋友们区块链
机器学�
深度学�
计算机视觉
自然语言处理
大数据
以太坊
Hyperledger
Torch
Apache UIMA
H2O
ROS
PredictionIO
TensorFlow
Caffe
NLTK
HDP
Autonomous car
灰狐咨询
灰狐推广
知识星球
�2019 Huihoo
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0