Are you over 18 and want to see adult content?
More Annotations

Contests, Giveaways & Sweepstakes - Sweeps Invasion
Are you over 18 and want to see adult content?

BLOG DE EDUCACION FISICA Y EDUCACION PARA LA SALUD. C.E.I.P. LA SANTA CRUZ
Are you over 18 and want to see adult content?

Позы и анимации для Симс 4 - Бесплатно на Sims4File
Are you over 18 and want to see adult content?

Curso de Inglês Online | Inglês 200 horas
Are you over 18 and want to see adult content?

Dono da Notícia | Últimas notícias do Piauí
Are you over 18 and want to see adult content?
GamePress - Databases, Guides, and News for your Favorite Games
Are you over 18 and want to see adult content?
Helium: Shopify developers, website design, themes, and apps
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of strapon-blog.net
Are you over 18 and want to see adult content?

A complete backup of buffet-jeizinen.ch
Are you over 18 and want to see adult content?

A complete backup of translateit.today
Are you over 18 and want to see adult content?

A complete backup of dog-health-guide.org
Are you over 18 and want to see adult content?

A complete backup of ministeriojuvenil.com
Are you over 18 and want to see adult content?
A complete backup of frankie-west.co.uk
Are you over 18 and want to see adult content?
Text
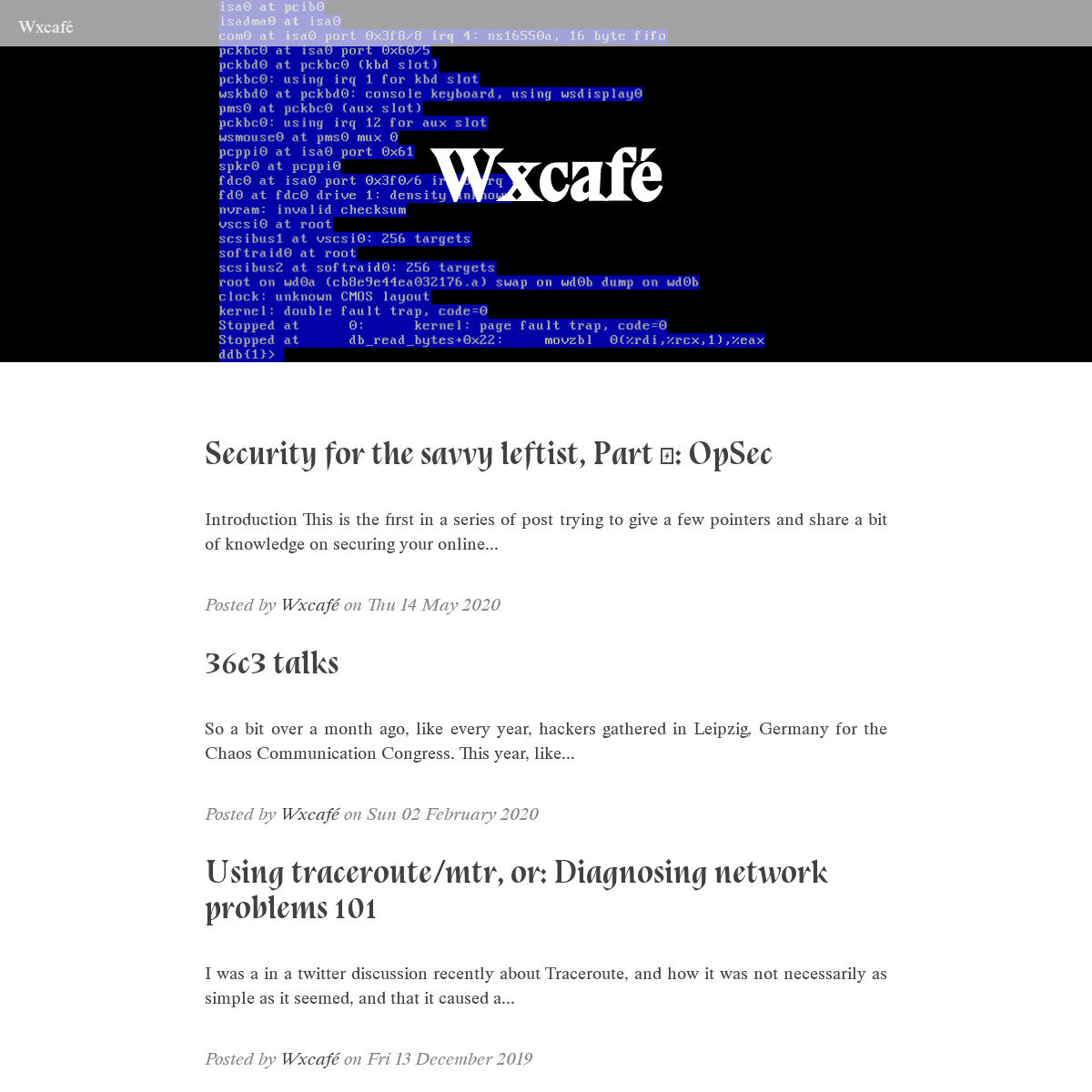
WXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes. 36C3 TALKS - WXCAFÉ 36c3 Infrastructure Review ⭐⭐⭐⭐. Like each year, the infrastructure review talks about how congress works and the people who make it work. I love watching these, I loved being an Angel when I was there, and I really like learning about the parts of organizing I didn’t know about. YUBIKEY FOR EVERYTHING The default PINs are 123456 for the user PIN and 12345678 for the admin PIN.. Do take caution to export the private keys for safekeeping BEFORE moving them to the yubikey (the gpg keytocard command MOVES the keys, after you’ve run it you don’t have the private keys available anymore to backup) (backups are easily done with gpg --armor --export-secret-keys > out.asc and gpg -MY KEYBOARD.IO
My Keyboard.io. Over a year ago now I bought a keyboard, and I wanted to write about it then, but I figured I’d wait until I could type on it correctly and actually tell if it was a good keyboard.. Turns out, it took me about three weeks to learn how to type correctly, and it’s a really, really good keyboard but I forgot about writing this🤦 So here we go.
WHEN A TOY ISN'T A TOY ANYMORE Let’s say, for the sake of argument, that there’s this guy named Nick. Nick is a nice person. He’s friends with a lot of queer people. Maybe he doesn’t always get everything about Socialism or Communism but he agrees that the world is unfair, and that aSDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
WXCAFÉ
Every git commit has an id like 3f29abcd233fa, also called 82#*+ DEFD #(!#7& +,5,+& $2 $", &#),.26, G)2&*&A()2 H)),$ 6,7 + #*& 3!0' %5) $!5 8#0 I/&$ 5+&)2&.(*+) C AAJWXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes. 36C3 TALKS - WXCAFÉ 36c3 Infrastructure Review ⭐⭐⭐⭐. Like each year, the infrastructure review talks about how congress works and the people who make it work. I love watching these, I loved being an Angel when I was there, and I really like learning about the parts of organizing I didn’t know about. YUBIKEY FOR EVERYTHING The default PINs are 123456 for the user PIN and 12345678 for the admin PIN.. Do take caution to export the private keys for safekeeping BEFORE moving them to the yubikey (the gpg keytocard command MOVES the keys, after you’ve run it you don’t have the private keys available anymore to backup) (backups are easily done with gpg --armor --export-secret-keys > out.asc and gpg -MY KEYBOARD.IO
My Keyboard.io. Over a year ago now I bought a keyboard, and I wanted to write about it then, but I figured I’d wait until I could type on it correctly and actually tell if it was a good keyboard.. Turns out, it took me about three weeks to learn how to type correctly, and it’s a really, really good keyboard but I forgot about writing this🤦 So here we go.
WHEN A TOY ISN'T A TOY ANYMORE Let’s say, for the sake of argument, that there’s this guy named Nick. Nick is a nice person. He’s friends with a lot of queer people. Maybe he doesn’t always get everything about Socialism or Communism but he agrees that the world is unfair, and that aSDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
WXCAFÉ
Every git commit has an id like 3f29abcd233fa, also called 82#*+ DEFD #(!#7& +,5,+& $2 $", &#),.26, G)2&*&A()2 H)),$ 6,7 + #*& 3!0' %5) $!5 8#0 I/&$ 5+&)2&.(*+) C AAJ WXCAFÉ - ARTICLES BY WXCAFÉ Security for the savvy leftist, Part Ⅰ: OpSec Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your onlineMY KEYBOARD.IO
My Keyboard.io. Over a year ago now I bought a keyboard, and I wanted to write about it then, but I figured I’d wait until I could type on it correctly and actually tell if it was a good keyboard.. Turns out, it took me about three weeks to learn how to type correctly, and it’s a really, really good keyboard but I forgot about writing this🤦 So here we go.
IN THIS ISSUE
The Internet Protocol Journal 3 What Is an Autonomous System? One of the best definitions of an Autonomous System can be found in an IETF document, RFC 4271 that describes BGPv4: “The classic definition of an Autonomous System is a set of routers un- THE ATTORNEY GENERAL'S G URN ELINES ON FEDERAL BUREAU … vi. monitoring and control ~-~- of -- undercover ---operations 17preparation of undercover employees, informants, and cooperating witnesses .17 a. b. review of conduct. ..17 SEPTEMBER 2005 VOLUME 8, NUMBER 3 IPv4 Address Space Consumption: continued The Internet Protocol Journal 4 Figure 3: IANA Allocations to RIRs — Sliding-Window 24-Month Average Taken by JUNE 1998 VOLUME 1, NUMBER 1 The Internet Protocol Journal 2 What Is a VPN? — Part I by Paul Ferguson, Cisco Systems and Geoff Huston, Telstra he term “VPN,” or Virtual Private NetworkIN THIS ISSUE
The Internet Protocol Journal 2 IPv4—How long do we have? by Geoff Huston, Telstra ne of those stories that keeps on appearing from timeto time is
MARCH 2011 VOLUME 14, NUMBER 1 The Internet Protocol Journal 2 A Rough Guide to Address Exhaustion by Geoff Huston, APNIC T he level of interest in IPv4 address exhaustionseems to be
JUNE 2002 VOLUME 5, NUMBER 2 BEEP: continued The Internet Protocol Journal 4 First, you decide that your protocol needs ordered, reliable delivery. This is a common requirement for most application protocols, includ- DECEMBER 2009 VOLUME 12, NUMBER 4 The Internet Protocol Journal 2 Cloud Computing—A Primer Part 2: Infrastructure and Implementation Topics by T. Sridhar C loud computing is an emerging area that affects IT infra-WXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
36C3 TALKS - WXCAFÉ 36c3 Infrastructure Review ⭐⭐⭐⭐. Like each year, the infrastructure review talks about how congress works and the people who make it work. I love watching these, I loved being an Angel when I was there, and I really like learning about the parts of organizing I didn’t know about. YUBIKEY FOR EVERYTHING The default PINs are 123456 for the user PIN and 12345678 for the admin PIN.. Do take caution to export the private keys for safekeeping BEFORE moving them to the yubikey (the gpg keytocard command MOVES the keys, after you’ve run it you don’t have the private keys available anymore to backup) (backups are easily done with gpg --armor --export-secret-keys > out.asc and gpg - POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes.MY KEYBOARD.IO
My Keyboard.io. Over a year ago now I bought a keyboard, and I wanted to write about it then, but I figured I’d wait until I could type on it correctly and actually tell if it was a good keyboard.. Turns out, it took me about three weeks to learn how to type correctly, and it’s a really, really good keyboard but I forgot about writing this🤦 So here we go.
WHEN A TOY ISN'T A TOY ANYMORE Let’s say, for the sake of argument, that there’s this guy named Nick. Nick is a nice person. He’s friends with a lot of queer people. Maybe he doesn’t always get everything about Socialism or Communism but he agrees that the world is unfair, and that aSDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
WXCAFÉ
Every git commit has an id like 3f29abcd233fa, also called 82#*+ DEFD #(!#7& +,5,+& $2 $", &#),.26, G)2&*&A()2 H)),$ 6,7 + #*& 3!0' %5) $!5 8#0 I/&$ 5+&)2&.(*+) C AAJWXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
36C3 TALKS - WXCAFÉ 36c3 Infrastructure Review ⭐⭐⭐⭐. Like each year, the infrastructure review talks about how congress works and the people who make it work. I love watching these, I loved being an Angel when I was there, and I really like learning about the parts of organizing I didn’t know about. YUBIKEY FOR EVERYTHING The default PINs are 123456 for the user PIN and 12345678 for the admin PIN.. Do take caution to export the private keys for safekeeping BEFORE moving them to the yubikey (the gpg keytocard command MOVES the keys, after you’ve run it you don’t have the private keys available anymore to backup) (backups are easily done with gpg --armor --export-secret-keys > out.asc and gpg - POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes.MY KEYBOARD.IO
My Keyboard.io. Over a year ago now I bought a keyboard, and I wanted to write about it then, but I figured I’d wait until I could type on it correctly and actually tell if it was a good keyboard.. Turns out, it took me about three weeks to learn how to type correctly, and it’s a really, really good keyboard but I forgot about writing this🤦 So here we go.
WHEN A TOY ISN'T A TOY ANYMORE Let’s say, for the sake of argument, that there’s this guy named Nick. Nick is a nice person. He’s friends with a lot of queer people. Maybe he doesn’t always get everything about Socialism or Communism but he agrees that the world is unfair, and that aSDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
WXCAFÉ
Every git commit has an id like 3f29abcd233fa, also called 82#*+ DEFD #(!#7& +,5,+& $2 $", &#),.26, G)2&*&A()2 H)),$ 6,7 + #*& 3!0' %5) $!5 8#0 I/&$ 5+&)2&.(*+) C AAJMY KEYBOARD.IO
My Keyboard.io. Over a year ago now I bought a keyboard, and I wanted to write about it then, but I figured I’d wait until I could type on it correctly and actually tell if it was a good keyboard.. Turns out, it took me about three weeks to learn how to type correctly, and it’s a really, really good keyboard but I forgot about writing this🤦 So here we go.
WHEN A TOY ISN'T A TOY ANYMORE Let’s say, for the sake of argument, that there’s this guy named Nick. Nick is a nice person. He’s friends with a lot of queer people. Maybe he doesn’t always get everything about Socialism or Communism but he agrees that the world is unfair, and that aIN THIS ISSUE
The Internet Protocol Journal 3 What Is an Autonomous System? One of the best definitions of an Autonomous System can be found in an IETF document, RFC 4271 that describes BGPv4: “The classic definition of an Autonomous System is a set of routers un- THE ATTORNEY GENERAL'S G URN ELINES ON FEDERAL BUREAU … vi. monitoring and control ~-~- of -- undercover ---operations 17preparation of undercover employees, informants, and cooperating witnesses .17 a. b. review of conduct. ..17FROM THE EDITOR
The Internet Protocol Journal 4 • Mail Delivery Agent (MDA): The MDA is responsible for transfer - ring the message from the MHS to the Message Store (MS). • Message Store (MS): An MUA can employ a long-term MS. An MS can be located on a remote server or on the samemachine as the
IP MULTI-ADRESSING AND MULTIPATH TCP The Internet Protocol Journal 2 IP Multi-Adressing and Multipath TCP by Geoff Huston, APNIC T he Transmission Control Protocol (TCP) is a core protocol of theIN THIS ISSUE
The Internet Protocol Journal 2 RIPE Atlas: A Global Internet Measurement Network by RIPE NCC Staff R IPE Atlas is a global Internet measurement network that provides an JUNE 1998 VOLUME 1, NUMBER 1 The Internet Protocol Journal 2 What Is a VPN? — Part I by Paul Ferguson, Cisco Systems and Geoff Huston, Telstra he term “VPN,” or Virtual Private NetworkIN THIS ISSUE
The Internet Protocol Journal 2 Gigabit TCP by Geoff Huston, APNIC I n looking back over some 30 years of experience with the Inter-net, the critical component of the Internet Protocol Suite that has JUNE 2002 VOLUME 5, NUMBER 2 BEEP: continued The Internet Protocol Journal 4 First, you decide that your protocol needs ordered, reliable delivery. This is a common requirement for most application protocols, includ-WXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes.BUILD - WXCAFE.NET
“Embrace diversity. Unite— or be divided, robbed, ruled, killed by those who see you as prey. Embrace diversity or be destroyed. There isno end
SDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
IN THIS ISSUE
The Internet Protocol Journal 3 Another widely adopted AAA protocol, which predates RADIUS as an RFC by four years, is the Terminal AccessController Access
THE ATTORNEY GENERAL'S G URN ELINES ON FEDERAL BUREAU … vi. monitoring and control ~-~- of -- undercover ---operations 17preparation of undercover employees, informants, and cooperating witnesses .17 a. b. review of conduct. ..17 JUNE 1998 VOLUME 1, NUMBER 1 The Internet Protocol Journal 2 What Is a VPN? — Part I by Paul Ferguson, Cisco Systems and Geoff Huston, Telstra he term “VPN,” or Virtual Private Network MARCH 2011 VOLUME 14, NUMBER 1 The Internet Protocol Journal 3 Perhaps the term “address” is somewhat of a misnomer in this con-text, but it may well be too lateto change that now.
WXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes.BUILD - WXCAFE.NET
“Embrace diversity. Unite— or be divided, robbed, ruled, killed by those who see you as prey. Embrace diversity or be destroyed. There isno end
SDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
IN THIS ISSUE
The Internet Protocol Journal 3 Another widely adopted AAA protocol, which predates RADIUS as an RFC by four years, is the Terminal AccessController Access
THE ATTORNEY GENERAL'S G URN ELINES ON FEDERAL BUREAU … vi. monitoring and control ~-~- of -- undercover ---operations 17preparation of undercover employees, informants, and cooperating witnesses .17 a. b. review of conduct. ..17 JUNE 1998 VOLUME 1, NUMBER 1 The Internet Protocol Journal 2 What Is a VPN? — Part I by Paul Ferguson, Cisco Systems and Geoff Huston, Telstra he term “VPN,” or Virtual Private Network MARCH 2011 VOLUME 14, NUMBER 1 The Internet Protocol Journal 3 Perhaps the term “address” is somewhat of a misnomer in this con-text, but it may well be too lateto change that now.
YUBIKEY FOR EVERYTHING The default PINs are 123456 for the user PIN and 12345678 for the admin PIN.. Do take caution to export the private keys for safekeeping BEFORE moving them to the yubikey (the gpg keytocard command MOVES the keys, after you’ve run it you don’t have the private keys available anymore to backup) (backups are easily done with gpg --armor --export-secret-keys > out.asc and gpg - POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes. WHEN A TOY ISN'T A TOY ANYMORE Let’s say, for the sake of argument, that there’s this guy named Nick. Nick is a nice person. He’s friends with a lot of queer people. Maybe he doesn’t always get everything about Socialism or Communism but he agrees that the world is unfair, and that a MOVING TO TH̶E̶ ̶U̶S̶ ̶NEW YORK So, uh, yeah. Even though it might not have been evident if you extrapolated my sleep cycle from my twitter activity, I’ve always lived in France, I was born there and I grew up there.IN THIS ISSUE
The Internet Protocol Journal 3 What Is an Autonomous System? One of the best definitions of an Autonomous System can be found in an IETF document, RFC 4271 that describes BGPv4: “The classic definition of an Autonomous System is a set of routers un-FROM THE EDITOR
The Internet Protocol Journal 4 • Mail Delivery Agent (MDA): The MDA is responsible for transfer - ring the message from the MHS to the Message Store (MS). • Message Store (MS): An MUA can employ a long-term MS. An MS can be located on a remote server or on the samemachine as the
IP MULTI-ADRESSING AND MULTIPATH TCP The Internet Protocol Journal 2 IP Multi-Adressing and Multipath TCP by Geoff Huston, APNIC T he Transmission Control Protocol (TCP) is a core protocol of the SEPTEMBER 2005 VOLUME 8, NUMBER 3 IPv4 Address Space Consumption: continued The Internet Protocol Journal 4 Figure 3: IANA Allocations to RIRs — Sliding-Window 24-Month Average Taken by MARCH 2001 VOLUME 4, NUMBER 1 The BGP Routing Table: continued The Internet Protocol Journal 4 Figure 2: BGP Table Growth 1988–1994 CIDR Deployment The response from the engineering community was the introduction of JUNE 2002 VOLUME 5, NUMBER 2 BEEP: continued The Internet Protocol Journal 4 First, you decide that your protocol needs ordered, reliable delivery. This is a common requirement for most application protocols, includ-WXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes.BUILD - WXCAFE.NET
“Embrace diversity. Unite— or be divided, robbed, ruled, killed by those who see you as prey. Embrace diversity or be destroyed. There isno end
SDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
IN THIS ISSUE
The Internet Protocol Journal 3 Another widely adopted AAA protocol, which predates RADIUS as an RFC by four years, is the Terminal AccessController Access
THE ATTORNEY GENERAL'S G URN ELINES ON FEDERAL BUREAU … vi. monitoring and control ~-~- of -- undercover ---operations 17preparation of undercover employees, informants, and cooperating witnesses .17 a. b. review of conduct. ..17 JUNE 1998 VOLUME 1, NUMBER 1 The Internet Protocol Journal 2 What Is a VPN? — Part I by Paul Ferguson, Cisco Systems and Geoff Huston, Telstra he term “VPN,” or Virtual Private Network MARCH 2011 VOLUME 14, NUMBER 1 The Internet Protocol Journal 3 Perhaps the term “address” is somewhat of a misnomer in this con-text, but it may well be too lateto change that now.
WXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes.BUILD - WXCAFE.NET
“Embrace diversity. Unite— or be divided, robbed, ruled, killed by those who see you as prey. Embrace diversity or be destroyed. There isno end
SDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
IN THIS ISSUE
The Internet Protocol Journal 3 Another widely adopted AAA protocol, which predates RADIUS as an RFC by four years, is the Terminal AccessController Access
THE ATTORNEY GENERAL'S G URN ELINES ON FEDERAL BUREAU … vi. monitoring and control ~-~- of -- undercover ---operations 17preparation of undercover employees, informants, and cooperating witnesses .17 a. b. review of conduct. ..17 JUNE 1998 VOLUME 1, NUMBER 1 The Internet Protocol Journal 2 What Is a VPN? — Part I by Paul Ferguson, Cisco Systems and Geoff Huston, Telstra he term “VPN,” or Virtual Private Network MARCH 2011 VOLUME 14, NUMBER 1 The Internet Protocol Journal 3 Perhaps the term “address” is somewhat of a misnomer in this con-text, but it may well be too lateto change that now.
YUBIKEY FOR EVERYTHING The default PINs are 123456 for the user PIN and 12345678 for the admin PIN.. Do take caution to export the private keys for safekeeping BEFORE moving them to the yubikey (the gpg keytocard command MOVES the keys, after you’ve run it you don’t have the private keys available anymore to backup) (backups are easily done with gpg --armor --export-secret-keys > out.asc and gpg - POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes. WHEN A TOY ISN'T A TOY ANYMORE Let’s say, for the sake of argument, that there’s this guy named Nick. Nick is a nice person. He’s friends with a lot of queer people. Maybe he doesn’t always get everything about Socialism or Communism but he agrees that the world is unfair, and that a MOVING TO TH̶E̶ ̶U̶S̶ ̶NEW YORK So, uh, yeah. Even though it might not have been evident if you extrapolated my sleep cycle from my twitter activity, I’ve always lived in France, I was born there and I grew up there.IN THIS ISSUE
The Internet Protocol Journal 3 What Is an Autonomous System? One of the best definitions of an Autonomous System can be found in an IETF document, RFC 4271 that describes BGPv4: “The classic definition of an Autonomous System is a set of routers un-FROM THE EDITOR
The Internet Protocol Journal 4 • Mail Delivery Agent (MDA): The MDA is responsible for transfer - ring the message from the MHS to the Message Store (MS). • Message Store (MS): An MUA can employ a long-term MS. An MS can be located on a remote server or on the samemachine as the
SEPTEMBER 2005 VOLUME 8, NUMBER 3 IPv4 Address Space Consumption: continued The Internet Protocol Journal 4 Figure 3: IANA Allocations to RIRs — Sliding-Window 24-Month Average Taken by IP MULTI-ADRESSING AND MULTIPATH TCP The Internet Protocol Journal 2 IP Multi-Adressing and Multipath TCP by Geoff Huston, APNIC T he Transmission Control Protocol (TCP) is a core protocol of the MARCH 2001 VOLUME 4, NUMBER 1 The BGP Routing Table: continued The Internet Protocol Journal 4 Figure 2: BGP Table Growth 1988–1994 CIDR Deployment The response from the engineering community was the introduction of JUNE 2002 VOLUME 5, NUMBER 2 BEEP: continued The Internet Protocol Journal 4 First, you decide that your protocol needs ordered, reliable delivery. This is a common requirement for most application protocols, includ-WXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes.BUILD - WXCAFE.NET
“Embrace diversity. Unite— or be divided, robbed, ruled, killed by those who see you as prey. Embrace diversity or be destroyed. There isno end
SDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
IN THIS ISSUE
The Internet Protocol Journal 3 Another widely adopted AAA protocol, which predates RADIUS as an RFC by four years, is the Terminal AccessController Access
THE ATTORNEY GENERAL'S G URN ELINES ON FEDERAL BUREAU … vi. monitoring and control ~-~- of -- undercover ---operations 17preparation of undercover employees, informants, and cooperating witnesses .17 a. b. review of conduct. ..17 JUNE 1998 VOLUME 1, NUMBER 1 The Internet Protocol Journal 2 What Is a VPN? — Part I by Paul Ferguson, Cisco Systems and Geoff Huston, Telstra he term “VPN,” or Virtual Private Network MARCH 2011 VOLUME 14, NUMBER 1 The Internet Protocol Journal 3 Perhaps the term “address” is somewhat of a misnomer in this con-text, but it may well be too lateto change that now.
WXCAFÉ
Security for the savvy leftist, Part Ⅰ: OpSec. Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online Posted by USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a lot of confusion on the user side and a lot of frustration on the network admin side.So I decided to write this little guide on how traceroute and mtr work, how to use it, and how to read the tea leaves interpretthe output.
POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes.BUILD - WXCAFE.NET
“Embrace diversity. Unite— or be divided, robbed, ruled, killed by those who see you as prey. Embrace diversity or be destroyed. There isno end
SDN ARCHITECTURE
The Internet Protocol Journal 3 Another factor leading to the need for rapid response in allocat-ing network resources is the increasing use by employees of mobile DECEMBER 1998 VOLUME 1, NUMBER 3 The New SNMPv3 Proposed Internet Standards: continued The Internet Protocol Journal 6 The topmost layer is the PDU processing layer. Atthis layer, manage-
IN THIS ISSUE
The Internet Protocol Journal 3 Another widely adopted AAA protocol, which predates RADIUS as an RFC by four years, is the Terminal AccessController Access
THE ATTORNEY GENERAL'S G URN ELINES ON FEDERAL BUREAU … vi. monitoring and control ~-~- of -- undercover ---operations 17preparation of undercover employees, informants, and cooperating witnesses .17 a. b. review of conduct. ..17 JUNE 1998 VOLUME 1, NUMBER 1 The Internet Protocol Journal 2 What Is a VPN? — Part I by Paul Ferguson, Cisco Systems and Geoff Huston, Telstra he term “VPN,” or Virtual Private Network MARCH 2011 VOLUME 14, NUMBER 1 The Internet Protocol Journal 3 Perhaps the term “address” is somewhat of a misnomer in this con-text, but it may well be too lateto change that now.
YUBIKEY FOR EVERYTHING The default PINs are 123456 for the user PIN and 12345678 for the admin PIN.. Do take caution to export the private keys for safekeeping BEFORE moving them to the yubikey (the gpg keytocard command MOVES the keys, after you’ve run it you don’t have the private keys available anymore to backup) (backups are easily done with gpg --armor --export-secret-keys > out.asc and gpg - POCKETBOOK DISSASSEMBLY AND ROOT So uh a few years (! time flies) back I wanted to get an ereader to (e-read?) read books for cheap and not carry a suitcase of paperbacks whenever I traveled (plus a lot of other advantages. I like ebooks, they’re tiny, convenient and disposable. There are lots of books I prefer reading on paper, but I can’t deny ebooks are neat sometimes. WHEN A TOY ISN'T A TOY ANYMORE Let’s say, for the sake of argument, that there’s this guy named Nick. Nick is a nice person. He’s friends with a lot of queer people. Maybe he doesn’t always get everything about Socialism or Communism but he agrees that the world is unfair, and that a MOVING TO TH̶E̶ ̶U̶S̶ ̶NEW YORK So, uh, yeah. Even though it might not have been evident if you extrapolated my sleep cycle from my twitter activity, I’ve always lived in France, I was born there and I grew up there.IN THIS ISSUE
The Internet Protocol Journal 3 What Is an Autonomous System? One of the best definitions of an Autonomous System can be found in an IETF document, RFC 4271 that describes BGPv4: “The classic definition of an Autonomous System is a set of routers un-FROM THE EDITOR
The Internet Protocol Journal 4 • Mail Delivery Agent (MDA): The MDA is responsible for transfer - ring the message from the MHS to the Message Store (MS). • Message Store (MS): An MUA can employ a long-term MS. An MS can be located on a remote server or on the samemachine as the
SEPTEMBER 2005 VOLUME 8, NUMBER 3 IPv4 Address Space Consumption: continued The Internet Protocol Journal 4 Figure 3: IANA Allocations to RIRs — Sliding-Window 24-Month Average Taken by IP MULTI-ADRESSING AND MULTIPATH TCP The Internet Protocol Journal 2 IP Multi-Adressing and Multipath TCP by Geoff Huston, APNIC T he Transmission Control Protocol (TCP) is a core protocol of the MARCH 2001 VOLUME 4, NUMBER 1 The BGP Routing Table: continued The Internet Protocol Journal 4 Figure 2: BGP Table Growth 1988–1994 CIDR Deployment The response from the engineering community was the introduction of JUNE 2002 VOLUME 5, NUMBER 2 BEEP: continued The Internet Protocol Journal 4 First, you decide that your protocol needs ordered, reliable delivery. This is a common requirement for most application protocols, includ- Toggle navigation WxcaféWXCAFÉ
SECURITY FOR THE SAVVY LEFTIST, PART Ⅰ: OPSEC Introduction This is the first in a series of post trying to give a few pointers and share a bit of knowledge on securing your online... Posted by Wxcafé on Thu 14 May 202036C3 TALKS
So a bit over a month ago, like every year, hackers gathered in Leipzig, Germany for the Chaos Communication Congress. This year,like...
Posted by Wxcafé on Sun 02 February2020
USING TRACEROUTE/MTR, OR: DIAGNOSING NETWORK PROBLEMS 101 I was a in a twitter discussion recently about Traceroute, and how it was not necessarily as simple as it seemed, and that it caused a... Posted by Wxcafé on Fri 13 December2019
MY KEYBOARD.IO
My Keyboard.io Over a year ago now I bought a keyboard, and I wanted to write about it then, but I figured I’d wait until I could type... Posted by Wxcafe on Fri 19 July 2019‼️CON
So, this past weekend I was at ‼️con (pronounced bang bang con), a conference in NYC about “The joy, excitement, and surprise of... Posted by Wxcafé on Mon 13 May 2019 WHEN A TOY ISN'T A TOY ANYMORE Let’s say, for the sake of argument, that there’s this guy named Nick. Nick is a nice person. He’s friends with a lot of queerpeople....
Posted by Wxcafé on Sun 28 April2019
MOVING TO TH̶E̶ ̶U̶S̶ ̶NEW YORK So, uh, yeah. Even though it might not have been evident if you extrapolated my sleep cycle from my twitter activity, I’ve alwayslived...
Posted by Wxcafé on Mon 04 February2019
YUBIKEY FOR EVERYTHING EDIT: Update 07/07/2018, added SSH_AUTH_SOCK information, a few pointers about key generation and backup, and info about gpg-agent’sbad...
Posted by Wxcafé on Sat 07 July2018
(NEO)MUTT FUCKERY WITH MULTIPART MESSAGES I’ve been using Mutt, and then Neomutt, as an email client on my laptops for a while (I generally use Evolution on my desktop,because...
Posted by Wxcafé on Tue 03 July2018
POC||GTFO 0X18
So PoC||GTFO 0x18 was released in PDF today. Contrary to issue 0x17, and like all previous issues, I wasn’t able to get it in paper... Posted by Wxcafé on Mon 25 June2018
-------------------------* Older Posts →
Page 1 / 5
------------------------- -------------------------* __ __
* __ __
* __ __
* __ __
* __ __
* __ __
* __ __
Blog powered by Pelican , which takes great advantage of Python . Theme is based on Pelican Clean Blog Fonts by Velvetyne Type FoundryDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0