Are you over 18 and want to see adult content?
More Annotations

A complete backup of parktours.com.au
Are you over 18 and want to see adult content?
A complete backup of successdynamicsinstitute.com
Are you over 18 and want to see adult content?
A complete backup of travelanddestinations.com
Are you over 18 and want to see adult content?
Favourite Annotations
A complete backup of worldwidewives.com
Are you over 18 and want to see adult content?
A complete backup of www.neatmovies.com
Are you over 18 and want to see adult content?

A complete backup of www.kaufmich.com
Are you over 18 and want to see adult content?

A complete backup of www.lushstories.com
Are you over 18 and want to see adult content?
Text
COMPANY
CTO of ShiftLeft. Chetan is a serial entrepreneur with over 20+ years of experience in authoring and architecting mission critical software. His expertise includes building web-scale distributed infrastructure, personalization algorithms, complex event processing, fraud detection, and prevention in investment/retail banking domains. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databasesC# | SHIFTLEFT DOCS
ShiftLeft offers a sample application that you can use to run and test NG SAST. It also includes a functioning configuration file to demonstrate how you can leverage Azure Pipelines or GitHub Actions to automate code analysis whenever you open a new Pull Request (PR). To HOW TO DETECT 0-DAY VULNERABILITIES How to Detect 0-day Vulnerabilities. A 0-day vulnerability is unknown to, or unaddressed by, developers and security researchers and is considered a severe threat. Until an 0-day vulnerability is identified and mitigated, hackers can exploit it. This use case is based on CVE-2018-19859, a vulnerability allowing an attacker to executearbitrary
SCANNING FOR SECRETS IN SOURCE CODE The most straightforward way to detect hardcoded credentials is to use text search and regex. Hardcoded credentials such as API keys, encryption keys, and database passwords can often be discovered by grepping for keywords such as “key”, “secret”, “password”, or “aws”. These searches target identifiers, like variable names,that
FORRESTER: THE STATE OF APPLICATION SECURITY Download Forrester's The State of Application Security report. SHIFTLEFTGET STARTEDTERMS OF SERVICEWHITEPAPERSWATCH WEBINARCOMPANY Contextual Security Education. Finding bugs isn’t the hard part, it’s fixing them. ShiftLeft Educate is an optional add-on that embeds security training directly into ShiftLeft CORE allowing developers to learn in real-time how to fix issues without having to switch context. Learn More. CODE PROPERTY GRAPH EXPLAINED Data Flow Tracker . The workhorse of the CPG is a state-of-the-art data-flow tracker. The data-flow tracker is interprocedural, flow-sensitive, context-sensitive, field-sensitive, and operates on an intermediate code representation (see semantic code property graphs).The engine performs on-the-fly points-to analysis to resolve call sites and is able to benefit from the results of constant INTELLIGENT SOFTWARE COMPOSITION ANALYSIS Intelligent SCA Reduces Your OSS Vulnerability Tickets by 90%. ShiftLeft’s Intelligent SCA uses the full power of Code Property Graph to analyze both custom and open-source vulnerabilities and introduces the concept of “Attacker Reachability” to prioritize only a subset of vulnerabilities for mitigation.COMPANY
CTO of ShiftLeft. Chetan is a serial entrepreneur with over 20+ years of experience in authoring and architecting mission critical software. His expertise includes building web-scale distributed infrastructure, personalization algorithms, complex event processing, fraud detection, and prevention in investment/retail banking domains. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databasesC# | SHIFTLEFT DOCS
ShiftLeft offers a sample application that you can use to run and test NG SAST. It also includes a functioning configuration file to demonstrate how you can leverage Azure Pipelines or GitHub Actions to automate code analysis whenever you open a new Pull Request (PR). To HOW TO DETECT 0-DAY VULNERABILITIES How to Detect 0-day Vulnerabilities. A 0-day vulnerability is unknown to, or unaddressed by, developers and security researchers and is considered a severe threat. Until an 0-day vulnerability is identified and mitigated, hackers can exploit it. This use case is based on CVE-2018-19859, a vulnerability allowing an attacker to executearbitrary
SCANNING FOR SECRETS IN SOURCE CODE The most straightforward way to detect hardcoded credentials is to use text search and regex. Hardcoded credentials such as API keys, encryption keys, and database passwords can often be discovered by grepping for keywords such as “key”, “secret”, “password”, or “aws”. These searches target identifiers, like variable names,that
FORRESTER: THE STATE OF APPLICATION SECURITY Download Forrester's The State of Application Security report.COMPANY
CTO of ShiftLeft. Chetan is a serial entrepreneur with over 20+ years of experience in authoring and architecting mission critical software. His expertise includes building web-scale distributed infrastructure, personalization algorithms, complex event processing, fraud detection, and prevention in investment/retail banking domains.SHIFTLEFT | LEARN
Directory Traversal. Learn how to use NG SAST to identify and fix the areas of your code that make your application vulnerable to directory traversal exploitation. Start Course. Free Training. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.SHIFTLEFT WEBINAR
Developer-based from the start, ShiftLeft CORE enables organizations of all sizes to help create secure products. We know the difficulties of trying to integrate security into DevOps workflows and have created ShiftLeft CORE to securely write applications without disruptingcurrent processes.
JAVA | SHIFTLEFT DOCS Requirements#. NG SAST supports the analysis of applications written in Java 7 through Java 11. We offer partial support for apps written in Java 14 and 15 (please reach out to ShiftLeft for additional details). Your build environment must have at least 16 GB of memory available. NG SAST utilizes Java SE Runtime Environment 8; ifnecessary, you
BEATING THE OWASP BENCHMARK WITH ALOK SHUKLA Photo by Aaron Burden on Unsplash. Welcome back to another episode of sources and sinks. The OWASP benchmark project is an OWASP initiative designed to measure the accuracy of security scanners. SECURITY COMPLIANCE REPORTS WITH SHIFTLEFT SCAN Clone them locally using git. Invoke ShiftLeft Scan for each repo. Copy the reports into a separate directory. The below script should work with bash and tested on Linux, Mac, and with WSL on Windows. If this script fails with ssh authentication errors, make sure that your ssh public key is added to GitHub and that you have the read access to MITIGATING NOSQL INJECTION ATTACKS: PART 2 Mitigating NoSQL Injection Attacks: Part 2. This is the second part of a two-part series on NoSQL injections. Last time, we covered the anatomy of a NoSQL injection, as well as how to mitigate it. In this post, we will look at specific injection attack types, FORRESTER: THE STATE OF APPLICATION SECURITY Download Forrester's The State of Application Security report. INSERTING SECURITY IN GITHUB PULL REQUESTS! This post builds up in a previous post about inserting code analysis into GitHub pull requests, in this post, we will focus on implementing this workflow based on GitHub Actions for aSHIFTLEFT
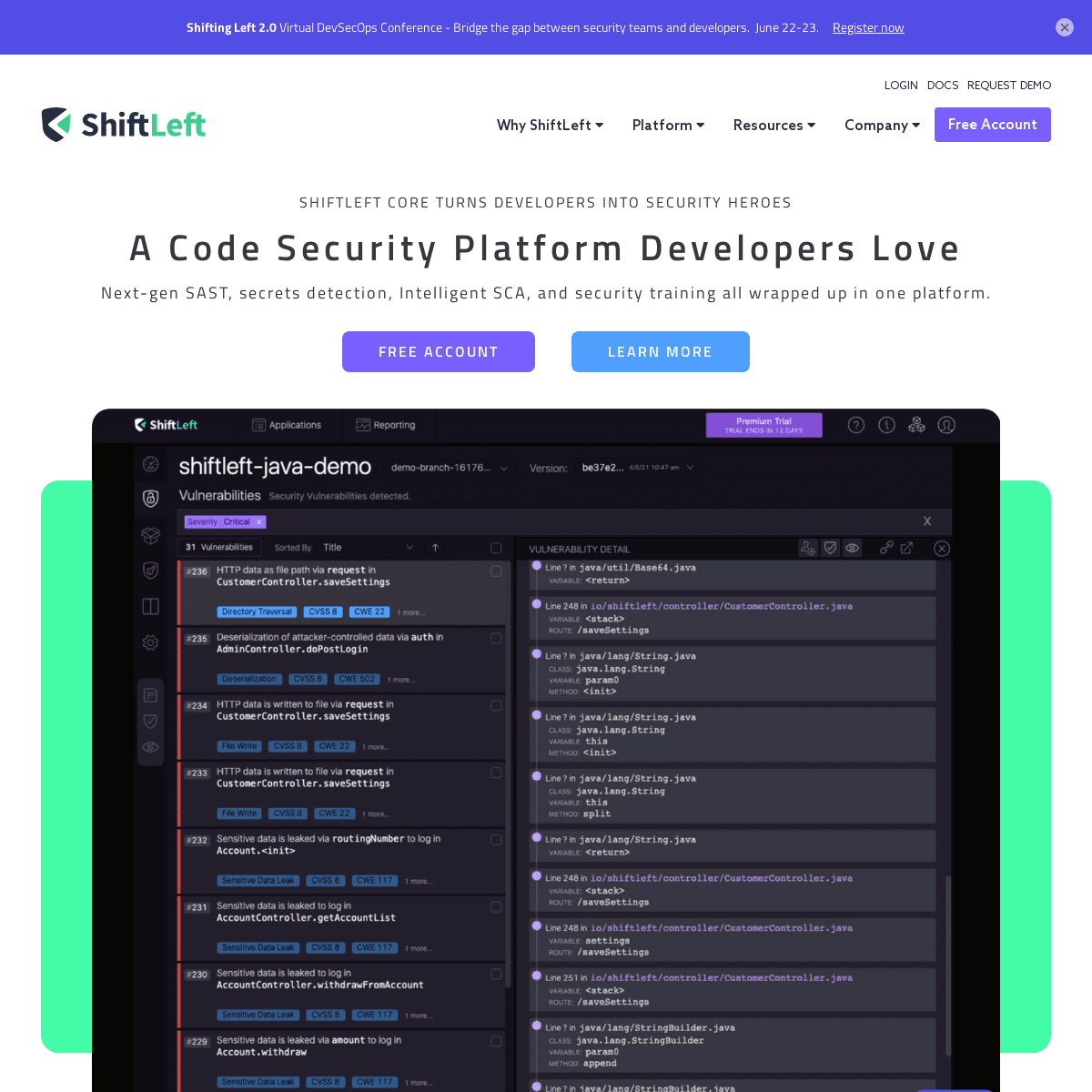
ShiftLeft CORE turns developers into security heroes. A Code Security Platform Developers Love Next-gen SAST, secrets detection, Intelligent SCA, and security training all wrapped up in one platform. CODE PROPERTY GRAPH EXPLAINED Data Flow Tracker . The workhorse of the CPG is a state-of-the-art data-flow tracker. The data-flow tracker is interprocedural, flow-sensitive, context-sensitive, field-sensitive, and operates on an intermediate code representation (see semantic code property graphs).The engine performs on-the-fly points-to analysis to resolve call sites and is able to benefit from the results of constant INTELLIGENT SOFTWARE COMPOSITION ANALYSIS Intelligent SCA Reduces Your OSS Vulnerability Tickets by 90%. ShiftLeft’s Intelligent SCA uses the full power of Code Property Graph to analyze both custom and open-source vulnerabilities and introduces the concept of “Attacker Reachability” to prioritize only a subset of vulnerabilities for mitigation. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databasesC# | SHIFTLEFT DOCS
ShiftLeft offers a sample application that you can use to run and test NG SAST. It also includes a functioning configuration file to demonstrate how you can leverage Azure Pipelines or GitHub Actions to automate code analysis whenever you open a new Pull Request (PR). To THE IMPORTANCE OF APPLICATION SECURITY The Importance of Application Security The two most important problems in Cybersecurity today are phishing and vulnerabilities. The #1 tacticused by
SCANNING FOR SECRETS IN SOURCE CODE The most straightforward way to detect hardcoded credentials is to use text search and regex. Hardcoded credentials such as API keys, encryption keys, and database passwords can often be discovered by grepping for keywords such as “key”, “secret”, “password”, or “aws”. These searches target identifiers, like variable names,that
DIRECTORY TRAVERSAL (DUBBED ZIPSLIP) VULNERABILITY Recently, we’ve identified a number of our customers who are susceptible to a Directory traversal vulnerability. The exploit chain (circumstances to exploit the vulnerability) is being triggered by customer application’s dependency on a DeepLearning4j ArchiveUtils utility. This vulnerability is particularly tricky to catch, because it is contextual: The exposure comes from how impacted INSERTING SECURITY IN GITHUB PULL REQUESTS! This post builds up in a previous post about inserting code analysis into GitHub pull requests, in this post, we will focus on implementing this workflow based on GitHub Actions for aSHIFTLEFT
ShiftLeft CORE turns developers into security heroes. A Code Security Platform Developers Love Next-gen SAST, secrets detection, Intelligent SCA, and security training all wrapped up in one platform. CODE PROPERTY GRAPH EXPLAINED Data Flow Tracker . The workhorse of the CPG is a state-of-the-art data-flow tracker. The data-flow tracker is interprocedural, flow-sensitive, context-sensitive, field-sensitive, and operates on an intermediate code representation (see semantic code property graphs).The engine performs on-the-fly points-to analysis to resolve call sites and is able to benefit from the results of constant INTELLIGENT SOFTWARE COMPOSITION ANALYSIS Intelligent SCA Reduces Your OSS Vulnerability Tickets by 90%. ShiftLeft’s Intelligent SCA uses the full power of Code Property Graph to analyze both custom and open-source vulnerabilities and introduces the concept of “Attacker Reachability” to prioritize only a subset of vulnerabilities for mitigation. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databasesC# | SHIFTLEFT DOCS
ShiftLeft offers a sample application that you can use to run and test NG SAST. It also includes a functioning configuration file to demonstrate how you can leverage Azure Pipelines or GitHub Actions to automate code analysis whenever you open a new Pull Request (PR). To THE IMPORTANCE OF APPLICATION SECURITY The Importance of Application Security The two most important problems in Cybersecurity today are phishing and vulnerabilities. The #1 tacticused by
SCANNING FOR SECRETS IN SOURCE CODE The most straightforward way to detect hardcoded credentials is to use text search and regex. Hardcoded credentials such as API keys, encryption keys, and database passwords can often be discovered by grepping for keywords such as “key”, “secret”, “password”, or “aws”. These searches target identifiers, like variable names,that
DIRECTORY TRAVERSAL (DUBBED ZIPSLIP) VULNERABILITY Recently, we’ve identified a number of our customers who are susceptible to a Directory traversal vulnerability. The exploit chain (circumstances to exploit the vulnerability) is being triggered by customer application’s dependency on a DeepLearning4j ArchiveUtils utility. This vulnerability is particularly tricky to catch, because it is contextual: The exposure comes from how impacted INSERTING SECURITY IN GITHUB PULL REQUESTS! This post builds up in a previous post about inserting code analysis into GitHub pull requests, in this post, we will focus on implementing this workflow based on GitHub Actions for aCOMPANY
CTO of ShiftLeft. Chetan is a serial entrepreneur with over 20+ years of experience in authoring and architecting mission critical software. His expertise includes building web-scale distributed infrastructure, personalization algorithms, complex event processing, fraud detection, and prevention in investment/retail banking domains. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.OCULAR - SHIFTLEFT
Ocular is a scala-based read-eval-print-loop (REPL) tool to traverse the graph. For example, Ocular enables you to query for all the sources and sinks of a critical data variable. It can list every transform on each route to ensure that data is always handled properly and never leaking to a logger.SHIFTLEFT BLOG
ShiftLeft is NextGen code analysis, purpose-built to automate security workflows delivering the right developer with the right vulnerabilities at the right time.SHIFTLEFT WEBINAR
Developer-based from the start, ShiftLeft CORE enables organizations of all sizes to help create secure products. We know the difficulties of trying to integrate security into DevOps workflows and have created ShiftLeft CORE to securely write applications without disruptingcurrent processes.
THE IMPORTANCE OF APPLICATION SECURITY The Importance of Application Security The two most important problems in Cybersecurity today are phishing and vulnerabilities. The #1 tacticused by
JAVA | SHIFTLEFT DOCS Requirements#. NG SAST supports the analysis of applications written in Java 7 through Java 11. We offer partial support for apps written in Java 14 and 15 (please reach out to ShiftLeft for additional details). Your build environment must have at least 16 GB of memory available. NG SAST utilizes Java SE Runtime Environment 8; ifnecessary, you
HOW TO REVIEW CODE FOR VULNERABILITIES Some Code Analysis Jargon. Before we go on, there are a few concepts that you should understand: “sources”, “sinks”, and “data flow”. In code analysis speak, a “source” is the code that allows a vulnerability to happen. Whereas a “sink” is where the vulnerability actually happens. Take command injection vulnerabilities, for FORRESTER: THE STATE OF APPLICATION SECURITY Download Forrester's The State of Application Security report. INSERTING SECURITY IN GITHUB PULL REQUESTS! This post builds up in a previous post about inserting code analysis into GitHub pull requests, in this post, we will focus on implementing this workflow based on GitHub Actions for a SHIFTLEFTGET STARTEDTERMS OF SERVICEWHITEPAPERSWATCH WEBINARCOMPANY ShiftLeft CORE turns developers into security heroes. A Code Security Platform Developers Love Next-gen SAST, secrets detection, Intelligent SCA, and security training all wrapped up in one platform. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed. INSTALL | SHIFTLEFT DOCS This article will show you how to install the ShiftLeft CLI, as well as how to associate it with your ShiftLeft account.CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databases SHIFTLEFT API REFERENCE ShiftLeft is a next-gen code analysis platform purpose built for developers.. Its Code Property Graph (CPG) depicts your application's control flow, program dependencies, and abstract syntax trees as a single data structure, enabling you to understand fundamentally what each version of your app does and find any scenarios that may pose risks.. Integrate Code Analysis into an Existing Workflow#C# | SHIFTLEFT DOCS
.NET 5.0 is not currently supported. Machine Requirements#. We recommend running NG SAST on a machine with a minimum of 4 GB RAM and 2 CPU Cores.For each subsequent 100,000 lines of code that you submit for analysis, we recommend an additional 2 GB RAM and 1+ CPU Core. HOW TO DETECT 0-DAY VULNERABILITIES Then run java2cpg with the -w flag, followed by a comma-separated list of package-names (com.google.refine, org.openrefine) to be included in the CPG.Only the parts of the application with the package prefixes com.google.refine and org.openrefine are included in the CPG. For relatively large applications such as OpenRefine, focusing on specific application parts can save computing and QUICKSTART | SHIFTLEFT DOCS Ocular is a command-line tool for static code analysis. Ocular can help you find and correct security vulnerabilities in programs with hundreds of thousands lines of code, including flaws that are extremely difficult to detect. It includes an interactive shell and powerful automation capabilities, all centered around a data structure specifically designed for vulnerability discovery: the Code 6 REQUIREMENTS FOR ACHIEVING DEVSECOPS Just as widespread cloud application adoption has led to the emergence of cloud-centric management tools (Okta, New Relic, Mulesoft, etc.), as the DevOps movement reaches ubiquity, the need for DevSecOpsbecomes more acute.
DIRECTORY TRAVERSAL (DUBBED ZIPSLIP) VULNERABILITY Recently, we’ve identified a number of our customers who are susceptible to a Directory traversal vulnerability. The exploit chain (circumstances to exploit the vulnerability) is being triggered by customer application’s dependency on a DeepLearning4j ArchiveUtils utility. This vulnerability is particularly tricky to catch, because it is contextual: The exposure comes from how impacted SHIFTLEFTGET STARTEDTERMS OF SERVICEWHITEPAPERSWATCH WEBINARCOMPANY ShiftLeft CORE turns developers into security heroes. A Code Security Platform Developers Love Next-gen SAST, secrets detection, Intelligent SCA, and security training all wrapped up in one platform. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed. INSTALL | SHIFTLEFT DOCS This article will show you how to install the ShiftLeft CLI, as well as how to associate it with your ShiftLeft account.CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databases SHIFTLEFT API REFERENCE ShiftLeft is a next-gen code analysis platform purpose built for developers.. Its Code Property Graph (CPG) depicts your application's control flow, program dependencies, and abstract syntax trees as a single data structure, enabling you to understand fundamentally what each version of your app does and find any scenarios that may pose risks.. Integrate Code Analysis into an Existing Workflow#C# | SHIFTLEFT DOCS
.NET 5.0 is not currently supported. Machine Requirements#. We recommend running NG SAST on a machine with a minimum of 4 GB RAM and 2 CPU Cores.For each subsequent 100,000 lines of code that you submit for analysis, we recommend an additional 2 GB RAM and 1+ CPU Core. HOW TO DETECT 0-DAY VULNERABILITIES Then run java2cpg with the -w flag, followed by a comma-separated list of package-names (com.google.refine, org.openrefine) to be included in the CPG.Only the parts of the application with the package prefixes com.google.refine and org.openrefine are included in the CPG. For relatively large applications such as OpenRefine, focusing on specific application parts can save computing and QUICKSTART | SHIFTLEFT DOCS Ocular is a command-line tool for static code analysis. Ocular can help you find and correct security vulnerabilities in programs with hundreds of thousands lines of code, including flaws that are extremely difficult to detect. It includes an interactive shell and powerful automation capabilities, all centered around a data structure specifically designed for vulnerability discovery: the Code 6 REQUIREMENTS FOR ACHIEVING DEVSECOPS Just as widespread cloud application adoption has led to the emergence of cloud-centric management tools (Okta, New Relic, Mulesoft, etc.), as the DevOps movement reaches ubiquity, the need for DevSecOpsbecomes more acute.
DIRECTORY TRAVERSAL (DUBBED ZIPSLIP) VULNERABILITY Recently, we’ve identified a number of our customers who are susceptible to a Directory traversal vulnerability. The exploit chain (circumstances to exploit the vulnerability) is being triggered by customer application’s dependency on a DeepLearning4j ArchiveUtils utility. This vulnerability is particularly tricky to catch, because it is contextual: The exposure comes from how impactedCOMPANY
Chetan is a serial entrepreneur with over 20+ years of experience in authoring and architecting mission critical software. His expertise includes building web-scale distributed infrastructure, personalization algorithms, complex event processing, fraud detection,and prevention in
CODE PROPERTY GRAPH EXPLAINED Data Flow Tracker . The workhorse of the CPG is a state-of-the-art data-flow tracker. The data-flow tracker is interprocedural, flow-sensitive, context-sensitive, field-sensitive, and operates on an intermediate code representation (see semantic code property graphs).The engine performs on-the-fly points-to analysis to resolve call sites and is able to benefit from the results of constant BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.OCULAR - SHIFTLEFT
Powerful Query Language for Total Customization Ocular enables you to query your applications’ Code Property Graphs.Ocular is a scala-based read-eval-print-loop (REPL) tool to traverse the graph. ANALYZING HELLOSHIFTLEFT WITH NG SAST Step 3: View Your Results#. Per the instructions printed to the Terminal/Bash, open up the URL provided. This will bring you to the ShiftLeft Dashboard, where you willSHIFTLEFT WEBINAR
Developer-based from the start, ShiftLeft CORE enables organizations of all sizes to help create secure products. We know the difficulties of trying to integrate security into DevOps workflows and have created ShiftLeft CORE to securely write applications without disruptingcurrent processes.
SETTING UP NG SAST ONTO A LOCAL WORKSTATION Using the ShiftLeft CLI to Authenticate#. Once you have the ShiftLeft CLI installed, you need to associate the CLI with your ShiftLeft account. The ShiftLeft CLI command sl auth is used to authenticate with ShiftLeft and associate your applications with your organization. ANALYZING GITHUB REPOSITORIES USING NG SAST This article will walk you through the ShiftLeft workflow by showing you how to set up automated code analysis using NextGen Static Analysis (NG SAST) for a GitHub repository. MITIGATING NOSQL INJECTION ATTACKS: PART 2 This is the second part of a two-part series on NoSQL injections. Last time, we covered the anatomy of a NoSQL injection, as well as how to mitigate it.In this post, we will look at specific injection attack types, namely Server-Side JavaScript and Blind NoSQL injections. INSERTING SECURITY IN GITHUB PULL REQUESTS! This post builds up in a previous post about inserting code analysis into GitHub pull requests, in this post, we will focus on implementing this workflow based on GitHub Actions for a SHIFTLEFTGET STARTEDTERMS OF SERVICEWHITEPAPERSWATCH WEBINARCOMPANY Contextual Security Education. Finding bugs isn’t the hard part, it’s fixing them. ShiftLeft Educate is an optional add-on that embeds security training directly into ShiftLeft CORE allowing developers to learn in real-time how to fix issues without having to switch context. Learn More. INTELLIGENT SOFTWARE COMPOSITION ANALYSIS Intelligent SCA Reduces Your OSS Vulnerability Tickets by 90%. ShiftLeft’s Intelligent SCA uses the full power of Code Property Graph to analyze both custom and open-source vulnerabilities and introduces the concept of “Attacker Reachability” to prioritize only a subset of vulnerabilities for mitigation. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed. INSTALL | SHIFTLEFT DOCS This article will show you how to install the ShiftLeft CLI, as well as how to associate it with your ShiftLeft account. SHIFTLEFT API REFERENCE ShiftLeft is a next-gen code analysis platform purpose built for developers.. Its Code Property Graph (CPG) depicts your application's control flow, program dependencies, and abstract syntax trees as a single data structure, enabling you to understand fundamentally what each version of your app does and find any scenarios that may pose risks.. Integrate Code Analysis into an Existing Workflow#CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databasesC# | SHIFTLEFT DOCS
ShiftLeft offers a sample application that you can use to run and test NG SAST. It also includes a functioning configuration file to demonstrate how you can leverage Azure Pipelines or GitHub Actions to automate code analysis whenever you open a new Pull Request (PR). To QUICKSTART | SHIFTLEFT DOCS Quickstart. Ocular is a command-line tool for static code analysis. Ocular can help you find and correct security vulnerabilities in programs with hundreds of thousands lines of code, including flaws that are extremely difficult to detect. It includes an interactive shell and powerful automation capabilities, all centered around a data HOW TO DETECT 0-DAY VULNERABILITIES How to Detect 0-day Vulnerabilities. A 0-day vulnerability is unknown to, or unaddressed by, developers and security researchers and is considered a severe threat. Until an 0-day vulnerability is identified and mitigated, hackers can exploit it. This use case is based on CVE-2018-19859, a vulnerability allowing an attacker to executearbitrary
DIRECTORY TRAVERSAL (DUBBED ZIPSLIP) VULNERABILITY Recently, we’ve identified a number of our customers who are susceptible to a Directory traversal vulnerability. The exploit chain (circumstances to exploit the vulnerability) is being triggered by customer application’s dependency on a DeepLearning4j ArchiveUtils utility. This vulnerability is particularly tricky to catch, because it is contextual: The exposure comes from how impacted SHIFTLEFTGET STARTEDTERMS OF SERVICEWHITEPAPERSWATCH WEBINARCOMPANY Contextual Security Education. Finding bugs isn’t the hard part, it’s fixing them. ShiftLeft Educate is an optional add-on that embeds security training directly into ShiftLeft CORE allowing developers to learn in real-time how to fix issues without having to switch context. Learn More. INTELLIGENT SOFTWARE COMPOSITION ANALYSIS Intelligent SCA Reduces Your OSS Vulnerability Tickets by 90%. ShiftLeft’s Intelligent SCA uses the full power of Code Property Graph to analyze both custom and open-source vulnerabilities and introduces the concept of “Attacker Reachability” to prioritize only a subset of vulnerabilities for mitigation. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed. INSTALL | SHIFTLEFT DOCS This article will show you how to install the ShiftLeft CLI, as well as how to associate it with your ShiftLeft account. SHIFTLEFT API REFERENCE ShiftLeft is a next-gen code analysis platform purpose built for developers.. Its Code Property Graph (CPG) depicts your application's control flow, program dependencies, and abstract syntax trees as a single data structure, enabling you to understand fundamentally what each version of your app does and find any scenarios that may pose risks.. Integrate Code Analysis into an Existing Workflow#CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databasesC# | SHIFTLEFT DOCS
ShiftLeft offers a sample application that you can use to run and test NG SAST. It also includes a functioning configuration file to demonstrate how you can leverage Azure Pipelines or GitHub Actions to automate code analysis whenever you open a new Pull Request (PR). To QUICKSTART | SHIFTLEFT DOCS Quickstart. Ocular is a command-line tool for static code analysis. Ocular can help you find and correct security vulnerabilities in programs with hundreds of thousands lines of code, including flaws that are extremely difficult to detect. It includes an interactive shell and powerful automation capabilities, all centered around a data HOW TO DETECT 0-DAY VULNERABILITIES How to Detect 0-day Vulnerabilities. A 0-day vulnerability is unknown to, or unaddressed by, developers and security researchers and is considered a severe threat. Until an 0-day vulnerability is identified and mitigated, hackers can exploit it. This use case is based on CVE-2018-19859, a vulnerability allowing an attacker to executearbitrary
DIRECTORY TRAVERSAL (DUBBED ZIPSLIP) VULNERABILITY Recently, we’ve identified a number of our customers who are susceptible to a Directory traversal vulnerability. The exploit chain (circumstances to exploit the vulnerability) is being triggered by customer application’s dependency on a DeepLearning4j ArchiveUtils utility. This vulnerability is particularly tricky to catch, because it is contextual: The exposure comes from how impactedCOMPANY
CTO of ShiftLeft. Chetan is a serial entrepreneur with over 20+ years of experience in authoring and architecting mission critical software. His expertise includes building web-scale distributed infrastructure, personalization algorithms, complex event processing, fraud detection, and prevention in investment/retail banking domains. CODE PROPERTY GRAPH EXPLAINED Data Flow Tracker . The workhorse of the CPG is a state-of-the-art data-flow tracker. The data-flow tracker is interprocedural, flow-sensitive, context-sensitive, field-sensitive, and operates on an intermediate code representation (see semantic code property graphs).The engine performs on-the-fly points-to analysis to resolve call sites and is able to benefit from the results of constant BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.OCULAR - SHIFTLEFT
Ocular is a scala-based read-eval-print-loop (REPL) tool to traverse the graph. For example, Ocular enables you to query for all the sources and sinks of a critical data variable. It can list every transform on each route to ensure that data is always handled properly and never leaking to a logger. ANALYZING HELLOSHIFTLEFT WITH NG SAST Step 3: View Your Results#. Per the instructions printed to the Terminal/Bash, open up the URL provided. This will bring you to the ShiftLeft Dashboard, where you will ANALYZING GITHUB REPOSITORIES USING NG SAST This article will walk you through the ShiftLeft workflow by showing you how to set up automated code analysis using NextGen Static Analysis (NG SAST) for a GitHub repository.SHIFTLEFT WEBINAR
Developer-based from the start, ShiftLeft CORE enables organizations of all sizes to help create secure products. We know the difficulties of trying to integrate security into DevOps workflows and have created ShiftLeft CORE to securely write applications without disruptingcurrent processes.
SETTING UP NG SAST ONTO A LOCAL WORKSTATION Using the ShiftLeft CLI to Authenticate#. Once you have the ShiftLeft CLI installed, you need to associate the CLI with your ShiftLeft account. The ShiftLeft CLI command sl auth is used to authenticate with ShiftLeft and associate your applications with your organization. MITIGATING NOSQL INJECTION ATTACKS: PART 2 Mitigating NoSQL Injection Attacks: Part 2. This is the second part of a two-part series on NoSQL injections. Last time, we covered the anatomy of a NoSQL injection, as well as how to mitigate it. In this post, we will look at specific injection attack types, INSERTING SECURITY IN GITHUB PULL REQUESTS! This post builds up in a previous post about inserting code analysis into GitHub pull requests, in this post, we will focus on implementing this workflow based on GitHub Actions for a SHIFTLEFTGET STARTEDTERMS OF SERVICEWHITEPAPERSWATCH WEBINARCOMPANY Contextual Security Education. Finding bugs isn’t the hard part, it’s fixing them. ShiftLeft Educate is an optional add-on that embeds security training directly into ShiftLeft CORE allowing developers to learn in real-time how to fix issues without having to switch context. Learn More.COMPANY
CTO of ShiftLeft. Chetan is a serial entrepreneur with over 20+ years of experience in authoring and architecting mission critical software. His expertise includes building web-scale distributed infrastructure, personalization algorithms, complex event processing, fraud detection, and prevention in investment/retail banking domains. INTELLIGENT SOFTWARE COMPOSITION ANALYSIS Intelligent SCA Reduces Your OSS Vulnerability Tickets by 90%. ShiftLeft’s Intelligent SCA uses the full power of Code Property Graph to analyze both custom and open-source vulnerabilities and introduces the concept of “Attacker Reachability” to prioritize only a subset of vulnerabilities for mitigation.OCULAR - SHIFTLEFT
Ocular is a scala-based read-eval-print-loop (REPL) tool to traverse the graph. For example, Ocular enables you to query for all the sources and sinks of a critical data variable. It can list every transform on each route to ensure that data is always handled properly and never leaking to a logger. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databasesC# | SHIFTLEFT DOCS
ShiftLeft offers a sample application that you can use to run and test NG SAST. It also includes a functioning configuration file to demonstrate how you can leverage Azure Pipelines or GitHub Actions to automate code analysis whenever you open a new Pull Request (PR). To HOW TO DETECT 0-DAY VULNERABILITIES How to Detect 0-day Vulnerabilities. A 0-day vulnerability is unknown to, or unaddressed by, developers and security researchers and is considered a severe threat. Until an 0-day vulnerability is identified and mitigated, hackers can exploit it. This use case is based on CVE-2018-19859, a vulnerability allowing an attacker to executearbitrary
JAVA | SHIFTLEFT DOCS Requirements#. NG SAST supports the analysis of applications written in Java 7 through Java 11. We offer partial support for apps written in Java 14 and 15 (please reach out to ShiftLeft for additional details). Your build environment must have at least 16 GB of memory available. NG SAST utilizes Java SE Runtime Environment 8; ifnecessary, you
FORRESTER: THE STATE OF APPLICATION SECURITY Download Forrester's The State of Application Security report. SHIFTLEFTGET STARTEDTERMS OF SERVICEWHITEPAPERSWATCH WEBINARCOMPANY Contextual Security Education. Finding bugs isn’t the hard part, it’s fixing them. ShiftLeft Educate is an optional add-on that embeds security training directly into ShiftLeft CORE allowing developers to learn in real-time how to fix issues without having to switch context. Learn More.COMPANY
CTO of ShiftLeft. Chetan is a serial entrepreneur with over 20+ years of experience in authoring and architecting mission critical software. His expertise includes building web-scale distributed infrastructure, personalization algorithms, complex event processing, fraud detection, and prevention in investment/retail banking domains. INTELLIGENT SOFTWARE COMPOSITION ANALYSIS Intelligent SCA Reduces Your OSS Vulnerability Tickets by 90%. ShiftLeft’s Intelligent SCA uses the full power of Code Property Graph to analyze both custom and open-source vulnerabilities and introduces the concept of “Attacker Reachability” to prioritize only a subset of vulnerabilities for mitigation.OCULAR - SHIFTLEFT
Ocular is a scala-based read-eval-print-loop (REPL) tool to traverse the graph. For example, Ocular enables you to query for all the sources and sinks of a critical data variable. It can list every transform on each route to ensure that data is always handled properly and never leaking to a logger. BUSINESS LOGIC FLAWS Business Logic Flaws Require a New Approach. Traditional static application security testing (SAST) cannot detect business logic flaws because it does not understand the unique aspects of your code, such as business domain workflow, logic of the programmer, and the ways in which the business logic can be tampered with or bypassed.CODE PROPERTY GRAPH
The Code Property Graph is a data structure designed to mine large codebases for instances of programming patterns. These patterns are formulated in a domain-specific language (DSL) based on Scala.It serves as a single intermediate program representation across all languages supported by Ocular. Property graphs are a generic abstraction supported by many contemporary graph databasesC# | SHIFTLEFT DOCS
ShiftLeft offers a sample application that you can use to run and test NG SAST. It also includes a functioning configuration file to demonstrate how you can leverage Azure Pipelines or GitHub Actions to automate code analysis whenever you open a new Pull Request (PR). To HOW TO DETECT 0-DAY VULNERABILITIES How to Detect 0-day Vulnerabilities. A 0-day vulnerability is unknown to, or unaddressed by, developers and security researchers and is considered a severe threat. Until an 0-day vulnerability is identified and mitigated, hackers can exploit it. This use case is based on CVE-2018-19859, a vulnerability allowing an attacker to executearbitrary
JAVA | SHIFTLEFT DOCS Requirements#. NG SAST supports the analysis of applications written in Java 7 through Java 11. We offer partial support for apps written in Java 14 and 15 (please reach out to ShiftLeft for additional details). Your build environment must have at least 16 GB of memory available. NG SAST utilizes Java SE Runtime Environment 8; ifnecessary, you
FORRESTER: THE STATE OF APPLICATION SECURITY Download Forrester's The State of Application Security report.COMPANY
CTO of ShiftLeft. Chetan is a serial entrepreneur with over 20+ years of experience in authoring and architecting mission critical software. His expertise includes building web-scale distributed infrastructure, personalization algorithms, complex event processing, fraud detection, and prevention in investment/retail banking domains.SHIFTLEFT
ShiftLeft. Sign In. ShiftLeft CORE is the Modern Code Security Platform Loved by Developers:SHIFTLEFT
ShiftLeft
OCULAR - SHIFTLEFT
Ocular is a scala-based read-eval-print-loop (REPL) tool to traverse the graph. For example, Ocular enables you to query for all the sources and sinks of a critical data variable. It can list every transform on each route to ensure that data is always handled properly and never leaking to a logger. SCALA | SHIFTLEFT DOCS The ShiftLeft Dashboard's findings list can include URLs that, when used, will direct you to the specific source code lines where the vulnerability occurs. However, to leverage ShiftLeft's source code view with Scala applications, you must augment the source code filepaths. NG SAST uses the byte code, not the source code, foranalysis, so you
ANALYZING HELLOSHIFTLEFT WITH NG SAST Step 3: View Your Results#. Per the instructions printed to the Terminal/Bash, open up the URL provided. This will bring you to the ShiftLeft Dashboard, where you will ANALYZING GITHUB REPOSITORIES USING NG SAST This article will walk you through the ShiftLeft workflow by showing you how to set up automated code analysis using NextGen Static Analysis (NG SAST) for a GitHub repository. SETTING UP NG SAST ONTO A LOCAL WORKSTATION Using the ShiftLeft CLI to Authenticate#. Once you have the ShiftLeft CLI installed, you need to associate the CLI with your ShiftLeft account. The ShiftLeft CLI command sl auth is used to authenticate with ShiftLeft and associate your applications with your organization. JAVA | SHIFTLEFT DOCS Requirements#. NG SAST supports the analysis of applications written in Java 7 through Java 11. We offer partial support for apps written in Java 14 and 15 (please reach out to ShiftLeft for additional details). Your build environment must have at least 16 GB of memory available. NG SAST utilizes Java SE Runtime Environment 8; ifnecessary, you
DEV + SEC + OPS ! = DEVSECOPS. SECURITY VENDORS AND CODE Ops problem — meme. Security: If this person does their job well, then the developer, ops, and the business would wrongly tag them as the only person in the team who always delays or blocks the delivery or the release.People are never fans of testing especially testing that takes time and resources. Over time, this person would be so detached that they would either stop contributing ideas or* Login
* Docs
* Request Demo
* Why ShiftLeft __
* How It Works
* Code Property Graph Explained* Use Cases __
* Operational Speed
* Business Logic Flaws * Developer Friendly Security Workflows* Platform __
* ShiftLeft CORE
* Intelligent Software Composition Analysis * Developer Security Education* Ocular
* Resources __
* Blog
* Webinars
* Whitepapers
* Datasheets and Case Studies * Open Source Resources * Free Security Training* Company __
* About ShiftLeft
* News
* Press Release
* Careers
* Contact
* Free Account
ShiftLeft CORE turns developers into security heroes A CODE SECURITY PLATFORM DEVELOPERS LOVE Next-gen SAST, secrets detection, Intelligent SCA, and security training all wrapped up in one platform.* FREE ACCOUNT
* LEARN MORE
TRUSTED BY
SHIFTLEFT CORE:
THE CODE SECURITY PLATFORM FOR MODERN DEV TEAMS LIGHTNING FAST CODE ANALYSIS With our unique Code Property Graph engine, ShiftLeft CORE’s SAST capabilities enables up to 40x faster scan times. Stop waiting forresults!
Learn More
PROVABLE ACCURACY
With an above 74% average OWASP Benchmark score, ShiftLeft CORE’s SAST capabilities gives you the most accurate findings possible. Oh, and we include an easy to use benchmarking tool in our platform.TEST OUR CLAIM
DEV-FRIENDLY WORKFLOWS Find fast, fix faster. With a 5x decrease in Mean-Time-To-Remediation (MTTR), you can focus on fixing security vulnerabilities in your existing workflows instead of continual context switching.Learn More
INTELLIGENT SCA
Software Composition Analysis (SCA) is a crucial part of any organization’s DevSecOps practice but can you separate the signal from the noise? Intelligent SCA reduces the amount of tickets by over 90% in our real-world tests by focusing only on vulnerabilities reachable by an attacker.Learn More
CONTEXTUAL SECURITY EDUCATION Finding bugs isn’t the hard part, it’s fixing them. ShiftLeft Educate is an optional add-on that embeds security training directly into ShiftLeft CORE allowing developers to learn in real-time how to fix issues without having to switch context.Learn More
AUTOMATICALLY FIND BUSINESS LOGIC FLAWS IN DEV Identify vulnerabilities that are unique to your code base before theyreach production.
Hardcoded Secrets
Data Leakage
Auth Bypass
Rootkits
Backdoors
Logic Bombs
Learn More
GET COMPLIANT. STAY COMPLIANT. Demonstrate and maintain compliance with security and privacy regulations such as SOC 2, PCI-DSS, GDPR, and CCPA.Watch Webinar
RESOURCES
ON-DEMAND WEBINAR
SolarWinds Live Analysis with ShiftLeftWatch Now __
__
WHITEPAPER
Why ShiftLeft is the most accurate code analysisRead More __
WHITEPAPER
Modeling and Discovering Vulnerabilities with Code Property GraphsGet Started __
OUR INTEGRATIONS
All the integrations you need to efficiently find, prioritize, and remediate vulnerabilities.SEE HOW IT WORKS
Learn how you can identify and fix vulnerabilities in 4 easy steps.Learn More
WHY SHIFTLEFT
* How It Works
* Code Property Graph Explained* Use Cases
* Operational Speed
* Business Logic Flaws * Developer Friendly Security WorkflowsPLATFORM
* ShiftLeft CORE
* Intelligent Software Composition Analysis * Developer Security Education* Ocular
RESOURCES
* Blog
* Webinars
* Whitepapers
* Datasheets and Case Studies * Open Source ResourcesCOMPANY
* About ShiftLeft
* News
* Press Release
* Careers
* Contact
* Status
* Privacy & Security* Terms of Use
* Ocular Terms
* __
* __
* __
� 2017-2021 Shiftleft.io. All Rights Reserved×
×
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0