Are you over 18 and want to see adult content?
More Annotations

TIP.ba | Internet Vijesnik – TIP – Najnovije vijesti TK, BiH, Regija i Svijet
Are you over 18 and want to see adult content?
A complete backup of parkett-pflegemittel.de
Are you over 18 and want to see adult content?
Профессиональный синонимайзер онлайн, повышение уникальности текста, повысить антиплагиат
Are you over 18 and want to see adult content?

A complete backup of sek-aun.blogspot.com
Are you over 18 and want to see adult content?

Online radio stations from Ghana, listen live radio
Are you over 18 and want to see adult content?

Pacific Northwest Tourist | Things to do and places to go in the Great Pacific Northwest.
Are you over 18 and want to see adult content?

Web Design Company Dubai | Websites Designers and Developers Abu Dhabi / Dubai / Sharjah
Are you over 18 and want to see adult content?
centralhypnotherapy.com | 525: SSL handshake failed
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://spiritofburgas.com
Are you over 18 and want to see adult content?

A complete backup of https://brundage.com
Are you over 18 and want to see adult content?
A complete backup of https://tovertsololanon.tk
Are you over 18 and want to see adult content?

A complete backup of https://landiown.com
Are you over 18 and want to see adult content?

A complete backup of https://worldmapblank.com
Are you over 18 and want to see adult content?
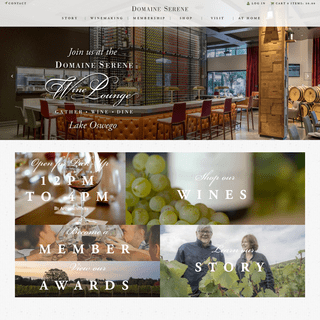
A complete backup of https://domaineserene.com
Are you over 18 and want to see adult content?

A complete backup of https://bio-pack.ru
Are you over 18 and want to see adult content?

A complete backup of https://fodesep.gov.co
Are you over 18 and want to see adult content?

A complete backup of https://aberseo.com
Are you over 18 and want to see adult content?

A complete backup of https://museoestebanvicente.es
Are you over 18 and want to see adult content?

A complete backup of https://goodhabitz.com
Are you over 18 and want to see adult content?

A complete backup of https://denverboyscouts.org
Are you over 18 and want to see adult content?
Text
software
GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
STORING CURRENCY IN POSTGRESQL WHAT IS AN ABUSER STORY (SOFTWARE) RIETTA.COM APPLICATION SECURITY & DEVELOPMENT Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
STORING CURRENCY IN POSTGRESQL WHAT IS AN ABUSER STORY (SOFTWARE) RIETTA.COM APPLICATION SECURITY & DEVELOPMENT Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
ABOUT RIETTA.COM
Mission Statement Our mission is to enable client investment into a stable foundation for their business critical applications. This is enabled by a balanced focus on people, processes, and technology. While good application security involves technology, it requires people to be educated and empowered first. We advocate that clients eschew short term thinking and instead invest with a long RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. CROSS-SITE SCRIPTING INJECTION ATTACKS USING SVG IMAGES Cross-Site Scripting attacks can come from a variety of vectors, this article is an explaination of an unusual vector where javascript is embedded within a scalable vector graphics image. TESTING: YOUR FUTURE SELF WILL THANK YOU Testing: Your Future Self Will Thank You. Wren Steitle — 2021-04-27. Testing isn’t always a glamorous endeavor. It’s akin to confirming someone else’s scientific results: needed, and not noteworthy. But I would argue that in fact, testing can be as important as the code we write. Testing serves as a great way to get a good view of the HOW TO SET UP AND ENCRYPT AN EXTERNAL SSD AND RUN DOCKER Docker is a powerful tool for developing, shipping, and running applications. It allows us to encapsulate our applications into containers, which then gives us the ability to run entire applications without the hassle of setting up our local machines with custom libraries and dependencies for WHAT IS AN ABUSER STORY (SOFTWARE) In software development and product management, an abuser story is a user story from the point of view of a malicious adversary. Abuser stories are used with agile software development methodologies as the basis for defining the activities that should be actively blocked or mitigated by the software and proven by automated regression testing. HOW TO CALCULATE AGE IN MYSQL While PostgreSQL has a built in age() command, MySQL does not. Imagine we have a users table with a birthdate field and we need to figure out how old they are. We could accomplish this by subtracting the current date with the date the user was born on. RESET MYSQL ROOT PASSWORD WITH ONE COMMAND Fortunately, I had administrative access to the server through SSH and thus was able to reset the MySQL root password with the package management script. It only took one, simple command. sudo dpkg-reconfigure mysql-server-5.5. After entering my system password for sudo, I was prompted for the password I wanted to use for MySQL. INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
USING IPTABLES TO REQUIRE CLOUDFLARE FOR ALL HTTP/HTTPS For some of our clients, Rietta uses CloudFlare.com for its web application firewall and content distribution network (CDN) services. CloudFlare is installed on a domain by changing the domain’s DNS servers to resolve to CloudFlare, which then proceeds to serve as a proxy between the web and the web server running the protected application. Once this is setup it is expected that all general WHAT IS AN ABUSER STORY (SOFTWARE) INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
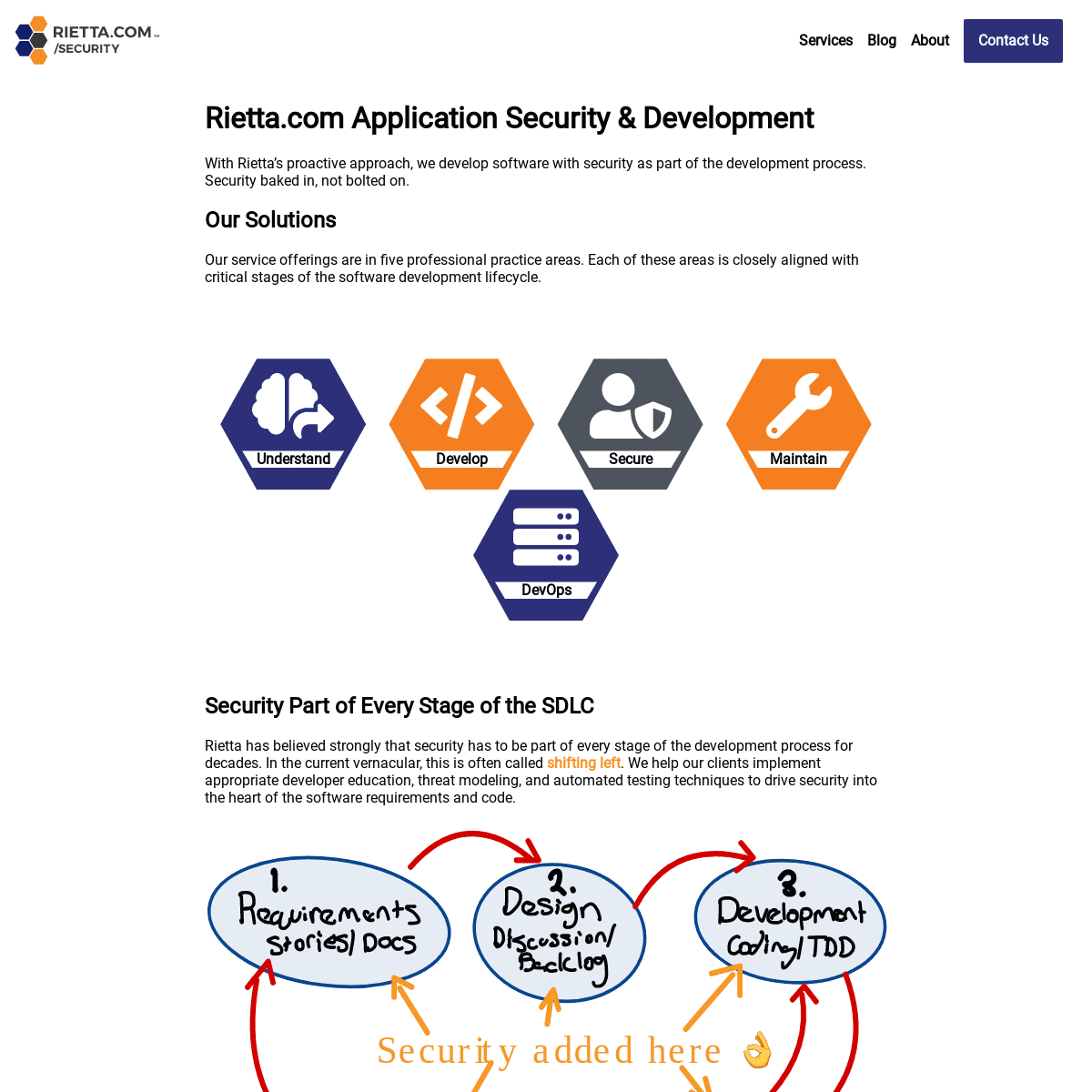
USING IPTABLES TO REQUIRE CLOUDFLARE FOR ALL HTTP/HTTPS For some of our clients, Rietta uses CloudFlare.com for its web application firewall and content distribution network (CDN) services. CloudFlare is installed on a domain by changing the domain’s DNS servers to resolve to CloudFlare, which then proceeds to serve as a proxy between the web and the web server running the protected application. Once this is setup it is expected that all general WHAT IS AN ABUSER STORY (SOFTWARE) RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our HOW TO SET UP AND ENCRYPT AN EXTERNAL SSD AND RUN DOCKER Docker is a powerful tool for developing, shipping, and running applications. It allows us to encapsulate our applications into containers, which then gives us the ability to run entire applications without the hassle of setting up our local machines with custom libraries and dependencies for WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS? GitHub provides three options when merging in commits, these three options being: Create a Merge Commit. Squash and Merge. Rebase and Merge Merging with a merge commit, squash merging, and “Rebase & Merge” should be pretty familiar as these are commands that are already commonly used when working on dev branches to keep commits onPRs tidy.
WHAT IS AN ABUSER STORY (SOFTWARE) In software development and product management, an abuser story is a user story from the point of view of a malicious adversary. Abuser stories are used with agile software development methodologies as the basis for defining the activities that should be actively blocked or mitigated by the software and proven by automated regression testing. COMMERCIAL INFORMATION SECURITY CLASSIFICATION SYSTEM When you read books on security, at some point the importance of classified information systems is covered. These typically look at Mandatory Access Control in the context of military classifications, such as top secret, secret, for official use only, and sensitive but unclassified. While the existence of commercial classification systems in use outside of a government context may be USING IPTABLES TO REQUIRE CLOUDFLARE FOR ALL HTTP/HTTPS For some of our clients, Rietta uses CloudFlare.com for its web application firewall and content distribution network (CDN) services. CloudFlare is installed on a domain by changing the domain’s DNS servers to resolve to CloudFlare, which then proceeds to serve as a proxy between the web and the web server running the protected application. Once this is setup it is expected that all general RAILS: TYPEERROR: NIL CAN'T BE COERCED INTO FLOAT A few observations: This is correct behavior because Ruby as a language cannot assume that a nil object is equivalent to 0. It will not automatically convert the value to 0 for the purposes of completing the computation. nil implements to_f, which returns 0.0 as a float. nil implements to_i, which returns 0 as an integer.SWAP FILES AND AWS
For research projects and other non-critical applications hosted on AWS, staying within the free tier of AWS services can be a challange. Adding a swapfile can be a way to mitigate memory issues while not needing to upgrade to a larger EC2 instance. IS THE COLEMAK OR DVORAK KEYBOARD LAYOUT BEST FOR YOU? The steps to add the alternate keyboard layouts to your Android phone are: With English selected as the language, choose Dvorak (or Colemak) as the layout and tap the Add button. Go back to the main menu of the Google Keyboard and tap Input languages (its the first on the list) Uncheck the Use system language (default) and check the the RESET MYSQL ROOT PASSWORD WITH ONE COMMAND Fortunately, I had administrative access to the server through SSH and thus was able to reset the MySQL root password with the package management script. It only took one, simple command. sudo dpkg-reconfigure mysql-server-5.5. After entering my system password for sudo, I was prompted for the password I wanted to use for MySQL. RIETTA.COM APPLICATION SECURITY & DEVELOPMENT Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
HOW TO SET UP AND ENCRYPT AN EXTERNAL SSD AND RUN DOCKERSEE MORE ONRIETTA.COM
MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
RESTRICT WHO CAN PUSH TO MATCHING BRANCHES ON GITHUBSEE MORE ONRIETTA.COM
RIETTA.COM APPLICATION SECURITY & DEVELOPMENT Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
HOW TO SET UP AND ENCRYPT AN EXTERNAL SSD AND RUN DOCKERSEE MORE ONRIETTA.COM
MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
RESTRICT WHO CAN PUSH TO MATCHING BRANCHES ON GITHUBSEE MORE ONRIETTA.COM
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to ourABOUT RIETTA.COM
Mission Statement Our mission is to enable client investment into a stable foundation for their business critical applications. This is enabled by a balanced focus on people, processes, and technology. While good application security involves technology, it requires people to be educated and empowered first. We advocate that clients eschew short term thinking and instead invest with a long HOW TO SET UP AND ENCRYPT AN EXTERNAL SSD AND RUN DOCKER Docker is a powerful tool for developing, shipping, and running applications. It allows us to encapsulate our applications into containers, which then gives us the ability to run entire applications without the hassle of setting up our local machines with custom libraries and dependencies for REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. COMMERCIAL INFORMATION SECURITY CLASSIFICATION SYSTEM When you read books on security, at some point the importance of classified information systems is covered. These typically look at Mandatory Access Control in the context of military classifications, such as top secret, secret, for official use only, and sensitive but unclassified. While the existence of commercial classification systems in use outside of a government context may be WHAT IS AN ABUSER STORY (SOFTWARE) In software development and product management, an abuser story is a user story from the point of view of a malicious adversary. Abuser stories are used with agile software development methodologies as the basis for defining the activities that should be actively blocked or mitigated by the software and proven by automated regression testing. USING IPTABLES TO REQUIRE CLOUDFLARE FOR ALL HTTP/HTTPS For some of our clients, Rietta uses CloudFlare.com for its web application firewall and content distribution network (CDN) services. CloudFlare is installed on a domain by changing the domain’s DNS servers to resolve to CloudFlare, which then proceeds to serve as a proxy between the web and the web server running the protected application. Once this is setup it is expected that all general IS THE COLEMAK OR DVORAK KEYBOARD LAYOUT BEST FOR YOU? The steps to add the alternate keyboard layouts to your Android phone are: With English selected as the language, choose Dvorak (or Colemak) as the layout and tap the Add button. Go back to the main menu of the Google Keyboard and tap Input languages (its the first on the list) Uncheck the Use system language (default) and check the the RESET MYSQL ROOT PASSWORD WITH ONE COMMAND Fortunately, I had administrative access to the server through SSH and thus was able to reset the MySQL root password with the package management script. It only took one, simple command. sudo dpkg-reconfigure mysql-server-5.5. After entering my system password for sudo, I was prompted for the password I wanted to use for MySQL. RIETTA.COM APPLICATION SECURITY & DEVELOPMENT Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
RESTRICT WHO CAN PUSH TO MATCHING BRANCHES ON GITHUBSEE MORE ONRIETTA.COM
WHAT IS AN ABUSER STORY (SOFTWARE) RIETTA.COM APPLICATION SECURITY & DEVELOPMENT Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
RESTRICT WHO CAN PUSH TO MATCHING BRANCHES ON GITHUBSEE MORE ONRIETTA.COM
WHAT IS AN ABUSER STORY (SOFTWARE) RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to ourABOUT RIETTA.COM
Mission Statement Our mission is to enable client investment into a stable foundation for their business critical applications. This is enabled by a balanced focus on people, processes, and technology. While good application security involves technology, it requires people to be educated and empowered first. We advocate that clients eschew short term thinking and instead invest with a long LAVA LAMPS PROVIDING RANDOMNESS FOR SECURITY! Lava lamps providing randomness for security! Frank Rietta — 2021-05-11. Clients and new co-workers often ask me about my lava lamp that I keep in my home office in view of the web cam. Besides being cool, I do this intentionally to celebrate the lava lamp’s role in keeping the Internet secure! According to Wikipedia, “Lavarand was a HOW TO SET UP AND ENCRYPT AN EXTERNAL SSD AND RUN DOCKER Docker is a powerful tool for developing, shipping, and running applications. It allows us to encapsulate our applications into containers, which then gives us the ability to run entire applications without the hassle of setting up our local machines with custom libraries and dependencies for REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. COMMERCIAL INFORMATION SECURITY CLASSIFICATION SYSTEM When you read books on security, at some point the importance of classified information systems is covered. These typically look at Mandatory Access Control in the context of military classifications, such as top secret, secret, for official use only, and sensitive but unclassified. While the existence of commercial classification systems in use outside of a government context may be WHAT IS AN ABUSER STORY (SOFTWARE) In software development and product management, an abuser story is a user story from the point of view of a malicious adversary. Abuser stories are used with agile software development methodologies as the basis for defining the activities that should be actively blocked or mitigated by the software and proven by automated regression testing. IS THE COLEMAK OR DVORAK KEYBOARD LAYOUT BEST FOR YOU? The steps to add the alternate keyboard layouts to your Android phone are: With English selected as the language, choose Dvorak (or Colemak) as the layout and tap the Add button. Go back to the main menu of the Google Keyboard and tap Input languages (its the first on the list) Uncheck the Use system language (default) and check the theSWAP FILES AND AWS
For research projects and other non-critical applications hosted on AWS, staying within the free tier of AWS services can be a challange. Adding a swapfile can be a way to mitigate memory issues while not needing to upgrade to a larger EC2 instance. INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
USING IPTABLES TO REQUIRE CLOUDFLARE FOR ALL HTTP/HTTPS For some of our clients, Rietta uses CloudFlare.com for its web application firewall and content distribution network (CDN) services. CloudFlare is installed on a domain by changing the domain’s DNS servers to resolve to CloudFlare, which then proceeds to serve as a proxy between the web and the web server running the protected application. Once this is setup it is expected that all general WHAT IS AN ABUSER STORY (SOFTWARE) INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A MANUALLY EDITING GIT HUNKS: THE EASY WAY 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
USING IPTABLES TO REQUIRE CLOUDFLARE FOR ALL HTTP/HTTPS For some of our clients, Rietta uses CloudFlare.com for its web application firewall and content distribution network (CDN) services. CloudFlare is installed on a domain by changing the domain’s DNS servers to resolve to CloudFlare, which then proceeds to serve as a proxy between the web and the web server running the protected application. Once this is setup it is expected that all general WHAT IS AN ABUSER STORY (SOFTWARE) RIETTA.COM APPLICATION SECURITY & DEVELOPMENT Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. LAVA LAMPS PROVIDING RANDOMNESS FOR SECURITY! Lava lamps providing randomness for security! Frank Rietta — 2021-05-11. Clients and new co-workers often ask me about my lava lamp that I keep in my home office in view of the web cam. Besides being cool, I do this intentionally to celebrate the lava lamp’s role in keeping the Internet secure! According to Wikipedia, “Lavarand was a WHAT IS AN ABUSER STORY (SOFTWARE) In software development and product management, an abuser story is a user story from the point of view of a malicious adversary. Abuser stories are used with agile software development methodologies as the basis for defining the activities that should be actively blocked or mitigated by the software and proven by automated regression testing. HOW TO SET UP AND ENCRYPT AN EXTERNAL SSD AND RUN DOCKER Docker is a powerful tool for developing, shipping, and running applications. It allows us to encapsulate our applications into containers, which then gives us the ability to run entire applications without the hassle of setting up our local machines with custom libraries and dependencies for WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS? GitHub provides three options when merging in commits, these three options being: Create a Merge Commit. Squash and Merge. Rebase and Merge Merging with a merge commit, squash merging, and “Rebase & Merge” should be pretty familiar as these are commands that are already commonly used when working on dev branches to keep commits onPRs tidy.
RAILS: TYPEERROR: NIL CAN'T BE COERCED INTO FLOAT A few observations: This is correct behavior because Ruby as a language cannot assume that a nil object is equivalent to 0. It will not automatically convert the value to 0 for the purposes of completing the computation. nil implements to_f, which returns 0.0 as a float. nil implements to_i, which returns 0 as an integer.SWAP FILES AND AWS
For research projects and other non-critical applications hosted on AWS, staying within the free tier of AWS services can be a challange. Adding a swapfile can be a way to mitigate memory issues while not needing to upgrade to a larger EC2 instance. IS THE COLEMAK OR DVORAK KEYBOARD LAYOUT BEST FOR YOU? The steps to add the alternate keyboard layouts to your Android phone are: With English selected as the language, choose Dvorak (or Colemak) as the layout and tap the Add button. Go back to the main menu of the Google Keyboard and tap Input languages (its the first on the list) Uncheck the Use system language (default) and check the the RIETTA.COM APPLICATION SECURITY & DEVELOPMENTRIETTA FLEA MARKET FACEBOOKRIETTA RANCH FLEARIETTA WALLENDA 1963 DEATHRIETTA WALLENDA DEATHRIETTA FLEA MARKET HUBBARDSTONRIETTA RANCH HUBBARDSTON Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. MANUALLY EDITING GIT HUNKS: THE EASY WAYGIT CREATE PATCH FROM LAST COMMITGIT DIFF PATCHGIT GENERATE PATCH FOR LATEST COMMITGIT PATCH APPLY TO FILEGIT PATCH FORMAT DETECTION FAILEDGIT PATCH P1 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256?IS SHA256 SAFE TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
RIETTA.COM APPLICATION SECURITY & DEVELOPMENTRIETTA FLEA MARKET FACEBOOKRIETTA RANCH FLEARIETTA WALLENDA 1963 DEATHRIETTA WALLENDA DEATHRIETTA FLEA MARKET HUBBARDSTONRIETTA RANCH HUBBARDSTON Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. MANUALLY EDITING GIT HUNKS: THE EASY WAYGIT CREATE PATCH FROM LAST COMMITGIT DIFF PATCHGIT GENERATE PATCH FOR LATEST COMMITGIT PATCH APPLY TO FILEGIT PATCH FORMAT DETECTION FAILEDGIT PATCH P1 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256?IS SHA256 SAFE TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
RIETTA.COM APPLICATION SECURITY & DEVELOPMENT Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our CONTACT US – RIETTA Call Rietta at +1 770-623-2059. Office hours are Monday - Friday,9:00am - 5:00pm EST
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using ADEVOPS – RIETTA
One thing it isn’t, is one size fits all. Our team of experienced architects and developers can help you define what DevOps should mean for your organization or environment. From test driven development to rapid and automated delivery tools, getting from design to done can be faster than ever with the right processes, tools and team. HOW TO SET UP AND ENCRYPT AN EXTERNAL SSD AND RUN DOCKER Docker is a powerful tool for developing, shipping, and running applications. It allows us to encapsulate our applications into containers, which then gives us the ability to run entire applications without the hassle of setting up our local machines with custom libraries and dependencies for RESTRICT WHO CAN PUSH TO MATCHING BRANCHES ON GITHUB Restrict Who Can Push to Matching Branches on Github. Frank Rietta — 2019-05-09 (Last Updated: 2019-10-23 ) An anonymous attacker has been compromising Git repositories and demanding ransom. This attacker stole the contents and used a force push to wipe the remote repository causing many to lose access to their critical source code assets.SWAP FILES AND AWS
For research projects and other non-critical applications hosted on AWS, staying within the free tier of AWS services can be a challange. Adding a swapfile can be a way to mitigate memory issues while not needing to upgrade to a larger EC2 instance. WHAT IS AN ABUSER STORY (SOFTWARE) In software development and product management, an abuser story is a user story from the point of view of a malicious adversary. Abuser stories are used with agile software development methodologies as the basis for defining the activities that should be actively blocked or mitigated by the software and proven by automated regression testing. USING IPTABLES TO REQUIRE CLOUDFLARE FOR ALL HTTP/HTTPS For some of our clients, Rietta uses CloudFlare.com for its web application firewall and content distribution network (CDN) services. CloudFlare is installed on a domain by changing the domain’s DNS servers to resolve to CloudFlare, which then proceeds to serve as a proxy between the web and the web server running the protected application. Once this is setup it is expected that all general RIETTA.COM APPLICATION SECURITY & DEVELOPMENTRIETTA FLEA MARKET FACEBOOKRIETTA RANCH FLEARIETTA WALLENDA 1963 DEATHRIETTA WALLENDA DEATHRIETTA FLEA MARKET HUBBARDSTONRIETTA RANCH HUBBARDSTON Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. MANUALLY EDITING GIT HUNKS: THE EASY WAYGIT CREATE PATCH FROM LAST COMMITGIT DIFF PATCHGIT GENERATE PATCH FOR LATEST COMMITGIT PATCH APPLY TO FILEGIT PATCH FORMAT DETECTION FAILEDGIT PATCH P1 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256?IS SHA256 SAFE TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
RIETTA.COM APPLICATION SECURITY & DEVELOPMENTRIETTA FLEA MARKET FACEBOOKRIETTA RANCH FLEARIETTA WALLENDA 1963 DEATHRIETTA WALLENDA DEATHRIETTA FLEA MARKET HUBBARDSTONRIETTA RANCH HUBBARDSTON Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our INTRODUCTION TO OPENPGP: DECRYPT THIS MESSAGESEE MORE ON RIETTA.COM GENERATE OPENSSL RSA KEY PAIR FROM THE COMMAND LINE While Encrypting a File with a Password from the Command Line using OpenSSL is very useful in its own right, the real power of the OpenSSL library is its ability to support the use of public key cryptograph for encrypting or validating data in an unattended manner (where the password is not required to encrypt) is done with public keys.. TheCommands to Run
BEST DATA TYPE TO STORE MONEY IN MYSQL? The DECIMAL and NUMERIC types store exact numeric data values. These types are used when it is important to preserve exact precision, for example with monetary data. In MySQL, NUMERIC is implemented as DECIMAL, so the following remarks about DECIMAL apply equally to NUMERIC. The DECIMAL data type allows you to specify the total numberof digits
GET THE CURRENT YEAR IN THE RUBY PROGRAMMING LANGUAGE The fastest methods are bolded. Time.new.year seems to be a good balance on performance if you are using either the latest MRI, Ruby 2.2 or JRuby at the time of this writing.. Further reading. I hope this helps you learn a little bit more about Ruby. It really is one of the best, most fun programming languages to work in. MANUALLY EDITING GIT HUNKS: THE EASY WAYGIT CREATE PATCH FROM LAST COMMITGIT DIFF PATCHGIT GENERATE PATCH FOR LATEST COMMITGIT PATCH APPLY TO FILEGIT PATCH FORMAT DETECTION FAILEDGIT PATCH P1 1 # Manual hunk edit mode -- see bottom for a quick guide. 2 class User < ApplicationRecord 3 + 4 + def method_a 5 + puts "bar" 6 + end 11 end 12 # --- 13 # To remove '-' lines, make them ' ' lines (context). 14 # To remove '+' lines, delete them. 15 # Lines starting with # will be removed. Once the unwanted hunks are removed, we canexit and
REALLY BAD PASSWORDS (WITH UNSALTED HASHES) The June, 2012, LinkedIn password breach reminds us all the need to protect our user’s passwords. The following table includes a series of really, really bad passwords. These are passwords that are trivially cracked using an automated tool, such as John the Ripper, or have been found through public password hacks as being in use by real people. This is a simple rainbow table because it lists WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256?IS SHA256 SAFE TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using A WHAT'S THE DIFFERENCE BETWEEN THE 3 GITHUB MERGE METHODS?SEE MORE ONRIETTA.COM
RIETTA.COM APPLICATION SECURITY & DEVELOPMENT Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called shifting left. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of thesoftware
RIETTA'S APP SECURITY SERVICES Our mission is to provide you with a stable foundation for your secure operations, Rietta’s services are built around the Secure Software Development Lifecycle (SSDLC). Our service offerings in five practice areas (each represented by a hexagon in our logo). While these areas may seem disconnected, they are all directly related to our CONTACT US – RIETTA Call Rietta at +1 770-623-2059. Office hours are Monday - Friday,9:00am - 5:00pm EST
WHAT IS THE DIFFERENCE BETWEEN BCRYPT AND SHA256? TL;DR; SHA1, SHA256, and SHA512 are all fast hashes and are bad for passwords. SCRYPT and BCRYPT are both a slow hash and are good for passwords. Always use slow hashes, never fast hashes. SANS’ Securing Web Application Technologies Checklist is offering a bit of bad security advice for the everyday web application developer, under the heading “Store User Passwords Using ADEVOPS – RIETTA
One thing it isn’t, is one size fits all. Our team of experienced architects and developers can help you define what DevOps should mean for your organization or environment. From test driven development to rapid and automated delivery tools, getting from design to done can be faster than ever with the right processes, tools and team. HOW TO SET UP AND ENCRYPT AN EXTERNAL SSD AND RUN DOCKER Docker is a powerful tool for developing, shipping, and running applications. It allows us to encapsulate our applications into containers, which then gives us the ability to run entire applications without the hassle of setting up our local machines with custom libraries and dependencies for RESTRICT WHO CAN PUSH TO MATCHING BRANCHES ON GITHUB Restrict Who Can Push to Matching Branches on Github. Frank Rietta — 2019-05-09 (Last Updated: 2019-10-23 ) An anonymous attacker has been compromising Git repositories and demanding ransom. This attacker stole the contents and used a force push to wipe the remote repository causing many to lose access to their critical source code assets.SWAP FILES AND AWS
For research projects and other non-critical applications hosted on AWS, staying within the free tier of AWS services can be a challange. Adding a swapfile can be a way to mitigate memory issues while not needing to upgrade to a larger EC2 instance. WHAT IS AN ABUSER STORY (SOFTWARE) In software development and product management, an abuser story is a user story from the point of view of a malicious adversary. Abuser stories are used with agile software development methodologies as the basis for defining the activities that should be actively blocked or mitigated by the software and proven by automated regression testing. USING IPTABLES TO REQUIRE CLOUDFLARE FOR ALL HTTP/HTTPS For some of our clients, Rietta uses CloudFlare.com for its web application firewall and content distribution network (CDN) services. CloudFlare is installed on a domain by changing the domain’s DNS servers to resolve to CloudFlare, which then proceeds to serve as a proxy between the web and the web server running the protected application. Once this is setup it is expected that all general Services Blog AboutContact Us
RIETTA.COM APPLICATION SECURITY & DEVELOPMENT With Rietta’s proactive approach, we develop software with security as part of the development process. Security baked in, not bolted on.OUR SOLUTIONS
Our service offerings are in five professional practice areas. Each of these areas is closely aligned with critical stages of the software development lifecycle.UNDERSTAND
DEVELOP
SECURE
DEVOPS
MAINTAIN
SECURITY PART OF EVERY STAGE OF THE SDLC Rietta has believed strongly that security has to be part of every stage of the development process for decades. In the current vernacular, this is often called SHIFTING LEFT. We help our clients implement appropriate developer education, threat modeling, and automated testing techniques to drive security into the heart of the software requirements and code. Also, never forget maintenance! When the development is done, the code is shipped, you have to proactively maintain your business applications or they cannot be considered secure. Our maintenance program is specifically designed for this.OUR CLIENTS
Our clients include innovated startups, IoT device manufacturers, government agencies, and established enterprises migrating workloads to the cloud. Given the sensitive nature of our work, we are bound to keep most of our client work confidential. WE’RE A REMOTE NATIVE COMPANY Rietta is not just a Cloud Native company, we’re Remote Natives. We were a 100% remote team before 2020 and will remain so long after the COVID 19 pandemic has passed into history. Remote collaboration and effective secure work from home are baked deep into our culture andbusiness processes.
RISK ASSESSMENT MINI COURSE (FREE CONTENT WITH E-MAIL) We believe so strongly in developer education, that we will give you a free copy of a 30 page Risk Assessment mini course. This material is directly out of a full day workshop that we have taught at well known Fortune 500 companies to help their development teams be more secure. If you’re interested, just contact us and we’ll send you thedocuments.
LATEST FROM THE RIETTA BLOG CROSS-SITE SCRIPTING INJECTION ATTACKS USING SVG IMAGES Cross-Site Scripting attacks can come from a variety of vectors, this article is an explaination of an unusual vector where javascript is embedded within a scalable vector graphics image. LAVA LAMPS PROVIDING RANDOMNESS FOR SECURITY! Lava Lamps as a security tool is an old idea, once covered by a patent. This is why I proudly display a Lava Lamp in my office withinmy web cam shot.
TESTING: YOUR FUTURE SELF WILL THANK YOU Testing, while not always glorious, is a vital part of a good code base. Tests and code should go hand in hand. Home Services Newsletter BlogAbout Contact Us
This website uses cookies and analytics trackers to process your information. See our Privacy Policy for details. � 1999-2021 Rietta Inc.Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0