Are you over 18 and want to see adult content?
More Annotations
A complete backup of commercialobserver.com
Are you over 18 and want to see adult content?
A complete backup of process-productions.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of teammini-max.com
Are you over 18 and want to see adult content?

A complete backup of sekolahbagiilmu.blogspot.com
Are you over 18 and want to see adult content?
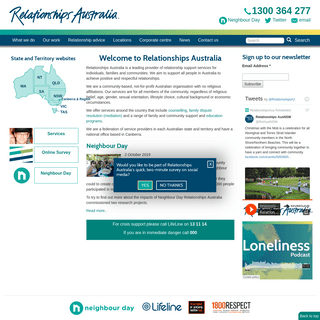
A complete backup of relationships.org.au
Are you over 18 and want to see adult content?
A complete backup of eulenpesch-liesenfeld.de
Are you over 18 and want to see adult content?

A complete backup of fewo-von-privat.de
Are you over 18 and want to see adult content?
Text
PRICING - INTEZER
Enterprise. Protected hosts. 10. Up to 50. 50 - 50K+. Detect and terminate unauthorized and malicious code. Monitor and log any new application running in your cloud environment. Quick onboarding process. Protect your cloud workloads in less than 24h. INTEZER - CVE-2021-27075: MICROSOFT AZURE VULNERABILITY As part of the responsible disclosure policy, we reported the vulnerability to Microsoft Security Response Center (MSRC). They soon patched and assigned it CVE-2021-27075 . This vulnerability would have allowed an unprivileged user to leak any Azure VM extension’s private data. Paired with the design of the VMAccess extension, anofficial
ABOUT - INTEZER
About. Intezer has created the world’s first cyber immune system against malicious code. The company detects mutations of any threat seen in history by recognizing even the slightest amount of code reuse. This technology is helping security teams protect their cloud workloads and accelerate incident response. INTEZER - ROYAL FLUSH: PRIVILEGE ESCALATION VULNERABILITY Royal Flush: Privilege Escalation Vulnerability in Azure Functions. One of the most common benefits of transitioning to cloud services is the shared responsibility for securing your assets. But cloud providers are not immune to security mistakes such as a vulnerability or misconfiguration. This is the second escalation of privileges (EoP INTEZER - 9 TOOLS TO USE RIGHT NOW TO IMPROVE AZURE Azure Defender can also be used to ensure runtime security of AKS nodes and clusters that host your containers. While there is a focus on security capabilities for Windows workloads, there are limited native options in Azure available for securing Linux against post-vulnerability exploitation and other in-memory threats. INTEZER - HABITSRAT USED TO TARGET LINUX AND WINDOWS SERVERSSEE MOREON INTEZER.COM
INTEZER - RUSSIAN APT USES COVID-19 LURES TO DELIVER ZEBROCYSEE MOREON INTEZER.COM
INTEZER - CLOUD WORKLOAD SECURITY: WHAT YOU NEED TO KNOW Cloud Workload Security: What You Need to Know - Part 1. Cloud proliferation is on the rise, and more than ever before, security teams are on the lookout for solutions that align with evolving cloud security paradigms. Given the evolving threat landscapes and more sophisticated cyber attacks being reported daily, it’s clear thatyour security
WWW.INTEZER.COM
www.intezer.com
INTEZER: RUNTIME PROTECTION FOR CLOUD WORKLOADSWHY INTEZERTECHNOLOGYPARTNERSBLOGRESOURCESGET STARTED FOR FREE Intezer is a leading provider in the incident response ‘last mile’. Most organizations have some network security or endpoint protection platform that blocks code from running in their environment; but that is where most investigations stop without a better understanding of the potential actor targeting them.PRICING - INTEZER
Enterprise. Protected hosts. 10. Up to 50. 50 - 50K+. Detect and terminate unauthorized and malicious code. Monitor and log any new application running in your cloud environment. Quick onboarding process. Protect your cloud workloads in less than 24h. INTEZER - CVE-2021-27075: MICROSOFT AZURE VULNERABILITY As part of the responsible disclosure policy, we reported the vulnerability to Microsoft Security Response Center (MSRC). They soon patched and assigned it CVE-2021-27075 . This vulnerability would have allowed an unprivileged user to leak any Azure VM extension’s private data. Paired with the design of the VMAccess extension, anofficial
ABOUT - INTEZER
About. Intezer has created the world’s first cyber immune system against malicious code. The company detects mutations of any threat seen in history by recognizing even the slightest amount of code reuse. This technology is helping security teams protect their cloud workloads and accelerate incident response. INTEZER - ROYAL FLUSH: PRIVILEGE ESCALATION VULNERABILITY Royal Flush: Privilege Escalation Vulnerability in Azure Functions. One of the most common benefits of transitioning to cloud services is the shared responsibility for securing your assets. But cloud providers are not immune to security mistakes such as a vulnerability or misconfiguration. This is the second escalation of privileges (EoP INTEZER - 9 TOOLS TO USE RIGHT NOW TO IMPROVE AZURE Azure Defender can also be used to ensure runtime security of AKS nodes and clusters that host your containers. While there is a focus on security capabilities for Windows workloads, there are limited native options in Azure available for securing Linux against post-vulnerability exploitation and other in-memory threats. INTEZER - HABITSRAT USED TO TARGET LINUX AND WINDOWS SERVERSSEE MOREON INTEZER.COM
INTEZER - RUSSIAN APT USES COVID-19 LURES TO DELIVER ZEBROCYSEE MOREON INTEZER.COM
INTEZER - CLOUD WORKLOAD SECURITY: WHAT YOU NEED TO KNOW Cloud Workload Security: What You Need to Know - Part 1. Cloud proliferation is on the rise, and more than ever before, security teams are on the lookout for solutions that align with evolving cloud security paradigms. Given the evolving threat landscapes and more sophisticated cyber attacks being reported daily, it’s clear thatyour security
WWW.INTEZER.COM
www.intezer.com
GET STARTED WITH INTEZER Malware analysis platform. Quickly analyze files and devices to immediately understand the What, Who, and How of a potential cyber incident, by identifying code reuse and similarities between software. Read more. Analyze up to 50 files every month. Get Started for Free. Premium features and plans that fit your needs. Request a Demo.BLOG - INTEZER
4. Chinese APTs Rising: Key Takeaways from the Intezer Analyze Community in May. 1) Pirpi (APT3) APT3, commonly referred to as Gothic Panda, TG-0110 and Buckeye, is a Chinese cyber espionage group Shaul Holtzman. INTEZER - TOP 10 LINUX SERVER HARDENING AND SECURITY BEST If you have servers connected to the internet, you likely have valuable data stored on them that needs to be protected from bad actors. Linux server hardening is a set of measures used to reduce the attack surface and improve the security of your servers. INTEZER - REDUCE THE ATTACK SURFACE WITH THESE UNIQUE Prioritize immediate risks in your cloud production environment. Recently added Intezer Protect features for reducing the likelihood of an attack have a unique runtime component. Here is what makes configuration checks and vulnerability assessment for installedpackages so useful.
CONTAINER SECURITY
Continuously monitors your entire stack in runtime for every code and application that is running. With so much code running in your systems, from third party libraries to proprietary software and operating system code, Intezer Protect organizes this mess giving you full runtime visibility. INTEZER - HABITSRAT USED TO TARGET LINUX AND WINDOWS SERVERS The HabitsRAT is a multi-operating system malware targeting both Windows and Linux environments. There is a lot of code reuse between the two variants. It provides the attacker with the capability to execute arbitrary code on the infected machine. To protect its C2 communication, the data is encrypted and signed using PGP. INTEZER - WHY RELYING ON THE CLOUD PROVIDER FOR SECURITY 73% of organizations using the cloud are not sure which parts of security fall under their responsibility.Ultimately, the customer is responsible for security in the cloud, meaning protecting the workloads (applications and code) hosted on top of the virtual resources created in the cloud provider’s platform.Whereas the cloud provider is responsible for the security of the cloud, meaning theYEAR OF THE GOPHER
The adoption of Go by nation state-backed threat actors hasn't been as prominent as can be seen with non-nation state-backed threat actors. It may be due to them staying with what they believe is true and tested and the advantages Go INTEZER - HIDDENWASP MALWARE STINGS TARGETED LINUX SYSTEMS Intezer has discovered a new, sophisticated malware named HiddenWasp, targeting Linux systems. Unlike common Linux malware, HiddenWasp is not focused on crypto-mining or DDoS activity, but rather it is a trojan purely used for targeted remote control.WWW.INTEZER.COM
www.intezer.com
This website stores cookies and tracking technologies. These cookies are used in order to improve your browsing experience, for analytics purposes, and to serve targeted ads. By using and accessing this site, you agree to our Terms of Use and Privacy Policy .Accept
INTEZER PROTECT COMMUNITY EDITION NOW AVAILABLE.Try it Free
Search for:
* Intezer Protect
* Intezer Analyze
* Company
* Why Intezer
* Technology
* About
* Events
* News
* Careers
* Contact Us
* Partners
* Blog
* Resources
* Docs
* Pricing
* Get Started for Free * Get Started for FreeSearch for:
MALWARE ANALYSIS PLATFORM Classify malware in seconds by recognizing even the slightest amount of code reuse. Automate end-to-end malware investigationsUSED BY
* IR/SOC Teams
* Threat Intel Teams* Government
* MSSPs
USED FOR
Malware Analysis
* Classification
* Attribution
* Reverse Engineering(IDA
+ Ghidra
)
Threat Hunting
* Proactive Hunting
* YARA rules
Incident Response
* Live Memory Analysis* Memory Dump
* Forensics
* SOAR integrations
Learn More
Get Started for Free CLOUD WORKLOAD PROTECTION PLATFORM Protect all types of compute resources. Verify your environments are running 100% trusted codeCAPABILITIES
* Real-time Threat Detection * Runtime Code Visibility & Control * Vulnerability Management* Cloud Compliance
SECURITY FOR
Linux Servers
Kubernetes
Containers
AWS
Google Cloud
Azure
Learn More
Get Started for Free RUNTIME PROTECTION FOR YOUR CLOUD WORKLOADS PROVEN LINUX THREAT DETECTION WITH NO MANUAL POLICIES OR OVERHEAD FORYOUR TEAM
Get Started for FreeLearn More
PROTECT ALL COMPUTE RESOURCES UNDER ONE ROOF Including VMs, containers, and anything that runs code, while guarding against unauthorized or malicious code in runtime.See it in Action
TRUSTED BY
__ Previous
__ Next
WITHOUT RUNTIME SECURITY, ATTACKS GO UNDETECTED Fixing vulnerabilities to reduce the attack surface is vital. Detecting attacks when they occur in runtime is just as important. Runtime protection covers most attack vectors and functions as a last line of defense after an attacker has exploited a vulnerability ormisconfiguration.
Advantages of Runtime ProtectionRequest a Demo
Get Started for Free FULL VISIBILITY AND CONTROL OVER YOUR ENVIRONMENT Intezer’s lightweight sensor inspects every application, process or code running across your environment in memory, verifying you’re running 100% trusted code round-the-clock.How it Works
BORN IN THE CLOUD
* Holistic security for all types of compute resources: VMs, containers, Kubernetes, CaaS and FaaS * Integrated threat intelligence specializing in Linux threats * Integrate with your favorite DevOps tools including Chef, Puppet,Ansible and more
REDUCE ATTACK SURFACE * Identify and disable unwanted or risky applications * Identify vulnerabilities in runtime * Identify misconfigurations * Align with security benchmarks (CIS, NIST)VISIBILITY
* Monitor and log any running application or code * Visual dashboard showing high-level security status of all computeresources
DETECT
* Detect malicious code and malware in runtime * Detect unrecognized or unauthorized code * Detect exploitation of known and unknown vulnerabilities * Detect suspicious shell commands and Living off the Land (LotL)attacks
RESPOND
* Quickly terminate any unauthorized code without harming production * Contextual alerts including origin of code and malware family * Root Cause Analysis for incidents; identify the point of compromise in order to quickly fix the vulnerability * Seamlessly integrate with tools such as SIEM, SOAR and even SlackMORE THAN
500 COMPANIES
and government agencies use Intezer to defend against the latestthreats.
Niyo PearsonSubject Matter Expert for ONE Gas, Inc. Intezer is a leading provider in the incident response ‘last mile’. Most organizations have some network security or endpoint protection platform that blocks code from running in their environment; but that is where most investigations stop without a better understanding of the potential actor targeting them. Intezer has helped reshape ONE Gas incident response to remove the manual steps to attempt to perform this analysis which can take days to weeks, instead gleaming insight within minutes. Niyo PearsonSubject Matter Expert for ONE Gas, Inc. Intezer is a leading provider in the incident response ‘last mile’. Most organizations have some network security or endpoint protection platform that blocks code from running in their environment; but that is where most investigations stop without a better understanding of the potential actor targeting them. Intezer has helped reshape ONE Gas incident response to remove the manual steps to attempt to perform this analysis which can take days to weeks, instead gleaming insight within minutes. Niyo PearsonSubject Matter Expert for ONE Gas, Inc. Intezer is a leading provider in the incident response ‘last mile’. Most organizations have some network security or endpoint protection platform that blocks code from running in their environment; but that is where most investigations stop without a better understanding of the potential actor targeting them. Intezer has helped reshape ONE Gas incident response to remove the manual steps to attempt to perform this analysis which can take days to weeks, instead gleaming insight within minutes. Niyo PearsonSubject Matter Expert for ONE Gas, Inc. Intezer is a leading provider in the incident response ‘last mile’. Most organizations have some network security or endpoint protection platform that blocks code from running in their environment; but that is where most investigations stop without a better understanding of the potential actor targeting them. Intezer has helped reshape ONE Gas incident response to remove the manual steps to attempt to perform this analysis which can take days to weeks, instead gleaming insight within minutes. Niyo PearsonSubject Matter Expert for ONE Gas, Inc. Intezer is a leading provider in the incident response ‘last mile’. Most organizations have some network security or endpoint protection platform that blocks code from running in their environment; but that is where most investigations stop without a better understanding of the potential actor targeting them. Intezer has helped reshape ONE Gas incident response to remove the manual steps to attempt to perform this analysis which can take days to weeks, instead gleaming insight within minutes.Our Partners
__ Previous
__ Next
Request a Demo
Get Started for Free SPECIALIZING IN LINUX THREAT DETECTION Attackers are shifting their focus to target cloud and Linux-based infrastructure. Intezer is leading the charge in researching the latest Linux threats. STANTINKO’S PROXY AFTER YOUR APACHE SERVERRead more »
WATCH YOUR CONTAINERS: DOKI INFECTING DOCKER SERVERS IN THE CLOUDRead more »
CVE-2020-16995: MICROSOFT AZURE NETWORK WATCHER LINUX EXTENSION EOPRead more »
Access our weekly Linux Threat FeedWHY INTEZER?
NOT ANOTHER ANOMALY DETECTION SOLUTION We analyze the code! PROVEN LINUX THREAT DETECTION NO MANUAL RULES OR POLICIES NO IMPACT ON PRODUCTION PERFORMANCELEARN MORE
SANS WEBCAST: QUICK WINS FOR SECURING CLOUD WORKLOADSView resource »
CLOUD WORKLOAD SECURITY: WHAT YOU NEED TO KNOW – PART 1View resource »
TTPS MATRIX FOR LINUX CLOUD SERVERSView resource »
IPSTORM DETECTION & RESPONSE GUIDEView resource »
OUR PRODUCTS
Intezer Protect
CLOUD WORKLOAD PROTECTION PLATFORM Defend your cloud workloads in runtime against unauthorized andmalicious code.
Protect 10 cloud servers for freeIntezer Analyze
MALWARE ANALYSIS
PLATFORM
Get clear classification for your threats in seconds. Classify 50 files per month for freeFirst Name
Last Name
Job Title
Company
Country
United StatesCanadaAfghanistanAlbaniaAlgeriaAndorraAngolaAntigua and BarbudaArgentinaArmeniaArubaAustraliaAustriaAzerbaijanBahamasBahrainBangladeshBarbadosBelarusBelgiumBelizeBeninBermudaBhutanBoliviaBosnia and HerzegovinaBotswanaBrazilBruneiBulgariaBurkina FasoBurundiCambodiaCameroonCape VerdeCayman IslandsCentral African RepublicChadChileChinaColombiaComorosDemocratic Republic of the Congo (Kinshasa)Congo, Republic of(Brazzaville)Costa RicaCroatiaCubaCyprusCzechiaDenmarkDjiboutiDominicaDominican RepublicEast Timor (Timor-Leste)EcuadorEgyptEl SalvadorEquatorial GuineaEritreaEstoniaEthiopiaFijiFinlandFranceGabonGambiaGeorgiaGermanyGhanaGibraltarGreeceGrenadaGuatemalaGuineaGuinea-BissauGuyanaHaitiHondurasHong KongHungaryIcelandIndiaIndonesiaIran, Islamic Republic ofIraqIrelandIsraelItalyIvory CoastJamaicaJapanJordanKazakhstanKenyaKiribatiKorea, Democratic People's Republic of(North Korea)Korea, Republic ofKosovoKuwaitKyrgyzstanLao People's Democratic RepublicLatviaLebanonLesothoLiberiaLibyaLiechtensteinLithuaniaLuxembourgMacauMacedonia, Rep. ofMadagascarMalawiMalaysiaMaldivesMaliMaltaMarshall IslandsMauritaniaMauritiusMexicoMicronesia, Federal States ofMoldovaMonacoMongoliaMontenegroMoroccoMozambiqueMyanmar, BurmaNamibiaNauruNepalNetherlandsNew CaledoniaNew ZealandNicaraguaNigerNigeriaNorwayOmanPakistanPalauPalestinian territoriesPanamaPapua New GuineaParaguayPeruPhilippinesPolandPortugalPuerto RicoQatarRomaniaRussian FederationRwandaSaint Kitts and NevisSaint LuciaSaint Vincent and the GrenadinesSamoaSan MarinoSao Tome and PrincipeSaudi ArabiaSenegalSerbiaSeychellesSierra LeoneSingaporeSlovakiaSloveniaSolomon IslandsSomaliaSouth AfricaSouth SudanSpainSri LankaSudanSurinameSwazilandSwedenSwitzerlandSyria,Syrian Arab
RepublicTaiwanTajikistanTanzaniaThailandTibetTogoTongaTrinidad and TobagoTunisiaTurkeyTurkmenistanTuvaluUgandaUkraineUnited Arab EmiratesUnited KingdomUruguayUzbekistanVanuatuVatican City State (Holy See)VenezuelaVietnamYemenZambiaZimbabwe Select StateAlabamaAlaskaAmerican SamoaArizonaArkansasCaliforniaColoradoConnecticutDelawareDistrict of ColumbiaFloridaGeorgiaGuamHawaiiIdahoIllinoisIndianaIowaKansasKentuckyLouisianaMaineMarylandMassachusettsMichiganMinnesotaMississippiMissouriMontanaNebraskaNevadaNew HampshireNew JerseyNew MexicoNew YorkNorth CarolinaNorth DakotaNorthern Mariana IslandsOhioOklahomaOregonPennsylvaniaPuerto RicoRhode IslandSouth CarolinaSouth DakotaTennesseeTexasUnited States Minor Outlying IslandsUtahVermontVirgin IslandsVirginiaWashingtonWest VirginiaWisconsinWyomingPhone
* Intezer Protect
* Intezer Analyze
* Company
* Why Intezer
* Technology
* About
* Events
* News
* Careers
* Contact us
* Partners
* Blog
* Resources
* Docs
* Pricing
� Intezer.com 2021 All rights reserved* Terms of Use
* Privacy Policy
* __
* __
* __
* __
* __
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0