Are you over 18 and want to see adult content?
More Annotations

A complete backup of ecuworldwide.com
Are you over 18 and want to see adult content?
A complete backup of nostraightnews.com
Are you over 18 and want to see adult content?

A complete backup of haravdotnet.co.il
Are you over 18 and want to see adult content?
A complete backup of mkhere.blogspot.com
Are you over 18 and want to see adult content?
A complete backup of autoreviewhub.com
Are you over 18 and want to see adult content?
A complete backup of mrlovenstein.com
Are you over 18 and want to see adult content?
A complete backup of painterartist.com
Are you over 18 and want to see adult content?

A complete backup of razainterior.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of visitvalencia.com
Are you over 18 and want to see adult content?

A complete backup of freecodesmarket.com
Are you over 18 and want to see adult content?
A complete backup of truereligion-jeans.org.uk
Are you over 18 and want to see adult content?

A complete backup of chinaforklift.com
Are you over 18 and want to see adult content?
A complete backup of verzekervoordelig.nl
Are you over 18 and want to see adult content?
Text
awareness
29 MUST-KNOW CYBERSECURITY STATISTICS FOR 2020 29 Must-know Cybersecurity Statistics for 2020. The damage related to cybercrime is projected to hit $6 trillion annually by 2021, according to Cybersecurity Ventures.To give you a better view of the current state of overall security, we’ve collected 29 vital statistics about data breaches, hacking, industry-specific statistics, as well asspending and costs.
ENTERPRISE CYBERSECURITY POSTURE WITH CYBER OBSERVER Enterprise Cybersecurity Posture with Cyber Observer Reporting Cybersecurity performance is important for business success. IT team leaders, CISOs, SOC, auditors, risk officers and others generate reports to show cybersecurity gaps and vulnerabilities the organization faces, in order to manage and communicate enterprise cybersecurity posture to C-level management and board of CYBERSECURITY LAYERS While organizations have fortified themselves with an abundance of security technologies, many of them struggle to determine their enterprise cybersecurity level. Therefore, companies are striving to develop an action plan to improve and meet compliance and enterprise security needs. Cyber Observer developed a unified single-pane-of-glass framework that displays performance data andprovides
CYBER OBSERVER AND CROWDSTRIKE SOLUTION BRIEF The integration between Cyber Observer and CrowdStrike offers CxOs powerful and effective resilience visibility along with compliance validation and controls, to secure and monitor Tenable.SC in an unprecedented manner. COVERAGE GAP ANALYSIS Coverage Gap analysis is the third layer of Cyber Observer, designed and developed to indicate and present cybersecurity coverage gaps in currently deployed enterprise tools. Moreover, the platform proactively provides a list of lacking security capabilities for optimal cybersecurity coverage recommended by the industry. CONTINUOUS CYBERSECURITY MANAGEMENT AND AWARENESS SOLUTION The Challenge ‘As defenders, we have access to an extraordinary array of security tools and technology, security standards, training and classes, certifications, vulnerability WWW.CYBER-OBSERVER.COM www.cyber-observer.com COMPREHENSIVE CYBERSECURITY MANAGEMENT SOLUTION Continuous end-to-end security program awareness. Cyber Observer is the premier continuous controls monitoring (CCM) solution. It enables security and risk management leaders to continuously monitor their enterprise tools and align their cybersecurity posture with major frameworks, regulations, and standards. ABOUT - CYBER OBSERVER ABOUT. Merlin Ventures – A Key Partner. Merlin Ventures is the strategic arm of Merlin Cyber, a solutions provider with nearly 25 years of security industry experience partnering with U.S. federal government agencies and private and public corporations both large and small. As a strategic investor, Merlin Ventures helps visionary companies rapidly scale to deliver disruptive solutions for THE SECOND LAYER OF CYBERSECURITY The second layer of Cybersecurity – Continuous Security Domains Status. Due to enterprises understandably struggle with the challenge of managing intricate, fast-changing environments, Cyber Observer designed a unique end-to-end single-pane-of-glass platform that performs continuous monitoring while providing management andawareness
29 MUST-KNOW CYBERSECURITY STATISTICS FOR 2020 29 Must-know Cybersecurity Statistics for 2020. The damage related to cybercrime is projected to hit $6 trillion annually by 2021, according to Cybersecurity Ventures.To give you a better view of the current state of overall security, we’ve collected 29 vital statistics about data breaches, hacking, industry-specific statistics, as well asspending and costs.
ENTERPRISE CYBERSECURITY POSTURE WITH CYBER OBSERVER Enterprise Cybersecurity Posture with Cyber Observer Reporting Cybersecurity performance is important for business success. IT team leaders, CISOs, SOC, auditors, risk officers and others generate reports to show cybersecurity gaps and vulnerabilities the organization faces, in order to manage and communicate enterprise cybersecurity posture to C-level management and board of CYBERSECURITY LAYERS While organizations have fortified themselves with an abundance of security technologies, many of them struggle to determine their enterprise cybersecurity level. Therefore, companies are striving to develop an action plan to improve and meet compliance and enterprise security needs. Cyber Observer developed a unified single-pane-of-glass framework that displays performance data andprovides
CYBER OBSERVER AND CROWDSTRIKE SOLUTION BRIEF The integration between Cyber Observer and CrowdStrike offers CxOs powerful and effective resilience visibility along with compliance validation and controls, to secure and monitor Tenable.SC in an unprecedented manner. COVERAGE GAP ANALYSIS Coverage Gap analysis is the third layer of Cyber Observer, designed and developed to indicate and present cybersecurity coverage gaps in currently deployed enterprise tools. Moreover, the platform proactively provides a list of lacking security capabilities for optimal cybersecurity coverage recommended by the industry. CONTINUOUS CYBERSECURITY MANAGEMENT AND AWARENESS SOLUTION The Challenge ‘As defenders, we have access to an extraordinary array of security tools and technology, security standards, training and classes, certifications, vulnerability WWW.CYBER-OBSERVER.COM www.cyber-observer.com NEWS - CYBER OBSERVER News. January 19, 2021 |. Verietyinfo. The latest version of Cyber Observer provides a new visibility of cybersecurity risk attitudes. verietyinfo.com. January 19, 2021 |. Business wire. Cyber Observer’s Latest Release Provides New Visibility Into Cybersecurity RiskPosture.
HOW IT WORKS
Cyber Observer’s core engine is very flexible and powerful and can support unlimited CSCs, retrieved from unlimited data sources (on-premises security tools, cloud tools and services, IT tools related to security, self-assessment data sources, etc.), unlimited security views, and unlimited users. Customers can copy and modify theout-of-the
FEATURES AND BENEFITS Cyber Observer connectors continuously retrieve CSCs and then save and store the raw data in a historical database. This database allows organizations to keep track of admin activities, firewall rule changes, policy changes, malware definition updates, tool configuration changes, comparison reports, and much more. RequestDemo.
REMOTE CYBERSECURITY MANAGEMENT Cyber Observer White-Paper REMOTE CYBERSECURITY MANAGEMENT 6 To enable secure and fast remote access to corporate resources from any network, and from any device, you need to protect your network with SSL VPNcapabilities.
USE CASES-V3
USE CASE. Vulnerability Prioritization. The Problem: Organizations lack efficient ways to qualify the severity of their risks or prioritize the protection of their most critical or high-value assets. The Solution: Cyber Observer enables organizations to create specific, customized views based on their critical business assets. Security and risk management executives can modify polling 4 KEYS TO COMPREHENSIVE CYBERSECURITY MANAGEMENT A REMOTE 4 Keys to comprehensive cybersecurity management a Remote Workforce. The COVID-19 outbreak has affected many aspects of our daily life. We are staying home, working remotely and communicating with our colleagues, partners, prospects, and customers using cloud-basedsolutions.
CYBER OBSERVER CITED BY GARTNER IN NEW DIGITAL RISK In new Digital Risk Management category, Cyber Observer cited by Gartner Gartner recently released their latest Competitive Landscape on Integrated Risk Management (IRM) (paywall) solutions and has cited Cyber Observer as a vendor in one of its fastest growing segment. The categories under IRM – heir to the oft-maligned GRC market – include audit, compliance, WWW.CYBER-OBSERVER.COM www.cyber-observer.com WHAT IS CONTINUOUS CONTROLS MONITORING? What is Continuous Controls Monitoring? Critical Security Controls (CSCs) are a recommended set of actions for cybersecurity that provide ways to help prevent and stop attacks on critical data and systems. Nearly every cybersecurity practitioner is working to implement and improve their implementation of security controls. SHORTEN YOUR PATH TO ANNUAL SWIFT CSCF COMPLIANCE Shorten Your Path to Annual SWIFT CSCF Compliance. In response to a series of cyberattacks, SWIFT (The Society for Worldwide Interbank Financial Telecommunication) established a standard set of security controls designed to help financial institutes secure their local environments and to foster awareness and good practices for the entireSWIFT community.
COMPREHENSIVE CYBERSECURITY MANAGEMENT SOLUTION Continuous end-to-end security program awareness. Cyber Observer is the premier continuous controls monitoring (CCM) solution. It enables security and risk management leaders to continuously monitor their enterprise tools and align their cybersecurity posture with major frameworks, regulations, and standards. ABOUT - CYBER OBSERVER ABOUT. Merlin Ventures – A Key Partner. Merlin Ventures is the strategic arm of Merlin Cyber, a solutions provider with nearly 25 years of security industry experience partnering with U.S. federal government agencies and private and public corporations both large and small. As a strategic investor, Merlin Ventures helps visionary companies rapidly scale to deliver disruptive solutions for THE SECOND LAYER OF CYBERSECURITY The second layer of Cybersecurity – Continuous Security Domains Status. Due to enterprises understandably struggle with the challenge of managing intricate, fast-changing environments, Cyber Observer designed a unique end-to-end single-pane-of-glass platform that performs continuous monitoring while providing management andawareness
29 MUST-KNOW CYBERSECURITY STATISTICS FOR 2020 29 Must-know Cybersecurity Statistics for 2020. The damage related to cybercrime is projected to hit $6 trillion annually by 2021, according to Cybersecurity Ventures.To give you a better view of the current state of overall security, we’ve collected 29 vital statistics about data breaches, hacking, industry-specific statistics, as well asspending and costs.
CYBERSECURITY LAYERS While organizations have fortified themselves with an abundance of security technologies, many of them struggle to determine their enterprise cybersecurity level. Therefore, companies are striving to develop an action plan to improve and meet compliance and enterprise security needs. Cyber Observer developed a unified single-pane-of-glass framework that displays performance data andprovides
CYBER OBSERVER AND CROWDSTRIKE SOLUTION BRIEF The integration between Cyber Observer and CrowdStrike offers CxOs powerful and effective resilience visibility along with compliance validation and controls, to secure and monitor Tenable.SC in an unprecedented manner. COVERAGE GAP ANALYSIS Coverage Gap analysis is the third layer of Cyber Observer, designed and developed to indicate and present cybersecurity coverage gaps in currently deployed enterprise tools. Moreover, the platform proactively provides a list of lacking security capabilities for optimal cybersecurity coverage recommended by the industry. CONTINUOUS CYBERSECURITY MANAGEMENT AND AWARENESS SOLUTION The Challenge ‘As defenders, we have access to an extraordinary array of security tools and technology, security standards, training and classes, certifications, vulnerability CYBER OBSERVER AND MICROSOFT TEAMS INTEGRATION Yes, I would like to receive communications from Cyber Observer. Please read more about our Privacy Policy. SHORTEN YOUR PATH TO ANNUAL SWIFT CSCF COMPLIANCE Shorten Your Path to Annual SWIFT CSCF Compliance. In response to a series of cyberattacks, SWIFT (The Society for Worldwide Interbank Financial Telecommunication) established a standard set of security controls designed to help financial institutes secure their local environments and to foster awareness and good practices for the entireSWIFT community.
COMPREHENSIVE CYBERSECURITY MANAGEMENT SOLUTION Continuous end-to-end security program awareness. Cyber Observer is the premier continuous controls monitoring (CCM) solution. It enables security and risk management leaders to continuously monitor their enterprise tools and align their cybersecurity posture with major frameworks, regulations, and standards. ABOUT - CYBER OBSERVER ABOUT. Merlin Ventures – A Key Partner. Merlin Ventures is the strategic arm of Merlin Cyber, a solutions provider with nearly 25 years of security industry experience partnering with U.S. federal government agencies and private and public corporations both large and small. As a strategic investor, Merlin Ventures helps visionary companies rapidly scale to deliver disruptive solutions for THE SECOND LAYER OF CYBERSECURITY The second layer of Cybersecurity – Continuous Security Domains Status. Due to enterprises understandably struggle with the challenge of managing intricate, fast-changing environments, Cyber Observer designed a unique end-to-end single-pane-of-glass platform that performs continuous monitoring while providing management andawareness
29 MUST-KNOW CYBERSECURITY STATISTICS FOR 2020 29 Must-know Cybersecurity Statistics for 2020. The damage related to cybercrime is projected to hit $6 trillion annually by 2021, according to Cybersecurity Ventures.To give you a better view of the current state of overall security, we’ve collected 29 vital statistics about data breaches, hacking, industry-specific statistics, as well asspending and costs.
CYBERSECURITY LAYERS While organizations have fortified themselves with an abundance of security technologies, many of them struggle to determine their enterprise cybersecurity level. Therefore, companies are striving to develop an action plan to improve and meet compliance and enterprise security needs. Cyber Observer developed a unified single-pane-of-glass framework that displays performance data andprovides
CYBER OBSERVER AND CROWDSTRIKE SOLUTION BRIEF The integration between Cyber Observer and CrowdStrike offers CxOs powerful and effective resilience visibility along with compliance validation and controls, to secure and monitor Tenable.SC in an unprecedented manner. COVERAGE GAP ANALYSIS Coverage Gap analysis is the third layer of Cyber Observer, designed and developed to indicate and present cybersecurity coverage gaps in currently deployed enterprise tools. Moreover, the platform proactively provides a list of lacking security capabilities for optimal cybersecurity coverage recommended by the industry. CONTINUOUS CYBERSECURITY MANAGEMENT AND AWARENESS SOLUTION The Challenge ‘As defenders, we have access to an extraordinary array of security tools and technology, security standards, training and classes, certifications, vulnerability CYBER OBSERVER AND MICROSOFT TEAMS INTEGRATION Yes, I would like to receive communications from Cyber Observer. Please read more about our Privacy Policy. SHORTEN YOUR PATH TO ANNUAL SWIFT CSCF COMPLIANCE Shorten Your Path to Annual SWIFT CSCF Compliance. In response to a series of cyberattacks, SWIFT (The Society for Worldwide Interbank Financial Telecommunication) established a standard set of security controls designed to help financial institutes secure their local environments and to foster awareness and good practices for the entireSWIFT community.
ENTERPRISE CYBERSECURITY POSTURE WITH CYBER OBSERVER Enterprise Cybersecurity Posture with Cyber Observer Reporting Cybersecurity performance is important for business success. IT team leaders, CISOs, SOC, auditors, risk officers and others generate reports to show cybersecurity gaps and vulnerabilities the organization faces, in order to manage and communicate enterprise cybersecurity posture to C-level management and board ofHOW IT WORKS
Cyber Observer’s core engine is very flexible and powerful and can support unlimited CSCs, retrieved from unlimited data sources (on-premises security tools, cloud tools and services, IT tools related to security, self-assessment data sources, etc.), unlimited security views, and unlimited users. Customers can copy and modify theout-of-the
REMOTE CYBERSECURITY MANAGEMENT Cyber Observer experts are uniquely qualified to help organizations transition smoothly to a more secure environment. Our platform is ideally suited to provide CISOs and security teams with continuous remote visibility into their enterprise cybersecurity posture: coverage gaps. misfunctioning tools. abnormal deviations and more. CYBER OBSERVER SWIFT CSCF TECHNICAL VIEW AND COVERAGE Cyber Observer SWIFT CSCF. technical view and coverage. In response to recent cyberattacks, SWIFT issued baseline security requirements through its Customer Security Controls Framework. The CSC framework helps financial institutes to set up cybersecurity controls to implement in their local environments. To help you to conduct anindependent
WWW.CYBER-OBSERVER.COM www.cyber-observer.com THE COMPLEXITY OF MORE CYBERSECURITY TOOLS The complexity of more cybersecurity tools In the challenging cybersecurity landscape of today, there is an over-abundance of cybersecurity tools. As the number of breaches proliferated, so have the solutions and technologies designed to stop them.SOLUTION PROVIDERS
PARTNERS. Solution Providers. Cyber Observer provides a unique opportunity for solution partners, to bring valuable and innovative cybersecurity management solutions and services to customers. WHAT IS CONTINUOUS CONTROLS MONITORING? What is Continuous Controls Monitoring? Critical Security Controls (CSCs) are a recommended set of actions for cybersecurity that provide ways to help prevent and stop attacks on critical data and systems. Nearly every cybersecurity practitioner is working to implement and improve their implementation of security controls. FEATURES AND BENEFITS Cyber Observer connectors continuously retrieve CSCs and then save and store the raw data in a historical database. This database allows organizations to keep track of admin activities, firewall rule changes, policy changes, malware definition updates, tool configuration changes, comparison reports, and much more. RequestDemo.
CYBER OBSERVER AND FIREEYE NX SOLUTION BRIEF The integration between Cyber Observer and FireEye offers CxOs powerful and effective resilience visibility, along with compliance validation and controls, to secure and monitor FireEye NX in an unprecedented manner. Cyber Observer deploys to the corporate network automatically, in a matter of a few hours, predefined with securitydomains
COMPREHENSIVE CYBERSECURITY MANAGEMENT SOLUTION Continuous end-to-end security program awareness. Cyber Observer is the premier continuous controls monitoring (CCM) solution. It enables security and risk management leaders to continuously monitor their enterprise tools and align their cybersecurity posture with major frameworks, regulations, and standards. THE SECOND LAYER OF CYBERSECURITY The second layer of Cybersecurity – Continuous Security Domains Status. Due to enterprises understandably struggle with the challenge of managing intricate, fast-changing environments, Cyber Observer designed a unique end-to-end single-pane-of-glass platform that performs continuous monitoring while providing management andawareness
29 MUST-KNOW CYBERSECURITY STATISTICS FOR 2020 29 Must-know Cybersecurity Statistics for 2020. The damage related to cybercrime is projected to hit $6 trillion annually by 2021, according to Cybersecurity Ventures.To give you a better view of the current state of overall security, we’ve collected 29 vital statistics about data breaches, hacking, industry-specific statistics, as well asspending and costs.
ENTERPRISE CYBERSECURITY POSTURE WITH CYBER OBSERVER Enterprise Cybersecurity Posture with Cyber Observer Reporting Cybersecurity performance is important for business success. IT team leaders, CISOs, SOC, auditors, risk officers and others generate reports to show cybersecurity gaps and vulnerabilities the organization faces, in order to manage and communicate enterprise cybersecurity posture to C-level management and board of COVERAGE GAP ANALYSIS Coverage Gap analysis is the third layer of Cyber Observer, designed and developed to indicate and present cybersecurity coverage gaps in currently deployed enterprise tools. Moreover, the platform proactively provides a list of lacking security capabilities for optimal cybersecurity coverage recommended by the industry. CYBERSECURITY LAYERS While organizations have fortified themselves with an abundance of security technologies, many of them struggle to determine their enterprise cybersecurity level. Therefore, companies are striving to develop an action plan to improve and meet compliance and enterprise security needs. Cyber Observer developed a unified single-pane-of-glass framework that displays performance data andprovides
CYBER OBSERVER AND CROWDSTRIKE SOLUTION BRIEF The integration between Cyber Observer and CrowdStrike offers CxOs powerful and effective resilience visibility along with compliance validation and controls, to secure and monitor Tenable.SC in an unprecedented manner. CONTINUOUS CYBERSECURITY MANAGEMENT AND AWARENESS SOLUTION The Challenge ‘As defenders, we have access to an extraordinary array of security tools and technology, security standards, training and classes, certifications, vulnerability CYBER OBSERVER CITED BY GARTNER IN NEW DIGITAL RISK In new Digital Risk Management category, Cyber Observer cited by Gartner Gartner recently released their latest Competitive Landscape on Integrated Risk Management (IRM) (paywall) solutions and has cited Cyber Observer as a vendor in one of its fastest growing segment. The categories under IRM – heir to the oft-maligned GRC market – include audit, compliance, CYBER OBSERVER AND FIREEYE NX SOLUTION BRIEF The integration between Cyber Observer and FireEye offers CxOs powerful and effective resilience visibility, along with compliance validation and controls, to secure and monitor FireEye NX in an unprecedented manner. Cyber Observer deploys to the corporate network automatically, in a matter of a few hours, predefined with securitydomains
COMPREHENSIVE CYBERSECURITY MANAGEMENT SOLUTION Continuous end-to-end security program awareness. Cyber Observer is the premier continuous controls monitoring (CCM) solution. It enables security and risk management leaders to continuously monitor their enterprise tools and align their cybersecurity posture with major frameworks, regulations, and standards. THE SECOND LAYER OF CYBERSECURITY The second layer of Cybersecurity – Continuous Security Domains Status. Due to enterprises understandably struggle with the challenge of managing intricate, fast-changing environments, Cyber Observer designed a unique end-to-end single-pane-of-glass platform that performs continuous monitoring while providing management andawareness
29 MUST-KNOW CYBERSECURITY STATISTICS FOR 2020 29 Must-know Cybersecurity Statistics for 2020. The damage related to cybercrime is projected to hit $6 trillion annually by 2021, according to Cybersecurity Ventures.To give you a better view of the current state of overall security, we’ve collected 29 vital statistics about data breaches, hacking, industry-specific statistics, as well asspending and costs.
ENTERPRISE CYBERSECURITY POSTURE WITH CYBER OBSERVER Enterprise Cybersecurity Posture with Cyber Observer Reporting Cybersecurity performance is important for business success. IT team leaders, CISOs, SOC, auditors, risk officers and others generate reports to show cybersecurity gaps and vulnerabilities the organization faces, in order to manage and communicate enterprise cybersecurity posture to C-level management and board of COVERAGE GAP ANALYSIS Coverage Gap analysis is the third layer of Cyber Observer, designed and developed to indicate and present cybersecurity coverage gaps in currently deployed enterprise tools. Moreover, the platform proactively provides a list of lacking security capabilities for optimal cybersecurity coverage recommended by the industry. CYBERSECURITY LAYERS While organizations have fortified themselves with an abundance of security technologies, many of them struggle to determine their enterprise cybersecurity level. Therefore, companies are striving to develop an action plan to improve and meet compliance and enterprise security needs. Cyber Observer developed a unified single-pane-of-glass framework that displays performance data andprovides
CYBER OBSERVER AND CROWDSTRIKE SOLUTION BRIEF The integration between Cyber Observer and CrowdStrike offers CxOs powerful and effective resilience visibility along with compliance validation and controls, to secure and monitor Tenable.SC in an unprecedented manner. CONTINUOUS CYBERSECURITY MANAGEMENT AND AWARENESS SOLUTION The Challenge ‘As defenders, we have access to an extraordinary array of security tools and technology, security standards, training and classes, certifications, vulnerability CYBER OBSERVER CITED BY GARTNER IN NEW DIGITAL RISK In new Digital Risk Management category, Cyber Observer cited by Gartner Gartner recently released their latest Competitive Landscape on Integrated Risk Management (IRM) (paywall) solutions and has cited Cyber Observer as a vendor in one of its fastest growing segment. The categories under IRM – heir to the oft-maligned GRC market – include audit, compliance, CYBER OBSERVER AND FIREEYE NX SOLUTION BRIEF The integration between Cyber Observer and FireEye offers CxOs powerful and effective resilience visibility, along with compliance validation and controls, to secure and monitor FireEye NX in an unprecedented manner. Cyber Observer deploys to the corporate network automatically, in a matter of a few hours, predefined with securitydomains
HOW IT WORKS
Cyber Observer’s core engine is very flexible and powerful and can support unlimited CSCs, retrieved from unlimited data sources (on-premises security tools, cloud tools and services, IT tools related to security, self-assessment data sources, etc.), unlimited security views, and unlimited users. Customers can copy and modify theout-of-the
ENTERPRISE CYBERSECURITY POSTURE WITH CYBER OBSERVER Enterprise Cybersecurity Posture with Cyber Observer Reporting Cybersecurity performance is important for business success. IT team leaders, CISOs, SOC, auditors, risk officers and others generate reports to show cybersecurity gaps and vulnerabilities the organization faces, in order to manage and communicate enterprise cybersecurity posture to C-level management and board ofSOLUTION PROVIDERS
PARTNERS. Solution Providers. Cyber Observer provides a unique opportunity for solution partners, to bring valuable and innovative cybersecurity management solutions and services to customers. 4 KEYS TO COMPREHENSIVE CYBERSECURITY MANAGEMENT A REMOTE 4 Keys to comprehensive cybersecurity management a Remote Workforce. The COVID-19 outbreak has affected many aspects of our daily life. We are staying home, working remotely and communicating with our colleagues, partners, prospects, and customers using cloud-basedsolutions.
CYBER OBSERVER V3.5 NEW FEATURES 5. SWIFT view The SWIFT CSCF view is a built-in and pre-defined view in Cyber Observer and contains the framework's security controlsdomains:
CYBER OBSERVER CITED BY GARTNER IN NEW DIGITAL RISK In new Digital Risk Management category, Cyber Observer cited by Gartner Gartner recently released their latest Competitive Landscape on Integrated Risk Management (IRM) (paywall) solutions and has cited Cyber Observer as a vendor in one of its fastest growing segment. The categories under IRM – heir to the oft-maligned GRC market – include audit, compliance, REMOTE CYBERSECURITY MANAGEMENT Cyber Observer White-Paper REMOTE CYBERSECURITY MANAGEMENT 6 To enable secure and fast remote access to corporate resources from any network, and from any device, you need to protect your network with SSL VPNcapabilities.
WHAT IS CONTINUOUS CONTROLS MONITORING? What is Continuous Controls Monitoring? Critical Security Controls (CSCs) are a recommended set of actions for cybersecurity that provide ways to help prevent and stop attacks on critical data and systems. Nearly every cybersecurity practitioner is working to implement and improve their implementation of security controls. WWW.CYBER-OBSERVER.COM www.cyber-observer.com CYBER OBSERVER AND OFFICE 365 INTEGRATION The integration between Cyber Observer and Office 365 offers CxOs powerful and effective resilience visibility along with compliance validation and controls, to secure and monitor Office 365 in an unprecedented manner. Cyber Observer deploys to the corporate network automatically, in a matter of a few hours, predefined with securitydomains
COMPREHENSIVE CYBERSECURITY MANAGEMENT SOLUTION Continuous end-to-end security program awareness. Cyber Observer is the premier continuous controls monitoring (CCM) solution. It enables security and risk management leaders to continuously monitor their enterprise tools and align their cybersecurity posture with major frameworks, regulations, and standards. THE SECOND LAYER OF CYBERSECURITY The second layer of Cybersecurity – Continuous Security Domains Status. Due to enterprises understandably struggle with the challenge of managing intricate, fast-changing environments, Cyber Observer designed a unique end-to-end single-pane-of-glass platform that performs continuous monitoring while providing management andawareness
29 MUST-KNOW CYBERSECURITY STATISTICS FOR 2020 29 Must-know Cybersecurity Statistics for 2020. The damage related to cybercrime is projected to hit $6 trillion annually by 2021, according to Cybersecurity Ventures.To give you a better view of the current state of overall security, we’ve collected 29 vital statistics about data breaches, hacking, industry-specific statistics, as well asspending and costs.
ENTERPRISE CYBERSECURITY POSTURE WITH CYBER OBSERVER Enterprise Cybersecurity Posture with Cyber Observer Reporting Cybersecurity performance is important for business success. IT team leaders, CISOs, SOC, auditors, risk officers and others generate reports to show cybersecurity gaps and vulnerabilities the organization faces, in order to manage and communicate enterprise cybersecurity posture to C-level management and board of COVERAGE GAP ANALYSIS Coverage Gap analysis is the third layer of Cyber Observer, designed and developed to indicate and present cybersecurity coverage gaps in currently deployed enterprise tools. Moreover, the platform proactively provides a list of lacking security capabilities for optimal cybersecurity coverage recommended by the industry. CYBERSECURITY LAYERS While organizations have fortified themselves with an abundance of security technologies, many of them struggle to determine their enterprise cybersecurity level. Therefore, companies are striving to develop an action plan to improve and meet compliance and enterprise security needs. Cyber Observer developed a unified single-pane-of-glass framework that displays performance data andprovides
CYBER OBSERVER AND CROWDSTRIKE SOLUTION BRIEF The integration between Cyber Observer and CrowdStrike offers CxOs powerful and effective resilience visibility along with compliance validation and controls, to secure and monitor Tenable.SC in an unprecedented manner. CONTINUOUS CYBERSECURITY MANAGEMENT AND AWARENESS SOLUTION The Challenge ‘As defenders, we have access to an extraordinary array of security tools and technology, security standards, training and classes, certifications, vulnerability CYBER OBSERVER CITED BY GARTNER IN NEW DIGITAL RISK In new Digital Risk Management category, Cyber Observer cited by Gartner Gartner recently released their latest Competitive Landscape on Integrated Risk Management (IRM) (paywall) solutions and has cited Cyber Observer as a vendor in one of its fastest growing segment. The categories under IRM – heir to the oft-maligned GRC market – include audit, compliance, CYBER OBSERVER AND FIREEYE NX SOLUTION BRIEF The integration between Cyber Observer and FireEye offers CxOs powerful and effective resilience visibility, along with compliance validation and controls, to secure and monitor FireEye NX in an unprecedented manner. Cyber Observer deploys to the corporate network automatically, in a matter of a few hours, predefined with securitydomains
COMPREHENSIVE CYBERSECURITY MANAGEMENT SOLUTION Continuous end-to-end security program awareness. Cyber Observer is the premier continuous controls monitoring (CCM) solution. It enables security and risk management leaders to continuously monitor their enterprise tools and align their cybersecurity posture with major frameworks, regulations, and standards. THE SECOND LAYER OF CYBERSECURITY The second layer of Cybersecurity – Continuous Security Domains Status. Due to enterprises understandably struggle with the challenge of managing intricate, fast-changing environments, Cyber Observer designed a unique end-to-end single-pane-of-glass platform that performs continuous monitoring while providing management andawareness
29 MUST-KNOW CYBERSECURITY STATISTICS FOR 2020 29 Must-know Cybersecurity Statistics for 2020. The damage related to cybercrime is projected to hit $6 trillion annually by 2021, according to Cybersecurity Ventures.To give you a better view of the current state of overall security, we’ve collected 29 vital statistics about data breaches, hacking, industry-specific statistics, as well asspending and costs.
ENTERPRISE CYBERSECURITY POSTURE WITH CYBER OBSERVER Enterprise Cybersecurity Posture with Cyber Observer Reporting Cybersecurity performance is important for business success. IT team leaders, CISOs, SOC, auditors, risk officers and others generate reports to show cybersecurity gaps and vulnerabilities the organization faces, in order to manage and communicate enterprise cybersecurity posture to C-level management and board ofHOW IT WORKS
Cyber Observer’s core engine is very flexible and powerful and can support unlimited CSCs, retrieved from unlimited data sources (on-premises security tools, cloud tools and services, IT tools related to security, self-assessment data sources, etc.), unlimited security views, and unlimited users. Customers can copy and modify theout-of-the
ENTERPRISE CYBERSECURITY POSTURE WITH CYBER OBSERVER Enterprise Cybersecurity Posture with Cyber Observer Reporting Cybersecurity performance is important for business success. IT team leaders, CISOs, SOC, auditors, risk officers and others generate reports to show cybersecurity gaps and vulnerabilities the organization faces, in order to manage and communicate enterprise cybersecurity posture to C-level management and board ofSOLUTION PROVIDERS
PARTNERS. Solution Providers. Cyber Observer provides a unique opportunity for solution partners, to bring valuable and innovative cybersecurity management solutions and services to customers. 4 KEYS TO COMPREHENSIVE CYBERSECURITY MANAGEMENT A REMOTE 4 Keys to comprehensive cybersecurity management a Remote Workforce. The COVID-19 outbreak has affected many aspects of our daily life. We are staying home, working remotely and communicating with our colleagues, partners, prospects, and customers using cloud-basedsolutions.
CYBER OBSERVER V3.5 NEW FEATURES 5. SWIFT view The SWIFT CSCF view is a built-in and pre-defined view in Cyber Observer and contains the framework's security controlsdomains:
CYBER OBSERVER CITED BY GARTNER IN NEW DIGITAL RISK In new Digital Risk Management category, Cyber Observer cited by Gartner Gartner recently released their latest Competitive Landscape on Integrated Risk Management (IRM) (paywall) solutions and has cited Cyber Observer as a vendor in one of its fastest growing segment. The categories under IRM – heir to the oft-maligned GRC market – include audit, compliance, REMOTE CYBERSECURITY MANAGEMENT Cyber Observer White-Paper REMOTE CYBERSECURITY MANAGEMENT 6 To enable secure and fast remote access to corporate resources from any network, and from any device, you need to protect your network with SSL VPNcapabilities.
WHAT IS CONTINUOUS CONTROLS MONITORING? What is Continuous Controls Monitoring? Critical Security Controls (CSCs) are a recommended set of actions for cybersecurity that provide ways to help prevent and stop attacks on critical data and systems. Nearly every cybersecurity practitioner is working to implement and improve their implementation of security controls. WWW.CYBER-OBSERVER.COM www.cyber-observer.com CYBER OBSERVER AND OFFICE 365 INTEGRATION The integration between Cyber Observer and Office 365 offers CxOs powerful and effective resilience visibility along with compliance validation and controls, to secure and monitor Office 365 in an unprecedented manner. Cyber Observer deploys to the corporate network automatically, in a matter of a few hours, predefined with securitydomains
This website stores cookies on your computer. These cookies are used to improve your website experience and provide more personalized services to you, both on this website and through other media. To find out more about the cookies we use, see our Privacy Policy. We won't track your information when you visit our site. But in order to comply with your preferences, we'll have to use just one tiny cookie so that you're not asked to make this choice again.Accept Decline
* Solution
* What is Continuous Controls Monitoring? * Features and Benefits* How it Works
* Frameworks and Standards * Common Integrations* Use Cases
* Asset Management
* Risk Posture Monitoring * Vulnerability Prioritization * Compliance Auditing* Board Reporting
* Partners
* Solution Providers* Become a Partner
* Insights & News
* Blog
* Resource Library
* News
* About
* About Cyber Observer* Executive Team
* Contact
Request Demo
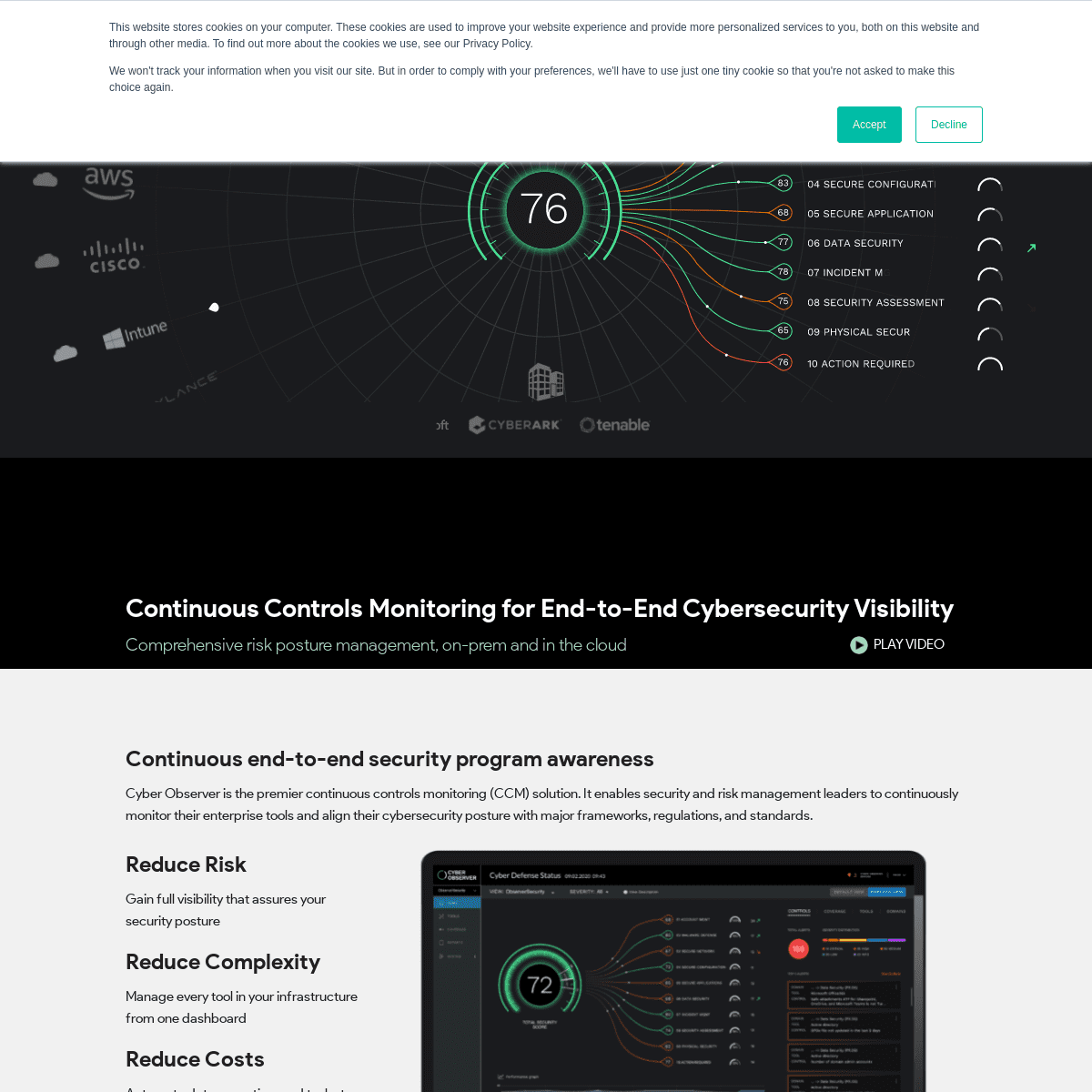
CONTINUOUS CONTROLS MONITORING FOR END-TO-END CYBERSECURITY VISIBILITY Comprehensive risk posture management, on-prem and in the cloudPLAY VIDEO
CONTINUOUS END-TO-END SECURITY PROGRAM AWARENESS Cyber Observer is the premier continuous controls monitoring (CCM) solution. It enables security and risk management leaders to continuously monitor their enterprise tools and align their cybersecurity posture with major frameworks, regulations, andstandards.
REDUCE RISK
Gain full visibility that assures your security postureREDUCE COMPLEXITY
Manage every tool in your infrastructure from one dashboardREDUCE COSTS
Automate data, reporting, and tasks to save time and money ON-PREM TOOLS STATUS Cyber Observer continuously monitors enterprise security and IT infrastructure tools to verify that they are well-configured, up and running, and performing their functions. IN-CLOUD TOOLS STATUS Cyber Observer continuously monitors cloud platforms (AWS, Azure, Google) and other Cloud services to verify that they are well-configured and secured.RISK POSTURE VIEWS
Cyber Observer identifies security gaps that exist and provides recommendations for fixing. SECURITY COVERAGE STATUS Cyber Observer comes equipped with industry best practices and recommendations on cybersecurity coverage needed based on tools capabilities and thousands of Critical Security Controls (CSCs). BEHAVIORAL DEVIATION ALERTS Cyber Observer’s analytics engine continuously polls all the deployed cyber and IT tools for highly valuable data and calculates the activities that represent normal behavior. CONTINUOUS REPORTING Cyber Observer’s Reporting module provides updated information about enterprise cybersecurity tools status and risk posture. CONTINUOUS COMPLIANCE Continuous monitoring on how your organization is meeting international standards–such as NIST, ISO 27001, PCI-DSS and more–by continuously retrieving Critical Security Controls (CSCs) from your security and related tools.Request Demo
On-Prem
Tools Status
In-cloud
Tools Status
Risk Posture
Views
Security Coverage
Status
Behavioral
Deviation Alerts
Continuous
Reporting
Compliance
Monitoring
PRE-BUILT ASSESSMENTS TO HELP ENSURE COMPLIANCE5346
Supported CSCs
83
Supported tools
8
Supported standards
SEAMLESS INTEGRATIONS WITH POPULAR SECURITY TOOLSFEATURED USE CASES
ASSET
MANAGEMENT
Organizations implement dozens of different security tools from different vendors to secure their digital data and IT environments.Read More >>
RISK POSTURE
MONITORING
The challenging cybersecurity landscape of today comes with an over-abundance of cybersecurity tools.Read More >>
VULNERABILITY
PRIORITIZATION
Organizations lack efficient ways to qualify the severity of their risks or prioritize the protection of their most critical orhigh-value assets.
Read More >>
COMPLIANCE
AUDITING
Organizations need to comply with a multitude of industry security standards, regulations, and frameworks.Read More >>
BOARD
REPORTING
Organizations need to continuously report to board members, C-level management, auditors, risk officers.Read More >>
INSIGHTS AND NEWS
ONE PAGER
THE PREMIER CCM SOLUTION NOW BETTER THAN EVERWHITE PAPER
CYBER OBSERVER SWIFT CSCF TECHNICAL VIEWSOLUTION BRIEF
CYBER OBSERVER AND MICROSOFT TEAMS INTEGRATIONView all Insights
“Cyber Observer empowers us to have full visibility into our network. It is easier for us to manage our cybersecurity assets and understand what has gone wrong within minutes. We are also able to identify any security gaps in our network and this has helped us to ease our daily workload” - - Root Security "As defenders we have access to an extraordinary array of security tools and technology, security standards, training and classes, certifications, vulnerability databases, guidance, best practices, catalogues of security controls, and countless security checklists, benchmarks, and recommendations. But all of this technology, information, and oversight has become a veritable ‘Fog of More.’ Critical Security Controls (CSCs) are a recommended set of actions for cyber defense that provide specific and actionable ways to stop today\'s most pervasive and dangerous aacks" - -SANS “Cyber Observer empowers us to have full visibility into our network. It is easier for us to manage our cybersecurity assets and understand what has gone wrong within minutes. We are also able to identify any security gaps in our network and this has helped us to ease our daily workload” - - Root Security "As defenders we have access to an extraordinary array of security tools and technology, security standards, training and classes, certifications, vulnerability databases, guidance, best practices, catalogues of security controls, and countless security checklists, benchmarks, and recommendations. But all of this technology, information, and oversight has become a veritable ‘Fog of More.’ Critical Security Controls (CSCs) are a recommended set of actions for cyber defense that provide specific and actionable ways to stop today\'s most pervasive and dangerous aacks" - -SANSSOLUTION
* What is Continuous Controls Monitoring? * Features and Benefits* How it works
* Frameworks and Standards * Common IntegrationsUSE CASES
* Asset Management
* Risk Posture Monitoring * Vulnerability Prioritization * Compliance Auditing* Board Reporting
PARTNERS
* SOLUTION PROVIDERS* BECOME A PARTNER
INSIGHTS & NEWS
* BLOG
* RESOURCE LIBRARY
* NEWS
ABOUT
* About Cyber Observer* Executive Team
* CONTACT
COPYRIGHT © 2021 | CONTACT US| PRIVACY
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0