Are you over 18 and want to see adult content?
More Annotations

A complete backup of www.forbes.com/sites/brianmazique/2020/02/09/ufc-247-controversial-judge-defends-his-shocking-scorecard-for
Are you over 18 and want to see adult content?

A complete backup of www.chinatimes.com/realtimenews/20200208003307-260405
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://universal-robots.com
Are you over 18 and want to see adult content?

A complete backup of https://jonathabrooke.com
Are you over 18 and want to see adult content?

A complete backup of https://soroptimist.nl
Are you over 18 and want to see adult content?

A complete backup of https://travian.fr
Are you over 18 and want to see adult content?
A complete backup of https://robman.info
Are you over 18 and want to see adult content?
A complete backup of https://vikiwat.com
Are you over 18 and want to see adult content?
A complete backup of https://apparentlyapparel.com
Are you over 18 and want to see adult content?
A complete backup of https://kettwig.de
Are you over 18 and want to see adult content?
A complete backup of https://mhsrv.com
Are you over 18 and want to see adult content?

A complete backup of https://redpepper.org.uk
Are you over 18 and want to see adult content?
A complete backup of https://hip-hop.ru
Are you over 18 and want to see adult content?
Text
LIVE HACKING
January 28, 2015. (LiveHacking.Com) – Following Google’s disclose of a number of zero day vulnerabilities in OS X, Apple has released a huge set of patches that fix a range of Critical security problems on OS X, iOS, Apple TV, and Safari. Starting with OS X, Apple’s patches fix 54 separate CVEs including 11 from Google’s Project Zero.TRAINING VIDEOS
Training Videos. The Live Hacking educational videos are a dedicated resource for those wanting to learn about the tools and utilities used by criminal hackers as the first step in preparing to defeat them. These tutorial videos cover a wide range of ethical hacking topics and tools from network fingerprinting to password and packet sniffing. DOWNLOAD LIVE HACKING ISO IMAGES —–—– Live Hacking DVD and Live Hacking CD are Linux live distribution focused on penetration testing and ethical hacking. LIVE HACKING DVD APPLICATION LIST Application List. —–—–. The Live Hacking DVD is packed with tools and utilities for ethical hacking, penetration testing and countermeasure verification. The DVD includes hacking tools for DNS, reconnaissance, foot-printing (gathering information about computerson the network
LIVE HACKING LINUX DVD The Live Hacking DVD is designed for ethical computer hacking, meaning that it contains the tools and utilities you need to test and hack your own network but using the tools and techniques that more malicious hackers would use. The Live Hacking DVD is based on open source technology and uses the popular Ubuntu Linux distribution asits base.
DSNIFF | LIVE HACKING Dsniff is a collection of tools for network auditing and penetration testing. dsniff, filesnarf, mailsnarf, msgsnarf, urlsnarf, and webspy passively monitor a network for interesting data (passwords, e-mail, files, etc.). arpspoof, dnsspoof, and macof facilitate the interception of network traffic normally unavailable to an attacker (e.g, due to layer-2 switching). sshmitm and webmitmETHICAL HACKING
August 30, 2011 by Ethical Hacker. ( LiveHacking.Com) – Crowdsourcing, a term first used back in 2006, has proved a popular way to outsource tasks to large groups or communities (i.e. “the crowd”), where small actions by large numbers can achieve quick results. This idea has now been adopted in the area of penetrationtesting.
TCPREPLAY | LIVE HACKING TCPreplay. Tcpreplay is a suite of BSD licensed tools written by Aaron Turner for UNIX (and Win32 under Cygwin) operating systems which gives you the ability to use previously captured traffic in libpcap format to test a variety of network devices. It allows you to classify traffic as client or server, rewrite Layer 2, 3 and 4 headers and THE TOP NINE BEST PRACTICES FOR NETWORK SCANNING Follow these nine best practices for network scanning, and you’ll get the best bang for your buck out of your network scanner. 1. Update regularly. Generating general network reports (Source: gfi.com) A network scanner helps you to find when your systems are out of date, and with new vulnerabilities discovered regularly, it is critical that THE DIFFERENCE BETWEEN AN EXPOIT AND VULNERABILITY Exploiting is the act of trying to turn a vulnerability (a weakness) into an actual way to breach a system. A vulnerability can therefore be ‘exploited’ to turn it into viable method to attack a system. In software (rather than whole systems including the people, the computers, the firewalls and the networks etc), the most common typeof
LIVE HACKING
January 28, 2015. (LiveHacking.Com) – Following Google’s disclose of a number of zero day vulnerabilities in OS X, Apple has released a huge set of patches that fix a range of Critical security problems on OS X, iOS, Apple TV, and Safari. Starting with OS X, Apple’s patches fix 54 separate CVEs including 11 from Google’s Project Zero.TRAINING VIDEOS
Training Videos. The Live Hacking educational videos are a dedicated resource for those wanting to learn about the tools and utilities used by criminal hackers as the first step in preparing to defeat them. These tutorial videos cover a wide range of ethical hacking topics and tools from network fingerprinting to password and packet sniffing. DOWNLOAD LIVE HACKING ISO IMAGES —–—– Live Hacking DVD and Live Hacking CD are Linux live distribution focused on penetration testing and ethical hacking. LIVE HACKING DVD APPLICATION LIST Application List. —–—–. The Live Hacking DVD is packed with tools and utilities for ethical hacking, penetration testing and countermeasure verification. The DVD includes hacking tools for DNS, reconnaissance, foot-printing (gathering information about computerson the network
LIVE HACKING LINUX DVD The Live Hacking DVD is designed for ethical computer hacking, meaning that it contains the tools and utilities you need to test and hack your own network but using the tools and techniques that more malicious hackers would use. The Live Hacking DVD is based on open source technology and uses the popular Ubuntu Linux distribution asits base.
DSNIFF | LIVE HACKING Dsniff is a collection of tools for network auditing and penetration testing. dsniff, filesnarf, mailsnarf, msgsnarf, urlsnarf, and webspy passively monitor a network for interesting data (passwords, e-mail, files, etc.). arpspoof, dnsspoof, and macof facilitate the interception of network traffic normally unavailable to an attacker (e.g, due to layer-2 switching). sshmitm and webmitmETHICAL HACKING
August 30, 2011 by Ethical Hacker. ( LiveHacking.Com) – Crowdsourcing, a term first used back in 2006, has proved a popular way to outsource tasks to large groups or communities (i.e. “the crowd”), where small actions by large numbers can achieve quick results. This idea has now been adopted in the area of penetrationtesting.
TCPREPLAY | LIVE HACKING TCPreplay. Tcpreplay is a suite of BSD licensed tools written by Aaron Turner for UNIX (and Win32 under Cygwin) operating systems which gives you the ability to use previously captured traffic in libpcap format to test a variety of network devices. It allows you to classify traffic as client or server, rewrite Layer 2, 3 and 4 headers and THE TOP NINE BEST PRACTICES FOR NETWORK SCANNING Follow these nine best practices for network scanning, and you’ll get the best bang for your buck out of your network scanner. 1. Update regularly. Generating general network reports (Source: gfi.com) A network scanner helps you to find when your systems are out of date, and with new vulnerabilities discovered regularly, it is critical that THE DIFFERENCE BETWEEN AN EXPOIT AND VULNERABILITY Exploiting is the act of trying to turn a vulnerability (a weakness) into an actual way to breach a system. A vulnerability can therefore be ‘exploited’ to turn it into viable method to attack a system. In software (rather than whole systems including the people, the computers, the firewalls and the networks etc), the most common typeof
LIVE HACKING LINUX DVD The Live Hacking DVD is designed for ethical computer hacking, meaning that it contains the tools and utilities you need to test and hack your own network but using the tools and techniques that more malicious hackers would use. The Live Hacking DVD is based on open source technology and uses the popular Ubuntu Linux distribution asits base.
TOOLS | LIVE HACKING November 23, 2015 by Live Hacking. Nmap project released Nmap 7 after three years and half development. The new version of Nmap had more 100 contributors and 3,200 code commits since Nmap 6. The new version has 171 Nmap Scripting Engine (NSE) and supports fully IPv6 from host discovery to port scanning to OS detection. TUTORIALS | LIVE HACKING March 26, 2012 by GFI Software. ( LiveHacking.com) – A vulnerability scanner is an essential tool for any systems administrator. Vulnerabilities on your network and in your software can easily lead to compromised systems. There is a false impression that it requires a lot of skill to compromise a computer system.P0F | LIVE HACKING
P0f. P0f is an advanced passive OS/network fingerprinting utility for use in IDS environments, honeypots environments, firewalls and servers in addition to penetration test and ethical hacking. TCPREPLAY | LIVE HACKING TCPreplay. Tcpreplay is a suite of BSD licensed tools written by Aaron Turner for UNIX (and Win32 under Cygwin) operating systems which gives you the ability to use previously captured traffic in libpcap format to test a variety of network devices. It allows you to classify traffic as client or server, rewrite Layer 2, 3 and 4 headers and SSLDUMP | LIVE HACKING SSLdump is an SSLv3/TLS network protocol analyzer. It identifies TCP connections on the chosen network interface and attempts to interpret them as SSLv3/TLS traffic. DHCPDUMP | LIVE HACKING DHCPdump: It parse DHCP packets from tcpdump.This package provides a tool for visualization of DHCP packets as recorded and output by tcpdump to analyze DHCP serverADOBE FLASH PLAYER
It has been a rough week for Internet Explorer. Over the weekend Microsoft released Security Advisory 2963983 about a zero-day exploit in IE which is being used in the wild. Then yesterday Adobe released an emergency security update to fix a critical flaw in its Flash Player.As a result of Adobe’s patch, Microsoft has also updated the version of Adobe Flash Player built-in to InternetVULNERABILITY
(LiveHacking.Com) – The well known credit card company American Express has fixed an SQL injection security vulnerability on its web site that allowed direct access to the server’s database.THUNDERBIRD
February 20, 2012 by Ethical Hacker. ( LiveHacking.Com) – Less then 7 days after the release of Firefox 10.0.1, Mozilla has now released a new version of Firefox (10.0.2) and Thunderbird (also 10.0.2) to fix a Critical libpng integer overflow vulnerability. The bug, which affects Firefox, Thunderbird, SeaMonkey, is an integer overflow in theLIVE HACKING
January 28, 2015. (LiveHacking.Com) – Following Google’s disclose of a number of zero day vulnerabilities in OS X, Apple has released a huge set of patches that fix a range of Critical security problems on OS X, iOS, Apple TV, and Safari. Starting with OS X, Apple’s patches fix 54 separate CVEs including 11 from Google’s Project Zero.TRAINING VIDEOS
Training Videos. The Live Hacking educational videos are a dedicated resource for those wanting to learn about the tools and utilities used by criminal hackers as the first step in preparing to defeat them. These tutorial videos cover a wide range of ethical hacking topics and tools from network fingerprinting to password and packet sniffing. LIVE HACKING DVD APPLICATION LIST Application List. —–—–. The Live Hacking DVD is packed with tools and utilities for ethical hacking, penetration testing and countermeasure verification. The DVD includes hacking tools for DNS, reconnaissance, foot-printing (gathering information about computerson the network
DOWNLOAD LIVE HACKING ISO IMAGES —–—– Live Hacking DVD and Live Hacking CD are Linux live distribution focused on penetration testing and ethical hacking. DSNIFF | LIVE HACKING Dsniff is a collection of tools for network auditing and penetration testing. dsniff, filesnarf, mailsnarf, msgsnarf, urlsnarf, and webspy passively monitor a network for interesting data (passwords, e-mail, files, etc.). arpspoof, dnsspoof, and macof facilitate the interception of network traffic normally unavailable to an attacker (e.g, due to layer-2 switching). sshmitm and webmitmETHICAL HACKING
August 30, 2011 by Ethical Hacker. ( LiveHacking.Com) – Crowdsourcing, a term first used back in 2006, has proved a popular way to outsource tasks to large groups or communities (i.e. “the crowd”), where small actions by large numbers can achieve quick results. This idea has now been adopted in the area of penetrationtesting.
P0F | LIVE HACKING
P0f. P0f is an advanced passive OS/network fingerprinting utility for use in IDS environments, honeypots environments, firewalls and servers in addition to penetration test and ethical hacking. MICROSOFT | LIVE HACKING September 21, 2012 by Ethical Hacker. ( LiveHacking.Com) – Microsoft has announced that it will release an out-of-band update to Internet Explorer to fix the recently found zero-day vulnerability that affects IE 6, 7, 8 and 9. The flaw was discovered by Eric Romang, a security researcher, who was monitoring some servers suspected of serving DHCPDUMP | LIVE HACKING DHCPdump: It parse DHCP packets from tcpdump.This package provides a tool for visualization of DHCP packets as recorded and output by tcpdump to analyze DHCP server THE DIFFERENCE BETWEEN AN EXPOIT AND VULNERABILITY Exploiting is the act of trying to turn a vulnerability (a weakness) into an actual way to breach a system. A vulnerability can therefore be ‘exploited’ to turn it into viable method to attack a system. In software (rather than whole systems including the people, the computers, the firewalls and the networks etc), the most common typeof
LIVE HACKING
January 28, 2015. (LiveHacking.Com) – Following Google’s disclose of a number of zero day vulnerabilities in OS X, Apple has released a huge set of patches that fix a range of Critical security problems on OS X, iOS, Apple TV, and Safari. Starting with OS X, Apple’s patches fix 54 separate CVEs including 11 from Google’s Project Zero.TRAINING VIDEOS
Training Videos. The Live Hacking educational videos are a dedicated resource for those wanting to learn about the tools and utilities used by criminal hackers as the first step in preparing to defeat them. These tutorial videos cover a wide range of ethical hacking topics and tools from network fingerprinting to password and packet sniffing. LIVE HACKING DVD APPLICATION LIST Application List. —–—–. The Live Hacking DVD is packed with tools and utilities for ethical hacking, penetration testing and countermeasure verification. The DVD includes hacking tools for DNS, reconnaissance, foot-printing (gathering information about computerson the network
DOWNLOAD LIVE HACKING ISO IMAGES —–—– Live Hacking DVD and Live Hacking CD are Linux live distribution focused on penetration testing and ethical hacking. DSNIFF | LIVE HACKING Dsniff is a collection of tools for network auditing and penetration testing. dsniff, filesnarf, mailsnarf, msgsnarf, urlsnarf, and webspy passively monitor a network for interesting data (passwords, e-mail, files, etc.). arpspoof, dnsspoof, and macof facilitate the interception of network traffic normally unavailable to an attacker (e.g, due to layer-2 switching). sshmitm and webmitmETHICAL HACKING
August 30, 2011 by Ethical Hacker. ( LiveHacking.Com) – Crowdsourcing, a term first used back in 2006, has proved a popular way to outsource tasks to large groups or communities (i.e. “the crowd”), where small actions by large numbers can achieve quick results. This idea has now been adopted in the area of penetrationtesting.
P0F | LIVE HACKING
P0f. P0f is an advanced passive OS/network fingerprinting utility for use in IDS environments, honeypots environments, firewalls and servers in addition to penetration test and ethical hacking. MICROSOFT | LIVE HACKING September 21, 2012 by Ethical Hacker. ( LiveHacking.Com) – Microsoft has announced that it will release an out-of-band update to Internet Explorer to fix the recently found zero-day vulnerability that affects IE 6, 7, 8 and 9. The flaw was discovered by Eric Romang, a security researcher, who was monitoring some servers suspected of serving DHCPDUMP | LIVE HACKING DHCPdump: It parse DHCP packets from tcpdump.This package provides a tool for visualization of DHCP packets as recorded and output by tcpdump to analyze DHCP server THE DIFFERENCE BETWEEN AN EXPOIT AND VULNERABILITY Exploiting is the act of trying to turn a vulnerability (a weakness) into an actual way to breach a system. A vulnerability can therefore be ‘exploited’ to turn it into viable method to attack a system. In software (rather than whole systems including the people, the computers, the firewalls and the networks etc), the most common typeof
MALWARE | LIVE HACKING June 3, 2014 by Ethical Hacker. ( LiveHacking.Com) – A multi-national team of security experts and law enforcement agencies including the U.S. Department of Justice, the FBI, Europol, and the UK’s National Cyber Crime Unit have successfully disrupted the GameOver Zeus botnet. The malware, which is a peer-to-peer (P2P)variant of the Zeus
ANTIVIRUS | LIVE HACKING (LiveHacking.com) — The Department of Homeland Security, which was created in response to the September 11 attacks and is tasked with protecting the USA from terrorist attacks, has awarded McAfee (which is a wholly owned subsidiary of Intel) a multi-year Enterprise Level Agreement contract with a potential value of up to $12 million. SSLDUMP | LIVE HACKING SSLdump is an SSLv3/TLS network protocol analyzer. It identifies TCP connections on the chosen network interface and attempts to interpret them as SSLv3/TLS traffic. TCPREPLAY | LIVE HACKING TCPreplay. Tcpreplay is a suite of BSD licensed tools written by Aaron Turner for UNIX (and Win32 under Cygwin) operating systems which gives you the ability to use previously captured traffic in libpcap format to test a variety of network devices. It allows you to classify traffic as client or server, rewrite Layer 2, 3 and 4 headers andSECURITY BREACH
According to Bloomberg, Target had invested $1.6 million installing a malware detection tool from FireEye. Target used a team of security specialists in Bangalore to monitor its network. On Saturday, Nov. 30, the hackers uploaded malware to Target’s network so that they could copy the stolen credit card details. LINUX | LIVE HACKING August 7, 2012 by Ethical Hacker. ( LiveHacking.com) — Over a month ago an anonymous coder sent a small C program to Dave Airlie, who maintains the Direct Rendering Manager (DRM) subsystem in the Linux kernel, that allows an attacker to gain root access to a Linux machine by exploiting a vulnerability in NVIDIA’s Linux drivers.JANUARY 2012
(LiveHacking.Com) – In the on going saga about source code stolen from Symantec in 2006, the company has now updated its “Claims by Anonymous about Symantec Source Code” to notify its customers that “all pcAnywhere 12.0, 12.1 and 12.5 customers are at increased risk” and to “recommends that customers only use pcAnywhere forbusiness
FEBRUARY 2015
(LiveHacking.Com) – A new Cross Site Scripting (XSS) vulnerability has been found in IE 11. According to an email sent by David Leo, a researcher with information security company Deusen, to the Full Disclosure mailing list, the vulnerability can allow an attacker to steal anything from a third party domain, and likewise inject anything into a third party domain. MAY 2011 | LIVE HACKING Lockheed Martin, the US defense contractor and manufacturer of a variety of military products including the Trident missile and F-16, has acknowledged that its IT systems came under “a significant and tenacious attack” last week, but that due to the fast work of its security team it was able to protect all systems and data. MAY 2013 | LIVE HACKING (LiveHacking.Com) – Less than a week ago Microsoft revealed that version 8 of its web browser Internet Explorer suffers from a nasty remote code execution vulnerability that could catch users if they mistakenly follow a link, in an email or instant message, to amalicious website.
May 17, 2020
* TERMS OF SERVICE
* Privacy Policy
* Disclaimer
* Contact
LIVE HACKING
Ethical Hacking | Penetration Testing* Home
* Bookshelf
* Security Bulletins * Training Videos »* Amap
* DHCPdump
* DNSmap
* Dsniff
* Fping
* Hping
* John the Ripper
* Metoscan
* Nmap
* P0f
* SING
* SSLdump
* TCPdump
* TCPreplay
* Wireshark
* Live Hacking DVD » * About Live Hacking Distro.* Application List
* Download Live Hacking* DVD Label
* Tools
* Tutorials
* Vulnerabilities »* Linux
* Microsoft
* MySql
* OpenBSD
* OpenSC
* OpenSSL
* PlayStation3
* Safari
* SAP
* Thunderbird
* WordPress
* Wep Application
* Wire-less
* SeaMonkey
* SQL Injection
* WebOS
* Adobe
* Apple
* Attacks
* Antivirus
* Cryptography
* Ethical Hacking
* Microsoft
* Malware
* Security
* Linux
You are here: Home / Archives forAndroid
MANY ANDROID APPS OPEN TO MAN-IN-THE-MIDDLE ATTACKS DUE TO WEAK SSLUSAGE
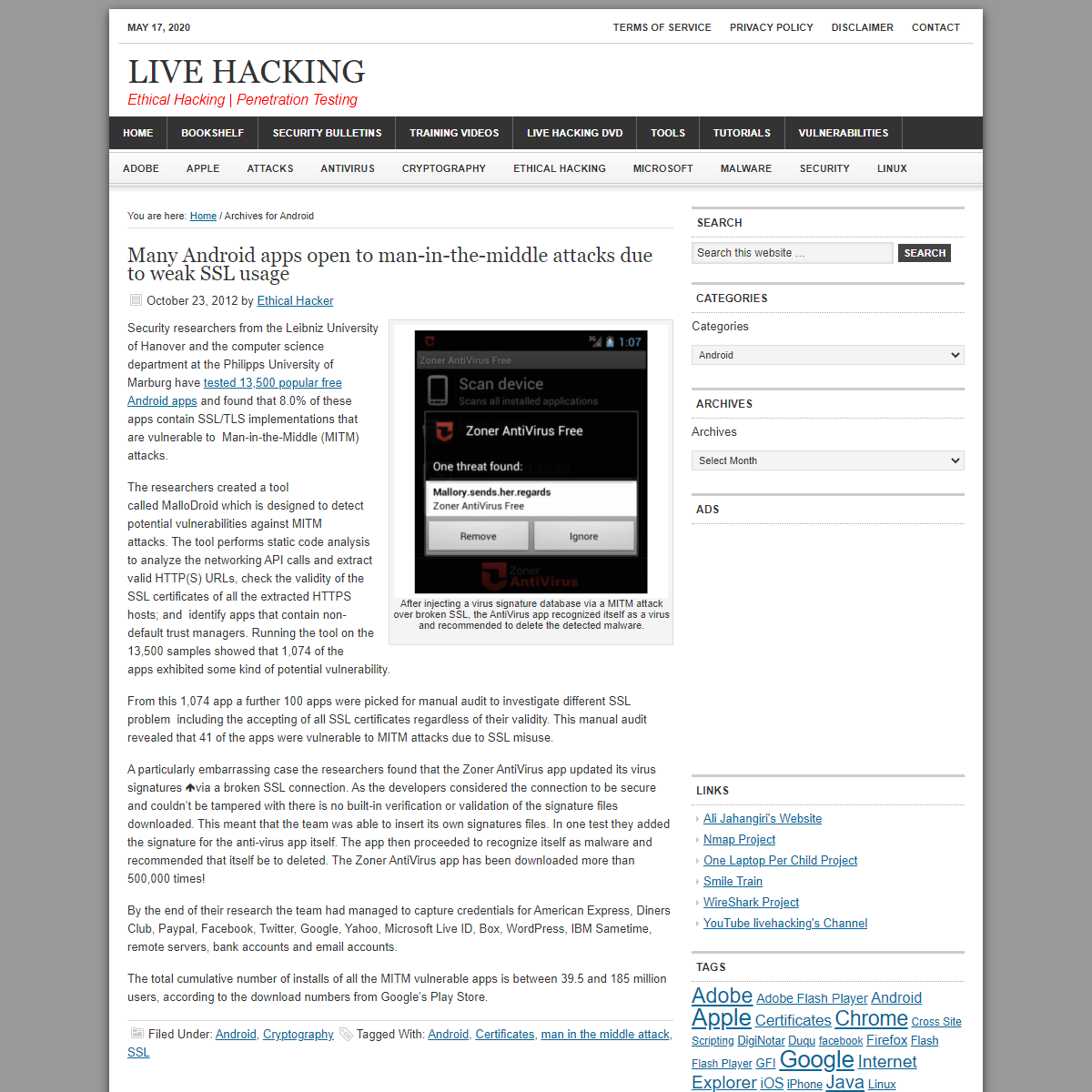
October 23, 2012 by Ethical Hacker After injecting a virus signature database via a MITM attack over broken SSL, the AntiVirus app recognized itself as a virus and recommended to delete the detected malware. Security researchers from the Leibniz University of Hanover and the computer science department at the Philipps University of Marburg have tested 13,500 popular free Android appsand
found that 8.0% of these apps contain SSL/TLS implementations that are vulnerable to Man-in-the-Middle (MITM) attacks. The researchers created a tool called MalloDroid which is designed to detect potential vulnerabilities against MITM attacks. The tool performs static code analysis to analyze the networking API calls and extract valid HTTP(S) URLs, check the validity of the SSL certificates of all the extracted HTTPS hosts; and identify apps that contain non-default trust managers. Running the tool on the 13,500 samples showed that 1,074 of the apps exhibited some kind of potential vulnerability. From this 1,074 app a further 100 apps were picked for manual audit to investigate different SSL problem including the accepting of all SSL certificates regardless of their validity. This manual audit revealed that 41 of the apps were vulnerable to MITM attacks due toSSL misuse.
A particularly embarrassing case the researchers found that the Zoner AntiVirus app updated its virus signatures via a broken SSL connection. As the developers considered the connection to be secure and couldn’t be tampered with there is no built-in verification or validation of the signature files downloaded. This meant that the team was able to insert its own signatures files. In one test they added the signature for the anti-virus app itself. The app then proceeded to recognize itself as malware and recommended that itself be to deleted. The Zoner AntiVirus app has been downloaded more than 500,000 times! By the end of their research the team had managed to capture credentials for American Express, Diners Club, Paypal, Facebook, Twitter, Google, Yahoo, Microsoft Live ID, Box, WordPress, IBM Sametime, remote servers, bank accounts and email accounts. The total cumulative number of installs of all the MITM vulnerable apps is between 39.5 and 185 million users, according to the download numbers from Google’s Play Store. Filed Under: Android ,Cryptography
Tagged With: Android , Certificates , man inthe middle attack
, SSL
WEBKIT VULNERABILITY ALLOWS ATTACKERS TO TAKE CONTROL OF ANDROIDDEVICES
February 27, 2012 by Ethical Hacker(LiveHacking.Com
) – CrowdStrike, a new security technology company formed by key cyber security executives from McAfee, will demonstrate a new WebKit based attack against Google Android which results in the attacker gaining access to critical system processes and taking complete control of the victim’s device. The firm plans the demo as part of its debut at the RSA Conference2012.
To launch the attack a hacker sends an email or text message that tricks the recipient (via social engineering) to click on a link, which in turn infects the device. At this point, the hacker gains complete control of the phone, enabling him to eavesdrop on phone calls and monitor the location of the device. Since WebKit is also used in Google Chrome, Research in Motion’s BlackBerry, Apple’s Safari web browser and Apple’s iOS devices, this could open up exploits across multiple platforms. > “With modifications and perhaps use of different exploits, this > attack will work on every smartphone device and represents the > biggest security threat on those devices,” said Dmitri > Alperovitch, chief technology officer and co-founder of CrowdStrike. The CrowdStrike exploit only works on Android 2.2 (Froyo) but Alperovitch said he expects to have a second version of the hack soon that can attack phones running Android 2.3 (Gingerbread, which runs on about 59% of all Android devices). The consequences of such a vulnerability are enormous as once the hole is patched in the WebKit project it can take months for the fix to trickle down to actual devices. Worse still many handset manufacturers NEVER update the firmware on older phones meaning that some Android 2.2 users will be left with a vulnerable phone with no possibility of a fix other than resorting to custom ROM images. Filed Under: Android ,Android
,
Google , VulnerabilityTagged With:
Android , CrowdStrike, WebKit
MCAFEE SAYS MALWARE SURPASSED 75 MILLION SAMPLES IN 2011 February 22, 2012 by Ethical Hacker(LiveHacking.Com
) – McAfee has released its Q4 2011Threat Report
(a PDF) and it shows that last year McAfee collected over 75 million unique malware samples! It also shows that 2011 was by far the busiest periods for mobile malware with Android the number one target for writers of mobile malware. The most common type of Android malware is the for-profit SMS-sending Trojans, which earn cyber-criminals significant amounts of money by sending messages to premium services. The rooting Android devices is getting easier and easier and there are now apps which combine vulnerability exploits to root phones with the click of a button. However the downside of this is that malware writers can repackage the very same root exploits apps with malware. There is a sliver of good news in that the overall growth of PC malware is on the decline and is much lower that this time last year. The report also noted a continued decline in Fake AV malware with AutoRun and password-stealing Trojan malware showing only slight declines. However the context of this is that McAfee’s cumulative number of unique malware samples exceeded the 75 million samples. In Q4 2011, the most common type of remote attack was via vulnerabilities in Microsoft Windows remote procedure calls. This was followed by a very close race between SQL-injection and cross-site scripting attacks. The result is that the number of reported data breaches has more than doubled since 2009 with more than 40 breaches publicly reported in Q4 alone. “Although the release of new malware slowed a bit in Q4, mobile malware continued to increase and recorded its busiest year to date,” Dave Marcus, Director, Security Research at McAfee said in ablog post
.
Filed Under: Android ,Antivirus , Malware
Tagged With: Android, Malware
, McAfee
DDOS ATTACK TOOL COMES TO ANDROID February 21, 2012 by Ethical Hacker(LiveHacking.Com
) – McAfree has reportedthat
the common Low Orbit Ion Cannon (LOIC) denial of service (DoS) tool has been ported to Android. ‘Ported’ might be too strong of a word as this mobile device version is in fact a wrapper around the Javascript version. Nonetheless, this is an interesting advancement in the ubiquity of hacking tools. Hacktivism (hacking as political or social protest) is becoming increasingly popular with groups like Anonymous using hacking tools to launch distributed denial of service attacks on organizations all over the world. LOIC , one such tool used by the hackers, was originally developed to stress-test websites, however it has now been effectively used by hackers to take websites offline by sending a flood of TCP/UDP packets which overwhelms the server and makes it inaccessible. Originally written in C#, LOIC inspired the creation of an independent JavaScript version. This version allowed a DoS attacked to be launched from a web browser. In conjunction with PasteHTML, which allows anyone to post HTML onto the web anonymously (no pun intended), and the free AppsGeyser service, which converts web pages into an App, an Android App has been created which encapsulates the Javascript version of LOIC in an Android app. Specifically, the version spotted by McAfee, targets the Argentinian government, but theoretically an Android app can be created to attack any web site. When the app is launched a WebView component is used to run the JavaScript that sends 1,000 HTTP requests with the message “We are LEGION!” as one of theparameters.
> “Creating Android applications that perform DoS attacks is now > easy: It requires only the URL of an active web LOIC–and zero > programming skills–thanks to automated online tools,” wrote > Carlos Castillo for McAfee. Filed Under: Android ,Attack , Attacks
Tagged With: Android, Anonymous
, DDOS
, DoS
, LOIC
, McAfee
GOOGLE’S BOUNCER TO TRY AND KEEP MALWARE OUT OF THE ANDROID MARKET February 6, 2012 by Ethical Hacker(LiveHacking.Com
) – One of the weakest aspects to Google’ Android eco system is that it is far too easy for hackers to submit apps which contain malware. Until now Google seemed to largely ignore the issue and only removed malicious apps if someone complained. However that could all be changing. Google has announced a new service codenamed Bouncer, which scans the Android Market for potentially malicious apps without requiring developers to go through an Apple-like application approval process. The Bouncer does two things. First it performs a set of analyses on newly submitted apps (as well as on applications already in Android Market), and secondly it keeps an eye on developer accounts to help prevent malicious and repeat-offending developers from coming back. Once an application is uploaded, the Bouncer starts analyzing it for known malware, spyware and trojans. It also looks for behaviors that indicate an application might be misbehaving, and compares it against previously analyzed apps to detect possible red flags. To do this Google run every application in a simulator to see how it will run on an Android device to look for hidden, malicious behavior. It seems that the Bouncer has been running for at least the last six months as Google reporting that between the first and second halves of 2011, it saw a 40% decrease in the number of potentially-malicious downloads from Android Market. > “No security approach is foolproof, and added scrutiny can often > lead to important improvements. Our systems are getting better at > detecting and eliminating malware every day, and we continue to > invite the community to work with us to keep Android safe.” said> Google.
Filed Under: Android ,Google , Malware
Tagged With: Android, Bouncer
, Malware
NSA MAKE AN INITIAL PUBLIC RELEASE OF SECURITY ENHANCED ANDROID January 17, 2012 by Ethical Hacker (LiveHacking.Com ) –The
National Security Agency, part of the United States Department of Defense which is responsible for the interception and decryption of foreign communications, has made an initial public releaseof Security
Enhanced (SE) Android, a special version of the Linux based mobile device operating system created to identify and address critical gapsin its security.
The initial aim of the SE Android is to implement the SELinux access control policies, including the Mandatory Access Control (MAC) system. MAC defines and enforces a system-wide security policy which controls all processes, objects, and operations. This means that MAC can confine flawed and malicious applications, even ones that run as “root”, and can prevent privilege escalation. As well as SELinux for Android, SE Android offer the following uniquefeatures:
* Per-file security labeling support for yaffs2 * Filesystem images (yaffs2 and ext4) labeled at build time * Kernel permission checks controlling Binder IPC * Labeling of service sockets and socket files created by init * Labeling of device nodes created by ueventd * Flexible, configurable labeling of apps and app data directories * Userspace permission checks controlling use of the Zygote socketcommands
* Minimal port of SELinux userspace * Small TE policy written from scratch for Android * Confined domains for system services and apps * Use of MLS categories to isolate apps As part a presentation (PDF)
given at the 2011 Linux Security Summit, Stephen Smalley of the NSA explained how with SELinux incorporated into Android the “Gingerbreak” vulnerability, which exploited a problem in the Android volume daemon ‘vold’, would have stopped the exploit six different ways and make the underlying vulnerability completelyunreachable.
More details about SE Android including build instructions can be found on the project’s wiki.
Filed Under: Android ,Linux , Open Source
, Security
Tagged With: NationalSecurity Agency
, NSA
, SE Android
, SELinux
GOOGLE REMOVES 22 DANGEROUS APPS FROM ANDROID MARKET December 13, 2011 by Ethical Hacker(LiveHacking.Com
) – Over the past week Google has removed 22 malicious apps from its official Android Marketplace again highlighting the weakness of Google’s (almost non-existant) approval process. The malicious apps were spotted by the mobile security company Lookout who then notified Google. In response Google removed the apps. The apps all used the RuFraud malware to send SMS messages to premium rate numbers. The apps didn’t affect users in the USA, but it did target users in Great Britain, Italy, Israel, France, and Germany as well as Russia, Azerbaijan, Armenia, Georgia, Czech Republic, Poland, Kazakhstan, Belarus, Latvia, Kyrgyzstan, Tajikistan, Ukraine andEstonia.
The initial batch of apps that Google posted in the Android Market place appeared as horoscope apps with an unclear ToS pointing out the charges. Once the app started, tapping on “Continue” meant the user accepted the terms. Next come apps designed to capture a wider audience: 3 wallpaper apps for popular movies (including Twilight), and 3 apps claiming to be downloaders for popular games such as Angry Birds and Cut the Rope. The final wave of apps again masqueraded as free versions of popular games. In total 22 apps appeared in the Android Market and were downloaded over 14,000 times. Do the maths. That is a very quick way to make some money and Google helped by not having a decent app reviewprocess.
Filed Under: Android , Google Tagged With: Android , Android Market, RuFraud
BITDEFENDER RELEASES CARRIER IQ FINDER FOR ANDROID December 6, 2011 by Ethical Hacker(LiveHacking.Com
) – Carrier IQ
has been very much in the headlines this week with accusations, rebuttals and counter accusations over privacy deficiencies in Carrier IQ’s mobile phone diagnostic system. The system is shipped by default on a number of Android based mobile devices. Although designed “just” to help carriers improve their networks there are concerns that the software is tracking and recording morethan it should.
As a result Bitdefender have created a new tool that identifies the presence of the controversial mobile network diagnostic tool. > “Bitdefender values users’ privacy and their right to take > informed decisions when entering a deal with a mobile carrier,” > said Alexandru Balan, senior Product Manager of the Bitdefender > Mobile Unit. “Although the manufacturer claims that only some of > the information provided through the Carrier IQ application is used > by the carrier, the amount of personal data the app has access to > raises serious privacy concerns.” Unfortunately the Bitdefender tool isn’t able to disable or uninstall the Carrer IQ app as it is deeply buried in the devicefirmware.
The application can be freely downloaded via the Android Market here.
Filed Under: Android , News Tagged With: Android, Bitdefender
, Carrier IQ
CARRIER IQ FIGHTS BACK – SAYS IT ISN’T SNOOPING December 2, 2011 by Ethical Hacker(LiveHacking.Com
) – Carrier IQ hit back at allegations made by security researcher Trevor Eckhart that their Android app is recording and forwarding all kinds of personal information. The company has issued another press release to “clarify” what its app does and one of the company’s VPs has been speaking to AllThingsD.
In the press release Carrier IQ states that its app: * Measures and summarizes performance of a device to assist Operators in delivering better service. * Does NOT record, store or transmit the contents of SMS messages, email, photographs, audio or video. * Operates exclusively within that framework and under the laws of the applicable jurisdiction. Any data gathered is transmitted over anencrypted channel.
In the interview with AllThingD, Andrew Coward, Carrier IQ’s VP of marketing, says that the app receives a huge amount of information from the operating system. But just because it receives it doesn’t mean that it’s being used to gather intelligence about the user or is passed along to the carrier: * “What the Eckhart video demonstrates is that there’s a great deal of information available on a handset,” says Coward. “What it doesn’t show is that all information is processed, stored, or forwarded out of the device.” * “If there’s a dropped call, the carriers want to know about it,” says Coward. “So we record where you were when the call dropped, and the location of the tower being used. … Similarly, if you send an SMS to me and it doesn’t go through, the carriers want to know that, too. And they want to know why — if it’s a problem with your handset or the network.” * “We don’t read SMS messages. We see them come in. We see the phone numbers attached to them. But we are not storing, analyzing or otherwise processing the contents of those messages.” * “It’s the operator that determines what data is collected,” says Carrier IQ CEO Larry Lenhart. “They make that decision based on their privacy standards and their agreement with their users, and weimplement it.”
* “What’s actually gathered, stored and transmitted to the carrier is determined by its end-user agreement,” he says. “And, as I’m sure you’re aware, the carriers are highly sensitive about what data they’re allowed to capture and what they’re not allowedto capture.”
Filed Under: Android , News Tagged With: Android, Carrier IQ
, Trevor Eckhart
ANDROID FLAW ALLOWS APPS TO SEND SMS MESSAGES AND RECORD CALLS WITHOUTPERMISSION
December 1, 2011 by Ethical Hacker(LiveHacking.Com
) – A group of researchers from North Carolina State University have discoveredflaws
in non-vanilla versions of Android which leak permissions or capabilities to other applications. By exploiting these leaked capabilities a 3rd party app can send SMS messages, record calls and even reboot the phone without asking for any permission. Unlike Apple who strictly control their App Store and offer only one source for downloads, Android has multiple app stores and none of them, including the official Google Market, perform any kind of security checks on the apps made available for download. This means that when vulnerabilities are discovered in Android, hackers are free to upload apps to the Android Market which exploit the weaknesses. To combat this, Android uses a permissions model where any app wanting to do something extra (including connecting to the Internet) needs to ask permission from the user. The model is severely flawed as most non-technical people have no idea what these permissions mean and normally just accept them anyway. Michael Grace, Yajin Zhou, Zhi Wang and Xuxian Jiang have discovered that non-vanilla versions of Android come with extra pre-loaded apps and that these bundled apps have access to some permissions that are too privileged to be granted to third-party apps. The team built an app called Woodpecker which scans the pre-loaded apps to see which apps offer a public interface exposing a capability that would normally require permission. They also use another technique to find “implicit capabilities” among apps signed with the same user identifier. The researchers analyzed eight popular Android (2.2 and 2.3 based)smartphones (HTC
Legend, HTC EVO 4G, HTC Wildfire S, Motorola Droid and Droid X, Samsung Epic 4G and the Google Nexus One & Nexus S) and discovered 11 privileged permissions that are “leaked”. One phone, the HTC EVO 4G, leaks eight permissions.In a video
posted on YouTube Michael Grace demonstrates the installation of the Woodpecker app (which required no special permissions) and then how the app was able to record sounds (including phone calls), send an SMS message (which could have been to a premium phone number) and reboot the device without asking. > “The results are worrisome: among the 13 privileged permissions > examined so far, 11 were leaked, with individual phones leaking up > to eight permissions. These leaked capabilities can be exploited to > wipe out the user data, send out SMS messages (e.g., to premium > numbers), record user conversation, or obtain the user’s > geo-location data on the affected phones – all without asking for > any permission” say the report authors. Filed Under: Android ,News , Open Source
Tagged With:
Android , Android Market , Android Permissions, North Carolina
State University
Next Page »
SEARCH
CATEGORIES
Categories Select Category Address Resolution Protocol Adobe Amazon Android Antivirus ClamWin Microsoft Security Essentials Panda Security Apple ATM Attack Attacks Book Botnet Business Application Chrome Cisco Cloud Computing Cryptography Cyber Forensic Data Breach Defcon DNS EC-Council Ethical Hacking Event Facebook Firefox Google HP ICANN IDS IETF India Intelligence Driven Response Intenet Explorer Interception Intrusion Detection System Java Linux Live Hacking Macintosh Malware Microsoft Mozilla News Open Source Penetration Test QuickTime Red Hat Red Hat Enterprise Linux Reverse-Engineering Secure Programming Security Security Report Smartphone Tools Tutorials Uncategorized Video VMware Vulnerability Adobe Android Apache Apple ca Canon Chrome Cisco D-Link Exim Firefox Flash Player GSM Network Linux Microsoft MySql OpenBSD OpenSC OpenSSL PlayStation3 Safari SAP SeaMonkey SQL Injection Thunderbird twitter TYPO3 WebOS Wep Application Wire-less WordPress VxWorks Web Browsers Web Crawler Whitepaper Windows Wireless YouTubeARCHIVES
Archives Select Month November 2015 April 2015 March 2015 February 2015 January 2015 December 2014 November 2014 October 2014 September 2014 August 2014 July 2014 June 2014 May 2014 April 2014 March 2014 February 2014 January 2014 December 2013 November 2013 October 2013 September 2013 August 2013 July 2013 June 2013 May 2013 April 2013 March 2013 February 2013 January 2013 December 2012 November 2012 October 2012 September 2012 August 2012 July 2012 June 2012 May 2012 April 2012 March 2012 February 2012 January 2012 December 2011 November 2011 October 2011 September 2011 August 2011 July 2011 June 2011 May 2011 April 2011 March 2011 February 2011 January 2011 December 2010 November 2010 October 2010 September 2010 August 2010 July 2010 April 2010 March 2010 February 2010 December 2009 November2009
ADS
LINKS
* Ali Jahangiri's Website* Nmap Project
* One Laptop Per Child Project* Smile Train
* WireShark Project
* YouTube livehacking's ChannelTAGS
Adobe Adobe Flash PlayerAndroid
Apple
Certificates
Chrome
Cross Site ScriptingDigiNotar
Duqu
Firefox
Flash
Flash Player
GFI
Internet Explorer
iOS
iPhone
Java
Linux
Malware
Microsoft
Microsoft Windows
Mozilla
Oracle
OS X
Patch Tuesday
Privacy
remote attack
RSA
Safari
Security Breach
Sergey Glazunov
SSL
Stuxnet
Symantec
Trojan
Tutorials
VLC
Vulnerability Scannerwindows
WordPress
XSS
Zero Day
Zero day exploit
WHO'S ONLINE
* 0 Members.
* 7 Guests.
META
* Entries RSS
* Comments RSS
� Copyright 2009 - 2013 LiveHacking.Com � All Rights Reserved · Powered by ArtSec Group LLC�
� Information Security News, Ethical Hacking Training and Tutorials, Penetration Testing Tools and Techniques · All trademarks and copyrights on this page are owned by their respective owners. Unless otherwise stated the contents of this website are licenced under Attribution-NonCommercial-ShareAlike 3.0 Unported (CC BY-NC-SA 3.0).
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0