Are you over 18 and want to see adult content?
More Annotations
A complete backup of https://zittauer-schmalspurbahn.de
Are you over 18 and want to see adult content?
A complete backup of https://neco.gov.ng
Are you over 18 and want to see adult content?
A complete backup of https://ja.wikipedia.org
Are you over 18 and want to see adult content?

A complete backup of https://fbdirectory.in
Are you over 18 and want to see adult content?

A complete backup of https://rakenapp.com
Are you over 18 and want to see adult content?
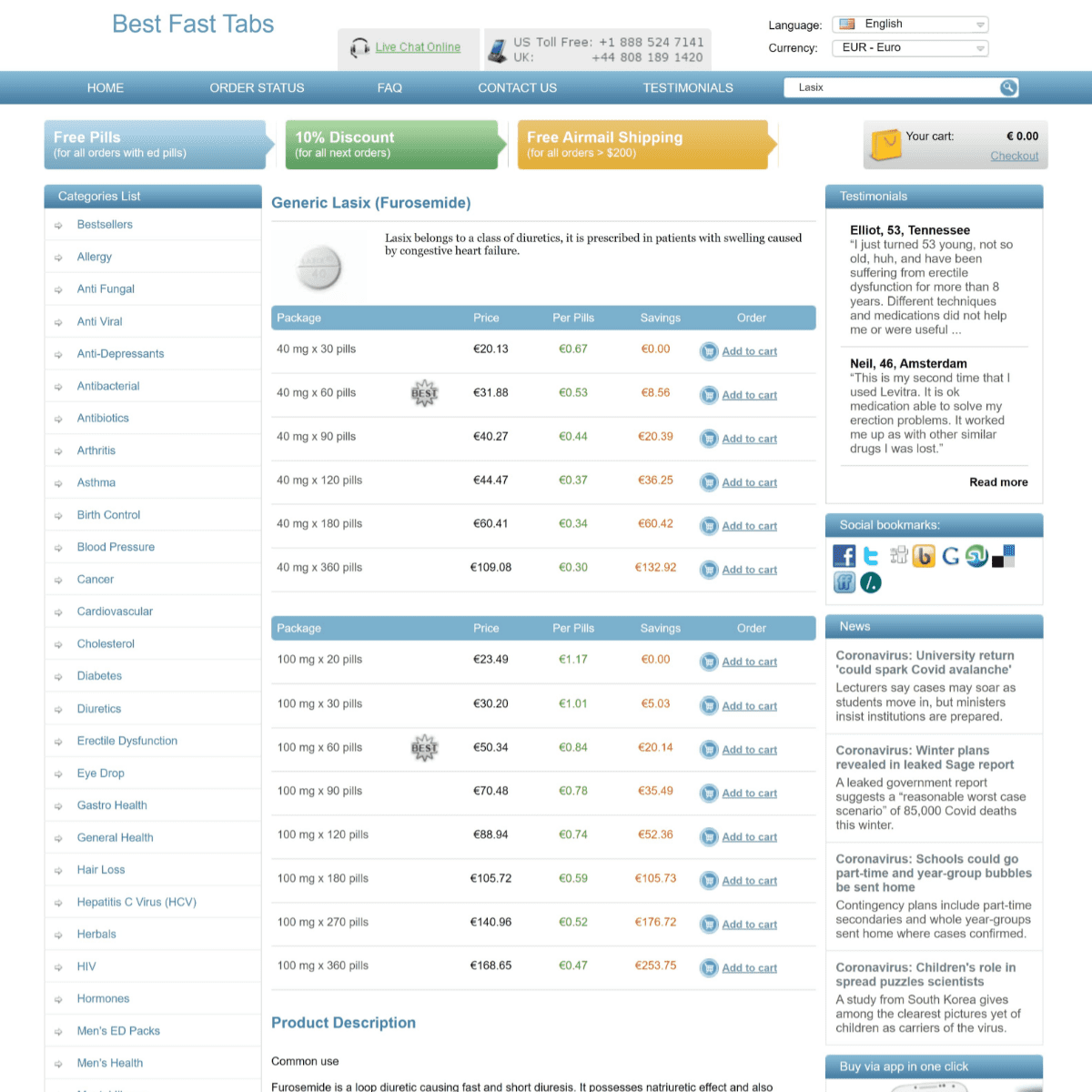
A complete backup of https://lasixa.com
Are you over 18 and want to see adult content?
A complete backup of https://nichbelize.org
Are you over 18 and want to see adult content?

A complete backup of https://badgerinc.com
Are you over 18 and want to see adult content?
A complete backup of https://europeancabinets.com
Are you over 18 and want to see adult content?
A complete backup of https://technologydecisions.com.au
Are you over 18 and want to see adult content?
A complete backup of https://mytec.com.mx
Are you over 18 and want to see adult content?

A complete backup of https://cookilicious.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://swbg-conservationfund.org
Are you over 18 and want to see adult content?

A complete backup of https://librosgratisweb.com
Are you over 18 and want to see adult content?
A complete backup of https://pfizer.fi
Are you over 18 and want to see adult content?
A complete backup of https://makeapullrequest.com
Are you over 18 and want to see adult content?
A complete backup of https://fighter-planes.com
Are you over 18 and want to see adult content?

A complete backup of https://ywcamuskoka.com
Are you over 18 and want to see adult content?
A complete backup of https://instah.com
Are you over 18 and want to see adult content?

A complete backup of https://centerforagroforestry.org
Are you over 18 and want to see adult content?
A complete backup of https://michael-kors.com.es
Are you over 18 and want to see adult content?
A complete backup of https://1000degreespizza.com
Are you over 18 and want to see adult content?
Text
site.
HOW TO IMPLEMENT THE ASD ESSENTIAL 8 VIA GROUP POLICY The Australian Government Department called the Australian Signals Directorate has a list of mitigation strategies that is used to help protect IT system against security risks. This list is called the “ASD Essential 8“. While this its generated by the Australian Government department it is an excellent starting point for securing any organisation or government IT Assets. The really great GROUP POLICY FAQ #2: HOW DO YOU MAP A PRINTER USING GROUP Now to map the printers all you need to do is go to the Printer Extension option of the Group Policy you want to apply the setting from (see below). All you need to do now is put the UNC Path of the printer in the “Shared path:” text field and your done. No more batch files, vbscripts or KIX scripts to edit and maintain for mappingprinters.
HOW TO TROUBLESHOOT APPLOCKER AppLocker is a great new feature that was introduced in Windows 7 that allowed IT Admins to prevent the running of certain application in their corporate environment (e.g. Chrome). However there are a number of steps and pre-requisites for this feature to work that seem to catch people up quite often. So below is a simple troubleshooting flowchart that
HOW TO FIX SEARCHOCS.ADMX ERROR AFTER UPGRADE TO WINDOWS Before I begin this article might be, for some of you, this will be well know information and it might all seem rather logical. But I continue to see questions being asked on forums as how as a Group Policy administrator can I prevent HOW TO REMOVE CPASSWORD VALUES FROM ACTIVE DIRECTORY With the recent MS14-025 security patch Microsoft has removed the ability to configure passwords in Group Policy Preferences via the User Interface. However this update does not remove the password value from AD nor does it stop the value being applied to computers/users. So, if you have apply MS14-025 and you have also implemented another way of managing the local WHY YOU SHOULD NEVER USE A PRESHARED KEY WITH IPSEC Why you should never use a Preshared Key with IPSEC. IPSEC is an amazing, but not often used technology that allows you to authenticate, allow, deny, protect and/or encrypt network traffic between windows and non-window computers. It has been around since at least Windows 2000 days but it is some time difficult to set up. GROUP POLICY SETTING OF THE WEEK 26B The “Do not allow Windows Messenger to be run” will prevent any user from running Windows Messenger that comes out of the box with Windows XP. Now Windows Messenger 4.6 that comes with Windows XP is no longer supported but disabling the program should help avoid any confusion for user that also have Windows Live Messenger installed. HOW TO USE GROUP POLICY TO CONTROL SERVICES Step 1. Edit a computer Group Policy Object that is targeted to the computers that you want to control the service. Step 2. Navigate to Computer Configuration > Preferences > Control Panel Settings > Services. Step 3. In the menu click on Action > New > Service and now click on the “” button next to the Service Name field. HOW TO USE GROUP POLICY TO CONFIGURED INI FILES In my example I already have a file created called C:\test.ini with the following values. TIP: If the INI file is a global configuration file you will probably need to make this change as a computer policy as standard users probably won’t need have the permission to make changes to the file. Select the “Update” action and fill out the BLOCKED SITE BASED GPO DUE TO BLOCKED SOM The obvious, and remove the the Blocked Inheritance on the OU that the computer object is located. Link the Site based GPO to an OU below the Blocked Inheritance. If you do this you lose the ability to dynamically apply the setting based on the site that the computer is located which then defeats the purpose of having the GPO linked at thesite.
HOW TO IMPLEMENT THE ASD ESSENTIAL 8 VIA GROUP POLICY The Australian Government Department called the Australian Signals Directorate has a list of mitigation strategies that is used to help protect IT system against security risks. This list is called the “ASD Essential 8“. While this its generated by the Australian Government department it is an excellent starting point for securing any organisation or government IT Assets. The really great GROUP POLICY FAQ #2: HOW DO YOU MAP A PRINTER USING GROUP Now to map the printers all you need to do is go to the Printer Extension option of the Group Policy you want to apply the setting from (see below). All you need to do now is put the UNC Path of the printer in the “Shared path:” text field and your done. No more batch files, vbscripts or KIX scripts to edit and maintain for mappingprinters.
HOW TO TROUBLESHOOT APPLOCKER AppLocker is a great new feature that was introduced in Windows 7 that allowed IT Admins to prevent the running of certain application in their corporate environment (e.g. Chrome). However there are a number of steps and pre-requisites for this feature to work that seem to catch people up quite often. So below is a simple troubleshooting flowchart that
HOW TO FIX SEARCHOCS.ADMX ERROR AFTER UPGRADE TO WINDOWS Before I begin this article might be, for some of you, this will be well know information and it might all seem rather logical. But I continue to see questions being asked on forums as how as a Group Policy administrator can I prevent HOW TO REMOVE CPASSWORD VALUES FROM ACTIVE DIRECTORY With the recent MS14-025 security patch Microsoft has removed the ability to configure passwords in Group Policy Preferences via the User Interface. However this update does not remove the password value from AD nor does it stop the value being applied to computers/users. So, if you have apply MS14-025 and you have also implemented another way of managing the local WHY YOU SHOULD NEVER USE A PRESHARED KEY WITH IPSEC Why you should never use a Preshared Key with IPSEC. IPSEC is an amazing, but not often used technology that allows you to authenticate, allow, deny, protect and/or encrypt network traffic between windows and non-window computers. It has been around since at least Windows 2000 days but it is some time difficult to set up. GROUP POLICY SETTING OF THE WEEK 26B The “Do not allow Windows Messenger to be run” will prevent any user from running Windows Messenger that comes out of the box with Windows XP. Now Windows Messenger 4.6 that comes with Windows XP is no longer supported but disabling the program should help avoid any confusion for user that also have Windows Live Messenger installed. HOW TO USE GROUP POLICY TO CONFIGURE HOME PAGE SETTINGS One of the most common setting that Group Policy is used for it so configure browser home pages settings. There are a number of ways that this can be done in Part 1 i am going to go thought the changing the Home Page setting using a native Group Policy. EDGE CHROMIUM GROUP POLICY SETTINGS For all of its issues, Internet Explorer has been the most prolific Group Policy enabled applications ever released. Even the recent versions of Edge with Windows 10 still does not hold up to the old versions of IE when it comes to sheer number of supported settings. HOW TO USE GROUP POLICY PREFERENCES TO MANAGE WINDOWS Step 5. Click on the Common Tab and tick “Item-Level Targeting”. Step 6. Click on the targeting button. First of all we are going to create a collection that will target the Business House Power Plan to only the weekdays of the week. Step 7. In the targeting Editor clickon
HOW TO USE GROUP POLICY PREFERENCE ENABLE AUTO-LOGON The below article shows you how to use Group Policy Preference to setup the registry keys on a computer so that it automatically logs onto when its turned on. While doing this is potentially huge security issue and not something I would generally recommend IT staff might want to implement on computers that are highly locked down and usedfor
HOW TO TROUBLESHOOT APPLOCKER AppLocker is a great new feature that was introduced in Windows 7 that allowed IT Admins to prevent the running of certain application in their corporate environment (e.g. Chrome). However there are a number of steps and pre-requisites for this feature to work that seem to catch people up quite often. So below is a simple troubleshooting flowchart that
WHY CAN IT TAKE 10+ HOURS FOR GROUP POLICY SETTINGS TO APPLY? Have you ever applied a Group Policy and then waited the standard 90 minutes for the setting to apply only to find out that after a few hours the policy still has not been set yet. Even trying to force a GPUPDATE still does not trigger the change but then the next day the policy has applied as expected. What ACTIVE DIRECTORY STRUCTURE GUIDELINES Isolate your Administrator Resources If you are an organisation of any significant size you probably have a delegated cretin duties to specific teams (e.g. help desk or desktop support) via the way of administrator groups. This would allow you to easily grant the required permission for a IT support person to a specific user by only adding them to one group. HOW TO CONFIGURE GROUP POLICY TO USE DATA RECOVERY AGENTS As I previously mentioned in Part 1 “use Group Policy to save “How to use BitLocker to Go” recovery keys in Active Directory – Part 1” one of the cool new features in Windows 7 is the ability to encrypt removable storage devices to help prevent the loss of data within an organisation while storing a copy of the decryption key in Active Directory. Another way to encrypt the removable GROUP POLICY SETTING OF THE WEEK 26B The “Do not allow Windows Messenger to be run” will prevent any user from running Windows Messenger that comes out of the box with Windows XP. Now Windows Messenger 4.6 that comes with Windows XP is no longer supported but disabling the program should help avoid any confusion for user that also have Windows Live Messenger installed. HOW TO MITIGATE THE SHAREPOINT XSS SECURITY ISSUE WITH There is currently a Cross Site Scripting issue with SharePoint 3.0 and 2007 which could allow someone to maliciously run an arbitrary script that could allow elevation of privilege in the SharePoint site. There is currently no hotfix out for this issues however you can mitigate this issue by enabling the XSS Filter in Internet Explorer 8. Unfortunately this is HOW TO USE GROUP POLICY TO CONTROL SERVICES Step 1. Edit a computer Group Policy Object that is targeted to the computers that you want to control the service. Step 2. Navigate to Computer Configuration > Preferences > Control Panel Settings > Services. Step 3. In the menu click on Action > New > Service and now click on the “” button next to the Service Name field. HOW TO USE GROUP POLICY TO CONFIGURED INI FILESHOW TO EDIT INI FILESHOW TO CHANGE INI FILESHOW TO FIND INI FILESHOW TO OPEN INI FILESGROUP POLICY FILESGROUP POLICY PREFERENCES FILES WILDCARD In my example I already have a file created called C:\test.ini with the following values. TIP: If the INI file is a global configuration file you will probably need to make this change as a computer policy as standard users probably won’t need have the permission to make changes to the file. Select the “Update” action and fill out the HOW TO IMPLEMENT THE ASD ESSENTIAL 8 VIA GROUP POLICY The Australian Government Department called the Australian Signals Directorate has a list of mitigation strategies that is used to help protect IT system against security risks. This list is called the “ASD Essential 8“. While this its generated by the Australian Government department it is an excellent starting point for securing any organisation or government IT Assets. The really great HOW TO USE GROUP POLICY PREFERENCES TO MANAGE WINDOWS Step 5. Click on the Common Tab and tick “Item-Level Targeting”. Step 6. Click on the targeting button. First of all we are going to create a collection that will target the Business House Power Plan to only the weekdays of the week. Step 7. In the targeting Editor clickon
EDGE CHROMIUM GROUP POLICY SETTINGS For all of its issues, Internet Explorer has been the most prolific Group Policy enabled applications ever released. Even the recent versions of Edge with Windows 10 still does not hold up to the old versions of IE when it comes to sheer number of supported settings. HOW TO USE GROUP POLICY PREFERENCE ENABLE AUTO-LOGON The below article shows you how to use Group Policy Preference to setup the registry keys on a computer so that it automatically logs onto when its turned on. While doing this is potentially huge security issue and not something I would generally recommend IT staff might want to implement on computers that are highly locked down and usedfor
USING GROUP POLICY TO CONFIGURE DESKTOP WALLPAPER Group Policy is of course one of the best ways you can lockdown and configure your windows systems in your environment and one of the most commonly configured setting in Group Policy is the ability to configured the Desktop Wallpaper (a.k.a. Background) image. HOW TO REMOVE CPASSWORD VALUES FROM ACTIVE DIRECTORYHOW TO FIND SAVEDPASSWORDS
With the recent MS14-025 security patch Microsoft has removed the ability to configure passwords in Group Policy Preferences via the User Interface. However this update does not remove the password value from AD nor does it stop the value being applied to computers/users. So, if you have apply MS14-025 and you have also implemented another way of managing the local BLOCKED SITE BASED GPO DUE TO BLOCKED SOM The obvious, and remove the the Blocked Inheritance on the OU that the computer object is located. Link the Site based GPO to an OU below the Blocked Inheritance. If you do this you lose the ability to dynamically apply the setting based on the site that the computer is located which then defeats the purpose of having the GPO linked at thesite.
EDGE CHROMIUM IE MODE NOW WORKS Well, we did not have to wait long and as of today Edge Chromium Dev Channel version 77.0.223.0 has been fixed and IE Mode will now work as expected. Now you can run all your old “important” work related web sites without having to run them in a different window (see below). But serious, this is a fantastic feature that should remove alot
HOW TO USE GROUP POLICY TO CONTROL SERVICES Step 1. Edit a computer Group Policy Object that is targeted to the computers that you want to control the service. Step 2. Navigate to Computer Configuration > Preferences > Control Panel Settings > Services. Step 3. In the menu click on Action > New > Service and now click on the “” button next to the Service Name field. HOW TO USE GROUP POLICY TO CONFIGURED INI FILESHOW TO EDIT INI FILESHOW TO CHANGE INI FILESHOW TO FIND INI FILESHOW TO OPEN INI FILESGROUP POLICY FILESGROUP POLICY PREFERENCES FILES WILDCARD In my example I already have a file created called C:\test.ini with the following values. TIP: If the INI file is a global configuration file you will probably need to make this change as a computer policy as standard users probably won’t need have the permission to make changes to the file. Select the “Update” action and fill out the HOW TO IMPLEMENT THE ASD ESSENTIAL 8 VIA GROUP POLICY The Australian Government Department called the Australian Signals Directorate has a list of mitigation strategies that is used to help protect IT system against security risks. This list is called the “ASD Essential 8“. While this its generated by the Australian Government department it is an excellent starting point for securing any organisation or government IT Assets. The really great HOW TO USE GROUP POLICY PREFERENCES TO MANAGE WINDOWS Step 5. Click on the Common Tab and tick “Item-Level Targeting”. Step 6. Click on the targeting button. First of all we are going to create a collection that will target the Business House Power Plan to only the weekdays of the week. Step 7. In the targeting Editor clickon
EDGE CHROMIUM GROUP POLICY SETTINGS For all of its issues, Internet Explorer has been the most prolific Group Policy enabled applications ever released. Even the recent versions of Edge with Windows 10 still does not hold up to the old versions of IE when it comes to sheer number of supported settings. HOW TO USE GROUP POLICY PREFERENCE ENABLE AUTO-LOGON The below article shows you how to use Group Policy Preference to setup the registry keys on a computer so that it automatically logs onto when its turned on. While doing this is potentially huge security issue and not something I would generally recommend IT staff might want to implement on computers that are highly locked down and usedfor
USING GROUP POLICY TO CONFIGURE DESKTOP WALLPAPER Group Policy is of course one of the best ways you can lockdown and configure your windows systems in your environment and one of the most commonly configured setting in Group Policy is the ability to configured the Desktop Wallpaper (a.k.a. Background) image. HOW TO REMOVE CPASSWORD VALUES FROM ACTIVE DIRECTORYHOW TO FIND SAVEDPASSWORDS
With the recent MS14-025 security patch Microsoft has removed the ability to configure passwords in Group Policy Preferences via the User Interface. However this update does not remove the password value from AD nor does it stop the value being applied to computers/users. So, if you have apply MS14-025 and you have also implemented another way of managing the local BLOCKED SITE BASED GPO DUE TO BLOCKED SOM The obvious, and remove the the Blocked Inheritance on the OU that the computer object is located. Link the Site based GPO to an OU below the Blocked Inheritance. If you do this you lose the ability to dynamically apply the setting based on the site that the computer is located which then defeats the purpose of having the GPO linked at thesite.
EDGE CHROMIUM IE MODE NOW WORKS Well, we did not have to wait long and as of today Edge Chromium Dev Channel version 77.0.223.0 has been fixed and IE Mode will now work as expected. Now you can run all your old “important” work related web sites without having to run them in a different window (see below). But serious, this is a fantastic feature that should remove alot
HOW TO USE GROUP POLICY TO ALLOW OR BLOCK URL’S This is another article I have written that address’s the commonly asked question on the Group Policy forum as to how you can use group policy to block or allow users to specific web site URL’s. It goes without saying that the most effective way to implement content filtering for the internet is to maintain list of sites on your proxy server/firewall in your organisation. HOW TO USE GROUP POLICY PREFERENCE ENABLE AUTO-LOGON The below article shows you how to use Group Policy Preference to setup the registry keys on a computer so that it automatically logs onto when its turned on. While doing this is potentially huge security issue and not something I would generally recommend IT staff might want to implement on computers that are highly locked down and usedfor
EDGE CHROMIUM GROUP POLICY SETTINGS For all of its issues, Internet Explorer has been the most prolific Group Policy enabled applications ever released. Even the recent versions of Edge with Windows 10 still does not hold up to the old versions of IE when it comes to sheer number of supported settings. USING GROUP POLICY TO CONFIGURE DESKTOP WALLPAPER Group Policy is of course one of the best ways you can lockdown and configure your windows systems in your environment and one of the most commonly configured setting in Group Policy is the ability to configured the Desktop Wallpaper (a.k.a. Background) image. HOW TO APPLY A GROUP POLICY OBJECT TO INDIVIDUAL USERS OR Step 1. Select the Group Policy Object in the Group Policy Management Console (GPMC) and the click on the “Delegation” tab and then click on the “Advanced” button. Step 2. Select the “Authenticated Users” security group and then scroll down to the “Apply Group Policy” permission and HOW TO SETUP WORK FOLDER USING GROUP POLICY Work Folders is a great new server role feature with Windows Server 2012 R2 that allows your end user to sync their files over multiple device at work and at home. Think of it as SkyDrive hosted on Windows Server in your own server room rather than by a third party. While there are a lot more technically impressive features HOW TO DISABLE SMB1 USING GROUP POLICY ADMINISTRATIVE To disable client-side processing of the SMBv1 protocol (recommended), do ALL of the following: * Set the SMBv1 client driver to “Disable driver” using the “Configure SMB v1 client driver” setting; * Enable this setting; * In the “Configure LanmanWorkstation dependencies” text box, enter the following three lines of text:Bowser
HOW TO RESET THE DEFAULT DOMAIN GROUP POLICY OBJECTS The command to restore the GPO’s to default is as simple as running the “DCGPOFIX.exe” from a command line and press “Y” twice when prompted. Now you are done. You will notice any changes to the GPO have now been removed or reverted back to the default settings. Monitor your systems for any adverse affect and make sure that youhave
HOW TO CONFIGURE IIS TO SUPPORT LARGE AD TOKEN WITH GROUP Active Directory Token Bloat is an issue in AD where user are is a member of too many security groups. As such their account exceed the default 12k token size limit in Windows that is set on their internal AD Security Token. This is a common problem for many large organisation that have many security groups and in most situation HOW TO RESET A ROAMING PROFILE IN WINDOWS 7 After a user repeatedly was logged on with with a temporary profile, I wanted to “fix” it by restoring an older version of their profile. The notes in this article were spot on for removing the former roaming profile folder-contents from their workstation, though I did have to delete the now-empty profile folder within Users on the workstation. GROUP POLICY CENTRAL News, Tips and Tutorials for all your Group Policy needssAdvertise Here
* Home
* News
* Best Practices
* Tutorials
* Group Policy FAQ
* Archives
* Preferences
* Files
* Setting of the Week* USB Settings
* Videos
* Microsft KB Focus
* TechEd
* Hotfixes
* Contact
* Forum / About
* Privacy Policy
RECENT POSTS
Posted in News Tip
EDGE CHROMIUM IE MODE NOW WORKS Alan Burchill 25/07/2019Leave a comment
In the past few weeks there has been a lot of post about the new Enterprise features coming with the new Edge Chromium version of the browser. Unfortunately the main feature that enterprises were waiting for did not work… until today.Continue Reading...
Posted in News Tip
EDGE CHROMIUM GROUP POLICY SETTINGS Alan Burchill 20/06/2019Leave a comment
Microsoft Edge Chromium Group Policy setting have been released for testing, take a look at how to download the new settings and what settings are still missing.Continue Reading...
Posted in News Security SECURITY BASELINE TEMPLATE FOR WINDOWS 1903 Alan Burchill 27/05/2019Leave a comment
Microsoft has released the latest security template for Windows version (Windows 10 and Windows Server) 1903. These templates contain updated guidance and recommendations as to what setting should or should not be configured to your domain joined PC. The security template is actually just a bunch of reports, documents, GPO backups and tools that are consolidated in a s single…Continue Reading...
Posted in News
NEW AND FIXED GROUP POLICY SETTING WITH WINDOWS 10 KB4490481 Alan Burchill 03/04/2019Leave a comment
New and fixed Group Policy Setting with Windows 10 KB4490481Continue Reading...
Posted in News Security SECURITY BASELINE RECOMMENDATION FOR WINDOWS 10 1809 Alan Burchill 21/11/2018Leave a comment
After its initial release and then withdrawal of Windows 10 1809 update due to a number of potential data loss issues, Microsoft has now again released the OS to wide scale deployment. As a such a number of other release have now come from Microsoft, namely the Security Baseline templates GPO’s, documentation with recommended guidance and scripts to help secure…Continue Reading...
Posted in News
NEW MICROSOFT EDGE MDM AND GROUP POLICY SETTINGS Alan Burchill 19/07/2018Leave a comment
Microsoft just documented the new policy setting for Microsoft Edge. These settings can be configured via both MDM and Group Policy. To get use the policy settings you need to be running at least Windows 10 Preview build 17718. Then you can then install Group Policy management Console (now part of Core OS) and trial the new Policysettings. For a…
Continue Reading...
Posted in News
MICROSOFT RELEASES V2 OF THE WINDOWS 1803 ADMINISTRATIVE TEMPLATESPACK
Alan Burchill 17/07/2018Leave a comment
Back in May 2018 Microsoft released the Windows 1803 ADMX/ADML file pack . This was par for the course as with each release of Windows Microsoft would also release a new version of the ADMX/ADML Administrative Templates Pack. However, the release in May could cause an error in GPMC if you had previously had an old version of theSerachOCR.ADMX…
Continue Reading...
Posted in KB Focus
GROUP POLICY HOTFIX FOR DEFENDER MITIGATION OPTIONS ERROR Alan Burchill 12/07/2018Leave a comment
Just a quick note that Microsoft has recently release a hot fix KB4338819 that fixes and issue with the Mitigation option. This is a Windows Defender setting that can be found under the Administrative Templates>Computers>System>Mitigation Options setting. The fix is described as: Addresses an issue that may cause the Mitigation Options Group Policy client-side extension to fail during GPO processing….Continue Reading...
Page 1 of 5312 3
4
5
...10
20
30
...»
Last »
Advertise Here
FEATURED POST
How to stop local administrators from bypassing Group Policy 2015-03-09 • 10 Comments Before I begin this article might be, for some of you, this will be well know information and it might all seem rather logical. But I continue to see questions being asked on forums as how as a Group Policy administrator can I prevent...Search for:
FOLLOW US
POPULAR POSTS
How to use Group Policy Preferences to Secure Local AdministratorGroups
2010-01-21 • 172 Comments One problem I see all the time is IT administrator never being able to control who is a local administrator... How to configure Roaming Profiles and Folder Redirection 2010-08-18 • 134 Comments Read Me First: If you are using Folder Redirection with Windows 7 in your organisation then I would definitely recommend that... Updated – MS16-072 may break your User Group Policies“by-design”
2016-06-16 • 76 Comments This is a PSA for all Group Policy administrator about MS16-072 that was release yesterday. This patch fixed a man...CATEGORIES
* Best Practice
(40)
* FAQ (2)
* Funny (3)
* Group Policy FAQ
(3)
* hotfix (7)
* KB Focus (5)
* News (146)
* Other Site Links
(15)
* Podcast (2)
* Review (3)
* ScreenCast (4)
* Security (33)
* Setting of the Week(41)
* Site News (19)
* TechEd (35)
* Tip (36)
* Tutorials (117)
* Uncategorized
(6)
* Video (46)
ARCHIVES
Archives Select Month July 2019 June 2019 May 2019 April 2019 November 2018 July 2018 June 2018 May 2018 March 2018 January 2018 October 2017 August 2017 June 2017 May 2017 April 2017 March 2017 February 2017 January 2017 November 2016 October 2016 August 2016 July 2016 June 2016 May 2016 April 2016 March 2016 February 2016 November 2015 October 2015 August 2015 July 2015 June 2015 May 2015 March 2015 February 2015 January 2015 November 2014 October 2014 September 2014 August 2014 May 2014 April 2014 March 2014 January 2014 December 2013 November 2013 October 2013 September 2013 July 2013 June 2013 May 2013 April 2013 March 2013 February 2013 January 2013 December 2012 November 2012 October 2012 September 2012 August 2012 July 2012 June 2012 May 2012 April 2012 March 2012 February 2012 January 2012 December 2011 November 2011 October 2011 September 2011 August 2011 July 2011 June 2011 May 2011 April 2011 March 2011 February 2011 January 2011 December 2010 November 2010 October 2010 September 2010 August 2010 July 2010 June 2010 May 2010 April 2010 March 2010 February 2010 January 2010 December 2009 November 2009 October 2009 September 2009 July 2009 May 2009TAGS
Active Directory
ADMX adobe reader
Advanced
Advanced Group PolicyManagement
AGPM AppLocker
Basic
Feedly
GPMC
Group Policy
Group Policy
Prefereces
Group Policy Preferenceshotfix
IE9
IFTTT
Intermediate
Internet Explorer
Internet Explorer
9 Internet
Explorer 11
Jeremy Moskowitz
new Zealand PasswordPopular
Power Plan
Powershell
Recently Read
Remote Server Admin
Tools
RSAT Security
Security Compliance
Manager
SOE start menu
TechEd
TechEd 2009
TechEd 2011
TechNet Edge
Vista
Windows 7
Windows 8
Windows 8.1
Windows 10
Windows Server 2008 R2Windows XP
wsus
Select
LanguageAfrikaansAlbanianAmharicArabicArmenianAzerbaijaniBasqueBelarusianBengaliBosnianBulgarianCatalanCebuanoChichewaChinese(Simplified)Chinese
(Traditional)CorsicanCroatianCzechDanishDutchEsperantoEstonianFilipinoFinnishFrenchFrisianGalicianGeorgianGermanGreekGujaratiHaitian CreoleHausaHawaiianHebrewHindiHmongHungarianIcelandicIgboIndonesianIrishItalianJapaneseJavaneseKannadaKazakhKhmerKoreanKurdish (Kurmanji)KyrgyzLaoLatinLatvianLithuanianLuxembourgishMacedonianMalagasyMalayMalayalamMalteseMaoriMarathiMongolianMyanmar (Burmese)NepaliNorwegianPashtoPersianPolishPortuguesePunjabiRomanianRussianSamoanScots GaelicSerbianSesothoShonaSindhiSinhalaSlovakSlovenianSomaliSpanishSundaneseSwahiliSwedishTajikTamilTeluguThaiTurkishUkrainianUrduUzbekVietnameseWelshXhosaYiddishYorubaZuluPoweredby Translate
* RSS - Posts
* RSS - Comments
SUBSCRIBE VIA EMAIL
Scan or Click
Copyright © 2019 Group Policy Central Privacy & Cookies: This site uses cookies. By continuing to use this website, you agree to their use. To find out more, including how to control cookies, see here: CookiePolicy
ORIGINAL TEXT
Contribute a better translation -------------------------Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0