Are you over 18 and want to see adult content?
More Annotations

A complete backup of https://canoncolorlaserprinter.com
Are you over 18 and want to see adult content?

A complete backup of https://orangestreetnews.com
Are you over 18 and want to see adult content?

A complete backup of https://maytaghvac.com
Are you over 18 and want to see adult content?

A complete backup of https://atradiuscollections.com
Are you over 18 and want to see adult content?

A complete backup of https://lpoc.co.uk
Are you over 18 and want to see adult content?

A complete backup of https://eucpn.org
Are you over 18 and want to see adult content?
A complete backup of https://quebarato.com.br
Are you over 18 and want to see adult content?

A complete backup of https://miamicopywriter.com
Are you over 18 and want to see adult content?

A complete backup of https://contemporarywoods.com
Are you over 18 and want to see adult content?

A complete backup of https://happyherbalist.com
Are you over 18 and want to see adult content?

A complete backup of https://kkh.com.sg
Are you over 18 and want to see adult content?

A complete backup of https://vironit.com
Are you over 18 and want to see adult content?
Favourite Annotations
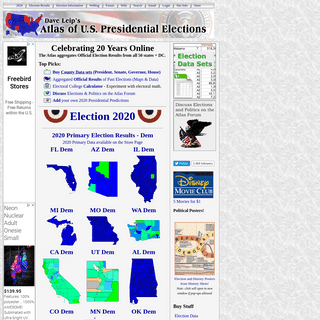
A complete backup of uselectionatlas.org
Are you over 18 and want to see adult content?
A complete backup of planetperplex.com
Are you over 18 and want to see adult content?

A complete backup of painresearchforum.org
Are you over 18 and want to see adult content?
A complete backup of seadoosportboats.com
Are you over 18 and want to see adult content?
Text
FEISTY DUCK
Hardenize is our network and application security monitoring platform, designed to automatically discover and monitor your assets and give you full visibility of the entire network perimeter. Website discovery and inventory. Host and network monitoring. Comprehensive protocol coverage: TLS, PKI, email, application security. PURCHASE THE BEST TLS TRAINING IN THE WORLD MATERIALS FOR Trainer-Led Remote Training. In addition to purchasing the materials, we recommend that the key members of the team attend one of our trainer-led public trainings. Remote training takes place over four half-days (3.5 hours a day). We are also available to organise LOG IN | FEISTY DUCK Please enter your email address and password to log in. If you've made a purchase but never logged in, please reset your password. PRACTICAL TLS AND PKI TRAINING Join us on this remote, tutor-led, training that covers the theory and practice of SSL/TLS and Internet PKI. Four half-days, packed with information. Taught by Scott Helme and designed by Ivan Ristić, this practical training course will take you through everything you need to know to deploy secure servers and design secure web applications.FEISTY DUCK
Feisty Duck is a small publishing house with focus on computer security and open source topics. Our books are published in a way that bridges the gap between traditional publishing and the new digitalage.
BULLETPROOF TLS NEWSLETTER Bulletproof TLS Newsletter. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in this space. Maintained by Hanno Böck. CurrentIssue. 77.
BULLETPROOF SSL AND TLS About the Author. Ivan Ristić writes computer security books and builds security products. His book Bulletproof SSL and TLS, the result of more than a decade of research and study, is widely recognised as the de-facto SSL/TLS and PKI reference manual. His work on SSL Labs made hundreds of thousands of web sites more secure. NONCE REUSE IN GCM, ANOTHER PADDING ORACLE, HTTPS BY Designed by Ivan Ristić, the author of SSL Labs, Bulletproof SSL and TLS, and Hardenize, our course covers everything you need to know to deploy secure servers and encrypted web applications.. Remote and trainer-led, with small classes and a choice of timezones. Join over 1,500 students who have benefited from more than a decade of deep TLSand PKI expertise.
MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
APACHE SECURITY: CHAPTER 7. ACCESS CONTROL 7. Access Control. Access control is an important part of security and is its most visible aspect, leading people to assume it is security. You may need to introduce access control to your system for a few reasons. The first and or most obvious reason is to allow some people to see (or do) what you want them to see/do while keeping the othersout.
FEISTY DUCK
Hardenize is our network and application security monitoring platform, designed to automatically discover and monitor your assets and give you full visibility of the entire network perimeter. Website discovery and inventory. Host and network monitoring. Comprehensive protocol coverage: TLS, PKI, email, application security. PURCHASE THE BEST TLS TRAINING IN THE WORLD MATERIALS FOR Trainer-Led Remote Training. In addition to purchasing the materials, we recommend that the key members of the team attend one of our trainer-led public trainings. Remote training takes place over four half-days (3.5 hours a day). We are also available to organise LOG IN | FEISTY DUCK Please enter your email address and password to log in. If you've made a purchase but never logged in, please reset your password. PRACTICAL TLS AND PKI TRAINING Join us on this remote, tutor-led, training that covers the theory and practice of SSL/TLS and Internet PKI. Four half-days, packed with information. Taught by Scott Helme and designed by Ivan Ristić, this practical training course will take you through everything you need to know to deploy secure servers and design secure web applications.FEISTY DUCK
Feisty Duck is a small publishing house with focus on computer security and open source topics. Our books are published in a way that bridges the gap between traditional publishing and the new digitalage.
BULLETPROOF TLS NEWSLETTER Bulletproof TLS Newsletter. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in this space. Maintained by Hanno Böck. CurrentIssue. 77.
BULLETPROOF SSL AND TLS About the Author. Ivan Ristić writes computer security books and builds security products. His book Bulletproof SSL and TLS, the result of more than a decade of research and study, is widely recognised as the de-facto SSL/TLS and PKI reference manual. His work on SSL Labs made hundreds of thousands of web sites more secure. NONCE REUSE IN GCM, ANOTHER PADDING ORACLE, HTTPS BY Designed by Ivan Ristić, the author of SSL Labs, Bulletproof SSL and TLS, and Hardenize, our course covers everything you need to know to deploy secure servers and encrypted web applications.. Remote and trainer-led, with small classes and a choice of timezones. Join over 1,500 students who have benefited from more than a decade of deep TLSand PKI expertise.
MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
APACHE SECURITY: CHAPTER 7. ACCESS CONTROL 7. Access Control. Access control is an important part of security and is its most visible aspect, leading people to assume it is security. You may need to introduce access control to your system for a few reasons. The first and or most obvious reason is to allow some people to see (or do) what you want them to see/do while keeping the othersout.
BOOKS | FEISTY DUCK
Books. We are a small publishing house, but each one of our books is carefully selected and designed to provide a comprehensive and authoritative resource. Uniquely, our flagship books—on TLS, PKI, and OpenSSL—are continuously updated. LOG IN | FEISTY DUCK Please enter your email address and password to log in. If you've made a purchase but never logged in, please reset your password.FEISTY DUCK
Feisty Duck is a small publishing house with focus on computer security and open source topics. Our books are published in a way that bridges the gap between traditional publishing and the new digitalage.
MODSECURITY HANDBOOK ISBN: 978-1907117077. This book exists to document every single aspect of ModSecurity and to teach you how to use it. It’s as simple as that. ModSecurity is a fantastic tool, but it’s let down by the poor quality of the documentation. As a result, the adoption is not as good as it could be; application security is difficult on its own, and APACHE SECURITY: CHAPTER 8. LOGGING AND MONITORING 8 Logging and Monitoring. 8. Logging and Monitoring. One of the most important tasks of an administrator is to configure a system to be secure, but it is also necessary to know it is secure. The only way to know a system is secure (and behaving correctly) is through informative and trustworthy log files. Though the security point ofview is
SSL/TLS AND PKI HISTORY Workshop. Previous versions of SSL and TLS were either rushed (SSL v2 and SSL v3) or maintenance efforts (TLS v1.0-v1.2). With TLS v1.3, the working group is taking a different approach; after more than two years in development, a workshop is held to carefully analyse the new designs. February 2016. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 4. LOGGING Every audit log entry begins with part A, which contains the basic information about the transaction: time, unique ID, source IP address, source port, destination IP address, and destination port:--6b253045-A-- SopXW38EAAE9YbLQ 192.168.3.1 2387 192.168.3.111 8080. Part B contains the request headers and nothing else: MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 2. INSTALLATION The installation is quite easy. First, download the package and copy the dynamic libraries into the modules/ folder (of the Apache installation). Then, modify your Apache configuration to activate ModSecurity: LoadModule security2_module modules/mod_security2.so. BULLETPROOF SSL AND TLS BULLETPROOF SSL AND TLS Understanding and Deploying SSL/TLS and PKI to Secure Servers and Web Applications Ivan Ristić Free edition: GettingStarted
CERTIFICATE TRANSPARENCY LOGGING IS NOW MANDATORY Certificate Transparency logging is now mandatory. 30 April 2018. Author: Hanno Böck. This issue was distributed to 44,829 email subscribers. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in thisspace.
FEISTY DUCK
Hardenize is our network and application security monitoring platform, designed to automatically discover and monitor your assets and give you full visibility of the entire network perimeter. Website discovery and inventory. Host and network monitoring. Comprehensive protocol coverage: TLS, PKI, email, application security. PURCHASE THE BEST TLS TRAINING IN THE WORLD MATERIALS FOR Trainer-Led Remote Training. In addition to purchasing the materials, we recommend that the key members of the team attend one of our trainer-led public trainings. Remote training takes place over four half-days (3.5 hours a day). We are also available to organise PRACTICAL TLS AND PKI TRAINING Join us on this remote, tutor-led, training that covers the theory and practice of SSL/TLS and Internet PKI. Four half-days, packed with information. Taught by Scott Helme and designed by Ivan Ristić, this practical training course will take you through everything you need to know to deploy secure servers and design secure web applications. BULLETPROOF TLS NEWSLETTER Bulletproof TLS Newsletter. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in this space. Maintained by Hanno Böck. CurrentIssue. 77.
SSL/TLS AND PKI HISTORY Workshop. Previous versions of SSL and TLS were either rushed (SSL v2 and SSL v3) or maintenance efforts (TLS v1.0-v1.2). With TLS v1.3, the working group is taking a different approach; after more than two years in development, a workshop is held to carefully analyse the new designs. February 2016. BULLETPROOF SSL AND TLS About the Author. Ivan Ristić writes computer security books and builds security products. His book Bulletproof SSL and TLS, the result of more than a decade of research and study, is widely recognised as the de-facto SSL/TLS and PKI reference manual. His work on SSL Labs made hundreds of thousands of web sites more secure. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
NONCE REUSE IN GCM, ANOTHER PADDING ORACLE, HTTPS BY Designed by Ivan Ristić, the author of SSL Labs, Bulletproof SSL and TLS, and Hardenize, our course covers everything you need to know to deploy secure servers and encrypted web applications.. Remote and trainer-led, with small classes and a choice of timezones. Join over 1,500 students who have benefited from more than a decade of deep TLSand PKI expertise.
OPENSSL COOKBOOK: CHAPTER 2. TESTING TLS WITH OPENSSL Due to a bug in OpenSSL, at the time of writing session resumption testing doesn’t work in combination with TLS 1.3. Until the bug is resolved, 31 the best you can do is test the earlier protocol versions. Use the -no_tls1_3 switch. The previous command will producea sea of
APACHE SECURITY: CHAPTER 8. LOGGING AND MONITORING 8 Logging and Monitoring. 8. Logging and Monitoring. One of the most important tasks of an administrator is to configure a system to be secure, but it is also necessary to know it is secure. The only way to know a system is secure (and behaving correctly) is through informative and trustworthy log files. Though the security point ofview is
FEISTY DUCK
Hardenize is our network and application security monitoring platform, designed to automatically discover and monitor your assets and give you full visibility of the entire network perimeter. Website discovery and inventory. Host and network monitoring. Comprehensive protocol coverage: TLS, PKI, email, application security. PURCHASE THE BEST TLS TRAINING IN THE WORLD MATERIALS FOR Trainer-Led Remote Training. In addition to purchasing the materials, we recommend that the key members of the team attend one of our trainer-led public trainings. Remote training takes place over four half-days (3.5 hours a day). We are also available to organise PRACTICAL TLS AND PKI TRAINING Join us on this remote, tutor-led, training that covers the theory and practice of SSL/TLS and Internet PKI. Four half-days, packed with information. Taught by Scott Helme and designed by Ivan Ristić, this practical training course will take you through everything you need to know to deploy secure servers and design secure web applications. BULLETPROOF TLS NEWSLETTER Bulletproof TLS Newsletter. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in this space. Maintained by Hanno Böck. CurrentIssue. 77.
SSL/TLS AND PKI HISTORY Workshop. Previous versions of SSL and TLS were either rushed (SSL v2 and SSL v3) or maintenance efforts (TLS v1.0-v1.2). With TLS v1.3, the working group is taking a different approach; after more than two years in development, a workshop is held to carefully analyse the new designs. February 2016. BULLETPROOF SSL AND TLS About the Author. Ivan Ristić writes computer security books and builds security products. His book Bulletproof SSL and TLS, the result of more than a decade of research and study, is widely recognised as the de-facto SSL/TLS and PKI reference manual. His work on SSL Labs made hundreds of thousands of web sites more secure. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
NONCE REUSE IN GCM, ANOTHER PADDING ORACLE, HTTPS BY Designed by Ivan Ristić, the author of SSL Labs, Bulletproof SSL and TLS, and Hardenize, our course covers everything you need to know to deploy secure servers and encrypted web applications.. Remote and trainer-led, with small classes and a choice of timezones. Join over 1,500 students who have benefited from more than a decade of deep TLSand PKI expertise.
OPENSSL COOKBOOK: CHAPTER 2. TESTING TLS WITH OPENSSL Due to a bug in OpenSSL, at the time of writing session resumption testing doesn’t work in combination with TLS 1.3. Until the bug is resolved, 31 the best you can do is test the earlier protocol versions. Use the -no_tls1_3 switch. The previous command will producea sea of
APACHE SECURITY: CHAPTER 8. LOGGING AND MONITORING 8 Logging and Monitoring. 8. Logging and Monitoring. One of the most important tasks of an administrator is to configure a system to be secure, but it is also necessary to know it is secure. The only way to know a system is secure (and behaving correctly) is through informative and trustworthy log files. Though the security point ofview is
BOOKS | FEISTY DUCK
Books. We are a small publishing house, but each one of our books is carefully selected and designed to provide a comprehensive and authoritative resource. Uniquely, our flagship books—on TLS, PKI, and OpenSSL—are continuously updated. LOG IN | FEISTY DUCK Please enter your email address and password to log in. If you've made a purchase but never logged in, please reset your password.FEISTY DUCK
Feisty Duck is a small publishing house with focus on computer security and open source topics. Our books are published in a way that bridges the gap between traditional publishing and the new digitalage.
SIGN UP | FEISTY DUCK Your Contact Information. Please enter your contact information below. Frankly, the email address is the only part that matters. BULLETPROOF SSL AND TLS About the Author. Ivan Ristić writes computer security books and builds security products. His book Bulletproof SSL and TLS, the result of more than a decade of research and study, is widely recognised as the de-facto SSL/TLS and PKI reference manual. His work on SSL Labs made hundreds of thousands of web sites more secure. SSL/TLS AND PKI HISTORY Workshop. Previous versions of SSL and TLS were either rushed (SSL v2 and SSL v3) or maintenance efforts (TLS v1.0-v1.2). With TLS v1.3, the working group is taking a different approach; after more than two years in development, a workshop is held to carefully analyse the new designs. February 2016. APACHE SECURITY: CHAPTER 8. LOGGING AND MONITORING 8 Logging and Monitoring. 8. Logging and Monitoring. One of the most important tasks of an administrator is to configure a system to be secure, but it is also necessary to know it is secure. The only way to know a system is secure (and behaving correctly) is through informative and trustworthy log files. Though the security point ofview is
MODSECURITY HANDBOOK ISBN: 978-1907117077. This book exists to document every single aspect of ModSecurity and to teach you how to use it. It’s as simple as that. ModSecurity is a fantastic tool, but it’s let down by the poor quality of the documentation. As a result, the adoption is not as good as it could be; application security is difficult on its own, and MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 4. LOGGING Every audit log entry begins with part A, which contains the basic information about the transaction: time, unique ID, source IP address, source port, destination IP address, and destination port:--6b253045-A-- SopXW38EAAE9YbLQ 192.168.3.1 2387 192.168.3.111 8080. Part B contains the request headers and nothing else: CERTIFICATE TRANSPARENCY LOGGING IS NOW MANDATORY Certificate Transparency logging is now mandatory. 30 April 2018. Author: Hanno Böck. This issue was distributed to 44,829 email subscribers. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in thisspace.
FEISTY DUCK
Hardenize is our network and application security monitoring platform, designed to automatically discover and monitor your assets and give you full visibility of the entire network perimeter. Website discovery and inventory. Host and network monitoring. Comprehensive protocol coverage: TLS, PKI, email, application security. PURCHASE THE BEST TLS TRAINING IN THE WORLD MATERIALS FOR Trainer-Led Remote Training. In addition to purchasing the materials, we recommend that the key members of the team attend one of our trainer-led public trainings. Remote training takes place over four half-days (3.5 hours a day). We are also available to organise PRACTICAL TLS AND PKI TRAINING Join us on this remote, tutor-led, training that covers the theory and practice of SSL/TLS and Internet PKI. Four half-days, packed with information. Taught by Scott Helme and designed by Ivan Ristić, this practical training course will take you through everything you need to know to deploy secure servers and design secure web applications. BULLETPROOF TLS NEWSLETTER Bulletproof TLS Newsletter. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in this space. Maintained by Hanno Böck. CurrentIssue. 77.
SSL/TLS AND PKI HISTORY Workshop. Previous versions of SSL and TLS were either rushed (SSL v2 and SSL v3) or maintenance efforts (TLS v1.0-v1.2). With TLS v1.3, the working group is taking a different approach; after more than two years in development, a workshop is held to carefully analyse the new designs. February 2016. BULLETPROOF SSL AND TLS About the Author. Ivan Ristić writes computer security books and builds security products. His book Bulletproof SSL and TLS, the result of more than a decade of research and study, is widely recognised as the de-facto SSL/TLS and PKI reference manual. His work on SSL Labs made hundreds of thousands of web sites more secure. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
NONCE REUSE IN GCM, ANOTHER PADDING ORACLE, HTTPS BY Designed by Ivan Ristić, the author of SSL Labs, Bulletproof SSL and TLS, and Hardenize, our course covers everything you need to know to deploy secure servers and encrypted web applications.. Remote and trainer-led, with small classes and a choice of timezones. Join over 1,500 students who have benefited from more than a decade of deep TLSand PKI expertise.
OPENSSL COOKBOOK: CHAPTER 2. TESTING TLS WITH OPENSSL Due to a bug in OpenSSL, at the time of writing session resumption testing doesn’t work in combination with TLS 1.3. Until the bug is resolved, 31 the best you can do is test the earlier protocol versions. Use the -no_tls1_3 switch. The previous command will producea sea of
APACHE SECURITY: CHAPTER 8. LOGGING AND MONITORING 8 Logging and Monitoring. 8. Logging and Monitoring. One of the most important tasks of an administrator is to configure a system to be secure, but it is also necessary to know it is secure. The only way to know a system is secure (and behaving correctly) is through informative and trustworthy log files. Though the security point ofview is
FEISTY DUCK
Hardenize is our network and application security monitoring platform, designed to automatically discover and monitor your assets and give you full visibility of the entire network perimeter. Website discovery and inventory. Host and network monitoring. Comprehensive protocol coverage: TLS, PKI, email, application security. PURCHASE THE BEST TLS TRAINING IN THE WORLD MATERIALS FOR Trainer-Led Remote Training. In addition to purchasing the materials, we recommend that the key members of the team attend one of our trainer-led public trainings. Remote training takes place over four half-days (3.5 hours a day). We are also available to organise PRACTICAL TLS AND PKI TRAINING Join us on this remote, tutor-led, training that covers the theory and practice of SSL/TLS and Internet PKI. Four half-days, packed with information. Taught by Scott Helme and designed by Ivan Ristić, this practical training course will take you through everything you need to know to deploy secure servers and design secure web applications. BULLETPROOF TLS NEWSLETTER Bulletproof TLS Newsletter. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in this space. Maintained by Hanno Böck. CurrentIssue. 77.
SSL/TLS AND PKI HISTORY Workshop. Previous versions of SSL and TLS were either rushed (SSL v2 and SSL v3) or maintenance efforts (TLS v1.0-v1.2). With TLS v1.3, the working group is taking a different approach; after more than two years in development, a workshop is held to carefully analyse the new designs. February 2016. BULLETPROOF SSL AND TLS About the Author. Ivan Ristić writes computer security books and builds security products. His book Bulletproof SSL and TLS, the result of more than a decade of research and study, is widely recognised as the de-facto SSL/TLS and PKI reference manual. His work on SSL Labs made hundreds of thousands of web sites more secure. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
NONCE REUSE IN GCM, ANOTHER PADDING ORACLE, HTTPS BY Designed by Ivan Ristić, the author of SSL Labs, Bulletproof SSL and TLS, and Hardenize, our course covers everything you need to know to deploy secure servers and encrypted web applications.. Remote and trainer-led, with small classes and a choice of timezones. Join over 1,500 students who have benefited from more than a decade of deep TLSand PKI expertise.
OPENSSL COOKBOOK: CHAPTER 2. TESTING TLS WITH OPENSSL Due to a bug in OpenSSL, at the time of writing session resumption testing doesn’t work in combination with TLS 1.3. Until the bug is resolved, 31 the best you can do is test the earlier protocol versions. Use the -no_tls1_3 switch. The previous command will producea sea of
APACHE SECURITY: CHAPTER 8. LOGGING AND MONITORING 8 Logging and Monitoring. 8. Logging and Monitoring. One of the most important tasks of an administrator is to configure a system to be secure, but it is also necessary to know it is secure. The only way to know a system is secure (and behaving correctly) is through informative and trustworthy log files. Though the security point ofview is
BOOKS | FEISTY DUCK
Books. We are a small publishing house, but each one of our books is carefully selected and designed to provide a comprehensive and authoritative resource. Uniquely, our flagship books—on TLS, PKI, and OpenSSL—are continuously updated. LOG IN | FEISTY DUCK Please enter your email address and password to log in. If you've made a purchase but never logged in, please reset your password.FEISTY DUCK
Feisty Duck is a small publishing house with focus on computer security and open source topics. Our books are published in a way that bridges the gap between traditional publishing and the new digitalage.
SIGN UP | FEISTY DUCK Your Contact Information. Please enter your contact information below. Frankly, the email address is the only part that matters. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
SSL/TLS AND PKI HISTORY Workshop. Previous versions of SSL and TLS were either rushed (SSL v2 and SSL v3) or maintenance efforts (TLS v1.0-v1.2). With TLS v1.3, the working group is taking a different approach; after more than two years in development, a workshop is held to carefully analyse the new designs. February 2016. MODSECURITY HANDBOOK ISBN: 978-1907117077. This book exists to document every single aspect of ModSecurity and to teach you how to use it. It’s as simple as that. ModSecurity is a fantastic tool, but it’s let down by the poor quality of the documentation. As a result, the adoption is not as good as it could be; application security is difficult on its own, and APACHE SECURITY: CHAPTER 8. LOGGING AND MONITORING 8 Logging and Monitoring. 8. Logging and Monitoring. One of the most important tasks of an administrator is to configure a system to be secure, but it is also necessary to know it is secure. The only way to know a system is secure (and behaving correctly) is through informative and trustworthy log files. Though the security point ofview is
MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 4. LOGGING Every audit log entry begins with part A, which contains the basic information about the transaction: time, unique ID, source IP address, source port, destination IP address, and destination port:--6b253045-A-- SopXW38EAAE9YbLQ 192.168.3.1 2387 192.168.3.111 8080. Part B contains the request headers and nothing else: LIBRARY: OPENSSL COOKBOOK, 3ED This book is free. You can read the HTML version without registration. If you'd like to access the PDF and EPUB formats, please log in orsign up.
FEISTY DUCK
Hardenize is our network and application security monitoring platform, designed to automatically discover and monitor your assets and give you full visibility of the entire network perimeter. Website discovery and inventory. Host and network monitoring. Comprehensive protocol coverage: TLS, PKI, email, application security. PURCHASE THE BEST TLS TRAINING IN THE WORLD MATERIALS FOR Trainer-Led Remote Training. In addition to purchasing the materials, we recommend that the key members of the team attend one of our trainer-led public trainings. Remote training takes place over four half-days (3.5 hours a day). We are also available to organise PRACTICAL TLS AND PKI TRAINING Join us on this remote, tutor-led, training that covers the theory and practice of SSL/TLS and Internet PKI. Four half-days, packed with information. Taught by Scott Helme and designed by Ivan Ristić, this practical training course will take you through everything you need to know to deploy secure servers and design secure web applications.FEISTY DUCK
Feisty Duck is a small publishing house with focus on computer security and open source topics. Our books are published in a way that bridges the gap between traditional publishing and the new digitalage.
BULLETPROOF TLS NEWSLETTER Bulletproof TLS Newsletter. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in this space. Maintained by Hanno Böck. CurrentIssue. 77.
OPENSSL COOKBOOK
The definitive guide to using the OpenSSL command line for configuration and testing, by Ivan Ristić. For system administrators, developers, and IT security professionals, this book provides a comprehensive coverage of the ever-changing field of SSL/TLS and Internet PKI. Written by Ivan Ristić, a security researcher andauthor of SSL Labs
BULLETPROOF SSL AND TLS About the Author. Ivan Ristić writes computer security books and builds security products. His book Bulletproof SSL and TLS, the result of more than a decade of research and study, is widely recognised as the de-facto SSL/TLS and PKI reference manual. His work on SSL Labs made hundreds of thousands of web sites more secure. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
NONCE REUSE IN GCM, ANOTHER PADDING ORACLE, HTTPS BY Designed by Ivan Ristić, the author of SSL Labs, Bulletproof SSL and TLS, and Hardenize, our course covers everything you need to know to deploy secure servers and encrypted web applications.. Remote and trainer-led, with small classes and a choice of timezones. Join over 1,500 students who have benefited from more than a decade of deep TLSand PKI expertise.
APACHE SECURITY: CHAPTER 7. ACCESS CONTROL 7. Access Control. Access control is an important part of security and is its most visible aspect, leading people to assume it is security. You may need to introduce access control to your system for a few reasons. The first and or most obvious reason is to allow some people to see (or do) what you want them to see/do while keeping the othersout.
FEISTY DUCK
Hardenize is our network and application security monitoring platform, designed to automatically discover and monitor your assets and give you full visibility of the entire network perimeter. Website discovery and inventory. Host and network monitoring. Comprehensive protocol coverage: TLS, PKI, email, application security. PURCHASE THE BEST TLS TRAINING IN THE WORLD MATERIALS FOR Trainer-Led Remote Training. In addition to purchasing the materials, we recommend that the key members of the team attend one of our trainer-led public trainings. Remote training takes place over four half-days (3.5 hours a day). We are also available to organise PRACTICAL TLS AND PKI TRAINING Join us on this remote, tutor-led, training that covers the theory and practice of SSL/TLS and Internet PKI. Four half-days, packed with information. Taught by Scott Helme and designed by Ivan Ristić, this practical training course will take you through everything you need to know to deploy secure servers and design secure web applications.FEISTY DUCK
Feisty Duck is a small publishing house with focus on computer security and open source topics. Our books are published in a way that bridges the gap between traditional publishing and the new digitalage.
BULLETPROOF TLS NEWSLETTER Bulletproof TLS Newsletter. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in this space. Maintained by Hanno Böck. CurrentIssue. 77.
OPENSSL COOKBOOK
The definitive guide to using the OpenSSL command line for configuration and testing, by Ivan Ristić. For system administrators, developers, and IT security professionals, this book provides a comprehensive coverage of the ever-changing field of SSL/TLS and Internet PKI. Written by Ivan Ristić, a security researcher andauthor of SSL Labs
BULLETPROOF SSL AND TLS About the Author. Ivan Ristić writes computer security books and builds security products. His book Bulletproof SSL and TLS, the result of more than a decade of research and study, is widely recognised as the de-facto SSL/TLS and PKI reference manual. His work on SSL Labs made hundreds of thousands of web sites more secure. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
NONCE REUSE IN GCM, ANOTHER PADDING ORACLE, HTTPS BY Designed by Ivan Ristić, the author of SSL Labs, Bulletproof SSL and TLS, and Hardenize, our course covers everything you need to know to deploy secure servers and encrypted web applications.. Remote and trainer-led, with small classes and a choice of timezones. Join over 1,500 students who have benefited from more than a decade of deep TLSand PKI expertise.
APACHE SECURITY: CHAPTER 7. ACCESS CONTROL 7. Access Control. Access control is an important part of security and is its most visible aspect, leading people to assume it is security. You may need to introduce access control to your system for a few reasons. The first and or most obvious reason is to allow some people to see (or do) what you want them to see/do while keeping the othersout.
BOOKS | FEISTY DUCK
Books. We are a small publishing house, but each one of our books is carefully selected and designed to provide a comprehensive and authoritative resource. Uniquely, our flagship books—on TLS, PKI, and OpenSSL—are continuously updated. LOG IN | FEISTY DUCK Please enter your email address and password to log in. If you've made a purchase but never logged in, please reset your password. SIGN UP | FEISTY DUCK Your Contact Information. Please enter your contact information below. Frankly, the email address is the only part that matters. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 3 As already discussed, it is root that owns everything by default, and we assign ownership to apache only where that is necessary.. In two cases (/opt/modsecurity and /opt/modsecurity/var), we need to allow apache to access a folder so that it can get to a subfolder; we do this by creating a group, also called apache, of which user apache isthe only member.
SSL/TLS AND PKI HISTORY Workshop. Previous versions of SSL and TLS were either rushed (SSL v2 and SSL v3) or maintenance efforts (TLS v1.0-v1.2). With TLS v1.3, the working group is taking a different approach; after more than two years in development, a workshop is held to carefully analyse the new designs. February 2016. MODSECURITY HANDBOOK: GETTING STARTED: CHAPTER 4. LOGGING Every audit log entry begins with part A, which contains the basic information about the transaction: time, unique ID, source IP address, source port, destination IP address, and destination port:--6b253045-A-- SopXW38EAAE9YbLQ 192.168.3.1 2387 192.168.3.111 8080. Part B contains the request headers and nothing else: APACHE SECURITY: CHAPTER 8. LOGGING AND MONITORING 8 Logging and Monitoring. 8. Logging and Monitoring. One of the most important tasks of an administrator is to configure a system to be secure, but it is also necessary to know it is secure. The only way to know a system is secure (and behaving correctly) is through informative and trustworthy log files. Though the security point ofview is
OPENSSL COOKBOOK: CHAPTER 2. TESTING TLS WITH OPENSSL Due to a bug in OpenSSL, at the time of writing session resumption testing doesn’t work in combination with TLS 1.3. Until the bug is resolved, 31 the best you can do is test the earlier protocol versions. Use the -no_tls1_3 switch. The previous command will producea sea of
BULLETPROOF SSL AND TLS BULLETPROOF SSL AND TLS Understanding and Deploying SSL/TLS and PKI to Secure Servers and Web Applications Ivan Ristić Free edition: GettingStarted
CERTIFICATE TRANSPARENCY LOGGING IS NOW MANDATORY Certificate Transparency logging is now mandatory. 30 April 2018. Author: Hanno Böck. This issue was distributed to 44,829 email subscribers. Bulletproof TLS Newsletter is a free periodic newsletter bringing you commentary and news surrounding SSL/TLS and Internet PKI, designed to keep you informed about the latest developments in thisspace.
ERROR: JAVASCRIPT APPEARS TO BE DISABLED This web site will not operate correctly without JavaScript. Apologies for the inconvenience. Home Training Books Sign In Learn how to secure your business from attacks with our practical security courses, taught by top experts in their fields THE BEST TLS TRAININGIN THE WORLD
Designed by the author of the much acclaimed _Bulletproof SSL and TLS_, the
_SSL Labs_ server test and most recently _Hardenize_ monitoring tools, this practical two-day training course will teach you how to deploy secure servers and encrypted web applications and understand both the theory and practice of Internet PKI. Next trainings: Remote, 15-18 Oct 2019; London, 19-20 Nov 2019 MORE »MODSECURITY
MASTERCLASS
This two-day course designed by the co-author of our _ModSecurity Handbook 2ED_ will help you set up an Apache webserver and install ModSecurity together with a tight ruleset. We will configure the server and talk about every single detail of the configuration to give you an expert understanding of how your server works and behaves. Next trainings: Zurich, 30 Oct - 1 Nov 2019; London, 25-26 Nov 2019 MORE » BULLETPROOF TLS NEWSLETTER Bulletproof TLS Newsletter is a free notification service that brings you fresh SSL/TLS and Internet PKI news. This newsletter came out of need to send regular and sometimes urgent notifications to the readers of my books interested in encryption. I aim to send newsletters infrequently, at most once amonth. MORE »
SSL/TLS AND PKI HISTORY A comprehensive history of the most important events that shaped the SSL/TLS and PKI ecosystem, based on our book _Bulletproof SSL andTLS_. MORE »
OUR BOOKS
ModSecurity Handbook (2nd Edition) 2017 The definitive guide to the popular open source web application firewall, written by Christian Folini and Ivan Ristić, the principal author of ModSecurity. This book contains everything you need to successfully deploy and maintain a ModSecurity installation, in oneplace.
Bulletproof SSL and TLS 2017 The complete guide to deploying secure servers and web applications.This book, which provides comprehensive coverage of the ever-changing field of SSL/TLS and Web PKI, is intended for IT security professionals, system administrators, and developers, with the main focus on getting things done. Apache Security 2005 FREE This all-purpose guide for locking down Apache arms readers with all the information they need to securely deploy applications. Administrators and programmers alike will benefit from a concise introduction to the theory of securing Apache, plus a wealth of practical advice and real-life examples. OpenSSL Cookbook 2015 FREE This free book provides complete coverage of OpenSSL installation, configuration, and key and certificate management. The appendix includes _SSL/TLS Deployment Best Practices_, a concise guide to designing and deploying secure web sites and applications. DIGITAL BOOKS FROM OTHER PUBLISHERS In addition to publishing our own books, we provide digital distribution services to other publishers. The following books are currently distributed by us: * Programming in Lua, Fourth Edition * Lua Programming GemsNEWS
SSL/TLS and PKI training now available remotely31 Jan 2019
_The Best TLS Training in the World_ is now available as a remote option for in-house teams. Public trainings coming soon! MORE » Bulletproof SSL and TLS, 2017 Revision12 July 2017
Bulletproof SSL and TLS is once again fully up to date! All updates are included with your original purchase. Read about it on Ivan's blog,
get the latest version and see exactly what's changed. MORE » ModSecurity Handbook, Second EditionOut Now
29 June 2017
ModSecurity Handbook, Second Edition is now complete, and the paperback will be available on 15th July! Preorder now on Amazon, or order the digital book from Feisty Duck. MORE » Programming in Lua 4ed Now Available26 April 2017
We are very happy to announce that the fourth edition of the excellent _Programming in Lua_ is now available as an ebook. MORE » Working with Manicode Security6 January 2017
We are thrilled to announce that we are starting 2017 with a collaboration with Jim Manico and Manicode Security. MORE » Feisty Duck Ltd is registered in England, company number 6694169. Registered address: 1-2 Craven Road, London W5 2UA, United Kingdom Website Terms of Use Terms and Conditions Privacy Shipping Rates Support AboutContact
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0








