Are you over 18 and want to see adult content?
More Annotations
A complete backup of juicyglamour.com
Are you over 18 and want to see adult content?
A complete backup of commonsensehealth.com
Are you over 18 and want to see adult content?
A complete backup of noahwebsterhouse.org
Are you over 18 and want to see adult content?

A complete backup of aerospecialties.com
Are you over 18 and want to see adult content?
A complete backup of betoncentralen.gl
Are you over 18 and want to see adult content?

A complete backup of sushikashiba.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of nikerosherunshoes.org.uk
Are you over 18 and want to see adult content?

A complete backup of magnetdunyasi.com
Are you over 18 and want to see adult content?
A complete backup of projectsandcastle.org
Are you over 18 and want to see adult content?

A complete backup of ibccoaching.com.br
Are you over 18 and want to see adult content?
A complete backup of bettercarenetwork.org
Are you over 18 and want to see adult content?
Text
following flags:
UGC NET COMPUTER SCIENCE Operating Systems 02. 11. The maximum amount of information that is available in one portion of the disk access arm for a removal disk pack (without further movement of the arm with multiple heads) (A) a plate of data. (B) a cylinder of data. (C) a track of data. (D) a block of data. 12. UGC NET COMPUTER SCIENCE 1.A Critical region: In concurrent programming, a critical section/region is a piece of code that accesses a shared resource that must not be concurrently accessed by more than one thread of execution.Some synchronization mechanism is required at the entry and exit of the critical section to ensure exclusive use (Mutual exclusion), for example a semaphore. UGC NET COMPUTER SCIENCE 24. A. 100 K, 500 K, 200 K, 300 K and 600 K (in order) and processes of 212 K, 417 K, 112 K, and 426 K. According the to the first fit algorithm, the memmory will be scanned to find out the memory portion that is enough for the arriving process, The first such portion found is allocated to the process. UGC NET COMPUTER SCIENCE 1.A 2.B The Mandelbrot set is the set of values of c in the complex plane for which the orbit of 0 under iteration of the complex quadratic polynomial z n+1 = z n 2 + c remains bounded. That is, a complex number c is part of the Mandelbrot set if, when starting with z0 = 0 and applying the iteration repeatedly, the absolute value of z n remains bounded however large n gets. UGC NET COMPUTER SCIENCE Kruskal's algorithm is a greedy algorithm in graph theory that finds a minimum spanning tree for a connected weighted graph. This means it finds a subset of the edges that forms a tree that includes every vertex, where the total weight of all the edges in the tree is minimized. Where E is the number of edges in the graph and V is thenumber of
UGC NET COMPUTER SCIENCE The Object-Modelling Technique (OMT) is an object modelling language for software modelling and designing. It was developed around 1991 by Rumbaugh, Blaha, Premerlani, Eddy and Lorensen as a method to develop object-oriented systems and to support object-oriented programming. It describes Object model or static structure of the system. UGC NET COMPUTER SCIENCE B. A B-tree is a tree data structure that keeps data sorted and allows searches, sequential access, insertions, and deletions in logarithmic time. The B-tree is a generalization of a binary search tree in that a node can have more than two children. A B-tree is kept balanced by requiring that all leaf nodes be at the same depth. UGC NET COMPUTER SCIENCE A. 100 K, 500 K, 200 K, 300 K and 600 K (in order) and processes of 212 K, 417 K, 112 K, and 426 K. According the to the first fit algorithm, the memmory will be scanned to find out the memory portion that is enough for the arriving process, The first such portion found is allocated to the process. UGC NET COMPUTER SCIENCE Any grammar can be proved ambiguous if we are able to find at least one string with more than one left-most derivation accepted by thegrammar.
UGC NET COMPUTER SCIENCE 17.D In order to open a file with a stream object we use its member function open(): open (filename, mode); Where filename is a null-terminated character sequence of type const char * (the same type that string literals have) representing the name of the file to be opened, and mode is an optional parameter with a combination of thefollowing flags:
UGC NET COMPUTER SCIENCE Operating Systems 02. 11. The maximum amount of information that is available in one portion of the disk access arm for a removal disk pack (without further movement of the arm with multiple heads) (A) a plate of data. (B) a cylinder of data. (C) a track of data. (D) a block of data. 12. UGC NET COMPUTER SCIENCE 1.A Critical region: In concurrent programming, a critical section/region is a piece of code that accesses a shared resource that must not be concurrently accessed by more than one thread of execution.Some synchronization mechanism is required at the entry and exit of the critical section to ensure exclusive use (Mutual exclusion), for example a semaphore. UGC NET COMPUTER SCIENCE 24. A. 100 K, 500 K, 200 K, 300 K and 600 K (in order) and processes of 212 K, 417 K, 112 K, and 426 K. According the to the first fit algorithm, the memmory will be scanned to find out the memory portion that is enough for the arriving process, The first such portion found is allocated to the process. UGC NET COMPUTER SCIENCE 1.A 2.B The Mandelbrot set is the set of values of c in the complex plane for which the orbit of 0 under iteration of the complex quadratic polynomial z n+1 = z n 2 + c remains bounded. That is, a complex number c is part of the Mandelbrot set if, when starting with z0 = 0 and applying the iteration repeatedly, the absolute value of z n remains bounded however large n gets. UGC NET COMPUTER SCIENCE Kruskal's algorithm is a greedy algorithm in graph theory that finds a minimum spanning tree for a connected weighted graph. This means it finds a subset of the edges that forms a tree that includes every vertex, where the total weight of all the edges in the tree is minimized. Where E is the number of edges in the graph and V is thenumber of
UGC NET COMPUTER SCIENCE The Object-Modelling Technique (OMT) is an object modelling language for software modelling and designing. It was developed around 1991 by Rumbaugh, Blaha, Premerlani, Eddy and Lorensen as a method to develop object-oriented systems and to support object-oriented programming. It describes Object model or static structure of the system. UGC NET COMPUTER SCIENCE B. A B-tree is a tree data structure that keeps data sorted and allows searches, sequential access, insertions, and deletions in logarithmic time. The B-tree is a generalization of a binary search tree in that a node can have more than two children. A B-tree is kept balanced by requiring that all leaf nodes be at the same depth. UGC NET COMPUTER SCIENCE A. 100 K, 500 K, 200 K, 300 K and 600 K (in order) and processes of 212 K, 417 K, 112 K, and 426 K. According the to the first fit algorithm, the memmory will be scanned to find out the memory portion that is enough for the arriving process, The first such portion found is allocated to the process. UGC NET COMPUTER SCIENCE Any grammar can be proved ambiguous if we are able to find at least one string with more than one left-most derivation accepted by thegrammar.
UGC NET COMPUTER SCIENCE 24. A. 100 K, 500 K, 200 K, 300 K and 600 K (in order) and processes of 212 K, 417 K, 112 K, and 426 K. According the to the first fit algorithm, the memmory will be scanned to find out the memory portion that is enough for the arriving process, The first such portion found is allocated to the process. UGC NET COMPUTER SCIENCE 17.A Freequency = 1/Period. So freeq = 1 / 1000 x 10^-3 Hz = 1 Hz = 10^-3 KHz 18.D A switch is nearly identical to a network hub, but a switch generally contains more intelligence than a hub.Unlike hubs, network switches are capable of inspecting data packets as they are received, determining the source and destination device of each packet, and forwarding them appropriately. UGC NET COMPUTER SCIENCE 11.B Refer Solution to question number 7 12.B In software project management, software testing, and software engineering, verification and validation (V&V) is the process of checking that a software system meets specifications and that it fulfils its intended purpose. UGC NET COMPUTER SCIENCE 11.Assume that we have constructor functions for both base class and derived class. Now consider the declaration in main( ). Base * P = new Derived; in what sequence will the constructor be called? UGC NET COMPUTER SCIENCE 01. _____ is process of extracting previously not known valid and actionable information from large data to make crucial business and strategic decisions. UGC NET COMPUTER SCIENCE 1.If a relation with a Schema R is decomposed into two relations R1 and R2 such that (R1 ∪ R2) = R1 then which one of the following is to be satisfied for a lossless joint decomposition (→ indicates functional dependency) (A) (R1 ∩ R2) → R1 or R1 ∩ R2 → R2 UGC NET COMPUTER SCIENCE Initialize the dictionary to contain all strings of length one. Find the longest string W in the dictionary that matches the current input. Emit the dictionary index for W to output and remove W from the input. Add W followed by the next symbol in the input to the dictionary. Goto Step 2.
UGC NET COMPUTER SCIENCE Data Communication and Computer Networks 01. 1. The technique of temporarily delaying outgoing acknowledgements so that they can be hooked onto the next outgoing data frame is known as 10. Match the following: a. Application layer 1. UGC NET COMPUTER SCIENCE A. In a binary tree of height h the total number of nodes is at most 20 + 21 + .. 2h = 2h + 1 – 1. A binary tree is a complete binary tree, when it has maximum number of nodes. 9. D. Let C (n) be the number of distinct binary trees with n nodes, Then: C (n) =. so for n=5, C (n) = 10! / (6!)5! = 42. 10. UGC NET COMPUTER SCIENCE 24. A. 100 K, 500 K, 200 K, 300 K and 600 K (in order) and processes of 212 K, 417 K, 112 K, and 426 K. According the to the first fit algorithm, the memmory will be scanned to find out the memory portion that is enough for the arriving process, The first such portion found is allocated to the process. UGC NET COMPUTER SCIENCE - TOPIC WISE SOLVED Computer Science's Topic wise questions and their answers for UGC NETExamination
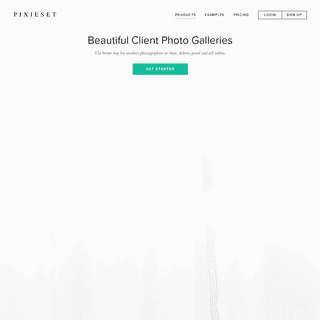
TUESDAY, JANUARY 20, 2015DATA STRUCTURES 03
21. Merge sort makes two recursive calls. Which statement is true after these two recursive calls finish, but before the merge step ? (A) The array elements form a heap. (B) Elements in each half of the array are sorted amongst themselves. (C) Elements in the first half of the array are less than or equal to elements in second half of the array. (D) All of the above 22. Searching for an element in the hash table requires O(1) time for the ___ time, whereas for direct addressing it holds for the ___ time. (A) worst case, average (B) worst case, worst case (C) average, worst case (D) best, average 23. An algorithm is made up of 2 modules M1 and M2. If time complexity of modules M1 and M2 are h(n) and g(n) respectively, the time complexity of the algorithm is (A) min (h(n), g(n)) (B) max (h(n), g(n)) (C) h(n) + g(n) (D) h(n) * g(n) 24. What is the maximum number of parenthesis that will appear on the stack at any one time for parenthesis expression given by (( ) ( ( ) )( ( ) ) )
(A) 2 (B) 3 (C) 4 (D) 5 25. The reverse polish notation equivalent to the infix expression ((A + B) * C + D)/(E + F + G) (A) A B + C * D + EF + G + / (B) A B + C D * + E F + G + / (C) A B + C * D + E F G + +/ (D) A B + C * D + E + F G + / 26. ___ comparisons are necessary in the worst case to find both the maximum and minimum of n numbers. (A) 2n – 2 (B) n +floor (lg n) – 2
(C) floor (3n/2) – 2 (D) 2 * lg n – 2 27. Let A and B be two n × n matrices. The efficient algorithm to multiply the two matrices has the time complexity (A) O(n3) (B) O(n2.81) (C) O(n2.67) (D) O(n2) 28. Assuming there are n keys and each key is in the range . The run time of bucket sort is (A) O(n) (B) O(n * lg n) (C) O(n * lg m) (D) O(n + m) 29.What is the value of the postfix expression ? a b c d + – ∗ (where a = 8, b = 4, c = 2 and d = 5) (A) – 3/8 (B) 8/3 (C) 24 (D) 24 30. If the queue is implemented with a linked list, keeping track of a front pointer and a rear pointer, which of these pointers will change during an insertion into a nonempty queue ? (A) Neither of the pointers change (B) Only front pointer changes (C) Only rear pointer changes (D) Both of the pointers changesSOLUTIONS
21. B
22. C
23. B
24. B
25. A
26. C
27. B
28. D
29. D
30. C
Posted by Unknown at11:14 AM
Reactions:
No comments:
Email This
BlogThis!
Share
to Twitter
Share
to Facebook
Share
to Pinterest
Labels: Computer Science, Data
Structures
, MCQ
, solved question
paper
,
UGC NET
TUESDAY, OCTOBER 29, 2013 PROGRAMMING (C, C++ ...) 02 11. Assume that we have constructor functions for both base class and derived class. Now consider the declaration in main( ). Base * P = new Derived; in what sequence will the constructor be called? (A) Derived class constructor followed by Base class constructor. (B) Base class constructor followed by derived class constructor. (C) Base class constructor will not be called. (D) Derived class constructor will not be called. 12. printf(“%c”, 100);(A) prints 100
(B) prints ASCII equivalent of 100(C) prints garbage
(D) none of the above 13. Which API is used to draw a circle ? (A) Circle( ) (B) Ellipse( ) (C) RoundRect( ) (D) Pie( ) 14. Which of the following are two special functions that are meant for handling exception, that occur during exception handling itself? (A) void terminate ( ) and void unexpected ( ) (B) Non void terminate ( ) and void unexpected ( ) (C) void terminate ( ) and non void unexpected ( ) (D) Non void terminate ( ) and non void unexpected ( ) 15. Match the following with respect to C++ data types: a. User defined type 1. Qualifier b. Built in type 2. Union c. Derived type 3. Void d. Long double 4. PointerCode :
a b c d
(A) 2 3 4 1
(B) 3 1 4 2
(C) 4 1 2 3
(D) 3 4 1 2
16. Enumeration is a process of (A) Declaring a set of numbers (B) Sorting a list of strings (C) Assigning a legal values possible for a variable (D) Sequencing a list of operators 17. Which of the following mode declaration is used in C++ to open afile for input?
(A) ios : : app
(B) in : : ios
(C) ios : : file
(D) ios : : in
18. What is the result of the following expression?(1 & 2) + (3 & 4)
(A) 1
(B) 3
(C) 2
(D) 0
SOLUTIONS
11. B
Here A derived class object is created first and then assigned to a base class pointer. Whenever a derived class object is created, the base class constructor gets called first and then the derived classconstructor.
12. B
13. B
14. A
The visual C++ Standard requires that UNEXPECTED() is called when a function throws an exception that is not on its throw list. The TERMINATE( ) function is used with visual C++ exception handling and is called in the following cases: * A matching catch handler cannot be found for a thrown C++exception.
* An exception is thrown by a destructor function during stackunwind.
* The stack is corrupted after throwing an exception. Both the functions does not return anything.15. A
16. C
An enum is a user-defined type consisting of a set of named constants called enumerators. The colors of the rainbow would be mapped likethis.:
_ enum rainbowcolors { red, orange, yellow, green, blue, indigo, violet) }_ Now internally, the compiler will use an int to hold these and if no values are supplied, red will be 0, orange is 1 etc.17. D
In order to open a file with a stream object we use its memberfunction open():
open (filename, mode); Where filename is a null-terminated character sequence of type const char * (the same type that string literals have) representing the name of the file to be opened, and mode is an optional parameter with a combination of the following flags: * _ios::in_ Open for input operations. * _ios::out_ Open for output operations. * _ios::binary_ Open in binary mode. * _ios::ate_ Set the initial position at the end of the file. If this flag is not set to any value, the initial position is the beginning of the file. * _ios::app_ All output operations are performed at the end of the file, appending the content to the current content of the file. This flag can only be used in streams open for output-only operations. * _ios::trunc_ If the file opened for output operations already existed before, its previous content is deleted and replaced by thenew one.
18. D
& represents bitwise AND. Converting the given values in the expression to 4 bit binary we have: (1 & 2) + (3 & 4) = (0001 & 0010) + (0011 & 0100) = (0000) + (0000) = 0 + 0 = 0 Posted by Unknown at9:00 PM
Reactions:
No comments:
Email This
BlogThis!
Share
to Twitter
Share
to Facebook
Share
to Pinterest
Labels: C , C++
, Computer
Science
, MCQ
, solved question
paper
,
UGC NET
Older Posts
Home
Subscribe to: Posts (Atom)SEARCH THIS BLOG
BLOG ARCHIVE
* ▼ 2015 (1)
* ▼ January (1) * Data Structures 03* ► 2013 (18)
* ► October (1)* ► August (3)
* ► July (14)
TOTAL PAGEVIEWS
0
20
1
48
2
25
3
45
4
15
5
43
6
90
7
73
8
28
9
40
10
57
11
40
12
48
13
18
14
13
15
33
16
30
17
38
18
35
19
35
20
45
21
48
22
73
23
68
24
40
25
28
26
30
27
13
28
38
29
28
48,701
(C) . Simple theme. Powered by Blogger .Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0