Are you over 18 and want to see adult content?
More Annotations
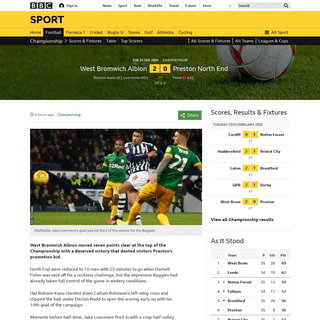
A complete backup of www.bbc.co.uk/sport/football/51532949
Are you over 18 and want to see adult content?
A complete backup of apostrophe.ua/article/lime/events/2020-02-24/kak-proshel-6-vyipusk-golosu-krani-10-i-komu-udalos-razvernut-
Are you over 18 and want to see adult content?

A complete backup of www.livehindustan.com/entertainment/story-indian-idol-11-finale-live-update-sunny-hindustani-rohit-raut-adr
Are you over 18 and want to see adult content?
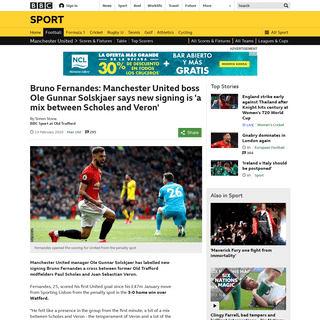
A complete backup of www.bbc.co.uk/sport/football/51607355
Are you over 18 and want to see adult content?

A complete backup of www.setn.com/News.aspx?NewsID=695884
Are you over 18 and want to see adult content?

A complete backup of news.cts.com.tw/cts/life/202002/202002251991697.html
Are you over 18 and want to see adult content?

A complete backup of www.nownews.com/news/20200225/3955266/
Are you over 18 and want to see adult content?

A complete backup of www.bfm.ru/news/437461
Are you over 18 and want to see adult content?
Favourite Annotations

Best Zero Gravity Chair Review Updated July 2019! - Best Zero Gravity Chair HQ
Are you over 18 and want to see adult content?

A complete backup of viverelosgatos.com
Are you over 18 and want to see adult content?
DealMirror.com: Best Deals for Designers & Developers - DealMirror - DealMirror
Are you over 18 and want to see adult content?

Gaming Asylum | The world's largest life community
Are you over 18 and want to see adult content?
Text
ESPAÑOL e INGLES
CCNA 3 CHAPTER 1 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 1 v5 Exam Answers 2013 Scaling NetworksCisco CCNA 3 Chapter 1 v5 ANSWERS1How can an enterprise network be designed to optimize bandwidth?by deploying a collapsed core modelby installing devices with failover capabilitiesby organizing the network to control traffic patternsby limiting the size of failure domains_____2Which statement describes a characteristic of CCNA 4 CHAPTER 4 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 4 v5 exam answers 2013CCNA 4 Chapter 4 v5 exam answers Routing and Switching Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141.What is a characteristic of Frame Relay that provides more flexibility than a dedicated line?Customers use dedicated circuits in increments of 64 kb/s.Dedicated physical circuits CCNA 1 CHAPTER 6 V5.0 ANSWERS CCNA 1 Chapter 6 v5.0 answers1.During the process of forwarding traffic, what will the router do immediately after matching the destination IP address to a network on a directly connected routing table entry?switch the packet to the directly connected interfacelook up the next-hop address for the packetdiscard the traffic after consulting the route tableanalyze the CCNA 3 CHAPTER 9 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 9 v5 Exam Answers 2013 Scaling NetworksRouting and Switching (Version 5.0) – ScaN Chapter 9 ExamThis exam will cover material from Chapter 9 of the CCNA R&S Scaling Networks curriculum.1Beginning with the Cisco IOS Software Release 15.0, which license is a prerequisite for installing additional technology pack licenses?DATAIPBase SECUC_____2How long is the evaluation CCNA 4 CHAPTER 8 V5 EXAM ANSWERS 2013 23. Fill in the blank. The syslog protocol uses UDP port 514 and is the most common method to access system messages provided by networking devices. CCNA 4 Chapter 8 v5 exam answers 2013, CISCO CCNA ANSWERS, CCNA 4 Ch 8 exam test CCNA 4 CHAPTER 9 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 9 v5 exam answers 2013CCNA 4 Chapter 9 v5 exam answers R&S Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141. Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information shouldnetwork engineers
CCNA 3 CHAPTER 4 V5.0 EXAM ANSWERS (ESPAÑOL) CCNA 3 Capítulo 4 v5 respuestas del examen 2013 Redes de escalaCCNA 3 Capítulo 4 v5 respuestas del examen Redes escalado 2014 Routing y SwitchingCapítulo 4 SCAN Exam - Redes de escala (versión 5.0)1¿Qué tres estándares Wi-Fi funcionan en el rango de 2,4 GHz de frecuencias? (Elija tres opciones).802.11ac 802.11g 802.11a 802.11n 802.11b_____3¿Qué característica de puntos de CCNA 4 CHAPTER 7 V5.0 EXAM ANSWERS (ESPAÑOL) CCNA 4 Capítulo 7 Examen v5 contesta 2013CCNA 4 Capítulo 7 Examen v5 contesta R & S Redes de conexiónCISCO CCNA RESPUESTAS V5 enrutamiento y la conmutación TEST DE PREGUNTAS Y RESPUESTAS 2013-20141. ¿Cómo es "tunneling" logrado en una VPN? Nuevas cabeceras de uno o más protocolos de VPN encapsula los paquetes originales. Todos lospaquetes entre
CCNA2 PRACTICE FINAL V5.0 EXAM ANSWERS (ESPAÑOL) …TRANSLATE THISPAGE
CCNA 2 Práctica Examen final v5.0 preguntas y respuestas 2013CCNA 2 Práctica Examen final v5.0 Preguntas y Respuestas 2013, CCNA 2 Routing y Switching Esenciales v5 Práctica Examen Final1¿Cuál es el orden de los tipos de paquetes que utiliza un enrutador OSPF para establecer la convergencia? Hola, DBD, LSR, LSU, LSAck LSAck, Hola, DBD, LSU, LSR LSU, LSAck, CCNA V5 EXAMENES ESPAÑOL INGLES CISCO CCNA v5 exam answers, CCNA 1 , CCNA 2 , CCNA 3 , CCNA 4 | enESPAÑOL e INGLES
CCNA 3 CHAPTER 1 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 1 v5 Exam Answers 2013 Scaling NetworksCisco CCNA 3 Chapter 1 v5 ANSWERS1How can an enterprise network be designed to optimize bandwidth?by deploying a collapsed core modelby installing devices with failover capabilitiesby organizing the network to control traffic patternsby limiting the size of failure domains_____2Which statement describes a characteristic of CCNA 4 CHAPTER 4 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 4 v5 exam answers 2013CCNA 4 Chapter 4 v5 exam answers Routing and Switching Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141.What is a characteristic of Frame Relay that provides more flexibility than a dedicated line?Customers use dedicated circuits in increments of 64 kb/s.Dedicated physical circuits CCNA 1 CHAPTER 6 V5.0 ANSWERS CCNA 1 Chapter 6 v5.0 answers1.During the process of forwarding traffic, what will the router do immediately after matching the destination IP address to a network on a directly connected routing table entry?switch the packet to the directly connected interfacelook up the next-hop address for the packetdiscard the traffic after consulting the route tableanalyze the CCNA 3 CHAPTER 9 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 9 v5 Exam Answers 2013 Scaling NetworksRouting and Switching (Version 5.0) – ScaN Chapter 9 ExamThis exam will cover material from Chapter 9 of the CCNA R&S Scaling Networks curriculum.1Beginning with the Cisco IOS Software Release 15.0, which license is a prerequisite for installing additional technology pack licenses?DATAIPBase SECUC_____2How long is the evaluation CCNA 4 CHAPTER 8 V5 EXAM ANSWERS 2013 23. Fill in the blank. The syslog protocol uses UDP port 514 and is the most common method to access system messages provided by networking devices. CCNA 4 Chapter 8 v5 exam answers 2013, CISCO CCNA ANSWERS, CCNA 4 Ch 8 exam test CCNA 4 CHAPTER 9 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 9 v5 exam answers 2013CCNA 4 Chapter 9 v5 exam answers R&S Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141. Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information shouldnetwork engineers
CCNA 3 CHAPTER 4 V5.0 EXAM ANSWERS (ESPAÑOL) CCNA 3 Capítulo 4 v5 respuestas del examen 2013 Redes de escalaCCNA 3 Capítulo 4 v5 respuestas del examen Redes escalado 2014 Routing y SwitchingCapítulo 4 SCAN Exam - Redes de escala (versión 5.0)1¿Qué tres estándares Wi-Fi funcionan en el rango de 2,4 GHz de frecuencias? (Elija tres opciones).802.11ac 802.11g 802.11a 802.11n 802.11b_____3¿Qué característica de puntos de CCNA 4 CHAPTER 7 V5.0 EXAM ANSWERS (ESPAÑOL) CCNA 4 Capítulo 7 Examen v5 contesta 2013CCNA 4 Capítulo 7 Examen v5 contesta R & S Redes de conexiónCISCO CCNA RESPUESTAS V5 enrutamiento y la conmutación TEST DE PREGUNTAS Y RESPUESTAS 2013-20141. ¿Cómo es "tunneling" logrado en una VPN? Nuevas cabeceras de uno o más protocolos de VPN encapsula los paquetes originales. Todos lospaquetes entre
CCNA2 PRACTICE FINAL V5.0 EXAM ANSWERS (ESPAÑOL) …TRANSLATE THISPAGE
CCNA 2 Práctica Examen final v5.0 preguntas y respuestas 2013CCNA 2 Práctica Examen final v5.0 Preguntas y Respuestas 2013, CCNA 2 Routing y Switching Esenciales v5 Práctica Examen Final1¿Cuál es el orden de los tipos de paquetes que utiliza un enrutador OSPF para establecer la convergencia? Hola, DBD, LSR, LSU, LSAck LSAck, Hola, DBD, LSU, LSR LSU, LSAck, CCNA 3 CHAPTER 6 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 6 v5 Exam Answers 2013 Scaling NetworksRouting and Switching (Version 5.0) – ScaN Chapter 6 ExamThis exam will cover material from Chapter 6 of the CCNA R&S Scaling Networks curriculum.1Which statement describes a multiarea OSPF network?It consists of multiple network areas that are daisy-chained together.It requires a three-layer hierarchical network design CCNA 3 CHAPTER 8 V5 EXAM ANSWERS R&S SCALING NETWORKS 2013 CISCO CCNA ANSWERS V5 ROUTING AND SWITCHING 2013-2014 QUESTIONS AND ANSWERS QUIZ TEST. CISCO CCNA Scaling Networks (Version 5.0) – ScaN Chapter 8 Exam – EIGRP Advanced Configurations and Troubleshooting. This exam will cover material from Chapter 8 of the CCNA R&S Scaling Networks curriculum. Refer to the exhibit. CCNA 2 ROUTING AND SWITCHING ESSENTIALS FINAL EXAM ANSWERS CCNA 2 Routing and Switching Essentials Final Exam Answers1.What are two features of a link-state routing protocol? (Choose two.)The database information for each router is obtained from the same source.Routers send triggered updates in response to a change.Routers create a topology of the network by using information from other routers. Paths are chosen based on the CCNA 4 CHAPTER 3 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 3 v5 exam answers 2013CCNA 4 Chapter 3 v5.0 Exam Answers R&S Connecting Networks – Broadband Solutions – 2013/2014CISCO CCNA Questions and Answers v5 Quiz TEST (Version 5.0) Chapter 3 ExamThis exam will cover material from Chapter 3 of the CCNA R&SConnecting Networks curriculum.1.Which address is used in theAddress field of a
CCNA 3 CHAPTER 3 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 3 v5 Exam Answers 2013 Scaling NetworksScaling Networks (Version 5.0) – ScaN Chapter 3 Exam1What is the most cost-effective method of solving interface congestion that is caused by a high level of traffic between two switches?increase uplink speedaggregate ports by using EtherChannelinsert a router between the switchesadd more VLANs to reduce broadcast CCNA 3 CHAPTER 2 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 2 v5 Exam Answers 2013 Scaling NetworksRouting and Switching Scaling Networks (Version 5.0) – ScaN Chapter 2 Exam1Refer to the exhibit. A network engineer is troubleshooting host connectivity on a LAN that uses a first hop redundancy protocol. Which IPv4 gateway address should be configured on the CCNA 2 CHAPTER 5 V5.0 ANSWERS CCNA 2 Chapter 5 v5.0 answers1Refer to the exhibit. The switch does the routing for the hosts that connect to VLAN 5. If the PC accesses a web server from the Internet, at what point will a VLAN number be added to the frame?No VLAN number is added to the frame in thisdesign.point Apoint
CCNA 2 PRACTICE FINAL EXAM V5.0 QUESTIONS AND ANSWERS 2013 CCNA 2 Practice Final Exam v5.0 Questions and Answers 20131What is the order of packet types used by an OSPF router to establish convergence?Hello, DBD, LSR, LSU, LSAckLSAck, Hello, DBD, LSU, LSRLSU, LSAck, Hello, DBD, LSRHello, LSAck, LSU, LSR, DBD2Which two keywords can be used in an access control list to replace a wildcard mask CCNA 4 CHAPTER 1 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 1 v5 exam answers 2013CCNA 4 Chapter 1 v5 exam answers 2014 Routing and Switching v5 Connecting Networks, CCNA 4 chapter 1 v5 CISCO CCNA ANSWERS1.What are two structured engineering CCNA 4 CHAPTER 5 V5 EXAM ANSWERS 2014 CCNA 4 Chapter 5 v5 exam answers 2014CCNA 4 Chapter 5 v5 exam answers R&S Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141 Typically, which network device would be used to perform NAT for a corporate environment?DHCP serverhost devicerouterserverswitch_____2 What is the group of publicIPv4
CCNA V5 EXAMENES ESPAÑOL INGLES CISCO CCNA v5 exam answers, CCNA 1 , CCNA 2 , CCNA 3 , CCNA 4 | enESPAÑOL e INGLES
CCNA 3 CHAPTER 1 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 1 v5 Exam Answers 2013 Scaling NetworksCisco CCNA 3 Chapter 1 v5 ANSWERS1How can an enterprise network be designed to optimize bandwidth?by deploying a collapsed core modelby installing devices with failover capabilitiesby organizing the network to control traffic patternsby limiting the size of failure domains_____2Which statement describes a characteristic of CCNA 2 V5.0 (INGLES) CCNA 2 Chapter 8 v5.0 answers. CCNA 2 Chapter 8 v5.0 Exam Answers Routing and Switching Essentials – Single-Area OSPF – 2013/2014. CISCO CCNA Questions and Answers v5 Quiz TEST (Version 5.0) Chapter 8 Exam. This exam will cover material from Chapter 8 of the CCNA R&S Routing and Switching Essentials curriculum. 1. CCNA 1 CHAPTER 6 V5.0 ANSWERS CCNA 1 Chapter 6 v5.0 answers1.During the process of forwarding traffic, what will the router do immediately after matching the destination IP address to a network on a directly connected routing table entry?switch the packet to the directly connected interfacelook up the next-hop address for the packetdiscard the traffic after consulting the route tableanalyze the CCNA 4 CHAPTER 4 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 4 v5 exam answers 2013CCNA 4 Chapter 4 v5 exam answers Routing and Switching Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141.What is a characteristic of Frame Relay that provides more flexibility than a dedicated line?Customers use dedicated circuits in increments of 64 kb/s.Dedicated physical circuits CCNA 2 CHAPTER 5 V5.0 ANSWERS CCNA 2 Chapter 5 v5.0 answers1Refer to the exhibit. The switch does the routing for the hosts that connect to VLAN 5. If the PC accesses a web server from the Internet, at what point will a VLAN number be added to the frame?No VLAN number is added to the frame in thisdesign.point Apoint
CCNA 2 CHAPTER 3 V5.0 ANSWERS CCNA 2 Chapter 3 v5.0 answersCCNA 2 Chapter 3 v5.0 answers Routing and SWitching Essentials, RSE exam, CISCO CCNA quIZ TEST ANSWERS, CCNA 2 CH 3 20141.Which three statements accurately describe VLAN types? (Choose three).After the initial boot of an unconfigured switch, all ports are members of the default VLAN.A management VLAN is any VLAN CCNA 4 CHAPTER 8 V5 EXAM ANSWERS 2013 23. Fill in the blank. The syslog protocol uses UDP port 514 and is the most common method to access system messages provided by networking devices. CCNA 4 Chapter 8 v5 exam answers 2013, CISCO CCNA ANSWERS, CCNA 4 Ch 8 exam testTHOMASTERRONES
1.Logical link control is implemented in software. 2.The data link layer uses LLC to communicate with the upper layers of the protocol suite. The LLC sublayer interacts directly with the NIC driver software. The LLC sublayer is responsible for the placement and retrieval of frames on and off the media. CCNA 3 CHAPTER 4 V5.0 EXAM ANSWERS (ESPAÑOL) CCNA 3 Capítulo 4 v5 respuestas del examen 2013 Redes de escalaCCNA 3 Capítulo 4 v5 respuestas del examen Redes escalado 2014 Routing y SwitchingCapítulo 4 SCAN Exam - Redes de escala (versión 5.0)1¿Qué tres estándares Wi-Fi funcionan en el rango de 2,4 GHz de frecuencias? (Elija tres opciones).802.11ac 802.11g 802.11a 802.11n 802.11b_____3¿Qué característica de puntos de CCNA V5 EXAMENES ESPAÑOL INGLES CISCO CCNA v5 exam answers, CCNA 1 , CCNA 2 , CCNA 3 , CCNA 4 | enESPAÑOL e INGLES
CCNA 3 CHAPTER 1 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 1 v5 Exam Answers 2013 Scaling NetworksCisco CCNA 3 Chapter 1 v5 ANSWERS1How can an enterprise network be designed to optimize bandwidth?by deploying a collapsed core modelby installing devices with failover capabilitiesby organizing the network to control traffic patternsby limiting the size of failure domains_____2Which statement describes a characteristic of CCNA 2 V5.0 (INGLES) CCNA 2 Chapter 8 v5.0 answers. CCNA 2 Chapter 8 v5.0 Exam Answers Routing and Switching Essentials – Single-Area OSPF – 2013/2014. CISCO CCNA Questions and Answers v5 Quiz TEST (Version 5.0) Chapter 8 Exam. This exam will cover material from Chapter 8 of the CCNA R&S Routing and Switching Essentials curriculum. 1. CCNA 1 CHAPTER 6 V5.0 ANSWERS CCNA 1 Chapter 6 v5.0 answers1.During the process of forwarding traffic, what will the router do immediately after matching the destination IP address to a network on a directly connected routing table entry?switch the packet to the directly connected interfacelook up the next-hop address for the packetdiscard the traffic after consulting the route tableanalyze the CCNA 4 CHAPTER 4 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 4 v5 exam answers 2013CCNA 4 Chapter 4 v5 exam answers Routing and Switching Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141.What is a characteristic of Frame Relay that provides more flexibility than a dedicated line?Customers use dedicated circuits in increments of 64 kb/s.Dedicated physical circuits CCNA 2 CHAPTER 5 V5.0 ANSWERS CCNA 2 Chapter 5 v5.0 answers1Refer to the exhibit. The switch does the routing for the hosts that connect to VLAN 5. If the PC accesses a web server from the Internet, at what point will a VLAN number be added to the frame?No VLAN number is added to the frame in thisdesign.point Apoint
CCNA 2 CHAPTER 3 V5.0 ANSWERS CCNA 2 Chapter 3 v5.0 answersCCNA 2 Chapter 3 v5.0 answers Routing and SWitching Essentials, RSE exam, CISCO CCNA quIZ TEST ANSWERS, CCNA 2 CH 3 20141.Which three statements accurately describe VLAN types? (Choose three).After the initial boot of an unconfigured switch, all ports are members of the default VLAN.A management VLAN is any VLAN CCNA 4 CHAPTER 8 V5 EXAM ANSWERS 2013 23. Fill in the blank. The syslog protocol uses UDP port 514 and is the most common method to access system messages provided by networking devices. CCNA 4 Chapter 8 v5 exam answers 2013, CISCO CCNA ANSWERS, CCNA 4 Ch 8 exam testTHOMASTERRONES
1.Logical link control is implemented in software. 2.The data link layer uses LLC to communicate with the upper layers of the protocol suite. The LLC sublayer interacts directly with the NIC driver software. The LLC sublayer is responsible for the placement and retrieval of frames on and off the media. CCNA 3 CHAPTER 4 V5.0 EXAM ANSWERS (ESPAÑOL) CCNA 3 Capítulo 4 v5 respuestas del examen 2013 Redes de escalaCCNA 3 Capítulo 4 v5 respuestas del examen Redes escalado 2014 Routing y SwitchingCapítulo 4 SCAN Exam - Redes de escala (versión 5.0)1¿Qué tres estándares Wi-Fi funcionan en el rango de 2,4 GHz de frecuencias? (Elija tres opciones).802.11ac 802.11g 802.11a 802.11n 802.11b_____3¿Qué característica de puntos de CCNA 3 CHAPTER 6 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 6 v5 Exam Answers 2013 Scaling NetworksRouting and Switching (Version 5.0) – ScaN Chapter 6 ExamThis exam will cover material from Chapter 6 of the CCNA R&S Scaling Networks curriculum.1Which statement describes a multiarea OSPF network?It consists of multiple network areas that are daisy-chained together.It requires a three-layer hierarchical network design CCNA 3 CHAPTER 8 V5 EXAM ANSWERS R&S SCALING NETWORKS 2013 CISCO CCNA ANSWERS V5 ROUTING AND SWITCHING 2013-2014 QUESTIONS AND ANSWERS QUIZ TEST. CISCO CCNA Scaling Networks (Version 5.0) – ScaN Chapter 8 Exam – EIGRP Advanced Configurations and Troubleshooting. This exam will cover material from Chapter 8 of the CCNA R&S Scaling Networks curriculum. Refer to the exhibit. CCNA 3 CHAPTER 9 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 9 v5 Exam Answers 2013 Scaling NetworksRouting and Switching (Version 5.0) – ScaN Chapter 9 ExamThis exam will cover material from Chapter 9 of the CCNA R&S Scaling Networks curriculum.1Beginning with the Cisco IOS Software Release 15.0, which license is a prerequisite for installing additional technology pack licenses?DATAIPBase SECUC_____2How long is the evaluation CCNA 4 CHAPTER 3 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 3 v5 exam answers 2013CCNA 4 Chapter 3 v5.0 Exam Answers R&S Connecting Networks – Broadband Solutions – 2013/2014CISCO CCNA Questions and Answers v5 Quiz TEST (Version 5.0) Chapter 3 ExamThis exam will cover material from Chapter 3 of the CCNA R&SConnecting Networks curriculum.1.Which address is used in theAddress field of a
CCNA 3 CHAPTER 3 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 3 v5 Exam Answers 2013 Scaling NetworksScaling Networks (Version 5.0) – ScaN Chapter 3 Exam1What is the most cost-effective method of solving interface congestion that is caused by a high level of traffic between two switches?increase uplink speedaggregate ports by using EtherChannelinsert a router between the switchesadd more VLANs to reduce broadcast CCNA 1 PRACTICE FINAL EXAM V5.0 CCNA 1 Practice Final Exam v5.0 Questions and Answers 20131. A network administrator has been issued a network address of 192.31.7.64/26. How many subnets of equal size could be created from the assigned /26 network by using a /28 prefix?4Remember:A /26 prefix requires the first 2 bits of the last octet for the network portion. CCNA V5 EXAMENES ESPAÑOL INGLES CISCO CCNA v5 exam answers, CCNA 1 , CCNA 2 , CCNA 3 , CCNA 4 | enESPAÑOL e INGLES
CCNA 4 CHAPTER 5 V5 EXAM ANSWERS 2014 CCNA 4 Chapter 5 v5 exam answers 2014CCNA 4 Chapter 5 v5 exam answers R&S Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141 Typically, which network device would be used to perform NAT for a corporate environment?DHCP serverhost devicerouterserverswitch_____2 What is the group of publicIPv4
CCNA 1 FINAL EXAM V5.0 2013 CCNA 1 R&S: Introduction to Networks Final Exam v5.0 2013CCNA 1 R&S: Introduction to Networks Final Exam v5.0 2013 routing and Switching Quiz test1Refer to the exhibit.The network administrator enters these commands into the R1 router:R1# copy running-config tftpAddress or name of remote host ?When the router prompts for an address orremote host
CCNA 2 CHAPTER 4 V5.0 ANSWERS CCNA 2 Chapter 4 v5.0 answers_____1.Refer to the exhibit. What will the router do with a packet that has a destination IP address of 192.168.12.227?Drop the packet.Send the packet out the GigabitEthernet0/1 interface.Send the packet out the Serial0/0/0 interface.Send the packet out the GigabitEthernet0/0 interface._____2.What two pieces of information are displayed in theoutput of
CCNA V5 EXAMENES ESPAÑOL INGLES CISCO CCNA v5 exam answers, CCNA 1 , CCNA 2 , CCNA 3 , CCNA 4 | enESPAÑOL e INGLES
CCNA 3 CHAPTER 1 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 1 v5 Exam Answers 2013 Scaling NetworksCisco CCNA 3 Chapter 1 v5 ANSWERS1How can an enterprise network be designed to optimize bandwidth?by deploying a collapsed core modelby installing devices with failover capabilitiesby organizing the network to control traffic patternsby limiting the size of failure domains_____2Which statement describes a characteristic of CCNA 3 CHAPTER 9 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 9 v5 Exam Answers 2013 Scaling NetworksRouting and Switching (Version 5.0) – ScaN Chapter 9 ExamThis exam will cover material from Chapter 9 of the CCNA R&S Scaling Networks curriculum.1Beginning with the Cisco IOS Software Release 15.0, which license is a prerequisite for installing additional technology pack licenses?DATAIPBase SECUC_____2How long is the evaluation CCNA 4 CHAPTER 4 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 4 v5 exam answers 2013CCNA 4 Chapter 4 v5 exam answers Routing and Switching Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141.What is a characteristic of Frame Relay that provides more flexibility than a dedicated line?Customers use dedicated circuits in increments of 64 kb/s.Dedicated physical circuits CCNA 1 CHAPTER 6 V5.0 ANSWERS CCNA 1 Chapter 6 v5.0 answers1.During the process of forwarding traffic, what will the router do immediately after matching the destination IP address to a network on a directly connected routing table entry?switch the packet to the directly connected interfacelook up the next-hop address for the packetdiscard the traffic after consulting the route tableanalyze the CCNA 4 CHAPTER 9 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 9 v5 exam answers 2013CCNA 4 Chapter 9 v5 exam answers R&S Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141. Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information shouldnetwork engineers
CCNA 4 CHAPTER 8 V5 EXAM ANSWERS 2013 23. Fill in the blank. The syslog protocol uses UDP port 514 and is the most common method to access system messages provided by networking devices. CCNA 4 Chapter 8 v5 exam answers 2013, CISCO CCNA ANSWERS, CCNA 4 Ch 8 exam test CCNA 2 CHAPTER 4 V5.0 ANSWERS CCNA 2 Chapter 4 v5.0 answers_____1.Refer to the exhibit. What will the router do with a packet that has a destination IP address of 192.168.12.227?Drop the packet.Send the packet out the GigabitEthernet0/1 interface.Send the packet out the Serial0/0/0 interface.Send the packet out the GigabitEthernet0/0 interface._____2.What two pieces of information are displayed in theoutput of
THOMASTERRONES
1.Logical link control is implemented in software. 2.The data link layer uses LLC to communicate with the upper layers of the protocol suite. The LLC sublayer interacts directly with the NIC driver software. The LLC sublayer is responsible for the placement and retrieval of frames on and off the media. CCNA 4 CHAPTER 7 V5.0 EXAM ANSWERS (ESPAÑOL) CCNA 4 Capítulo 7 Examen v5 contesta 2013CCNA 4 Capítulo 7 Examen v5 contesta R & S Redes de conexiónCISCO CCNA RESPUESTAS V5 enrutamiento y la conmutación TEST DE PREGUNTAS Y RESPUESTAS 2013-20141. ¿Cómo es "tunneling" logrado en una VPN? Nuevas cabeceras de uno o más protocolos de VPN encapsula los paquetes originales. Todos lospaquetes entre
CCNA V5 EXAMENES ESPAÑOL INGLES CISCO CCNA v5 exam answers, CCNA 1 , CCNA 2 , CCNA 3 , CCNA 4 | enESPAÑOL e INGLES
CCNA 3 CHAPTER 1 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 1 v5 Exam Answers 2013 Scaling NetworksCisco CCNA 3 Chapter 1 v5 ANSWERS1How can an enterprise network be designed to optimize bandwidth?by deploying a collapsed core modelby installing devices with failover capabilitiesby organizing the network to control traffic patternsby limiting the size of failure domains_____2Which statement describes a characteristic of CCNA 3 CHAPTER 9 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 9 v5 Exam Answers 2013 Scaling NetworksRouting and Switching (Version 5.0) – ScaN Chapter 9 ExamThis exam will cover material from Chapter 9 of the CCNA R&S Scaling Networks curriculum.1Beginning with the Cisco IOS Software Release 15.0, which license is a prerequisite for installing additional technology pack licenses?DATAIPBase SECUC_____2How long is the evaluation CCNA 4 CHAPTER 4 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 4 v5 exam answers 2013CCNA 4 Chapter 4 v5 exam answers Routing and Switching Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141.What is a characteristic of Frame Relay that provides more flexibility than a dedicated line?Customers use dedicated circuits in increments of 64 kb/s.Dedicated physical circuits CCNA 1 CHAPTER 6 V5.0 ANSWERS CCNA 1 Chapter 6 v5.0 answers1.During the process of forwarding traffic, what will the router do immediately after matching the destination IP address to a network on a directly connected routing table entry?switch the packet to the directly connected interfacelook up the next-hop address for the packetdiscard the traffic after consulting the route tableanalyze the CCNA 4 CHAPTER 9 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 9 v5 exam answers 2013CCNA 4 Chapter 9 v5 exam answers R&S Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141. Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information shouldnetwork engineers
CCNA 4 CHAPTER 8 V5 EXAM ANSWERS 2013 23. Fill in the blank. The syslog protocol uses UDP port 514 and is the most common method to access system messages provided by networking devices. CCNA 4 Chapter 8 v5 exam answers 2013, CISCO CCNA ANSWERS, CCNA 4 Ch 8 exam test CCNA 2 CHAPTER 4 V5.0 ANSWERS CCNA 2 Chapter 4 v5.0 answers_____1.Refer to the exhibit. What will the router do with a packet that has a destination IP address of 192.168.12.227?Drop the packet.Send the packet out the GigabitEthernet0/1 interface.Send the packet out the Serial0/0/0 interface.Send the packet out the GigabitEthernet0/0 interface._____2.What two pieces of information are displayed in theoutput of
THOMASTERRONES
1.Logical link control is implemented in software. 2.The data link layer uses LLC to communicate with the upper layers of the protocol suite. The LLC sublayer interacts directly with the NIC driver software. The LLC sublayer is responsible for the placement and retrieval of frames on and off the media. CCNA 4 CHAPTER 7 V5.0 EXAM ANSWERS (ESPAÑOL) CCNA 4 Capítulo 7 Examen v5 contesta 2013CCNA 4 Capítulo 7 Examen v5 contesta R & S Redes de conexiónCISCO CCNA RESPUESTAS V5 enrutamiento y la conmutación TEST DE PREGUNTAS Y RESPUESTAS 2013-20141. ¿Cómo es "tunneling" logrado en una VPN? Nuevas cabeceras de uno o más protocolos de VPN encapsula los paquetes originales. Todos lospaquetes entre
CCNA 2 V5.0 (INGLES) CCNA 2 Chapter 8 v5.0 answers. CCNA 2 Chapter 8 v5.0 Exam Answers Routing and Switching Essentials – Single-Area OSPF – 2013/2014. CISCO CCNA Questions and Answers v5 Quiz TEST (Version 5.0) Chapter 8 Exam. This exam will cover material from Chapter 8 of the CCNA R&S Routing and Switching Essentials curriculum. 1. CCNA 3 CHAPTER 6 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 6 v5 Exam Answers 2013 Scaling NetworksRouting and Switching (Version 5.0) – ScaN Chapter 6 ExamThis exam will cover material from Chapter 6 of the CCNA R&S Scaling Networks curriculum.1Which statement describes a multiarea OSPF network?It consists of multiple network areas that are daisy-chained together.It requires a three-layer hierarchical network design CCNA 3 CHAPTER 8 V5 EXAM ANSWERS R&S SCALING NETWORKS 2013 CISCO CCNA ANSWERS V5 ROUTING AND SWITCHING 2013-2014 QUESTIONS AND ANSWERS QUIZ TEST. CISCO CCNA Scaling Networks (Version 5.0) – ScaN Chapter 8 Exam – EIGRP Advanced Configurations and Troubleshooting. This exam will cover material from Chapter 8 of the CCNA R&S Scaling Networks curriculum. Refer to the exhibit. CCNA 4 CHAPTER 3 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 3 v5 exam answers 2013CCNA 4 Chapter 3 v5.0 Exam Answers R&S Connecting Networks – Broadband Solutions – 2013/2014CISCO CCNA Questions and Answers v5 Quiz TEST (Version 5.0) Chapter 3 ExamThis exam will cover material from Chapter 3 of the CCNA R&SConnecting Networks curriculum.1.Which address is used in theAddress field of a
CCNA 4 CHAPTER 4 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 4 v5 exam answers 2013CCNA 4 Chapter 4 v5 exam answers Routing and Switching Connecting NetworksCISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS 2013-20141.What is a characteristic of Frame Relay that provides more flexibility than a dedicated line?Customers use dedicated circuits in increments of 64 kb/s.Dedicated physical circuits CCNA 3 CHAPTER 3 V5 EXAM ANSWERS 2013 SCALING NETWORKS CCNA 3 Chapter 3 v5 Exam Answers 2013 Scaling NetworksScaling Networks (Version 5.0) – ScaN Chapter 3 Exam1What is the most cost-effective method of solving interface congestion that is caused by a high level of traffic between two switches?increase uplink speedaggregate ports by using EtherChannelinsert a router between the switchesadd more VLANs to reduce broadcast CCNA 2 CHAPTER 3 V5.0 ANSWERS CCNA 2 Chapter 3 v5.0 answersCCNA 2 Chapter 3 v5.0 answers Routing and SWitching Essentials, RSE exam, CISCO CCNA quIZ TEST ANSWERS, CCNA 2 CH 3 20141.Which three statements accurately describe VLAN types? (Choose three).After the initial boot of an unconfigured switch, all ports are members of the default VLAN.A management VLAN is any VLAN CCNA 2 PRACTICE FINAL EXAM V5.0 QUESTIONS AND ANSWERS 2013 CCNA 2 Practice Final Exam v5.0 Questions and Answers 20131What is the order of packet types used by an OSPF router to establish convergence?Hello, DBD, LSR, LSU, LSAckLSAck, Hello, DBD, LSU, LSRLSU, LSAck, Hello, DBD, LSRHello, LSAck, LSU, LSR, DBD2Which two keywords can be used in an access control list to replace a wildcard mask CCNA 4 CHAPTER 1 V5 EXAM ANSWERS 2013 CCNA 4 Chapter 1 v5 exam answers 2013CCNA 4 Chapter 1 v5 exam answers 2014 Routing and Switching v5 Connecting Networks, CCNA 4 chapter 1 v5 CISCO CCNA ANSWERS1.What are two structured engineering CCNA 3 CHAPTER 4 V5.0 EXAM ANSWERS (ESPAÑOL) CCNA 3 Capítulo 4 v5 respuestas del examen 2013 Redes de escalaCCNA 3 Capítulo 4 v5 respuestas del examen Redes escalado 2014 Routing y SwitchingCapítulo 4 SCAN Exam - Redes de escala (versión 5.0)1¿Qué tres estándares Wi-Fi funcionan en el rango de 2,4 GHz de frecuencias? (Elija tres opciones).802.11ac 802.11g 802.11a 802.11n 802.11b_____3¿Qué característica de puntos de CCNA V5 EXAMENES ESPAÑOL INGLES Saltar al contenido.* Acerca de
EXAMENES CCNA V5 EN ESPAÑOL E INGLES – COPIAR FACIL Examenes CCNA v5 en ESPAÑOL e INGLES – COPIAR FACIL Hola amigos, les dejo un video tutorial de como plajear facil en el examen de ccna, copiar facilsuerte y saludos…
Anuncios
Report this ad
Report this ad
__0 Comentarios
__Deja
un comentario
__ 4 diciembre, 2014thomasterrones
CCNA
CCNA 4 PRACTICE FINAL EXAM V5 R&S CONNECTING NETWORKS 2014 CCNA 4 PRACTICE FINAL EXAM V5 R&S CONNECTING NETWORKS 2014 CCNA 4 Practice Final Exam v5 R&S Connecting Networks 2014 Answers, Routing and Switching R&S, CISCO CCNA ANSWERS Quiz TEST PRACTICE FINAL2014
1
Which is a clientless VPN solution for mobile workers?GRE
SSL
SSH
IPsec
_______________________________________________________________2
For a VPN, which technology provides secure remote access overbroadband?
ADSL
QoS
IPSEC
LTE
_______________________________________________________________3
A technician is talking to a colleague at a rival company and comparing DSL transfer rates between the two companies. Both companies are in the same city, use the same service provider, and have the same rate/service plan. What is the explanation for why Company A reports higher download speeds than Company B? Company B shares the conection to the DSLAM with more clients thanCompany A.
Company A only uses microfilters on branch locations. COMPANY A IS CLOSER TO THE SERVICE PROVIDER. Company B has a higher volume of POTS voice traffic than Company A. _______________________________________________________________4
How does an SNMP trap aid network monitoring and management? It flags attempts to begin a DoS attack on the network. It collects information for the management station by using pollingdevices.
It reports to the management station by responding to polls. IT SENDS AN ALERT MESSAGE TO THE MANAGEMENT STATION WHEN A THRESHOLDIS REACHED.
_______________________________________________________________5
Refer to the exhibit. A PC at address 10.1.1.45 is unable to access the Internet. What is the most likely cause of the problem? The inside and outside interfaces have been configured backwards. The wrong netmask was used on the NAT pool. THE NAT POOL HAS BEEN EXHAUSTED. Access-list 1 has not been configured properly. _______________________________________________________________6
Refer to the exhibit. A network administrator has configured routers RTA and RTB, but cannot ping from serial interface to serial interface. Which layer of the OSI model is the most likely cause ofthe problem?
network
physical
application
DATA LINK
transport
_______________________________________________________________7
A user is unable to connect to the Internet. The network administrator decides to use the top-down troubleshooting approach. Which action should the administrator perform first? Check the patch cable connection from the PC to the wall. Run the tracert command to identify the faulty device. ENTER AN IP ADDRESS IN THE ADDRESS BAR OF THE WEB BROWSER TO DETERMINEIF DNS HAS FAILED.
Run the ipconfig command to verify the IP address, subnet mask, andgateway on the PC.
_______________________________________________________________8
Refer to the exhibit. A network administrator has configured router Edge_Router as shown in the output. Connectivity is failing between Edge_Router and a non-Cisco router running Frame Relay. What should be done to repair this Layer 2 connectivity? Modify the OSPF process-id from 10 to 1. Issue the frame-relay lmi-type ansi command on interface serial 0/1/0. ISSUE THE IETF KEYWORD WHEN ENABLING FRAME RELAY ON INTERFACE SERIAL0/1/0.
Issue the broadcast keyword when performing static mapping on interface serial 0/1/0. Correct the IP address used in the frame-relay map command. _______________________________________________________________9
What is an advantage of packet-switched technology over circuit-switched technology? Packet-switched networks do not require an expensive permanent connection to each endpoint. PACKET-SWITCHED NETWORKS CAN EFFICIENTLY USE MULTIPLE ROUTES INSIDE A SERVICE PROVIDER NETWORK. Packet-switched networks usually experience lower latency than circuit-switched networks experience. Packet-switched networks are less susceptible to jitter than circuit-switched networks are. _______________________________________________________________10
A network administrator has moved the company intranet web server from a switch port to a dedicated router interface. How can the administrator determine how this change has affected performance and availability on the company intranet? Interview departmental administrative assistants and determine if they think load time for web pages has improved. Compare the hit counts on the company web server for the current week to the values that were recorded in previous weeks. Determine performance on the intranet by monitoring load times of company web pages from remote sites. CONDUCT A PERFORMANCE TEST AND COMPARE WITH THE BASELINE THAT WAS ESTABLISHED PREVIOUSLY. _______________________________________________________________11
Which statement describes cable? The cable subscriber must purchase a cable modem termination system(CMTS)
DELIVERING SERVICES OVER A CABLE NETWORK REQUIRES DOWNSTREAM FREQUENCIES IN THE 50 TO 860 MHZ RANGE, AND UPSTREAM FREQUENCIES IN THE 5 TO 42 MHZ RANGE. Each cable subscriber has dedicated upstream and downstream bandwidth. Cable subscribers may expect up to 27 Mbps of bandwidth on the uploadpath.
_______________________________________________________________12
Which syslog entry has a severity code that indicates the most serioussituation?
MAR 17 06:42:22: 10.1.1.1 %LINK-3-UPDOWN: INTERFACE FASTETHERNET0/3, CHANGED STATE TO DOWN Mar 17 06:43:02: 10.1.1.1 %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/3, changed state to up Mar 17 06:42:21: 10.1.1.1 %CDP-4-DUPLEX_MISMATCH: duplex mismatch discovered on FastEthernet0/3 (not half duplex), with NA-1.30.foo.com FastEthernet0/24 (half duplex). Mar 17 06:03:21: 10.1.1.1 %SYS-6-BOOTTIME: Time taken to reboot after reload = 551932 seconds Mar 17 06:42:20: 10.1.1.1 %SYS-5-CONFIG_I: Configured from console by mwmwm on vty0 (192.168.254.5) Mar 17 06:42:22: 10.1.1.1 %LINEPROTO-5-UPDOWN: Line protocol on Interface FastEthernet0/3, changed state to down _______________________________________________________________13
Refer to the exhibit. R3 has the following configuration: R3# show running-config –some output text omitted–interface serial0
bandwidth 128
ip address 192.168.11.2 255.255.255.0 encapsulation frame-relay frame-relay map ip 192.168.11.2 30 broadcast After the command R3# debug frame-relay packet is executed, a ping is issued from R3 to R1 but is unsuccessful. Based on the output of the debug command shown in the graphic and the router configuration, whatis the problem?
AN INCORRECT IP ADDRESS EXISTS IN THE MAP STATEMENT. No clock rate has been configured on interface s0. The encapsulation frame-relay command is missing the broadcastkeyword.
There is an incorrect DLCI number in the map statement _______________________________________________________________14
A technician has been asked to configure a broadband connection for a teleworker. The technician has been instructed that all uploads and downloads for the connection must use existing phone lines. Which broadband technology should be used?cable
ISDN
DSL
POTS
_______________________________________________________________15
Which WAN technology uses a fixed payload of 48 bytes and is transported across both switched and permanent virtual circuits?ISDN
metro Ethernet
Frame Relay
ATM
_______________________________________________________________16
Which two statements about NetFlow are true? (Choose two.) NetFlow can be used to collect performance indicators such as interface errors, CPU usage, and memory usage. NetFlow traffic collectors use a “pull” based model to acquire traffic statistics from ports of interest. NetFlow can be used to monitor traffic statistics, including packetpayload content.
NETFLOW IS A CISCO-SPECIFIC FEATURE THAT ENABLES THE COLLECTION OF DETAILED TRAFFIC PROFILES. NETFLOW CAN BE USED TO CREATE BASELINE DOCUMENTATION. NetFlow is a network monitoring and event reporting tool. _______________________________________________________________17
Which three items are normally included when a log message is generated by a syslog client and forwarded to a syslog server? (Choosethree.)
community ID
checksum field
DATE AND TIME OF MESSAGE ID OF SENDING DEVICElength of message
MESSAGE ID
_______________________________________________________________18
Which statement is true about NCP? NCP establishes the initial link between PPP devices. NCP tests the link to ensure that the link quality is sufficient. EACH NETWORK PROTOCOL HAS A CORRESPONDING NCP. Link termination is the responsibility of NCP. _______________________________________________________________19
What is IPsec?
a protocol that is used to create a VPN at Layer 2 of the OSI model a 56-bit authentication and encryption method that must be used tocreate VPN tunnels
a means by which routers and VPN gateways read and forward packets with encrypted packet headers A SPECIFICATION FOR THE WAY IN WHICH A GROUP OF PROTOCOLS AND ALGORITHMS COMBINE TO CREATE VPNS _______________________________________________________________20
Launch PT Hide and Save PT Open the PT Activity. Perform the tasks in the activity instructions and then answer the question. Which message is displayed on the web browser?PPP IS WORKING!
Configured correctly!PPP configured!
Well done!
_______________________________________________________________21
Which statement is true about the operation of a site-to-site VPNconnection?
The data is encrypted by the VPN gateway at the sending side and decrypted by the target host. The data is encrypted by the sending host and decrypted by the VPN gateway at the receiving side. THE DATA IS ENCRYPTED AND DECRYPTED BY VPN GATEWAYS AT BOTH THE SENDING AND RECEIVING SIDES. The data is encrypted and decrypted by the sending and target hosts. _______________________________________________________________22
Refer to the exhibit. What type of Layer 2 encapsulation will be used for connection D on the basis of this configuration on a newlyinstalled router:
RtrA(config)# interface serial0/0/0 RtrA(config-if)# ip address 128.107.0.2 255.255.255.252 RtrA(config-if)# no shutdownPPP
HDLC
Ethernet
Frame Relay
_______________________________________________________________23
What are two characteristics of DSL technology? (Choose two.) FILTERS AND SPLITTERS ALLOW POTS AND DSL TRAFFIC TO SHARE THE SAMEMEDIUM.
DSL download rates are reduced by large volumes of POTS voice traffic. SERVICE PROVIDERS DEPLOY DSL IN THE LOCAL LOOP OF THE TELEPHONENETWORK.
DSL is a shared medium that allows many users to share bandwidth available from the DSLAM. Uploads typically offer larger transfer rates than downloads. _______________________________________________________________24
Refer to the exhibit. A small office uses an ISR to provide connectivity for both wired and wireless computers. One day, a sales person who is using a laptop cannot connect to Server1 through the wireless network. A network technician attempts to determine if the problem is on the wireless or the wired network. The technician pings successfully from the wireless laptop to the default gateway IP address on the ISR. What should be the next troubleshooting step? PING FROM SERVER1 TO ITS GATEWAY IP ADDRESS. Ping from Server1 to PC1. Ping from the laptop to the Ethernet port on the cable modem. Ping from the laptop to PC1 _______________________________________________________________25
What are two WAN connection enhancements that are achieved by implementing PPPoE? (Choose two.) Encapsulating Ethernet frames within PPP frames is an efficient use ofbandwidth.
DSL CHAP features are included in PPPoE. PPP ENABLES THE ISP TO ASSIGN AN IP ADDRESS TO THE CUSTOMER WANINTERFACE.
An Ethernet link supports a number of data link protocols. CHAP ENABLES CUSTOMER AUTHENTICATION AND ACCOUNTING. _______________________________________________________________26
A company has been assigned the 203.0.113.0/27 block of IP addresses by the ISP. The company has over 6000 internal devices. What type of NAT would be most appropriate for the employee workstations of thecompany?
dynamic NAT
DYNAMIC NAT OVERLOAD USING THE POOL OF ADDRESSESstatic NAT
port forwarding
PAT off the external router interface _______________________________________________________________27
What are two significant benefits that are provided by IPsec? (Choosetwo.)
ENCAPSULATION
ENCRYPTION
automatic creation of a private network automatic creation of a public networkauthentication
_______________________________________________________________28
What makes the Cisco EasyVPN application a useful tool for VPNimplementation?
It ensures that remote workers actually use the VPN for connectivity. IT SIMPLIFIES THE CONFIGURATION TASKS FOR THE DEVICE THAT IS USED ASTHE VPN SERVER.
It allows a greater variety of network devices to be used for VPNconnections.
It provides encryption algorithms unavailable in other systems. _______________________________________________________________29
What is the purpose of the Cisco Enterprise Architecture? It provides services and functionality to the core layer by grouping various components into a single component that is located in theaccess layer.
It replaces the three-layer hierarchical model with a flat networkapproach.
It reduces overall network traffic by grouping server farms, the management server, corporate intranet, and e-commerce routers in thesame layer.
IT PROVIDES AN ENTERPRISE-WIDE SYSTEM NETWORK ARCHITECTURE THAT HELPS PROTECT, OPTIMIZE, AND GROW THE NETWORK INFRASTRUCTURE THAT SUPPORTS THE BUSINESS PROCESSES OF A COMPANY. _______________________________________________________________30
Which basic network module of the Enterprise Architecture is the fundamental component of a campus design?services module
data center
enterprise edge
ACCESS-DISTRIBUTION
_______________________________________________________________31
Refer to the exhibit. An administrator is trying to configure PAT on R1, but PC-A is unable to access the Internet. The administrator tries to ping a server on the Internet from PC-A and collects the debugs that are shown in the exhibit. Based on this output, what is most likely the cause of the problem? The inside and outside NAT interfaces have been configured backwards. The NAT source access list matches the wrong address range. The address on Fa0/0 should be 64.100.0.1. THE INSIDE GLOBAL ADDRESS IS NOT ON THE SAME SUBNET AS THE ISP. _______________________________________________________________32
Which statement best describes a WAN? WAN is another name for the Internet. A WAN is a public utility that enables access to the Internet. A WAN INTERCONNECTS LANS OVER LONG DISTANCES. A WAN is a LAN that is extended to provide secure remote networkaccess.
_______________________________________________________________33
Refer to the exhibit. A ping from R1 to 10.1.1.2 is successful, but a ping from R1 to any address in the 192.168.2.0 network fails. What is the cause of this problem? There is no gateway of last resort at R1. The serial interface between the two routers is down. THE STATIC ROUTE FOR 192.168.2.0 IS INCORRECTLY CONFIGURED. A default route is not configured on R1. _______________________________________________________________34
Refer to the exhibit. Based on the configuration of R1, which device is the inside host and what is the inside local address of this host? PC-B with address 64.100.0.100 PC-A with address 64.100.0.100 PC-B WITH ADDRESS 209.165.200.225 PC-A with address 209.165.200.225 _______________________________________________________________35
Which three statements are true regarding the Frame Relay LMI? (Choosethree.)
The LMI types supported by Cisco routers are CISCO and IETF. THE LMI USES RESERVED DLCIS TO EXCHANGE MESSAGES BETWEEN THE DTE ANDDCE.
The LMI type must always be manually configured. The available LMI types are CHAP and PAP. THE LMI PROVIDES A VIRTUAL CIRCUIT (VC) STATUS MECHANISM. THE LMI TYPE CONFIGURED ON THE ROUTER MUST MATCH THE ONE USED ON THEFRAME RELAY SWITCH.
_______________________________________________________________36
What type of installation is needed to view syslog messages? A syslog client must be installed on a workstation. Because any network equipment can interpret syslog messages, nothing special is needed to view them. A syslog server must be installed on a router. A SYSLOG SERVER MUST BE INSTALLED ON A WORKSTATION. _______________________________________________________________37
What are three Frame Relay congestion management mechanisms? (Choosethree.)
BECN
FECN
DE
DLCI
Inverse ARP
LMI
_______________________________________________________________38
What is the relationship between the DE and the CIR in Frame Relay? The DE bit will indicate when the CIR committed burst size should beapplied.
WHEN THE CIR ON A GIVEN DLCI IS EXCEEDED, THE DE BIT OF FRAMES ABOVETHE CIR IS SET.
When the CIR is exceeded, an Inverse ARP DE message notifies the source to reduce frame transmission speed. The XON/XOFF flow control mechanism sets the DE bit when the CIR isexceeded.
_______________________________________________________________39
What can cause a reduction in available bandwidth on a cable broadbandconnection?
distance from the central office of the provider committed information ratesmaller cells
NUMBER OF SUBSCRIBERS _______________________________________________________________40
The output of the show ip interface brief command indicates that Serial0 is up but the line protocol is down. What are two possible causes for the line protocol being in the down state? (Choose two.) An incorrect default gateway is set on the router. KEEPALIVES ARE NOT BEING SENT BY THE REMOTE DEVICE. A network is missing from the routing protocol configuration. The clock rate is not set on the DTE. THE ENCAPSULATION ON THE SERIAL0 INTERFACE IS INCORRECT. _______________________________________________________________41
Launch PT Hide and Save PT Open the PT activity. Perform the tasks in the activity instructions and then answer the question. What is the IP address or range of IP addresses that are used as the inside global address for packets that originate from PC1 and are going to the server? 209.165.200.231 – 209.165.200.239192.168.10.21
209.165.200.225 – 200.165.200.229 192.168.10.1 – 192.168.10.254209.165.200.231
_______________________________________________________________42
Which three algorithms can be used to encrypt user data in an IPSec VPN framework? (Choose three.)AES
SHA
Diffie-Hellman
DES
ESP
3DES
_______________________________________________________________43
An administrator needs to configure a router so that internal network servers are accessible from the Internet. Each server is configured with a private IPv4 address. What type of NAT should the administratorconfigure?
dynamic NAT
PAT
NAT overloading
STATIC NAT
_______________________________________________________________44
Which two Layer 1 requirements are outlined in the Data-over-Cable Service Interface Specification (DOCSIS)? (Choose two.)CHANNEL WIDTHS
MODULATION TECHNIQUESmaximum data rate
access method
compression techniques _______________________________________________________________45
What are three parameters that are used by NetFlow to classify traffic? (Choose three.)TOS FIELD
number of packets
PORT NUMBER
INGRESS INTERFACE
egress interface
number of bytes
_______________________________________________________________46
Which two products are part of the Cisco Collaboration Architecture?(Choose two.)
Cisco Unified Computing CISCO UNIFIED COMMUNICATIONS Cisco Borderless End Point CISCO TELEPRESENCE Cisco Virtual Private Network _______________________________________________________________47
How many addresses will be available for dynamic NAT translation when a router is configured with the following commands? Router(config)#ip nat pool TAME 209.165.201.23 209.165.201.30 netmask255.255.255.224
Router(config)#ip nat inside source list 9 pool TAME31
24
9
10
8
7
_______________________________________________________________48
In the Cisco Enterprise Architectures network design approach what is the purpose of the enterprise edge module? to provide high-speed connectivity and protection for servers TO PROVIDE INTERNET, VPN, AND WAN CONNECTIONS to forward traffic from one local network to another to provide access to IP telephony services, wireless controller services, and unified services _______________________________________________________________49
How does STDM allocate bandwidth on a serial connection? It ensures that bandwidth is allocated to each channel or time slot regardless of whether the station using the channel has data totransmit.
It ensures each of the time slices are assigned to individualconversations.
IT KEEPS TRACK OF CONVERSATIONS THAT REQUIRE EXTRA BANDWIDTH. IT THEN DYNAMICALLY REASSIGNS UNUSED TIME SLICES ON AN AS-NEEDED BASIS. It statically assigns bandwidth based upon pre-assigned time slots. _______________________________________________________________50
Refer to the exhibit. While planning an upgrade, a network administrator uses the Cisco NetFlow utility to analyze data flow in the current network. What generated the most packets?TCP-OTHER
UDP-DNS
TCP-Telnet
UDP-other
ICMP
__0 Comentarios
__Deja
un comentario
__ 4 diciembre, 2014thomasterrones
CCNA 4 V5.0 (INGLES) CCNA 4 V5 FINAL EXAM CONNECTING NETWORKS ROUTING AND SWITCHING CCNA 4 V5 FINAL EXAM CONNECTING NETWORKS ROUTING AND SWITCHING CCNA 4 v5 Final Exam Routing and Switching Connecting Networks 1 WHY IS IT USEFUL CATEGORIZE NETWORKS BY SIZE WHEN DISCUSSING NETWORKDESIGN?
Knowing the number of connected devices will define how many additional layers will be added to the three-tier hierarchical networkdesign.
Knowing the number of connected devices will define how many multilayer switches will be necessary at the core layer. A high-level redundancy at the access layer may be better implemented if the number of connected devices is know. THE COMPLEXITY OF NETWORKING INFRASTRUCTURE WILL VARY ACCORDING TO THE NUMBER OF CONNECTED DEVICES. 2 WHICH TWO STATEMENTS ARE TRUE REGARDING A PPP CONNECTION BETWEEN TWO CISCO ROUTERS? (CHOOSE TWO.) Only a single NCP is allowed between the two routers. NCP terminates the link when data exchange is complete. With CHAP authentication, the routers exchange plain text passwords. LCP TESTS THE QUALITY OF THE LINK. LCP MANAGES COMPRESSION ON THE LINK. 3 WHAT IS A DISADVANTAGE OF A PACKET-SWITCHED NETWORK COMPARED TO A CIRCUIT-SWITCHED NETWORK?fixed capacity
HIGHER LATENCY
less flexibility
higher cost
4 WHICH STATEMENT DESCRIBES A CHARACTERISTIC OF DENSE WAVELENGTH DIVISION MULTIPLEXING (DWDM)? it assigns incoming electrical signals to specific frequencies. IT CAN BE USED IN LONG-RANGE COMMUNICATIONS, LIKE CONNECTIONS BETWEENISPS.
it enables bidirectional communications over one pair of coppercables.
it supports the SONET standard, but not the SDH standard.5
REFER TO THE EXHIBIT. A NETWORK ADMINISTRATOR IS TROUBLESHOOTING THE OSPF NETWORK. THE 10.10.0.0/16 NETWORK IS NOT SHOWING UP IN THE ROUTING TABLE OF ROUTER1. WHAT IS THE PROBABLE CAUSE OF THIS PROBLEM? The OSPF process is configured incorrectly on Router1. THERE IS AN INCORRECT WILDCARD MASK STATEMENT FOR NETWORK 10.10.0.0/16ON ROUTER2.
The OSPF process is not running on Router2. The serial interface on Router2 is down. 6 THE SECURITY POLICY IN A COMPANY SPECIFIES THAT THE STAFF IN THE SALES DEPARTMENT MUST USE A VPN TO CONNECT TO THE CORPORATE NETWORK TO ACCESS THE SALES DATA WHEN THEY TRAVEL TO MEET CUSTOMERS. WHAT COMPONENT IS NEEDED BY THE SALES STAFF TO ESTABLISH A REMOTE VPNCONNECTION?
VPN appliance
VPN concentrator
VPN CLIENT SOFTWARE
VPN gateway
7 A NETWORK ADMINISTRATOR IS TROUBLESHOOTING THE DYNAMIC NAT THAT IS CONFIGURED ON ROUTER R2. WHICH COMMAND CAN THE ADMINISTRATOR USE TO SEE THE TOTAL NUMBER OF ACTIVE NAT TRANSLATIONS AND THE NUMBER OF ADDRESSES THAT ARE ALLOCATED FROM THE NAT POOL? R2# show ip nat translations R2# clear ip nat translation R2# show running-config R2# SHOW IP NAT STATISTICS 8 WHICH THREE PARTS OF A FRAME RELAY LAYER 2 PDU ARE USED FOR CONGESTION CONTROL? (CHOOSE THREE.)THE FECN BIT
THE BECN BIT
the C/R bit
the 10-bit DLCI
the Extended Address fieldTHE DE BIT
9 WHICH TWO STATEMENTS CORRECTLY DESCRIBE ASYMMETRIC ENCRYPTION USED WITH AN IPSEC VPN? (CHOOSE TWO.) The same encryption keys must be manually configured on each device. PUBLIC KEY ENCRYPTION IS A TYPE OF ASYMMETRIC ENCRYPTION. ENCRYPTION AND DECRYPTION USE A DIFFERENT KEY. A shared secret key is used to perform encryption and descryption. AES is an example of an asymmetric encryption protocol. 10 WHICH WAN TECHNOLOGY CAN SERVE AS THE UNDERLYING NETWORK TO CARRY MULTIPLE TYPES OF NETWORK TRAFFIC SUCH AS IP, ATM, ETHERNET, AND DSL?MPLS
ISDN
Ethernet WAN
Frame Relay
11 DRAG AND DROOP
PLACE THE OPTIONS IN THE FOLLOWING ORDER:PAP CHARACTERISTICS
USES TWO-WAY HANDSHAKESINGLE CHALLENGE
WEAK AUTHENTICATION
CLEAR TEXT PASSWORDS CHAP CHARACTERISTICS USES THREE-WAY HANDSHAKEREPEATED CHALLENGES
STRONG AUTHENTICATIONENCRYPTED PASSWORDS
12 WHICH COMMAND CAN BE USED TO CHECK THE INFORMATION ABOUT CONGESTION ON A FRAME RELAY LINK? show frame-relay lmishow interfaces
SHOW FRAME-RELAY PVC show frame-relay map 13 WHICH TWO STATEMENTS DESCRIBE REMOTE ACCESS VPNS? (CHOOSE TWO.) CLIENT SOFTWARE IS USUALLY REQUIRED TO BE ABLE TO ACCESS THE NETWORK. Remote access VPNs are used to connect entire networks, such as a branch office to headquarters. REMOTE ACCESS VPNS SUPPORT THE NEEDS OF TELECOMMUTERS AND MOBILEUSERS.
A leased line is required to implement remote access VPNs. End users are not aware that VPNs exists.14
REFER TO THE EXHIBIT. WHICH THREE STEPS ARE REQUIRED TO CONFIGURE MULTILIK PPP ON THE HQ ROUTER? (CHOOSE THREE.) Bind the multilink bundle to the Fast Ethernet interface. Enable PPP encapsulation on the multilink interface. ASSIGN THE SERIAL INTERFACES TO THE MULTILINK BUNDLE. CREATE AND CONFIGURE THE MULTILINK INTERFACE. Assign the Fast Ethernet interface to the multilink bundle ENABLE PPP ENCAPSULATION ON THE SERIAL INTERFACES. 15 WHAT ARE TWO EXAMPLES OF NETWORK PROBLEMS THAT ARE FOUND AT THE DATA LINK LAYER? (CHOOSE TWO.) incorrect interface clock rates late collisions and jabberFRAMING ERRORS
electromagnetic interface ENCAPSULATION ERRORS 16 WHAT IS THE PROTOCOL THAT PROVIDES ISPS THE ABILITY TO SEND PPP FRAMES OVER DSL NETWORKS?CHAP
ADSL
PPPOE
LTE
17 WHAT IS REQUIRED FOR A HOST TO USE AN SSL VPN TO CONNECT TO A REMOTE NETWORK DEVICE? The host must be connected to wired network. A site-to-site VPN must be preconfigured. A WEB BROWSER MUST BE INSTALLED ON THE HOST. VPN client software must be installed.18
REFER TO THE EXHIBIT. A NETWORK ADMINISTRATOR HAS IMPLEMENTED THE CONFIGURATION IN THE DISPLAYED OUTPUT. WHAT IS MISSING FROM THE CONFIGURATION THAT WOULD BE PREVENTING OSPF ROUTING UPDATES FROM PASSING TO THE FRAME RELAY SERVICE PROVIDER? The command to disable split horizon has not been issued. The passive-interface command has not been issued on interface serial0/1/0
The directly connected neighbor should have been identified by usingstatic mapping.
THE BROADCAST KEYWORD HAS NOT BEEN ISSUED.19
REFER TO THE EXHIBIT. AN ADMINISTRATOR IS CONFIGURING NAT TO PROVIDE INTERNET ACCESS TO THE INSIDE NETWORK. AFTER THE CONFIGURTATION IS COMPLETED, USERS ARE UNABLE TO ACCESS THE INTERNET. WHAT IS THE CAUSEOF THE PROBLEM?
The inside and outside interfaces are backwards. The ACL is referencing the wrong network address. THE NAT INSIDE SOURCE COMMAND IS REFERRING TO THE WRONG ACL. The NAT pool is using an invalid address range. 20 A COMPANY CONNECTS TO ONE ISP VIA MULTIPLE CONNECTIONS. WHAT IS THE NAME GIVEN TO THIS TYPE OF CONNECTION?multihomed
single-homed
dual-multihomed
DUAL-HOMED
21
REFER TO THE EXHIBIT. ON THE BASIS OF THE OUTPUT, WHICH TWO STATEMENTS ABOUT NETWORK CONNECTIVITY ARE CORRECT? (CHOOSE TWO.) THERE IS CONNECTIVITY BETWEEN THIS DEVICE AND THE DEVICE AT192.168.100.1.
The average transmission time between the two hosts is 2 miliseconds. This host does not have a default gateway configured. The connectivity between these two hosts allows for videoconferencingcalls.
THERE ARE 4 HOPS BETWEEN THIS DEVICE AND THE DEVICE AT 192.168.100.1. 22 A NETWORK ADMINISTRATOR IS CONFIGURING A PPP LINK WITH THECOMMANDS:
R1(CONFIG-IF)# ENCAPSULATION PPP R1(CONFIG-IF)# PPP QUALITY 70 WHAT IS THE EFFECT OF THESE COMMANDS? The NCP will send a message to the sending device if the link usagereaches 70 percent.
THE PPP LINK WILL BE CLOSED DOWN IF THE LINK QUALITY DROPS BELOW 70PERCENT.
The LCP establishment phase will not start until the bandwidth reaches70 percent or more.
The PPP link will not be established if more than 30 percent of options cannot be accepted. 23 WHICH IEEE STANDARD DEFINES THE WIMAX TECHNOLOGY?802.5
802.11
802.16
802.3
24 WHICH THREE FLOWS ASSOCIATED WITH CONSUMER APPLICATIONS ARE SUPPORTED BY NETFLOW COLLECTORS? (CHOOSE THREE.)ACCOUNTING
NETWORK MONITORING
error correction
bandwidth regulationquality of service
BILLING
25
REFER TO THE EXHIBIT. WHAT KIND OF NAT IS BEING CONFIGURED ON R1?NAT overload
dynamic NAT
PORT FORWARDING
PAT
26
27 WHAT IS THE DEFAULT LOCATION FOR CISCO ROUTERS AND SWITCHES TO SEND CRITICAL LOGGING EVENTS?syslog server
virtual terminal
CONSOLE PORT
auxiliary port
28 IN THE DATA GATHERING PROCESS, WHICH TYPE OF DEVICE WILL LISTEN FOR TRAFFIC, BUT ONLY GATHER TRAFFIC STATISTICS?SNMP agent
NETFLOW COLLECTOR
syslog server
NMS
29 WHAT IS A CHARACTERISTIC OF FRAME RELAY THAT ALLOWS CUSTOMER DATA TRANSMISSIONS TO DYNAMICALLY “BURST” OVER THEIR CIR FOR SHORTPERIODS OF TIME?
The combination of LMI status messages and Inverse ARP messages enables the CIR to be exceeded. THE PHYSICAL CIRCUITS OF THE FRAME RELAY NETWORK ARE SHARED BETWEEN SUBSCRIBERS AND THERE MAY BE TIMES WHEN UNUSED BANDWIDTH IS AVAILABLE. BECN and FECN messages notify the router that the CIR can be exceeded. Bursting is enabled by the configuration of multiple subinterfaces on one physical interface. 30 WHICH SNMP MESSAGE TYPE INFORMS THE NETWORK MANAGEMENT SYSTEM (NMS) IMMEDIATELY OF CERTAIN SPECIFIED EVENTS?GET response
SET request
GET request
TRAP
31 WHICH STATEMENT IS A CHARACTERISTIC OF SNMP MIBS? The SNMP agent uses the SNMP manager to access information within theMIB.
The MIB structure for a given device includes only variables that are specific to that device or vendor. The MIB organizes variables in a flat manner. THE NMS MUST HAVE ACCESS TO THE MIB IN ORDER FOR SNMP TO OPERATEPROPERLY.
32 WHAT BENEFIT DOES NAT64 PROVIDE? IT ALLOWS SITES TO CONNECT IPV6 HOSTS TO AN IPV4 NETWORK BY TRANSLATING THE IPV6 ADDRESSES TO IPV4 ADDRESSES. It allows sites to connect multiple IPv4 hosts to the Internet via the use of a single public IPv4 address. It allows sites to use private IPv4 addresses, and thus hides the internal addressing structure form hosts on public IPv4 networks. It allows sites to use private IPv6 addresses and translates them to global IPv6 addresses. 33 WHAT IS THE EXPECTED BEHAVIOR OF AN ADSL SERVICE? The user can select the upload and download rates based on need. The download and upload rates are the same. The upload rate is faster than the download rate. THE DOWNLOAD RATE IS FASTER THAN THE UPLOAD RATE. 34 THE DLCI NUMBER ASSIGNED TO A FRAME RELAY CIRCUIT IS TO BE MANUALLY ADDED ON A POINT-TO-POINT LINK. WHICH THREE SUBINTERFACE COMMANDS COULD BE USED TO COMPLETE THE CONFIGURATION? (CHOOSE THREE.) frame-relay map ip ip-address dlci frame-relay map ip ip-address dlci broadcastno shutdown
IP ADDRESS IP-ADDRESS MASK encapsulation farme-relayBANDWIDTH KILOBITS
FARME-RELAY INTERFACE DLCI DLCI 35 A GROUP OF WINDOWS PCS IN A NEW SUBNET HAS BEEN ADDED TO AN ETHERNET NETWORK. WHEN TESTING THE CONNECTIVITY, A TECHNICIAN FINDS THAT THESE PCS CAN ACCESS LOCAL NETWORK RESOURCES BUT NOT THE INTERNET RESOURCES. TO TROUBLESHOOT THE PROBLEM, THE TECHNICIAN WANTS TO INITIALLY CONFIRM THE IP ADDRESS AND DNS CONFIGURATIONS ON THE PCS, AND ALSO VERIFY CONNECTIVITY TO THE LOCAL ROUTER. WHICH THREE WINDOWS CLI COMMANDS AND UTILITIES WILL PROVIDE THE NECESARY INFORMATION?(CHOOSE THREE.)
tracert
telnet
PING
netsh interface ipv6 show neighborNSLOOKUP
arp -a
IPCONFIG
36
REFER TO THE EXHIBIT. ROUTER R1 WAS CONFIGURED BY A NETWORK ADMINISTRATOR TO USE SNMP VERSION 2. THE FOLLOWING COMMANDS WEREISSUED:
R1(config)# snmp-server community batonaug ro SNMP_ACL R1(config)# snmp-server contact Wayne World R1(config)# snmp-server host 192.168.1.3 version 2c batonaug R1(config)# ip access-list standard SNMP_ACL R1(config-std-nacl)# permit 192.168.10.3 WHY IS THE ADMINISTRATOR NOT ABLE TO GET ANY INFORMATION FROM R1? The snmp-server community command needs to include the rw keyword. The snmp-server location command is missing. THERE IS A PROBLEM WITH THE ACL CONFIGURATION. The snmp-server enable traps command is missing. 37 WHICH BROADBAND TECHNOLOGY WOULD BE BEST FOR A SMALL OFFICE THAT REQUIRES FAST UPSTREAM CONNECTIONS?DSL
Cable
FIBER-TO-THE-HOME
WiMax
38
REFER TO THE EXHIBIT. THE INSIDE LOCAL IP ADDRESS OF PC-A IS 192.168.0.200. WHAT WILL BE THE INSIDE GLOBAL ADDRESS OF PACKETS FROM PC-A AFTER THEY ARE TRANSLATED BY R1?192.168.0.1
172.16.0.1
209.165.200.225
10.0.0.1
192.168.0.200
39 WHAT IS A TYPE OF VPN THAT IS GENERALLY TRANSPARENT TO THE ENDUSER?
remote access
public
SITE-TO-SITE
private
40 WHICH TWO STATEMENTS ABOUT DSL ARE TRUE? (CHOOSE TWO.) USER CONNECTIONS ARE AGGREGATED AT A DSLAM LOCATED AT THE CO uses RF signal transmission users are on a shared medium LOCAL LOOP CAN BE UP TO 3.5 MILES (5.5KM) physical and data link layers are defined by DOCSIS41
REFER TO THE EXHIBIT. WHICH THREE EVENTS WILL OCCUR AS A RESULT OF THE CONFIGURATION SHOWN ON R1? (CHOOSE THREE.) Only traffic that originates from the GigabitEthernet 0/1 interfacewill be monitored.
MESSAGES THAT ARE SENT TO THE SYSLOG SERVER WILL BE LIMITED TO LEVELS3 OR LOWER.
MESSAGES THAT ARE SENT TO THE SYSLOG SERVER WILL USE 192.168.1.5 AS THE DESTINATION IP ADDRESS. THE SYSLOG MESSAGES WILL CONTAIN THE IP ADDRESS THE GIGABITETHERNET0/1 INTERFACE.
Messages that are sent to the syslog server will be limited to levels3 and higher.
For multiple occurrences of the same error, only the first three messages will be sent to the server. 42 WHICH TWO CHARACTERISTICS DESCRIBE TIME-DIVISION MULTIPLEXING?(CHOOSE TWO.)
TRAFFIC IS ALLOCATED BANDWIDTH ACROSS A SINGLE WIRE BASED ON PREASSIGNED TIME SLOTS. Bandwidth is allocated to channels based on whether a station has datato transmit.
Encoding technology provides high data throughput in a minimum RF spectrum by supporting parallel data transmission. DATA CAPACITY ACROSS A SINGLE LINK INCREASES AS BITS FROM MULTIPLE SOURCES ARE TRANSMITTED USING INTERLEAVED SLICES OF TIME. Depending on the configured layer 2 protocol, data is transmitted across two or more channels via the use of time slots. 43 WHICH TWO SPECIALIZED TROUBLESHOOTING TOOLS CAN MONITOR THE AMOUNT OF TRAFFIC THAT PASSES THROUGH A SWITCH? (CHOOSE TWO.)TDR
DTX cable analyzer
NAM
digital multimeter
PORTABLE NETWORK ANALYZER 44 WHICH CIRCUMSTANCE WOULD RESULT IN AN ENTERPRISE DECIDING TO IMPLEMENT A CORPORATE WAN? WHEN ITS EMPLOYEES BECOME DISTRIBUTED ACROSS MANY BRANCH LOCATIONS when the enterprise decides to secure its corporate LAN when the network will span multiple buildings when the number of employees exceeds the capacity of the LAN 45 WHICH ALGORITHM IS CONSIDERED INSECURE FOR USE IN IPSEC ENCRYPTION?RSA
3DES
SHA-1
AES
46 WHAT IS ONE ADVANTAGE TO DESIGNING NETWORKS IN BULDING BLOCK FASHION FOR LARGE COMPANIES? fewer required physical resources increased network access time coarse security controlFAILURE ISOLATION
47 WHICH TWO TECHNOLOGIES ARE IMPLEMENTED BY ORGANIZATIONS TO SUPPORT TELEWORKER REMOTE CONNECTIONS? (CHOOSE TWO.)CMTS
VPN
CDMA
IPSEC
DOCSIS
48 A BRANCH OFFICE USES A LEASED LINE TO CONNECT TO THE CORPORATE NETWORK. THE LEAD NETWORK ENGINEER CONFIRMS CONNECTIVITY BETWEEN USERS IN THE BRANCH OFFICE, BUT NONE OF THE USERS CAN ACCESS CORPORATE HEADQUARTERS. SYSTEM LOGS INDICATE THAT NOTHING HAS CHANGED IN THE BRANCH OFFICE NETWORK. WHAT SHOULD THE ENGINEER CONSIDER NEXT TO RESOLVE THIS NETWORK OUTAGE? The network technician for the branch office should troubleshoot the switched infrastructure. The server administrator in the branch office should reconfigured theDHCP server.
THE SERVICE PROVIDER FOR THE BRANCH OFFICE SHOULD TROUBLESHOOT THE ISSUE STARTING FROM THE POINT OF DEMARCATION. The system administartor in the branch office should reconfigure the default gateway on the user PCs.49
REFER TO THE EXHIBIT. WHICH IP ADDRESS IS CONFIGURED ON THE PHYSICAL INTERFACE OF THE CORP ROUTER?10.1.1.1
209.165.202.134
10.1.1.2
209.165.202.133
50 HOW MANY 64 KB/S VOICE CHANNELS ARE COMBINED TO PRODUCE A T1 LINE?8
32
24
16
51 WHICH NETWORK MODULE MAINTAINS THE RESOURCES THAT EMPLOYEES, PARTNERS, AND CUSTOMERS RELY ON TO EFFECTIVELY CREATE, COLABORATE, AND INTERACT WITH INFORMATION?services
access-distribution
DATA-CENTER
enterprise edge
52 WHICH BROADBAND SOLUTION IS APPROPRIATE FOR A HOME USER WHO NEEDS A WIRED CONNECTION NOT LIMITED BY DISTANCE?ADSL
CABLE
DSL
WiMax
53 A NETWORK ADMINISTRATOR IS ASKED TO DESIGN A SYSTEM TO ALLOW SIMULTANEOUS ACCESS TO THE INTERNET FOR 250 USERS. THE ISP CAN ONLY SUPPLY FIVE PUBLIC IP ADDRESSES FOR THIS NETWORK. WHAT TECHNOLOGY CAN THE ADMINISTRATOR USE TO ACCOMPLISH THIS TASK? classless interdomain routing variable length subnet masksclassful subnetting
PORT-BASED NETWORK ADDRESS TRANSLATION 54 WHAT IS THE PURPOSE OF A MESSAGE HASH IN A VPN CONNECTION? It ensures that the data is coming from the correct source. It ensures that the data cannot be duplicated and replayed to thedestination.
IT ENSURES THAT THE DATA HAS NOT CHANGED WHILE IN TRANSIT. It ensures that the data cannot be read in plain text. 55 WHICH TYPE OF TRAFFIC WOULD MOST LIKELY HAVE PROBLEMS WHEN PASSING THROUGH A NAT DEVICE?DNS
Telnet
HTTP
ICMP
IPSEC
56 USERS ARE REPORTING LONGER DELAYS IN AUTHENTICATION AND IN ACCESSING NETWORK RESOURCES DURING CERTAIN TIME PERIODS OF THE WEEK. WHAT KIND OF INFORMATION SHOULD NETWORK ENGINEERS CHECK TO FIND OUT IF THIS SITUATION IS PART OF A NORMAL NETWORK BEHAVIOR? network configuration files syslog records and messages debug output and packet captures THE NETWORK PERFORMANCE BASELINE 57 WHAT ARE THREE BENEFITS OF USING FRAME RELAY FOR WAN CONNECTIVITY?(CHOOSE THREE.)
MATURE TECHNOLOGY
QoS support using the IP precedence field integrated encryption ONE PHYSICAL INTERFACE THAT CAN BE USED FOR SEVERAL CIRCUITSREASONABLE COST
seamless direct connectivity to an Ethernet LAN 58 WHAT TYPE OF INFORMATION IS COLLECTED BY CISCO NETFLOW?interface errors
TRAFFIC STATISTICS
memory usage
CPU usage
59 WHICH TECHNOLOGY REQUIRES THE USE OF PPPOE TO PROVIDE PPP CONNECTIONS TO CUSTOMERS?dialup ISDN modem
T1
DSL
dialup analog modem
60 UNDER WHICH TWO CATEGORIES OF WAN CONNECTIONS DOES FRAME RELAY FIT?(CHOOSE TWO.)
PACKET-SWITCHED
PRIVATE INFRASTRUCTURE public infrastructureInternet
dedicated
61 WHAT ARE THREE CHARACTERISTICS OF THE GENERIC ROUTING ENCAPSULATION (GRE) PROTOCOL? (CHOOSE THREE.) GRE TUNNELS SUPPORT MULTICAST TRAFFIC. GRE CREATES ADDITIONAL OVERLOAD FOR PACKETS THAT ARE TRAVELING THROUGHTHE VPN.
GRE uses AES for encryption unless otherwise specified BY DEFAULT, GRE DOES NOT INCLUDE ANY FLOW CONTROL MECHANISMS. Developed by the IETF, GRE is a secure tunneling protocol that was designed for Cisco routers. GRE provides encapsulation for a single protocol type that is traveling through the VPN. 62 AN INTERCITY BUS COMPANY WANTS TO OFFER CONSTAT INTERNET CONNECTIVITY TO THE USERS TRAVELING ON THE BUSES. WHICH TWO TYPES OF WAN INFRASTRUCTURE WOULD MEET THE REQUIREMENTS? (CHOOSE TWO.)CELLULAR
dedicated
private infrastructurecircuit-switched
PUBLIC INFRASTRUCTURE 63 WHAT IS USED AS THE DEFAULT EVENT LOGGING DESTINATION FOR CISCO ROUTERS AND SWITCHES?syslog server
terminal line
workstation
CONSOLE LINE
64. ANOTHER NEW QUESTION: WHAT EQUIPMENT AT THE CABLE SERVICE PROVIDER OFFICE CONNECTS THE OFFICE TO THE SUBSCRIBER LOCATIONS?DSLAM
CSU/DSU
CMTS
access server
65. WHICH PPP PROTOCOL ALLOWS A DEVICE TO SPECIFY AN IP ADDRESS FOR ROUTING OVER THE PPP LINK?PAP
LCP
IPCP
CHAP
66. WHAT TERM IS USED TO IDENTIFY THE POINT WHERE THE CUSTOMER NETWORK ENDS AND THE SERVICE PROVIDER NETWORK BEGINS?the central office
the local loop
CSU/DSU
THE DEMARCATION POINT 67. REFER TO THE EXHIBIT. A NETWORK ADMINISTRATOR DISCOVERS THAT HOST A IS HAVING TROUBLE WITH INTERNET CONNECTIVITY, BUT THE SERVER FARM HAS FULL CONNECTIVITY. IN ADDITION, HOST A HAS FULL CONNECTIVITY TO THE SERVER FARM. WHAT IS A POSSIBLE CAUSE OF THIS PROBLEM? Host A has an incorrect default gateway configured Host A has an incorrect subnet mask NAT IS REQUIRED FOR THE HOST A NETWORK The router has an incorrect gateway Host A has an overlapping network address__0 Comentarios
__Deja
un comentario
__ 4 diciembre, 2014thomasterrones
CCNA 4 V5.0 (INGLES) CCNA 4 CHAPTER 9 V5 EXAM ANSWERS 2013 CCNA 4 CHAPTER 9 V5 EXAM ANSWERS 2013 CCNA 4 CHAPTER 9 V5 EXAM ANSWERS R&S CONNECTING NETWORKS CISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS2013-2014
1. Users are reporting longer delays in authentication and in accessing network resources during certain time periods of the week. What kind of information should network engineers check to find out if this situation is part of a normal network behavior? syslog records and messages THE NETWORK PERFORMANCE BASELINE debug output and packet captures network configuration files _______________________________________________________________ 2. A team of engineers has identified a solution to a significant network problem. The proposed solution is likely to affect critical network infrastructure components. What should the team follow while implementing the solution to avoid interfering with other processesand infrastructure?
CHANGE-CONTROL PROCEDURES one of the layered troubleshooting approaches knowledge base guidelines syslog messages and reports _______________________________________________________________ 3. After which step in the network troubleshooting process would one of the layered troubleshooting methods be used? documenting symptoms determining ownershipnarrowing the scope
GATHERING SYMPTOMS FROM SUSPECT DEVICES _______________________________________________________________ 4. A user reports that the workstation cannot connect to a networked printer in the office in order to print a report created with word processing software. Which troubleshooting action by the helpdesk technician would follow the divide-and-conquer approach? Ask the user to launch the web browser. Ask the user to save the working document. ASK THE USER TO ISSUE THE IPCONFIG COMMAND. Ask the user to unplug and reattach the network cable. _______________________________________________________________ 5. A network engineer is troubleshooting a network problem and can successfully ping between two devices. However, Telnet between the same two devices does not work. Which OSI layers should the administrator investigate next?all of the layers
FROM THE NETWORK LAYER TO THE APPLICATION LAYER from the network layer to the physical layer only the network layer _______________________________________________________________ 6. Which troubleshooting method begins by examining cable connectionsand wiring issues?
top-down
BOTTOM-UP
substitution
divide-and-conquer
_______________________________________________________________7.
Refer to the exhibit. Which two statements describe the results of entering these commands?(Choose two.)
R1 WILL SEND SYSTEM MESSAGES OF LEVELS 0 (EMERGENCIES) TO LEVEL 4 (WARNINGS) TO A SERVER. R1 will not send critical system messages to the server until the command debug all is entered. R1 will reset all the warnings to clear the log. R1 will output the system messages to the local RAM. THE SYSLOG SERVER HAS THE IPV4 ADDRESS 192.168.10.10. _______________________________________________________________ 8. An administrator is troubleshooting an Internet connectivity problem on a router. The output of the show interfaces gigabitethernet 0/0 command reveals higher than normal framing errors on the interface that connects to the Internet. At what layer of the OSI model is the problem likely occurring?Layer 1
LAYER 2
Layer 3
Layer 4
Layer 7
_______________________________________________________________ 9. Users report that the new web site http://www.company1.biz cannot be accessed. The helpdesk technician checks and verifies that the web site can be accessed with http://www.company1.biz:90. Which layer in the TCP/IP model is involved in troubleshooting this issue?application
TRANSPORT
internet
network access
_______________________________________________________________ 10. A user reports that after an OS patch of the networking subsystem has been applied to a workstation, it performs very slowly when connecting to network resources. A network technician tests the link with a cable analyzer and notices that the workstation sends an excessive number of frames smaller than 64 bytes and also other meaningless frames. What is the possible cause of the problem?cabling faults
CORRUPTED NIC DRIVER Ethernet signal attenuation corrupted application installation _______________________________________________________________ 11. A network administrator is configuring SSH on a router. When verifying the configuration, the administrator notices that the SSH connection requests fail, but the Telnet connection requests from the same workstation are successful. Which two parts of the router configuration should be checked to try to locate the problem? (Choosetwo.)
The ip access-class command is missing. The password is misconfigured on the console line. THE TRANSPORT INPUT COMMAND IS INCORRECT ON THE VTY LINES. A standard ACL is possibly blocking the workstation from access to therouter.
AN EXTENDED ACL THAT IS REFERENCING THE PORT ARGUMENT FOR SSH ISMISCONFIGURED.
_______________________________________________________________ 12. A user in a large office calls technical support to complain that a PC has suddenly lost connectivity to the network. The technician asks the caller to talk to nearby users to see if other machines are affected. The caller reports that several immediate neighbors in the same department have a similar problem and that they cannot ping each other. Those who are seated in other departments have connectivity. What should the technician check as the first step in troubleshootingthe issue?
the power outlet to the PC that is used by the caller the trunks between switches in the wiring closet THE STATUS OF THE DEPARTMENTAL WORKGROUP SWITCH IN THE WIRING CLOSET the cable that connects the PC of the caller to the network jack the cable connection between a PC and a network outlet that is used bya neighbor
_______________________________________________________________ 13. After cables were reconnected to a switch in a wiring closet, several PCs that had been previously configured manually can no longer access resources outside the local network. The PC configurations were not altered in the process and resources on the local network can still be accessed. What is a possible cause of the problem? The cabling to the PCs is faulty. THE PCS ARE NO LONGER ON THE CORRECT VLAN. The DHCP server has been misconfigured. The DNS configuration on the PCs is incorrect. _______________________________________________________________14.
Refer to the exhibit. On the basis of the output, which two statements about network connectivity are correct? (Choose two.) THERE IS CONNECTIVITY BETWEEN THIS DEVICE AND THE DEVICE AT192.168.100.1.
The connectivity between these two hosts allows for videoconferencingcalls.
THERE ARE 4 HOPS BETWEEN THIS DEVICE AND THE DEVICE AT 192.168.100.1. The average transmission time between the two hosts is 2 miliseconds. This host does not have a default gateway configured. _______________________________________________________________ 15. Fill in the blank. Use the ARP to verify IPv4 address to Layer 2 Ethernet address mappings on a host computer. _______________________________________________________________ 16. Which two specialized troubleshooting tools can monitor the amount of traffic that passes through a switch? (Choose two.)digital multimeter
TDR
NAM
PORTABLE NETWORK ANALYZERDTX cable analyzer
_______________________________________________________________ 17. A group of Windows PCs in a new subnet has been added to an Ethernet network. When testing the connectivity, a technician finds that these PCs can access local network resources but not the Internet resources. To troubleshoot the problem, the technician wants to initially confirm the IP address and DNS configurations on the PCs, and also verify connectivity to the local router. Which three Windows CLI commands and utilities will provide the necessary information?(Choose three.)
IPCONFIG
telnet
PING
arp -a
NSLOOKUP
tracert
netsh interface ipv6 show neighbor _______________________________________________________________ 18. A company is setting up a web site with SSL technology to protect the authentication credentials required to access the web site. A network engineer needs to verify that the setup is correct and that the authentication is indeed encrypted. Which tool should be used?baselining tool
cable analyzer
PROTOCOL ANALYZER
fault-management tool _______________________________________________________________ 19. In which step of gathering symptoms does the network engineer determine if the problem is at the core, distribution, or access layerof the network?
Determine ownership.NARROW THE SCOPE.
Gather information.
Document the symptoms. Determine the symptoms. _______________________________________________________________ 20. A network technician is troubleshooting an email connection problem. Which question to the end-user will provide clear information to better define the problem? How big are the emails you tried to send? WHEN DID YOU FIRST NOTICE YOUR EMAIL PROBLEM? Is your email working now? What kind of equipment are you using to send emails? _______________________________________________________________ 21. A network engineer issues the show cdp neighbor command on several network devices during the process of network documentation. What is the purpose of performing this command? TO OBTAIN INFORMATION ABOUT DIRECTLY CONNECTED CISCO DEVICES to check the networks that are advertised by the neighboring routers to verify the network addresses that are attached to the networkdevices
to check the connectivity of PCs that are connected to the networkdevices
_______________________________________________________________22.
Refer to exhibit. A network engineer is troubleshooting a WAN connectivity problem. A ping to a remote router is successful and an attempt to telnet to the same router displays the exhibited output. What does the output verify? A Telnet password has not been configured on the remote router. THE TRANSPORT LAYER IS CONNECTING SUCCESSFULLY. The web server service is password protected. The remote router IPv6 address is incorrect. _______________________________________________________________ 23. When should a network performance baseline be measured? after normal work hours to reduce possible interruptions DURING NORMAL WORK HOURS OF AN ORGANIZATION when a denial of service attack to the network is detected and blocked immediately after the main network devices restarted _______________________________________________________________ 24. Which number represents the most severe level of syslog logging?7
0
1
10
_______________________________________________________________25.
CCNA 4 Chapter 9 v5 exam answers 2013, CISCO CCNA ANSWERS, CCNA 4 Ch 9 exam test quiz 2014, CISCO CCNA 4 chapter 9 exam answers__0 Comentarios
__Deja
un comentario
__ 4 diciembre, 2014thomasterrones
CCNA 4 V5.0 (INGLES) CCNA 4 CHAPTER 7 V5 PRACTICE SKILLS ASSESSMENT PT ACTVITY CCNA 4 CHAPTER 7 V5 PRACTICE SKILLS ASSESSMENT PT ACTVITY CCNA4 Chapter 7 v5 Practice Skills Assessment PT Connecting Networks Many thanks for Jerry.ADDRESSING TABLE:
DEVICE
INTERFACE
IP ADDRESS
R1
S0/0/0.2
192.168.0.1/30
S0/0/0.3
192.168.0.5/30
S0/0/1
198.51.100.1/30
T0
192.168.0.9/30
R2
G0/0
10.2.0.1/24
S0/0/0.1
192.168.0.2/30
S0/0/0.3
192.168.0.13/30
R3
G0/0
10.3.0.1/24
S0/0/0.1
192.168.0.6/30
S0/0/0.2
192.168.0.14/30
R4
G0/0
10.4.0.1/24
S0/0/1
203.0.113.1/30
T0
192.168.0.10/30
Frame Relay Table:
DEVICE
INTERFACE
DLCI
R1
S0/0/0.2
122
S0/0/0.3
123
R2
S0/0/0.1
221
S0/0/0.3
223
R3
S0/0/0.1
321
S0/0/0.2
322
HOSTNAME NORTH (CENTRAL, R3)int s0/0/0
encapsulation frame-relayno shutdown
exit
int s0/0/0.2 point-to-point ip add 192.168.0.1 255.255.255.252 frame-relay interface-dlci 122no shutdown
exit
int s0/0/0.3 point-to-point ip add 192.168.0.5 255.255.255.252 frame-relay interface-dlci 123no shutdown
exit
int s0/0/1
encapsulation hdlc
ip add 198.51.100.1 255.255.255.252no shutdown
exit
int T0
ip add 192.168.0.9 255.255.255.252 tunnel source s0/0/1 tunnel destination 203.0.113.1no shutdown
exit
router ospf 1
network 192.168.0.0 0.0.0.3 area 0 network 192.168.0.4 0.0.0.3 area 0 network 198.51.100.0 0.0.0.3 area 0 passive-interface s0/0/1 default-information originateexit
ip route 0.0.0.0 0.0.0.0 198.51.100.2 HOSTNAME EAST (BRANCH-1, R2)int s0/0/0
encapsulation frame-relayno shutdown
exit
int s0/0/0.1 point-to-point ip add 192.168.0.2 255.255.255.252 frame-relay interface-dlci 221no shutdown
exit
int s0/0/0.3 point-to-point ip add 192.168.0.13 255.255.255.252 frame-relay interface-dlci 223no shutdown
exit
int g0/0
ip add 10.2.0.1 255.255.255.0no shutdown
exit
router ospf 1
network 10.2.0.0 0.0.0.255 area 0 network 192.168.0.0 0.0.0.3 area 0 network 192.168.0.12 0.0.0.3 area 0 passive-interface g0/0exit
HOSTNAME WEST (BRANCH-2, R1)int s0/0/0
encapsulation frame-relayno shutdown
int s0/0/0.1 point-to-point ip add 192.168.0.6 255.255.255.252 frame-relay interface-dlci 321no shutdown
int s0/0/0.2 point-to-point ip add 192.168.0.14 255.255.255.252 frame-relay interface-dlci 322no shutdown
int g0/0
ip add 10.3.0.1 255.255.255.0no shutdown
router ospf 1
network 10.3.0.0 0.0.0.255 area 0 network 192.168.0.4 0.0.0.3 area 0 network 192.168.0.12 0.0.0.3 area 0 passive-interface g0/0exit
HOSTNAME SOUTH (REMOTE, R4)int s0/0/1
encapsulation hdlc
ip add 203.0.113.1 255.255.255.252no shutdown
exit
int T0
ip add 192.168.0.10 255.255.255.252 tunnel source s0/0/1 tunnel destination 198.51.100.1no shutdown
exit
int g0/0
ip add 10.4.0.1 255.255.255.0no shutdown
exit
ip route 0.0.0.0 0.0.0.0 s0/0/1__0 Comentarios
__Deja
un comentario
__ 4 diciembre, 2014thomasterrones
CCNA 4 V5.0 (INGLES) CCNA 4 CHAPTER 8 V5 EXAM ANSWERS 2013 CCNA 4 CHAPTER 8 V5 EXAM ANSWERS 2013 CCNA 4 CHAPTER 8 V5 EXAM ANSWERS R&S CONNECTING NETWORKS CISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS2013-2014
1.
Refer to the exhibit. Which two conclusions can be drawn from the syslog message that was generated by the router? (Choose two.) This message resulted from an unusual error requiring reconfigurationof the interface.
This message indicates that the interface should be replaced. THIS MESSAGE IS A LEVEL 5 NOTIFICATION MESSAGE. THIS MESSAGE INDICATES THAT SERVICE TIMESTAMPS HAVE BEEN CONFIGURED. This message indicates that the interface changed state five times. _______________________________________________________________ 2. A network technician has issued the service timestamps log datetimecommand in the
configuration of the branch router. Which additional command is required to include the date and time in logged events? Branch1(config)# service timestamps log uptime BRANCH1# CLOCK SET 08:00:00 05 AUG 2013 Branch1(config)# service timestamps debug datetime Branch1# copy running-config startup-config _______________________________________________________________3.
Refer to the exhibit. From what location have the syslog messages beenretrieved?
syslog server
syslog client
ROUTER RAM
router NVRAM
_______________________________________________________________4.
Refer to the exhibit. What does the number 17:46:26.143 represent? the time passed since the syslog server has been started THE TIME WHEN THE SYSLOG MESSAGE WAS ISSUED the time passed since the interfaces have been up the time on the router when the show logging command was issued _______________________________________________________________ 5. What are SNMP trap messages? messages that are used by the NMS to query the device for data UNSOLICITED MESSAGES THAT ARE SENT BY THE SNMP AGENT AND ALERT THE NMS TO A CONDITION ON THE NETWORK messages that are used by the NMS to change configuration variables inthe agent device
messages that are sent periodically by the NMS to the SNMP agents that reside on managed devices to query the device fordata
_______________________________________________________________ 6. How can SNMP access be restricted to a specific SNMP manager? Use the snmp-server community command to configure the community string with no access level. Specify the IP address of the SNMP manager by using the snmp-serverhost command.
Use the snmp-server traps command to enable traps on an SNMP manager. DEFINE AN ACL AND REFERENCE IT BY USING THE SNMP-SERVER COMMUNITYCOMMAND.
_______________________________________________________________ 7. A network administrator issues two commands on a router: R1(config)# snmp-server host 10.10.50.25 version 2c campus R1(config)# snmp-server enable traps What can be concluded after the commands are entered? No traps are sent, because the notification-types argument was notspecified yet.
Traps are sent with the source IP address as 10.10.50.25. IF AN INTERFACE COMES UP, A TRAP IS SENT TO THE SERVER. The snmp-server enable traps command needs to be used repeatedly if a particular subset of trap types is desired. _______________________________________________________________ 8. What is a difference between SNMP and NetFlow? Unlike NetFlow, SNMP uses a “push”-based model. NETFLOW COLLECTS MORE DETAILED TRAFFIC STATISTICS ON IP NETWORKS THANSNMP DOES.
SNMP only gathers traffic statistics, whereas NetFlow can also collect many other performance indicators, such as interface errors and CPU usage. Unlike NetFlow, SNMP may be used to provide IP accounting for billingpurposes.
_______________________________________________________________ 9. How does NetFlow function on a Cisco router or multilayer switch? Netflow captures and analyzes traffic. ONE USER CONNECTION TO AN APPLICATION EXISTS AS TWO NETFLOW FLOWS. On 2960 switches, Netlow allows for data export. NetFlow does not consume any additional memory. _______________________________________________________________ 10. Which type of information can an administrator obtain with the show ip cache flow command? the NetFlow version that is enabled whether NetFlow is configured on the correct interface and in thecorrect direction
the configuration of the export parameters THE PROTOCOL THAT USES THE LARGEST VOLUME OF TRAFFIC _______________________________________________________________ 11. What is the most common purpose of implementing NetFlow in a networked environment? TO SUPPORT ACCOUNTING AND MONITORING WITH CONSUMER APPLICATIONS to actively capture traffic from networked devices to monitor live data usage and to control traffic flow with setmessages
to passively capture changing events that occur in the network and to perform after-the-fact-analysis _______________________________________________________________ 12. Which destination do Cisco routers and switches use by default when sending syslog messages for all severity levels?RAM
NVRAM
nearest syslog serverCONSOLE
_______________________________________________________________ 13. Which SNMP feature provides a solution to the main disadvantage ofSNMP polling?
SNMP community stringsSNMP set messages
SNMP get messages
SNMP TRAP MESSAGES
_______________________________________________________________ 14. Which statement describes SNMP operation? A get request is used by the SNMP agent to query the device for data. A SET REQUEST IS USED BY THE NMS TO CHANGE CONFIGURATION VARIABLES INTHE AGENT DEVICE.
An NMS periodically polls the SNMP agents that are residing on managed devices by using traps to query the devices for data. An SNMP agent that resides on a managed device collects information about the device and stores that information remotely in the MIB that is located on the NMS. _______________________________________________________________ 15. A network administrator has issued the logging trap 4 global configuration mode command. What is the result of this command? After four events, the syslog client will send an event message to thesyslog server.
The syslog client will send to the syslog server any event message that has a severity level of 4 and higher. The syslog client will send to the syslog server event messages with an identification trap level of only 4. THE SYSLOG CLIENT WILL SEND TO THE SYSLOG SERVER ANY EVENT MESSAGE THAT HAS A SEVERITY LEVEL OF 4 AND LOWER. _______________________________________________________________ 16. When logging is used, which severity level indicates that a deviceis unusable?
Critical – Level 2Alert – Level 1
EMERGENCY-LEVEL 0
Error-Level 3
17.
Refer to the exhibit. While planning an upgrade, a network administrator uses the Cisco NetFlow utility to analyze data flow in the current network. Which protocol used the greatest amount ofnetwork time?
TCP-FTP
TCP-Telnet
UDP-DNS
TCP-other
UDP-OTHER
_______________________________________________________________ 18. Which two statements describe items to be considered in configuring NetFlow? (Choosetwo.)
Netflow requires both management and agent software. NetFlow can only be used if all devices on the network support it. NETFLOW CAN ONLY BE USED IN A UNIDIRECTIONAL FLOW. Netflow requires UDP port 514 for notification messages. NETFLOW CONSUMES ADDITIONAL MEMORY. _______________________________________________________________ 19. When SNMPvl or SNMPv2 is being used, which feature provides secure access to MIB objects?message integrity
source validation
COMMUNITY STRINGS
packet encryption
_______________________________________________________________20.
Refer to the exhibit. What can be concluded from the produced output? AN ACL WAS CONFIGURED TO RESTRICT SNMP ACCESS TO AN SNMP MANAGER. This is the output of the show snmp command without any parameters. The system contact was not configured with the snmp server contactcommand
_______________________________________________________________ 21. What are the most common syslog messages? output messages that are generated from debug output LINKUP AND LINK DOWN MESSAGES those that occur when a packet matches a parameter condition in anaccess control list
error messages about hardware or software malfunctions _______________________________________________________________ 22. A network administrator has issued the snmp-server user adminl admin v3 encrypted auth md5 abc789 priv des 256 key99 command. What are two features of this command? (Choose two.) It forces the network manager to log into the agent to retrieve theSNMP messages.
It restricts SNMP access to defined SNMP managers. IT USES THE MD5 AUTHENTICATION OF THE SNMP MESSAGES. It allows a network administrator to configure a secret encrypted password on the SNMP server. IT ADDS A NEW USER TO THE SNMP GROUP. _______________________________________________________________ 23. Fill in the blank. The SYSLOG protocol uses UDP port 514 and is the most common method to access system messages provided by networking devices. CCNA 4 Chapter 8 v5 exam answers 2013, CISCO CCNA ANSWERS, CCNA 4 Ch 8 exam test quiz 2014, CISCO CCNA 4 chapter 8 exam answers__0 Comentarios
__Deja
un comentario
__ 4 diciembre, 2014thomasterrones
CCNA 4 V5.0 (INGLES) CCNA 4 CHAPTER 7 V5 EXAM ANSWERS 2013 CCNA 4 CHAPTER 7 V5 EXAM ANSWERS 2013 CCNA 4 CHAPTER 7 V5 EXAM ANSWERS R&S CONNECTING NETWORKS CISCO CCNA ANSWERS V5 ROUTING AND SWITCHING TEST QUESTION AND ANSWERS2013-2014
1. How is “tunneling” accomplished in a VPN? NEW HEADERS FROM ONE OR MORE VPN PROTOCOLS ENCAPSULATE THE ORIGINALPACKETS.
All packets between two hosts are assigned to a single physical medium to ensure that the packets are kept private. Packets are disguised to look like other types of traffic so that they will be ignored by potential attackers. A dedicated circuit is established between the source and destination devices for the duration of the connection. ____________________________________________________________________ 2. Which two scenarios are examples of remote access VPNs? (Choosetwo.)
A toy manufacturer has a permanent VPN connection to one of its partssuppliers.
All users at a large branch office can access company resources through a single VPN connection. A MOBILE SALES AGENT IS CONNECTING TO THE COMPANY NETWORK VIA THE INTERNET CONNECTION AT A HOTEL. A small branch office with three employees has a Cisco ASA that is used to create a VPN connection to the HQ. AN EMPLOYEE WHO IS WORKING FROM HOME USES VPN CLIENT SOFTWARE ON A LAPTOP IN ORDER TO CONNECT TO THE COMPANY NETWORK. ____________________________________________________________________3.
Refer to the exhibit. Which IP address would be configured on the tunnel interface of the destination router?172.16.1.1
172.16.1.2
209.165.200.225
209.165.200.226
____________________________________________________________________ 4. Which statement correctly describes IPsec? IPSEC WORKS AT LAYER 3, BUT CAN PROTECT TRAFFIC FROM LAYER 4 THROUGHLAYER 7.
IPsec uses algorithms that were developed specifically for thatprotocol.
IPsec implements its own method of authentication. IPsec is a Cisco proprietary standard. ____________________________________________________________________ 5. What is an IPsec protocol that provides data confidentiality and authentication for IP packets?AH
ESP
RSA
IKE
____________________________________________________________________ 6. Which three statements describe the building blocks that make up the IPsec protocol framework?(Choose three.)
IPSEC USES ENCRYPTION ALGORITHMS AND KEYS TO PROVIDE SECURE TRANSFEROF DATA.
IPsec uses Diffie-Hellman algorithms to encrypt data that is transferred through the VPN. IPsec uses 3DES algorithms to provide the highest level of security for data that is transferred through a VPN. IPSEC USES SECRET KEY CRYPTOGRAPHY TO ENCRYPT MESSAGES THAT ARE SENTTHROUGH A VPN.
IPsec uses Diffie-Hellman as a hash algorithm to ensure integrity of data that is transmitted through a VPN. IPSEC USES ESP TO PROVIDE CONFIDENTIAL TRANSFER OF DATA BY ENCRYPTINGIP PACKETS.
____________________________________________________________________ 7. What key question would help determine whether an organization should use an SSL VPN or an IPsec VPN for the remote access solution of the organization? Is a Cisco router used at the destination of the remote access tunnel? What applications or network resources do the users need for access? Are both encryption and authentication required? DO USERS NEED TO BE ABLE TO CONNECT WITHOUT REQUIRING SPECIAL VPNSOFTWARE?
____________________________________________________________________ 8. What is the purpose of a message hash in a VPN connection? It ensures that the data cannot be duplicated and replayed to thedestination.
It ensures that the data is coming from the correct source. IT ENSURES THAT THE DATA HAS NOT CHANGED WHILE IN TRANSIT. It ensures that the data cannot be read in plain text. ____________________________________________________________________ 9. A network design engineer is planning the implementation of a cost-effective method to interconnect multiple networks securely over the Internet. Which type of technology is required?a dedicated ISP
A VPN GATEWAY
a leased line
a GRE IP tunnel
____________________________________________________________________ 10. What is one benefit of using VPNs for remote access? lower protocol overhead POTENTIAL FOR REDUCED CONNECTIVITY COSTS increased quality of service ease of troubleshooting ____________________________________________________________________ 11. Which statement describes a characteristic of IPsec VPNs? IPsec can secure traffic at Layers 1 through 3. IPSEC WORKS WITH ALL LAYER 2 PROTOCOLS. IPsec encryption causes problems with routing. IPsec is a framework of Cisco proprietary protocols ____________________________________________________________________ 12. What is the purpose of the generic routing encapsulation tunnelingprotocol?
to support basic unencrypted IP tunneling using multivendor routers between remote sites to provide fixed flow-control mechanisms with IP tunneling betweenremote sites
TO MANAGE THE TRANSPORTATION OF IP MULTICAST AND MULTIPROTOCOL TRAFFIC BETWEEN REMOTE SITES to provide packet level encryption of IP traffic between remote sites ____________________________________________________________________ 13. Which algorithm is an asymmetrical key cryptosystem?3DES
DES
AES
RSA
____________________________________________________________________ 14. A network design engineer is planning the implementation of an IPsec VPN. Which hashing algorithm would provide the strongest level of message integrity?512-BIT SHA
AES
SHA-1
MD5
____________________________________________________________________ 15. What two encryption algorithms are used in IPsec VPNs? (Choosetwo.)
IKE
DH
PSK
3DES
AES
____________________________________________________________________ 16. Which statement describes a feature of site-to-site VPNs? INTERNAL HOSTS SEND NORMAL, UNENCAPSULATED PACKETS. VPN client software is installed on each host. The VPN connection is not statically defined. Individual hosts can enable and disable the VPN connection. ____________________________________________________________________ 17. Which Cisco VPN solution provides limited access to internal network resources by utilizing a Cisco ASA and provides browser-basedaccess only?
CLIENTLESS SSL VPN
IPsec
SSL
client-based SSL VPN ____________________________________________________________________ 18. Which two algorithms use Hash-based Message Authentication Code for message authentication? (Choose two.)AES
DES
3DES
MD5
SHA
____________________________________________________________________ 19. Which function of IPsec security services allows the receiver to verify that the data was transmitted without being changed or alteredin any way?
confidentiality
anti-replay protectionDATA INTEGRITY
authentication
____________________________________________________________________20.
Open the PT Activity. Perform the tasks in the activity instructions and then answer the question. What problem is preventing the hosts from communicating across the VPN tunnel? The EIGRP configuration is incorrect. The tunnel destinations addresses are incorrect. THE TUNNEL IP ADDRESSES ARE INCORRECT. The tunnel source interfaces are incorrect ____________________________________________________________________ 21. What is the purpose of utilizing Diffie-Hellman (DH) algorithms as part of the IPsec standard? DH algorithms allow unlimited parties to establish a shared public key that is used by encryption and hash algorithms. DH algorithms allow two parties to establish a shared public key that is used by encryption and hash algorithms. DH ALGORITHMS ALLOW TWO PARTIES TO ESTABLISH A SHARED SECRET KEY THAT IS USED BY ENCRYPTION AND HASH ALGORITHMS. DH algorithms allow unlimited parties to establish a shared secret key that is used by encryption and hash algorithms. ____________________________________________________________________22.
Refer to the exhibit. A tunnel was implemented between routers R1 and R2. Which two conclusions can be drawn from the R1 command output?(Choose two.)
THE DATA THAT IS SENT ACROSS THIS TUNNEL IS NOT SECURE. This tunnel mode provides encryption. This tunnel mode does not support IP multicast tunneling. A GRE TUNNEL IS BEING USED. This tunnel mode is not the default tunnel interface mode for CiscoIOS software.
____________________________________________________________________ 23. Two corporations have just completed a merger. The network engineer has been asked to connect the two corporate networks without the expense of leased lines. Which solution would be the most cost effective method of providing a proper and secure connection between the two corporate networks? Cisco AnyConnect Secure Mobility Client with SSLFrame Relay
remote access VPN using IPsec Cisco Secure Mobility Clientless SSL VPNSITE-TO-SITE VPN
____________________________________________________________________ 24. Which remote access implementation scenario will support the use of generic routing encapsulation tunneling? a mobile user who connects to a SOHO site A CENTRAL SITE THAT CONNECTS TO A SOHO SITE WITHOUT ENCRYPTION a branch office that connects securely to a central site a mobile user who connects to a router at a central site CCNA 4 Chapter 7 v5 exam answers 2013, CISCO CCNA ANSWERS, CCNA 4 Ch 7 exam test quiz 2014, CISCO CCNA 4 chapter 7 exam answers__0 Comentarios
__Deja
un comentario
__ 4 diciembre, 2014thomasterrones
CCNA 4 V5.0 (INGLES) NAVEGADOR DE ARTÍCULOS__ Older posts
Buscar
CATEGORÍAS
* CCNA
* CCNA 1 V5.0
* CCNA 1 V5.0 (INGLES)* CCNA 2 V5.0
* CCNA 2 V5.0 (INGLES)* CCNA 3 V5.0
* CCNA 3 V5.0 (INGLES)* CCNA 4 V5.0
* CCNA 4 V5.0 (INGLES) http://img.urlfb.com/rs/ENTRADAS RECIENTES
* Examenes CCNA v5 en ESPAÑOL e INGLES – COPIAR FACIL * CCNA 4 Practice Final Exam v5 R&S Connecting Networks 2014 * CCNA 4 v5 Final Exam Connecting Networks Routing and Switching * CCNA 4 Chapter 9 v5 exam answers 2013 * CCNA 4 Chapter 7 v5 Practice Skills Assessment PT actvityAnuncios
Report this ad
Blog de WordPress.com. CCNA v5 examenes ESPAÑOL INGLES Blog de WordPress.com.Publicar en
Cancelar
Privacidad & Cookies: este sitio usa cookies. Al continuar usando este sitio, estás de acuerdo con su uso. Para saber más, incluyendo como controlar las cookies, mira aquí: Política de Cookies.* Seguir
*
* CCNA v5 examenes ESPAÑOL INGLES* Personalizar
* Seguir
* Regístrate
* Acceder
* Denunciar este contenido * Gestionar las suscripciones * Contraer esta barraDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0