Are you over 18 and want to see adult content?
More Annotations

A complete backup of www.topboard.org
Are you over 18 and want to see adult content?
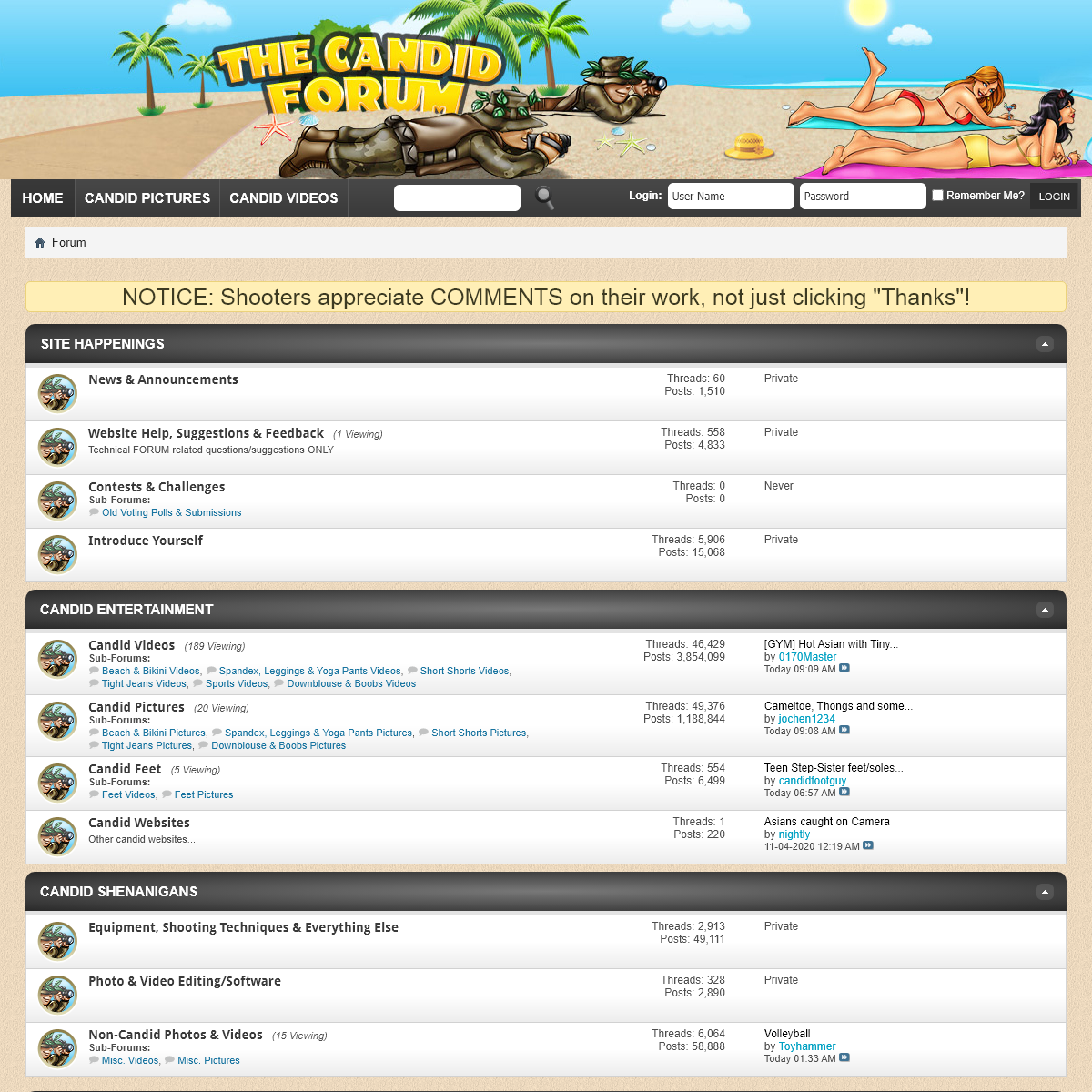
A complete backup of www.thecandidforum.com
Are you over 18 and want to see adult content?
A complete backup of www.www.streamray.com
Are you over 18 and want to see adult content?

A complete backup of www.www.zenra.net
Are you over 18 and want to see adult content?

A complete backup of www.www.nanabook.com
Are you over 18 and want to see adult content?
A complete backup of www.dvdgayonline.com
Are you over 18 and want to see adult content?
Favourite Annotations
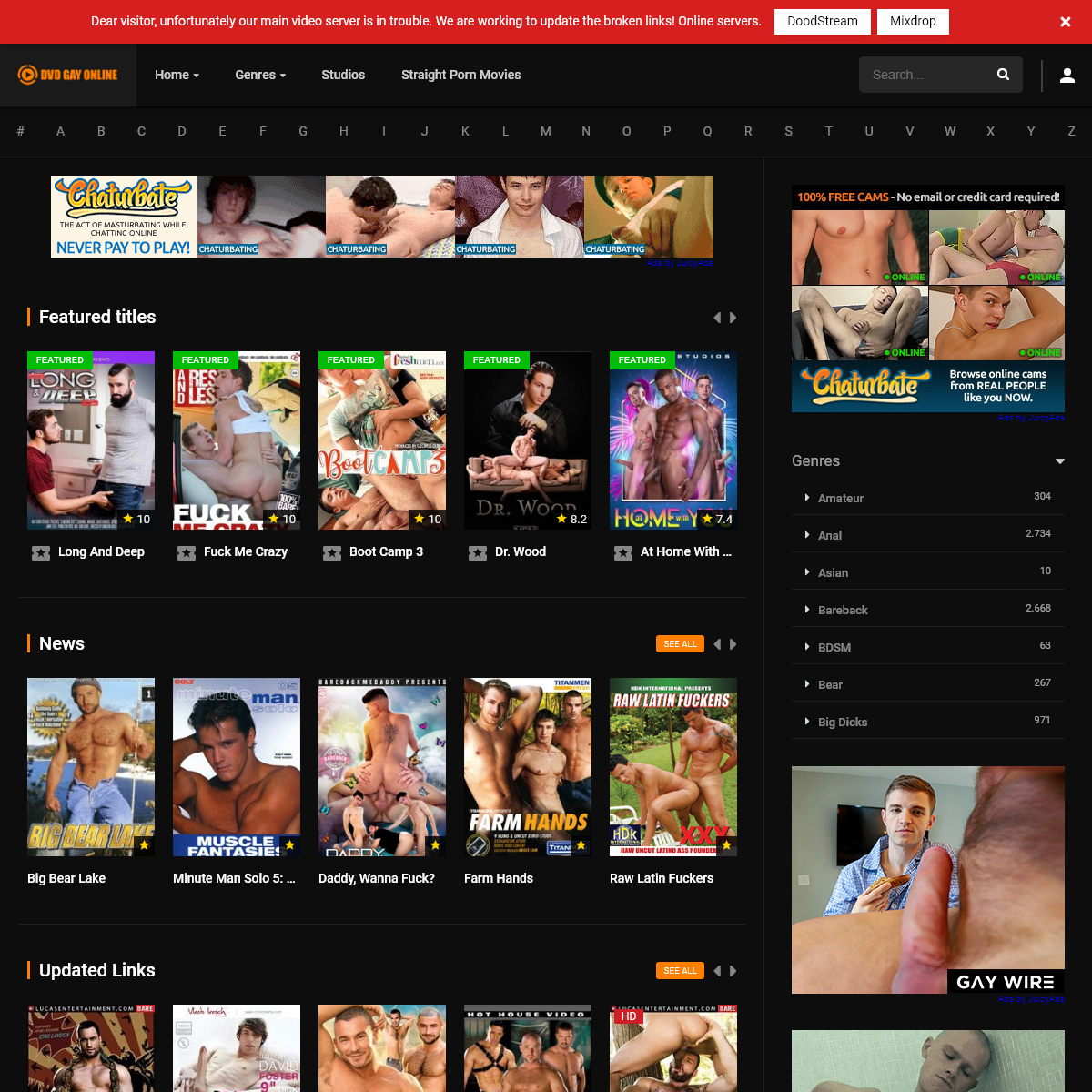
A complete backup of https://unpkediri.ac.id
Are you over 18 and want to see adult content?

A complete backup of https://codeguru.com
Are you over 18 and want to see adult content?
A complete backup of https://autonomy.paris
Are you over 18 and want to see adult content?
A complete backup of https://theforexreview.com
Are you over 18 and want to see adult content?

A complete backup of https://lagop.com
Are you over 18 and want to see adult content?

A complete backup of https://ricardolevinsmorales.com
Are you over 18 and want to see adult content?
A complete backup of https://thevacationer.com
Are you over 18 and want to see adult content?
A complete backup of https://sondrioevalmalenco.it
Are you over 18 and want to see adult content?
A complete backup of https://businesswebadmin.com
Are you over 18 and want to see adult content?

A complete backup of https://coenloans.com
Are you over 18 and want to see adult content?

A complete backup of https://proaudio.com
Are you over 18 and want to see adult content?
A complete backup of https://ezcmining.website
Are you over 18 and want to see adult content?
Text
DISCLOSURE
Bastille’s breakthrough and patented work provides Bastille the ability to disambiguate multiple cell phones and accurately locate those individual devices in real-time. Bastille holds 26 US Patents. Learn more about Bastille's technology. Bastille shows each device as a “dot on a floor plan map”. Bastille allows you to accuratelyINTRODUCTION
Bastille provides corporations and agencies the ability to discover, locate, and mitigate radio borne threats to their assets, facilities and networks. These threats arise from managed, unmanaged and rogue wireless, IoT and Cellular devices. Bastille does this protection by using Software Defined Radios (SDRs) to passively observe the entire CELL PHONE DETECTION Detect and Locate Unauthorized Cell phones. Bastille is the first and only product to detect and locate cellular phones within a building based only on their cellular signal. Real-time detection with alerts plus DVR-like playback for forensics. Cellular phones are a great business productivity tool, but they are also the most ubiquitousBASTILLE ENTERPRISE
The Bastille Sensor Array is the 4th-generation Software Defined Radio (SDR) sensor array from Bastille. It contains two scanning 802.11ac Wi-Fi receivers, two SDR receiver front ends that can each sample at 61.44 MSps and sense from 25 MHz to 6 GHz. An array of bespoke internal antennas have been optimized to maximize detection and BASTILLE FLYAWAY KIT The Bastille FlyAway Kit is a fully self-contained unit for real-time, 24/7 Cellular, Bluetooth, BLE and Wi-Fi Device Detection, Identification and Location. It covers an area up to 5,000 square feet and can detect and locate Wi-Fi, Bluetooth and BLE devices within 30 minutes, and Cellular phones within 90 minutes. CELLULAR INTRUSION DETECTION Cellular, Bluetooth, BLE & Wi-Fi Intrusion Detection. Bastille’s real-time Cellular, Bluetooth, BLE and Wi-Fi detection and location system locates all authorized and unauthorized devices within a campus or forward deployed location, accurately places dots on a floor-plan map for device location and sends alerts when a device is found where it should not be or doing what it should not do. CONTACT — BASTILLE Atlanta Office 1000 Marietta St. #224 Atlanta, GA 30318. Demo & Training Center 590 Herndon Parkway, Suite 400 Herndon, VA 20170. Santa Cruz Office 499 Lake Ave VULNERABLE WIRELESS PERIPHERALS Vulnerable Wireless Peripherals . Billions of wireless peripherals are vulnerable to the MouseJack, KeySniffer and KeyJack vulnerabilities discovered by the Bastille Research Team.. These vulnerabilities enable hackers to collect confidential information, impersonate users and carry out attacks on computers and corporate networks. GOVERNMENT - WIRELESS INTRUSION DETECTION SYSTEM (WIDS Bastille’s Cellular Intrusion Detection is the first system which accurately detects, counts, and locates cellular devices inside your facility. To be clear, we can track devices via Bluetooth and WiFi like the other companies but the bad actors turn off those signals when they plan to undertake bad actions. To know that your facility is CABLETAP — BASTILLE CableTap Our research revealed a wide array of critical vulnerabilities in ISP-provided, RDK-based wireless gateways and set-top boxes. We demonstrated that it was possible to remotely and wirelessly tap all Internet and voice traffic passing through anaffected gateway.
BASTILLEINTRODUCTIONRESEARCH MISSIONRESEARCH TEAMVULNERABILITYDISCLOSURE
Bastille’s breakthrough and patented work provides Bastille the ability to disambiguate multiple cell phones and accurately locate those individual devices in real-time. Bastille holds 26 US Patents. Learn more about Bastille's technology. Bastille shows each device as a “dot on a floor plan map”. Bastille allows you to accuratelyINTRODUCTION
Bastille provides corporations and agencies the ability to discover, locate, and mitigate radio borne threats to their assets, facilities and networks. These threats arise from managed, unmanaged and rogue wireless, IoT and Cellular devices. Bastille does this protection by using Software Defined Radios (SDRs) to passively observe the entire CELL PHONE DETECTION Detect and Locate Unauthorized Cell phones. Bastille is the first and only product to detect and locate cellular phones within a building based only on their cellular signal. Real-time detection with alerts plus DVR-like playback for forensics. Cellular phones are a great business productivity tool, but they are also the most ubiquitousBASTILLE ENTERPRISE
The Bastille Sensor Array is the 4th-generation Software Defined Radio (SDR) sensor array from Bastille. It contains two scanning 802.11ac Wi-Fi receivers, two SDR receiver front ends that can each sample at 61.44 MSps and sense from 25 MHz to 6 GHz. An array of bespoke internal antennas have been optimized to maximize detection and BASTILLE FLYAWAY KIT The Bastille FlyAway Kit is a fully self-contained unit for real-time, 24/7 Cellular, Bluetooth, BLE and Wi-Fi Device Detection, Identification and Location. It covers an area up to 5,000 square feet and can detect and locate Wi-Fi, Bluetooth and BLE devices within 30 minutes, and Cellular phones within 90 minutes. CELLULAR INTRUSION DETECTION Cellular, Bluetooth, BLE & Wi-Fi Intrusion Detection. Bastille’s real-time Cellular, Bluetooth, BLE and Wi-Fi detection and location system locates all authorized and unauthorized devices within a campus or forward deployed location, accurately places dots on a floor-plan map for device location and sends alerts when a device is found where it should not be or doing what it should not do. CONTACT — BASTILLE Atlanta Office 1000 Marietta St. #224 Atlanta, GA 30318. Demo & Training Center 590 Herndon Parkway, Suite 400 Herndon, VA 20170. Santa Cruz Office 499 Lake Ave VULNERABLE WIRELESS PERIPHERALS Vulnerable Wireless Peripherals . Billions of wireless peripherals are vulnerable to the MouseJack, KeySniffer and KeyJack vulnerabilities discovered by the Bastille Research Team.. These vulnerabilities enable hackers to collect confidential information, impersonate users and carry out attacks on computers and corporate networks. GOVERNMENT - WIRELESS INTRUSION DETECTION SYSTEM (WIDS Bastille’s Cellular Intrusion Detection is the first system which accurately detects, counts, and locates cellular devices inside your facility. To be clear, we can track devices via Bluetooth and WiFi like the other companies but the bad actors turn off those signals when they plan to undertake bad actions. To know that your facility is CABLETAP — BASTILLE CableTap Our research revealed a wide array of critical vulnerabilities in ISP-provided, RDK-based wireless gateways and set-top boxes. We demonstrated that it was possible to remotely and wirelessly tap all Internet and voice traffic passing through anaffected gateway.
INTRODUCTION
Bastille provides corporations and agencies the ability to discover, locate, and mitigate radio borne threats to their assets, facilities and networks. These threats arise from managed, unmanaged and rogue wireless, IoT and Cellular devices. Bastille does this protection by using Software Defined Radios (SDRs) to passively observe the entireOUR MISSION
Our Mission. Founded in 2014, Bastille is the leader in enterprise threat detection through software-defined radio. Bastille provides full visibility into the known and unknown mobile, wireless and Internet of Things (IoT) devices inside an enterprise’s corporate airspace – together known as the Internet of Radios. IN PLACE MONITORING SYSTEM (IPMS) in-place monitoring SYSTEMS. Bastille Audit is a 30-day review of your airspace. In addition to revealing potential cyber-threats for data exfiltration, Bastille Audit will provide In-Place Monitoring for all RF-enabled devices in your airspace. To request a 30 Day BastilleBASTILLE EXPRESS
Bastille Express is a fully self-contained unit for real-time, 24/7 Cellular, Bluetooth, BLE and Wi-Fi Device Detection, Identification and Location. It covers an area up to 5,000 square feet and can detect and locate Wi-Fi, Bluetooth and BLE devices within 30 minutes, and Cellular phones within 90 minutes.MANAGEMENT TEAM
Christian Sepulveda is VP Engineering at Bastille Networks, leading engineering and product management teams. Christian was previously one of five partners who built Pivotal Labs from 20 developers to 2,000 developers. As VP Corporate Development, Christian negotiated the sale of Pivotal Labs to EMC and stayed through the sale and transition.BASTILLE DEMO
Request a Bastille Demo to learn more about finding cell phones, RF devices, and constant monitoring for Wi-Fi hotspots, Cellular hotspots, and Bluetooth hotspots. WIRELESS INTRUSION DETECTION SYSTEMS (WIDS) Its last release was in 2004. Commercial tools, including Bastille's, provide a supported WIDS with a convenient user interface. Bastille monitors the RF-spectrum from 60 Mhz to 6 Ghz, covering a wide range of RF-enabled devices from IoT, through cell phones and hotspots all the way up to rogue Wi-Fi and other RF potential threats. A network WEBINAR: BASTILLE RED BLUE TEAMS Bastille detects the persistent threats that other network-only solutions cannot detect sending data, of up 150 fields per device, to your SIEM and existing enterprise infrastructure to give you all the information you need to identify and locate threats. During the webinar Bob discusses use cases and techniques, plus demonstrates theBastille
WHAT IS MOUSEJACK!
MouseJack. Announced by Bastille in 2016, MouseJack is still an open vulnerability affecting devices sold today. MouseJack is a class of vulnerabilities that affects the vast majority of wireless, non-Bluetooth keyboards and mice. These peripherals are 'connected' to a host computer using a radio transceiver, commonly a small USBdongle.
KEYJACK — BASTILLE KeyJack. The KeyJack vulnerability allows encrypted keystrokes to be injected into a vulnerable wireless keyboard’s dongle without knowledge of the encryption key. Certain wireless keyboards implement encryption, but miss a subtlety that allows an attacker to inject keystrokes into the dongle after sniffing legitimate traffic from thekeyboard.
BASTILLEINTRODUCTIONRESEARCH MISSIONRESEARCH TEAMVULNERABILITYDISCLOSURE
Bastille’s breakthrough and patented work provides Bastille the ability to disambiguate multiple cell phones and accurately locate those individual devices in real-time. Bastille holds 26 US Patents. Learn more about Bastille's technology. Bastille shows each device as a “dot on a floor plan map”. Bastille allows you to accuratelyINTRODUCTION
Bastille provides corporations and agencies the ability to discover, locate, and mitigate radio borne threats to their assets, facilities and networks. These threats arise from managed, unmanaged and rogue wireless, IoT and Cellular devices. Bastille does this protection by using Software Defined Radios (SDRs) to passively observe the entireOUR MISSION
Our Mission. Founded in 2014, Bastille is the leader in enterprise threat detection through software-defined radio. Bastille provides full visibility into the known and unknown mobile, wireless and Internet of Things (IoT) devices inside an enterprise’s corporate airspace – together known as the Internet of Radios.BASTILLE ENTERPRISE
The Bastille Sensor Array is the 4th-generation Software Defined Radio (SDR) sensor array from Bastille. It contains two scanning 802.11ac Wi-Fi receivers, two SDR receiver front ends that can each sample at 61.44 MSps and sense from 25 MHz to 6 GHz. An array of bespoke internal antennas have been optimized to maximize detection and CELLULAR INTRUSION DETECTION Cellular, Bluetooth, BLE & Wi-Fi Intrusion Detection. Bastille’s real-time Cellular, Bluetooth, BLE and Wi-Fi detection and location system locates all authorized and unauthorized devices within a campus or forward deployed location, accurately places dots on a floor-plan map for device location and sends alerts when a device is found where it should not be or doing what it should not do. BASTILLE FLYAWAY KIT The Bastille FlyAway Kit is a fully self-contained unit for real-time, 24/7 Cellular, Bluetooth, BLE and Wi-Fi Device Detection, Identification and Location. It covers an area up to 5,000 square feet and can detect and locate Wi-Fi, Bluetooth and BLE devices within 30 minutes, and Cellular phones within 90 minutes. CYBER THREAT HUNTING Bastille Threat Hunter is a portable kit which can be used anywhere within the enterprise to reveal the nature and location of RF and wireless based attacks being used to gain access to your systems and/or exfiltrate data.. Bastille’s real-time, portable and fully integrated Threat Hunting solution offers Threat Hunting professionals Discovery, Analysis and Action of vulnerable devices IN PLACE MONITORING SYSTEM (IPMS) in-place monitoring SYSTEMS. Bastille Audit is a 30-day review of your airspace. In addition to revealing potential cyber-threats for data exfiltration, Bastille Audit will provide In-Place Monitoring for all RF-enabled devices in your airspace. To request a 30 Day Bastille VULNERABLE WIRELESS PERIPHERALS Vulnerable Wireless Peripherals . Billions of wireless peripherals are vulnerable to the MouseJack, KeySniffer and KeyJack vulnerabilities discovered by the Bastille Research Team.. These vulnerabilities enable hackers to collect confidential information, impersonate users and carry out attacks on computers and corporate networks. CABLETAP — BASTILLE CableTap Our research revealed a wide array of critical vulnerabilities in ISP-provided, RDK-based wireless gateways and set-top boxes. We demonstrated that it was possible to remotely and wirelessly tap all Internet and voice traffic passing through anaffected gateway.
BASTILLEINTRODUCTIONRESEARCH MISSIONRESEARCH TEAMVULNERABILITYDISCLOSURE
Bastille’s breakthrough and patented work provides Bastille the ability to disambiguate multiple cell phones and accurately locate those individual devices in real-time. Bastille holds 26 US Patents. Learn more about Bastille's technology. Bastille shows each device as a “dot on a floor plan map”. Bastille allows you to accuratelyINTRODUCTION
Bastille provides corporations and agencies the ability to discover, locate, and mitigate radio borne threats to their assets, facilities and networks. These threats arise from managed, unmanaged and rogue wireless, IoT and Cellular devices. Bastille does this protection by using Software Defined Radios (SDRs) to passively observe the entireOUR MISSION
Our Mission. Founded in 2014, Bastille is the leader in enterprise threat detection through software-defined radio. Bastille provides full visibility into the known and unknown mobile, wireless and Internet of Things (IoT) devices inside an enterprise’s corporate airspace – together known as the Internet of Radios.BASTILLE ENTERPRISE
The Bastille Sensor Array is the 4th-generation Software Defined Radio (SDR) sensor array from Bastille. It contains two scanning 802.11ac Wi-Fi receivers, two SDR receiver front ends that can each sample at 61.44 MSps and sense from 25 MHz to 6 GHz. An array of bespoke internal antennas have been optimized to maximize detection and CELLULAR INTRUSION DETECTION Cellular, Bluetooth, BLE & Wi-Fi Intrusion Detection. Bastille’s real-time Cellular, Bluetooth, BLE and Wi-Fi detection and location system locates all authorized and unauthorized devices within a campus or forward deployed location, accurately places dots on a floor-plan map for device location and sends alerts when a device is found where it should not be or doing what it should not do. BASTILLE FLYAWAY KIT The Bastille FlyAway Kit is a fully self-contained unit for real-time, 24/7 Cellular, Bluetooth, BLE and Wi-Fi Device Detection, Identification and Location. It covers an area up to 5,000 square feet and can detect and locate Wi-Fi, Bluetooth and BLE devices within 30 minutes, and Cellular phones within 90 minutes. CYBER THREAT HUNTING Bastille Threat Hunter is a portable kit which can be used anywhere within the enterprise to reveal the nature and location of RF and wireless based attacks being used to gain access to your systems and/or exfiltrate data.. Bastille’s real-time, portable and fully integrated Threat Hunting solution offers Threat Hunting professionals Discovery, Analysis and Action of vulnerable devices IN PLACE MONITORING SYSTEM (IPMS) in-place monitoring SYSTEMS. Bastille Audit is a 30-day review of your airspace. In addition to revealing potential cyber-threats for data exfiltration, Bastille Audit will provide In-Place Monitoring for all RF-enabled devices in your airspace. To request a 30 Day Bastille VULNERABLE WIRELESS PERIPHERALS Vulnerable Wireless Peripherals . Billions of wireless peripherals are vulnerable to the MouseJack, KeySniffer and KeyJack vulnerabilities discovered by the Bastille Research Team.. These vulnerabilities enable hackers to collect confidential information, impersonate users and carry out attacks on computers and corporate networks. CABLETAP — BASTILLE CableTap Our research revealed a wide array of critical vulnerabilities in ISP-provided, RDK-based wireless gateways and set-top boxes. We demonstrated that it was possible to remotely and wirelessly tap all Internet and voice traffic passing through anaffected gateway.
CELL PHONE DETECTION Detect and Locate Unauthorized Cell phones. Bastille is the first and only product to detect and locate cellular phones within a building based only on their cellular signal. Real-time detection with alerts plus DVR-like playback for forensics. Cellular phones are a great business productivity tool, but they are also the most ubiquitousIN THE NEWS
Host Eric Michaels and guest Bob Baxley, CTO Bastille discuss Zone Detection for Healthcare. Listen. May 5, 2021. Apr 7, 2021. IN PLACE MONITORING SYSTEM (IPMS) in-place monitoring SYSTEMS. Bastille Audit is a 30-day review of your airspace. In addition to revealing potential cyber-threats for data exfiltration, Bastille Audit will provide In-Place Monitoring for all RF-enabled devices in your airspace. To request a 30 Day BastilleKEY TECHNOLOGIES
The focus for most customers is obtaining visibility into devices using the Big Four protocols: Cellular, Wi-Fi, Bluetooth and Bluetooth Low Energy. Bastille detects and locates them all of the time. Other vendors cannot detect cellular at all or can only detect cellular whenthe phone sends a
MANAGEMENT TEAM
Christian Sepulveda is VP Engineering at Bastille Networks, leading engineering and product management teams. Christian was previously one of five partners who built Pivotal Labs from 20 developers to 2,000 developers. As VP Corporate Development, Christian negotiated the sale of Pivotal Labs to EMC and stayed through the sale and transition. DEPLOYMENT — BASTILLE HOW BASTILLE IS DEPLOYED. Our proprietary sensors are usually installed in the space above the dropped ceiling of the area to be protected. The sensor units are powered by POE (Power Over Ethernet). The sensors are constructed of a special custom polymer which both permits them to perceive the full spectrum of radio emissions, but isalso
WIRELESS INTRUSION DETECTION SYSTEM (WIDS) Bastille’s Cellular Intrusion Detection is the first system which accurately detects, counts, and locates cellular devices inside your facility. To be clear, we can track devices via Bluetooth and WiFi like the other companies but the bad actors turn off those signals when they plan to undertake bad actions. To know that your facility is WEBINAR: BASTILLE TACTICAL SOLUTIONS Bastille Tactical Solutions Portable Kits for Cellular & RF Based Threat Detection and Location. Learn how to Detect and Locate unauthorized Cellular, Bluetooth, BLE, Wi-Fi and IoT devices at temporary sites such as forward deployed, conference/hotel, tent, andother
ROGUE CELL TOWERS
Rogue Cell Towers. The Bastille Research Team proactively monitors for new radio-borne threats. Their breakthrough research and discoveries such as MouseJack and KeySniffer help to keep not just Bastille clients, but the larger ecosystem safe. Each month, Bastille Research reports on and ranks the most prevalent and most pernicious attacks.WHAT IS MOUSEJACK!
MouseJack. Announced by Bastille in 2016, MouseJack is still an open vulnerability affecting devices sold today. MouseJack is a class of vulnerabilities that affects the vast majority of wireless, non-Bluetooth keyboards and mice. These peripherals are 'connected' to a host computer using a radio transceiver, commonly a small USBdongle.
BASTILLEINTRODUCTIONRESEARCH MISSIONRESEARCH TEAMVULNERABILITYDISCLOSURE
Bastille’s breakthrough and patented work provides Bastille the ability to disambiguate multiple cell phones and accurately locate those individual devices in real-time. Bastille holds 26 US Patents. Learn more about Bastille's technology. Bastille shows each device as a “dot on a floor plan map”. Bastille allows you to accuratelyINTRODUCTION
Bastille provides corporations and agencies the ability to discover, locate, and mitigate radio borne threats to their assets, facilities and networks. These threats arise from managed, unmanaged and rogue wireless, IoT and Cellular devices. Bastille does this protection by using Software Defined Radios (SDRs) to passively observe the entireOUR MISSION
Our Mission. Founded in 2014, Bastille is the leader in enterprise threat detection through software-defined radio. Bastille provides full visibility into the known and unknown mobile, wireless and Internet of Things (IoT) devices inside an enterprise’s corporate airspace – together known as the Internet of Radios.BASTILLE ENTERPRISE
The Bastille Sensor Array is the 4th-generation Software Defined Radio (SDR) sensor array from Bastille. It contains two scanning 802.11ac Wi-Fi receivers, two SDR receiver front ends that can each sample at 61.44 MSps and sense from 25 MHz to 6 GHz. An array of bespoke internal antennas have been optimized to maximize detection and CELLULAR INTRUSION DETECTION Cellular, Bluetooth, BLE & Wi-Fi Intrusion Detection. Bastille’s real-time Cellular, Bluetooth, BLE and Wi-Fi detection and location system locates all authorized and unauthorized devices within a campus or forward deployed location, accurately places dots on a floor-plan map for device location and sends alerts when a device is found where it should not be or doing what it should not do. BASTILLE FLYAWAY KIT The Bastille FlyAway Kit is a fully self-contained unit for real-time, 24/7 Cellular, Bluetooth, BLE and Wi-Fi Device Detection, Identification and Location. It covers an area up to 5,000 square feet and can detect and locate Wi-Fi, Bluetooth and BLE devices within 30 minutes, and Cellular phones within 90 minutes. GOVERNMENT - CELLULAR INTRUSION DETECTION Bastille’s Cellular Intrusion Detection is the first system which accurately detects, counts, and locates cellular devices inside your facility in real-time, 24/7. To be clear, we can track devices via Bluetooth and WiFi like the other companies but the bad actors turnoff
VULNERABLE WIRELESS PERIPHERALS Vulnerable Wireless Peripherals . Billions of wireless peripherals are vulnerable to the MouseJack, KeySniffer and KeyJack vulnerabilities discovered by the Bastille Research Team.. These vulnerabilities enable hackers to collect confidential information, impersonate users and carry out attacks on computers and corporate networks. WIRELESS INTRUSION DETECTION SYSTEM (WIDS) Bastille’s Cellular Intrusion Detection is the first system which accurately detects, counts, and locates cellular devices inside your facility. To be clear, we can track devices via Bluetooth and WiFi like the other companies but the bad actors turn off those signals when they plan to undertake bad actions. To know that your facility is WIRELESS INTRUSION DETECTION SYSTEMS (WIDS) BASTILLEINTRODUCTIONRESEARCH MISSIONRESEARCH TEAMVULNERABILITYDISCLOSURE
Bastille’s breakthrough and patented work provides Bastille the ability to disambiguate multiple cell phones and accurately locate those individual devices in real-time. Bastille holds 26 US Patents. Learn more about Bastille's technology. Bastille shows each device as a “dot on a floor plan map”. Bastille allows you to accuratelyINTRODUCTION
Bastille provides corporations and agencies the ability to discover, locate, and mitigate radio borne threats to their assets, facilities and networks. These threats arise from managed, unmanaged and rogue wireless, IoT and Cellular devices. Bastille does this protection by using Software Defined Radios (SDRs) to passively observe the entireOUR MISSION
Our Mission. Founded in 2014, Bastille is the leader in enterprise threat detection through software-defined radio. Bastille provides full visibility into the known and unknown mobile, wireless and Internet of Things (IoT) devices inside an enterprise’s corporate airspace – together known as the Internet of Radios.BASTILLE ENTERPRISE
The Bastille Sensor Array is the 4th-generation Software Defined Radio (SDR) sensor array from Bastille. It contains two scanning 802.11ac Wi-Fi receivers, two SDR receiver front ends that can each sample at 61.44 MSps and sense from 25 MHz to 6 GHz. An array of bespoke internal antennas have been optimized to maximize detection and CELLULAR INTRUSION DETECTION Cellular, Bluetooth, BLE & Wi-Fi Intrusion Detection. Bastille’s real-time Cellular, Bluetooth, BLE and Wi-Fi detection and location system locates all authorized and unauthorized devices within a campus or forward deployed location, accurately places dots on a floor-plan map for device location and sends alerts when a device is found where it should not be or doing what it should not do. BASTILLE FLYAWAY KIT The Bastille FlyAway Kit is a fully self-contained unit for real-time, 24/7 Cellular, Bluetooth, BLE and Wi-Fi Device Detection, Identification and Location. It covers an area up to 5,000 square feet and can detect and locate Wi-Fi, Bluetooth and BLE devices within 30 minutes, and Cellular phones within 90 minutes. GOVERNMENT - CELLULAR INTRUSION DETECTION Bastille’s Cellular Intrusion Detection is the first system which accurately detects, counts, and locates cellular devices inside your facility in real-time, 24/7. To be clear, we can track devices via Bluetooth and WiFi like the other companies but the bad actors turnoff
VULNERABLE WIRELESS PERIPHERALS Vulnerable Wireless Peripherals . Billions of wireless peripherals are vulnerable to the MouseJack, KeySniffer and KeyJack vulnerabilities discovered by the Bastille Research Team.. These vulnerabilities enable hackers to collect confidential information, impersonate users and carry out attacks on computers and corporate networks. WIRELESS INTRUSION DETECTION SYSTEM (WIDS) Bastille’s Cellular Intrusion Detection is the first system which accurately detects, counts, and locates cellular devices inside your facility. To be clear, we can track devices via Bluetooth and WiFi like the other companies but the bad actors turn off those signals when they plan to undertake bad actions. To know that your facility is WIRELESS INTRUSION DETECTION SYSTEMS (WIDS)OUR MISSION
Our Mission. Founded in 2014, Bastille is the leader in enterprise threat detection through software-defined radio. Bastille provides full visibility into the known and unknown mobile, wireless and Internet of Things (IoT) devices inside an enterprise’s corporate airspace – together known as the Internet of Radios. CELL PHONE DETECTION Detect and Locate Unauthorized Cell phones. Bastille is the first and only product to detect and locate cellular phones within a building based only on their cellular signal. Real-time detection with alerts plus DVR-like playback for forensics. Cellular phones are a great business productivity tool, but they are also the most ubiquitous GOVERNMENT - CELLULAR INTRUSION DETECTION Bastille’s Cellular Intrusion Detection is the first system which accurately detects, counts, and locates cellular devices inside your facility in real-time, 24/7. To be clear, we can track devices via Bluetooth and WiFi like the other companies but the bad actors turnoff
CELLULAR INTRUSION DETECTION Download the data sheet on cellular intrusion detection. Bastille is the first and only product able to detect and locate cellular phones within a building using only their cellular signal. Bastille delivers real-time detection and location with alerts, plus DVR-like playback for forensics. Companies and government agencies can best protectMANAGEMENT TEAM
Christian Sepulveda is VP Engineering at Bastille Networks, leading engineering and product management teams. Christian was previously one of five partners who built Pivotal Labs from 20 developers to 2,000 developers. As VP Corporate Development, Christian negotiated the sale of Pivotal Labs to EMC and stayed through the sale and transition. WIRELESS INTRUSION DETECTION SYSTEM (WIDS) Bastille’s Cellular Intrusion Detection is the first system which accurately detects, counts, and locates cellular devices inside your facility. To be clear, we can track devices via Bluetooth and WiFi like the other companies but the bad actors turn off those signals when they plan to undertake bad actions. To know that your facility isBASTILLE DEMO
Request a Bastille Demo to learn more about finding cell phones, RF devices, and constant monitoring for Wi-Fi hotspots, Cellular hotspots, and Bluetooth hotspots.ROGUE CELL TOWERS
Rogue Cell Towers. The Bastille Research Team proactively monitors for new radio-borne threats. Their breakthrough research and discoveries such as MouseJack and KeySniffer help to keep not just Bastille clients, but the larger ecosystem safe. Each month, Bastille Research reports on and ranks the most prevalent and most pernicious attacks. CUSTOMERS - DANA FOUNDATION Internet of Radios. "Bastille is a must have because of the sheer proliferation of all of the mobile devices that we've seen over the past four to five years. Cell phones, obviously, they've been out there for a while, but also mobile products that use industrial protocols that we know nothing about." Dana Foundation -WHAT IS MOUSEJACK!
MouseJack. Announced by Bastille in 2016, MouseJack is still an open vulnerability affecting devices sold today. MouseJack is a class of vulnerabilities that affects the vast majority of wireless, non-Bluetooth keyboards and mice. These peripherals are 'connected' to a host computer using a radio transceiver, commonly a small USBdongle.
VISIT US AT DODIIS 2019 - BOOTH 344 - SCHEDULE A DEMOProduct
Enterprise
Government
Solutions
Enterprise
Government
Research
Introduction
Research Mission
Research Team
GitHub
Vulnerability Disclosure Top Internet of Radios VulnerabilitiesKeySniffer
MouseJack
KeyJack
CableTap
SirenJack
Resources
Webinars
Data Sheets
White Papers
Videos
Education - RF101
Education - RF ProtocolsWhiteboards
About
Our Mission
Management Team
Awards
Careers
Events
Privacy Policy
Contact
Demo
Product
Enterprise
Government
Solutions
Enterprise
Government
Research
Introduction
Research Mission
Research Team
GitHub
Vulnerability Disclosure Top Internet of Radios VulnerabilitiesKeySniffer
MouseJack
KeyJack
CableTap
SirenJack
Resources
Webinars
Data Sheets
White Papers
Videos
Education - RF101
Education - RF ProtocolsWhiteboards
About
Our Mission
Management Team
Awards
Careers
Events
Privacy Policy
Contact
Demo
CELLULAR INTRUSION DETECTIONLearn more
WATCH VIDEO
IS IT REALLY WIDS IF YOU DON'T SEE CELLULAR? Many vendors sell "Wireless Intrusion Detection Systems" (WIDS). However, these systems only detect intrusions by Wi-Fi and Bluetooth devices. By far the biggest wireless intrusions are by way of cellular phones and the Bad Guys turn off Wi-Fi and Bluetooth when they don't want to be detected.Only Bastille can add cellular signal detection and accurate cellular location to any WIDS platform.Learn more
Data sheet on Cellular Intrusion Detection Download the data sheet ENFORCE "NO CELL PHONES ALLOWED" POLICIES If your policy or contract requires you to exclude cell phones from an area, use Bastille to enforce "No Cell Phones Allowed" policies. Bastille also gives you an audit trail to prove that policy is beingenforced.
Bastille’s Cellular Intrusion Detection includes DVR functionality to record historic cell phone, Wi-Fi and Bluetooth devices location for forensic investigations" id="yui_3_17_2_1_1565645182691_145"> Bastille’s Cellular Intrusion Detection includes DVR functionality to record historic cell phone, Wi-Fi and Bluetooth devices location for forensic investigationsREQUEST A DEMO
ENTERPRISE SECURITY
Bastille is the first company to enable enterprise security teams to assess and mitigate the risk associated with the growing Internet of Radios. Bastille’s patented software and security sensors bring visibility to devices emitting radio signals (Wi-Fi, cellular, wireless dongles and other IoT communications) in your organization’s airspace.BASTILLE TECHNOLOGY
Bastille’s technology scans the entire radio spectrum, identifying devices on frequencies from 60 MHz to 6 GHz. This data is then gathered and stored, and mapped so that you can understand what devices are transmitting data, and from where in your corporate airspace. This provides improved situational awareness of potential cyber threats and post-event forensic analysis. Read the AITE Group Report by Senior Analyst, Danielle Tierney on Cell phone regulation and compliance in Financial Markets. Watch the Webinar." id="yui_3_17_2_1_1565645182691_162"> Read the AITE Group Report by Senior Analyst, Danielle Tierney on Cell phone regulation and compliance in Financial Markets. Watch the Webinar.
WHO IS USING BASTILLE? Learn more about Bastille from Jon Miller, Chief Research Officer at Cylance" id="yui_3_17_2_1_1565645182691_179"> Learn more about Bastille from Jon Miller, Chief Research Officer atCylance
IT'S TIME TO TAKE THE BLINDERS OFF Learn more about Bastille Awards & Recognition" id="yui_3_17_2_1_1565645182691_197"> Learn more about Bastille Awards & Recognition Threats are becoming more complex as criminals look for new ways to use technology in their quest for valuable data. As the number of connected devices grows to more than 20 billion by 2020, the Internet of Things (IoT) will provide an unprecedented expansion of new threat vectors and Enterprises need to be able to respond. And what do 15 billion (75%) of these new devices have in common? … Radios! Much like the radios in other Wi-Fi and cellular devices. Bastille is providing solutions to allow Enterprise companies to Secure theInternet of Radios.
> “Now someone has finally taken a look and found that virtually all > of (these devices) are vulnerable. That’s pretty scary.” — Samy Kamkar in Wired Magazine -------------------------PRESS
Why you should really, really update your Logitech wireless dongle. MouseJack never really went awayREAD MORE
This Radio Hacker could Hijack Citywide Emergency Sirens to play anysound.
READ MORE
------------------------- "Cyberattack in Dallas Sets Sirens Blaring by Radio Signal,Authorities say"
Wall
Street Journal asks Bastille about the threats of hackers using radios rather than conventional computer intrusion techniques ------------------------- "Experts say wireless mice or keyboards could be vulnerable to “MouseJack” security threat" - San Francisco television stationKRON4
covers
MouseJack. Vince Cestone and Gabe Slate reporting. Bastille in the news:Back to Top
Privacy Policy
Events
Vulnerabilities
Rogue Cell Towers
Rogue Wi-Fi
Bluetooth Data Extraction Eavesdropping devices Vulnerable Wireless Peripherals Unapproved Cellular Device Presence Unapproved Wireless Cameras Wireless Building Controls Unapproved IoT devices Building Alarm SystemsJob Openings
Vulnerability DisclosureBastille Audit
Contact us
� 2019 Bastille Networks Internet Security. All Rights Reserved.Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0