Are you over 18 and want to see adult content?
More Annotations
A complete backup of pro-custom-essay.co.uk
Are you over 18 and want to see adult content?

A complete backup of sarahscucinabella.com
Are you over 18 and want to see adult content?
A complete backup of intheredrecords.com
Are you over 18 and want to see adult content?

A complete backup of kruss-scientific.com
Are you over 18 and want to see adult content?
A complete backup of kellymcgonigal.com
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of shopflawlessbeauty.com
Are you over 18 and want to see adult content?
A complete backup of infrastructure.gov.au
Are you over 18 and want to see adult content?
Text
COMMAND LISTING
Command Name: Description: AT+LSYNCSTART: No description: AT+LTEBANDSCANPRI: No description: AT+LTEBGTIMER GOOGLE - ATCOMMANDS.ORG Model: Android Version: Image Name: Nexus 5: 6.0.1: hammerhead-mmb29k-factory-e5796b14: Nexus 5: 6.0.1: hammerhead-m4b30x-factory-10cfaa5cAT+CEMODE
Search. AT+CEMODE. Description: Reads and sets UE modes of operation for EPS Found In Vendors: Huawei; Lenovo; Samsung; Known Arguments:COMMAND LISTING
Command Listing. 3500 commands in the database. Allows reading and changing terminal profile data stored in NVRAM used only at SIM initialization (does not remove/add functionality of module) SAMSUNG - AT COMMANDS Model: Android Version: Image Name: Galaxy Nexus: 4.0.1: GT-I9250_I9250XXFAKK6_I9250OXXKJ2_4.0.1_THL: GT-B5510: 2.3.6AT+VZWAPNE
Search. AT+VZWAPNE. Description: Manage APN settings Found In Vendors: ASUS; Lenovo; LG; Motorola; ZTE; Known Arguments: ATTENTION SPANNED: COMPREHENSIVE ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem Dave (Jing) Tian1, Grant Hernandez1, Joseph I. Choi1, Vanessa Frost1, Christie Ruales1, Patrick Traynor1, Hayawardh Vijayakumar2, Lee Harrison2, Amir Rahmati2,3, Michael Grace2, and Kevin R. B. Butler1 1Florida Institute for Cybersecurity (FICS) Research, University of Florida, Gainesville, FL, ASUS - ATCOMMANDS.ORG Model: Android Version: Image Name: ASUS_X008: 6.0: UL-ASUS_X008-CN-13.0.0.25-user: ASUS_X008: 6.0: UL-ZC520TL_X008-CN_CTCC-13.0.0.14-userAT+CNMI
AT+CNMI. Description: Specifies handling of newly arrived SMS messages (forward directly to PC or save in message storage and only notify the PC of the save location.AT+CGCONTRDP
Search. AT+CGCONTRDP. Description: PDP context read dynamic parameters Found In Vendors: ASUS; Huawei; Lenovo; LineageOS; MotorolaCOMMAND LISTING
Command Name: Description: AT+LSYNCSTART: No description: AT+LTEBANDSCANPRI: No description: AT+LTEBGTIMER GOOGLE - ATCOMMANDS.ORG Model: Android Version: Image Name: Nexus 5: 6.0.1: hammerhead-mmb29k-factory-e5796b14: Nexus 5: 6.0.1: hammerhead-m4b30x-factory-10cfaa5cAT+CEMODE
Search. AT+CEMODE. Description: Reads and sets UE modes of operation for EPS Found In Vendors: Huawei; Lenovo; Samsung; Known Arguments:COMMAND LISTING
Command Listing. 3500 commands in the database. Allows reading and changing terminal profile data stored in NVRAM used only at SIM initialization (does not remove/add functionality of module) SAMSUNG - AT COMMANDS Model: Android Version: Image Name: Galaxy Nexus: 4.0.1: GT-I9250_I9250XXFAKK6_I9250OXXKJ2_4.0.1_THL: GT-B5510: 2.3.6AT+VZWAPNE
Search. AT+VZWAPNE. Description: Manage APN settings Found In Vendors: ASUS; Lenovo; LG; Motorola; ZTE; Known Arguments: ATTENTION SPANNED: COMPREHENSIVE ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem Dave (Jing) Tian1, Grant Hernandez1, Joseph I. Choi1, Vanessa Frost1, Christie Ruales1, Patrick Traynor1, Hayawardh Vijayakumar2, Lee Harrison2, Amir Rahmati2,3, Michael Grace2, and Kevin R. B. Butler1 1Florida Institute for Cybersecurity (FICS) Research, University of Florida, Gainesville, FL, ASUS - ATCOMMANDS.ORG Model: Android Version: Image Name: ASUS_X008: 6.0: UL-ASUS_X008-CN-13.0.0.25-user: ASUS_X008: 6.0: UL-ZC520TL_X008-CN_CTCC-13.0.0.14-userAT+CNMI
AT+CNMI. Description: Specifies handling of newly arrived SMS messages (forward directly to PC or save in message storage and only notify the PC of the save location.AT+CGCONTRDP
Search. AT+CGCONTRDP. Description: PDP context read dynamic parameters Found In Vendors: ASUS; Huawei; Lenovo; LineageOS; MotorolaCOMMAND LISTING
Command Listing. 3500 commands in the database. Displaying 1401 —1500. «.
AT+CGREG
AT+CGREG. Description: Returns the GPRS network registration status ofthe device.
SAMSUNG - NRD90M
command name: at#pbdyn: at$nsri: at%imei: at%swv: at*4gallcputest: at*4gphytest: at*4gscctest: at*apnSAMSUNG - MMB29K
command name: at!tat: at#pbdyn: at$nsri: at&tas: at*4gallcputest: at*4gphytest: at*4gscctest: at*apnSAMSUNG - LMY48B
command name: at+akseedno: at+ambssync: at+analogtv: at+aotkeywr: at+apchiptt: at+arotatec: at+atsctestSAMSUNG - LMY48B
command name: at*mcgdseccontext: at*mcnfg: at*mcsq: at*mcusa: at*mdbcf: at*mdnpn: at*mdsptst: at*mdtmfSAMSUNG - LMY48B
command name: at*mpgs: at*mplmn: at*mproc: at*mprof: at*mqcfi: at*mqpin: at*mqpv: at*mqsc: at*mqspn: at*mqssigASUS - MMB29M
ASUS - MMB29M. Vendor: ASUS Filename: UL-ASUS_X007D-WW-13.0.6.48-user Build ID: MMB29M Model: UNKNOWN Product: WW_Phone (ASUS_X007D) AT Commands Found. 58 AT commands in this image. Displaying 1 — 20 «1; 2; 3 »
ASUS - LRX22G
ASUS - LRX22G. Vendor: ASUS Filename: UL-ASUS_Z00RD-WW-12.8.5.118-user Build ID: LRX22G Model: ASUS_Z00RD Product: WW_Phone (ASUS_Z00RD_1) AT Commands Found. 69 ATAT^SSDUPD
Search. AT^SSDUPD. Description: No description Found In Vendors: Google; ASUS; Huawei; Lenovo; LineageOS; MotorolaCOMMAND LISTING
Command Name: Description: AT+LSYNCSTART: No description: AT+LTEBANDSCANPRI: No description: AT+LTEBGTIMER GOOGLE - ATCOMMANDS.ORG Model: Android Version: Image Name: Nexus 5: 6.0.1: hammerhead-mmb29k-factory-e5796b14: Nexus 5: 6.0.1: hammerhead-m4b30x-factory-10cfaa5cAT+CEMODE
Search. AT+CEMODE. Description: Reads and sets UE modes of operation for EPS Found In Vendors: Huawei; Lenovo; Samsung; Known Arguments:COMMAND LISTING
Command Listing. 3500 commands in the database. Allows reading and changing terminal profile data stored in NVRAM used only at SIM initialization (does not remove/add functionality of module) SAMSUNG - AT COMMANDS Model: Android Version: Image Name: Galaxy Nexus: 4.0.1: GT-I9250_I9250XXFAKK6_I9250OXXKJ2_4.0.1_THL: GT-B5510: 2.3.6AT+VZWAPNE
Search. AT+VZWAPNE. Description: Manage APN settings Found In Vendors: ASUS; Lenovo; LG; Motorola; ZTE; Known Arguments: ATTENTION SPANNED: COMPREHENSIVE ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem Dave (Jing) Tian1, Grant Hernandez1, Joseph I. Choi1, Vanessa Frost1, Christie Ruales1, Patrick Traynor1, Hayawardh Vijayakumar2, Lee Harrison2, Amir Rahmati2,3, Michael Grace2, and Kevin R. B. Butler1 1Florida Institute for Cybersecurity (FICS) Research, University of Florida, Gainesville, FL, ASUS - ATCOMMANDS.ORG Model: Android Version: Image Name: ASUS_X008: 6.0: UL-ASUS_X008-CN-13.0.0.25-user: ASUS_X008: 6.0: UL-ZC520TL_X008-CN_CTCC-13.0.0.14-userAT+CNMI
AT+CNMI. Description: Specifies handling of newly arrived SMS messages (forward directly to PC or save in message storage and only notify the PC of the save location.AT+CGCONTRDP
Search. AT+CGCONTRDP. Description: PDP context read dynamic parameters Found In Vendors: ASUS; Huawei; Lenovo; LineageOS; MotorolaCOMMAND LISTING
Command Name: Description: AT+LSYNCSTART: No description: AT+LTEBANDSCANPRI: No description: AT+LTEBGTIMER GOOGLE - ATCOMMANDS.ORG Model: Android Version: Image Name: Nexus 5: 6.0.1: hammerhead-mmb29k-factory-e5796b14: Nexus 5: 6.0.1: hammerhead-m4b30x-factory-10cfaa5cAT+CEMODE
Search. AT+CEMODE. Description: Reads and sets UE modes of operation for EPS Found In Vendors: Huawei; Lenovo; Samsung; Known Arguments:COMMAND LISTING
Command Listing. 3500 commands in the database. Allows reading and changing terminal profile data stored in NVRAM used only at SIM initialization (does not remove/add functionality of module) SAMSUNG - AT COMMANDS Model: Android Version: Image Name: Galaxy Nexus: 4.0.1: GT-I9250_I9250XXFAKK6_I9250OXXKJ2_4.0.1_THL: GT-B5510: 2.3.6AT+VZWAPNE
Search. AT+VZWAPNE. Description: Manage APN settings Found In Vendors: ASUS; Lenovo; LG; Motorola; ZTE; Known Arguments: ATTENTION SPANNED: COMPREHENSIVE ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem Dave (Jing) Tian1, Grant Hernandez1, Joseph I. Choi1, Vanessa Frost1, Christie Ruales1, Patrick Traynor1, Hayawardh Vijayakumar2, Lee Harrison2, Amir Rahmati2,3, Michael Grace2, and Kevin R. B. Butler1 1Florida Institute for Cybersecurity (FICS) Research, University of Florida, Gainesville, FL, ASUS - ATCOMMANDS.ORG Model: Android Version: Image Name: ASUS_X008: 6.0: UL-ASUS_X008-CN-13.0.0.25-user: ASUS_X008: 6.0: UL-ZC520TL_X008-CN_CTCC-13.0.0.14-userAT+CNMI
AT+CNMI. Description: Specifies handling of newly arrived SMS messages (forward directly to PC or save in message storage and only notify the PC of the save location.AT+CGCONTRDP
Search. AT+CGCONTRDP. Description: PDP context read dynamic parameters Found In Vendors: ASUS; Huawei; Lenovo; LineageOS; MotorolaCOMMAND LISTING
Command Listing. 3500 commands in the database. Displaying 1401 —1500. «.
AT+CGREG
AT+CGREG. Description: Returns the GPRS network registration status ofthe device.
SAMSUNG - NRD90M
command name: at#pbdyn: at$nsri: at%imei: at%swv: at*4gallcputest: at*4gphytest: at*4gscctest: at*apnSAMSUNG - MMB29K
command name: at!tat: at#pbdyn: at$nsri: at&tas: at*4gallcputest: at*4gphytest: at*4gscctest: at*apnSAMSUNG - LMY48B
command name: at+akseedno: at+ambssync: at+analogtv: at+aotkeywr: at+apchiptt: at+arotatec: at+atsctestSAMSUNG - LMY48B
command name: at*mcgdseccontext: at*mcnfg: at*mcsq: at*mcusa: at*mdbcf: at*mdnpn: at*mdsptst: at*mdtmfSAMSUNG - LMY48B
command name: at*mpgs: at*mplmn: at*mproc: at*mprof: at*mqcfi: at*mqpin: at*mqpv: at*mqsc: at*mqspn: at*mqssigASUS - MMB29M
ASUS - MMB29M. Vendor: ASUS Filename: UL-ASUS_X007D-WW-13.0.6.48-user Build ID: MMB29M Model: UNKNOWN Product: WW_Phone (ASUS_X007D) AT Commands Found. 58 AT commands in this image. Displaying 1 — 20 «1; 2; 3 »
ASUS - LRX22G
ASUS - LRX22G. Vendor: ASUS Filename: UL-ASUS_Z00RD-WW-12.8.5.118-user Build ID: LRX22G Model: ASUS_Z00RD Product: WW_Phone (ASUS_Z00RD_1) AT Commands Found. 69 ATAT^SSDUPD
Search. AT^SSDUPD. Description: No description Found In Vendors: Google; ASUS; Huawei; Lenovo; LineageOS; MotorolaCOMMAND LISTING
Command Listing. 3500 commands in the database. Allows reading and changing terminal profile data stored in NVRAM used only at SIM initialization (does not remove/add functionality of module)AT+CEMODE
Search. AT+CEMODE. Description: Reads and sets UE modes of operation for EPS Found In Vendors: Huawei; Lenovo; Samsung; Known Arguments:AT+VZWAPNE
Search. AT+VZWAPNE. Description: Manage APN settings Found In Vendors: ASUS; Lenovo; LG; Motorola; ZTE; Known Arguments:COMMAND LISTING
Command Name: Description: AT+LSYNCSTART: No description: AT+LTEBANDSCANPRI: No description: AT+LTEBGTIMER SAMSUNG - AT COMMANDS Model: Android Version: Image Name: Galaxy Nexus: 4.0.1: GT-I9250_I9250XXFAKK6_I9250OXXKJ2_4.0.1_THL: GT-B5510: 2.3.6 ATTENTION SPANNED: COMPREHENSIVE ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem Dave (Jing) Tian1, Grant Hernandez1, Joseph I. Choi1, Vanessa Frost1, Christie Ruales1, Patrick Traynor1, Hayawardh Vijayakumar2, Lee Harrison2, Amir Rahmati2,3, Michael Grace2, and Kevin R. B. Butler1 1Florida Institute for Cybersecurity (FICS) Research, University of Florida, Gainesville, FL, GOOGLE - ATCOMMANDS.ORG Model: Android Version: Image Name: Nexus 5: 6.0.1: hammerhead-mmb29k-factory-e5796b14: Nexus 5: 6.0.1: hammerhead-m4b30x-factory-10cfaa5cAT+CGCONTRDP
Search. AT+CGCONTRDP. Description: PDP context read dynamic parameters Found In Vendors: ASUS; Huawei; Lenovo; LineageOS; Motorola ASUS - ATCOMMANDS.ORG Model: Android Version: Image Name: ASUS_X008: 6.0: UL-ASUS_X008-CN-13.0.0.25-user: ASUS_X008: 6.0: UL-ZC520TL_X008-CN_CTCC-13.0.0.14-userAT+CGREG
AT+CGREG. Description: Returns the GPRS network registration status ofthe device.
COMMAND LISTING
Command Listing. 3500 commands in the database. Allows reading and changing terminal profile data stored in NVRAM used only at SIM initialization (does not remove/add functionality of module)AT+CEMODE
Search. AT+CEMODE. Description: Reads and sets UE modes of operation for EPS Found In Vendors: Huawei; Lenovo; Samsung; Known Arguments:AT+VZWAPNE
Search. AT+VZWAPNE. Description: Manage APN settings Found In Vendors: ASUS; Lenovo; LG; Motorola; ZTE; Known Arguments:COMMAND LISTING
Command Name: Description: AT+LSYNCSTART: No description: AT+LTEBANDSCANPRI: No description: AT+LTEBGTIMER SAMSUNG - AT COMMANDS Model: Android Version: Image Name: Galaxy Nexus: 4.0.1: GT-I9250_I9250XXFAKK6_I9250OXXKJ2_4.0.1_THL: GT-B5510: 2.3.6 ATTENTION SPANNED: COMPREHENSIVE ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem Dave (Jing) Tian1, Grant Hernandez1, Joseph I. Choi1, Vanessa Frost1, Christie Ruales1, Patrick Traynor1, Hayawardh Vijayakumar2, Lee Harrison2, Amir Rahmati2,3, Michael Grace2, and Kevin R. B. Butler1 1Florida Institute for Cybersecurity (FICS) Research, University of Florida, Gainesville, FL, GOOGLE - ATCOMMANDS.ORG Model: Android Version: Image Name: Nexus 5: 6.0.1: hammerhead-mmb29k-factory-e5796b14: Nexus 5: 6.0.1: hammerhead-m4b30x-factory-10cfaa5cAT+CGCONTRDP
Search. AT+CGCONTRDP. Description: PDP context read dynamic parameters Found In Vendors: ASUS; Huawei; Lenovo; LineageOS; Motorola ASUS - ATCOMMANDS.ORG Model: Android Version: Image Name: ASUS_X008: 6.0: UL-ASUS_X008-CN-13.0.0.25-user: ASUS_X008: 6.0: UL-ZC520TL_X008-CN_CTCC-13.0.0.14-userAT+CGREG
AT+CGREG. Description: Returns the GPRS network registration status ofthe device.
AT+CGREG
AT+CGREG. Description: Returns the GPRS network registration status ofthe device.
AT+CNMI
AT+CNMI. Description: Specifies handling of newly arrived SMS messages (forward directly to PC or save in message storage and only notify the PC of the save location.SAMSUNG - NRD90M
command name: at#pbdyn: at$nsri: at%imei: at%swv: at*4gallcputest: at*4gphytest: at*4gscctest: at*apnSAMSUNG - LMY48B
command name: at+akseedno: at+ambssync: at+analogtv: at+aotkeywr: at+apchiptt: at+arotatec: at+atsctestSAMSUNG - MMB29K
command name: at!tat: at#pbdyn: at$nsri: at&tas: at*4gallcputest: at*4gphytest: at*4gscctest: at*apnSAMSUNG - LMY48B
command name: at*mcgdseccontext: at*mcnfg: at*mcsq: at*mcusa: at*mdbcf: at*mdnpn: at*mdsptst: at*mdtmfSAMSUNG - LMY48B
command name: at*mpgs: at*mplmn: at*mproc: at*mprof: at*mqcfi: at*mqpin: at*mqpv: at*mqsc: at*mqspn: at*mqssigASUS - MMB29M
ASUS - MMB29M. Vendor: ASUS Filename: UL-ASUS_X007D-WW-13.0.6.48-user Build ID: MMB29M Model: UNKNOWN Product: WW_Phone (ASUS_X007D) AT Commands Found. 58 AT commands in this image. Displaying 1 — 20 «1; 2; 3 »
SAMSUNG - NMF26X
command name: at#pbdyn: at$nsri: at%imei: at%swv: at*4gallcputest: at*4gphytest: at*4gscctest: at*apnSAMSUNG - LMY48B
command name: at#pbdyn: at$nsri: at*4gallcputest: at*4gphytest: at*4gscctest: at*apn: at*get: at*ipifstatusCOMMAND LISTING
Command Name: Description: AT+LSYNCSTART: No description: AT+LTEBANDSCANPRI: No description: AT+LTEBGTIMER GOOGLE - ATCOMMANDS.ORG Model: Android Version: Image Name: Nexus 5: 6.0.1: hammerhead-mmb29k-factory-e5796b14: Nexus 5: 6.0.1: hammerhead-m4b30x-factory-10cfaa5cAT+CEMODE
Search. AT+CEMODE. Description: Reads and sets UE modes of operation for EPS Found In Vendors: Huawei; Lenovo; Samsung; Known Arguments:COMMAND LISTING
Command Listing. 3500 commands in the database. Allows reading and changing terminal profile data stored in NVRAM used only at SIM initialization (does not remove/add functionality of module) ASUS - ATCOMMANDS.ORG Model: Android Version: Image Name: ASUS_X008: 6.0: UL-ASUS_X008-CN-13.0.0.25-user: ASUS_X008: 6.0: UL-ZC520TL_X008-CN_CTCC-13.0.0.14-user SAMSUNG - AT COMMANDS Model: Android Version: Image Name: Galaxy Nexus: 4.0.1: GT-I9250_I9250XXFAKK6_I9250OXXKJ2_4.0.1_THL: GT-B5510: 2.3.6AT+VZWAPNE
Search. AT+VZWAPNE. Description: Manage APN settings Found In Vendors: ASUS; Lenovo; LG; Motorola; ZTE; Known Arguments: ATTENTION SPANNED: COMPREHENSIVE ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem Dave (Jing) Tian1, Grant Hernandez1, Joseph I. Choi1, Vanessa Frost1, Christie Ruales1, Patrick Traynor1, Hayawardh Vijayakumar2, Lee Harrison2, Amir Rahmati2,3, Michael Grace2, and Kevin R. B. Butler1 1Florida Institute for Cybersecurity (FICS) Research, University of Florida, Gainesville, FL,AT+CGCONTRDP
Search. AT+CGCONTRDP. Description: PDP context read dynamic parameters Found In Vendors: ASUS; Huawei; Lenovo; LineageOS; MotorolaASUS - MMB29M
ASUS - MMB29M. Vendor: ASUS Filename: UL-ASUS_X007D-WW-13.0.6.48-user Build ID: MMB29M Model: UNKNOWN Product: WW_Phone (ASUS_X007D) AT Commands Found. 58 AT commands in this image. Displaying 1 — 20 «1; 2; 3 »
COMMAND LISTING
Command Name: Description: AT+LSYNCSTART: No description: AT+LTEBANDSCANPRI: No description: AT+LTEBGTIMER GOOGLE - ATCOMMANDS.ORG Model: Android Version: Image Name: Nexus 5: 6.0.1: hammerhead-mmb29k-factory-e5796b14: Nexus 5: 6.0.1: hammerhead-m4b30x-factory-10cfaa5cAT+CEMODE
Search. AT+CEMODE. Description: Reads and sets UE modes of operation for EPS Found In Vendors: Huawei; Lenovo; Samsung; Known Arguments:COMMAND LISTING
Command Listing. 3500 commands in the database. Allows reading and changing terminal profile data stored in NVRAM used only at SIM initialization (does not remove/add functionality of module) ASUS - ATCOMMANDS.ORG Model: Android Version: Image Name: ASUS_X008: 6.0: UL-ASUS_X008-CN-13.0.0.25-user: ASUS_X008: 6.0: UL-ZC520TL_X008-CN_CTCC-13.0.0.14-user SAMSUNG - AT COMMANDS Model: Android Version: Image Name: Galaxy Nexus: 4.0.1: GT-I9250_I9250XXFAKK6_I9250OXXKJ2_4.0.1_THL: GT-B5510: 2.3.6AT+VZWAPNE
Search. AT+VZWAPNE. Description: Manage APN settings Found In Vendors: ASUS; Lenovo; LG; Motorola; ZTE; Known Arguments: ATTENTION SPANNED: COMPREHENSIVE ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem Dave (Jing) Tian1, Grant Hernandez1, Joseph I. Choi1, Vanessa Frost1, Christie Ruales1, Patrick Traynor1, Hayawardh Vijayakumar2, Lee Harrison2, Amir Rahmati2,3, Michael Grace2, and Kevin R. B. Butler1 1Florida Institute for Cybersecurity (FICS) Research, University of Florida, Gainesville, FL,AT+CGCONTRDP
Search. AT+CGCONTRDP. Description: PDP context read dynamic parameters Found In Vendors: ASUS; Huawei; Lenovo; LineageOS; MotorolaASUS - MMB29M
ASUS - MMB29M. Vendor: ASUS Filename: UL-ASUS_X007D-WW-13.0.6.48-user Build ID: MMB29M Model: UNKNOWN Product: WW_Phone (ASUS_X007D) AT Commands Found. 58 AT commands in this image. Displaying 1 — 20 «1; 2; 3 »
ATTENTION SPANNED: COMPREHENSIVE ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem Dave (Jing) Tian1, Grant Hernandez1, Joseph I. Choi1, Vanessa Frost1, Christie Ruales1, Patrick Traynor1, Hayawardh Vijayakumar2, Lee Harrison2, Amir Rahmati2,3, Michael Grace2, and Kevin R. B. Butler1 1Florida Institute for Cybersecurity (FICS) Research, University of Florida, Gainesville, FL, SAMSUNG - AT COMMANDS Model: Android Version: Image Name: SM-G930W8: 7.0: G930W8VLU2BQH1_G930W8OYA2BQH1_RWC_4files: SM-G935F: 6.0.1: SAMSUNG - AT COMMANDS Model: Android Version: Image Name: SM-J510FN: 6.0.1: J510FNXXU1APF8_J510FNOLE1APF3_XID: SM-J510GN: 6.0.1: J510GNDXU1APF4_J510GNOLB1APF4_XME MOTOROLA - MPJ24.139-48 Motorola - MPJ24.139-48. Vendor: Motorola Filename: XT1642_ATHENE_6.0.1_MPJ24.139-48_cid50_subsidy-DEFAULT_CFC.xml Build ID: MPJ24.139-48 Model: Moto G (4) Product: athene_retail (athene) AT Commands Found. 59 AT commands in this image. Displaying 1 — 20 «1; 2; 3 »
AT+CGREG
AT+CGREG. Description: Returns the GPRS network registration status ofthe device.
ASUS - MMB29P
ASUS - MMB29P. Vendor: ASUS Filename: UL-Z00L-WW-21.40.1220.2171-user Build ID: MMB29P Model: ASUS_Z00LD Product: WW_Z00L (ASUS_Z00L_63) AT Commands Found. 59 AT commands in this image. Displaying 1 — 20 «1; 2; 3 »
ASUS - LRX22G
ASUS - LRX22G. Vendor: ASUS Filename: UL-ASUS_Z00RD-WW-12.8.5.118-user Build ID: LRX22G Model: ASUS_Z00RD Product: WW_Phone (ASUS_Z00RD_1) AT Commands Found. 69 ATASUS - LMY47I
command name: at#cls: at$csq: at%accel: at%acs: at%alarm: at%alb: at%avr: at%btad: at%bttm: at%cam: at%cctSAMSUNG - LMY48B
command name: at#pbdyn: at$nsri: at*4gallcputest: at*4gphytest: at*4gscctest: at*apn: at*get: at*ipifstatus HUAWEI - HUAWEIY520-U22 command name: at+wifi: at+witof: at+wnam: at+writebarcode: at+wrmp: at+wsos: at@gbv: at@gcsf: at@scc: at^allverAT+DB
* Home (current)
* Database
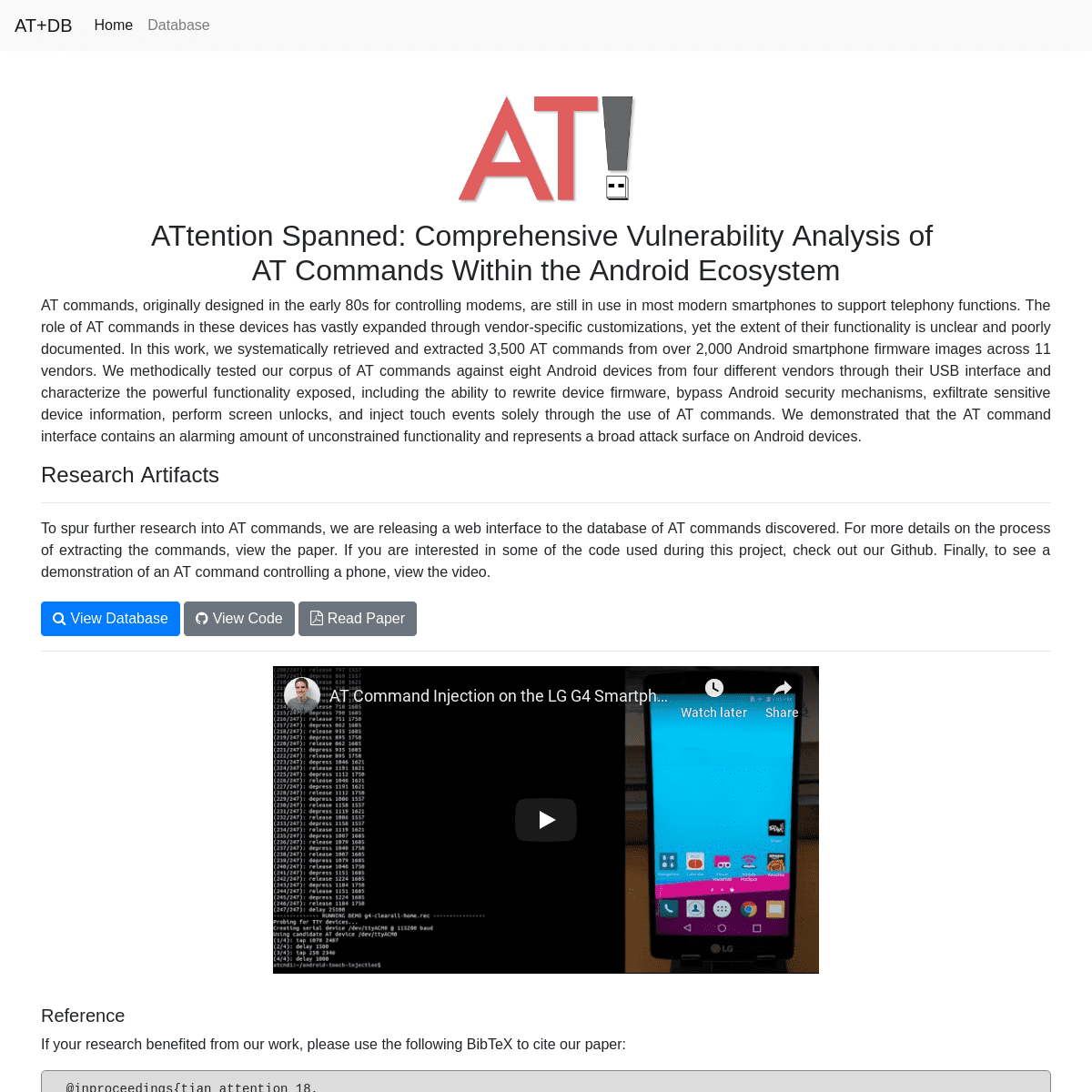
ATTENTION SPANNED: COMPREHENSIVE VULNERABILITY ANALYSIS OF AT COMMANDS WITHIN THE ANDROID ECOSYSTEM AT commands, originally designed in the early 80s for controlling modems, are still in use in most modern smartphones to support telephony functions. The role of AT commands in these devices has vastly expanded through vendor-specific customizations, yet the extent of their functionality is unclear and poorly documented. In this work, we systematically retrieved and extracted 3,500 AT commands from over 2,000 Android smartphone firmware images across 11 vendors. We methodically tested our corpus of AT commands against eight Android devices from four different vendors through their USB interface and characterize the powerful functionality exposed, including the ability to rewrite device firmware, bypass Android security mechanisms, exfiltrate sensitive device information, perform screen unlocks, and inject touch events solely through the use of AT commands. We demonstrated that the AT command interface contains an alarming amount of unconstrained functionality and represents a broad attack surfaceon Android devices.
RESEARCH ARTIFACTS
------------------------- To spur further research into AT commands, we are releasing a web interface to the database of AT commands discovered. For more details on the process of extracting the commands, view the paper. If you are interested in some of the code used during this project, check out our Github. Finally, to see a demonstration of an AT command controlling a phone, view the video. __ View Database __ View Code__ Read Paper
-------------------------REFERENCE
If your research benefited from our work, please use the following BibTeX to cite our paper: @inproceedings{tian_attention_18, author = {Dave Tian and Grant Hernandez and Joseph Choi and Vanessa Frost and Christie Ruales and Kevin Butler and Patrick Traynor and Hayawardh Vijayakumar and Lee Harrison and Amir Rahmati and Mike Grace}, title = {{ATtention Spanned: Comprehensive Vulnerability Analysis of AT Commands Within the Android Ecosystem}}, booktitle = {27th {USENIX} Security Symposium ({USENIX} Security 18)},year = {2018},
isbn = {978-1-931971-232}, address = {Baltimore, MD}, pages = {351--366}, url = {https://www.usenix.org/conference/usenixsecurity18/presentation/tian}, publisher = {{USENIX} Association},}
FAQ
------------------------- WHAT ARE AT COMMANDS? AT (ATtention) commands were first developed by Dennis Hayes in 1981 for controlling modems. These commands, when accepted by a modem in data mode (without needing a separate port), allow: selection of communication protocol, setting of line speed, dialing numbers, hanging up calls, etc. Since their inception in the 1980s, AT commands have become the preferred means of controlling modems, with standardized AT command sets being issued by authorities such as the International Telephone Union (ITU-T) and the European Telecommunications Standards Institute (ETSI). WHAT ABOUT AT COMMANDS ON (ANDROID) SMARTPHONES? Smartphones contain cellular baseband processors that provide modem functionality, allowing these devices to communicate with the cellular network, and accept AT commands for configuration. Beyond just standardized modem commands, we found that some Android device manufacturers will add custom/proprietary AT commands; these extended AT commands often do not invoke telephony-related functionality but instead access other resources on the device. HOW DOES THIS AFFECT ME? On _some_ Android smartphones, an AT command interface is exposed over USB without USB debugging enabled. Unfortunately, some devices do not authenticate this interface or allow it to be used from the lockscreen. We found that in some cases the "charge-only" USB mode may also fail to block AT commands. This means unsuspecting users who plug in their phones to a USB port for charging or data transfer may have their devices locally compromised by a (possibly pre-recorded) sequence of AT commands. Furthermore, many commands, such as those for ex-filtrating sensitive data, have no visible side-effects. HAVE YOU FOUND ANY VULNERABILITIES? Yes. We have notified each vendor of any relevant findings and have worked with their security teams to remediate the issues. For LG we were assigned the vulnerability number LVE-SMP-180001. DID YOU FIND ANY REMOTELY EXPLOITABLE VULNERABILITIES? No. All of our investigation centered on the device's USB connection. We _did not_ investigate remote AT attack surface, but the first places we would look would be the BlueTooth interface and thebaseband.
DO YOU HAVE A LIST OF DEVICES THAT THIS AFFECTS? We do in our full paper linked above. While we could not test every device we tried to study more at once than previous work.BUT WHAT ABOUT X?
If you have further questions not answered by this page or by our paper, please reach out to the authors on Twitter __ (Grant Hernandez, Dave Tian
, Kevin Butler
) or via the email in the pagefooter.
PRESS COVERAGE
* “Exploiting Decades-Old Telephone Tech to Break into AndroidDevices”
— Wired
* “AT Command Hitch Leaves Android Phones Open to Attack” — Threatpost article * “Smartphone security risk compared to 'having a ghost user onyour phone'”
— UF News article
* “What the hack: UF research reveals smartphones can be hacked viaUSB”
— the independent florida alligator article * “Smartphones From 11 OEMs Vulnerable to Attacks via Hidden ATCommands”
— BleepingComputer article * “How to Protect Yourself From Public USB Charging Ports” — How-To Geek Article * “Smartphones from 11 OEMs, Including Google, Samsung, HTC, Lenovo and Sony, Vulnerable to Attacks Via Hidden AT Commands” — slashdot.org post * “Attention Spanned: Comprehensive Android Vulnerability Analysisof AT Commands”
— Hacker News mention * “Android mobile devices from 11 vendors are exposed to ATCommands attacks”
— Security Affairs article * “Android at the mercy of AT Commands” — Fudzilla article * “Android smartphones can be hacked with AT commands attacks” — Tech Worm article * “How These Android Smartphone Can Be Hacked With Simple ATcommands”
— Fossbytes article * “Modern smartphones vulnerable to old-school attack” — The Kim Komando Show article * “Open AT Commands: a Huge Loophole Exploit in Android Revealed” — Hacker Combat Community article * “Vulnerability Found in Major Manufacturers of Android Phones” — SecurePoint Blog article * “Smartphones are vulnerable to hacking commands for ancientmodems”
— Hybrid Techcar article * “New security risk for smartphones brings you a “ghostuser””
— Android Community article* “AT Commands”
— SANS Daily Network Security Podcast (Stormiest) for Monday, August27th 2018
* “Android-Smartphones durch Modem-Befehle verwundbar” — golem.de article * “У 11 производителей Android-смартфонов обнаружили уязвимость к AT-командам”— Tproger article
* “Злоумышленники могут получить полный удаленный доступ к Android-устройству через порт публичной USB-зарядки”— habr article
* “Miliony smartfonów można zhackować ukrytymi komendami AT” — Niebezpiecznik articleACKNOWLEDGMENTS
------------------------- We'd like to thank Samsung Research America for kickstarting the initial research during Dave Tian's internship and for lending us Android devices for testing. This work was supported by the National Science Foundation under grants CNS-1540217, CNS-1526718, CNS-1564140, and CNS-1617474.* __
* __
* __
Florida Institute _for_ Cyber Security Research� 2018
Website designed by Grant HernandezLogo by Joseph Choi
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0