Are you over 18 and want to see adult content?
More Annotations

A complete backup of gameofwifes.tumblr.com
Are you over 18 and want to see adult content?

A complete backup of leisuredayssmithsfalls.ca
Are you over 18 and want to see adult content?

A complete backup of business-management-degree.net
Are you over 18 and want to see adult content?
A complete backup of darmanshow.blog.ir
Are you over 18 and want to see adult content?

A complete backup of acadmatecetis21.blogspot.com
Are you over 18 and want to see adult content?
A complete backup of gigapurbalingga.net
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of sport.se.pl/pilka-nozna/liga-mistrzow/tottenham-rb-lipsk-tv-online-transmisja-na-zywo-liga-mistrzow-gdzie-o
Are you over 18 and want to see adult content?
A complete backup of aajtak.intoday.in/story/bhoot-the-haunted-ship-review-in-hindi-vicky-kaushal-bhumi-pednekar-movie-reaction-
Are you over 18 and want to see adult content?
A complete backup of www.indiatoday.in/movies/regional-cinema/story/mamata-banerjee-on-tapas-pal-death-we-will-miss-the-supersta
Are you over 18 and want to see adult content?
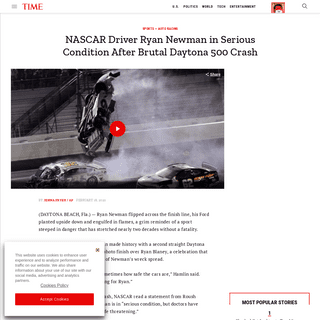
A complete backup of time.com/5785571/daytona-500-crash-ryan-newman/
Are you over 18 and want to see adult content?
Text
HADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ABOUT ALEPH RESEARCH About Page of Aleph Research. We are a team of researchers focused on discovering security vulnerabilities. REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. GOOGLE NEXUS 6 & 6P EDL TRIGGERING Google Nexus 6 & 6P EDL triggering through ADB. As one can see, the enable_edl module parameter, that can be controlled through sysfs, determines whether it’s possible to reboot into EDL or not.Despite that, a root attacker capable on writing on files with the sysfs SELinux context can set that variable. The Google Nexus 6P Firehose programmer has been leaked ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ABOUT ALEPH RESEARCH About Page of Aleph Research. We are a team of researchers focused on discovering security vulnerabilities. REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. GOOGLE NEXUS 6 & 6P EDL TRIGGERING Google Nexus 6 & 6P EDL triggering through ADB. As one can see, the enable_edl module parameter, that can be controlled through sysfs, determines whether it’s possible to reboot into EDL or not.Despite that, a root attacker capable on writing on files with the sysfs SELinux context can set that variable. The Google Nexus 6P Firehose programmer has been leaked ALEPH RESEARCH POSTS ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18. ABOUT ALEPH RESEARCH About Page of Aleph Research. We are a team of researchers focused on discovering security vulnerabilities. REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface.BREAKING ALGORITHMS
Introduction. This post introduces Z3; an MIT licensed SMT solver from Microsoft Research.We’ll discuss some typical uses of SMT solvers, show how to generate constraints using Z3’s Python bindings and provide an example for the use of this technology for WebApp security. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. INITROOT: HELLO MOTO initroot: Hello Moto. In the previous blog post, we suggested that CVE-2016-10277 could affect other Motorola devices. After receiving a few reports on Twitter that this was indeed the case, we acquired a couple of Motorola devices, updated to the latest available build we received over-the-air: INITROOT: BYPASSING NEXUS 6 SECURE BOOT THROUGH KERNEL initroot: Bypassing Nexus 6 Secure Boot through Kernel Command-line Injection. In the May 2017 Android Security Bulletin, Google released a patch to a critical and unique vulnerability CVE-2016-10277 in the Nexus 6 Motorola bootloader we had found and responsibly disclosed. It should be noted that although we only verified this issue on Nexus 6 MOTOROLA ANDROID BOOTLOADER UNLOCKING A RE User re-locks the device. Bootloader writes an entry under the sp partition, with an HMAC produced by TEE. User unlocks the device. Bootloader removes that entry. Conclusion: An unrestricted root (as one could gain by exploiting CVE-2016-10277) can unlock a MOTOROLA ANDROID BOOTLOADER KERNEL The fsg-id, carrier and console parameters can contain arbitrary values, which eventually propagate to the kernel command line. Now, if the bootloader didn’t sanitize these arguments, one could pass arbitrary kernel command line arguments: $ fastboot oem config console "a foo=0 "$ fastboot oem config fsg-id "a bar=1" $ fastboot oem configcarrier "a baz=2"
ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ABOUT ALEPH RESEARCH About Page of Aleph Research. We are a team of researchers focused on discovering security vulnerabilities. REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. GOOGLE NEXUS 6 & 6P EDL TRIGGERING Google Nexus 6 & 6P EDL triggering through ADB. As one can see, the enable_edl module parameter, that can be controlled through sysfs, determines whether it’s possible to reboot into EDL or not.Despite that, a root attacker capable on writing on files with the sysfs SELinux context can set that variable. The Google Nexus 6P Firehose programmer has been leaked ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy. EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. ALEPH RESEARCH POSTS ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ABOUT ALEPH RESEARCH About Page of Aleph Research. We are a team of researchers focused on discovering security vulnerabilities. EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface.BREAKING ALGORITHMS
Introduction. This post introduces Z3; an MIT licensed SMT solver from Microsoft Research.We’ll discuss some typical uses of SMT solvers, show how to generate constraints using Z3’s Python bindings and provide an example for the use of this technology for WebApp security. INITROOT: BYPASSING NEXUS 6 SECURE BOOT THROUGH KERNEL initroot: Bypassing Nexus 6 Secure Boot through Kernel Command-line Injection. In the May 2017 Android Security Bulletin, Google released a patch to a critical and unique vulnerability CVE-2016-10277 in the Nexus 6 Motorola bootloader we had found and responsibly disclosed. It should be noted that although we only verified this issue on Nexus 6 QUALCOMM EDL FIREHOSE PROGRAMMERS PEEK … Technical Details. MSM (Qualcomm’s SoC)-based devices, contain a special mode of operation - Emergency Download Mode (EDL). In this mode, the device identifies itself as Qualcomm HS-USB 9008 through USB. EDL, is implemented by the Primary Bootloader (PBL), allows to escape from the unfortunate situation where the second stagebootloader
INITROOT: HELLO MOTO initroot: Hello Moto. In the previous blog post, we suggested that CVE-2016-10277 could affect other Motorola devices. After receiving a few reports on Twitter that this was indeed the case, we acquired a couple of Motorola devices, updated to the latest available build we received over-the-air: MOTOROLA ANDROID BOOTLOADER UNLOCKING A RE User re-locks the device. Bootloader writes an entry under the sp partition, with an HMAC produced by TEE. User unlocks the device. Bootloader removes that entry. Conclusion: An unrestricted root (as one could gain by exploiting CVE-2016-10277) can unlock a MOTOROLA ANDROID BOOTLOADER KERNEL The fsg-id, carrier and console parameters can contain arbitrary values, which eventually propagate to the kernel command line. Now, if the bootloader didn’t sanitize these arguments, one could pass arbitrary kernel command line arguments: $ fastboot oem config console "a foo=0 "$ fastboot oem config fsg-id "a bar=1" $ fastboot oem configcarrier "a baz=2"
ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy. EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy. EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. ALEPH RESEARCH POSTS ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ABOUT ALEPH RESEARCH About Page of Aleph Research. We are a team of researchers focused on discovering security vulnerabilities. EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface.BREAKING ALGORITHMS
Introduction. This post introduces Z3; an MIT licensed SMT solver from Microsoft Research.We’ll discuss some typical uses of SMT solvers, show how to generate constraints using Z3’s Python bindings and provide an example for the use of this technology for WebApp security. INITROOT: BYPASSING NEXUS 6 SECURE BOOT THROUGH KERNEL initroot: Bypassing Nexus 6 Secure Boot through Kernel Command-line Injection. In the May 2017 Android Security Bulletin, Google released a patch to a critical and unique vulnerability CVE-2016-10277 in the Nexus 6 Motorola bootloader we had found and responsibly disclosed. It should be noted that although we only verified this issue on Nexus 6 QUALCOMM EDL FIREHOSE PROGRAMMERS PEEK … Technical Details. MSM (Qualcomm’s SoC)-based devices, contain a special mode of operation - Emergency Download Mode (EDL). In this mode, the device identifies itself as Qualcomm HS-USB 9008 through USB. EDL, is implemented by the Primary Bootloader (PBL), allows to escape from the unfortunate situation where the second stagebootloader
INITROOT: HELLO MOTO initroot: Hello Moto. In the previous blog post, we suggested that CVE-2016-10277 could affect other Motorola devices. After receiving a few reports on Twitter that this was indeed the case, we acquired a couple of Motorola devices, updated to the latest available build we received over-the-air: MOTOROLA ANDROID BOOTLOADER UNLOCKING A RE User re-locks the device. Bootloader writes an entry under the sp partition, with an HMAC produced by TEE. User unlocks the device. Bootloader removes that entry. Conclusion: An unrestricted root (as one could gain by exploiting CVE-2016-10277) can unlock a MOTOROLA ANDROID BOOTLOADER KERNEL The fsg-id, carrier and console parameters can contain arbitrary values, which eventually propagate to the kernel command line. Now, if the bootloader didn’t sanitize these arguments, one could pass arbitrary kernel command line arguments: $ fastboot oem config console "a foo=0 "$ fastboot oem config fsg-id "a bar=1" $ fastboot oem configcarrier "a baz=2"
ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy. EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy. EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. ALEPH RESEARCH POSTS ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ABOUT ALEPH RESEARCH About Page of Aleph Research. We are a team of researchers focused on discovering security vulnerabilities. EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface.BREAKING ALGORITHMS
Introduction. This post introduces Z3; an MIT licensed SMT solver from Microsoft Research.We’ll discuss some typical uses of SMT solvers, show how to generate constraints using Z3’s Python bindings and provide an example for the use of this technology for WebApp security. INITROOT: BYPASSING NEXUS 6 SECURE BOOT THROUGH KERNEL initroot: Bypassing Nexus 6 Secure Boot through Kernel Command-line Injection. In the May 2017 Android Security Bulletin, Google released a patch to a critical and unique vulnerability CVE-2016-10277 in the Nexus 6 Motorola bootloader we had found and responsibly disclosed. It should be noted that although we only verified this issue on Nexus 6 QUALCOMM EDL FIREHOSE PROGRAMMERS PEEK … Technical Details. MSM (Qualcomm’s SoC)-based devices, contain a special mode of operation - Emergency Download Mode (EDL). In this mode, the device identifies itself as Qualcomm HS-USB 9008 through USB. EDL, is implemented by the Primary Bootloader (PBL), allows to escape from the unfortunate situation where the second stagebootloader
INITROOT: HELLO MOTO initroot: Hello Moto. In the previous blog post, we suggested that CVE-2016-10277 could affect other Motorola devices. After receiving a few reports on Twitter that this was indeed the case, we acquired a couple of Motorola devices, updated to the latest available build we received over-the-air: MOTOROLA ANDROID BOOTLOADER UNLOCKING A RE User re-locks the device. Bootloader writes an entry under the sp partition, with an HMAC produced by TEE. User unlocks the device. Bootloader removes that entry. Conclusion: An unrestricted root (as one could gain by exploiting CVE-2016-10277) can unlock a MOTOROLA ANDROID BOOTLOADER KERNEL The fsg-id, carrier and console parameters can contain arbitrary values, which eventually propagate to the kernel command line. Now, if the bootloader didn’t sanitize these arguments, one could pass arbitrary kernel command line arguments: $ fastboot oem config console "a foo=0 "$ fastboot oem config fsg-id "a bar=1" $ fastboot oem configcarrier "a baz=2"
ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy. EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy. EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. ALEPH RESEARCH POSTS ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ABOUT ALEPH RESEARCH About Page of Aleph Research. We are a team of researchers focused on discovering security vulnerabilities. EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface.BREAKING ALGORITHMS
Introduction. This post introduces Z3; an MIT licensed SMT solver from Microsoft Research.We’ll discuss some typical uses of SMT solvers, show how to generate constraints using Z3’s Python bindings and provide an example for the use of this technology for WebApp security. INITROOT: BYPASSING NEXUS 6 SECURE BOOT THROUGH KERNEL initroot: Bypassing Nexus 6 Secure Boot through Kernel Command-line Injection. In the May 2017 Android Security Bulletin, Google released a patch to a critical and unique vulnerability CVE-2016-10277 in the Nexus 6 Motorola bootloader we had found and responsibly disclosed. It should be noted that although we only verified this issue on Nexus 6 QUALCOMM EDL FIREHOSE PROGRAMMERS PEEK … Technical Details. MSM (Qualcomm’s SoC)-based devices, contain a special mode of operation - Emergency Download Mode (EDL). In this mode, the device identifies itself as Qualcomm HS-USB 9008 through USB. EDL, is implemented by the Primary Bootloader (PBL), allows to escape from the unfortunate situation where the second stagebootloader
INITROOT: HELLO MOTO initroot: Hello Moto. In the previous blog post, we suggested that CVE-2016-10277 could affect other Motorola devices. After receiving a few reports on Twitter that this was indeed the case, we acquired a couple of Motorola devices, updated to the latest available build we received over-the-air: MOTOROLA ANDROID BOOTLOADER UNLOCKING A RE User re-locks the device. Bootloader writes an entry under the sp partition, with an HMAC produced by TEE. User unlocks the device. Bootloader removes that entry. Conclusion: An unrestricted root (as one could gain by exploiting CVE-2016-10277) can unlock a MOTOROLA ANDROID BOOTLOADER KERNEL The fsg-id, carrier and console parameters can contain arbitrary values, which eventually propagate to the kernel command line. Now, if the bootloader didn’t sanitize these arguments, one could pass arbitrary kernel command line arguments: $ fastboot oem config console "a foo=0 "$ fastboot oem config fsg-id "a bar=1" $ fastboot oem configcarrier "a baz=2"
ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy. EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. ALEPH RESEARCHLEV ARONSKYTZACHY HORESHJONATHAN AFEKGIL MIRMOVITCHNOAMHADADROEE HAY
ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ALEPH RESEARCH VULNERABILITY REPORTS ALEPH-2018006. Potential DOS vulnerability in WCF services. 10/22/18. ALEPH-2018005. Potential DOS vulnerability in applications that use ASP.NET Web API. 10/22/18. ALEPH-2018004. Applications that use Newtonsoft.Json might be exposed to DOS vulnerability. 10/22/18.DON'T RUCK US AGAIN
Ruckus Networks is a company selling wired and wireless networking equipment and software. For the right context, we recommend checking our previous research found here. This current research resulted in 2 different pre-authentication remote code executions. Exploitation uses vulnerabilities such as information leakage, credentials overwrite REVISED HOMOGRAPH ATTACKS In this post we’ll talk about IDN Homograph attacks and how we bypass various browsers policies. As a side note, the name homograph is commonly used for this attack even though the term homoglyph is a better-suited name. This research started a few months back when Chrome had a different IDN policy. EXPLOITING QUALCOMM EDL PROGRAMMERS (2): STORAGE-BASEDSEE MORE ONALEPHSECURITY.COM
EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). DON'T RUCK US TOO HARD Symbolic link to /tmp: CVE-2019-19843. The above command showed us there was a symbolic link from /web/user/wps_tool_cache to /tmp directory. Since we ran R510 in a full QEMU system, we noticed there was some system logic stored in the /tmp directory. In particular, rpm.log was written as a part of system initialization. When examining this log file, we noticed that every day, rpmd created a REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface. EXPLOITING QUALCOMM EDL PROGRAMMERS (1): GAINING ACCESS There are many guides across the Internet for ‘unbricking’ Qualcomm-based mobile devices.All of these guides make use of Emergency Download Mode (EDL), an alternate boot-mode of the Qualcomm Boot ROM (Primary Bootloader). To make any use of this mode, users must get hold of OEM-signed programmers, which seem to be publicly available for various such devices. RUCKUS CLI (RKSCLI) JAILBREAK Ruckus CLI (rkscli) jailbreak. This is a command injection vulnerability via a crafted CLI command with admin privilege. ALEPH RESEARCH POSTS ALEPH-2018005. ALEPH-2018006. Overcoming (some) Spectre browser mitigations. By Noam Hadad & Jonathan Afek, 26-Jun 2018. , Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's Secure Boot. By Roee Hay & Noam Hadad, 22-Jan 2018. ABOUT ALEPH RESEARCH About Page of Aleph Research. We are a team of researchers focused on discovering security vulnerabilities. EXPLOITING CRASH HANDLERS: LPE ON UBUNTU Run the decoy process and “stall” the first Apport instance. Create a symlink to /usr/bin/sudo and rename the symlink to “a\rUid: 0\rGid: 0” (so we can have a suid program with injected Name in /proc/pid/status). Chdir to /etc/logrotate.d/. Create the crash program (from now on the process PID is crash_pid). REVISED HOMOGRAPH ATTACKS The internationalized domain name (IDN) homograph attack is a way a malicious party may deceive computer users about what remote system they are communicating with, by exploiting the fact that many different characters look alike. This is the best known, most prevalent form of attack (2019) for this attack surface.BREAKING ALGORITHMS
Introduction. This post introduces Z3; an MIT licensed SMT solver from Microsoft Research.We’ll discuss some typical uses of SMT solvers, show how to generate constraints using Z3’s Python bindings and provide an example for the use of this technology for WebApp security. INITROOT: BYPASSING NEXUS 6 SECURE BOOT THROUGH KERNEL initroot: Bypassing Nexus 6 Secure Boot through Kernel Command-line Injection. In the May 2017 Android Security Bulletin, Google released a patch to a critical and unique vulnerability CVE-2016-10277 in the Nexus 6 Motorola bootloader we had found and responsibly disclosed. It should be noted that although we only verified this issue on Nexus 6 QUALCOMM EDL FIREHOSE PROGRAMMERS PEEK … Technical Details. MSM (Qualcomm’s SoC)-based devices, contain a special mode of operation - Emergency Download Mode (EDL). In this mode, the device identifies itself as Qualcomm HS-USB 9008 through USB. EDL, is implemented by the Primary Bootloader (PBL), allows to escape from the unfortunate situation where the second stagebootloader
INITROOT: HELLO MOTO initroot: Hello Moto. In the previous blog post, we suggested that CVE-2016-10277 could affect other Motorola devices. After receiving a few reports on Twitter that this was indeed the case, we acquired a couple of Motorola devices, updated to the latest available build we received over-the-air: MOTOROLA ANDROID BOOTLOADER UNLOCKING A RE User re-locks the device. Bootloader writes an entry under the sp partition, with an HMAC produced by TEE. User unlocks the device. Bootloader removes that entry. Conclusion: An unrestricted root (as one could gain by exploiting CVE-2016-10277) can unlock a MOTOROLA ANDROID BOOTLOADER KERNEL The fsg-id, carrier and console parameters can contain arbitrary values, which eventually propagate to the kernel command line. Now, if the bootloader didn’t sanitize these arguments, one could pass arbitrary kernel command line arguments: $ fastboot oem config console "a foo=0 "$ fastboot oem config fsg-id "a bar=1" $ fastboot oem configcarrier "a baz=2"
א
00 _00
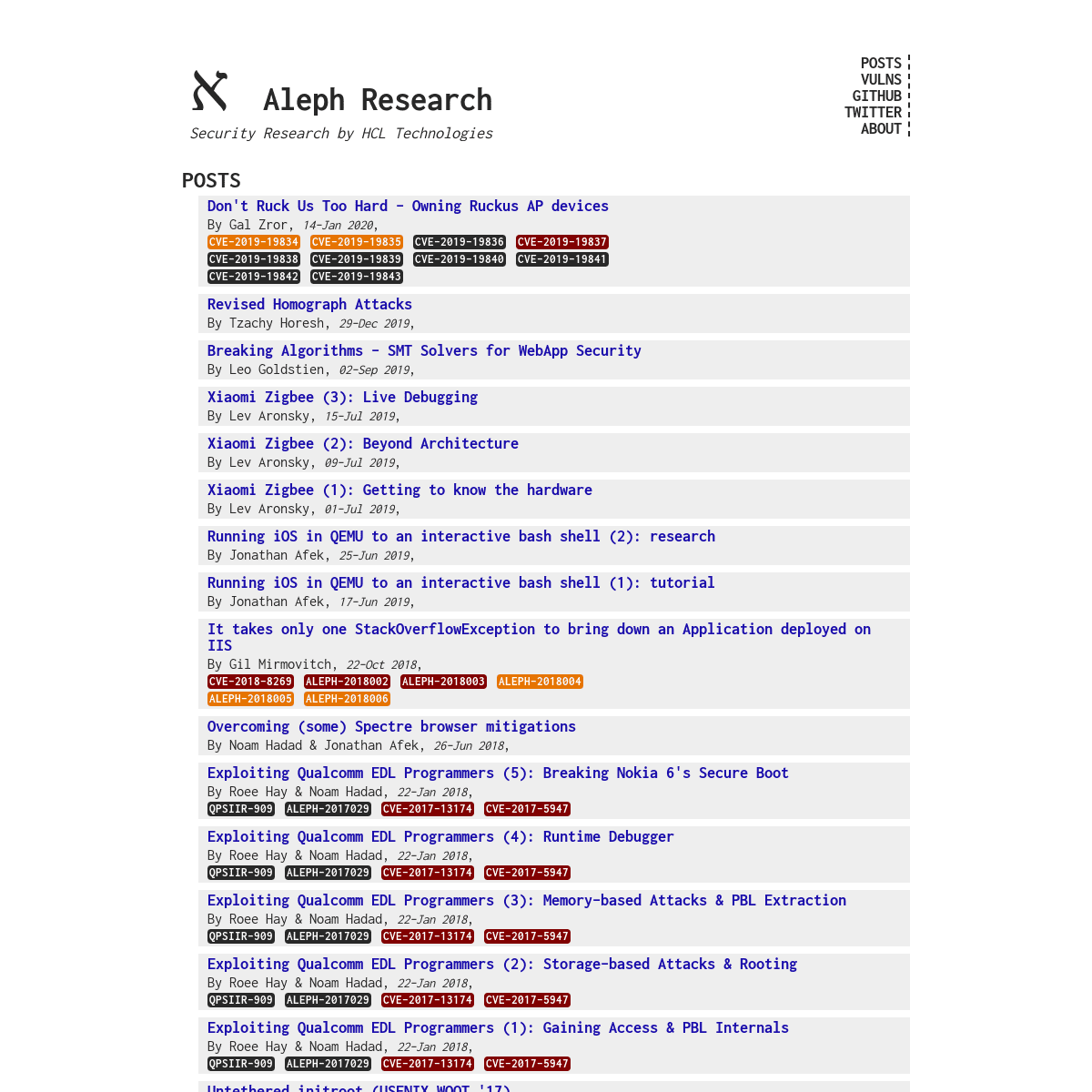
Aleph Research
* POSTS
* VULNS
* GITHUB
* ABOUT
SECURITY RESEARCH BY HCL TECHNOLOGIESBY HCL TECH
POSTS
* Don't Ruck Us Too Hard - Owning Ruckus AP devicesBy Gal Zror ,
14-Jan 2020,
CVE-2019-19834
CVE-2019-19835
CVE-2019-19836
CVE-2019-19837
CVE-2019-19838
CVE-2019-19839
CVE-2019-19840
CVE-2019-19841
CVE-2019-19842
CVE-2019-19843
* Revised Homograph AttacksBy Tzachy Horesh ,
29-Dec 2019,
* Breaking Algorithms - SMT Solvers for WebApp SecurityBy Leo Goldstien ,
02-Sep 2019,
* Xiaomi Zigbee (3): Live DebuggingBy Lev Aronsky ,
15-Jul 2019,
* Xiaomi Zigbee (2): Beyond ArchitectureBy Lev Aronsky ,
09-Jul 2019,
* Xiaomi Zigbee (1): Getting to know the hardwareBy Lev Aronsky ,
01-Jul 2019,
* Running iOS in QEMU to an interactive bash shell (2): researchBy Jonathan Afek ,
25-Jun 2019,
* Running iOS in QEMU to an interactive bash shell (1): tutorialBy Jonathan Afek ,
17-Jun 2019,
* It takes only one StackOverflowException to bring down an Application deployed on IISBy Gil Mirmovitch ,
22-Oct 2018,
CVE-2018-8269
ALEPH-2018002
ALEPH-2018003
ALEPH-2018004
ALEPH-2018005
ALEPH-2018006
* Overcoming (some) Spectre browser mitigations By Noam Hadad & Jonathan Afek ,26-Jun 2018,
* Exploiting Qualcomm EDL Programmers (5): Breaking Nokia 6's SecureBoot
By Roee Hay & Noam Hadad ,22-Jan 2018,
QPSIIR-909
ALEPH-2017029
CVE-2017-13174
CVE-2017-5947
* Exploiting Qualcomm EDL Programmers (4): Runtime Debugger By Roee Hay & Noam Hadad ,22-Jan 2018,
QPSIIR-909
ALEPH-2017029
CVE-2017-13174
CVE-2017-5947
* Exploiting Qualcomm EDL Programmers (3): Memory-based Attacks &PBL Extraction
By Roee Hay & Noam Hadad ,22-Jan 2018,
QPSIIR-909
ALEPH-2017029
CVE-2017-13174
CVE-2017-5947
* Exploiting Qualcomm EDL Programmers (2): Storage-based Attacks &Rooting
By Roee Hay & Noam Hadad ,22-Jan 2018,
QPSIIR-909
ALEPH-2017029
CVE-2017-13174
CVE-2017-5947
* Exploiting Qualcomm EDL Programmers (1): Gaining Access & PBLInternals
By Roee Hay & Noam Hadad ,22-Jan 2018,
QPSIIR-909
ALEPH-2017029
CVE-2017-13174
CVE-2017-5947
* Untethered initroot (USENIX WOOT '17)By Roee Hay ,
30-Aug 2017,
CVE-2016-10277
A-62345923
* Nexus 9 vs. Malicious Headphones, Take TwoBy Roee Hay ,
13-Jun 2017,
CVE-2017-0648
CVE-2017-0510
CVE-2017-0563
CVE-2017-0582
* initroot: Hello MotoBy Roee Hay ,
07-Jun 2017,
CVE-2016-10277
* initroot: Bypassing Nexus 6 Secure Boot through Kernel Command-line InjectionBy Roee Hay ,
23-May 2017,
CVE-2016-10277
CVE-2017-1000363
* OnePlus OTAs: Analysis & ExploitationBy Roee Hay ,
11-May 2017,
CVE-2017-5948
CVE-2017-8850
CVE-2017-8851
CVE-2016-10370
* Owning OnePlus 3/3T with a Malicious Charger: The Last Piece ofthe Puzzle
By Roee Hay ,
26-Mar 2017,
CVE-2017-5622
CVE-2017-5626
CVE-2017-5624
* Attacking Nexus 9 with Malicious HeadphonesBy Roee Hay ,
08-Mar 2017,
CVE-2017-0510
CVE-2017-0563
CVE-2017-0582
* Owning a Locked OnePlus 3/3T: Bootloader VulnsBy Roee Hay ,
08-Feb 2017,
CVE-2017-5626
CVE-2017-5624
* Attacking Nexus 6/6P Custom Boot Modes By Roee Hay & Michael Goberman ,05-Jan 2017,
CVE-2016-8467
CVE-2016-6678
VULNS
*
12/17/19
ALEPH-2019014 Ruckus CLI (rkscli) jailbreak*
12/17/19
CVE-2019-19843 Admin credentials leakage*
12/17/19
CVE-2019-19842 Remote command injection via a crafted HTTP request (cmdSpectraAnalysis)*
12/17/19
CVE-2019-19841 Remote command injection via a crafted HTTP request (cmdPacketCapture)*
12/17/19
CVE-2019-19840 Stack buffer overflow in zapexecutable
*
12/17/19
CVE-2019-19839 Remote command injection via a crafted HTTP request (cmdImportCategory)*
12/17/19
CVE-2019-19838 Remote command injection via a crafted HTTP request (cmdImportAvpPort)*
12/17/19
CVE-2019-19837 Information disclosurevulnerability
*
12/17/19
CVE-2019-19836 Remote code execution vulnerability via zap*
12/17/19
CVE-2019-19835 SSRF vulnerability in zap*
12/17/19
CVE-2019-19834 Ruckus CLI (ruckus_cli2)jailbreak
*
10/22/18
ALEPH-2018006 Potential DOS vulnerability inWCF services
*
10/22/18
ALEPH-2018005 Potential DOS vulnerability in applications that use ASP.NET Web API*
10/22/18
ALEPH-2018004 Applications that use Newtonsoft.Json might be exposed to DOS vulnerability*
10/22/18
ALEPH-2018003 DOS vulnerability in Azure ActiveDirectory Graph API
*
10/22/18
ALEPH-2018002 DOS Vulnerability in SharePoint2016 Server
*
10/22/18
CVE-2018-8269 OData Denial of ServiceVulnerability
*
01/22/18
ALEPH-2017029 Nokia 6/5 EDL triggering throughUSB
*
01/22/18
QPSIIR-909 Qualcomm EDL Firehose Programmers Peek and Poke Primitives*
01/22/18
CVE-2017-13174 Google Nexus 6 & 6P EDL triggering through ADB*
01/22/18
CVE-2017-5947 OnePlus EDL triggering through ADB or Hardware Key Combination*
01/09/18
CVE-2017-0829 Motorola Bootloader Old UTAGs may lead to Kernel Command-line Injection*
08/30/17
A-62345923 Motorola Android Bootloader Unlocking a Re-locked Bootloader from Platform OSDetails
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0