Are you over 18 and want to see adult content?
Other Annotations

A complete backup of deceiveyour.team
Are you over 18 and want to see adult content?
More Annotations

A complete backup of www.demorgen.be/tv-cultuur/duffy-onthult-waarom-ze-in-2011-plots-stopte-met-zingen-ik-werd-gevangengehouden
Are you over 18 and want to see adult content?
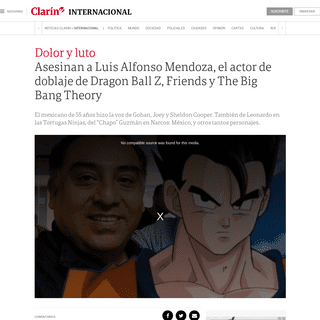
A complete backup of www.clarin.com/internacional/asesinan-luis-alfonso-mendoza-actor-doblaje-dragon-ball-z-friends-the-big-bang
Are you over 18 and want to see adult content?
Favourite Annotations

A complete backup of https://fxnewslive.com/moviesflix/
Are you over 18 and want to see adult content?
A complete backup of http://www.bseodisha.nic.in/
Are you over 18 and want to see adult content?

A complete backup of https://www.sbs.com.au/movies/
Are you over 18 and want to see adult content?
A complete backup of https://minuet.biz/ukraine/kiev/9978/ua/
Are you over 18 and want to see adult content?

A complete backup of https://libros.plus/the-sun-sister/
Are you over 18 and want to see adult content?

A complete backup of https://wiki.zoneminder.com/Ubiquiti
Are you over 18 and want to see adult content?
A complete backup of https://website.informer.com/v-s.mobi
Are you over 18 and want to see adult content?

A complete backup of https://tvserialsbd.blogspot.com/
Are you over 18 and want to see adult content?

A complete backup of https://getcouponsworld.com/gethotwiredcom
Are you over 18 and want to see adult content?

A complete backup of https://www.keyfora.com/search/webmail.com.cy
Are you over 18 and want to see adult content?
Text
Deceptive Security
*
* No menu assigned
_Press enter to begin your search_Programming
Walkthrough
DAILY CODING PROBLEM 1 — SOLUTION WALKTHROUGHBy Kevin Kirsche
| Programming
, Walkthrough
| No Comments
Buffer Overflow
Walkthrough
VULNSERVER KSTET WS2_32 RECV FUNCTION RE-USEBy Kevin Kirsche
| Buffer
Overflow ,
Walkthrough | 3
Comments
automation Walkthrough PATCHING A BINARY TO DISABLE ASLR USING PYTHONBy Kevin Kirsche
| automation
, Walkthrough
| No Comments
Buffer Overflow
Walkthrough
QUICKZIP 4.60.019 SEH BUFFER OVERFLOWBy Kevin Kirsche
| Buffer
Overflow ,
Walkthrough | No
Comments
Walkthrough
USING PYTHON’S STRUCT.PACK FUNCTION IN EXPLOIT DEVELOPMENTBy Kevin Kirsche
| Walkthrough
| No Comments
SLAE-x86
CREATING AN AES256-GCM SHELLCODE CRYPTERBy Kevin Kirsche
| SLAE-x86
| No Comments
SLAE-x86
CREATING 3 POLYMORPHIC SHELLCODE VARIANTS OF SHELL-STORM SAMPLESBy Kevin Kirsche
| SLAE-x86
| No Comments
SLAE-x86
ANALYZING METASPLOIT’S LINUX/X86/ADDUSER PAYLOADBy Kevin Kirsche
| SLAE-x86
| No Comments
SLAE-x86
ANALYZING METASPLOIT’S LINUX/X86/READ_FILE PAYLOADBy Kevin Kirsche
| SLAE-x86
| No Comments
SLAE-x86
ANALYZING METASPLOIT’S LINUX/X86/SHELL_FIND_TAG PAYLOADBy Kevin Kirsche
| SLAE-x86
| No Comments
1 2 3
Next
CATEGORIES
* automation
* Buffer Overflow
* Privilege Escalation * Privileged Exploit* Programming
* Public Exploit Release* SLAE-x86
* Walkthrough
* __
* __
� 2017–18 Deceptive Security — All Rights Reserved__
Details
Copyright © 2024 ArchiveBay.com. All rights reserved. Terms of Use | Privacy Policy | DMCA | 2021 | Feedback | Advertising | RSS 2.0